Professional Documents
Culture Documents
10th Semester - Information Technology Law - Part C
10th Semester - Information Technology Law - Part C
Uploaded by
Ajay Kumar0 ratings0% found this document useful (0 votes)
13 views5 pagesThe document discusses various issues related to the Information Technology Act of India. It addresses questions about unsolicited emails, defamation in online publications, the essential elements of a valid contract in a car parking transaction, financial crimes like unauthorized bank account debits, offensive online messages that could incite hatred or violence, punishments for hosting pornographic content online, software piracy, hacking of government websites, fraudulently acquiring sensitive information, hacking offenses by foreign nationals, and circumventing technological access controls for research purposes. The document examines these scenarios in the context of the relevant sections of the Information Technology Act.
Original Description:
Original Title
10th Semester - Information Technology Law -Part C
Copyright
© © All Rights Reserved
Available Formats
DOCX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThe document discusses various issues related to the Information Technology Act of India. It addresses questions about unsolicited emails, defamation in online publications, the essential elements of a valid contract in a car parking transaction, financial crimes like unauthorized bank account debits, offensive online messages that could incite hatred or violence, punishments for hosting pornographic content online, software piracy, hacking of government websites, fraudulently acquiring sensitive information, hacking offenses by foreign nationals, and circumventing technological access controls for research purposes. The document examines these scenarios in the context of the relevant sections of the Information Technology Act.
Copyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
Download as docx, pdf, or txt
0 ratings0% found this document useful (0 votes)
13 views5 pages10th Semester - Information Technology Law - Part C
10th Semester - Information Technology Law - Part C
Uploaded by
Ajay KumarThe document discusses various issues related to the Information Technology Act of India. It addresses questions about unsolicited emails, defamation in online publications, the essential elements of a valid contract in a car parking transaction, financial crimes like unauthorized bank account debits, offensive online messages that could incite hatred or violence, punishments for hosting pornographic content online, software piracy, hacking of government websites, fraudulently acquiring sensitive information, hacking offenses by foreign nationals, and circumventing technological access controls for research purposes. The document examines these scenarios in the context of the relevant sections of the Information Technology Act.
Copyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
Download as docx, pdf, or txt
You are on page 1of 5
10th Semester
Information Technology Law
Part C
1. Unsolicited emails are a menace. They should have a provision to unsubscribe them
or they may not be sent unless asked for. Many countries have enacted laws against
unsolicited mail known as Anti spam laws. Is the information technology act takes
care of such a problem? Discuss.
2. 'Dow Jones & Company incorporated' is the publisher of Wall street Journal. It also
publishes a magazine known as Barrons. This magazine is also put online on servers
maintained at New Jersey, USA. It carried an article 'Unholy Gains", which was
alleged to be defamatory to joseph Gutnick resident of Victoria, Australia. He filed a
suit for damages in Victoria. Preliminary objection was raised as to the
maintainability of the case in an Australian Court. Decide in the light of jurisdictional
issues and law.
3. A customer contacted with a car park machine representing the owner and he fed
his money into it and received a claim ticket for the purpose of parking of his car. Is
there a valid contract in this transaction? Explain how the essentials of a valid
contract are present in this transaction.
4. A bank employee inserts a program, into a bank's server, that deducts a small
amount of money, to say Rs.2/- a month, from the account of every customer. No
account holder probably notice this unauthorized debit, but the bank employee will
make a sizable amount of money every month. Discuss how the information
technology act handles such financial crimes.
5. Messages which are offensive to a particular religion, community, ethnic group or
political party are posted in a blog or a social networking site. Such messages might
have the effect of either inciting hatred in the minds of the people or communal
clashes between 2 groups. Is it an offence under the information technology act
2000? Examine.
6. A computer scientist accepts online payments and allows paying customers to view
or download pornographic pictures and videos from his website. Is it an offence
punishable under the information technology act,2000? Discuss the nature of
offence and the punishment for it.
7. In an Engineering college, private version of software is used in the computer lab. Is
there any violation of the Information technology act and the copyright act?
Examine.
8. The original homepage of a website belonging to a Government department is
substituted with another page by a computer miscreant. Disturbing images and
offensive phrases are displayed in the process. It affected the image of the
Government department. Are there adequate provisions under the information
technology act for counteracting this kind of problem? Examine.
