Professional Documents
Culture Documents
Experts Warn of Dangers From Breach of Voter System Software
Experts Warn of Dangers From Breach of Voter System Software
Uploaded by
DvddOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Experts Warn of Dangers From Breach of Voter System Software
Experts Warn of Dangers From Breach of Voter System Software
Uploaded by
DvddCopyright:
Available Formats
Public Notice Quick Search
CITY, ZIP, ID NUMBER
Advanced Search
What is a public notice? Disclaimer
legal News + public Notices about Us +
Home Calendar Statistics Courts Classifieds Notices Columns Archives Contact Us
Posted August 31, 2021
Tweet This | Share on Facebook
Experts warn of dangers from breach of headlines Detroit
voter system software
Veterans Legal Clinic helps a family
avoid homelessness
Mediators offer perspectives on
Dominion software is used in some 30 states, probate and trust resolution
including Michigan 40 states settle Google location-
tracking charges for $392M
By Christina A. Cassidy
Daily Briefs
Associated Press
Upper ranks: New Macomb Bar
president takes volunteer service
ATLANTA (AP) — Republican efforts questioning the outcome of the 2020 to a higher level
presidential race have led to voting system breaches that election security
experts say pose a heightened risk to future elections. headlines National
Copies of the Dominion Voting Systems software used to manage elections — Feeling the holiday stress? The ABA
is offering a number of wellness
from designing ballots to configuring voting machines and tallying results —
events
were distributed at an event this month in South Dakota organized by MyPillow
ACLU and BigLaw firm use ‘Orange
CEO Mike Lindell, an ally of former President Donald Trump who has made is the New Black’ in hashtag effort
unsubstantiated claims about last year’s election. to promote NY jail reform
Ahead of the Curve: My Year on the
“It’s a game-changer in that the environment we have talked about existing now Legal Education Beat
8th Circ. Denies Municipality's
is a reality,” said Matt Masterson, a former top election security official in the
Class Action Against Netflix, Hulu
Trump administration. “We told election officials, essentially, that you should Under State Franchising Law
assume this information is already out there. Now we know it is, and we don’t Court allows Jan. 6 committee to
know what they are going to do with it.” obtain phone records of Arizona
GOP chair
The software copies came from voting equipment in Mesa County, Colorado, Thomas blasts 6th Circuit’s
handling of post-conviction claims
and Antrim County, Michigan, where Trump allies had sue unsuccessfully
challenging the results from last fall.
Search Wayne County
Delinquent Taxes subject to
The Dominion software is used in some 30 states, including counties in
Foreclosure in 2022
California, Georgia and Michigan.
Election security pioneer Harri Hursti was at the South Dakota event and said
he and other researchers in attendance were provided three separate copies of
election management systems that run on the Dominion software. The data
indicated they were from Antrim and Mesa counties. While it’s not clear how
the copies came to be released at the event, they were posted online and made
available for public download.
The release gives hackers a “practice environment” to probe for vulnerabilities
they could exploit and a road map to avoid defenses, Hursti said. All the hackers
would need is physical access to the systems because they are not supposed to
be connected to the internet.
“The door is now wide open,” Hursti said. “The only question is, how do you
sneak in the door?”
A Dominion representative declined comment, citing an investigation.
U.S. election technology is dominated by just three vendors comprising 90% of
the market, meaning election officials cannot easily swap out their existing
technology. Release of the software copies essentially provides a blueprint for
those trying to interfere with how elections are run. They could sabotage the
system, alter the ballot design or even try to change results, said election
technology expert Kevin Skoglund.
“This disclosure increases both the likelihood that something happens and the
impact of what would happen if it does,” he said.
The effort by Republicans to examine voting equipment began soon after the
November presidential election as Trump challenged the results and blamed his
loss on widespread fraud, even though there has been no evidence of it.
Judges appointed by both Democrats and Republicans, election officials of both
parties and Trump’s own attorney general have dismissed the claims. A
coalition of federal and state election officials called the 2020 election the “most
secure” in U.S. history, and post-election audits across the country found no
significant anomalies.
