Professional Documents
Culture Documents
Access Control List
Access Control List
Uploaded by
Nguyễn Minh HoàngOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Access Control List
Access Control List
Uploaded by
Nguyễn Minh HoàngCopyright:
Available Formats
Faculty of Computer Science and Engineering – HCMC University of Technology
Computer Networks 1
Lab 11
ACCESS CONTROL LIST
Names: .......................................................................
Student No: ................................................................
Objectives
• Understanding Access Control List concepts and its usage
• Practising configuring Access Control List on Cisco Packet Tracer.
Content and Practice
I. Access Control List
Access control lists (ACLs) provide a means to filter packets by allowing a user to permit or
deny IP packets from crossing specified interfaces.
“Just imagine you come to a fair and see the guardian checking tickets. He only allows
people with suitable tickets to enter. Well, an access list’s function is same as that guardian”
(from http://www.9tut.com/access-list-tutorial)
Access lists filter network traffic by controlling whether packets are forwarded or blocked at
the router’s interfaces based on the criteria you specified within the access list.
To use ACLs, the system administrator must first configure ACLs and then apply them to
specific interfaces. There are 3 popular types of ACL: Standard, Extended and Named
ACLs.
Access list type Range
Standard 1-99, 1300-1999
Extended 100-199, 2000-2699
1. Standard IP Access List
Standard IP lists (1-99) only check source addresses of all IP packets.
Configuration Syntax
access-list access-list-number {permit | deny} {host|source source-wildcard|any}
Apply ACL to an interface
Computer Networks 1 – Laboratories 1
Faculty of Computer Science and Engineering – HCMC University of Technology
ip access-group access-list-number {in | out}
2. Extended IP Access List
Extended IP lists (100-199) check both source and destination addresses, specific
UDP/TCP/IP protocols, and destination ports.
Configuration Syntax
access-list access-list-number {permit | deny} protocol source {source-mask} destination
{destination-mask} [eq destination-port]
3. Named IP Access List
This allows standard and extended ACLs to be given names instead of numbers
Named IP Access List Configuration Syntax
ip access-list {standard | extended} {name | number}
Note: Where to place access list?
Standard IP access list should be placed close to destination.
Extended IP access lists should be placed close to the source.
4. Wildcard Mask
Wildcard masks are used with access lists to specify a host, network or part of a network.
The zeros and ones in a wildcard determine whether the corresponding bits in the IP address
should be checked or ignored for ACL purposes.
You have been familiar with “network mask” (netmask) concept. For example, the network
192.168.1.0/24 has the network mask 255.255.255.0.
Wildcard mask is the inversion of network mask. For example, consider network
172.23.16.0/20, its network mask is 255.255.240.0. This network mask is converted into
wildcard mask by converting all bits 0 to 1 and all bits 1 to 0.
255 = 1111 1111 -> convert into 0000 0000
240 = 1111 0000 -> convert into 0000 1111
0 = 0000 0000 -> convert into 1111 1111
Computer Networks 1 – Laboratories 2
Faculty of Computer Science and Engineering – HCMC University of Technology
Therefore 255.255.240.0 can be written in wildcard mask as
0000000.00000000.00001111.11111111 = 0.0.15.255
Remember, for the wildcard mask, 1′s are I DON’T CARE, and 0′s are I CARE.
Refer to these links to go into detail:
http://www.9tut.com/access-list-tutorial
http://www.9tut.com/access-list-tutorial/2
II. Practice
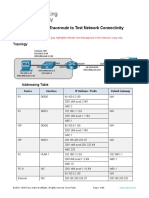
Network topology on Cisco Packet Tracer:
The computers and routers’ IP addresses, web servers and DNS servers have been already
configured.
Requirements:
1. Configure routing information for Router 1, 2, 3, using RIP. Do not advertise network
192.168.1.0 in RIP.
2. Ensure every host and server is reachable from others:
• Ping from laptop 2 to server bk.edu.vn.
• From command line of laptop 2, enter the command: nslookup bk.edu.vn
192.168.2.254
• Open web browser on laptop 2, access to server bk.edu.vn
• Ping from laptop 3 to server tuoitrenews.vn.
Computer Networks 1 – Laboratories 3
Faculty of Computer Science and Engineering – HCMC University of Technology
3. Configure Router 2 so that packet with source IP address: 192.168.1.101 is forbidden to
access bk.edu.vn (hint: use standard ip access list)
4. Configure Router 1 so that ICMP packet from outside world could not reach
tuoitrenews.vn server. (hint: use extended ip access list)
5. Configure Router 2 so that dns request from outside world to server 192.168.2.254 is
forbidden.
