Professional Documents
Culture Documents
Sentinel One DV Chea 2
Sentinel One DV Chea 2
Uploaded by
YOUSSEF DANANOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Sentinel One DV Chea 2
Sentinel One DV Chea 2
Uploaded by
YOUSSEF DANANCopyright:
Available Formats
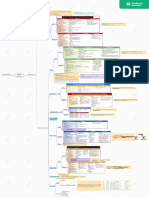
SECURITY ANALYST CHEATSHEET
QUERY SYNTAX QUERY SYNTAX
HOST/AGENT INFO PROCESS TREE
Hostname AgentName Process ID PID
OS AgentOS PID of the parent process ParentPID
Version of Agent AgentVersion Parent Process ParentProcessName
Domain name DNSRequest
Time parent process started to run ParentProcessStartTime
Site ID SiteId
Unique ID of parent process ParentProcessUniqueKey
Site name SiteName
Process command line ProcessCmd
Account ID AccountId
Display name of process ProcessDisplayName
Account Name AccountName
Generated ID of the group of
processes, from first parent to last ProcessGroupId
FILE/REGISTRY INTEGRITY generation (SentinelOne Patent)
File ID FileID
Pathname of running process ProcessImagePath
File Name FileFullName
SHA1 signature of running process ProcessImageSha1Hash
Date and time of file creation FileCreatedAt
String: SYSTEM (operating system
MD5 FileMD5 processes), HIGH (administrators),
Date and time of file change FileModifyAt MEDIUM (non-administrators), ProcessIntegrityLevel
LOW (temporary Internet files),
SHA1 signature FileSHA1
UNTRUSTED
SHA256 signature FileSHA256
Process Name ProcessName
SHA1 of file before it was changed OldFileSHA1
ID of the terminal session of a
Name of file before rename OldFileName ProcessSessionId
process
Identity of file signer Publisher
Process start time ProcessStartTime
Signature Status Signed Status
String: SYS_WIN32, SYS_WSL,
Verification Status Verified status ProcessSubSystem
SUBSYSTEM_UNKNOWN
Why not verified Why not verified
Unique ID of process ProcessUniqueKey
Registry Key Unique ID RegistryID
PID after relinked Rpid
Full path location of the
RegistryPath Thread ID Tid
Registry Key entry
ID of all objects associated TrueContext
with a detection
NETWORK DATA
String: GET, POST, PUT, DELETE NetworkMethod Username User
URL NetworkUrl
SCHEDULED TASKS
DNS response data DNSResponse
IP address of the destination DstIP Name of a scheduled task TaskName
Port number of destination DstPort Full path location of a
TaskPath
scheduled task
IP address of traffic source SrcIP
The file who has been executed executable file
Port number of traffic source SrcPort
Browser type Source
www.SentinelOne.com | Sales@SentinelOne.com | +1-855-868-3733 | 605 Fairchild Dr, Mountain View, CA 94043
HUNTING QUERIES
QUERY SYNTAX QUERY SYNTAX
ProcessCmd RegExp "net\s+user(?:(?!\s+/add) Clear Windows Event Logs ProcessCmd ContainsCIS "wevtutil cl system"
Net User Add User (?:.|\n))*\s+/add" Powershell or Wevtutil OR ProcessCmd ContainsCIS "Clear-EventLog"
processCmd = "REG ADD HKLM\SYSTEM\ ProcessCmd ContainsCIS "netsh firewall"
Enable SMBv1 CurrentControlSet\Services\LanmanServer\ netsh disable firewall AND ProcessCmd ContainsCIS "disable"
Parameters /v SMB1 /t REG_DWORD /d 1 /f"
Query logged in Users ProcessCmd ContainsCIS "quser"
Unusual Schedule ProcessCmd ContainsCIS "schtasks" AND
Task Created processName != "Manages scheduled tasks" Qwinsta - Display
information Terminal ProcessCmd ContainsCIS "qwinsta"
Powershell with Net DstIP Is Not Empty AND ProcessName Sessions
