Professional Documents
Culture Documents
Os Attack 82102
Os Attack 82102
Uploaded by
Deepanshu Raj SinghOriginal Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Os Attack 82102
Os Attack 82102
Uploaded by
Deepanshu Raj SinghCopyright:
Available Formats
Countermeasures for os attack :
1) Use licence version of os.
2) do not install third party softwares.
3) Always use firewall
4) Keep update your system periodically.
ATTACK : GAINING THE ACCESS OF DATA BY UNAUTHORIZED USER.
GAINING : ACCESSING DATA \ MODIFYING DATA \ DELETEING DATA.
TYPES OF ATTACKS : PASSIVE & ACTIVE
PASSIVE : NO MODIFICATION
ACTIVE : CAN BE MODIFIED.
OS ATTACKS:
1) GAINING ACCESS ATTACK
2) MISCONFIGURATION ATTACK
3) APPLICATION LEVEL ATTACK
GAINING ACCESS ATTACK:
---------------------
PASSWORD CRACKING :
1) BRUTEFORCE ATTACK
2) DICTIONARY ATTACK
3) RAINBOW TABLE ATTACK:
MAN IN THE MIDDLE ATTACK
PASSWORD GUESSING
MAWARE ATTACK
PHISHING ATTACK
===============================================
OS LEVEL ATTACK :
also called as os commanding
attacking on web server through remote.
and then executing system commands through browser.
====================
Application level attack :
SQL INJECTION
PHISHING
CROSS- SITE- SCRIPTING
SESSON HIJACKING
DENIAL OF SERVICE ATTACK
SESSION HIJACKING
==================
Misconfiguration attack:
Code injection attack
command injection attack
bruteforce
buffer overflow
xss attack
===================================================
1) Computer security: to protect the computer system and the data which is stored
in the system.
2) Cyber security: It is a process of protecting data, system nd networks against
cyber attack.
3) Information security : It is a process to protect information and information
system from threats
through security control to reach C.I.A.
4) cyber forensics: extracting dat as a proof for crime.
recovery process of deleted files. emails. audio videos.
5) Public network: accessible for all users across the globe. It is used by anyone.
unsecured.
6) Private network: It is a private because it follows non routable network. for
private organization. secured.
7) [ vulnerability: the potential to harm or loss.
vulnerability = exposure + resistance + reselience18:15 16-12-2021
exposure: risk propertyexit
resistence: action taken to prevent
resilience: ability to recover prior state. ]
8) confidentiality : limits acess to information or restrictions on information
access.
Integrity : assurance that the information is accurate
Availibility : definite and reliable access by authorized people.
- guide policies within an organizaiton
9) AAA: USED FOR NETWORK MANAGEMENT & security
Authentication: it is used to identify users.
Authorization: it is a process to enforcing policies to determine what type of
services can be use by user.
Accounting: It manages user consumed resources during access. It includes amount
of data user used and sent. login session time.
10) Cryptanalisis: studying cryptographic system to find weakness of the
cryptographic alogrithm and decipher the cipher text without knowing secret key
11) framework: ramework works as a kind of support structure for something to be
built on top of.
=======================
Metasploit: It is a ruby based penetration tesing platform to perform an exploit
code. making payloads.
Post exploitation process is also an improtant part.
It is used to dicovering vulnerabilities.
It is a framework.