9. Mr.'X' fraudulently acquires the sensitive information such as passwords and credit
card details and misrepresents himself and uses the parameters for his personal
purpose. What is the offence committed by Mr.X.
10. MR.X, a French national, sitting in paris hacked the computer system of M/S.Y
corporation India situated in Hyderabad. Whether Mr.X, a foreign national, can be
tried in India for the offence of hacking under the information technology act, 2000.
Discuss the legal position.
11. Mr.X, a research scholar,is pursuing his research after Ph.D. in law in Hyderabad.
For the purpose of his research he circumvents (unlocks) the technological
measures (locks) of an online database maker who deals with various E-Journals
online by 'Pay for use' method. Whether Mr.X is liable for committing any offence.
12.
You might also like
- Photography ContractDocument4 pagesPhotography ContractRocketLawyer78% (23)
- Module 2 Unified Course Pack CWTS 1 2021 2022Document13 pagesModule 2 Unified Course Pack CWTS 1 2021 2022Jelaine Bacatan CuestaNo ratings yet
- Contemporary Concepts of Management: Part OneDocument96 pagesContemporary Concepts of Management: Part OneJeffrey De BelenNo ratings yet
- A Book On Criminal Breach of Trust, Cheating and Cheque Dishonor Litigation by Nayeem Firoz (A Judge Working As The Member of Bangladesh Judicial Service)Document139 pagesA Book On Criminal Breach of Trust, Cheating and Cheque Dishonor Litigation by Nayeem Firoz (A Judge Working As The Member of Bangladesh Judicial Service)nayeem_8lawz100% (4)
- Cyber Security Law and Policies in IndiaDocument12 pagesCyber Security Law and Policies in Indiaindex PubNo ratings yet
- Unit 5Document18 pagesUnit 5Ashok KumarNo ratings yet
- Unit 4 and Unit 5 Class Notes - Cyber Security - 1518766008 PDFDocument12 pagesUnit 4 and Unit 5 Class Notes - Cyber Security - 1518766008 PDFkushwah_7701455660% (2)
- Cyber Law Research Paper TopicsDocument8 pagesCyber Law Research Paper Topicsafeawckew100% (1)
- Project Cyber CrimeDocument51 pagesProject Cyber CrimevesascNo ratings yet
- Cyber Law (NOTES FOR EXAM)Document56 pagesCyber Law (NOTES FOR EXAM)MrinalBhatnagarNo ratings yet
- Cyberspace Usages Challenges and Dispute ResolutionDocument32 pagesCyberspace Usages Challenges and Dispute ResolutionHarshita ChaturvediNo ratings yet
- Legal Regulation of Cyber Crimes in IndiaDocument9 pagesLegal Regulation of Cyber Crimes in IndiaSwarnaprava DashNo ratings yet
- Computer HackingDocument42 pagesComputer HackingsyahribayNo ratings yet
- Assignment 2Document3 pagesAssignment 2Ananya SinghNo ratings yet
- Cyber Crime and Law in India With Landmark JudgementsDocument4 pagesCyber Crime and Law in India With Landmark JudgementsSamataNo ratings yet
- Q1: Homework (Week 10 Application) 2-3 Pages 3 References: Cyber Security VL Case StudyDocument17 pagesQ1: Homework (Week 10 Application) 2-3 Pages 3 References: Cyber Security VL Case StudyFarhan Sheikh MuhammadNo ratings yet
- Bite of The Crackers: Computing. Manila, Philippines: Mindshapers Co., Inc. (Chapter 5 - Computer HackersDocument9 pagesBite of The Crackers: Computing. Manila, Philippines: Mindshapers Co., Inc. (Chapter 5 - Computer HackersJay BermudezNo ratings yet
- Computers and The Law Luis JoseDocument7 pagesComputers and The Law Luis Josesheillah0803No ratings yet
- Cybercrime ActDocument5 pagesCybercrime ActRhon NunagNo ratings yet