connections ContainsCIS "powershell"
Current Running Processes ProcessCmd ContainsCIS "tasklist"
(ProcessName ContainsCIS "windows command
processor" OR ProcessName ContainsCIS Net User - Query a User ProcessCmd ContainsCIS "net user"
Shell Process Creating File "powershell") AND FileModifyAt > "Mar 26,
2017 00:00:39" Query Network Shares ProcessCmd ContainsCIS "net share"
(ProcessName ContainsCIS "windows command Query Account &
ProcessCmd ContainsCIS "net accounts"
processor" OR ProcessName ContainsCIS Password Policy
Shell Process Modify or File "powershell") AND (FileModifyAt > "Mar 26,
Net Config - Query
2017 00:00:10" OR FileCreatedAt > "Mar 26, ProcessCmd ContainsCIS "net config
2017 00:00:31") Workstation Current Settings workstation"
Registry Alteration via ProcessCmd RegExp "reg\s+add" OR ProcessCmd Query AD ProcessCmd ContainsCIS "dsquery"
Command line RegExp "reg\s+del" ProcessCmd ContainsCIS "wmic useraccount get"
WMIC user account list OR ProcessCmd RegExp "wmic useraccount list"
processImagePath = "C:\Windows\System32\
svchost.exe running in a svchost.exe" AND User != "NT AUTHORITY\ WMIC NT Domain
SYSTEM" AND User != "NT AUTHORITY\LOCAL ProcessCmd ContainsCIS "wmic ntdomain"
unusual user context Object Query
SERVICE" AND User != "NT AUTHORITY\NETWORK
SERVICE" WMIC Group List on
ProcessCmd ContainsCIS "wmic group list"
Powershell runnning as Local System
ProcessName ContainsCIS "powershell" AND User
system user ContainsCIS "SYSTEM" WMIC List built in ProcessCmd ContainsCIS "wmic
ParentProcessName = "Windows PowerShell" AND System Accounts sysaccount list"
Powershell Scheduled
ProcessName = "Task Scheduler Configuration Reg Query - last 10 files ProcessCmd ContainsCIS "RecentDocs" AND
Tasks Created Tool" accessed or executed ProcessCmd ContainsCIS "REG QUERY" AND
FileCreatedAt > "Apr 2, 2017 00:00:03" AND by explorer ProcessCmd ContainsCIS "explorer"
Executable Created ProcessName ContainsCIS ".exe"
ProcessCmd ContainsCIS "Runonce" AND
Reg Query - RunOnce ProcessCmd ContainsCIS "REG QUERY"
ProcessName ContainsCIS "Host Process for
Suspicious Parent Windows Services" AND ParentProcessName !=
"Host Process for Windows Services" AND Reg Query - Check Patterns ProcessCmd ContainsCIS "Reg Query"
Process svchost.exe ParentProcessName != "Services and Controller AND ProcessCmd ContainsCIS "Disk" AND
for Virtual Machines ProcessCmd ContainsCIS "Enum"
app"
ParentProcessName = "Insert Vulnerable Query Group Policy
ProcessCmd ContainsCIS "gpresult"
Application name from Applications Tab" AND RSOP Data
Vulnerable App
(ProcessName ContainsCIS "Windows Command System Info - windows ProcessCmd ContainsCIS "systeminfo"
launching shell Processor" OR ProcessName ContainsCIS
"Powershell") ProcessCmd ContainsCIS "systeminfo" OR
ProcessCmd RegExp "ver >" OR ProcessCmd
Excel Running Shell ParentProcessName ContainsCIS "excel" AND System Info and RegExp "type\s+%APPDATA%" OR ProcessCmd
(ProcessName ContainsCIS "sh" OR ProcessName
or Python ContainsCIS "python") Network data gathering RegExp "ipconfig" OR ProcessCmd RegExp "net\
s+view" OR ProcessCmd RegExp "arp -a" OR
Whoami ProcessCmd ContainsCIS "whoami" ProcessCmd RegExp "netstat"
Powershell Get processCmd RegExp "powershell\.exe\s+echo\ WMIC Process Get - Process
ProcessCmd RegExp "wmic\s+process\s+get"
