Professional Documents
Culture Documents
Report Template
Report Template
Uploaded by
A NOriginal Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Report Template
Report Template
Uploaded by
A NCopyright:
Available Formats
< COMPANY NAME >
Penetration Test Report
Version 1.0
Author Your Name
Issue Date Report Submission Date
Table of Contents
1.0 <Company Name> Penetration Test Report 2
1.1 Introduction........................................................................................................................................................2
1.2 Scope..................................................................................................................................................................2
2.0 Executive Summary 3
2.1 - Recommendations..........................................................................................................................................3
3.0 Risk Assessment ………………………………………………………………………………………………… 4
3.1 - Likelihood......................................................................................................................................................4
3.2 - Impact.............................................................................................................................................................4
4.0 Findings Summary ……………………………………………………………………………………………………………………………. 5
5.0 Vulnerbility and Remedetion Report 6
6.0 Infromation gathering ………………………………………………………………………………………………………………………. 7
7.0 High Findings……………………………………………………………………………………………………………………………………. 8
7.1 - XXXXXX.......................................................................................................................................................8
8.0 Medium Findings…………………………………………………………………………………………………….………………………..38
8.1 - XXX XXX....................................................................................................................................................38
9.0 Low Findings…………………………………………………………………………………………………………………………………….45
9.1 - XXX XXXXX XXXX.................................................................................................................................45
Confidential Final Version 1|Page
1.0 <COMPANY NAME> Penetration Test Report
1.1 Introduction
Subject of this document is summary of penetration test performed against web applications owned by <Company
Name> company. Test was conducted according to rules of engagement defined and approved at the beginning by
both parties – customer and contractor. Black-box pentesting assignment was requested.
Black-box penetration test classification means that penetration tester has no internal knowledge about target system
architecture. He/she can use information commonly available on the Internet. More data can be collected during
reconnaissance phase based on observation of target system behavior. Black-box penetration test results gives
overview of vulnerabilities exploitable from outside the company network. It shows how unauthenticated actor can
take advantage of weaknesses existing in tested web application.
Time frame defined:
Penetration test start: XXXXX,
Penetration test end: XXXXXX.
1.2 Scope
To perform a Black Box Web Application Penetration Test against the web applications of the organization named
<Company Name>.
This is what the client organization defined as scope of the tests:
Dedicated Web Server: X.X.X.X
Domain: domain.com
Subdomains: all subdomains
2.0 – EXECUTIVE SUMMARY
Conducted penetration test uncovered several security weaknesses present in web applications owned by <Company
Name> company
Confidential Final Version 2|Page
When performing the penetration test, there were several alarming vulnerabilities that were identified on <Company
Name> networks. When performing the attacks, I was able to gain access to multiple XXXX, primarily due to
outdated patches and poor security configurations. During the testing, I had XXXXXX access to XXXX portal.
These systems as well as a brief description:
Subdomain Found: X
X High, X Med, X Low issue has been identified.
2.1 – Recommendations
I recommend patching the vulnerabilities identified during the testing to ensure that an attacker cannot exploit these
systems in the future. One thing to remember is that these systems require frequent patching and once patched,
should remain on a regular patch program to protect additional vulnerabilities that are discovered at a later date.
3.0 – RISK ASSESSMENT
3.1 Likelihood
Confidential Final Version 3|Page
The likelihood is a measurement of the capacity to carry out an attack. The factor will be the difficulty or skill
required to carry out the attach.
Risk Description
Critical An attacker is near-certain to carry out the threat event
High An untrained user could exploit the vulnerability. The vulnerability is obvious or easily
accessed
Medium The vulnerability required some hacking knowledge to carry out the attack
Low The vulnerability required significant time, skill , access and other resource to carry out the
attack
3.2 Impact
The impact is a measurement of the adverse effect carrying out an attack would have on the
organization.
