Professional Documents
Culture Documents
Secure Virtualization With SElinux
Secure Virtualization With SElinux
Uploaded by
FrederickSharmaOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Secure Virtualization With SElinux
Secure Virtualization With SElinux
Uploaded by
FrederickSharmaCopyright:
Available Formats
____________________________________________________________________________________________________ Overview | Admin
Image (c) HTS Systems [picasaweb.google.com/HandTruckSentrySystem]. Reused under the terms of Creative Commons Attribution-
Secure Virtualisation
No Derivative Works 3.0 Unported License.
with SELinux
There’s been much brouhaha over virtualisation. Have you ever wondered what
would happen if a single compromised VM compromised all the other VMs running
on the same hardware stack?
A
s the usage of virtualisation Before virtualisation, servers were generally
increases, the security that isolated physically isolated from each other (Figure
physical machines enjoy is at risk. 1). An attacker taking over one server would
Rogue processes in a guest OS might typically have control over just that. So, if
break out of the virtual machine and get access he wanted to breach the other machines on
to the host memory or other guests. Designing the network, he essentially had to launch a
security features within hypervisors can control network-based attack to exploit them. This
this. But in case of such incidents, the risks can limited the damage of network attacks. To
be mitigated by integrating Mandatory Access avoid these kinds of attacks, administrators
Controls (MAC) with virtualisation. used different tools like network firewalls,
With the integration of MAC-capable intrusion detection/prevention systems,
security schemes like SELinux, with and unified threat management systems to
virtualisation, the security position of guest mitigate the risks.
machines can be improved. With the advent of virtualisation, several
Let's take a look at how the scenario might guest machines run on the same single host
unfold. We can begin by examining the situation server (Figure 2), and probably as the same
as it existed in the good old days when one UID. This comes with its own risks. If an
physical machine ran a dedicated server: attacker gains access to a single virtual
www.LinuxForU.com | LINUX For You | MARCH 2010 | 35
Admin | Overview _ _________________________________________________________________________________________________________
machine, he then just needs to breach the hypervisor
running on the host. If there is a hypervisor vulnerability
currently existing in the wild, he can exploit it and can
thus, eventually, take over the rest of the virtual machines
running on the host.
Understanding sVirt
sVirt was introduced as a feature of Fedora 11, and conceived
as a security mechanism for Linux-based virtualisation
schemes like the (KVM)/Qemu, and lguest. It has been
developed primarily by Dan Walsh and James Morris, of Red
Hat. Some of the goals/use-cases of sVirt are listed below:
Providing virtualised services with a level of isolation
Figure 1: Server set-ups in the absence of virtualisation
similar to that previously afforded by physical separation.
Increased protection of the host from untrustworthy VM
guests (for example, for VM hosting providers, grid/cloud
servers, etc).
Increased protection of VM guests from each other in the
event of host flaws or misconfiguration. Some protection
may also be provided against a compromised host.
Strongly isolating desktop applications by running them
in separately labelled VMs (for example, online banking
in one VM and World of Warcraft in another; opening
untrustworthy office documents in an isolated VM for
view/print only).
How does it work?
sVirt essentially works by adding SELinux support to Figure 2: Server set-ups using virtualisation
the Linux virtualisation library libvirt. It is designed as a
pluggable security framework into the libvirt API (Figure 3).
It also supports other MAC security schemes like SMACK
(Simplified Mandatory Access Control Kernel), a security
kernel module. In a typical use, one ought not to even notice
sVirt running in the background.
As you already know, SELinux works by labelling
everything like files, devices, processes, etc. The libvirt
daemon (libvirtd) starts all virtual machines. And all virtual
machines run as separate processes. libvirtd dynamically
generates labels for the image files and starts the virtual
machines with the appropriate labels. The SELinux policy has
rules that allow the svirt_t processes to read/write svirt_
image_t files and devices.
This allows us to protect the host machine from any Figure 3: Simplified libvirt architecture with sVirt integration
of its VM guests. A virtual machine will only be able to
interact with the files and devices with the correct labels. A
compromised virtual machine would not be allowed to read to SELinux, which allows users to label files with
my home directory, for example, even if the virtual machine is categories. These categories are simply text labels, such
running as the root. as ‘Company_Confidential’ or ‘Medical_Records’. The
However, this ‘type’ protection does not prevent one sysadmin first configures the categories, then assigns users
virtual machine from attacking another. We need a way to to them, as required. In a nutshell, to access a file, a user
label the domains and the image files with the same TYPES. needs to be assigned to all of the categories with which the
Yet, at the same time, we need to stop virtual machine 1 file is labelled.
