Professional Documents
Culture Documents
Lab 07 - Working With Windows Processes
Lab 07 - Working With Windows Processes
Uploaded by
Trường Khang PhạmCopyright:
Available Formats
You might also like
- PERFORMING COMPUTER OPERATIONS (PCO) LO4 (TLE - IACSS9-12PCO-If-7)Document12 pagesPERFORMING COMPUTER OPERATIONS (PCO) LO4 (TLE - IACSS9-12PCO-If-7)Dianne Brucal - Matibag63% (8)
- Student Exploration - Weight and Mass (ANSWER KEY)Document3 pagesStudent Exploration - Weight and Mass (ANSWER KEY)Jaila Palmer [STUDENT]No ratings yet
- J0304201134 - J0304201060 - Pertemuan 2Document11 pagesJ0304201134 - J0304201060 - Pertemuan 2IvandenerolNo ratings yet
- Penetrating Windows 8 With Syringe UtiliDocument5 pagesPenetrating Windows 8 With Syringe UtiliAGBADAN Yao EricNo ratings yet
- UntitledDocument14 pagesUntitledsufiyanNo ratings yet
- What Are The SysInternals Tools and How Do You Use ThemDocument129 pagesWhat Are The SysInternals Tools and How Do You Use ThemaaronNo ratings yet
- Art of Anti DetectionDocument41 pagesArt of Anti DetectionGyamba Dukpa100% (1)
- Malware AnalysisDocument21 pagesMalware AnalysisAyush rawal100% (1)
- Art of Anti DetectionDocument34 pagesArt of Anti DetectionViineeNo ratings yet
- Module 07 Windows ForensicsDocument19 pagesModule 07 Windows ForensicsShaik Abdul Muneer100% (1)
- Dumping Code For Spying and Windows ToolsDocument13 pagesDumping Code For Spying and Windows ToolsRahul GandhiNo ratings yet
- Appdata GpoDocument4 pagesAppdata GpoEurípedes OliveiraNo ratings yet
- Unpacking Process Hollowing 671 690Document21 pagesUnpacking Process Hollowing 671 690Đồng Xuân ThànhNo ratings yet
- When Applications Crash Part I - WatsonDocument5 pagesWhen Applications Crash Part I - WatsonNagarjuna ReddyNo ratings yet
- WelcomeDocument23 pagesWelcomeabiramanNo ratings yet
- Further Readings: Check Your ProgressDocument22 pagesFurther Readings: Check Your Progresstamil selviNo ratings yet
- Unit 14: A. Reading Comprehension - 5 Operating Systems: Hidden SoftwareDocument4 pagesUnit 14: A. Reading Comprehension - 5 Operating Systems: Hidden SoftwareMuhammad Rizky Andriansyah SurataNo ratings yet
- Identify Running ProcessesDocument2 pagesIdentify Running ProcessesPrince NagacNo ratings yet
- The Windows Process JourneyDocument28 pagesThe Windows Process JourneyPremNo ratings yet
- Name: Grade/Score: Year/ Section/ Row #: DateDocument1 pageName: Grade/Score: Year/ Section/ Row #: DateLouella Jane Racho MartinezNo ratings yet
- Debugging Esc 468Document10 pagesDebugging Esc 468bharat013@gmail.comNo ratings yet
- Solomon Windows Internals TroubleshootingDocument106 pagesSolomon Windows Internals Troubleshootingjavier.4evermlcNo ratings yet
- Kali 5Document10 pagesKali 5michal hanaNo ratings yet
- 3.2.11 Lab - Exploring Processes, Threads, Handles, and Windows RegistryDocument4 pages3.2.11 Lab - Exploring Processes, Threads, Handles, and Windows Registrytinod18399No ratings yet
- ICT-CSS-12 Q1 W2 Mod 4Document16 pagesICT-CSS-12 Q1 W2 Mod 4AJ Bacarisas RochaNo ratings yet
- (InfoAcademy) CyberOpsAssociate-Lab 2 - Explore Windows Operating SystemDocument12 pages(InfoAcademy) CyberOpsAssociate-Lab 2 - Explore Windows Operating SystemChip CiprianNo ratings yet
- Vera ManualDocument13 pagesVera Manualdamner4No ratings yet
- What Is Computer Systems Servicing (CSS NCII) ?Document12 pagesWhat Is Computer Systems Servicing (CSS NCII) ?Jen PequitNo ratings yet
- Software CrackingDocument6 pagesSoftware CrackingNavneet NarwariyaNo ratings yet
- What Is Computer Systems Servicing (CSS NCII) ?Document11 pagesWhat Is Computer Systems Servicing (CSS NCII) ?rezhablo100% (1)
- SCTS 242: Network Intrusion Detection and Penetration TestingDocument21 pagesSCTS 242: Network Intrusion Detection and Penetration TestingAbraham AmselNo ratings yet
- Ankush ThakurDocument174 pagesAnkush Thakursoniya tewatiaNo ratings yet
- System Administration (Part 1) : Example Case QuestionsDocument8 pagesSystem Administration (Part 1) : Example Case QuestionsMay Thu HanNo ratings yet
- The Windows Process Journey: by Dr. Shlomi BoutnaruDocument39 pagesThe Windows Process Journey: by Dr. Shlomi Boutnaruhamid reza NasrNo ratings yet
- Mca SynopsisDocument28 pagesMca SynopsisRajbeer Kumar DasNo ratings yet
- Getting Full Speed With DelphiDocument25 pagesGetting Full Speed With DelphiDavis MontenegroNo ratings yet