Risk Description
Critical An attack would cause catastrophic or severe effect on operation, asset or other organization
High An attack would severely degrade mission capability. The attack may result in damage to
asset( data exposure)
Medium An attack would degrade the mission capability. An attack would allow for primary function to
application to resume, but at reduced effectiveness
Low An attack would degrade mission capability in a limited capacity. The attack may result in
marginal damage to assets
4.0 -- FINDINGS SUMMARY
Confidential Final Version 4|Page
Findings Likelihood Impact Rating Status
XXXXXXX Medium Critical High Open
XXXXXXXXXXXX Medium Critical High Open
XXXXXXXXXXX High High High Open
XXXXXXXXXX Medium Critical High Open
XXXXXXXXXX High High High Open
XX XXXXX XXX XXXXX Medium High High Open
XXX XXXXX XXX XXXXX Medium Medium Medium Open
XXX XXXXX XXX XXXXX Medium Medium Medium Open
XXX XXXXX XXX XXXXX High Medium Medium Open
XXX XXXXX Medium High High Open
XXX XXXXX Low Low Low Open
XXX XXXXX XXX XXXXX Low Low Low Open
XXX XXXXX XXX XXXXX Low Low Low Open
XXX XXXXX Low Low Low Open
XXX XXXXX Low Low Low Open
XXX XXXXX Low Low Low Open
Confidential Final Version 5|Page
5.0 – VULNERABILITY & REMEDATION REPORT
Penetration test finding classification, description and recommendations mentioned in the report are taken mostly
from OWASP TOP 10 project documentation available on site:
https://www.owasp.org/index.php/Category:OWASP_Top_Ten_Project.
The OWASPT TOP 10 is list of definitions of web application vulnerabilities they pose the most significant security
risks to organization when exploited.
Vulnerability Summary
< UPLOAD SOME CHARTS >
Confidential Final Version 6|Page
6.0 – INFROMATION GATHERING
The information gathering portion of a penetration test focuses on identifying the scope of the penetration test. I
started the pentest with finding all subdomains.
I have used multiple tools to make sure that I haven’t missed any domain.
Tools Used:
1) WFUZZ
2) Virustotal
3) Sublist3r
Above tools discovered multiple subdomains, the working one’s are below:
Confidential Final Version 7|Page
5.0 High Findings
5.1. Title: XXXXXX XXXXXXXXX
Rating: High
URL:
Description:
Proof of Concept:
Step 1
Step 2:
Step 3:
Remediation Steps:
Confidential Final Version 8|Page
6.0 Medium Findings
6.1. Title: XXXX XXXXXX
Rating: Medium
URL:
Description:
Proof of Concept:
Step 1:
Step 2:
Step 3:
Remediation Steps:
Confidential Final Version 9|Page
7.0 Low Findings
7.1. Title: XXXX XXXX XX
Rating: Low
URL:
Description :
Proof of Concept:
Step 1 :
Step 1 :
Step 1 :
Remediation Steps:
Confidential Final Version 10 |
Page
You might also like
- Metasploitable Pentest Report AssignmentDocument39 pagesMetasploitable Pentest Report Assignmentpatricktina06No ratings yet
- Penetration Testing Report PDFDocument19 pagesPenetration Testing Report PDFLikesh ShresthaNo ratings yet
- Offensive Security: Penetration Test Report For Internal Lab and ExamDocument14 pagesOffensive Security: Penetration Test Report For Internal Lab and ExamAshish Bhangale100% (1)
- Pentestreport RomioDocument72 pagesPentestreport Romioapi-508435779No ratings yet
- Kauda Game - A Case StudyDocument4 pagesKauda Game - A Case Studynavin9849No ratings yet
- Gameplay and Design PDFDocument349 pagesGameplay and Design PDFfuckyouNo ratings yet
- Offensive Security: Penetration Test Report For Internal Lab and ExamDocument13 pagesOffensive Security: Penetration Test Report For Internal Lab and Examscastell77No ratings yet
