Professional Documents
Culture Documents
True or False
True or False
Uploaded by
Chimou MKOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
True or False
True or False
Uploaded by
Chimou MKCopyright:
Available Formats
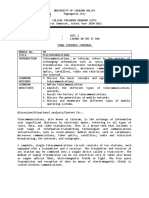
Chapter 1.
IoT development history and Overview
1. The Trojan room coffee pot of the computer laboratory in Cambridge University
is an example of an IoT solution. False
2. ITU referred to the IoT concept at the world summit on the information society
in 2005. True
3. NB-IoT is developed for 5G technologies. False
4. The first 3GPP standard for the 5G is Release-16. True
5. VR glasses, body fat scales, smart locks, and smart speakers are examples of
industry-related IoT products. False
6. Smart agriculture is an example of industry-related IoT products. True
7. IoT is an Internet where all things are interconnected. True
8. IoT requires moving from the internet of things to the internet of people. False
9. IoT model includes 4 layers. True
10. In the IoT model, the platform layer collects Information and process signals.
False
11. Huawei IoT solution architecture is 1+2+1. True
12. Huawei cloud IoT platform is open, pre-integrated and access-dependent. False
13. Bluetooth is an example of communication protocols used by IoT applications.
False
14. Fully open smart ONT requires a bit rate up to 1 Gbit/s. True
15. In the IoT model, device management and security maintenance are performed
by the platform. True
16. Huawei IoT Solution Architecture is 1+2+1 means: one IoT access method, two
platforms, and one IoT operating system. False
17. Huawei LiteOS features low power consumption, small size, and quick response.
True
18. NB-IoT stands for NearBand Internet of Things. False
19. Huawei LiteOS features basic kernel size less than 20 kB. False
20. 5G Architecture supports both NFV and SDN. True
HCIA-IoT V2.5 1 CC BY 4.0
1. Traffic management is a common problem in modern cities. True
2. Environmental sanitation is not included in the city management scenario. False
3. Device management in the smart city solution includes: 2G/3G/4G, fixed and
NB-IoT accesses. True
4. Smart streetlamp services do not include charging piles. False
5. Smart manhole cover solution can provide real-time monitoring. True
6. Security management is a common problem in campus management. True
7. Power consumption management is not covered in the smart campus solution.
False
8. In the campus solution, facial recognition can be used to manage visitors. True
9. NB-IoT is a common technology used to manage security in the smart campus
solution. False
10. AMI stands for Advanced Metering Interface. False
11. Randomness is a character in the desired AMI solution. False
12. V2X includes V2N, V2I, V2P, and V2V. True
13. DRIS consists of V2X server and V2X edge. True
14. DRIS and HUD can be integrated in an IoV solution. True
15. DRIS stands for Driver Road Infrastructure Service. False
16. It is not necessary in an ICT-based production system of smart manufacturing to
include intelligent sensing technologies. False
17. In 5IABCDE, E stands for Encryption. False
18. 5IABCDE includes five emerging technologies. False
19. Block chain is included in 5IABCDE. True
20. AIoT stands for Advanced Internet of Things. False
HCIA-IoT V2.5 2 CC BY 4.0
1. The Tesla incident is classified as a DDoS attack. False
2. In the Tesla incident, the network layer of the IoT architecture was attacked. False
3. DDoS stands for Distributed Denial of Service. True
4. Data interception and tampering is not considered as a security threat. False
5. API attacks are categorized as a pipe threat. False
6. Pipe detection, cloud-cloud synergy and trusted device authentication are
effective means to resolve security threats. True
7. Huawei IoT security system provides security to data, access and devices. True
8. In the Huawei IoT security system, digital signature process includes the use of
RSA2048 or SHA256. False
9. In the Huawei IoT security system, the use of digital signature includes
generation of public and private keys. True
