Professional Documents
Culture Documents
Oracle Estructura Académica
Oracle Estructura Académica
Uploaded by
cturinaOriginal Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Oracle Estructura Académica
Oracle Estructura Académica
Uploaded by
cturinaCopyright:
Available Formats
Oracle University | Contact Us: 1.800.529.
0165
Academic Structure Rel 9
Duration: 2 Days What you will learn In this course, participants complete activities that develop their knowledge of implementing academic structure for PeopleSoft Enterprise Campus Solutions as they revise and update an academic structure through online pages and Tree Manager. Participants learn about the difference between a single and multi-institution setup and how to define and use campus and location values and facilities as they relate to scheduling and facility groupings. Participants learn how to define academic careers as well as academic programs, plans, and sub-plans and look at the rules for defining academic terms and sessions and all related dates and time periods within an academic structure. Discussions abound about how each piece of the academic structure interacts with the others to form an interdependent system of rules and regulations that give business processes the foundation upon which they rely. Through a discussion of dynamic dates, students learn that many term and session dates affect more than one area of PeopleSoft Campus Solutions. Participants look at the association between setting up and organizing PeopleSoft Tree Manager and how security can then be established for specific departmental use of the course catalog, based on this hierarchy. Learn to: Evaluate the application of key academic structure components in your system Setup academic terms and sessions Define academic structure user security as it relates to PeopleSoft Enterprise Campus Solutions business process
Audience Business Analysts Functional Implementer Project Manager
Prerequisites Suggested Prerequisites Understanding of basic navigation and PeopleSoft concepts Use of control tables to enforce business rules Able to run processes and reports Course Objectives Provide an overview of academic structure. Evaluate the application of key academic structural components to your system. Describe how to set up academic terms and sessions. Explain the use of academic organizations, including PeopleSoft Tree Manager. Define user security for academic structure as it relates to PeopleSoft Campus
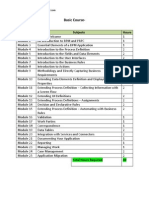
Course Topics
Copyright 2009, Oracle. All rights reserved.
Page 1
Setting Up Data at the System Level Identifying Academic Institutions, Record Groups, and tableset IDs Determining Academic Institutions and Setup Options Define Establishments, Locations and Campuses Set Up Buildings and Facilities Setting Up Data at the Academic Institution Level Setting up Grading Schemes Defining Repeat Schemes Defining Academic Institutions Setting Up Academic Groups, Careers, and Catalog Data Defining Academic Groups Defining Academic Careers Setting Up Unit Types and Conversion Rules Defining Career Pointers and Exception Rules Defining Repeat Checking Rules Setting Up Holiday Schedule Values Defining Instructors and Advisors Setting Up Academic Programs, Plans, and Subplans Defining an Academic Calendar Describing Enrollment Action Reasons Describing Academic Level and Load Rules Setting Up Academic Programs Setting Up Academic Terms and Sessions Defining Term Values Defining Time Periods Defining Academic Terms and Sessions Describing the Dynamic Dating Process Setting Up Academic Organizations Setting Up Organizations with PeopleSoft Tree Manager Defining Academic Groups Configuring Academic Organizations Assigning User Security to Academic Organizations Setting Up Academic Subjects Establishing Security Describing User Profiles, Roles and Permission Lists Describing Academic Structure Security Describing Component Specific Security Describing User Based Security Interactions Securing PeopleSoft Applications
Copyright 2009, Oracle. All rights reserved.