- Demo Pentest Report 1709741204Document19 pagesDemo Pentest Report 1709741204Baji ShaikNo ratings yet
- FINAL PENTESTING RevDocument24 pagesFINAL PENTESTING RevjoseNo ratings yet
- OSCP TemplateDocument7 pagesOSCP TemplateJunior Gabriel Cusi HuillcaNo ratings yet
- Sample ReportDocument11 pagesSample Reportqzombexzombe114No ratings yet
- Penetration Testing Report: DateDocument9 pagesPenetration Testing Report: DatetraeNo ratings yet
- Hands-On Investigation & Threat Hunting Workshop Guide V2 - October 2021 - W - o MachineDocument81 pagesHands-On Investigation & Threat Hunting Workshop Guide V2 - October 2021 - W - o MachineDC ExpertNo ratings yet
- The Assassin Squad Zbot and RYUK 1Document13 pagesThe Assassin Squad Zbot and RYUK 1Juana Ortega SantandeNo ratings yet
- Bug Bounty, How To StartDocument27 pagesBug Bounty, How To Startisha kudkarNo ratings yet
- IntruderReport - 06 Oct 2021Document15 pagesIntruderReport - 06 Oct 2021DigitalboxNo ratings yet
- IntruderReport - 04 Oct 2021Document13 pagesIntruderReport - 04 Oct 2021DigitalboxNo ratings yet
- Pentest Report: Tlp:WhiteDocument21 pagesPentest Report: Tlp:WhiteEsteban FigueroaNo ratings yet
- Week 2 Penetration Testing ReportDocument6 pagesWeek 2 Penetration Testing ReportJithukrishnan vNo ratings yet
- Cortex XDR Demo - Instructor GuideDocument34 pagesCortex XDR Demo - Instructor GuideAndrew RyanNo ratings yet
- Sample Web Application Security AssessmentDocument15 pagesSample Web Application Security AssessmentEsteban Francisco Sánchez MillaNo ratings yet
- Using ES 5.0 LabsDocument28 pagesUsing ES 5.0 LabsPanagiotis Poulopoulos50% (2)
- EXAMPLE-Penetration Testing Report v.1.0Document25 pagesEXAMPLE-Penetration Testing Report v.1.0Agrebi noor100% (1)
- Vulnerability Scan: Prepared byDocument14 pagesVulnerability Scan: Prepared byzitexitNo ratings yet
- Offensive Security: Penetration Test Report For Internal Lab and ExamDocument12 pagesOffensive Security: Penetration Test Report For Internal Lab and Examnobuyuki100% (1)
- Sample Penetration TestDocument35 pagesSample Penetration TestRohit KaundalNo ratings yet
- Operating System SecurityDocument20 pagesOperating System Securitynat-tamail.ruNo ratings yet
- GenerateDocument20 pagesGeneratebytesofusmanNo ratings yet
- Lab - Researching Network Attacks and Security Audit ToolsDocument4 pagesLab - Researching Network Attacks and Security Audit ToolsAlvaro Avila QuirosNo ratings yet
- XXX Report: Client Logo PlaceholderDocument37 pagesXXX Report: Client Logo PlaceholderMarioFernandoRentorNo ratings yet
- Pentest Report - Psiphon eDocument22 pagesPentest Report - Psiphon eAbumohammedNo ratings yet
- Anatomy of A Breach: How Hackers Break In-And How You Can Fight BackDocument21 pagesAnatomy of A Breach: How Hackers Break In-And How You Can Fight Backstyx.rootNo ratings yet
- Security Tools OverviewDocument12 pagesSecurity Tools Overviewinfo790100% (1)
- Public IncidentPlaybook MaliciousCodeDocument20 pagesPublic IncidentPlaybook MaliciousCodetramcar.forts-01No ratings yet
- PenTest XSSDocument53 pagesPenTest XSSЃорѓи Поп-ЃорѓиевNo ratings yet
- Lab 1 - Researching Network Attacks and Security Audit ToolsDocument5 pagesLab 1 - Researching Network Attacks and Security Audit ToolsJood salemNo ratings yet
- Va PT ReportDocument16 pagesVa PT ReportRobinNo ratings yet