- Sheetal Garg - Cyber ComplaintDocument3 pagesSheetal Garg - Cyber Complaintsanjana sethNo ratings yet
- FRB Im Dict3 Icte 10083 Lesson-4-Lesson-6Document36 pagesFRB Im Dict3 Icte 10083 Lesson-4-Lesson-6benceldominguez2No ratings yet
- 6 CyberLawsDocument11 pages6 CyberLawsPranzalNo ratings yet
- It ProjectDocument6 pagesIt Projectruchika singhNo ratings yet
- Answer IMPORTANT QUESTIONS REVISIONDocument9 pagesAnswer IMPORTANT QUESTIONS REVISIONMohd ShifanNo ratings yet
- Changes Required in The Amended IT Act, 2000Document7 pagesChanges Required in The Amended IT Act, 2000Adv (Dr.) Prashant MaliNo ratings yet
- Cyber Crimes and Legal ImplicationsDocument3 pagesCyber Crimes and Legal ImplicationsashaNo ratings yet
- IPR & Cyber Laws ManualDocument28 pagesIPR & Cyber Laws ManualAnshuman Biswas73% (22)
- Role of Intellectual Property in CyberspaceDocument5 pagesRole of Intellectual Property in Cyberspacetanish guptaNo ratings yet
- 2.jurisdictional Issues in Adjudication of Cyber Crimes PDFDocument29 pages2.jurisdictional Issues in Adjudication of Cyber Crimes PDFAshish BomzanNo ratings yet
- What Was The Violation Committed Under The Data Privacy Act of 2012?Document3 pagesWhat Was The Violation Committed Under The Data Privacy Act of 2012?Fuertes, CyrillNo ratings yet
- <!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/html4/loose.dtd"> <HTML><HEAD><META HTTP-EQUIV="Content-Type" CONTENT="text/html; charset=iso-8859-1"> <TITLE>ERROR: The requested URL could not be retrieved</TITLE> <STYLE type="text/css"><!--BODY{background-color:#ffffff;font-family:verdana,sans-serif}PRE{font-family:sans-serif}--></STYLE> </HEAD><BODY> <H1>ERROR</H1> <H2>The requested URL could not be retrieved</H2> <HR noshade size="1px"> <P> While trying to process the request: <PRE> TEXT http://www.scribd.com/titlecleaner?title=CyberCrime+Report.docx HTTP/1.1 Host: www.scribd.com Proxy-Connection: keep-alive Accept: */* Origin: http://www.scribd.com X-CSRF-Token: ea5b3d74fc35283c15ef440947b36a61b715cffd User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.31 (KHTML, like Gecko) Chrome/26.0.1410.64 Safari/537.31 X-Requested-With: XMLHttpRequest Referer: http://www.scribd.com/upload-document Accept-Encoding: gzip,deflDocument32 pages<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/html4/loose.dtd"> <HTML><HEAD><META HTTP-EQUIV="Content-Type" CONTENT="text/html; charset=iso-8859-1"> <TITLE>ERROR: The requested URL could not be retrieved</TITLE> <STYLE type="text/css"><!--BODY{background-color:#ffffff;font-family:verdana,sans-serif}PRE{font-family:sans-serif}--></STYLE> </HEAD><BODY> <H1>ERROR</H1> <H2>The requested URL could not be retrieved</H2> <HR noshade size="1px"> <P> While trying to process the request: <PRE> TEXT http://www.scribd.com/titlecleaner?title=CyberCrime+Report.docx HTTP/1.1 Host: www.scribd.com Proxy-Connection: keep-alive Accept: */* Origin: http://www.scribd.com X-CSRF-Token: ea5b3d74fc35283c15ef440947b36a61b715cffd User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.31 (KHTML, like Gecko) Chrome/26.0.1410.64 Safari/537.31 X-Requested-With: XMLHttpRequest Referer: http://www.scribd.com/upload-document Accept-Encoding: gzip,deflUttam KumarNo ratings yet
- Cyber Crime-Awareness and Security: A. IntroductionDocument16 pagesCyber Crime-Awareness and Security: A. IntroductionBhumikaNo ratings yet
