Professional Documents
Culture Documents
SSP Template
SSP Template
Uploaded by
SumitOriginal Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
SSP Template
SSP Template
Uploaded by
SumitCopyright:
Available Formats
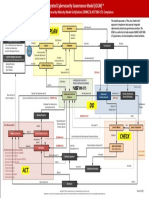
Implementing the NIST Risk Management Framework
with Ronald Woerner
Sample Information System Security Plan Template
The following NIST System Security Plan template has been provided as one example. Organizations may
use other formats and choose to update those to reflect any existing omissions based on this guidance. This
is not a mandatory format; it is recognized that numerous organizations and information security service
providers may have developed and implemented various approaches for information system security plan
development and presentation to suit their own needs for flexibility.
References
• NIST SP 800-18 Revision 1, Guide for Developing Security Plans for Federal Information Systems,
February 2006: https://csrc.nist.gov/publications/detail/sp/800-18/rev-1/final
• FedRAMP Templates: https://www.fedramp.gov/templates/
• FedRAMP System Security Plan (SSP) Moderate Baseline Template
• FedRAMP System Security Plan (SSP) Moderate Baseline Template, and FedRAMP Integrated
Inventory Workbook Template, Attachment 13
Implementing the NIST Risk Management Framework with Ronald Woerner 1 of 13
Implementing the NIST Risk Management Framework
with Ronald Woerner
Information System Security Plan Template
1. Information System Name/Title
Unique identifier and name given to the system
2. Information System Owner
Name, title, agency, address, email address, and phone number of the person who owns the system
3. Authorizing Official
Name, title, agency, address, email address, and phone number of the senior management official
designated as the authorizing official
4. Assignment of Security Responsibility
Name, title, address, email address, and phone number of the person who is responsible for the
security of the system
5. Information System Operational Status
Indicate the operational status of the system. If more than one status is selected, list which part of
the system is covered under each status.
Operational Under Major
Development Modification
6. Information System Type
Indicate if the system is a major application or a general support system. If the system contains minor
applications, list them in section 9, General System Description/Purpose.
Major General Support
Application System
7. General System Description/Purpose
Describe the function or purpose of the system and the information processes.
Implementing the NIST Risk Management Framework with Ronald Woerner 2 of 13
Implementing the NIST Risk Management Framework
with Ronald Woerner
8. System Environment
Provide a general description of the technical system. Include the primary hardware, software, and
communications equipment.
9. Inventory Workbook
Complete the applicable fields in the Integrated Inventory Workbook. A good example is found in
SSP ATTACHMENT 13: FedRAMP Integrated Inventory Workbook Template.
10. System Boundaries and Interconnections
Provide an explicit definition of the system’s network or computing system boundary. Include a
network diagram that portrays any boundaries and all its connections and components, including
the means for monitoring and controlling communications at the external boundary and at key
internal boundaries within the system. Address all components and managed interfaces of the
information system authorized for operation (for example, routers, firewalls).
Implementing the NIST Risk Management Framework with Ronald Woerner 3 of 13
Implementing the NIST Risk Management Framework
with Ronald Woerner
11. Information Types
This section describes how the information types used by the information system are
categorized for confidentiality, integrity, and availability sensitivity levels. The following tables
identify the information types that are input, stored, processed, and/or output from the target
information system.
Information Type (Use only
NIST 800-60 Identifier
information types from NIST
for Associated Confidentiality Integrity Availability
SP 800-60, Volumes I and II,
Information Type
as amended)
Choose level. Choose level. Choose level.
Low (L)
Moderate
High (H) (M) Low (L)
Moderate
High (H) (M) Low (L)
Moderate
High (H) (M)
Choose level. Choose level. Choose level.
Low (L)
Moderate
High (H) (M) Low (L)
Moderate
High (H) (M) Low (L)
Moderate
High (H) (M)
Choose level. Choose level. Choose level.
Low (L)
Moderate
High (H) (M) Low (L)
Moderate
High (H) (M) Low (L)
Moderate
High (H) (M)
12. Overall Information System Categorization
Based on the information provided above, identify the overall information system sensitivity
categorization (also known as the FIPS 199 categorization).