Clipboard Entry s+Get\-Process\s+\|\s+clip" data and sub commands
Powershell Get processCmd ContainsCIS "powershell.exe echo WMIC qfe - Gather
ProcessCmd ContainsCIS "wmic qfe"
Running Processes Get-Process" Windows Patch Data
Powershell Search processCmd ContainsCIS "powershell Get- ProcessName ContainsCIS "powershell"
for Doc Files ChildItem -Recurse -Include *.doc" AND (ProcessCmd ContainsCIS "Invoke-
Powershell suspicious Expression" OR ProcessCmd ContainsCIS
Find string processCmd ContainsCIS "findstr" "-encodedcommand" OR ProcessCmd ContainsCIS
commands "hidden" OR ProcessCmd ContainsCIS "write-
Windows 10 Get host" OR ProcessCmd ContainsCIS "Get-
ProcessCmd ContainsCIS "wmic nic"
Network Adaptor Details NetIPConfiguration")
Execute File in processCmd ContainsCIS "/FILE" AND ProcessCmd echo command ProcessCmd ContainsCIS "echo"
Appdata folder ContainsCIS "Appdata"
regsvr32 and scrobj.dll ProcessCmd ContainsCIS "regsvr32" AND
Nslookup ProcessCmd ContainsCIS "nslookup" register-unregister dll ProcessCmd ContainsCIS "scrobj.dll"
Net User Delete User
ProcessCmd RegExp "net\s+user(?:(?!\s+/ regsvr32 suspicious processName = "Microsoft(C) Register Server"
delete)(?:.|\n))*\s+/delete" downloads AND DstIP Is Not Empty
ProcessCmd RegExp "net\s+user(?:(?!\s+/ regsvr32 suspicious processName = "Microsoft(C) Register Server"
Net User Domain domain)(?:.|\n))*\s+/domain" file modification AND FileModifyAt > "Mar 1, 2019 00:00:45"
Add user to AD ProcessCmd ContainsCIS "dsadd user" ProcessCmd ContainsCIS "regsvr32" AND
ProcessCmd ContainsCIS "powershell.exe (RegistryPath ContainsCIS "machine\software\
Powershell add local user regsvr32 Persistence classes" OR ProcessCmd ContainsCIS "schtasks\
New-LocalUser"
s+/create")
Powershell upload or ProcessCmd ContainsCIS "(New-Object Net.
download methods Webclient)" ProcessCmd ContainsCIS "bitsadmin" AND
Bitsadmin suspicious (ProcessCmd ContainsCIS "transfer" OR
ProcessCmd ContainsCIS "setspn" AND ProcessCmd ContainsCIS "download" OR
Suspicious - List all commands ProcessCmd ContainsCIS ".ps1" OR ProcessCmd
ProcessCmd RegExp "-t" AND ProcessCmd RegExp
SPNs in a Domain "-q */*" ContainsCIS "powershell")
ProcessCmd ContainsCIS "vssadmin.exe list ProcessCmd ContainsCIS "reg add" AND
list vssadmin shadows shadows" Registry Persistence (ProcessCmd ContainsCIS "Run" OR ProcessCmd
ContainsCIS "Null")
Add user or Query local ProcessCmd ContainsCIS "net localgroup
admin group administrators" ProcessCmd ContainsCIS "copy" OR ProcessCmd
Copy commands ContainsCIS "xcopy"
Change firewall
ProcessCmd ContainsCIS "netsh advfirewall"
profile settings
www.SentinelOne.com | Sales@SentinelOne.com
+1-855-868-3733 | 605 Fairchild Dr, Mountain View, CA 94043
You might also like
- BeyondTrust Password Safe External PresentationDocument32 pagesBeyondTrust Password Safe External PresentationAnonymous H5wWChNo ratings yet
- Microsoft Sentinel Technical Playbook For MSSPsDocument60 pagesMicrosoft Sentinel Technical Playbook For MSSPsIlham SauqiNo ratings yet
- IDENTIKEY Authentication Server SDK Programmer's GuideDocument149 pagesIDENTIKEY Authentication Server SDK Programmer's GuideGeorge Szo CristianNo ratings yet
- Threat Hunting Worksheet Fillable - OlimpycDestroyerDocument1 pageThreat Hunting Worksheet Fillable - OlimpycDestroyerMiguelNo ratings yet