- LAB1Document6 pagesLAB1Yenna CayasaNo ratings yet
- Sap InterviewDocument2 pagesSap InterviewMohammed AseemNo ratings yet
- Penetration Testing ReportDocument25 pagesPenetration Testing Reportmatifj4n0987No ratings yet
- Putting Registry-/system-Cleanup Apps To The TestDocument8 pagesPutting Registry-/system-Cleanup Apps To The TestBill LeeNo ratings yet
- 110 - Exp - 2 - Updated 2Document4 pages110 - Exp - 2 - Updated 2hhcqfvj9kcNo ratings yet
- Csol570-Module 7Document14 pagesCsol570-Module 7api-694098467No ratings yet
- Introduction and SRS: Chapter-1Document38 pagesIntroduction and SRS: Chapter-1Akash MishraNo ratings yet
- Settlement DeedDocument9 pagesSettlement DeedSubramani SakthivelNo ratings yet
- DXWND ManualDocument31 pagesDXWND ManualHannah Mara TaiNo ratings yet
- CO1508 Computer Systems & Security - Week 10: Building Your Harmless Virus in C++ - Part 1 Windows RegistryDocument8 pagesCO1508 Computer Systems & Security - Week 10: Building Your Harmless Virus in C++ - Part 1 Windows RegistryEdward LeeNo ratings yet
- Cài đặt phần mềm Nessus trên backtrackDocument8 pagesCài đặt phần mềm Nessus trên backtrackthanglxNo ratings yet
- Introduction To Endpoint HuntingDocument88 pagesIntroduction To Endpoint HuntingmadhugoudaNo ratings yet
- OSY Solved Manual @diploma - WorldDocument160 pagesOSY Solved Manual @diploma - Worldcm4i10 Aditya baramde100% (6)
- Everyone Who Writes CodeDocument8 pagesEveryone Who Writes CodeFenil DesaiNo ratings yet
- Porting OSE Systems To LinuxDocument39 pagesPorting OSE Systems To Linuxclu5t3rNo ratings yet
- Sec401 Windows Linux Tutorial v1Document41 pagesSec401 Windows Linux Tutorial v1Snig KavNo ratings yet
- Desktop Support Engineer Interview Questions and AnswersDocument7 pagesDesktop Support Engineer Interview Questions and AnswersjosephNo ratings yet
- AplusCore2 DemoCramnotesDocument44 pagesAplusCore2 DemoCramnotesWayne WayneNo ratings yet
- Material of cs101Document64 pagesMaterial of cs101Zain AliNo ratings yet
- Page12 ToolboxDocument2 pagesPage12 ToolboxAruna GunatilakeNo ratings yet
- Hostel Management System Project Report.Document61 pagesHostel Management System Project Report.Kamal AcharyaNo ratings yet
- Wmic Trick O HackerDocument12 pagesWmic Trick O HackerjoseanNo ratings yet
- Windows 1693667965753Document57 pagesWindows 1693667965753Sandro MeloNo ratings yet
- Lab 2Document132 pagesLab 2mrsploogeNo ratings yet
- DCS Operating InstructionsDocument80 pagesDCS Operating InstructionsJavierNo ratings yet
- Compliance Factors Associated With Contact Lens-Related Dry EyeDocument6 pagesCompliance Factors Associated With Contact Lens-Related Dry EyeAlda Gitu RahmaNo ratings yet
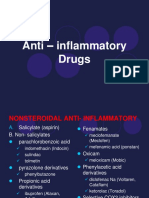
- 5 Anti - Inflammatory Drugs, Anti-Gout DrugsDocument15 pages5 Anti - Inflammatory Drugs, Anti-Gout DrugsAudrey Beatrice ReyesNo ratings yet
- Arunraj. N: Executive - Regional HRDocument3 pagesArunraj. N: Executive - Regional HRELAVAZHUTHINo ratings yet
- Pengaruh Pemberian Latihan Peregangan Terhadap PenDocument20 pagesPengaruh Pemberian Latihan Peregangan Terhadap PenBang DeanNo ratings yet
- What Is The Poet's Appeal To The People? Ans. The Poet Appeals To All TheDocument35 pagesWhat Is The Poet's Appeal To The People? Ans. The Poet Appeals To All Thecbs123abcNo ratings yet
- BRAINSTORMING: Key Take Aways: Tourism Systems and Models 2020Document4 pagesBRAINSTORMING: Key Take Aways: Tourism Systems and Models 2020Keith Loren ChavezNo ratings yet
- Connectors RephrasingDocument2 pagesConnectors RephrasingsoniaNo ratings yet
- Class II Subdivision Treatment With The Forsus Fatigue Resistant Device Vs Intermaxillary ElasticsDocument6 pagesClass II Subdivision Treatment With The Forsus Fatigue Resistant Device Vs Intermaxillary ElasticshemaadriNo ratings yet
- Digital Design: VerilogDocument92 pagesDigital Design: Verilogee206023No ratings yet
- The White Image in The Black Mind ReviewDocument87 pagesThe White Image in The Black Mind ReviewKhary Pestaina100% (5)
- Works by Others in Your Essay Edit 1Document5 pagesWorks by Others in Your Essay Edit 1api-667143998No ratings yet
- Simplified Primary Songs From FriendDocument60 pagesSimplified Primary Songs From Friendplay88No ratings yet