(running as svirt_t) from attacking virtual machine 2, which Note: The first thing the sysadmin will want to do with MCS
would also be running as svirt_t. is configure some categories. This can be done by editing
This is where the Multi Category Security (MCS) the /etc/selinux/targeted/setrans.conf file. This file specifies
mechanism comes into play. MCS is an enhancement how the internal MCS categories can be mapped to human-
36 | MARCH 2010 | LINUX For You | www.LinuxForU.com
_________________________________________________________________________________________________________ Overview | Admin
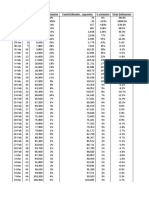
Table 1: Example VMs and their SELinux labels
Name Virtual Machine process Virtual Machine image label
label
Virtual system_u:system_r:svirt_t:s0: system_u:object_r:svirt_im-
Machine 1 c514,c932 age_t:s0:c514,c932
Virtual system_u:system_r:svirt_t:s0: system_u:object_r:svirt_
Machine 2 c101,c230 image_t:s0:c101,c230
readable formats. The following snippet system_u:object_r:svirt_image_t:s0:c514,c932
shows the typical contents of the
setrans.conf file: In the above snippets, take a look
at the MCS labels. Here, s0 indicates
s0:c0=CompanyConfidential the 'Sensitivity Level', and c514 as
s0:c1=PatientRecord well as c932 indicate the 'category of
s0:c2=Unclassified the data'. Administrators can define
s0:c3=TopSecret these categories.
If you attempt to change the
From the above snippet, the left SELinux context (using the chcon
hand side of the ‘equals to’ sign is command) of the VM image file, it will
the MCS security level, with the throw up SELinux AVC (Access Vector
corresponding human readable Cache) denials.
value on the right. To list the current SELinux prevents virtual
categories defined on your system, use machine 1 (system_u:system_r:
the chcat -L command. svirt_t:s0:c514,c932) from accessing
Each VM has unique MCS virtual machine 2's image file
categories, and the SELinux security (system_u:object_r:svirt_image_t:s0:
policy does not allow interaction c101,c230)—the VMs can't access
between different categories, each other's data, either on-disk or in-
irrespective of their actual values. The memory and hence cannot attack each
file systems' device/image for each VM other.
is also labelled with the VM's MCS
label, to prevent VMs from accessing References and
each other’s resources. acknowledgements
Till Fedora Core 5, the typical • Daniel Walsh: danwalsh.livejournal.
SELinux context consisted of only three com (sVirt blog posts/presentations/
fields: USER:ROLE:TYPE. inputs)
Later on, SELinux added one more • James Morris: http://blog.namei.
org ( sVirt blog posts/presentations/
field, so currently it's: USER:ROLE: inputs)
TYPE:MCS Label. • Amit Shah and rest of Red Hat
Let's look at the example of Table virtualization team: Review
1, where libvirt creates two virtual • svirt Wiki: http://selinuxproject.
org/page/SVirt
machines with dynamically generated • Libvirt Project page: http://wiki.
SELinux labels. libvirt.org
You can obtain the SELinux labels
for a running VM process, as follows:
By: Kashyap Chamarthy
# ps -eZ | grep qemu
Kashyap Charmarthy. The author has
system_u:system_r:svirt_t:s0:c514,c932 been working on security, identity
management and PKI technologies
You can obtain the SELinux labels for around three years and has a keen
interest in Linux-based virtualisation.
for the image, as follows: Currently he is working on open source
identity technologies at Red Hat.