Page 2
You might also like
- YEAR 3 APEP Guidelines v1.3Document42 pagesYEAR 3 APEP Guidelines v1.3Duncan AlexanderNo ratings yet
- Career Genogram RubricDocument1 pageCareer Genogram Rubricapi-360153811No ratings yet
- A Teaching Methodology (Supplimentary Docs.)Document73 pagesA Teaching Methodology (Supplimentary Docs.)Vireak Som0% (1)
- Academic Structure Rel 9 2Document4 pagesAcademic Structure Rel 9 2Luigi Raúl RomeroNo ratings yet
- Thesis Documentation For Online Grading SystemDocument7 pagesThesis Documentation For Online Grading Systemgj9cpzxs100% (2)
- R12.x Oracle HRMS Learning Management FundamentalsDocument4 pagesR12.x Oracle HRMS Learning Management FundamentalsMohamed ShanabNo ratings yet
- Literature Review Online Student Registration SystemDocument7 pagesLiterature Review Online Student Registration Systemea3j015dNo ratings yet
- Thesis School Management SystemDocument8 pagesThesis School Management Systemgjhr3grk100% (1)
- Online Class Scheduling System Thesis DocumentationDocument4 pagesOnline Class Scheduling System Thesis Documentationnicoleyoungaurora100% (2)
- Student Grading System Report 0727Document14 pagesStudent Grading System Report 0727Masud Ranna50% (4)
- Student Registration System Project Literature ReviewDocument8 pagesStudent Registration System Project Literature ReviewafdtakoeaNo ratings yet
- System ThesisDocument8 pagesSystem Thesisgbvr4f9w100% (2)
- Modules Subjects Hours: Basic CourseDocument5 pagesModules Subjects Hours: Basic CoursesanjaykumarguptaaNo ratings yet
- Fusion Applications HCM Talent Management Implementation D78268GC20 - 28 - USDocument3 pagesFusion Applications HCM Talent Management Implementation D78268GC20 - 28 - USMNo ratings yet
- AWS-Course OutlineDocument7 pagesAWS-Course OutlineJerusalem FeteneNo ratings yet
- PHD Thesis Business Process ManagementDocument5 pagesPHD Thesis Business Process Managementjpcbobkef100% (2)
- Sample Thesis Online Enrollment SystemDocument5 pagesSample Thesis Online Enrollment SystemPayForSomeoneToWriteYourPaperEverett100% (2)
- System Design Specification Thesis ExampleDocument8 pagesSystem Design Specification Thesis Examplestephaniebenjaminclarksville100% (1)
- Review of Related LiteratureDocument5 pagesReview of Related LiteratureEloisa PinedaNo ratings yet
- Online Grading System Thesis SampleDocument6 pagesOnline Grading System Thesis Samplefjcz1j5g100% (2)
- Sample Thesis in System Analysis and DesignDocument7 pagesSample Thesis in System Analysis and Designtifqbfgig100% (2)
- LMS Features RequirementsDocument48 pagesLMS Features Requirementsaymal khalidNo ratings yet
- School Management SystemDocument11 pagesSchool Management SystemGayle Marie RosalesNo ratings yet
- Systems Analysis & Design ML GUIDEDocument11 pagesSystems Analysis & Design ML GUIDEIan Dela Cruz OguinNo ratings yet
- Accounting Information System Course SyllabusDocument10 pagesAccounting Information System Course Syllabusali alhussainNo ratings yet
- Sample Thesis Introduction in Enrollment SystemDocument7 pagesSample Thesis Introduction in Enrollment Systembrookelordmanchester100% (2)
- Oracle History and ProfileDocument7 pagesOracle History and Profilesaisuryarohitreddy2002No ratings yet
- Peoplesoft Campus SolutionsDocument51 pagesPeoplesoft Campus SolutionsfarighNo ratings yet
- Mid Term PresentationDocument23 pagesMid Term PresentationRamit KumarNo ratings yet
- Enrollment System Thesis Documentation DownloadDocument5 pagesEnrollment System Thesis Documentation Downloaddnr3krf8100% (1)