- Depreciation Calculation in ExcelDocument8 pagesDepreciation Calculation in ExcelVasanth Kumar VNo ratings yet
- Ed 242 Activity Creating Online FormDocument3 pagesEd 242 Activity Creating Online FormJane Marie Albios TevesNo ratings yet
- NCF - 2015 - Npe - 1986Document20 pagesNCF - 2015 - Npe - 1986sanchitNo ratings yet
- antiheroDocument1 pageantiheroRakesh KumarNo ratings yet
- 11 Partnership DissolutionDocument10 pages11 Partnership DissolutionBabamu Kalmoni JaatoNo ratings yet
- Report On Han Fei Zi and The Legalist SchoolDocument4 pagesReport On Han Fei Zi and The Legalist SchoolEmmarlone96No ratings yet
- Art of Emerging EuropeDocument11 pagesArt of Emerging EuropeShane PajaberaNo ratings yet
- Kibor HistoryDocument3 pagesKibor HistorymaheenwarisNo ratings yet
- Electrochemistry in Ionic Liquids Vol 2Document279 pagesElectrochemistry in Ionic Liquids Vol 2Dairo CANo ratings yet
- Fybcom Sem 1 Module 3 EntrepreneurshipDocument13 pagesFybcom Sem 1 Module 3 EntrepreneurshipRahul ChoudharyNo ratings yet
- The Architects of Islamic CivilizationDocument372 pagesThe Architects of Islamic Civilizationlazut273No ratings yet
- English - The SeaDocument1 pageEnglish - The SeaRohan PritchardNo ratings yet
- Maoism in Bangla PDFDocument15 pagesMaoism in Bangla PDFAyub Khan JrNo ratings yet
- FlightDocument2 pagesFlightRich BaguiNo ratings yet
- GeniE UM Vol4 APP C2 AISC9thDocument11 pagesGeniE UM Vol4 APP C2 AISC9thBRIJITHNo ratings yet
- International Conference Technology and Engineering (MARTECH)Document9 pagesInternational Conference Technology and Engineering (MARTECH)Farah Mehnaz HossainNo ratings yet
Lab 07 - Working With Windows Processes
Lab 07 - Working With Windows Processes
Uploaded by
Trường Khang PhạmCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Lab 07 - Working With Windows Processes
Lab 07 - Working With Windows Processes
Uploaded by
Trường Khang PhạmCopyright:
Available Formats
1
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
GETTING STARTED
You are required to do a couple of different experiments to understand how processes
work and understand them better. The skills acquired in this lab will be later used when
doing malware analysis and it could also be used if you are doing threat hunting too.
NOTE(S):
1. PLEASE DO NOT RUN THESE SAMPLES ON OTHER NETWORKS.
2. The samples for this lab are in Lab_4_1.7z (password = infected)
The goals of this lab are to:
• Further understand the different Process Explorer properties and settings, what
they mean, and how to benefit from them.
• Understand more about threads and processes with network connections.
• Searching for strings in program image files and memory.
• Understand the different Windows sessions.
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
GETTING STARTED
By the end of the lab, you should have a better understanding of Windows processes,
threads, how to find strings in the image file and in memory, processes with network
connections, and the different Windows sessions and what each one is used for. You will
also have the ability to spot a suspicious process that tries to use a common Windows
process name.
• Sysinternals Process Explorer (procexp.exe)
• Sysinternals PsExec
• Process Hacker
• Windows Netcat
Make sure you have the VPN files ready to connect to the HERA lab environment.
Lab Network:
• You:
o IP: 192.168.210.10
• RDP Credentials:
o Username: AdminELS
o Passwords: Nu3pmkfyX
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
GETTING STARTED
To continue our understanding about Windows Processes, use Process Explorer to answer
the questions below. Some questions require you to do some research.
1. What do processes in pink represent?
2. Why are there two csrss.exe?
3. Which ports is your explorer.exe listening on? Is that normal, and why?
4. How many threads does your System Idle Process have and why?
Determine how strings found while doing static analysis can help you with your analysis.
What if the malware sample you are working on is obfuscated so the strings cannot be found
during a basic search? This is one way of using the process’s memory to help us in our
analysis.
Note: There are three experiments to help you understand this task.
Use netcat to run an experiment and determine how the netcat listener on port 9999 can be
seen in a process monitoring tool such as process explorer.