In Antrim County, a judge had allowed a forensic exam of voting equipment
after a brief mix-up of election results led to a suit alleging fraud. It was
dismissed in May. Hursti said the date on the software release matches the date
of the forensic exam.
Calls seeking information from Antrim County’s clerk and the local prosecutor’s
office were not immediately returned; a call to the judge’s office was referred to
the county clerk. The Michigan secretary of state’s office declined comment.
In Colorado, federal, state and local authorities are investigating whether Mesa
County elections staff might have provided unauthorized individuals access to
their systems. The county elections clerk, Tina Peters, appeared onstage with
Lindell in South Dakota and told the crowd her office was being targeted by
Democrats in the state.
Colorado Secretary of State Jena Griswold said she alerted federal election
security officials of the breach and was told it was not viewed as a “significant
heightening of the election risk landscape at this point.” This past week, Mesa
County commissioners voted to replace voting equipment that Griswold had
ordered could no longer be used.
Geoff Hale, who leads the election security effort at the U.S. Cybersecurity and
Infrastructure Security Agency, said his agency has always operated on the
assumption that system vulnerabilities are known by malicious actors.
Election officials are focused instead on ways they can reduce risk, such as
using ballots with a paper record that can be verified by the voter and rigorous
post-election audits, Hale said.
He said having Dominion’s software exposed publicly doesn’t change the
agency’s guidance.
Security researcher Jack Cable said he assumes U.S. adversaries already had
access to the software. He said he is more concerned the release would fan
distrust among the growing number of people not inclined to believe in the
security of U.S elections.
“It is a concern that people, in the pursuit of trying to show the system is
insecure, are actually making it more insecure,” said Cable, who recently joined
a cybersecurity firm run by former CISA Director Christopher Krebs and former
Facebook security chief Alex Stamos.
Concerns over access to voting machines and software first surfaced this year in
Arizona, where the Republican-controlled state Senate hired Cyber Ninjas, a
firm with no previous election experience, to audit the Maricopa County
election. The firm’s chief executive also had tweeted support of conspiracy
theories surrounding last year’s election.
After the county’s Dominion voting systems were turned over to the firm,
Arizona’s top election official said they could not be used again. The GOP-
controlled Maricopa County Board of Supervisors voted in July to replace them.
Dominion has filed suits contesting various unfounded claims about its systems.
In May, it called giving Cyber Ninjas access to its code “reckless,” given the
firm’s bias, and said it would cause “irreparable damage” to election security.
Election technology and security expert Ryan Macias, in Arizona earlier this
year to observe that review, was alarmed by a lack of cybersecurity protocols.
There was no information about who was given access, whether those people
had passed background checks or were asked to sign nondisclosure agreements.
Cyber Ninjas did not respond to an email with questions about the review and
their security protocols.
Macias was not surprised to hear that copies of Antrim County’s election
management system had surfaced online given the questionable motives of the
various groups conducting the reviews and the central role that voting systems
have played in conspiracy theories.
“This is what I anticipated would happen, and I anticipate it will happen yet
again coming out of Arizona,” Macias said. “These actors have no liability and
no rules of engagement.”