10. In the Huawei IoT security system, the signature verification is provided by the
terminal device. False
11. During the last two decades, the attackers' capability level has increased. True
12. Password guessing is an example of IoT attacks. False
13. DoS, phishing and encryption are examples of network attacks. False
14. In recent days, requirements on attackers' capabilities are low. True
15. As requirements on attackers' capabilities are decreasing, attackers' capability
level is decreasing as well. False
16. AI-based attacks and ransomware viruses are examples of attack tools developed
in the 2010s. True
17. 3T+1M means 3 security tires and 1 management layer. False
18. Anti-DDoS and signaling storms are part of the pipe security. True
19. A priority-based system is an anti-DDoS tool. True
20. The two-factor authentication can include: certificate and password. True
HCIA-IoT V2.5 3 CC BY 4.0
1. Ethernet uses CSMA/CA to detect collisions. False
2. FE stands for Fast Ethernet. True
3. Micro-B is a USB port Type. True
4. USB 4.0 bit rate can go up to 40 Gbit/s. True
5. In M-Bus technology, the power supply capability of the bus is 10 A. False
6. Bluetooth includes three types: BR/EDR, BLE and BLF. False
7. Wi-Fi can use 2.4 GHz UHF or 5 GHz SHF ISM radio frequency bands. True
8. GPRS bit rate is 9.6 kbps. False
9. UMTS is categorized as 2.5G. False
10. IMT-Advanced is the official name of 4G. True
11. LTE UE category 1 supports a downlink bit rate of up to 10 Mbit/s. True
12. 5G application scenarios are eMBB, mMTC and URLLC. True
13. Commercial use of the 5G started in 2020. False
14. NB-IoT is categorized as LPWA communication technology. True
15. SigFox bit rate is 1000 bit/s. False
16. 3G, 4G and 5G are considered high-rate and long-range technologies. False
17. Smart meter reading scenarios can use small-packet and ultra-long-range
technology such as 3G. False
18. Wi-Fi and Bluetooth are considered high-rate and short-range technologies. True
19. NB-IoT and LoRa are low-speed connection technologies. True
20. Z-Wave coverage can extend to 1 km. False
HCIA-IoT V2.5 4 CC BY 4.0
1. NB-IoT and NR can coexist.
True
2. The industry recognizes NB-IoT evolution and agrees to incorporate it into the
overall 5G plan. True
3. NB-IoT bandwidth is 200 kHz. False
4. NB-IoT downlink has 12 subcarriers each is 15kHz. True
5. OFDMA is an evolution of OFDM that combines it with FDMA. True
6. NB-IoT technology supports massive connections but it consumes remarkable
amount of energy. False
7. PSM stands for Power Sleeping Mode. False
8. In NB-IoT technology, PSM consumes the most amount of energy. False
9. NB-IoT uses retransmission over the air interface and ultra-narrow bandwidth to
provide an extra gain of over 20 dB compared with GSM. True
10. NB-IoT is based on cellular networks and coexists with other networks of this
type. True
11. NB-IoT standalone deployment is only based on LTE. False
12. NB-IoT supports three deployment modes. True
13. NB-IoT on the Boudica 150 chip supports full duplex channel. False
14. DRX period can be 1.28, 2.56, 5.12 or 10.24s, and it is determined by the
operator's network. True
15. The maximum eDRX period is 2.92 hours. True
16. An IoT device can be in the dormant state for up to 99% of the total time. True
17. PSM maximum period is 200 hours. False
18. Because NB-IoT uses repeated transmission, the downlink gain increased by
12 dB and the uplink gain increased by 9 dB. False
19. NB-IoT is a wide coverage technology. True
20. NB-IoT is not an example of LPWA communication technologies. False
HCIA-IoT V2.5 5 CC BY 4.0
1. NR stands for New Reality. False
2. Massive MIMO supports 64 transceiver antennas and 64 for receivers. True
3. Release 15 is the first 3GGP standard dedicated for 5G. True
4. In 5G, E2E latency is 10 ms. False
5. Compared to the 4G technology, latency in 5G is 30 to 50 times less. True
6. The throughput of 5G can go up to 10 Mbps. False
7. Compared to the 4G technology, throughput in 5G is 100 times higher. True
8. 5G can support a number of connections per km2 up to 1 million. True