Note: There is an experiment that will help you understand this task.
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
GETTING STARTED
In this task, we want to understand what Windows sessions are and how to interact with
them.
Note: There is an experiment that will help you understand this task.
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
Below, you can find solutions for each task. Remember though, that you can follow your
own strategy, which may be different from the one explained in the following lab.
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
SOLUTIONS – TASK #1
Let’s start by answering the questions given:
1. When we open Process Explorer, we can see that there are some processes in pink,
which represent based on procexp.exe’s documentation Windows services. Children
of these processes may be launched in a different color, as shown in Figure 2.1.
Figure 2.1 – Color Selection
This list of colors is found by going to Options → Colors selection.
2. The reason there are two Client Server Runtime (csrss.exe) processes running is
because there will be one (csrss.exe) for the system and then one for each user that
is logged into the machine. If there are two users logged into a machine, there would
be three csrss.exe processes. It would be suspicious if any one user had multiple
instances running. Csrss.exe is used for “Console Windows, creating and/or deleting
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
SOLUTIONS – TASK #1
threads, and some parts of the 16-bit virtual MS-DOS environment.” The details of
each process are shown in Figures 2.2 and 2.3, respectively.
Figure 2.2 – Details of System csrss.exe Instance
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
SOLUTIONS – TASK #1
Figure 2.3 – Details of Client csrss.exe Instance
Make sure you remember the full path to the csrss.exe program location and can
identify the parent of this process. The process IDs might be different, but they will
both show no parent name.
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
SOLUTIONS – TASK #1
Now, you might be asking “but how did you know which one is for the system and
which is for the client?” The answer is, if we check the Security tab, we can see under
which session each one of them is running. Our system’s instance is running under
Session 0, as shown in Figure 2.4, while the client’s instance is running under Session
1, as shown in Figure 2.5.
Figure 2.4 – System csrss.exe Instance in Session 0
Figure 2.5 – Client csrss.exe Instance in Session 1
Both csrss.exe processes are running under the user account named NT
AUTHORITY\SYSTEM which has the SID S-1-5-18. Remember these details, as they
are very important in case you are working on malware that is trying to run as a
csrss.exe process.
10
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
SOLUTIONS – TASK #1
3. Now, this is a good question about Explorer.exe, since this process is always running
when a user is logged into the system, it makes it a great target by attackers to inject
their shellcode and run it from there, why? Because again, it’s always running. So, if
we find an explorer.exe listening on some port or even some connections going out of
it, this means it is probably running some injected code. If we double click on
Explorer.exe, we can see the general process details in Figure 2.6.
Figure 2.6 – Explorer.exe Details
11
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
SOLUTIONS – TASK #1
Before going to the TCP/IP tab to answer the question, you should make sure you
notice that this process does not have a parent, since the parent launches explorer.exe
and terminates itself, it is running under the context of the user that is logged into the
system, and also this process is running in session 1, as shown in Figure 2.7.
Figure 2.7 – Explorer.exe Security Details
Now, go to the TCP/IP tab on the process details page as shown in Figure 2.8. We will
find that there is nothing listening there, which is the normal state of this process.
Figure 2.8 – Explorer.exe TCP/IP Details
12
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
SOLUTIONS – TASK #1
Explorer.exe should spawn the user’s programs, and nothing else. These siblings (or
child programs) can have listening ports, but explorer.exe itself should not. This is
true even if there are network shares that explorer.exe can access!
Another important detail to keep in mind, is explorer.exe runs out of
\%Systemroot%\Explorer.exe which is defined in the Windows Registry Key:
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\Shell
So, if you find the explorer on a system is not running out of system root and making
TCP/IP connections? Then it should be checked, since this is not normal at all!
Let’s do another test to understand cmd.exe processes a little. Open cmd.exe and
write down the process details. An instance of cmd.exe and it’s conhost.exe are
shown in Figure 2.9; in Figure 2.10, we can see the process details.
Figure 2.9 – Cmd.exe in Process Explorer
As shown, the cmd.exe has a process ID 6096 and the console host (conhost.exe) has
a process ID of 3656. Also, it is not only shown in Figure 2.9 that cmd.exe’s parent is
actually explorer.exe, but we can prove that from the cmd.exe details in Figure 2.10,
which shows that the explorer.exe is actually the parent of cmd.exe and it has the
3828 process ID.
13
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
SOLUTIONS – TASK #1
Figure 2.10 – Cmd.exe Details
Then, while in the command prompt, type cmd.exe again. What happened?
A new cmd.exe process is created, which is shown in Figure 2.11.
14
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
SOLUTIONS – TASK #1
Figure 2.11 – 2nd Cmd.exe Listed in Process Explorer
Is this another process or is it still the same process ,and do they match? Well, yes
this is another new process, but its parent is cmd.exe as shown in Figure 2.11 and is
proven by checking the new cmd.exe’s process details, which is shown in 2.12. We
can see that the cmd.exe ,which has a process ID of 3060, is the parent of the
cmd.exe that has the process ID 4400.