You are here: Home DETROIT > EXPERTS WARN OF DANGERS FROM BREACH OF VOTER SYSTEM SOFTWARE
Newspapers Legal News Contact Us
Detroit Advertise With Us Detroit Legal News
Flint-Genesee County Subscriptions 1409 Allen Rd, Suite B
Grand Rapids Forms Troy, Michigan 48083
Ingham County About Us
Jackson County Contact Us Phone: (248) 577-6100
Macomb Newstands Toll Free: (800) 875-5275
Muskegon (Norton- Public Notice Policies Fax: (248) 577-6111
Lakeshore)
Oakland County
Washtenaw County
PRIVACY POLICY | TERMS OF USE | FEEDBACK
You might also like
- Rigged: How the Media, Big Tech, and the Democrats Seized Our ElectionsFrom EverandRigged: How the Media, Big Tech, and the Democrats Seized Our ElectionsRating: 3.5 out of 5 stars3.5/5 (37)
- Experts' Letter To Lindsey Graham 20170113Document9 pagesExperts' Letter To Lindsey Graham 20170113MarilynMarks100% (1)
- US House Democrats Launch Investigation Into Arizona Senate Audit - Send Out Letter Demanding Answers From Cyber NinjasDocument13 pagesUS House Democrats Launch Investigation Into Arizona Senate Audit - Send Out Letter Demanding Answers From Cyber NinjasJim Hoft100% (2)
- The California Privacy Rights Act (CPRA) – An implementation and compliance guideFrom EverandThe California Privacy Rights Act (CPRA) – An implementation and compliance guideNo ratings yet
- IT468 Final PaperDocument16 pagesIT468 Final PaperRachel EspinozaNo ratings yet
- Dominion ReportDocument12 pagesDominion ReportRuss Taylor100% (1)
- Election Review - DLXXIXDocument4 pagesElection Review - DLXXIXAnonymous Qn8AvWvxNo ratings yet
- Voting Machine Firms Add Lobbyists Amid Election Hacker ConcernsDocument3 pagesVoting Machine Firms Add Lobbyists Amid Election Hacker Concernswise222No ratings yet
- Fox Dominion Lawsuit Exhibits 651-737 (Redacted)Document614 pagesFox Dominion Lawsuit Exhibits 651-737 (Redacted)Media Matters for AmericaNo ratings yet
- Election 2020 Setting The Record Straight - Dominion Voting SystemsDocument1 pageElection 2020 Setting The Record Straight - Dominion Voting SystemsMike Dee0% (1)
- Ramachandran Homeland Security Testimony - 01.20.22Document21 pagesRamachandran Homeland Security Testimony - 01.20.22The Brennan Center for JusticeNo ratings yet
- Indikasi Sangat Kuat Pencurangan Dalam Pemilu 2009Document22 pagesIndikasi Sangat Kuat Pencurangan Dalam Pemilu 2009Yusuf (Joe) Jussac, Jr. a.k.a unclejoeNo ratings yet
- 5-18-17 Georgia Voters' Press Release Regarding Voting SystemsDocument2 pages5-18-17 Georgia Voters' Press Release Regarding Voting SystemsCoalition for Good GovernanceNo ratings yet
- Michigan ComplaintDocument75 pagesMichigan ComplaintMike Burry100% (1)
- GOP Legal Attacks Create A Chilling Effect On Misinformation Research - The Washington PostDocument7 pagesGOP Legal Attacks Create A Chilling Effect On Misinformation Research - The Washington PostCeciliaNo ratings yet
- 03-15-08 OEN-'Voter Fraud' Phantom Returns To Haunt Policy MDocument3 pages03-15-08 OEN-'Voter Fraud' Phantom Returns To Haunt Policy MMark WelkieNo ratings yet
- 2021-07-26 Ramachandran - TestimonyDocument50 pages2021-07-26 Ramachandran - TestimonyThe Brennan Center for JusticeNo ratings yet
- Facial Recognition Database Used by FBI Is Out of Control, House Committee Hears - Technology - The GuardianDocument3 pagesFacial Recognition Database Used by FBI Is Out of Control, House Committee Hears - Technology - The GuardianpaulicalejerNo ratings yet
- Antrim Michigan Forensics Report, ASOG 13 Dec 2020Document23 pagesAntrim Michigan Forensics Report, ASOG 13 Dec 2020nolu chan100% (1)
- U.S. Election Integrity Plan Press Release, Sept. 21, 2021Document3 pagesU.S. Election Integrity Plan Press Release, Sept. 21, 2021GingerInk007No ratings yet