9. Compared to the 4G technology, 5G supports 1000 times the number of
connections. False
10. 4G and 5G supports slicing. False
11. IMT-Advanced is another name for 5G. False
12. SDN stands for Software-Driven Networking. False
13. NSA can coexist with SA. True
14. eNB stands for evolved NodeB. True
15. 5G New Radio can be full duplex or half duplex. False
16. 5G New Radio supports Massive MIMO. True
17. Sub-3 GHz means lower than 3000 MHz and C-band covers 3000 - 6000 MHz.
True
18. 5G New Radio extends to the visible light band. False
19. In 5G, URLLC scenarios need to provide ultra-high reliability and ultra-low
latency services. True
20. VR, AR and MR are examples of eMBB scenarios. True
HCIA-IoT V2.5 6 CC BY 4.0
1. True 2. False 3. False 4. True 5. True 6. False 7. False 8. False 9. True 10. False 11. False 12.
False 13. True 14. True 15. False 16. True 17. True 18. True 19. False 20. True
A. Mark the following True or False?
1. Industrial-grade design requirements include the need of the gateway to be
dustproof and waterproof. True
2. Enterprise routers temperature range is -40°C to +70°C. False
3. Industrial IoT gateway sets in-between the network and the cloud. False
4. Industrial IoT gateway includes extensive interfaces and protocols. True
5. Industrial IoT gateway uses edge computing to reduce latency. True
6. Edge computing reference architecture covers 4 domains: application, data,
cloud and device. False
7. The reliability of the star topology is high. False
8. Huawei RF networking technology is based on the bus topology. False
9. Bus topology is simple and easy to expand. True
10. Ring topology is easy to expand. False
11. The topology of the future home network will be star. False
12. A smart home network runs over a baseband connection. False
13. AP stands for Access Point. True
14. Huawei HiLink allows two connection modes: direct hardware and cloud-based.
True
15. STB stands for Set Tree Box. False
16. Smart home devices can use PLC. True
17. Security surveillance is one application of the smart home scenario. True
18. Huawei HiLink ecosystem connection includes modules, SDK and routers. True
19. HiLink SDK is used to connect the smart home application to the cloud. False
20. Wi-Fi, ZigBee, Z-Wave and Bluetooth are examples of wireless communication
technologies supported by the smart home gateway. True
HCIA-IoT V2.5 7 CC BY 4.0
1. An IoT platform requires device access decoupling, security and reliability. True
2. Decimal data are accepted format in Huawei cloud IoT platform. False
3. Huawei cloud IoT platform uses LwM2M and MQTT to access devices. True
4. Huawei cloud IoT platform is multi-network access, this means devices can
connect to the platform directly, through gateways or edge devices. False
5. Devices that use property protocols based on TCP/UDP can connect to the IoT
platform by using CIGs deployed on the cloud. True
6. HTTP is an asynchronous protocol. False
7. HTTP is a heavyweight protocol with many headers and rules, thus, it is not
suitable for restricted networks. True
8. CoAP is based on HTTP. True
9. CIG stands for Carrier Interworking Gateway. False
10. Device management includes device registration and activation. True
11. IoT platform has three ways to deliver commands: Immediate, delayed and
synchronic deliveries. False
12. In time-based triggers, actions can be set based on specific events. False
13. In the IoT platform, firmware and software upgrades for devices are achieved
through FOTA and SOTA respectively. True
14. In the IoT platform, hardware upgrade is called “Hardware-Over-The-Air”. False
15. Huawei cloud uses Identity and Access Management for application registration
authentication. True
16. Multi-temperature data management maximizes processing efficiency. True
17. Multi-temperature management classifies data into two levels: hot and cold. False
18. Huawei cloud IoT is access agnostic. True
19. The IoT platform has its own security strategies, it includs one for each of the
following: device, networking, service, access, data storage and access security.