15
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
SOLUTIONS – TASK #1
Figure 2.12 – 2nd Cmd.exe Details
Now, while they are both running the same executable image, they do not match,
because each one of them is a different process with its own different details.
16
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
SOLUTIONS – TASK #2
Feel free to do your experiments differently, the steps below are how I covered them, and I
hope they will help you understand the idea behind them.
EXPERIMENT #1
1. Double click on the program welcome.exe and record the process details. In my
case the details are shown in Figure 3.1.
Figure 3.1 – Welcome.exe Message Box and Process Details
17
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
SOLUTIONS – TASK #2
2. Now, go to the Strings tab and search for the text that is displayed for you in the
image. This are shown in Figure 3.2.
Figure 3.2 – Searching for Strings in Welcome.exe Image / Found
If you ask me did, I find the text? The answer, as shown in Figure 3.6, is yes. The
reason why I was able to find it, is because this string is part of the executable image
itself. Plus, that, the string is easily searched using tools we saw in our static analysis
18
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
SOLUTIONS – TASK #2
module. Also, if you look closely, you will not only see the “eLearnSecurity MAP”
string, but even the “Welcome to” string that is displayed in the message box.
Finally, if we search in the memory, we should also be able to find the string there
too. Check it out yourself.
EXPERIMENT #2
1. Open notepad.exe and write any text in it and save it as elsmapfile.txt. The process
details are shown in Figure 3.3 and are listed in ProcExp.exe as shown in Figure 3.4.
Figure 3.3 – Notepad.exe Process Details
19
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
SOLUTIONS – TASK #2
Figure 3.4 – Notepad.exe Process in Process Explorer
2. Now go to the Strings tab. Do a search for the file name you just created.
a. Did you find the file name? Why?
As shown in Figure 3.5, we couldn’t find the string, because it is not part of
the notepad.exe image file.
20
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
SOLUTIONS – TASK #2
Figure 3.5 – Searching Notepad.exe Strings for file name / Not Found
b. On the same Strings tab, select the Memory option and search again. Did you
find the file name?
Yes, as shown in Figure 3.6.
21
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
SOLUTIONS – TASK #2
Figure 3.6 – Searching Notepad.exe Strings for file name / Found
c. How do you think this could help us when dealing with Malware?
It will help us understand that if there is some information which is not part
of the image file (EXE) or only available after running the program, then we
can search the memory for that information. Whatever is hidden in the
executable itself is exposed in memory if we know where and how to search
22
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
SOLUTIONS – TASK #2
for it. Keep in mind that not all strings are searched for this way, but this is
just one way of doing things.
EXPERIMENT #3:
This time do the same thing, but by starting the program welcome2.exe and searching for
the strings you saw in the message box. In my case that is shown in Figure 3.7.
Figure 3.7 – Searching Welcome2.exe Strings for file name / Not Found
23
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
SOLUTIONS – TASK #2
As you can see, we were not able to find the text. If you load the program in CFF Explorer,
as shown in Figure 3.8, you will see that this program is actually packed, which means I can
only see what’s inside after unpacking the program.
Figure 3.8 – Welcome2.exe Packed Sections
Now, let us search for the strings in the memory of the process, which is shown in Figure
3.9.
24
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
SOLUTIONS – TASK #2
Figure 3.9 – Searching Welcome2.exe Strings for file name / Found
We were able to find the strings and that’s because the program was unpacked in memory
and now the strings inside are shown in memory.
25
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
SOLUTIONS – TASK #3
Open cmd.exe, then run the netcat program nc.exe as shown below (If the system asks you
for permission to open the port as shown in Figure 4.1, just select both networks and hit the
Allow access button):
> nc.exe -lvp 9999
Figure 4.1 – Running and Opening Firewall Ports for NetCat
Open another cmd.exe and make sure that the process is running properly by checking its
status using netstat as shown below:
> netstat -t tcp -an
I’m assuming you got something similar to the results shown in Figure 4.2.
26
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
SOLUTIONS – TASK #3
Figure 4.2 – Checking Status of NetCat Process
Now, in process explorer go and check the TCP/IP tab for nc.exe, which in my case are
shown in Figure 4.3.
Figure 4.3 –NetCat Process TCP/IP Status in Process Explorer
What we found is the same process status we saw in the cmd.exe when using netstat. This
also means we can check processes and their network status from process explorer. I
would recommend you check out what happens when another nc.exe connects to this
process.
27
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
SOLUTIONS – TASK #4
In this task, we want to understand what Windows sessions are and how to interact with
them. Open cmd.exe with administrative privileges. Then launch notepad.exe and record
the PID, PPID, Parent Process, Session #, and the User. In my case these are shown in Figures
5.1 and 5.2, respectively.
Figure 5.1 –Notepad.exe Process Details / Main
Figure 5.2 –Notepad.exe Process Details / Security
28
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
SOLUTIONS – TASK #4
Notepad.exe is running in session 1, which is an interactive session that our user can
interact with.
