Professional Documents
Culture Documents
0 ratings0% found this document useful (0 votes)
11 viewsAssignment 1
Assignment 1
Uploaded by
Swapnil RautkhedkarThis document contains 20 questions about various topics in cyber security and artificial intelligence. It asks about definitions of cyber security concepts like CIA and attributes, different types of cybercrimes and attacks such as phishing, social engineering, and ransomware. It also asks about vulnerabilities, threats, types of hackers, and how machine learning and AI are used for threat detection and strengthening cyber security defenses.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You might also like
- 300 Interview Questions For Cyber Security RolesDocument9 pages300 Interview Questions For Cyber Security Rolesmeetsudhar100% (1)
- The Threat Environment: Attackers and Their AttacksDocument8 pagesThe Threat Environment: Attackers and Their AttacksbseosNo ratings yet
- Cyber Security All Unit ImportantDocument5 pagesCyber Security All Unit Importantsinghnutan16novNo ratings yet
- Cyber Security Question For ReferenceDocument3 pagesCyber Security Question For ReferenceIsha ThakreNo ratings yet
- Cyber Security Some Sample Question Bank 2023 24Document2 pagesCyber Security Some Sample Question Bank 2023 24sanskarsatwik100No ratings yet
- Question Bank Cyber Security and Intellectual Property RightsDocument2 pagesQuestion Bank Cyber Security and Intellectual Property RightsmasumiNo ratings yet
- Cyber Security QuestionsDocument1 pageCyber Security QuestionsJulius E. CatiponNo ratings yet
- Interview Question P - 2Document1 pageInterview Question P - 2manishsamrat2905No ratings yet
- Review Questions / Module 1 / Unit 1 / Indicators of CompromiseDocument1 pageReview Questions / Module 1 / Unit 1 / Indicators of CompromiseDarlene Serrano LoweNo ratings yet
- Cybersecurity - 1ST Ia Question BankDocument1 pageCybersecurity - 1ST Ia Question BankAbdul Latheef NawasNo ratings yet
- Questuin Bank CSDocument1 pageQuestuin Bank CSrohitsharma30454545No ratings yet
- Cyber Security - AssessmentDocument1 pageCyber Security - Assessmentrakshita rajappaNo ratings yet
- Is Important QuestionsDocument64 pagesIs Important QuestionsNivithaNo ratings yet
- GK On Cyber Security - Cyber Crime, Cyber Attack (Question and Answer)Document16 pagesGK On Cyber Security - Cyber Crime, Cyber Attack (Question and Answer)Tang Kumar SovanNo ratings yet
- Cyber Security BCC301 Assignment 3 & 4Document6 pagesCyber Security BCC301 Assignment 3 & 4abhi.k.kashyap786No ratings yet
- 34735.question Bank CS501Document4 pages34735.question Bank CS501Akshay SinghNo ratings yet
- Cybersecurity - 1st Ia Question BankDocument1 pageCybersecurity - 1st Ia Question Bankaztec.sapphire11No ratings yet
- Interview Questions P - 1Document1 pageInterview Questions P - 1manishsamrat2905No ratings yet
- Interview QuestionsDocument3 pagesInterview Questionssivapavani4245No ratings yet
- Module 3Document44 pagesModule 3Shubham SarkarNo ratings yet
- Question Bank-InfoSecDocument1 pageQuestion Bank-InfoSecwast9197No ratings yet
- Fundamentals of Networking Assignemnt CDocument1 pageFundamentals of Networking Assignemnt Cabelcreed1994No ratings yet
- Cryptography AssignmentDocument4 pagesCryptography Assignmentmulugeta haileNo ratings yet
- QuestionsDocument1 pageQuestionsAarti jhaNo ratings yet
- Week2 ExerciseDocument2 pagesWeek2 ExerciseUmer Mushtaq GujjarNo ratings yet
- Computer System SecurityDocument1 pageComputer System Securityaditya2021cs081No ratings yet
- Internet Security 2004Document1 pageInternet Security 2004anon_584064050No ratings yet
- Cyber Security Interview PreparationDocument3 pagesCyber Security Interview Preparationsureshmenonpk692No ratings yet
- Ôn tập TACNDocument42 pagesÔn tập TACNKhánh MinhNo ratings yet
- Nis Qbank Final ExamDocument2 pagesNis Qbank Final ExamShrutiNo ratings yet
- QnbankDocument2 pagesQnbankBhartiNo ratings yet
- CSF Asgmt 1Document1 pageCSF Asgmt 1aapmklhguNo ratings yet
- Thergaon Pune Question Bank For Final Examination: Marathwada Mitra Mandal's PolytechnicDocument2 pagesThergaon Pune Question Bank For Final Examination: Marathwada Mitra Mandal's Polytechnicshruti gaware100% (1)
- Cyber SecurityDocument3 pagesCyber SecuritySAMAY N. JAINNo ratings yet
- Nis Qbank Final ExamDocument4 pagesNis Qbank Final Exam974-Abhijeet MotewarNo ratings yet
- Important QuestionsDocument6 pagesImportant QuestionsVivek DangiNo ratings yet
- Chapter 1 QuestionDocument1 pageChapter 1 Questionvrushabhb8055No ratings yet
- Mca QB ISDocument1 pageMca QB ISSRC ExamNo ratings yet
- Cyber Security-Unit-1&2Document2 pagesCyber Security-Unit-1&2RohitNo ratings yet
- 19cse304-Cybersecurity Answer KeyDocument19 pages19cse304-Cybersecurity Answer KeyabhiNo ratings yet
- Question Paper of Cryptography and Network SecurityDocument5 pagesQuestion Paper of Cryptography and Network SecurityAnkita Dwivedi100% (1)