Low Moderate High
13. Related Laws, Regulations, and Policies
List any laws or regulations that establish specific requirements for the confidentiality, integrity,
or availability of the data in the system.
Implementing the NIST Risk Management Framework with Ronald Woerner 4 of 13
Implementing the NIST Risk Management Framework
with Ronald Woerner
14. Minimum Security Control Documentation
Based on the completed information, select the appropriate minimum security control baseline
(low-, moderate-, high-impact) from NIST SP 800-53 latest revision.
Low Moderate High
For each minimum security control in the applicable baseline, provide a thorough description of how
that control is implemented or planned to be implemented. See NIST SP 800-53 Revision 4 Table D-2
for a listing of the different requirements for each initial control baseline.
The description should contain:
1. The security control title
2. How the security control is being implemented or planned to be implemented
3. Any scoping guidance that has been applied and what type of consideration
4. Indicate if the security control is a common control and who is responsible for
its implementation
For this exercise, you should pick three control categories and complete the required information
for each. See Attachment A for a sample. It is outside the scope of this document to include each
baseline control.
15. Information System Security Plan Completion Date: _________________________________
Enter the completion date of the plan
16. Information System Security Plan Approval Date: _________________________________
Enter the date the system security plan was approved and indicate if the approval documentation is
attached or on file.
Implementing the NIST Risk Management Framework with Ronald Woerner 5 of 13
Implementing the NIST Risk Management Framework
with Ronald Woerner
Attachment A: Sample Security Control Documentation
Awareness and Training (AT)
Table 39. AT-1: Security Awareness and Training Policy and Procedures
AT-1: Security Awareness and Training Policy and Procedures
Control
The organization develops, documents, and disseminates to applicable personnel, and reviews and updates (as
necessary), within every three hundred sixty-five (365) days:
a. A security and privacy awareness and training policy that addresses purpose, scope, roles,
responsibilities, management commitment, coordination among organizational entities,
and compliance;
a. Procedures to facilitate the implementation of the security and privacy awareness and training
policy and associated security and privacy awareness and training controls;
b. Security and privacy awareness and training policy; and
c. Security and privacy awareness and training procedures.
d. Security and privacy awareness and training plan.
Implementation Standards
1. An initial Security and Privacy awareness and training plan is developed and implemented that addresses
all requirements of the security and privacy training program. This plan should cover required policies
and procedures and a documented process for implementing basic privacy and awareness training for all
organizational users and contractors that includes understanding potential indicators of insider threats.
This plan should also include requirements for ensuring personnel with specific roles and responsibilities in
information security and privacy undergo more detailed and audience specific security and privacy training.
Guidance
This control addresses the establishment of policy and procedures for the effective implementation of security and
privacy controls and control enhancements in the AT family. Policy and procedures reflect applicable state and federal
laws, directives, regulations, policies, standards, and guidance. Security and privacy program policies and procedures
at the organization level may make the need for system-specific policies and procedures unnecessary. The policy
can be included as part of the general information security and privacy policy for organizations or, conversely, can
be represented by multiple policies reflecting the complex nature of certain organizations. The procedures can be
established for the security and privacy programs in general and for particular information systems, if needed. The
organizational risk management strategy is a key factor in establishing policy and procedures.
Implementing the NIST Risk Management Framework with Ronald Woerner 6 of 13
Implementing the NIST Risk Management Framework
with Ronald Woerner
AT-1: Security Awareness and Training Policy and Procedures
Related Control Requirement(s): PM-9
Control Implementation Description:
** Note: The Security and Privacy Awareness and Training Plan is a required artifact.
Responsibility: Agency Human Resources
Control Status: Implemented
The Agency ratified IT Security Policies and Standards with an effective implementation date of 01 December 2018.
Procedures are maintained by the respective maintenance units. The Agency adheres to the Organization IT Security
Policies and standards. Agency policies, standards and procedures are written to complement state policy.
The Agency ISO is responsible for security policy implementation and oversight. Agency Management is responsible for
annual review and approval of any updates to Policies and Standards.