Now go to the SysInternals directory and run the program psexec.exe using the following
command:
> psexec -s notepad.exe
If you are looking for the process notepad.exe under the psexec.exe under the explorer.exe
tree, stop and expand the services.exe tree and look under the service named
PSEXESVC.EXE ,as shown in Figure 5.3.
Figure 5.3 –Notepad.exe Process Running Under PSEXESVC.exe
Even if we can see on the command line that we did run the program and it is seen in
process explorer, we still cannot see it on our desktop. Go to the notepad.exe process
details and check the session number there. As shown in Figure 5.4, the process is running
29
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
SOLUTIONS – TASK #4
in session 0, which is why we cannot interact with it, since it is running in a different
isolated environment that our session does not have access to.
Figure 5.4 –Notepad.exe Process Running Under PSEXESVC.exe
The first thing is to keep in mind that we can’t interact with processes running in session 0
directly and also, they will not be visual to us, since they are running in another environment
which is isolated. Another important thing to check in Figure 5.4, is the user that is running
the process is NT AUTHORITY\SYSTEM and not our normal user (or administrator), which
is what the psexec tool provided our run of notepad.exe.
Another nice feature in Process Explorer that we can use as proof, is on the notepad.exe’s
main process details page, click on the Bring to Front button, what happens is the system
will raise an error saying there is no visual window for this program, even though we all
know that notepad.exe is a visual tool. This is shown in Figure 5.5.
Figure 5.5 –Error Raised when Bringing Process to Front
30
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
SOLUTIONS – TASK #4
Before we end this lab, let’s do one more test. Run the program psexec.exe again, but this
time using the following command (using the -i option) as shown below:
> psexec -i -s notepad.exe
The difference this time is:
1. Notepad.exe is now visual and we can interact with it.
2. The process is running in session number 1 and not 0.
3. We can use the Bring to Front button on the properties page of the process.
But with that said, the process as shown in Figure 5.6 is still:
4. Running with the NT AUTHORITY\SYSTEM context as we wanted.
5. The process is running under Services.exe tree not the explorer.exe tree.
Figure 5.6 –Notepad.exe Running with SYSTEM Privileges
31
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
KEY TAKEAWAYS
By the end of this lab, you should:
1. Get more understand about Windows processes and their properties.
2. Why we have more than one csrss.exe process and why explorer.exe should not be
doing any network connections itself.
3. Understand when we can find the strings in an executable’s image and when we
can’t.
4. Now know how to use process explorer to perform many different process
investigations.
5. Understand the idea of sessions and why malware would try to run in session 0.
32
© 2020 Caendra Inc. | MAPv1 | WORKING WITH WINDOWS PROCESSES
You might also like
- PERFORMING COMPUTER OPERATIONS (PCO) LO4 (TLE - IACSS9-12PCO-If-7)Document12 pagesPERFORMING COMPUTER OPERATIONS (PCO) LO4 (TLE - IACSS9-12PCO-If-7)Dianne Brucal - Matibag63% (8)
- Student Exploration - Weight and Mass (ANSWER KEY)Document3 pagesStudent Exploration - Weight and Mass (ANSWER KEY)Jaila Palmer [STUDENT]No ratings yet
- J0304201134 - J0304201060 - Pertemuan 2Document11 pagesJ0304201134 - J0304201060 - Pertemuan 2IvandenerolNo ratings yet
- Penetrating Windows 8 With Syringe UtiliDocument5 pagesPenetrating Windows 8 With Syringe UtiliAGBADAN Yao EricNo ratings yet
- UntitledDocument14 pagesUntitledsufiyanNo ratings yet
- What Are The SysInternals Tools and How Do You Use ThemDocument129 pagesWhat Are The SysInternals Tools and How Do You Use ThemaaronNo ratings yet
- Art of Anti DetectionDocument41 pagesArt of Anti DetectionGyamba Dukpa100% (1)
- Malware AnalysisDocument21 pagesMalware AnalysisAyush rawal100% (1)
- Art of Anti DetectionDocument34 pagesArt of Anti DetectionViineeNo ratings yet
- Module 07 Windows ForensicsDocument19 pagesModule 07 Windows ForensicsShaik Abdul Muneer100% (1)
- Dumping Code For Spying and Windows ToolsDocument13 pagesDumping Code For Spying and Windows ToolsRahul GandhiNo ratings yet