- Metasploit Pro - The Attacker's Playbook: Test Your Defenses More Efficiently With Metasploit ProDocument2 pagesMetasploit Pro - The Attacker's Playbook: Test Your Defenses More Efficiently With Metasploit Promadhan rajNo ratings yet
- Satiexs Penetration Test Report TemplateDocument11 pagesSatiexs Penetration Test Report TemplateXavi FerNo ratings yet
- Risk ManagementDocument39 pagesRisk Managementmeetnetn0% (1)
- Executive Summary: Table of ContentsDocument7 pagesExecutive Summary: Table of Contentsharitripathi52552gmail.comNo ratings yet
- Carbon Black MRG Ransomware Report WMDocument31 pagesCarbon Black MRG Ransomware Report WMСамсон КукушкинNo ratings yet
- Malware Incident ResponseDocument6 pagesMalware Incident Responsectbaby1No ratings yet
- Cortex Hands On Investigation and Threat Hunting WorkshopDocument57 pagesCortex Hands On Investigation and Threat Hunting Workshopdbf75No ratings yet
- PWK Example Report v1Document14 pagesPWK Example Report v1Patrick Manzanza100% (1)
- Operation Wocao: Shining A Light On One of China's Hidden Hacking GroupsDocument41 pagesOperation Wocao: Shining A Light On One of China's Hidden Hacking GroupsSheloqNo ratings yet
- Web Pentest TestPHP - 2023-06-05-01 - 24 - 01Document7 pagesWeb Pentest TestPHP - 2023-06-05-01 - 24 - 01ignaNo ratings yet
- Researching Network Attacks and Security Audit ToolsDocument4 pagesResearching Network Attacks and Security Audit ToolsAxelle CarcacheNo ratings yet
- PEN-200 Lab ReportDocument8 pagesPEN-200 Lab ReportSilver UchihaNo ratings yet
- Offensive Security Certified Professional Exam ReportDocument11 pagesOffensive Security Certified Professional Exam ReportrberrospiNo ratings yet
- Interview Preparation Part-3Document17 pagesInterview Preparation Part-3Abdul Mateen Ukkund100% (1)
- Penetration Testing Report: Report Prepared For: Mr. John Smith Report Prepared By: Dean SheldonDocument33 pagesPenetration Testing Report: Report Prepared For: Mr. John Smith Report Prepared By: Dean Sheldonkashif majeed janjuaNo ratings yet
- Nexpose Sample Xss Report 5Document62 pagesNexpose Sample Xss Report 5Milin ShahNo ratings yet
- Netscout University - Lab - DoS Host Alerts p1Document4 pagesNetscout University - Lab - DoS Host Alerts p1Elaouni AbdessamadNo ratings yet
- ES Admin - v7.1 - Id0501 - LabGuideDocument35 pagesES Admin - v7.1 - Id0501 - LabGuideymendezpNo ratings yet
- Metasploit LabsDocument11 pagesMetasploit Labsshoki666No ratings yet
- Public IncidentPlaybook PhishingDocument18 pagesPublic IncidentPlaybook Phishingtramcar.forts-01No ratings yet
- Vulnerability Assessment and Attack Plan Report (Rohit Roy) PDFDocument31 pagesVulnerability Assessment and Attack Plan Report (Rohit Roy) PDFRohit RoyNo ratings yet
- Section 10 Understanding Common Endpoint AttacksDocument20 pagesSection 10 Understanding Common Endpoint AttacksritaNo ratings yet
- Threat Intel Roundup - 3 July - 10 JulyDocument13 pagesThreat Intel Roundup - 3 July - 10 JulyAmr M. AminNo ratings yet
- HITB Ezine Issue 002Document49 pagesHITB Ezine Issue 002njvhNo ratings yet
- Hacking Essentials - The Beginner's Guide To Ethical Hacking And Penetration TestingFrom EverandHacking Essentials - The Beginner's Guide To Ethical Hacking And Penetration TestingRating: 3 out of 5 stars3/5 (1)
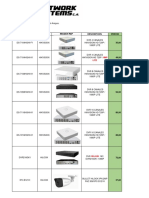
- Lista PreciosDocument2 pagesLista Preciospablotorres2403057No ratings yet
- My - Statement - 19 Jun, 2023 - 27 Jun, 2023 - 8458872769Document24 pagesMy - Statement - 19 Jun, 2023 - 27 Jun, 2023 - 8458872769Shani VermaNo ratings yet