Agency IT Security Policies and Standards were updated, approved and published in June 2018. This is a common control
for all systems.
The IT Security and Privacy Education and Awareness Training Standard is in effect for this control family.
HR workplace policy controls require all new employees who have access to the Agency network must complete IT
Security Awareness training. Security Awareness Training and HIPAA privacy security training are tracked as part of the
Supervisors New Employee Work Area Orientation Checklist. The Checklist is provided to the Supervisor by HR for the
purpose of tracking that all new hires are aware of their responsibilities. The checklist and all items on the checklist must
be completed and returned to HR within 30 days of the worker’s hiring date. All training is provided online; workers are
required to use an electronic signature to acknowledge they have completed the required training. Each January, the ISO
preforms a Timely Training Audit reviewing training records against a new hires list provided by HR to ensure staff has
completed all required training.
Training Policies, Procedures, and course content are reviewed and updated at minimum annually by the ISO, Agency
Management Team, and Agency business areas responsible for recertification training for their workers.
Assessment Procedure:
Assessment Objective
Determine if the organization has implemented all elements of the AT-1 control as described in the control requirements.
Assessment Methods and Objects
Examine: Security and privacy awareness and training policy and procedures; and other relevant documents
or records.
Interview: Organizational personnel with security and privacy awareness and training responsibilities; organizational
personnel with information security and privacy responsibilities.
Implementing the NIST Risk Management Framework with Ronald Woerner 7 of 13
Implementing the NIST Risk Management Framework
with Ronald Woerner
Table 40. AT-2: Security Awareness Training
AT-2: Security Awareness Training
Control
The organization provides basic security and privacy awareness training to information system users (including
managers, senior executives, and contractors):
a. As part of initial training for new users prior to accessing any system’s information;
b. When required by system changes, and within every three hundred sixty-five (365) days thereafter.
Implementation Standards
1. An information security and privacy education and awareness training program is developed and
implemented for all employees and individuals working on behalf of the organization and involved in
managing, using, and/or operating information systems.
1. Security and privacy awareness training is provided before granting access to systems and networks, and
within every three hundred sixty-five (365) days thereafter, to all employees and contractors to explain the
importance and responsibility in safeguarding Personally Identifiable Information (PII) and ensuring privacy,
as established in federal legislation and HHS Regulations and CMS and organization guidance.
Guidance
Organizations determine the appropriate content of security and privacy awareness training, and security and privacy
awareness techniques, based on the specific organizational requirements and the information systems to which
personnel have authorized access. The content includes a basic understanding of the need for information security and
user actions to maintain security and privacy, and to respond to suspected security and privacy incidents. The content
also addresses awareness of the need for operations security and privacy related to the organization’s information
security program. Security and privacy awareness techniques can include, for example, displaying posters, offering
supplies inscribed with security and privacy reminders, generating email advisories / notices from senior organizational
officials, displaying logon screen messages, and conducting information security and privacy awareness events.
Implementing the NIST Risk Management Framework with Ronald Woerner 8 of 13
Implementing the NIST Risk Management Framework
with Ronald Woerner
AT-2: Security Awareness Training
Related Control Requirement(s): AT-3, AT-4, PL-4, AR-5
Control Implementation Description:
Responsibility: Agency Information Security Office
Control Status: Implemented
Security Awareness Training and HIPAA privacy security training are mandatory for all new hires. All training is provided
online; workers are required to use an electronic signature to acknowledge they have completed the required training.
Each January, the ISO preforms a Timely Training Audit reviewing training records against a new hires list provided by HR
to ensure staff has completed all required training.
Training Policies, Procedures, and course content are reviewed and updated at minimum annually by the ISO, All workers
with access to confidential or restricted data are required to complete Certification training and re-certify annually
thereafter. This training is specific to the appropriate use and disclosure of confidential or restricted information.
Electronic signatures are captured to verify individual training and recertification has been completed. The ISO and HR
Managers are responsible for compliance with the AT control.
Assessment Procedure:
Assessment Objective
Determine if the organization has implemented all elements of the AT-2 control as described in the control requirements
and associated implementation standards.