paylod: carrying capacity of a packet
You might also like
- Core and Vue - Js - 2021Document479 pagesCore and Vue - Js - 2021Yousef ElsaeedNo ratings yet
- CEH: Certified Ethical Hacker v11 : Exam Cram Notes - First Edition - 2021From EverandCEH: Certified Ethical Hacker v11 : Exam Cram Notes - First Edition - 2021No ratings yet
- דוח פורנזי חילוץ דאטא מהאייפד של ברק לייזר עם מיילים וטלפונים של שופטיםDocument3,377 pagesדוח פורנזי חילוץ דאטא מהאייפד של ברק לייזר עם מיילים וטלפונים של שופטיםDasi ForerNo ratings yet
- The Certified Ethical Hacker Exam - version 8 (The concise study guide)From EverandThe Certified Ethical Hacker Exam - version 8 (The concise study guide)Rating: 3 out of 5 stars3/5 (9)
- Module 3 Introduction To Cyber Security Module 3 NotesDocument35 pagesModule 3 Introduction To Cyber Security Module 3 Notesminow33514No ratings yet
- Cyber Security Q&A Week1Document11 pagesCyber Security Q&A Week1infosys152000No ratings yet
- Chapter 3: Tools and Methods Used in CybercrimeDocument34 pagesChapter 3: Tools and Methods Used in CybercrimeNarasimha MurthyNo ratings yet
- CNS Sem V ESE Solution Winter 2022Document33 pagesCNS Sem V ESE Solution Winter 2022vartakashishNo ratings yet
- TRUE/FALSE. (0.5 PT Each) : Chapter 1 Quiz Name: Oluwole AdebusuyiDocument45 pagesTRUE/FALSE. (0.5 PT Each) : Chapter 1 Quiz Name: Oluwole AdebusuyiOluwole AdebusuyiNo ratings yet
- Securityandmanagement 210305165016Document15 pagesSecurityandmanagement 210305165016arti kumariNo ratings yet
- VAPT General QuestionsDocument9 pagesVAPT General Questionspepal38750No ratings yet
- A Java Based Network Intrusion Detection System (IDS)Document8 pagesA Java Based Network Intrusion Detection System (IDS)Prasanth ReddyNo ratings yet
- A Java Based Network Intrusion Detection System (IDS)Document14 pagesA Java Based Network Intrusion Detection System (IDS)Santosh ParsaNo ratings yet
- sample 2 PROTECTING A DISTRIBUTED SYSTEMDocument9 pagessample 2 PROTECTING A DISTRIBUTED SYSTEMummulhfathima.msecNo ratings yet
- Lecture 01 - Introduction To Information SecurityDocument22 pagesLecture 01 - Introduction To Information SecurityS t a r D u s tNo ratings yet
- Unit - V Cloud Security - Part2Document25 pagesUnit - V Cloud Security - Part2shinderohann02No ratings yet
- Unit 4 - Lecture Protection and SecurityDocument27 pagesUnit 4 - Lecture Protection and SecurityNishant NalawadeNo ratings yet
- Computer Security Ch2Document11 pagesComputer Security Ch2Gomlalaw tubeNo ratings yet
- Prince Mohammad Bin Fahd University College of Computer Engineering and Science Itap 3431 Network Security Assignment 1#Document4 pagesPrince Mohammad Bin Fahd University College of Computer Engineering and Science Itap 3431 Network Security Assignment 1#Cent SecurityNo ratings yet
- Assignment 3 Network SecurityDocument7 pagesAssignment 3 Network Securitykainat KhalidNo ratings yet
- G5 Quiz IT105Document4 pagesG5 Quiz IT105Josue TorzarNo ratings yet
- Interview Preparation Part-3Document17 pagesInterview Preparation Part-3Abdul Mateen Ukkund100% (1)
- Isaa Assignment 1Document4 pagesIsaa Assignment 1SANKALP MUKIM 20BDS0128No ratings yet
- AIS Chapter 4Document10 pagesAIS Chapter 4THOTslayer 420No ratings yet
- Lesson 2 - Cybersecurity OverviewDocument4 pagesLesson 2 - Cybersecurity Overviewyoussef sherifNo ratings yet
- CITS1003 6 VulnerabilitiesDocument34 pagesCITS1003 6 VulnerabilitiesPhyo MinNo ratings yet
- Chapter 3Document6 pagesChapter 3Sheila Mae AramanNo ratings yet
- NisDocument4 pagesNisChaitanya KurandaleNo ratings yet