True
20. The IoT platform cloud-based architecture is flexible but not scalable.False
HCIA-IoT V2.5 8 CC BY 4.0
1. Product development includes product management, model developing and
online debugging. True
2. The codec is also called “profile”. False
3. The profile describes what a device is, what it can do and how to control it. True
4. Only data that is matched with the product model is saved on the IoT platform.
True
5. The codec decodes binary data reported by application into JSON format that can
be read by the devices. False
6. NB-IoT devices have high requirements on power consumption, that is why their
application layer data uses JSON format. False
7. Graphical codec development is recommended. True
8. GET action is used to create a resource on the server. False
9. PUT action is used to update resources on the server. True
10. In an API message, path parameter includes the path part in the URL. True
11. In an API message, the body parameter is used after the question mark (?) in the
URL. False
12. Application access authentication is achieved by exchanging messages with the
platform's IAM. True
13. The status code in the response message of the querying device is 203. False
14. Creating a device requires registering it in the cloud first and then binding it. True
15. All developments on the device side can be achieved using MQTT and
CoAP/LwM2M. True
16. IoTDA stands for Internet of Things Data Analytics. False
17. Authentication for devices using LwM2M over CoAP is not possible. False
18. Authentication for devices is possible using Native MQTT or MQTTS. True
19. When deleting a device successfully, the returned code is 204. True
20. Querying device messages is achieved using the PUT method. False
HCIA-IoT V2.5 9 CC BY 4.0
1. OS is a computer program that manages hardware, software and firmware
resources. False
2. DOS and windows are examples of programming language handlers. False
3. Peripherals hardware includes external memory, input devices and output devices.
True
4. Internal memory includes RAM, REM and ROM. False
5. CPU stands for Central Programming Unit. False
6. Punched tapes are an example of the manual operation system. True
7. Multi-job batch processing OS developed to time-sharing OS. True
8. Time-sharing OS is an operating system that implements a specific function
within a defined time frame. False
9. In single-job batch processing OS programs are loaded into the memory and
executed individually. True
10. Network OS developed after distributed OS. False
11. IoT OS can operate in networks where the number of connections might grow up
to reach a limit of 10 billions. False
12. Open source Huawei LiteOS entered the IoT field in 2015. True
13. High requirements on performance and power consumption for videos are two
challenges facing the IoT OS. True
14. Smart terminals need to meet three standards: smart connections, smart
networking and smart management. True
15. Huawei LiteOS includes multiple kernels and one middleware. False
HCIA-IoT V2.5 10 CC BY 4.0
1. All programs process computer data through a simple set of instructions. True
2. To implement multiple functions, a register is used. False
3. MOV is a common ARM instruction, it is used to transfer data from memory to
register. False
4. There are two types of instruction sets in today’s typical architecture: RISC and
CISC. True
5. Standard MPUs have a system clock speed of 3 GHz. True
6. RAM stores data running in the program, it will disappear after the power goes
off. True
7. ROM data is lost after the power is off. False
8. An interface connects an internal device to an MCU. False
9. ADC stands for Analog-to-Digital Converter True
10. An interrupt is the process where the CPU stops to execute a new program. True
11. In terms of basic sensing functions, there are 5 types of sensing elements. False
12. RTD stands for Resistance Temperature Detector. True
13. A photoelectric sensor converts electrical signals into optical signals. False