Assessment Methods and Objects
Examine: Security and privacy awareness and training policy; procedures addressing security and privacy awareness
training implementation; appropriate codes of federal regulations; security and privacy awareness training curriculum;
security and privacy awareness training materials; security plan; training records; and other relevant documents
or records.
Interview: Organizational personnel with responsibilities for security and privacy awareness training; organizational
personnel comprising the general information system user community.
Test: Automated mechanisms managing security and privacy awareness training.
Implementing the NIST Risk Management Framework with Ronald Woerner 9 of 13
Implementing the NIST Risk Management Framework
with Ronald Woerner
Table 42. AT-3: Role-Based Security Training
AT-3: Role-Based Security Training
Control
The organization provides role-based security and privacy training to personnel with assigned security and privacy roles
and responsibilities:
c. Before authorizing access to the information system or performing assigned duties; and
d. When required by information system changes; and within every three hundred sixty-five (365)
days thereafter.
Implementation Standards
2. Require personnel with significant information security and privacy roles and responsibilities to undergo
appropriate information system security and privacy training prior to authorizing access to networks,
systems, and/or applications; when required by significant information system or system environment
changes; when an employee enters a new position that requires additional role-specific training; and for
refresher training within every three hundred sixty-five (365) days thereafter.
Guidance
Organizations determine the appropriate content of security and privacy training based on the assigned roles and
responsibilities of individuals and the specific security and privacy requirements of CMS and the information systems to
which personnel have authorized access. In addition, organizations provide enterprise architects, information system
developers, software developers, acquisition/procurement officials, information system managers, system/network
administrators, personnel conducting configuration management and auditing activities, personnel performing
independent verification and validation activities, security control assessors, and other personnel having access to
system-level software, adequate security- and privacy-related technical training specifically tailored for their assigned
duties. Comprehensive role-based training addresses management, operational, and technical roles and responsibilities
covering physical, personnel, and technical safeguards and countermeasures. Such training can include for example,
policies, procedures, tools, and artifacts for the organizational security roles defined. Organizations also provide the
training necessary for individuals to carry out their responsibilities related to operations and supply chain security within
the context of the organization’s information security programs. Role-based security and privacy training also applies to
contractors providing services to the organization.
Related Control Requirement(s): AT-2, AT-4, PL-4, PS-7, SA-3, AR-5
Implementing the NIST Risk Management Framework with Ronald Woerner 10 of 13
Implementing the NIST Risk Management Framework
with Ronald Woerner
AT-3: Role-Based Security Training
Control Implementation Description:
Responsibility: Agency Information Security Office
Control Status: Implemented
The ISO has oversight of this program and provides appropriate information to agency supervisors.
IT Security Awareness training is required for all agency staff upon initial hire and annually thereafter. Training is broken
down into four different roles based on staff functions:
- Agency Senior Leaders: Senior level Agency administrators, Division Chiefs/Deputy Chiefs, and Managers
- Agency Supervisory Staff – Those staff members who supervise the “line workers”
- Agency Staff – All other employees who do not fit into either of the above categories
- Agency IT Professionals – Those staff members responsible for the day-to-day operation of Agency IT resources.
All Agency workers with access to confidential or restricted data are required to complete certification training upon
initial hire and recertify annually thereafter.
Assessment Procedure:
Assessment Objective
Determine if the organization has implemented all elements of the AT-3 control as described in the control requirements
and associated implementation standards.
Assessment Methods and Objects
Examine: Security and privacy awareness and training policy; procedures addressing security and privacy training
implementation; codes of federal regulations; security and privacy training curriculum; security and privacy training
materials; security plan; training records; other relevant documents or records.
Interview: Organizational personnel with responsibilities for role-based, security- or privacy-related training; and
organizational personnel with assigned information system security or privacy roles and responsibilities.
Test: Automated mechanisms managing role-based security and privacy training.
Table 43. AT-4: Security Training Records
AT-4: Security Training Records
Control
The organization:
e. Documents and monitors individual information system security and privacy training activities including
basic security and privacy awareness training and specific information system security and privacy
training; and
f. Retains individual training records for a minimum of five (5) years.