- Unit-Iv Cyber-Crime and The Legal Landscape Around The WorldDocument20 pagesUnit-Iv Cyber-Crime and The Legal Landscape Around The WorldayushNo ratings yet
- Cyber Crime Essay ThesisDocument4 pagesCyber Crime Essay Thesisafcmausme100% (2)
- Cyber LawDocument7 pagesCyber LawSiva SrinivasanNo ratings yet
- AWR-168-W - Module 2 Post TestDocument8 pagesAWR-168-W - Module 2 Post TestshaamimahmedNo ratings yet
- Laws Against Hacking in IndiaDocument28 pagesLaws Against Hacking in IndiaUjjwal Mani TripathiNo ratings yet
- Cyber Crime Dissertation IdeasDocument6 pagesCyber Crime Dissertation IdeasPaperWritersCollegeSingapore100% (1)
- Cyber LawDocument7 pagesCyber LawJyoti BhutiaNo ratings yet
- Cyber Crime - Article / Case: Prepared By: Shabbir Shaikh Mba 1 Year Roll No. 135Document21 pagesCyber Crime - Article / Case: Prepared By: Shabbir Shaikh Mba 1 Year Roll No. 135shabbirNo ratings yet
- Institute of Law: Jiwaji University, Gwalior, (M.P.)Document24 pagesInstitute of Law: Jiwaji University, Gwalior, (M.P.)Adv Vinayak KamalNo ratings yet
- Institute of Law: Jiwaji University, Gwalior, (M.P.)Document24 pagesInstitute of Law: Jiwaji University, Gwalior, (M.P.)Adv Vinayak KamalNo ratings yet
- Institute of Law: Jiwaji University, Gwalior, (M.P.)Document24 pagesInstitute of Law: Jiwaji University, Gwalior, (M.P.)Adv Vinayak KamalNo ratings yet
- Module 3 and 4 Question Bank - CSPL - SolutionDocument16 pagesModule 3 and 4 Question Bank - CSPL - SolutionDeeksha ReddyNo ratings yet
- Research Paper About Computer CrimesDocument8 pagesResearch Paper About Computer Crimesaflbtlzaw100% (1)
- The Internet and Public Policy: Criminal Activity On The InternetDocument12 pagesThe Internet and Public Policy: Criminal Activity On The InternetJohnson SmithNo ratings yet
- Chapter Six: Electronic Commerce: Financial Concerns, Legal and Ethical IssuesDocument16 pagesChapter Six: Electronic Commerce: Financial Concerns, Legal and Ethical IssuesMiki MikiNo ratings yet
- Pecl Assign 3 MaterialDocument16 pagesPecl Assign 3 MaterialParag PiprewarNo ratings yet
- Offences & Penalties Under The IT Act, 2000Document10 pagesOffences & Penalties Under The IT Act, 2000natashaNo ratings yet
- Term Paper CybercrimeDocument8 pagesTerm Paper Cybercrimeaflskkcez100% (1)
- Research Paper On Cybercrime LawDocument7 pagesResearch Paper On Cybercrime Lawfvf237cz100% (1)
- An Overview On Cyber LawsDocument6 pagesAn Overview On Cyber LawsAjita AnanyaNo ratings yet
- Constitutional MalwareDocument43 pagesConstitutional MalwareAnonymous lVC1HGpHP3No ratings yet
- Tracing The Development of "Intermediary Liabilit 2Document7 pagesTracing The Development of "Intermediary Liabilit 2Madhav ZoadNo ratings yet
- IT Project LLMDocument23 pagesIT Project LLMsoumilNo ratings yet
- CYBER LAW Notes MBADocument6 pagesCYBER LAW Notes MBADipon GhoshNo ratings yet
- Philippines Cybercrime Law PaperDocument2 pagesPhilippines Cybercrime Law PaperPaul Claro CágroNo ratings yet
- Dos Donts of E-Commerce TransactionsDocument11 pagesDos Donts of E-Commerce Transactionsnupur jhodNo ratings yet
- IDENTITY THEFT - ExtraDocument19 pagesIDENTITY THEFT - ExtrapriyaNo ratings yet
- Cyber Unit-04Document15 pagesCyber Unit-04adityahammad02No ratings yet
- Study On Cyber Law's of IndiaDocument7 pagesStudy On Cyber Law's of IndiaIJRASETPublicationsNo ratings yet