# ls -lZ /var/lib/libvirt/qemu/images/f12.img
www.LinuxForU.com | LINUX For You | MARCH 2010 | 37
You might also like
- Virtual Machine Security: Jacob ZvirikuzheDocument35 pagesVirtual Machine Security: Jacob ZvirikuzheMohammad MazharNo ratings yet
- Cutting-Edge Perspective of Security Analysis For Xen Virtual MachinesDocument6 pagesCutting-Edge Perspective of Security Analysis For Xen Virtual MachinesIJERDNo ratings yet
- Virtualization Structures:Tools and MechanismsDocument8 pagesVirtualization Structures:Tools and MechanismsVasshiniNo ratings yet
- Unit-3 Resource VirtualizationDocument21 pagesUnit-3 Resource VirtualizationGeleta MitikuNo ratings yet
- Electrical Engineering and Computer Science DepartmentDocument12 pagesElectrical Engineering and Computer Science Departmenteecs.northwestern.eduNo ratings yet
- An Exhaustive Survey On Security Concerns and Solutions at Different Components of VirtualizationDocument38 pagesAn Exhaustive Survey On Security Concerns and Solutions at Different Components of Virtualizationjaime_parada3097No ratings yet
- Cloud Security Is Not (Just) Virtualization Security: A Short PaperDocument6 pagesCloud Security Is Not (Just) Virtualization Security: A Short PaperalonhazayNo ratings yet
- CC Ques Bank Cloud Computing QB UNIT 5Document7 pagesCC Ques Bank Cloud Computing QB UNIT 5aparna chinnarajNo ratings yet
- Virtualization Chapter ReaddingDocument29 pagesVirtualization Chapter Readdingm.zeeshanpc1No ratings yet
- Importance of Virtualization TechnologyDocument3 pagesImportance of Virtualization TechnologyRaja FawadNo ratings yet
- Securing and Self Recovery of Virtual Machines in CloudDocument10 pagesSecuring and Self Recovery of Virtual Machines in Cloudmiguex_reloadedNo ratings yet
- Term PapersDocument11 pagesTerm Papersdheeraj kumarNo ratings yet
- Installing and Using XenDocument52 pagesInstalling and Using Xensushants_49151525No ratings yet
- Virtualization: Concepts, Applications, and Performance ModelingDocument7 pagesVirtualization: Concepts, Applications, and Performance ModelingQuique AlvaradoNo ratings yet
- Unit 5Document36 pagesUnit 5AmudariaNo ratings yet
- CC Notes Unit 2Document26 pagesCC Notes Unit 2Soumyaranjan SahooNo ratings yet
- What Is Virtual Machine EscapeDocument2 pagesWhat Is Virtual Machine EscapesjmpakNo ratings yet
- Infrastructure As A Service (IAAS)Document12 pagesInfrastructure As A Service (IAAS)userdemo12334No ratings yet
- Security in A Virtualised WorldDocument4 pagesSecurity in A Virtualised WorldShaun NevilleNo ratings yet
- Welcome To International Journal of Engineering Research and Development (IJERD)Document5 pagesWelcome To International Journal of Engineering Research and Development (IJERD)IJERDNo ratings yet
- Forensic Analysis of Virtual Hard Drives: NtroductionDocument6 pagesForensic Analysis of Virtual Hard Drives: NtroductionKwameOpareNo ratings yet
- Unit 3Document24 pagesUnit 3surajit jatiNo ratings yet
- Chapter2-Introduction To Compute VirtualizationDocument18 pagesChapter2-Introduction To Compute Virtualizationhaithamokour11No ratings yet
- Virtual Machine Security Challenges: Case StudiesDocument14 pagesVirtual Machine Security Challenges: Case StudiesShaurya KapoorNo ratings yet
- Operating System Support For Virtual MachinesDocument14 pagesOperating System Support For Virtual MachinesLuciNo ratings yet
- System Penetration With Metasploit Framework: Ajit Kumar PradhanDocument5 pagesSystem Penetration With Metasploit Framework: Ajit Kumar PradhanXman ReturnsNo ratings yet