Implementing the NIST Risk Management Framework with Ronald Woerner 11 of 13
Implementing the NIST Risk Management Framework
with Ronald Woerner
AT-4: Security Training Records
Guidance
Procedures and training implementation should:
3. Identify employees with significant information security and privacy responsibilities and provide role-specific
training as follows:
a. All users of the organization information systems must be exposed to security and privacy awareness
materials at least every 365 days. Users of the organization’s information systems include employees,
contractors, students, guest researchers, visitors, and others who may need access to the information
systems and applications.
b. Executives must receive training in information security and privacy basics and policy level training in
security and privacy planning and management.
c. Program and functional managers must receive training in information security and privacy basics;
management- and implementation-level training in security and privacy planning and system/application
security and privacy management; and management- and implementation-level training in system/
application life-cycle management, risk management, and contingency planning.
d. Chief Information Officers (CIO), information security and privacy program managers, auditors, and other
security-oriented personnel (e.g., system and network administrators, and system/application security
and privacy officers) must receive training in information security and privacy basics and broad training
in security and privacy planning, system and application security and privacy management, system/
application life-cycle management, risk management, and contingency planning.
e. Information technology (IT) function management and operations personnel must receive training in
information security and privacy basics; management- and implementation-level training in security
and privacy planning and system/application security and privacy management; and management- and
implementation-level training in system/application life-cycle management, risk management, and
contingency planning.
4. Provide the organization information systems security and privacy awareness material/exposure to all new
employees before allowing them access to the systems.
5. Provide information systems security and privacy refresher training for employees as frequently as determined
necessary, based on the sensitivity of the information that the employees use or process.
6. Provide training whenever there is a significant change in the information system environment or procedures or
when an employee enters a new position that requires additional role-specific training.
Documentation for specialized training may be maintained by individual supervisors at the option of the organization.
Related Control Requirement(s): AT-2, AT-3, PM-14
Implementing the NIST Risk Management Framework with Ronald Woerner 12 of 13
Implementing the NIST Risk Management Framework
with Ronald Woerner
AT-4: Security Training Records
Control Implementation Description:
Responsibility: Agency Information Security Office
Control Status: Implemented
All training is provided online via the Agency web portal.
Upon completion of training, workers are required to read an acknowledgement statement then make the appropriate
selection to provide an electronic signature to register the completion of training, which is saved to a log file.
Supervisors have access to the training logs and can verify the training each worker has received to ensure new hires or
transferred workers have completed all required training.
The training log entries are archived.
Awareness and Training Family (AT) Security Controls Detail and Comment
Assessment Objective
Determine if the organization has implemented all elements of the AT-4 control as described in the control requirements.
Assessment Methods and Objects
Examine: Security and privacy awareness and training policy; procedures addressing security and privacy training
records; security and privacy awareness and training records; other relevant documents or records.
Interview: Organizational personnel with security and privacy training record retention responsibilities.
Test: Automated mechanisms supporting management of security and privacy training records.