14. Huawei LiteOS provides one single memory management algorithm: the static
memory allocation. False
15. An interrupt can be deleted. False
16. The message queue provides an asynchronous processing mechanism. True
17. An event is not associated with a task. True
18. A semaphore is used only to enable tasks to access system resources
synchronously. False
19. A mutex is a special binary queue. False
20. The system clock is also referred to as time scale or tick. True
HCIA-IoT V2.5 11 CC BY 4.0
1. AT commands are sent from DTE to DCE. True
2. After a TE sends an AT command to an MT, the MT sends backs the response.
True
3. AT commands stands for ATtraction commands. False
4. PUT command is a category of AT commands. False
5. Execution commands can be written with or without parameters. True
6. Set command is used to display valid parameter values set by other AT commands.
False
7. AT+<x>=P1 is the syntax of a read command. False
8. Execution command is used to instruct a module to execute a specific function.
True
9. AT+<x>=? is the syntax of a read command. False
10. AT+<x>=<…> is not a valid syntax of the AT commands.False
You might also like
- AAU5613 Product DescriptionDocument27 pagesAAU5613 Product DescriptionANA JOSEFINA SIMON FRANCIANo ratings yet
- 5G Model Tuning - ATOLLDocument66 pages5G Model Tuning - ATOLLfadil3m2422100% (8)
- Frederic Launay - NG-RAN and 5G-NR - 5G Radio Access Network and Radio Interface-Wiley-ISTE (2021)Document281 pagesFrederic Launay - NG-RAN and 5G-NR - 5G Radio Access Network and Radio Interface-Wiley-ISTE (2021)MAVR001No ratings yet
- A Seminar Report On 5GDocument17 pagesA Seminar Report On 5GSameer Tiwari100% (3)
- 5G Pci PlanningDocument11 pages5G Pci Planningabhaydeep bawaNo ratings yet
- Group5 NDP b4Document13 pagesGroup5 NDP b4Riya AgrawalNo ratings yet
- A Project Report On 5G Wireless TechnologyDocument20 pagesA Project Report On 5G Wireless TechnologySu Epimood100% (1)
- What You Need To Know About 5G: April 2020Document18 pagesWhat You Need To Know About 5G: April 2020sanket jainNo ratings yet
- Assignment 9Document3 pagesAssignment 9Ashish JainNo ratings yet
- Paving The Path To Narrowband 5G With Lte Internet of Things (Iot)Document16 pagesPaving The Path To Narrowband 5G With Lte Internet of Things (Iot)Matt ValroseNo ratings yet
- 5G Technology: Miteshree Rath, Chandani PatelDocument6 pages5G Technology: Miteshree Rath, Chandani PatelNeha LodheNo ratings yet
- Bpacket Routing and ForwardingDocument34 pagesBpacket Routing and ForwardingHAMDI GDHAMINo ratings yet
- Presented BY:-Jafar ShahDocument26 pagesPresented BY:-Jafar Shahyekoyesew100% (1)
- Upcoming 5-G Wireless Technology and Its Security ConceptDocument6 pagesUpcoming 5-G Wireless Technology and Its Security ConceptAngel ChiangNo ratings yet
- 5 Geneartion of Wireless Network: Keywords: Long Term Evolution, Nanocore, Flat IPDocument5 pages5 Geneartion of Wireless Network: Keywords: Long Term Evolution, Nanocore, Flat IPMunish KumarNo ratings yet
- IOT Wireless TechnologyDocument10 pagesIOT Wireless TechnologyAfridi NiloyNo ratings yet
- 5g Mobile Technology PPTDocument30 pages5g Mobile Technology PPTomprakkash1509100% (4)
- Key Concepts and Network Architecture For 5G Mobile TechnologyDocument6 pagesKey Concepts and Network Architecture For 5G Mobile Technologyrainbows7100% (1)
- IOT Wireless Technology - EditedDocument10 pagesIOT Wireless Technology - EditedMurgi kun :3No ratings yet
- Document1 Copy111Document15 pagesDocument1 Copy111Zahra JabarNo ratings yet
- Introduction of 5g Wireless SystemDocument4 pagesIntroduction of 5g Wireless SystemRam PadhiNo ratings yet
- 5 GDocument26 pages5 GRani ManugrahaniNo ratings yet
- Fettweis Boche ITSOC 2021 09 24Document10 pagesFettweis Boche ITSOC 2021 09 24josestalin120No ratings yet
- Yassein 2017Document5 pagesYassein 2017haval.alsofiNo ratings yet
- WPAn & WLAN (5G and G Family)Document43 pagesWPAn & WLAN (5G and G Family)Erman HamidNo ratings yet
- 5G Technology of Mobile CommunicationDocument5 pages5G Technology of Mobile CommunicationPorfirio DiazNo ratings yet