6. Ensure all configurationsc are right:
• Ping from laptop 2 to server bk.edu.vn: fail
• Ping from laptop 1 to server bk.edu.vn: successful
• From command line of laptop 1, enter the command: nslookup bk.edu.vn
192.168.2.254: successful
• Open web browser on laptop 2, access to server bk.edu.vn: fail
• Open web browser on laptop 1, access to server bk.edu.vn: successful
• Ping from laptop 3 to server tuoitrenews.vn: fail
• Open web browser on laptop 3, access to server tuoitrenews.vn: successful
III. Submission
Complete all tasks in section II, then submit Lab11_<student_code>.pkt onto Sakai.
Computer Networks 1 – Laboratories 4
You might also like
- Network Security All-in-one: ASA Firepower WSA Umbrella VPN ISE Layer 2 SecurityFrom EverandNetwork Security All-in-one: ASA Firepower WSA Umbrella VPN ISE Layer 2 SecurityNo ratings yet
- Ccna1 V7 Cap 1-3Document6 pagesCcna1 V7 Cap 1-3ask_gaby100% (1)
- Computer System Engineering Department ENCS413 Network Lab Access ListDocument13 pagesComputer System Engineering Department ENCS413 Network Lab Access Listak akNo ratings yet
- Mikrotik Router Configuration With Block Virus Ports by UmairDocument17 pagesMikrotik Router Configuration With Block Virus Ports by UmairUmair SaeedNo ratings yet
- ACL PT TestDocument10 pagesACL PT TestGilfer VasquezNo ratings yet
- Lab 1 5 3 PDFDocument4 pagesLab 1 5 3 PDFSan SokvisalNo ratings yet
- Lab Worksheet 7: Basic Access Control ListDocument5 pagesLab Worksheet 7: Basic Access Control ListCj LlemosNo ratings yet
- Data Communication & Computer Networking-lab-ManualDocument68 pagesData Communication & Computer Networking-lab-ManualTekalign TadesseNo ratings yet
- Lab 1Document11 pagesLab 1Tomas Rodriguez RamirezNo ratings yet
- Firewalls: Network SecurityDocument7 pagesFirewalls: Network SecurityRashmiDeshmukhNo ratings yet
- A1 - Lab 3 - Access Control List in Packet TracerDocument7 pagesA1 - Lab 3 - Access Control List in Packet Traceranjanneupane479No ratings yet
- CCNA 3 v7 Modules 3Document32 pagesCCNA 3 v7 Modules 3Leandro J. HinestrozaNo ratings yet
- Lab 6-.Access Control List in Packet TracerDocument6 pagesLab 6-.Access Control List in Packet TracerMuhammad BasimNo ratings yet
- 210-260 PassleaderDocument70 pages210-260 PassleaderKamib Hamibeb0% (1)
- Lab 8.3.4 Planning, Configuring and Verifying Extended AclsDocument5 pagesLab 8.3.4 Planning, Configuring and Verifying Extended AclsFery ArdiansyahNo ratings yet
- Tutorial 11 SolutionsDocument7 pagesTutorial 11 SolutionsDA Wei SunNo ratings yet
- Răspunsuri Test Final NetacadDocument26 pagesRăspunsuri Test Final NetacadLarisa DumitracheNo ratings yet
- ACL Practice Lab 3Document8 pagesACL Practice Lab 3LGBT Việt NamNo ratings yet
- ACL Practice Lab 1Document8 pagesACL Practice Lab 1LGBT Việt NamNo ratings yet
- SadafDocument7 pagesSadafutop8No ratings yet
- Experiment No. 3 Aim: To Assign Ipv4 Address To The Router in Packet Tracer. TheoryDocument8 pagesExperiment No. 3 Aim: To Assign Ipv4 Address To The Router in Packet Tracer. Theorydhruv darjiNo ratings yet
- Final PDFDocument18 pagesFinal PDFAaron PrzNo ratings yet
- Lab9 ACLDocument6 pagesLab9 ACLMohamed AymanNo ratings yet
- CN Lab Manual 2018Document121 pagesCN Lab Manual 2018Suresh RamanujamNo ratings yet
- Lab 1.4.3 Introductory Lab 3 - Access Control List Basics and Extended PingDocument5 pagesLab 1.4.3 Introductory Lab 3 - Access Control List Basics and Extended PingnickNo ratings yet
- Bosch - Networking Essentials and Basic ConceptsDocument10 pagesBosch - Networking Essentials and Basic ConceptsFábio Dos ReisNo ratings yet
- DCCNDocument10 pagesDCCNDEABELA GAMING 2No ratings yet
- 210 260 368qDocument123 pages210 260 368qamman1234100% (1)