Implementing the NIST Risk Management Framework with Ronald Woerner 13 of 13
You might also like
- HITRUST CSF Framework FAQ 9.6.0Document3 pagesHITRUST CSF Framework FAQ 9.6.0Elizabeth PatrickNo ratings yet
- Caterpillar 910 Wheel LoaderDocument4 pagesCaterpillar 910 Wheel LoaderAya Mariati100% (1)
- CIS RAM v2.1 Core Document Online.22.01Document27 pagesCIS RAM v2.1 Core Document Online.22.01Raman GautaNo ratings yet
- SOC 2 Audit Scoping Questionnaire 2021Document4 pagesSOC 2 Audit Scoping Questionnaire 2021RSA ArcherNo ratings yet
- AWS NIST 800 53 Security Controls MappingDocument3,308 pagesAWS NIST 800 53 Security Controls MappingManish AgarwalNo ratings yet
- NU - Urban Breach Handbook - TEBCDocument13 pagesNU - Urban Breach Handbook - TEBCiagaruNo ratings yet
- Giap Information Asset Register en v1.0Document26 pagesGiap Information Asset Register en v1.0sresearcher7100% (2)
- CISSP Whole Glossary2021Document64 pagesCISSP Whole Glossary2021babuNo ratings yet
- Csol 530 02 sp21Document16 pagesCsol 530 02 sp21api-593553237No ratings yet
- Policy Template Guide: NIST Cybersecurity FrameworkDocument17 pagesPolicy Template Guide: NIST Cybersecurity FrameworkHesham Elsayed100% (1)
- Cnssi 1253 PDFDocument96 pagesCnssi 1253 PDFAndrew ValenciaNo ratings yet
- Spotting The Adversary With Windows Event Log MonitoringDocument54 pagesSpotting The Adversary With Windows Event Log MonitoringnicolasvNo ratings yet
- FedRAMP Continuous Monitoring Strategy Guide v2.0Document14 pagesFedRAMP Continuous Monitoring Strategy Guide v2.0Nick ButtaNo ratings yet
- ComplianceForge Hierarchical Cybersecurity Governance FrameworkDocument1 pageComplianceForge Hierarchical Cybersecurity Governance FrameworkRajkumar RajamanikamNo ratings yet
- NIST 2 FrameworkDocument32 pagesNIST 2 Frameworkhamza056No ratings yet
- Dice Resume CV Lanre Akin HighlightedDocument3 pagesDice Resume CV Lanre Akin HighlightedkavinNo ratings yet
- Privileged Attack Vectors: Building Effective Cyber-Defense Strategies to Protect OrganizationsFrom EverandPrivileged Attack Vectors: Building Effective Cyber-Defense Strategies to Protect OrganizationsNo ratings yet
- 2021 04 27 Csiac Dod Cybersecurity Policy ChartDocument1 page2021 04 27 Csiac Dod Cybersecurity Policy Chartsrivatsan_ece0% (1)
- NIST RMF Roles and Responsibilities CrosswalkDocument30 pagesNIST RMF Roles and Responsibilities CrosswalkBe GanaNo ratings yet
- Microsoft SecurityDocument201 pagesMicrosoft SecurityShishir YadavNo ratings yet
- SEARCHITSecurity Assessment ToolDocument80 pagesSEARCHITSecurity Assessment Toolholamundo123No ratings yet
- Ciso Mindmap 2020 What Security Professionals Really Do?Document1 pageCiso Mindmap 2020 What Security Professionals Really Do?AJGMFAJ100% (1)
- Risk Assessment InstructionsDocument70 pagesRisk Assessment InstructionsFanny OjedaNo ratings yet
- Secure Configuration ManagementPolicy Template For CIS Control 4Document19 pagesSecure Configuration ManagementPolicy Template For CIS Control 4Ivan NinanNo ratings yet
- Framework For Reducing Cyber Risks To Critical InfrastructureDocument41 pagesFramework For Reducing Cyber Risks To Critical InfrastructureKalpana SupeNo ratings yet
- Implementing ISMS 9 Steps Aug 19Document12 pagesImplementing ISMS 9 Steps Aug 19Sudhanshu SinhaNo ratings yet
- Domain 1 CisaDocument93 pagesDomain 1 CisaRehanaNo ratings yet
- Recommended Security Baseline SettingsDocument28 pagesRecommended Security Baseline Settingsbalamurali_aNo ratings yet
- Identity and Access Management SuiteDocument2 pagesIdentity and Access Management SuiteVladan DabovicNo ratings yet