- Introducing Cyberark: Security For The Heart of The EnterpriseDocument9 pagesIntroducing Cyberark: Security For The Heart of The Enterprisesantoshs2002848No ratings yet
- ProductDefInterface FixDocument3 pagesProductDefInterface FixPARAS BAJAJNo ratings yet
- Azure Sentinel MGMT Using PowerShellDocument40 pagesAzure Sentinel MGMT Using PowerShellLakshmipathiMuruganNo ratings yet
- TR18 AD MSFT Defence at ScaleDocument31 pagesTR18 AD MSFT Defence at ScalekeepzthebeezNo ratings yet
- Siem - ReportDocument8 pagesSiem - Reportapi-335480408No ratings yet
- NeXpose User GuideDocument317 pagesNeXpose User GuidePrince WilliamsNo ratings yet
- Generic Product Keys For Windows 10Document3 pagesGeneric Product Keys For Windows 10Bladwijzer SyncNo ratings yet
- SentinelOne DV Cheatsheet Opt2-2Document3 pagesSentinelOne DV Cheatsheet Opt2-2gobfNo ratings yet
- Passwordless - Authentication - WP FinalDocument8 pagesPasswordless - Authentication - WP FinalyawahabNo ratings yet
- Corelight Threat Hunting Guide - 946762Document28 pagesCorelight Threat Hunting Guide - 946762subin28o5No ratings yet
- Technical Overview: Azure Sentinel Level 400Document40 pagesTechnical Overview: Azure Sentinel Level 400Xp rienceNo ratings yet
- Endpoint Security 10.6.0 - WebDocument57 pagesEndpoint Security 10.6.0 - WebDoan Dinh Long100% (1)
- Create A File That Brbbot - Exe Might Understand and Allow The Specimen To Download ItDocument23 pagesCreate A File That Brbbot - Exe Might Understand and Allow The Specimen To Download Itgekaco4432No ratings yet
- 01 - SA - 2022 - VRMMM - User Procedure - Guide - 20210928Document11 pages01 - SA - 2022 - VRMMM - User Procedure - Guide - 20210928Melody ShekharNo ratings yet
- SIEM Process FlowDocument1 pageSIEM Process FlowhallarmemonNo ratings yet
- What Is Identity and Access Management - Guide To IAMDocument8 pagesWhat Is Identity and Access Management - Guide To IAMharshNo ratings yet
- 2024ThreatDetectionReport RedCanaryDocument161 pages2024ThreatDetectionReport RedCanarywies551425100% (1)
- Cortex XDR Handson Workshop Lab GuideDocument64 pagesCortex XDR Handson Workshop Lab Guideamirel80No ratings yet
- Emerging Technology Analysis - SOARDocument11 pagesEmerging Technology Analysis - SOARsharmasunil6325No ratings yet
- SOAR in CybersecurityDocument7 pagesSOAR in CybersecurityITLeadup AmbassadeursNo ratings yet
- 2022 Threat Detection Report Full VersionDocument80 pages2022 Threat Detection Report Full VersionCarmelo ToledoNo ratings yet
- Multi-Factor Authentication With ISEDocument4 pagesMulti-Factor Authentication With ISERakesh BadayaNo ratings yet
- Darktrace: Best Practices For Small Teams: Data SheetDocument8 pagesDarktrace: Best Practices For Small Teams: Data SheetLuc CardNo ratings yet
- Deploying Darktrace AWS Security ModuleDocument11 pagesDeploying Darktrace AWS Security ModuleAndre GaioNo ratings yet
- SANS Malware Analysis & Reverse Engineering Cheat SheetDocument1 pageSANS Malware Analysis & Reverse Engineering Cheat Sheetcristhian sanchezNo ratings yet
- SentinelOne TrainingDocument6 pagesSentinelOne TrainingjaisinglaNo ratings yet
- Thales Luna Network 7 HSM PB v35Document3 pagesThales Luna Network 7 HSM PB v35NingNo ratings yet
- Scoping Questionnaire TemplateDocument3 pagesScoping Questionnaire Templatelagib78166No ratings yet