- The Problem of Algorithm Bias in AI & The Lack of Adequate RegulationDocument15 pagesThe Problem of Algorithm Bias in AI & The Lack of Adequate RegulationCGL Acting StudioNo ratings yet
- Election Review - DXXVIDocument7 pagesElection Review - DXXVIAnonymous Qn8AvWvxNo ratings yet
- Inside The Global Campaigns To Immunize Voters Against MisinformationDocument4 pagesInside The Global Campaigns To Immunize Voters Against MisinformationsheilumaNo ratings yet
- Complaint CJ Pearson v. Kemp 11.25.2020Document104 pagesComplaint CJ Pearson v. Kemp 11.25.2020PJ Media100% (14)
- Lindell FilingDocument82 pagesLindell FilingDaniel Chaitin94% (17)
- Complaint CJ Pearson v. Kemp 11.25.2020Document104 pagesComplaint CJ Pearson v. Kemp 11.25.2020BursebladesNo ratings yet
- 02-06-08 AlterNet-Super Tuesday's Voting Glitches by StevenDocument3 pages02-06-08 AlterNet-Super Tuesday's Voting Glitches by StevenMark WelkieNo ratings yet
- An Electoral System in CrisisDocument38 pagesAn Electoral System in CrisisAlexNo ratings yet
- Open Source, Open Democracy: Enhancing Transparency in US Voting Systems TechnologyDocument9 pagesOpen Source, Open Democracy: Enhancing Transparency in US Voting Systems TechnologyHoover InstitutionNo ratings yet
- Summary of The Return by Dick Morris:Trump's Big 2024 ComebackFrom EverandSummary of The Return by Dick Morris:Trump's Big 2024 ComebackNo ratings yet
- Silicon Valley Faces Regulatory Fight On Its Home TurfDocument5 pagesSilicon Valley Faces Regulatory Fight On Its Home TurfpippendanceNo ratings yet
- Election Review - MIDocument4 pagesElection Review - MIAnonymous Qn8AvWvxNo ratings yet
- Brennan Center Statement For The Fifth Bipartisan Senate Forum On Artificial IntelligenceDocument5 pagesBrennan Center Statement For The Fifth Bipartisan Senate Forum On Artificial IntelligenceThe Brennan Center for JusticeNo ratings yet
- Is The Telephone Company Violating Your Privacy-1Document13 pagesIs The Telephone Company Violating Your Privacy-1Sourav DashNo ratings yet
- IAPP US Federal Privacy WhitepaperDocument18 pagesIAPP US Federal Privacy WhitepaperTran Duc HungNo ratings yet
- Internet Voting:: Inevitable, Ineffectual or Both?Document27 pagesInternet Voting:: Inevitable, Ineffectual or Both?UgyenKpNo ratings yet
- Election Systems and Software ESS Corruption 07162019Document40 pagesElection Systems and Software ESS Corruption 07162019Glen YNo ratings yet
- Electronic Democracy: Using the Internet to Transform American PoliticsFrom EverandElectronic Democracy: Using the Internet to Transform American PoliticsNo ratings yet
- Selections in Minnesota: Consequences of the 2020 Election and How to Reclaim Control of Our GovernmentFrom EverandSelections in Minnesota: Consequences of the 2020 Election and How to Reclaim Control of Our GovernmentNo ratings yet
- Summary of Oath and Honor by Liz Cheney: A Memoir and a WarningFrom EverandSummary of Oath and Honor by Liz Cheney: A Memoir and a WarningRating: 4.5 out of 5 stars4.5/5 (3)
- The Democracy Index: Why Our Election System Is Failing and How to Fix ItFrom EverandThe Democracy Index: Why Our Election System Is Failing and How to Fix ItRating: 3 out of 5 stars3/5 (2)
- Electronic Electoral System: Simple, Abuse Free, Voter FriendlyFrom EverandElectronic Electoral System: Simple, Abuse Free, Voter FriendlyNo ratings yet
- The Grizzly Steppe Report (Unmasking the Russian Cyber Activity): Official Joint Analysis Report: Tools and Hacking Techniques Used to Interfere the U.S. ElectionsFrom EverandThe Grizzly Steppe Report (Unmasking the Russian Cyber Activity): Official Joint Analysis Report: Tools and Hacking Techniques Used to Interfere the U.S. ElectionsNo ratings yet