- Switch and Router ConfigurationDocument41 pagesSwitch and Router ConfigurationBroot KalNo ratings yet
- CCNAv2 Chapter 02Document22 pagesCCNAv2 Chapter 02Linux HamzaNo ratings yet
- CCNAv2 Chapter 02Document22 pagesCCNAv2 Chapter 02medrekNo ratings yet
- Configuring Security FeaturesDocument8 pagesConfiguring Security FeaturesedinNo ratings yet
- CCNA Security - Chapter 2 - Securing Network DevicesDocument175 pagesCCNA Security - Chapter 2 - Securing Network DevicesQuách HuyNo ratings yet
- acknowledgments, Sequencing, and Flow Control Are Characteristics of Which OSI Layer?Document9 pagesacknowledgments, Sequencing, and Flow Control Are Characteristics of Which OSI Layer?Desmond KcNo ratings yet
- Udemy Dump 2Document111 pagesUdemy Dump 2Gani RKNo ratings yet
- 210 260 PDFDocument151 pages210 260 PDFTalhaoui ZakariaNo ratings yet
- Permit Icmp Any Any Nd-Na Permit Icmp Any Any Nd-NsDocument15 pagesPermit Icmp Any Any Nd-Na Permit Icmp Any Any Nd-Nsmy_queen57No ratings yet
- Unit 3 FirewallDocument29 pagesUnit 3 FirewallIsmart LeoNo ratings yet
- Icnd Part 1, Vol 1Document367 pagesIcnd Part 1, Vol 1Tin Myo Thaw100% (1)
- Data Communication & Computer Network-lab-ManualDocument68 pagesData Communication & Computer Network-lab-ManualFitsum ErenaNo ratings yet
- CCNA LabManual NewDocument142 pagesCCNA LabManual Newyashveer100% (1)
- Access Control Lists: Advanced Systems Administration CourseDocument21 pagesAccess Control Lists: Advanced Systems Administration CourseKarthik GunasekaranNo ratings yet
- Lab For Extended AclsDocument5 pagesLab For Extended Aclscasilan_90No ratings yet
- Lab 5Document13 pagesLab 5Tomas Rodriguez RamirezNo ratings yet
- Lab 11 Access Control List ACL 21122022 115035amDocument5 pagesLab 11 Access Control List ACL 21122022 115035amharis faisalNo ratings yet
- HPATA Net Study GuideDocument32 pagesHPATA Net Study Guidemy_scribd_docsNo ratings yet
- Tutorial+Mikrotik+Step+by+Step+ Anung+MuhandanuDocument16 pagesTutorial+Mikrotik+Step+by+Step+ Anung+MuhandanuFaysal Ahmed PalashNo ratings yet
- Configure A DHCPDocument15 pagesConfigure A DHCPNuradiin AmanNo ratings yet
- CCNA Security PT Practice SBA 1Document4 pagesCCNA Security PT Practice SBA 1Oscar Patricio Morales RuedaNo ratings yet
- Final Ccna 2Document18 pagesFinal Ccna 2Wahyou DewiNo ratings yet
- Tom Peters Networking Troubleshooting Checklist Guerilla CISODocument2 pagesTom Peters Networking Troubleshooting Checklist Guerilla CISOshabuzmushfiqueNo ratings yet
- Cisco Network Administration Interview Questions: CISCO CCNA Certification ReviewFrom EverandCisco Network Administration Interview Questions: CISCO CCNA Certification ReviewRating: 4.5 out of 5 stars4.5/5 (6)
- Cisco Packet Tracer Implementation: Building and Configuring Networks: 1, #1From EverandCisco Packet Tracer Implementation: Building and Configuring Networks: 1, #1No ratings yet
- CISCO PACKET TRACER LABS: Best practice of configuring or troubleshooting NetworkFrom EverandCISCO PACKET TRACER LABS: Best practice of configuring or troubleshooting NetworkNo ratings yet
- Practice Test 15: ListeningDocument7 pagesPractice Test 15: ListeningNguyễn Minh HoàngNo ratings yet
- CSC358 Wireshark Assignment 1 SolutionDocument2 pagesCSC358 Wireshark Assignment 1 SolutionNguyễn Minh HoàngNo ratings yet
- Cored Architecture To Acclerate Ai Algorithms: LSI Logic Design (CO309D) Extra Assignment ReportDocument37 pagesCored Architecture To Acclerate Ai Algorithms: LSI Logic Design (CO309D) Extra Assignment ReportNguyễn Minh HoàngNo ratings yet
- 1913439 - Nguyễn Minh Hoàng - lab8Document3 pages1913439 - Nguyễn Minh Hoàng - lab8Nguyễn Minh HoàngNo ratings yet
- Restaurant POS 2.0: Software Engineering (CO3001)Document18 pagesRestaurant POS 2.0: Software Engineering (CO3001)Nguyễn Minh HoàngNo ratings yet