- Kerberos Authentication Protocol Simulation: Course: Cpe 597 B Advisor: Prof. Khaled ElleithyDocument32 pagesKerberos Authentication Protocol Simulation: Course: Cpe 597 B Advisor: Prof. Khaled ElleithyPhani PatibandlaNo ratings yet
- GravityZone OnPremise-1Document162 pagesGravityZone OnPremise-1Irina NastasescuNo ratings yet
- Darktrace Virtualized Enterprise Immune System DeploymentsDocument4 pagesDarktrace Virtualized Enterprise Immune System DeploymentsNelson JuniorNo ratings yet
- CCSK OverviewDocument24 pagesCCSK OverviewSaad MotenNo ratings yet
- Application SecurityDocument29 pagesApplication SecurityIhab AbdullahNo ratings yet
- Defense in Depth Checklist Controls: 50 Easy-to-Implement Controls To Strengthen Your SecurityDocument8 pagesDefense in Depth Checklist Controls: 50 Easy-to-Implement Controls To Strengthen Your SecurityManish AgarwalNo ratings yet
- Malware Analysis CIS-672: Lecture 01: IntroductionDocument37 pagesMalware Analysis CIS-672: Lecture 01: Introductionsarim imranNo ratings yet
- Soc RaciDocument2 pagesSoc RaciLyu SeyNo ratings yet
- Sophoslabs Ransomware Behavior ReportDocument29 pagesSophoslabs Ransomware Behavior ReportSaurabh SharmaNo ratings yet
- Threat Modeling Tool 2016 User GuideDocument59 pagesThreat Modeling Tool 2016 User GuideSenthilkumarmoorthyNo ratings yet
- Network Security EngineeringDocument17 pagesNetwork Security EngineeringGeorge PrintezisNo ratings yet
- Attacks and Vulnerabilities: Ilya Chalyt Nicholas EgeboDocument46 pagesAttacks and Vulnerabilities: Ilya Chalyt Nicholas EgeboAkash AgrawalNo ratings yet
- Ddos Handbook Online PDFDocument37 pagesDdos Handbook Online PDFMyat Min PaingNo ratings yet
- Career Path Syllabus - SOC Analyst Level 1Document3 pagesCareer Path Syllabus - SOC Analyst Level 1Muhammad IbrahimNo ratings yet
- Darktrace VSensors and Amazon VPC MirroringDocument15 pagesDarktrace VSensors and Amazon VPC MirroringAndre GaioNo ratings yet
- Utilising YARA For Malware Detection TLP GREEN PDFDocument10 pagesUtilising YARA For Malware Detection TLP GREEN PDFStratigus Pty LtdNo ratings yet
- Security Design PrinciplesDocument20 pagesSecurity Design Principlesroshanak attarNo ratings yet
- Information Security Unit - 1Document11 pagesInformation Security Unit - 1Lokesh Sai Kumar DasariNo ratings yet
- Securing Your Active Directory. Chapter 1 - Perform A Self-AuditDocument51 pagesSecuring Your Active Directory. Chapter 1 - Perform A Self-Auditcharbel100% (1)
- Abhishek: 20BCS3591@cuchd - in Chandel-B682061b8Document1 pageAbhishek: 20BCS3591@cuchd - in Chandel-B682061b8madhu jhaNo ratings yet
- 14 - OAuth Implementation Then LabDocument39 pages14 - OAuth Implementation Then LabUjjwal Joshi100% (1)
- Privileged Account Security Web Services SDK Implementation Guide PDFDocument273 pagesPrivileged Account Security Web Services SDK Implementation Guide PDFLeandro LomibaoNo ratings yet
- Cortex XSOAR: Redefining Security Orchestration, Automation, and ResponseDocument7 pagesCortex XSOAR: Redefining Security Orchestration, Automation, and ResponseHenry DsouzaNo ratings yet
- The Official Comptia Cysa Student Guide Exam Cs0 002 PDF FreeDocument675 pagesThe Official Comptia Cysa Student Guide Exam Cs0 002 PDF FreeManuel EspritNo ratings yet
- Security Threat and AWS Modeling Project LectureDocument11 pagesSecurity Threat and AWS Modeling Project LectureNopeNo ratings yet