- Tutorial 12: Question 01. Elaborate The Necessity of The Penetration Testing Execution StandardDocument7 pagesTutorial 12: Question 01. Elaborate The Necessity of The Penetration Testing Execution StandardSubesh Khadka Networking and IT SecurityNo ratings yet
- PAST YEAR CSDocument9 pagesPAST YEAR CSfaeqcs19No ratings yet
- Week 5Document28 pagesWeek 5Subuhi KashifNo ratings yet
- Microsoft Azure Well-Architected Framework - SecurityDocument37 pagesMicrosoft Azure Well-Architected Framework - SecuritymarcelovportuguesNo ratings yet
- Network Security: Compromises and Countermeasures: Key WordsDocument6 pagesNetwork Security: Compromises and Countermeasures: Key Wordsabdel_lakNo ratings yet
- C) 256 Bits AESDocument4 pagesC) 256 Bits AESsyafiq rossleyNo ratings yet
- Prevention, Detection, Recovery E.T.CDocument5 pagesPrevention, Detection, Recovery E.T.Cmahmoud janNo ratings yet
- Week6 KillChainDocument17 pagesWeek6 KillChainFrozoneNo ratings yet
- Operating System Chapter 6 - MADocument36 pagesOperating System Chapter 6 - MASileshi Bogale HaileNo ratings yet
- DBMS - Bba Unit 4Document16 pagesDBMS - Bba Unit 4Aman SinghNo ratings yet
- Securityindistributedsystems PDFDocument64 pagesSecurityindistributedsystems PDFSaumya KatiyarNo ratings yet
- Security ArchitectDocument25 pagesSecurity Architectoobidoo916No ratings yet
- A Study On Water Hole AttackDocument3 pagesA Study On Water Hole AttackRăzvan CeucaNo ratings yet
- CSX FDocument24 pagesCSX FCarlos sanchezNo ratings yet
- Red Team OperationsDocument15 pagesRed Team OperationsMarcelo JuniorNo ratings yet
- 00283931Document16 pages00283931Pablo Velarde AlvaradoNo ratings yet
- CH4 CS LectureDocument61 pagesCH4 CS LecturepyramidmistreNo ratings yet
- Session 03Document9 pagesSession 03bouzid.salim47No ratings yet
- A Novel Approach To Generate A Reverse Shell: Exploitation and PreventionDocument12 pagesA Novel Approach To Generate A Reverse Shell: Exploitation and PreventionMukah ErnestNo ratings yet
- Theory TimeTable SYBSC CSDocument4 pagesTheory TimeTable SYBSC CSpinkuchopra17No ratings yet
- Cyber Kill Chain (ADID Smail)Document26 pagesCyber Kill Chain (ADID Smail)Ismail AdidNo ratings yet
- Seven Steps To Effectively Defend Industrial Control SystemsDocument7 pagesSeven Steps To Effectively Defend Industrial Control SystemsGerardo F. GonzalezNo ratings yet
- COMPUTER SECURITY Definition & NeedDocument98 pagesCOMPUTER SECURITY Definition & Need142 Bhumika LachakeNo ratings yet
- IS Auditing - 4Document27 pagesIS Auditing - 4Wuiss AgonyNo ratings yet
- 2095 ALI SHAFQAT SHAFQAT SAGHIR - Final 9890 982598084Document12 pages2095 ALI SHAFQAT SHAFQAT SAGHIR - Final 9890 982598084Ali ShafqatNo ratings yet
- Introduction To Ethical HackingDocument31 pagesIntroduction To Ethical HackingAnjali Maurya100% (1)
- Assignment 01-Information SecurityDocument12 pagesAssignment 01-Information Security202017b2009No ratings yet
- Unit 5Document27 pagesUnit 5KOKA MADHUNo ratings yet
- It Security Procedures and Guidelines: Adrija SenDocument33 pagesIt Security Procedures and Guidelines: Adrija SenSaket AgarwalNo ratings yet
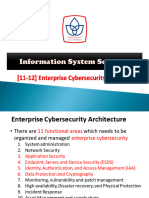
- PU Is Security - 12. Enterprise Cybersecurity ArchitectureDocument42 pagesPU Is Security - 12. Enterprise Cybersecurity ArchitecturealifaldindaNo ratings yet
- IntroDocument26 pagesIntroVarun Gupta0% (1)
- Network Security Unit 1Document33 pagesNetwork Security Unit 1smitcse2021No ratings yet
- Cybersec 1 2Document7 pagesCybersec 1 2MOHIT ELECTROVISION FBDNo ratings yet