- OWP Primavera Professional PDFDocument4 pagesOWP Primavera Professional PDFShafiNo ratings yet
- CasoRegistroCurso UMLDocument12 pagesCasoRegistroCurso UMLEel DdeNo ratings yet
- Systems Analysis and Design 10Th Edition Shelly Solutions Manual Full Chapter PDFDocument34 pagesSystems Analysis and Design 10Th Edition Shelly Solutions Manual Full Chapter PDFdariusluyen586100% (8)
- Systems Analysis and Design 10th Edition Shelly Solutions ManualDocument13 pagesSystems Analysis and Design 10th Edition Shelly Solutions Manualrowenagabrieleatq100% (24)
- University DatabaseDocument6 pagesUniversity DatabaseEvans OduorNo ratings yet
- Name-Dhruv Gangwar Sec-G Roll No - 24Document7 pagesName-Dhruv Gangwar Sec-G Roll No - 24gangwardhruvgangwarNo ratings yet
- Conceptual Framework Thesis IpoDocument5 pagesConceptual Framework Thesis Ipogbvhhgpj100% (2)
- DBMS-Chapter-2 notes-ER ModelDocument21 pagesDBMS-Chapter-2 notes-ER ModelHarsh ChitaliyaNo ratings yet
- Thesis Archive SystemDocument8 pagesThesis Archive Systemafkofvidg100% (2)
- Faculty Scheduling System Thesis DocumentationDocument4 pagesFaculty Scheduling System Thesis DocumentationApril Smith100% (1)
- Web-Based Thesis Capstone Project Defense Evaluation System of The CCS BiñanDocument17 pagesWeb-Based Thesis Capstone Project Defense Evaluation System of The CCS BiñanMan GeorgeNo ratings yet
- Training ReportDocument50 pagesTraining ReportAakash SharmaNo ratings yet
- Thesis Voting SystemDocument7 pagesThesis Voting SystemSomeoneWriteMyPaperSavannah100% (2)
- Using Oracle Enterprise Manager Cloud Control 12c - D73244GC10 - 1080544 - USDocument4 pagesUsing Oracle Enterprise Manager Cloud Control 12c - D73244GC10 - 1080544 - USJinendraabhiNo ratings yet
- Class Diagram ThesisDocument7 pagesClass Diagram ThesisArlene Smith100% (2)
- SAP SLCM - Product Architecture PDFDocument59 pagesSAP SLCM - Product Architecture PDFgusuarez75100% (1)
- Management Information System Thesis SampleDocument7 pagesManagement Information System Thesis Sampleballnimasal1972100% (2)
- Software Requirement Specification ForDocument9 pagesSoftware Requirement Specification ForythNo ratings yet
- Example of Thesis in System Analysis and DesignDocument8 pagesExample of Thesis in System Analysis and Designfc2b5myj100% (2)
- Systems Officer Processing QPR RD B278Document4 pagesSystems Officer Processing QPR RD B278Shintu DeyNo ratings yet
- Course Registration System Literature ReviewDocument5 pagesCourse Registration System Literature Reviewekvxrxrif100% (1)
- FIR SystemDocument40 pagesFIR SystemRahul Vasant SawantNo ratings yet
- Grading System Sample ThesisDocument6 pagesGrading System Sample Thesisafkodkedr100% (2)
- CIS 380 Spring2020Document12 pagesCIS 380 Spring2020ChristianNo ratings yet
- Oracle Fusion Talent ManagementDocument2 pagesOracle Fusion Talent ManagementsharadkadamNo ratings yet
- Thesis OperationalizationDocument5 pagesThesis Operationalizationkatieharrisannarbor100% (2)
- M.SC Thesis ProposalDocument7 pagesM.SC Thesis ProposalBuyPapersForCollegeCanada100% (2)
- Oracle HRMS Learning Management R12Document12 pagesOracle HRMS Learning Management R12Yogita Sarang100% (2)
- Sqa Computing Coursework 2013Document7 pagesSqa Computing Coursework 2013afazakemb100% (3)
- Thesis Online Grading System PDFDocument7 pagesThesis Online Grading System PDFynwtcpwff100% (2)
- System Development Life Cycle of A Student Management System For A UniversityDocument12 pagesSystem Development Life Cycle of A Student Management System For A UniversityMD:Rabbi sr RidoyNo ratings yet