- Cloud Resource VirtualizationDocument39 pagesCloud Resource VirtualizationSubhadip Das Sarma100% (1)
- Practicum - Research PaperDocument10 pagesPracticum - Research PaperGavin FitzpatrickNo ratings yet
- Unit III CCDocument69 pagesUnit III CCnocej81355No ratings yet
- Unit 2Document9 pagesUnit 2naveenaNo ratings yet
- Simulating Cyber AttacksDocument10 pagesSimulating Cyber AttackssmmsssNo ratings yet
- Virtual IzationDocument3 pagesVirtual IzationAzeddien SllameNo ratings yet
- Cloud Native Technologies 5Document9 pagesCloud Native Technologies 5serdal bilginNo ratings yet
- C10. Ubuntu and Cloud ComputingDocument37 pagesC10. Ubuntu and Cloud ComputingThanh Tuấn PhanNo ratings yet
- All UnitDocument35 pagesAll UnitrajakumariNo ratings yet
- Virtual IzationDocument40 pagesVirtual Izationshabir AhmadNo ratings yet
- VIRTUALIZATIONDocument31 pagesVIRTUALIZATIONmetheans_791455933No ratings yet
- 1) What Is A Virtual Machine?Document2 pages1) What Is A Virtual Machine?Beatriz GonçalvesNo ratings yet
- Final Unit III CC 2022Document71 pagesFinal Unit III CC 2022sairabanu pansareNo ratings yet
- Inside of StuxnetDocument6 pagesInside of Stuxnetajay_000No ratings yet
- Unit - 2 Virtual Machines and Virtualization of Clusters and Data CentersDocument28 pagesUnit - 2 Virtual Machines and Virtualization of Clusters and Data CentersAkkireddi SrinivasNo ratings yet
- A Security-Privacy Based Model For Operating Systems: Kalyani Kaviti 59142Document7 pagesA Security-Privacy Based Model For Operating Systems: Kalyani Kaviti 59142yaminiallu2612No ratings yet
- Trusting Your Cloud Provider. Protecting Private Virtual MachinesDocument11 pagesTrusting Your Cloud Provider. Protecting Private Virtual MachinesAleksanderNo ratings yet
- VirtualizationDocument13 pagesVirtualizationsupergamerr09No ratings yet
- Virtualization Security For Cloud Computing Service: Shengmei Luo Zhaoji Lin Xiaohua Chen Zhuolin Yang, Jianyong ChenDocument6 pagesVirtualization Security For Cloud Computing Service: Shengmei Luo Zhaoji Lin Xiaohua Chen Zhuolin Yang, Jianyong ChenVeera Reddy DasariNo ratings yet
- Club Hack Magazine 35 PDFDocument31 pagesClub Hack Magazine 35 PDFLeonardo Herrera RomeroNo ratings yet
- Multi Tier ArchitectureDocument5 pagesMulti Tier ArchitectureCătălin C ZotaNo ratings yet
- Virtualization: Virtual Machine TechnologyDocument9 pagesVirtualization: Virtual Machine TechnologyShreya ChakrabortyNo ratings yet
- DockerDocument14 pagesDockerThretha ReddyNo ratings yet
- Lynx FuzzerDocument6 pagesLynx FuzzerJohn NihaNo ratings yet
- Effective Way To Defend The Hypervisor Attacks in Cloud ComputingDocument6 pagesEffective Way To Defend The Hypervisor Attacks in Cloud ComputingVINOD DADASO SALUNKHE 20PHD0400No ratings yet
- VM Security WPDocument7 pagesVM Security WPneangelesNo ratings yet
- Virtual Machine SecurityDocument18 pagesVirtual Machine SecuritykaavyaNo ratings yet
- Patch Auditing in Infrastructure As A Service Clouds: Lionel Litty David LieDocument11 pagesPatch Auditing in Infrastructure As A Service Clouds: Lionel Litty David LiepulaksayNo ratings yet
- Towards Multi-Layer Autonomic Isolation of Cloud Computing and Networking ResourcesDocument4 pagesTowards Multi-Layer Autonomic Isolation of Cloud Computing and Networking ResourcesAPOB1983No ratings yet
- (IJCST-V11I4P4) :dr. Vinit A. Sinha, Dr. Vilas M. ThakareDocument9 pages(IJCST-V11I4P4) :dr. Vinit A. Sinha, Dr. Vilas M. ThakareEighthSenseGroupNo ratings yet