- CybersecurityDocument6 pagesCybersecurityblogsbyzmNo ratings yet
- Data Protection Law in IndiaDocument5 pagesData Protection Law in Indiaayush2657No ratings yet
- Cyber LawDocument4 pagesCyber LawnovaNo ratings yet
- Kyoto ProtocolDocument18 pagesKyoto Protocolcoolfaiz3100% (1)
- Eh 401 SG Mod 3 Complete Oblicon Rev TransDocument44 pagesEh 401 SG Mod 3 Complete Oblicon Rev TransEfrean BianesNo ratings yet
- Protests in The 1930s: Debbion Hyman, ContributorDocument6 pagesProtests in The 1930s: Debbion Hyman, ContributorMikaelia NesbethNo ratings yet
- Percentage Boq: Validate Print HelpDocument6 pagesPercentage Boq: Validate Print HelpSatish KumarNo ratings yet
- Academic Integrity Guide 2022Document18 pagesAcademic Integrity Guide 2022HAIQING GAONo ratings yet
- United States v. Frazier Derring, 4th Cir. (2016)Document3 pagesUnited States v. Frazier Derring, 4th Cir. (2016)Scribd Government DocsNo ratings yet
- Illustrated Parts Catalog JT15DDocument904 pagesIllustrated Parts Catalog JT15Dmarco.alvarezNo ratings yet
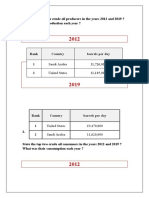
- State The Top Two Crude Oil Producers in The Years 2012 and 2019 ? What Was Their Production Each Year ?Document6 pagesState The Top Two Crude Oil Producers in The Years 2012 and 2019 ? What Was Their Production Each Year ?laoy aolNo ratings yet
- Offer Letter Delivery ExecutiveDocument3 pagesOffer Letter Delivery Executiveajinkyadiwakar717No ratings yet
- Legal Notice and ReplyDocument6 pagesLegal Notice and ReplyMystic ClashNo ratings yet
- USA Vs US IncDocument20 pagesUSA Vs US IncAbusaeed IrfanNo ratings yet
- KROKOTAK PRINT! - Printables For KidsDocument2 pagesKROKOTAK PRINT! - Printables For KidsFazekas AnnaNo ratings yet
- Laperal vs. RepublicDocument4 pagesLaperal vs. RepublicQueenie SabladaNo ratings yet
- (Bme - Group 3) Financial-Transaction-Worksheet-Sweet-Sea-Restaurant-Answers-1-4Document13 pages(Bme - Group 3) Financial-Transaction-Worksheet-Sweet-Sea-Restaurant-Answers-1-4Kyla Marie BayanNo ratings yet
- Notice To Chief Justice and Registrar of The Constitional CourtDocument2 pagesNotice To Chief Justice and Registrar of The Constitional CourtJoseph crnkovicNo ratings yet
- 2021 Revised Medical Assistance Application FormDocument2 pages2021 Revised Medical Assistance Application FormImelda Garais0% (1)
- FY FC Project NoticeDocument2 pagesFY FC Project NoticeMinakshi SharmaNo ratings yet
- Glimpses in The History of Occidental MindoroDocument94 pagesGlimpses in The History of Occidental MindoroRiu CarbonillaNo ratings yet
- MontesquieuDocument36 pagesMontesquieuClestine JuanNo ratings yet
- A Strategy For Effective Asset TracingDocument5 pagesA Strategy For Effective Asset TracingOnoriode OnakpoberuoNo ratings yet
- Kumar Vishwas 2012 7 PDFDocument10 pagesKumar Vishwas 2012 7 PDFHimanshu BahugunaNo ratings yet
- Joint - DisinterestedDocument2 pagesJoint - DisinterestedRichard DaliyongNo ratings yet
- 152-Article Text-818-1-10-20201031 PDFDocument11 pages152-Article Text-818-1-10-20201031 PDFputri525No ratings yet
- Course 1.2: What You Should KnowDocument27 pagesCourse 1.2: What You Should KnowGeorgios MilitsisNo ratings yet
- GR No. 127347, November 25, 1999Document5 pagesGR No. 127347, November 25, 1999Sherilyn Dela CruzNo ratings yet
- Management Accounting Solman CabreraDocument456 pagesManagement Accounting Solman CabreraAnnie Rapanut100% (2)