- Threat Hunting - Hunter or HuntedauthorDocument8 pagesThreat Hunting - Hunter or HuntedauthorMateen KianiNo ratings yet
- Network Programmability and Automation: Open TranscriptDocument9 pagesNetwork Programmability and Automation: Open TranscriptcasrilalsiNo ratings yet
- Cortex XDR 5Document13 pagesCortex XDR 5degadisa104No ratings yet
- MFS Team Season V FULL: Update NewsDocument4 pagesMFS Team Season V FULL: Update NewsBach TungNo ratings yet
- Class Activity - Identify Running ProcessesDocument3 pagesClass Activity - Identify Running ProcessesKwimpal NychaNo ratings yet
- WAS IssueDocument4 pagesWAS IssueVijay KumarNo ratings yet
- HPHWDiag LogDocument26 pagesHPHWDiag LogLuis Alberto Farfan RamosNo ratings yet
- Oriya Indic Input 3-User GuideDocument10 pagesOriya Indic Input 3-User GuideBoby JosephNo ratings yet
- LogDocument219 pagesLogJúlio Queiroz MachadoNo ratings yet
- Usbfix (Clean 1) Ceimec5-PcDocument4 pagesUsbfix (Clean 1) Ceimec5-PcDante LeccaNo ratings yet
- S.K.U College of Engineering & Technology, Anantapur: Curriculum Vitae'Document1 pageS.K.U College of Engineering & Technology, Anantapur: Curriculum Vitae'peoplesoft2oracleNo ratings yet
- Mindmap - Analysis ScenariosDocument1 pageMindmap - Analysis ScenariosJonasNo ratings yet
- MNFSTDocument7 pagesMNFSTAndrianNo ratings yet
- SDKSetup 7.0.6918.0Document25 pagesSDKSetup 7.0.6918.0DarmawanNo ratings yet
- How To Install Tems Discovery On Window 7Document1 pageHow To Install Tems Discovery On Window 7Bamidele Odediya50% (2)
- Transform Your Windows XP To Windows Vista Without Any Customization PackDocument10 pagesTransform Your Windows XP To Windows Vista Without Any Customization Packthejaswi100% (2)
- Serial KeysDocument2 pagesSerial KeysAdil Hamad100% (1)
- This Is An Icon Pack For TuneUp Styler. These IconsDocument1 pageThis Is An Icon Pack For TuneUp Styler. These IconsbinhpsNo ratings yet
- Setting Up Python and Visual Studio Code - Windows 10Document5 pagesSetting Up Python and Visual Studio Code - Windows 10ste.mc.uniNo ratings yet
- InstallDocument3 pagesInstallelkaNo ratings yet
- PW DebugDocument2 pagesPW DebugNanang WibisonoNo ratings yet
- Weekly Home Learning Plan Grade 9 - Computer Systems Servicing Ii Quarter 2Document3 pagesWeekly Home Learning Plan Grade 9 - Computer Systems Servicing Ii Quarter 2NielNo ratings yet
- Installation Manual For WindowsDocument7 pagesInstallation Manual For WindowsJoram MHNo ratings yet
- Tutorial Universal Theme Patcher, Take Ownership, and Windows Theme InstallerDocument8 pagesTutorial Universal Theme Patcher, Take Ownership, and Windows Theme InstallerchitraNo ratings yet
- Readme enDocument4 pagesReadme enLuzsilenny Peña RodriguezNo ratings yet
- ANT User Installation & Help ManualDocument5 pagesANT User Installation & Help ManualSuyash KhairnarNo ratings yet
- ReadmeDocument3 pagesReadmeIrfan RazaNo ratings yet
- Serial Number Windows 10 All VersionDocument9 pagesSerial Number Windows 10 All VersionAqsa Ashabul YaminNo ratings yet
- Darryl Resume NewDocument2 pagesDarryl Resume NewDarryl Chatty ChapmanNo ratings yet
- CompDocument66 pagesCompSofia JaneNo ratings yet
- NI-myDAQ Doesn't Work On Labview 12 64bits - Discussion ForumsDocument2 pagesNI-myDAQ Doesn't Work On Labview 12 64bits - Discussion ForumsArthur PoletoNo ratings yet