- Trusted CloudDocument5 pagesTrusted CloudTooba AamirNo ratings yet
- AZURE AZ 500 STUDY GUIDE-2: Microsoft Certified Associate Azure Security Engineer: Exam-AZ 500From EverandAZURE AZ 500 STUDY GUIDE-2: Microsoft Certified Associate Azure Security Engineer: Exam-AZ 500No ratings yet
- The Ordering of Rules in Panini's GrammarDocument8 pagesThe Ordering of Rules in Panini's GrammarFrederickSharmaNo ratings yet
- Bhandarkar Oriental Research InstituteDocument9 pagesBhandarkar Oriental Research InstituteFrederickSharmaNo ratings yet
- Bala Murali Krishna - Cover StoryDocument2 pagesBala Murali Krishna - Cover StoryFrederickSharmaNo ratings yet
- Sanskrit at Layola CollegeDocument27 pagesSanskrit at Layola CollegeFrederickSharmaNo ratings yet
- A Critical Study of Sanskrit PhoneticsDocument1 pageA Critical Study of Sanskrit PhoneticsFrederickSharmaNo ratings yet
- Rhotic Degemination in Sanskrit and The Etymology of Vedic Ūrú - Thigh', Hittite UZU (U) Walla - Id.'Document32 pagesRhotic Degemination in Sanskrit and The Etymology of Vedic Ūrú - Thigh', Hittite UZU (U) Walla - Id.'FrederickSharmaNo ratings yet
- A Critical Study of Sanskrit PhoneticsDocument1 pageA Critical Study of Sanskrit PhoneticsFrederickSharmaNo ratings yet
- Approximating NP-hard Problems: Efficient Algorithms and Their LimitsDocument71 pagesApproximating NP-hard Problems: Efficient Algorithms and Their LimitsFrederickSharmaNo ratings yet
- About SanskritDocument131 pagesAbout SanskritFrederickSharmaNo ratings yet
- Generative AI For Constructive CommunicationDocument56 pagesGenerative AI For Constructive CommunicationFrederickSharmaNo ratings yet
- Applied Sanskrit Grammar CourseDocument5 pagesApplied Sanskrit Grammar CourseFrederickSharmaNo ratings yet
- Secure Virtualization in LinuxDocument23 pagesSecure Virtualization in LinuxFrederickSharmaNo ratings yet
- S. N. Balagangadhara and Marianne Keppens: Reconceptualizingthe PostcolonialprojectDocument19 pagesS. N. Balagangadhara and Marianne Keppens: Reconceptualizingthe PostcolonialprojectFrederickSharmaNo ratings yet
- Nielsen Kai - On Taking Historical Materialism SeriouslyDocument20 pagesNielsen Kai - On Taking Historical Materialism SeriouslyFrederickSharmaNo ratings yet
- Is There A Curse of The Fields Medal?Document7 pagesIs There A Curse of The Fields Medal?FrederickSharmaNo ratings yet
- Poverty of Theistic CosmologyDocument54 pagesPoverty of Theistic CosmologyFrederickSharmaNo ratings yet
- Ergative Is Not InherentDocument6 pagesErgative Is Not InherentFrederickSharmaNo ratings yet
- The Ottoman Empire Judaism and Eastern EuropeDocument36 pagesThe Ottoman Empire Judaism and Eastern EuropeFrederickSharmaNo ratings yet
- Myrmikan Research 2022/08/11Document8 pagesMyrmikan Research 2022/08/11FrederickSharmaNo ratings yet
- Chetulim1 PDFDocument1 pageChetulim1 PDFFrederickSharmaNo ratings yet
- American Spoken English: DG DaviesDocument2 pagesAmerican Spoken English: DG DaviesFrederickSharmaNo ratings yet
- The American Horse Slaughter Prevention ActDocument16 pagesThe American Horse Slaughter Prevention ActFrederickSharmaNo ratings yet
- Narale Ratnakar. - Let's Learn Sanskrit Through English Medium. Level 1. Book 1 PDFDocument43 pagesNarale Ratnakar. - Let's Learn Sanskrit Through English Medium. Level 1. Book 1 PDFFrederickSharmaNo ratings yet
- American Spoken Language in Real LifeDocument150 pagesAmerican Spoken Language in Real LifeBorhan Uddin AzadNo ratings yet