- Marchese 2019Document4 pagesMarchese 2019Eko PrayitnoNo ratings yet
- Basics of Iot Networking Common Iot Terms: Iot Architecture and Protocols Unit IiDocument13 pagesBasics of Iot Networking Common Iot Terms: Iot Architecture and Protocols Unit IiMaitrayee SuleNo ratings yet
- Internet of ThingsDocument8 pagesInternet of ThingsJeison PantojaNo ratings yet
- Broadband Cellular Network Technology: 4G Is The Fourth Generation ofDocument12 pagesBroadband Cellular Network Technology: 4G Is The Fourth Generation ofSONAKSHI HANDOONo ratings yet
- IoT - Solution R&SDocument12 pagesIoT - Solution R&SAlfred NgNo ratings yet
- 1.2 IOT DemystifyingDocument6 pages1.2 IOT DemystifyingmohitNo ratings yet
- 5G Networking TechnologyDocument2 pages5G Networking TechnologyS M Shamim শামীমNo ratings yet
- 5g Technology 018Document7 pages5g Technology 018ابتسام احمدNo ratings yet
- 5G Mobile Technology: Abstract-Existing Research Work in Mobile Communication Is Related To 5G Technology. in 5GDocument5 pages5G Mobile Technology: Abstract-Existing Research Work in Mobile Communication Is Related To 5G Technology. in 5GA RNo ratings yet
- TopicDocument28 pagesTopicrohitNo ratings yet
- Impactof Internetof Things Io Ton 5 GDocument13 pagesImpactof Internetof Things Io Ton 5 Gsabinaahmetaj815No ratings yet
- Simulasi 3 - FileDocument6 pagesSimulasi 3 - FileIcha IcaNo ratings yet
- Project ReportDocument16 pagesProject ReportVIKAS NIGAMNo ratings yet
- Impactof Internetof Things Io Ton 5 GDocument13 pagesImpactof Internetof Things Io Ton 5 Gnuredin abdellahNo ratings yet
- An Approach To Wireless Network 6G TechnologyDocument9 pagesAn Approach To Wireless Network 6G TechnologyIJRASETPublicationsNo ratings yet
- 5G Mobile Wireless TechnologyDocument8 pages5G Mobile Wireless TechnologymohanrajNo ratings yet
- 5G SeminarDocument21 pages5G SeminarSani SufiyanNo ratings yet
- 5G in The Internet of Things Era: An Overview On Security and Privacy ChallengesDocument7 pages5G in The Internet of Things Era: An Overview On Security and Privacy Challengesmohammed BiratuNo ratings yet
- A Future Communication Technology: 5G: 0G 1G 2G 3G 4G 5GDocument8 pagesA Future Communication Technology: 5G: 0G 1G 2G 3G 4G 5GMuhammad Arslan AshrafNo ratings yet
- What Is 5G Technology: 5G Technology Stands For 5th Generation Mobile Technology. 5G Mobile Technology HasDocument12 pagesWhat Is 5G Technology: 5G Technology Stands For 5th Generation Mobile Technology. 5G Mobile Technology HasJamil Ahmad SaadNo ratings yet
- 5GDocument31 pages5GRaj VermaNo ratings yet
- Report On 5G and Its Impact: Mobile and Wireless CommunicationDocument14 pagesReport On 5G and Its Impact: Mobile and Wireless CommunicationAhad AliNo ratings yet
- 5G and The Internet of ThingsDocument12 pages5G and The Internet of ThingsJudelmar SalvadorNo ratings yet
- 5G and 4GDocument8 pages5G and 4GAgustin AsencioNo ratings yet
- Role of 5G Networks: Issues, Challenges and Applications: Arun Kumar Tripathi, Akash Rajak, Ajay Kumar ShrivastavaDocument7 pagesRole of 5G Networks: Issues, Challenges and Applications: Arun Kumar Tripathi, Akash Rajak, Ajay Kumar ShrivastavaShreya ShettyNo ratings yet
- A Review On 5G Technology PDFDocument5 pagesA Review On 5G Technology PDFrmsaqib1No ratings yet
- Future of Internet of ThingsDocument6 pagesFuture of Internet of ThingsMulatu TadeleNo ratings yet
- Project On Wireless System: Presented byDocument22 pagesProject On Wireless System: Presented byConnect Net cafeNo ratings yet
- 5G Wireless Technology: Akshita Singhal Department of ECE Global College of TechnologyDocument3 pages5G Wireless Technology: Akshita Singhal Department of ECE Global College of TechnologychhabraashishNo ratings yet
- IOT-Module 3Document73 pagesIOT-Module 3M.A rajaNo ratings yet
- Introduction To 5GDocument61 pagesIntroduction To 5Grf channel100% (1)
- 5G Heterogenous NetworkDocument9 pages5G Heterogenous NetworkBhumika PiplaniNo ratings yet