- Configuring ASA On GNS3 Allow ICMP PacketDocument5 pagesConfiguring ASA On GNS3 Allow ICMP PacketYawar AzizNo ratings yet
- Prisma SD Wan Netskope IntegrationDocument25 pagesPrisma SD Wan Netskope IntegrationIsrael RojasNo ratings yet
- 16.1.2 Lab - Configure Route Redistribution Between EIGRP and OSPF - ILMDocument32 pages16.1.2 Lab - Configure Route Redistribution Between EIGRP and OSPF - ILMAndrei Petru PârvNo ratings yet
- 13.3.2 Lab - Use Ping and Traceroute To Test Network Connectivity - ILMDocument20 pages13.3.2 Lab - Use Ping and Traceroute To Test Network Connectivity - ILMMariano PereyraNo ratings yet
- Mininet OpenflowDocument18 pagesMininet OpenflownshivegowdaNo ratings yet
- CSS - 05-Week 10 - Module 10 - What Is Command Prompt or CMDDocument4 pagesCSS - 05-Week 10 - Module 10 - What Is Command Prompt or CMDElixa HernandezNo ratings yet
- WWW Hackers Book Com Chapter Identifying AttackersDocument4 pagesWWW Hackers Book Com Chapter Identifying AttackersMandela E'mmaNo ratings yet
- IT Networking and Communication: MITS4004Document15 pagesIT Networking and Communication: MITS4004madan GaireNo ratings yet
- Computer Security Lab 4 Wireshark 1Document2 pagesComputer Security Lab 4 Wireshark 1Nayla GreigeNo ratings yet
- Cisco 2Document16 pagesCisco 2Laze SerafimovNo ratings yet
- Parallax 28015 DatasheetDocument20 pagesParallax 28015 DatasheetTeddy HeroNo ratings yet
- Introduction To Networking 2023Document27 pagesIntroduction To Networking 2023Gerald KapinguraNo ratings yet
- LAB Manual Tech Support DSL BroadbandDocument41 pagesLAB Manual Tech Support DSL BroadbandWaleed AhmadNo ratings yet
- Basic Access Control ListsDocument10 pagesBasic Access Control ListsVeera KrishnaNo ratings yet
- Experiment No.1 Aim: Fundamentals of Computer Network.: 1.ifconfig CommandDocument18 pagesExperiment No.1 Aim: Fundamentals of Computer Network.: 1.ifconfig CommandMahesh DhanawadeNo ratings yet
- CN Lab Questions Anna UniversityDocument4 pagesCN Lab Questions Anna UniversitysandhyaNo ratings yet
- DOC721 Cacti 20dec21 1138PM 182536Document17 pagesDOC721 Cacti 20dec21 1138PM 182536Vincentius VarianNo ratings yet
- The Bryant Advantage CCNP SWITCH Study GuideDocument434 pagesThe Bryant Advantage CCNP SWITCH Study GuideSalahMSalah100% (2)
- NIL - Small Site Multi-HomingDocument8 pagesNIL - Small Site Multi-HominganonimoefraNo ratings yet
- Modules 16 - 17 - Building and Securing A Small Network Exam Answers - Premium IT Exam & CertifiedDocument17 pagesModules 16 - 17 - Building and Securing A Small Network Exam Answers - Premium IT Exam & CertifiedGUESHNo ratings yet
- Sub Netting ConceptsDocument29 pagesSub Netting Conceptsvijayd_gowdaNo ratings yet
- Nguyen-Doan-Nhat-Minh 2b 3b 4a 4b 4cDocument32 pagesNguyen-Doan-Nhat-Minh 2b 3b 4a 4b 4cNhat MinhNo ratings yet
- g12 Css 1st QTR SLM - EdfDocument64 pagesg12 Css 1st QTR SLM - EdfYaj AnilomNo ratings yet
- CCNP SP SprouteDocument168 pagesCCNP SP SproutewjjjxsNo ratings yet
- 10.1.4.8 Lab - Configure ASA 5505 Basic Settings and Firewall Using ASDM - InstructorDocument49 pages10.1.4.8 Lab - Configure ASA 5505 Basic Settings and Firewall Using ASDM - InstructorCheickna warké CamaraNo ratings yet
- Assignment 3: RIP RoutingDocument7 pagesAssignment 3: RIP RoutinghareemmisbahNo ratings yet
- CN Lab ManualDocument42 pagesCN Lab ManualRuthvika BhimavarapuNo ratings yet
- GAO-ENET-102 Gigabit Ethernet Tester Module For 10G PacketDocument17 pagesGAO-ENET-102 Gigabit Ethernet Tester Module For 10G PacketTaha AlhatmiNo ratings yet
- M - WAGEEH Make USB Bootable For AIX - VIOS Total On VIODocument12 pagesM - WAGEEH Make USB Bootable For AIX - VIOS Total On VIOMohamed Wageeh DiabNo ratings yet
- 1Document5 pages1s sNo ratings yet