- Appalachian SpeechDocument195 pagesAppalachian SpeechFrederickSharmaNo ratings yet
- Silicon Graphics Octane 1210Document12 pagesSilicon Graphics Octane 1210Sam PanckeNo ratings yet
- Chapter 6: Architecture and InfrastructureDocument12 pagesChapter 6: Architecture and InfrastructureAhmed MohamadNo ratings yet
- 3D ModellingDocument47 pages3D Modellingcess rabajaNo ratings yet
- FINAL REVIEW - MergedDocument29 pagesFINAL REVIEW - MergedGayathri kNo ratings yet
- Epoca: User ManualDocument18 pagesEpoca: User ManualAntonio FavuzziNo ratings yet
- Resume Rajasekhar LingisettyDocument4 pagesResume Rajasekhar LingisettyAdmin DigiepitomeNo ratings yet
- Five Paradigms in The Psychology of ProgrammingDocument19 pagesFive Paradigms in The Psychology of ProgrammingHakan BayezitNo ratings yet
- January 2024Document2 pagesJanuary 2024Elmer MissiorNo ratings yet
- Teamcenter 12.3 Configure Your Business Data Model in Bmide: Siemens Siemens SiemensDocument1,044 pagesTeamcenter 12.3 Configure Your Business Data Model in Bmide: Siemens Siemens SiemensAnudeep Reddy SolletiNo ratings yet
- Nuevo Hoja de Cálculo de Microsoft ExcelDocument14 pagesNuevo Hoja de Cálculo de Microsoft ExcelMarcelo SalasNo ratings yet
- Case Study On Windows Ms. Jaya Gangwani Unit V: Case Study On WindowsDocument15 pagesCase Study On Windows Ms. Jaya Gangwani Unit V: Case Study On WindowsArpit GoswamiNo ratings yet
- Audition Form EngDocument2 pagesAudition Form EngJessie IsabelNo ratings yet
- Aerospace Sheetmetal Design - DassaultDocument331 pagesAerospace Sheetmetal Design - DassaultGehteuch Nixan100% (1)
- Swiss Timing - C++ DeveloperDocument2 pagesSwiss Timing - C++ Developermamatovmurat0No ratings yet
- Cs 401 Quiz 4Document4 pagesCs 401 Quiz 4b0300007No ratings yet
- NUP NetworkUpgradeProc IDX21 and Later To 30 RevC 110311Document86 pagesNUP NetworkUpgradeProc IDX21 and Later To 30 RevC 110311shahramNo ratings yet
- TSC TTP 244 PlusDocument2 pagesTSC TTP 244 Plussaasnalan palanisamyNo ratings yet
- BuildDocument3 pagesBuildkuro teknoNo ratings yet
- CS844 Series: Carbon/Sulfur by Combustion: Delivering The Right ResultsDocument6 pagesCS844 Series: Carbon/Sulfur by Combustion: Delivering The Right ResultsAlfredo MarcanoNo ratings yet
- Introduction To MS Team: Presentation By: Tech Support Client - InfrastructureDocument11 pagesIntroduction To MS Team: Presentation By: Tech Support Client - InfrastructureRajveer SinghNo ratings yet
- Lab Manual Soft Computing IT - 701Document60 pagesLab Manual Soft Computing IT - 701Devendra Singh KaushalNo ratings yet
- Simio Release NotesDocument65 pagesSimio Release NotesDaniel Alcorac Alemán HernándezNo ratings yet
- 20CS2203 - Software EngineeringDocument2 pages20CS2203 - Software Engineeringsowmitha devireddyNo ratings yet
- Welcome CICSDocument2 pagesWelcome CICSsdineeshkumarNo ratings yet
- MicrosoftTraining DevOpsDocument154 pagesMicrosoftTraining DevOpsCarlos DiasNo ratings yet
- Infographics ModuleDocument16 pagesInfographics Moduleanis jelita100% (1)
- Train Reservation System DocumentationDocument27 pagesTrain Reservation System DocumentationDev TwentiesNo ratings yet
- Chapter 1 Algorithm and Complexity Lesson 1Document18 pagesChapter 1 Algorithm and Complexity Lesson 1Christopher Roxas CheNo ratings yet
- GAMSTAT - NSS (Nand)Document42 pagesGAMSTAT - NSS (Nand)SUURAJ 29No ratings yet
- SMV Technical Reference Guide PDFDocument92 pagesSMV Technical Reference Guide PDFAlberto LeónNo ratings yet