- IotDocument9 pagesIotRavan bhoyeNo ratings yet
- 5G Technical ArticleDocument12 pages5G Technical ArticleDon Paton Roland KudoziaNo ratings yet
- A Literature Review of Security in 5G.Document9 pagesA Literature Review of Security in 5G.Merisha Subedi100% (1)
- 5g WorldDocument4 pages5g WorldSourav ChandraNo ratings yet
- An Insight To 4 Generation Wireless SystemDocument11 pagesAn Insight To 4 Generation Wireless Systemvenkat4uuuNo ratings yet
- Building the Internet of Things with IPv6 and MIPv6: The Evolving World of M2M CommunicationsFrom EverandBuilding the Internet of Things with IPv6 and MIPv6: The Evolving World of M2M CommunicationsNo ratings yet
- Module 9 Living in The IT EraDocument11 pagesModule 9 Living in The IT ErakvelezNo ratings yet
- Program (FINAL)Document5 pagesProgram (FINAL)dtvt40No ratings yet
- 5G Network Security Practices: An Overview and Best PracticesDocument5 pages5G Network Security Practices: An Overview and Best PracticesMauricio José Il-PanaderoNo ratings yet
- Mimo-Supporting Radio-Over-Fiber System and Its Application in Mmwave-Based Indoor 5G Mobile NetworkDocument11 pagesMimo-Supporting Radio-Over-Fiber System and Its Application in Mmwave-Based Indoor 5G Mobile NetworkDivanshu JainNo ratings yet
- Market Dynamics and Security Considerations of 5G: Anand R. Prasad, Sivakamy Lakshminarayanan and Sivabalan ArumugamDocument26 pagesMarket Dynamics and Security Considerations of 5G: Anand R. Prasad, Sivakamy Lakshminarayanan and Sivabalan Arumugammohd nazir shakeelNo ratings yet
- 6G Internet of Things A Comprehensive SurveyDocument25 pages6G Internet of Things A Comprehensive Survey2106224No ratings yet
- Release Notes: Analyzer Update July 2020Document19 pagesRelease Notes: Analyzer Update July 2020jedossousNo ratings yet
- Spectrum-NET Overview Oct 2 No NDADocument12 pagesSpectrum-NET Overview Oct 2 No NDAuxun100% (1)
- Generations of Mobile TechDocument12 pagesGenerations of Mobile Techseema fatimaNo ratings yet
- Openran and 5G: John Baker SVP, Business Development April 2020Document20 pagesOpenran and 5G: John Baker SVP, Business Development April 2020Nicholas Wilson100% (1)
- Why The EU Is Betting Big On 5G?Document36 pagesWhy The EU Is Betting Big On 5G?BackrusNo ratings yet
- Wireless Communications For Internet of Farming An Early 5G Measurement StudyDocument15 pagesWireless Communications For Internet of Farming An Early 5G Measurement Studyraul.aenaNo ratings yet
- 5G Trainin - ORAN CUSDocument4 pages5G Trainin - ORAN CUSNISHANT BANSALNo ratings yet
- Maxis IAR 2020 - Part 2Document218 pagesMaxis IAR 2020 - Part 2Princess Princess OutletNo ratings yet
- Filtered-OFDM - Enabler For Flexible Waveform in The 5th Generation Cellular NetworksDocument6 pagesFiltered-OFDM - Enabler For Flexible Waveform in The 5th Generation Cellular NetworksMichael Derrick OdhiamboNo ratings yet
- ZTE Ultra-High-Precision Time Synchronization Network Provides Technical Support For 5G CommercializationDocument5 pagesZTE Ultra-High-Precision Time Synchronization Network Provides Technical Support For 5G CommercializationJose ValenzuelaNo ratings yet
- CV Europass 20181105 Mansoor enDocument3 pagesCV Europass 20181105 Mansoor enAbdulaziz alhaidariNo ratings yet
- Vehicle To Vehicle CommunicationsDocument4 pagesVehicle To Vehicle CommunicationsRudraksh HaranNo ratings yet
- Abstract On 5gDocument7 pagesAbstract On 5gGaurav Mishra100% (2)
- 3GPP TR 22.872Document82 pages3GPP TR 22.872bhushan7408No ratings yet
- Mobility Load Balancing (5G RAN6.1 - Draft A)Document132 pagesMobility Load Balancing (5G RAN6.1 - Draft A)VVLNo ratings yet
- The Design and Applications of High-Performance 2019Document18 pagesThe Design and Applications of High-Performance 2019Roro SalazarNo ratings yet
- New Microsoft Word DocumentDocument7 pagesNew Microsoft Word Documenta_44mNo ratings yet
- Evolution of Cellular NetworksDocument20 pagesEvolution of Cellular NetworksBhanu KunniNo ratings yet
- Research ArticleDocument20 pagesResearch ArticlesoritamonerNo ratings yet