- Russian Cyber Activity – The Grizzly Steppe Report: Strategy and Hacking Techniques Used to Interfere the U.S. Elections and to exploit Government and Private SectorsFrom EverandRussian Cyber Activity – The Grizzly Steppe Report: Strategy and Hacking Techniques Used to Interfere the U.S. Elections and to exploit Government and Private SectorsNo ratings yet
- Russian Cyber Attack - Grizzly Steppe Report & The Rules of Cyber Warfare: Hacking Techniques Used to Interfere the U.S. Election and to Exploit Government & Private Sectors, Recommended Mitigation Strategies and International Cyber-Conflict LawFrom EverandRussian Cyber Attack - Grizzly Steppe Report & The Rules of Cyber Warfare: Hacking Techniques Used to Interfere the U.S. Election and to Exploit Government & Private Sectors, Recommended Mitigation Strategies and International Cyber-Conflict LawNo ratings yet
- The Lie Detectives: In Search of a Playbook for Winning Elections in the Disinformation AgeFrom EverandThe Lie Detectives: In Search of a Playbook for Winning Elections in the Disinformation AgeNo ratings yet
- The Rise of Big Data Policing: Surveillance, Race, and the Future of Law EnforcementFrom EverandThe Rise of Big Data Policing: Surveillance, Race, and the Future of Law EnforcementRating: 4.5 out of 5 stars4.5/5 (4)
- Russian Cyber Attack: The Rules of Cyber Warfare & Grizzly Steppe ReportFrom EverandRussian Cyber Attack: The Rules of Cyber Warfare & Grizzly Steppe ReportNo ratings yet
- Summary of Recoding America by Jennifer Pahlka: Why Government Is Failing in the Digital Age and How We Can Do BetterFrom EverandSummary of Recoding America by Jennifer Pahlka: Why Government Is Failing in the Digital Age and How We Can Do BetterNo ratings yet
- Debunked?: An auditor reviews the 2020 election—and the lessons learnedFrom EverandDebunked?: An auditor reviews the 2020 election—and the lessons learnedNo ratings yet
- The Battle for the Court: Interest Groups, Judicial Elections, and Public PolicyFrom EverandThe Battle for the Court: Interest Groups, Judicial Elections, and Public PolicyRating: 3 out of 5 stars3/5 (2)
- Kentucky Becomes Latest State To Take On Woke Banks, Asset ManagersDocument4 pagesKentucky Becomes Latest State To Take On Woke Banks, Asset ManagersDvddNo ratings yet
- California Faces Multiple Extreme Weather Events at Same TimeDocument3 pagesCalifornia Faces Multiple Extreme Weather Events at Same TimeDvddNo ratings yet
- Juan Pablo Ferrero (Auth.) - Democracy Against Neoliberalism in Argentina and BDocument269 pagesJuan Pablo Ferrero (Auth.) - Democracy Against Neoliberalism in Argentina and BDvddNo ratings yet
- Alkebulan African Dining Hall - WH: Pulse Nigeria Expo 2020 DubaiDocument2 pagesAlkebulan African Dining Hall - WH: Pulse Nigeria Expo 2020 DubaiDvddNo ratings yet
- Chaos in Brazil: Protesters Storm Capital, Destroying Supreme Court and CongressDocument14 pagesChaos in Brazil: Protesters Storm Capital, Destroying Supreme Court and CongressDvddNo ratings yet
- Federal Judge Rules That Parts of New Jersey Gun Law Are UnconstitutionalDocument4 pagesFederal Judge Rules That Parts of New Jersey Gun Law Are UnconstitutionalDvddNo ratings yet
- Julius K. Nyerere - Ujamaa - Essays On Socialism-Oxford University Press (1968)Document196 pagesJulius K. Nyerere - Ujamaa - Essays On Socialism-Oxford University Press (1968)DvddNo ratings yet
- Dominion Democracy Suite Release 41437 Version 1 Test ReportDocument26 pagesDominion Democracy Suite Release 41437 Version 1 Test ReportDvddNo ratings yet
- Term Paper Rough DraftDocument3 pagesTerm Paper Rough Draftapi-286275721100% (1)