- Computer System Security: 1-1 W (CC-Sem-3 & 4)Document155 pagesComputer System Security: 1-1 W (CC-Sem-3 & 4)श्री KrishnaNo ratings yet
- Cisco Meeting Server Deployment Planning and Preparation With Expressway GuideDocument30 pagesCisco Meeting Server Deployment Planning and Preparation With Expressway GuideBtakeshi1No ratings yet
- Unit 1 Introduction To Data StructureDocument41 pagesUnit 1 Introduction To Data StructureVansh ThakurNo ratings yet
- DarkplacesDocument44 pagesDarkplacesEsteban LeónNo ratings yet
- Manual Changes For SAP GatewayDocument11 pagesManual Changes For SAP Gatewaygaurav.jain190521No ratings yet
- Cisco Unified Communications Manager TCP and UDP Port UsageDocument18 pagesCisco Unified Communications Manager TCP and UDP Port UsageJames HavocNo ratings yet
- Database Design and Introduction To MySQL Day - 5Document16 pagesDatabase Design and Introduction To MySQL Day - 5ABHI GOUDNo ratings yet
- DP 1 3 PracticeDocument4 pagesDP 1 3 PracticeJessica IreneNo ratings yet
- How Watsco Is Building A New Business Model With Iot: Case StudyDocument8 pagesHow Watsco Is Building A New Business Model With Iot: Case StudyJasonNo ratings yet
- PCI DSS Policies and ProceduresDocument38 pagesPCI DSS Policies and Proceduresjustforfun2009No ratings yet
- EDR EVASION Unhook Syscalls Indirect Syacalls 1682700077Document32 pagesEDR EVASION Unhook Syscalls Indirect Syacalls 1682700077johnNo ratings yet
- Game LogDocument111 pagesGame Logxfqd2fw4xfNo ratings yet
- Developing A Web Application On The Mevn StackDocument33 pagesDeveloping A Web Application On The Mevn StackIshengoma KakweziNo ratings yet
- 2007 02 01b Janecek PerceptronDocument37 pages2007 02 01b Janecek PerceptronRadenNo ratings yet
- SAS-AF AppdevgdDocument228 pagesSAS-AF AppdevgdJerome VallonNo ratings yet
- Modicon M221 Logic Controllers: Catalog JanuaryDocument35 pagesModicon M221 Logic Controllers: Catalog JanuaryПавелNo ratings yet
- (Download) GX-Developer - Mitsubishi PLC - Software (Real 100%)Document12 pages(Download) GX-Developer - Mitsubishi PLC - Software (Real 100%)Mery Helen Barraza DelgadoNo ratings yet
- Mega Chill ManualDocument7 pagesMega Chill ManualDee RajaNo ratings yet
- Network Security StrategiesDocument378 pagesNetwork Security StrategiesFabio Caetano100% (6)
- SMD Type GPS Receiver Module: DescriptionDocument12 pagesSMD Type GPS Receiver Module: DescriptionTEIPRO COLOMBIANo ratings yet
- A To Z Index of Bash CommandsDocument4 pagesA To Z Index of Bash CommandsronschreinerNo ratings yet
- IEEE Standard 802.16 For Global Broadband Wireless AccessDocument33 pagesIEEE Standard 802.16 For Global Broadband Wireless Accesswork067No ratings yet
- CIT 218-Systems Administration and Maintenance - Unit 1Document10 pagesCIT 218-Systems Administration and Maintenance - Unit 1Noe Jhon SionilloNo ratings yet
- C# Special CharactersDocument7 pagesC# Special CharactersDivine SolutionsNo ratings yet
- Infor LN Analytics Foundation Installation GuideDocument44 pagesInfor LN Analytics Foundation Installation GuidetomactinNo ratings yet
- React To Svelte CheatsheetDocument1 pageReact To Svelte CheatsheetMário Sésso JúniorNo ratings yet
- 12th Science IT 80 Marks Paper 10.Document8 pages12th Science IT 80 Marks Paper 10.WICKED VINIT TRICKSNo ratings yet
- VERITAS Cluster Server For UNIX, Fundamentals: Lesson 7 Preparing Services For VCSDocument56 pagesVERITAS Cluster Server For UNIX, Fundamentals: Lesson 7 Preparing Services For VCSNirmal AsaithambiNo ratings yet
- A Project Report OnDocument84 pagesA Project Report OnyaminiNo ratings yet