- SOW SecurityDocument3 pagesSOW SecurityJohn Croson100% (2)
- SCF Secure Controls Framework GuideDocument23 pagesSCF Secure Controls Framework GuideManinder KaurNo ratings yet
- FedRAMP Security Controls PrefaceDocument2 pagesFedRAMP Security Controls PrefaceFedScoopNo ratings yet
- Wiley Data and Cybersecurity Ebooks Title List 2022Document24 pagesWiley Data and Cybersecurity Ebooks Title List 2022Dr.BNo ratings yet
- BITS Vulnerability Management Maturity ModelDocument19 pagesBITS Vulnerability Management Maturity ModelJack JacksonNo ratings yet
- Cap CibDocument34 pagesCap CibCoffee GeeNo ratings yet
- Information Security RiskDocument29 pagesInformation Security RiskdddibalNo ratings yet
- Pentest QuestionareDocument7 pagesPentest QuestionareMaqsood Alam100% (1)
- Security Control Matrix - PDF MounikaDocument8 pagesSecurity Control Matrix - PDF MounikadhanishlNo ratings yet
- Database Security RoadmapDocument1 pageDatabase Security Roadmapwaz32195No ratings yet
- Microsoft BitLocker - An Insider's GuideDocument7 pagesMicrosoft BitLocker - An Insider's Guideapmihai100% (1)
- CC - Entry Level Ultimate - Guide DigitalDocument9 pagesCC - Entry Level Ultimate - Guide DigitalManish JoshiNo ratings yet
- Integrated Cybersecurity Governance Model - CMMC VersionDocument1 pageIntegrated Cybersecurity Governance Model - CMMC VersionwenapoNo ratings yet
- FITSI-DC - Continuous MonitoringDocument52 pagesFITSI-DC - Continuous MonitoringifofanahNo ratings yet
- QRadar SIEM Deployment GuideDocument52 pagesQRadar SIEM Deployment GuideblancorojoNo ratings yet
- Zero Trust Readiness Assessment: BenefitsDocument3 pagesZero Trust Readiness Assessment: BenefitsLuis Barreto100% (1)
- Saas Security ChecklistDocument3 pagesSaas Security ChecklistSanthanamariyan TNo ratings yet
- Zero Trust Security: A Cheat SheetDocument9 pagesZero Trust Security: A Cheat SheetMeghana MeghaNo ratings yet
- FedRAMP Baseline Security Controls v1.0Document24 pagesFedRAMP Baseline Security Controls v1.0FedScoop100% (1)
- Cloud Security Technical Reference ArchitectureDocument70 pagesCloud Security Technical Reference ArchitectureKishoreNo ratings yet
- Security FrameworksDocument11 pagesSecurity FrameworksJackNo ratings yet
- Frank Ayirebi ResumeDocument2 pagesFrank Ayirebi Resumedurga prasad ravvaNo ratings yet
- ComplianceForge Hierarchical Cybersecurity Governance FrameworkDocument5 pagesComplianceForge Hierarchical Cybersecurity Governance FrameworkKPNo ratings yet
- Building Correlation Searches With Splunk Enterprise Security TakeawayDocument4 pagesBuilding Correlation Searches With Splunk Enterprise Security Takeawayshahbaz ahmedNo ratings yet
- SCF Security & Privacy Capability Maturity Model OverviewDocument14 pagesSCF Security & Privacy Capability Maturity Model OverviewGerardo Castro100% (1)
- Asset Management (ID - AM) : The Data,: NIST Cybersecurity Framework Function Category QuestionsDocument14 pagesAsset Management (ID - AM) : The Data,: NIST Cybersecurity Framework Function Category QuestionsHala Elasri100% (3)
- CISSP Domain One: Security and Risk Management-What You Need To Know For The ExamDocument14 pagesCISSP Domain One: Security and Risk Management-What You Need To Know For The ExamLaptop salesNo ratings yet
- Information Technology Security Audit A Complete Guide - 2021 EditionFrom EverandInformation Technology Security Audit A Complete Guide - 2021 EditionNo ratings yet
- HIPAA Compliance ChecklistDocument13 pagesHIPAA Compliance ChecklistahmedNo ratings yet