- Appdata GpoDocument4 pagesAppdata GpoEurípedes OliveiraNo ratings yet
- Unpacking Process Hollowing 671 690Document21 pagesUnpacking Process Hollowing 671 690Đồng Xuân ThànhNo ratings yet
- When Applications Crash Part I - WatsonDocument5 pagesWhen Applications Crash Part I - WatsonNagarjuna ReddyNo ratings yet
- WelcomeDocument23 pagesWelcomeabiramanNo ratings yet
- Further Readings: Check Your ProgressDocument22 pagesFurther Readings: Check Your Progresstamil selviNo ratings yet
- Unit 14: A. Reading Comprehension - 5 Operating Systems: Hidden SoftwareDocument4 pagesUnit 14: A. Reading Comprehension - 5 Operating Systems: Hidden SoftwareMuhammad Rizky Andriansyah SurataNo ratings yet
- Identify Running ProcessesDocument2 pagesIdentify Running ProcessesPrince NagacNo ratings yet
- The Windows Process JourneyDocument28 pagesThe Windows Process JourneyPremNo ratings yet
- Name: Grade/Score: Year/ Section/ Row #: DateDocument1 pageName: Grade/Score: Year/ Section/ Row #: DateLouella Jane Racho MartinezNo ratings yet
- Debugging Esc 468Document10 pagesDebugging Esc 468bharat013@gmail.comNo ratings yet
- Solomon Windows Internals TroubleshootingDocument106 pagesSolomon Windows Internals Troubleshootingjavier.4evermlcNo ratings yet
- Kali 5Document10 pagesKali 5michal hanaNo ratings yet
- 3.2.11 Lab - Exploring Processes, Threads, Handles, and Windows RegistryDocument4 pages3.2.11 Lab - Exploring Processes, Threads, Handles, and Windows Registrytinod18399No ratings yet
- ICT-CSS-12 Q1 W2 Mod 4Document16 pagesICT-CSS-12 Q1 W2 Mod 4AJ Bacarisas RochaNo ratings yet
- (InfoAcademy) CyberOpsAssociate-Lab 2 - Explore Windows Operating SystemDocument12 pages(InfoAcademy) CyberOpsAssociate-Lab 2 - Explore Windows Operating SystemChip CiprianNo ratings yet
- Vera ManualDocument13 pagesVera Manualdamner4No ratings yet
- What Is Computer Systems Servicing (CSS NCII) ?Document12 pagesWhat Is Computer Systems Servicing (CSS NCII) ?Jen PequitNo ratings yet
- Software CrackingDocument6 pagesSoftware CrackingNavneet NarwariyaNo ratings yet
- What Is Computer Systems Servicing (CSS NCII) ?Document11 pagesWhat Is Computer Systems Servicing (CSS NCII) ?rezhablo100% (1)
- SCTS 242: Network Intrusion Detection and Penetration TestingDocument21 pagesSCTS 242: Network Intrusion Detection and Penetration TestingAbraham AmselNo ratings yet
- Ankush ThakurDocument174 pagesAnkush Thakursoniya tewatiaNo ratings yet
- System Administration (Part 1) : Example Case QuestionsDocument8 pagesSystem Administration (Part 1) : Example Case QuestionsMay Thu HanNo ratings yet
- The Windows Process Journey: by Dr. Shlomi BoutnaruDocument39 pagesThe Windows Process Journey: by Dr. Shlomi Boutnaruhamid reza NasrNo ratings yet
- Mca SynopsisDocument28 pagesMca SynopsisRajbeer Kumar DasNo ratings yet
- Getting Full Speed With DelphiDocument25 pagesGetting Full Speed With DelphiDavis MontenegroNo ratings yet
- LAB1Document6 pagesLAB1Yenna CayasaNo ratings yet
- Sap InterviewDocument2 pagesSap InterviewMohammed AseemNo ratings yet
- Penetration Testing ReportDocument25 pagesPenetration Testing Reportmatifj4n0987No ratings yet
- Putting Registry-/system-Cleanup Apps To The TestDocument8 pagesPutting Registry-/system-Cleanup Apps To The TestBill LeeNo ratings yet
- 110 - Exp - 2 - Updated 2Document4 pages110 - Exp - 2 - Updated 2hhcqfvj9kcNo ratings yet
- Csol570-Module 7Document14 pagesCsol570-Module 7api-694098467No ratings yet
- Introduction and SRS: Chapter-1Document38 pagesIntroduction and SRS: Chapter-1Akash MishraNo ratings yet
- Settlement DeedDocument9 pagesSettlement DeedSubramani SakthivelNo ratings yet
- DXWND ManualDocument31 pagesDXWND ManualHannah Mara TaiNo ratings yet
- CO1508 Computer Systems & Security - Week 10: Building Your Harmless Virus in C++ - Part 1 Windows RegistryDocument8 pagesCO1508 Computer Systems & Security - Week 10: Building Your Harmless Virus in C++ - Part 1 Windows RegistryEdward LeeNo ratings yet
- Cài đặt phần mềm Nessus trên backtrackDocument8 pagesCài đặt phần mềm Nessus trên backtrackthanglxNo ratings yet
- Introduction To Endpoint HuntingDocument88 pagesIntroduction To Endpoint HuntingmadhugoudaNo ratings yet
- OSY Solved Manual @diploma - WorldDocument160 pagesOSY Solved Manual @diploma - Worldcm4i10 Aditya baramde100% (6)
- Everyone Who Writes CodeDocument8 pagesEveryone Who Writes CodeFenil DesaiNo ratings yet