- Argala: Illustration: Define Primary Argala and Virodha Argala On Lagna For A Standard BirthDocument4 pagesArgala: Illustration: Define Primary Argala and Virodha Argala On Lagna For A Standard Birthsurinder sangarNo ratings yet
- Advanced Presentation Skills WorkshopDocument34 pagesAdvanced Presentation Skills WorkshopJade Cemre ErciyesNo ratings yet
- Lapasan National High SchoolDocument3 pagesLapasan National High SchoolMiss SheemiNo ratings yet
- 5e - Ley Lines & Nexuses 1.0Document21 pages5e - Ley Lines & Nexuses 1.0Russo BrOficialNo ratings yet
- Tissue Preservation and Maintenance of Optimum Esthetics: A Clinical ReportDocument7 pagesTissue Preservation and Maintenance of Optimum Esthetics: A Clinical ReportBagis Emre GulNo ratings yet
- Tinder Reset GuideDocument13 pagesTinder Reset GuideAbel FekaduNo ratings yet
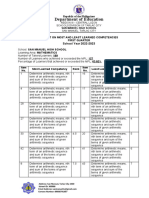
- Most and LEast LEarned Competencies 2022 2023 NUNAGDocument3 pagesMost and LEast LEarned Competencies 2022 2023 NUNAGJONATHAN NUNAGNo ratings yet
- A La CarteDocument3 pagesA La CarteJyot SoodNo ratings yet
- English Hots 1Document69 pagesEnglish Hots 1Aswin Shriram UmaThiagarajanNo ratings yet
- UNFCU Foundation Grant Application 2019Document4 pagesUNFCU Foundation Grant Application 2019Anonymous PbCsXeZNo ratings yet
- 13 Okol vs. Slimmer's World InternationalDocument2 pages13 Okol vs. Slimmer's World Internationaljed_sindaNo ratings yet
- kazan-helicopters (Russian Helicopters) 소개 2016Document33 pageskazan-helicopters (Russian Helicopters) 소개 2016Lee JihoonNo ratings yet
- Social Responsibility in The Jewelry IndustryDocument6 pagesSocial Responsibility in The Jewelry IndustryMK ULTRANo ratings yet
- 03 Preliminary PagesDocument12 pages03 Preliminary PagesBillie Jan Louie JardinNo ratings yet
- EnSight UserManualDocument868 pagesEnSight UserManualAnonymous scnl9rHNo ratings yet
- Happy Endings 2x03 - Yesandwitch PDFDocument40 pagesHappy Endings 2x03 - Yesandwitch PDFcoNo ratings yet
- APT1001.A2.01E.V1.0 - Preparation For Debug Kit SetupDocument2 pagesAPT1001.A2.01E.V1.0 - Preparation For Debug Kit SetupСергей КаревNo ratings yet
- Theory and Models of Consumer BehaviorDocument28 pagesTheory and Models of Consumer BehaviorNK ShresthaNo ratings yet
- 195 Santos v. NorthwestDocument4 pages195 Santos v. NorthwestAnn Julienne AristozaNo ratings yet
- 2004cwl Infrequent Pp52-103Document52 pages2004cwl Infrequent Pp52-103Henry LanguisanNo ratings yet
- Kerala Agricultural University: Main Campus, Vellanikkara, Thrissur - 680 656, KeralaDocument3 pagesKerala Agricultural University: Main Campus, Vellanikkara, Thrissur - 680 656, KeralaAyyoobNo ratings yet
- Corrected First Set of Admissions Us Bank ADJUST TO YOUR BANK PLAINTIFFDocument13 pagesCorrected First Set of Admissions Us Bank ADJUST TO YOUR BANK PLAINTIFF1SantaFean100% (1)
- Filler Metals: High Purity Solutions For Creep Resistant Steels - B2 SC and B3 SC AlloysDocument8 pagesFiller Metals: High Purity Solutions For Creep Resistant Steels - B2 SC and B3 SC AlloysimreNo ratings yet
- MRP PDFDocument45 pagesMRP PDFSamNo ratings yet
- Combustion & Fuels: Cement Process Engineering Vade-MecumDocument15 pagesCombustion & Fuels: Cement Process Engineering Vade-MecumJesus RodriguezNo ratings yet
- Simatic Step7 Graph7Document212 pagesSimatic Step7 Graph7loadsach100% (1)
- STP 491-1971Document90 pagesSTP 491-1971Tim SchouwNo ratings yet
- Fidelity Absolute Return Global Equity Fund PresentationDocument51 pagesFidelity Absolute Return Global Equity Fund Presentationpietro silvestriNo ratings yet
- Admin Law DigestDocument49 pagesAdmin Law DigestMichelle Muhrie TablizoNo ratings yet