- Is Analysts Job DescriptionDocument8 pagesIs Analysts Job Descriptionafvillodres7471No ratings yet
- Group Project Software Management: A Guide for University Students and InstructorsFrom EverandGroup Project Software Management: A Guide for University Students and InstructorsNo ratings yet
- PTS LemarDocument173 pagesPTS LemarYmel Jade De GuiaNo ratings yet
- Member MaharashtraDocument20 pagesMember MaharashtraKshitija BirjeNo ratings yet
- Akshata Gundeti CV EditedDocument1 pageAkshata Gundeti CV EditedSai PrasannaNo ratings yet
- Project-Based Learning and Problem-Based Learning For EFL Students' Writing Achievement at The Tertiary LevelDocument18 pagesProject-Based Learning and Problem-Based Learning For EFL Students' Writing Achievement at The Tertiary LevelIla Ilhami QoriNo ratings yet
- BALIK ARAL Individual Learning PlanDocument3 pagesBALIK ARAL Individual Learning PlanDiane Mae FabroaNo ratings yet
- Angelo Fuscablo CV 1Document2 pagesAngelo Fuscablo CV 1Jebie VillaNo ratings yet
- Seven Myths of MemoryDocument7 pagesSeven Myths of MemorycoconitaNo ratings yet
- A CFD Study of Pickup Truck AerodynamicsDocument9 pagesA CFD Study of Pickup Truck Aerodynamicssh1999No ratings yet
- Group-1-5a ResearchDocument7 pagesGroup-1-5a ResearchJerry Angelo MagnoNo ratings yet
- Increasing Female Educational OpportunitiesDocument3 pagesIncreasing Female Educational OpportunitiesAlemayehu DargeNo ratings yet
- Annual Supervisory Plan 2018-2019 First SemDocument4 pagesAnnual Supervisory Plan 2018-2019 First SemRosendo BernabeNo ratings yet
- Mathematics Extension 1 Year 12 Topic Guide ProofDocument6 pagesMathematics Extension 1 Year 12 Topic Guide ProofmichaelNo ratings yet
- Percakapan Bahasa Inggris Tentang HomeworkDocument8 pagesPercakapan Bahasa Inggris Tentang Homeworkxusmkxfng100% (1)
- Department of Labor: fs17c AdministrativeDocument3 pagesDepartment of Labor: fs17c AdministrativeUSA_DepartmentOfLaborNo ratings yet
- RULES - Unimpossible Missions University Edition Challenge - FN REVDocument11 pagesRULES - Unimpossible Missions University Edition Challenge - FN REVAnonymous 8nlNLKJNo ratings yet
- AllottmentLetterDocument1 pageAllottmentLetterAshwani KumarNo ratings yet
- Mandatory Disclosure 17Document546 pagesMandatory Disclosure 17kannambiNo ratings yet
- Engl1010 Revised Rhetorical AnalysisDocument5 pagesEngl1010 Revised Rhetorical Analysisapi-494950991No ratings yet
- Worksheet BRGY PROFILEDocument6 pagesWorksheet BRGY PROFILEMaybelyn de los ReyesNo ratings yet
- Brigada Eskwela Letters For Stakeholders 2023Document21 pagesBrigada Eskwela Letters For Stakeholders 2023Angel Lou LiwagonNo ratings yet
- Level 1, Module 1 Hot Spot Extra ReadingDocument3 pagesLevel 1, Module 1 Hot Spot Extra ReadingMarina VoiculescuNo ratings yet
- Post Test Educ 109 1 3Document18 pagesPost Test Educ 109 1 3Trexel MirasNo ratings yet
- Idlar New - Plain - MargieDocument10 pagesIdlar New - Plain - MargieMargie Macam Rodriguez100% (1)
- What Types of Water Is On The EarthDocument2 pagesWhat Types of Water Is On The Earthapi-252119419No ratings yet
- 2 (F) and 12 (B) Colleges - Proforma For Soliciting Xii Plan Requirements of The CollegeDocument15 pages2 (F) and 12 (B) Colleges - Proforma For Soliciting Xii Plan Requirements of The CollegeSenthil KumarNo ratings yet
- 1 FlyerDocument2 pages1 FlyerSheine Nasayao MatosNo ratings yet
- St. Lawrence School Lay TeachersDocument7 pagesSt. Lawrence School Lay TeachersLucia Lombardi BorzilloNo ratings yet