- Porting OSE Systems To LinuxDocument39 pagesPorting OSE Systems To Linuxclu5t3rNo ratings yet
- Sec401 Windows Linux Tutorial v1Document41 pagesSec401 Windows Linux Tutorial v1Snig KavNo ratings yet
- Desktop Support Engineer Interview Questions and AnswersDocument7 pagesDesktop Support Engineer Interview Questions and AnswersjosephNo ratings yet
- AplusCore2 DemoCramnotesDocument44 pagesAplusCore2 DemoCramnotesWayne WayneNo ratings yet
- Material of cs101Document64 pagesMaterial of cs101Zain AliNo ratings yet
- Page12 ToolboxDocument2 pagesPage12 ToolboxAruna GunatilakeNo ratings yet
- Hostel Management System Project Report.Document61 pagesHostel Management System Project Report.Kamal AcharyaNo ratings yet
- Wmic Trick O HackerDocument12 pagesWmic Trick O HackerjoseanNo ratings yet
- Windows 1693667965753Document57 pagesWindows 1693667965753Sandro MeloNo ratings yet
- Lab 2Document132 pagesLab 2mrsploogeNo ratings yet
- DCS Operating InstructionsDocument80 pagesDCS Operating InstructionsJavierNo ratings yet
- Compliance Factors Associated With Contact Lens-Related Dry EyeDocument6 pagesCompliance Factors Associated With Contact Lens-Related Dry EyeAlda Gitu RahmaNo ratings yet
- 5 Anti - Inflammatory Drugs, Anti-Gout DrugsDocument15 pages5 Anti - Inflammatory Drugs, Anti-Gout DrugsAudrey Beatrice ReyesNo ratings yet
- Arunraj. N: Executive - Regional HRDocument3 pagesArunraj. N: Executive - Regional HRELAVAZHUTHINo ratings yet
- Pengaruh Pemberian Latihan Peregangan Terhadap PenDocument20 pagesPengaruh Pemberian Latihan Peregangan Terhadap PenBang DeanNo ratings yet
- What Is The Poet's Appeal To The People? Ans. The Poet Appeals To All TheDocument35 pagesWhat Is The Poet's Appeal To The People? Ans. The Poet Appeals To All Thecbs123abcNo ratings yet
- BRAINSTORMING: Key Take Aways: Tourism Systems and Models 2020Document4 pagesBRAINSTORMING: Key Take Aways: Tourism Systems and Models 2020Keith Loren ChavezNo ratings yet
- Connectors RephrasingDocument2 pagesConnectors RephrasingsoniaNo ratings yet
- Class II Subdivision Treatment With The Forsus Fatigue Resistant Device Vs Intermaxillary ElasticsDocument6 pagesClass II Subdivision Treatment With The Forsus Fatigue Resistant Device Vs Intermaxillary ElasticshemaadriNo ratings yet
- Digital Design: VerilogDocument92 pagesDigital Design: Verilogee206023No ratings yet
- The White Image in The Black Mind ReviewDocument87 pagesThe White Image in The Black Mind ReviewKhary Pestaina100% (5)
- Works by Others in Your Essay Edit 1Document5 pagesWorks by Others in Your Essay Edit 1api-667143998No ratings yet
- Simplified Primary Songs From FriendDocument60 pagesSimplified Primary Songs From Friendplay88No ratings yet
- Depreciation Calculation in ExcelDocument8 pagesDepreciation Calculation in ExcelVasanth Kumar VNo ratings yet
- Ed 242 Activity Creating Online FormDocument3 pagesEd 242 Activity Creating Online FormJane Marie Albios TevesNo ratings yet
- NCF - 2015 - Npe - 1986Document20 pagesNCF - 2015 - Npe - 1986sanchitNo ratings yet
- antiheroDocument1 pageantiheroRakesh KumarNo ratings yet
- 11 Partnership DissolutionDocument10 pages11 Partnership DissolutionBabamu Kalmoni JaatoNo ratings yet
- Report On Han Fei Zi and The Legalist SchoolDocument4 pagesReport On Han Fei Zi and The Legalist SchoolEmmarlone96No ratings yet
- Art of Emerging EuropeDocument11 pagesArt of Emerging EuropeShane PajaberaNo ratings yet
- Kibor HistoryDocument3 pagesKibor HistorymaheenwarisNo ratings yet
- Electrochemistry in Ionic Liquids Vol 2Document279 pagesElectrochemistry in Ionic Liquids Vol 2Dairo CANo ratings yet
- Fybcom Sem 1 Module 3 EntrepreneurshipDocument13 pagesFybcom Sem 1 Module 3 EntrepreneurshipRahul ChoudharyNo ratings yet
- The Architects of Islamic CivilizationDocument372 pagesThe Architects of Islamic Civilizationlazut273No ratings yet
- English - The SeaDocument1 pageEnglish - The SeaRohan PritchardNo ratings yet
- Maoism in Bangla PDFDocument15 pagesMaoism in Bangla PDFAyub Khan JrNo ratings yet
- FlightDocument2 pagesFlightRich BaguiNo ratings yet
- GeniE UM Vol4 APP C2 AISC9thDocument11 pagesGeniE UM Vol4 APP C2 AISC9thBRIJITHNo ratings yet
- International Conference Technology and Engineering (MARTECH)Document9 pagesInternational Conference Technology and Engineering (MARTECH)Farah Mehnaz HossainNo ratings yet