- FiCEB - Spreadsheet - V01Document49 pagesFiCEB - Spreadsheet - V01Valiente ImperatorNo ratings yet
- California EDD User Guide Full - WebDocument5 pagesCalifornia EDD User Guide Full - WebHolmes Michael WilliamsNo ratings yet
- Kurdistan Region-Iraq Catholic University of Erbil: Course DescriptionDocument9 pagesKurdistan Region-Iraq Catholic University of Erbil: Course DescriptionDr-Raghad Al-FahamNo ratings yet
- Cover LetterDocument2 pagesCover LetterRojim OtadoyNo ratings yet
- Sr. Engineer - Vendor Development Department - Coimbatore - Jayem Automotives (P) LTDDocument3 pagesSr. Engineer - Vendor Development Department - Coimbatore - Jayem Automotives (P) LTDRoshini SweatNo ratings yet
- BreezeCONFIG Users Manual v5.1.17Document31 pagesBreezeCONFIG Users Manual v5.1.17Jose FerreiraNo ratings yet
- Sound System Reference Sound-PhilipsDocument69 pagesSound System Reference Sound-Philipsland_forecastNo ratings yet
- Effective Selling TechniquesDocument48 pagesEffective Selling TechniquesVikram Deshmukh100% (1)
- M.E. CseDocument69 pagesM.E. CseVijay RaghavanNo ratings yet
- Cyber Security - Lecture 11Document52 pagesCyber Security - Lecture 11Alan Jacob100% (3)
- José Miguel Moreno - La Guitarra Española (1536-1836) (CD) at DiscogsDocument2 pagesJosé Miguel Moreno - La Guitarra Española (1536-1836) (CD) at DiscogsPablo ArroyoNo ratings yet
- Foreign Object Debris Detection - Xsight SystemsDocument4 pagesForeign Object Debris Detection - Xsight SystemsIsrael ExporterNo ratings yet
- 8088/8086 MICROPROCESSOR Programming - Integer Instructions and ComputationsDocument11 pages8088/8086 MICROPROCESSOR Programming - Integer Instructions and Computationssai420No ratings yet
- HW4 OsDocument5 pagesHW4 OsDuy AnhNo ratings yet
- Grandstream-GXP2160 Phone SetupGuideDocument11 pagesGrandstream-GXP2160 Phone SetupGuideMario CuautleNo ratings yet
- Beginners Python Cheat Sheet PCC Functions PDFDocument2 pagesBeginners Python Cheat Sheet PCC Functions PDFbooklover2No ratings yet
- Cghs Form NewDocument3 pagesCghs Form Newmohankseb0% (1)
- Teacher Competencies For The Use of Information Communication TechnologyDocument18 pagesTeacher Competencies For The Use of Information Communication TechnologySheraldene Chavez EleccionNo ratings yet
- High Current Switching Regulators: DescriptionDocument22 pagesHigh Current Switching Regulators: DescriptionClaudio MartinsNo ratings yet
- Bingo - Marketing EnvironmentDocument4 pagesBingo - Marketing EnvironmentFahad MushtaqNo ratings yet
- TECNICO CCTV HIKVISION 27072022 DnetDocument5 pagesTECNICO CCTV HIKVISION 27072022 Dnetvictor molinaNo ratings yet
- Javacard Tutorial 2011 PDFDocument116 pagesJavacard Tutorial 2011 PDFJohn Moore50% (2)
- Machine (RAM), Instructions Are Executed One After Another (The CentralDocument3 pagesMachine (RAM), Instructions Are Executed One After Another (The CentralsankarwinningNo ratings yet
- Specification FOR Approval: Title 11.6" FHD TFT LCDDocument30 pagesSpecification FOR Approval: Title 11.6" FHD TFT LCDAranaya WayaNo ratings yet
- Java HashMap, LinkedHashMap and TreeMap - W3resourceDocument6 pagesJava HashMap, LinkedHashMap and TreeMap - W3resourcePradeep Kumar SNo ratings yet
- Information Systems in Global Business Today: © 2007 by Prentice HallDocument15 pagesInformation Systems in Global Business Today: © 2007 by Prentice HallpreetimgmNo ratings yet