- Security Architecture GuideDocument8 pagesSecurity Architecture GuidenicolepetrescuNo ratings yet
- CISM (Midterm)Document15 pagesCISM (Midterm)m_4_maina9376No ratings yet
- Combat Decision Making Process at The Tactical LevelDocument156 pagesCombat Decision Making Process at The Tactical LevelGreg Jackson100% (1)
- Revit-Structural Bim SpecialistDocument5 pagesRevit-Structural Bim SpecialistYoukhanna ZayiaNo ratings yet
- Servicemanual Panasonic kv-s2087 s1Document5 pagesServicemanual Panasonic kv-s2087 s1Ralf KöhlerNo ratings yet
- Example For Decision Making CriteriaDocument5 pagesExample For Decision Making CriteriaArly Kurt TorresNo ratings yet
- Infotech vs. COMELECDocument2 pagesInfotech vs. COMELECtheresaNo ratings yet
- Лаб №9Document21 pagesЛаб №9tbzlover0115No ratings yet
- Assignment AnsDocument6 pagesAssignment AnsVAIGESWARI A/P MANIAM STUDENTNo ratings yet
- Department of Information Technology: Question Bank TE IT AY-22-23 Sem VI Module 04: Clustering & Outlier AnalysisDocument4 pagesDepartment of Information Technology: Question Bank TE IT AY-22-23 Sem VI Module 04: Clustering & Outlier AnalysisAnurag SinghNo ratings yet
- Statistics in The Crem As of October 2020Document11 pagesStatistics in The Crem As of October 2020kamijou08No ratings yet
- Eco Tourism - Jafari Four PlatformsDocument4 pagesEco Tourism - Jafari Four PlatformsErnie Cinco Soria TestonNo ratings yet
- C4+ Maintenance ManualDocument28 pagesC4+ Maintenance Manualnorizam77100% (1)
- LASSOFF v. GOOGLE, INC. - Document No. 5Document2 pagesLASSOFF v. GOOGLE, INC. - Document No. 5Justia.comNo ratings yet
- Husqvarna TC 142T - 96051014600 (2016-08) Parts Diagram For CHASSIS - FRAMEDocument7 pagesHusqvarna TC 142T - 96051014600 (2016-08) Parts Diagram For CHASSIS - FRAMEmarcos garciaNo ratings yet
- Security Information and Event Management: Radboud University NijmegenDocument75 pagesSecurity Information and Event Management: Radboud University NijmegenproftechitspecialistNo ratings yet
- UK Wooden Pallet 1200 X 1000mmDocument1 pageUK Wooden Pallet 1200 X 1000mmRizwan rizviNo ratings yet
- Potent Drugs HandlingDocument4 pagesPotent Drugs HandlingOMKAR BHAVLENo ratings yet
- Lab Policies KOH Prep For Fungal Elements Affiliate Lab 8649 4Document3 pagesLab Policies KOH Prep For Fungal Elements Affiliate Lab 8649 4Geby JeonNo ratings yet
- 6 PDFDocument100 pages6 PDFKory JenoNo ratings yet
- Current Social Issues in The PhilippinesDocument1 pageCurrent Social Issues in The PhilippinesMr. FifthNo ratings yet
- College Athletes Protection and Compensation ActDocument50 pagesCollege Athletes Protection and Compensation ActCody Brunner100% (1)
- CCNPv6 SWITCH Lab1-1 Clearing Switches StudentDocument5 pagesCCNPv6 SWITCH Lab1-1 Clearing Switches StudentmmspeareNo ratings yet
- Classical Management TheoryDocument3 pagesClassical Management TheoryQuintine ZamoraNo ratings yet
- SNHU 107 Week 5 Final Project IDocument2 pagesSNHU 107 Week 5 Final Project Irachel.j.pinkardNo ratings yet
- CV Structural EngineerDocument5 pagesCV Structural EngineerMuhammad Ridha100% (1)
- Huawei V1 R3 Upgrade GuideDocument67 pagesHuawei V1 R3 Upgrade GuideMahmoud RiadNo ratings yet
- Online Library PowerPoint TemplatesDocument49 pagesOnline Library PowerPoint Templateskhozin albatawiNo ratings yet
- PIDTuningClassical - ControlsWikiDocument14 pagesPIDTuningClassical - ControlsWikiksameer_coepNo ratings yet
- Re - (Repeater-Builder) Midland Vehicular Repeater InfoDocument3 pagesRe - (Repeater-Builder) Midland Vehicular Repeater InfobbarinkNo ratings yet