- QB Cyber ScurityDocument3 pagesQB Cyber ScurityAnjan UtkarshNo ratings yet
- Assignment 2 Date of Allotment Date of Submission: 09-Sep-19 23-Sep-19Document3 pagesAssignment 2 Date of Allotment Date of Submission: 09-Sep-19 23-Sep-19Sunny SandhuNo ratings yet
- INS IMP QB (E-Next - In)Document3 pagesINS IMP QB (E-Next - In)LAPPY HUBNo ratings yet
- Cyber Crime & LawDocument2 pagesCyber Crime & LawShravani SalunkheNo ratings yet
- Cyber Security AssignmentDocument29 pagesCyber Security AssignmentDusk LightNo ratings yet
- Revision QuestionsDocument1 pageRevision QuestionsViktor InfinityNo ratings yet
- Unit 1 2 MarksDocument2 pagesUnit 1 2 Markssaranyaksr92No ratings yet
- Is SampleQuesDocument2 pagesIs SampleQuesaparna chinnarajNo ratings yet
- Cyber Security ApponixDocument4 pagesCyber Security ApponixAshokNo ratings yet
- Sic Prelim AssignmentDocument1 pageSic Prelim Assignmentwawet10014No ratings yet
- TEST DE NIVEAU DU COURS DE CyberOpsDocument5 pagesTEST DE NIVEAU DU COURS DE CyberOpsArnaud Semevo AhouandjinouNo ratings yet
- Lbti LTD Cybersecurity - 073153Document5 pagesLbti LTD Cybersecurity - 073153LIGHTHOUSE BUSINESS AND TECHNOLOGY INTEGRATION LTDNo ratings yet
- SyllabusDocument6 pagesSyllabusmanomahe0287No ratings yet
- Security Questions Interview QuestionsDocument11 pagesSecurity Questions Interview QuestionsSaurabh VashistNo ratings yet
- MCQ Questions CybersecurityDocument5 pagesMCQ Questions CybersecurityAakanksha NNo ratings yet
- SIC - VIVA QuestionsDocument3 pagesSIC - VIVA Questionsrohit rohitNo ratings yet
- Gujarat Technological UniversityDocument1 pageGujarat Technological UniversityCode AttractionNo ratings yet
- AICS - Assignment No-1Document14 pagesAICS - Assignment No-1Swapnil RautkhedkarNo ratings yet
- Syllabus - Applications of AI For CSFileDocument5 pagesSyllabus - Applications of AI For CSFileSwapnil RautkhedkarNo ratings yet
- Applications of AI in Cyber SecurityDocument89 pagesApplications of AI in Cyber SecuritySwapnil RautkhedkarNo ratings yet
- Advanced AIDocument4 pagesAdvanced AISwapnil RautkhedkarNo ratings yet
Assignment 1
Assignment 1
Uploaded by
Swapnil Rautkhedkar0 ratings0% found this document useful (0 votes)
11 views1 pageThis document contains 20 questions about various topics in cyber security and artificial intelligence. It asks about definitions of cyber security concepts like CIA and attributes, different types of cybercrimes and attacks such as phishing, social engineering, and ransomware. It also asks about vulnerabilities, threats, types of hackers, and how machine learning and AI are used for threat detection and strengthening cyber security defenses.
Original Description:
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThis document contains 20 questions about various topics in cyber security and artificial intelligence. It asks about definitions of cyber security concepts like CIA and attributes, different types of cybercrimes and attacks such as phishing, social engineering, and ransomware. It also asks about vulnerabilities, threats, types of hackers, and how machine learning and AI are used for threat detection and strengthening cyber security defenses.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
Download as pdf or txt
0 ratings0% found this document useful (0 votes)
11 views1 pageAssignment 1
Assignment 1
Uploaded by
Swapnil RautkhedkarThis document contains 20 questions about various topics in cyber security and artificial intelligence. It asks about definitions of cyber security concepts like CIA and attributes, different types of cybercrimes and attacks such as phishing, social engineering, and ransomware. It also asks about vulnerabilities, threats, types of hackers, and how machine learning and AI are used for threat detection and strengthening cyber security defenses.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
Download as pdf or txt
You are on page 1of 1
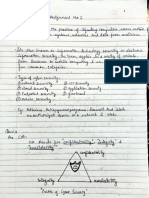
School of Computer Science, Engineering and Applications
Assignment 1 (Based on unit 1)
Basics of AI and CS
1. What is cyber security?
2. What does CIA stand for in cyber security?
3. What are the attributes of cyber security?
4. Define cybercrime and enlist cybercrime.
5. Explain salami slicing attack with an example.
6. What is phishing?
7. Write a note on Social engineering.
8. How do you find out whether a system is compromised or vulnerable?
9. What is a computer virus? Give its type.
10.What is cybercrime? Give some examples of cybercrime committed
against an individual.
11.Describe Threats and Vulnerability. Do they refer to the same thing?
12.Distinguish between cyberstalking and Cyberbullying
13. What do you mean by a cybercriminal? Differentiate Gray, black and
white hacker.
14.How do you mitigate the risk of Cross-Site Request Forgery (CSRF)?
15. Give some examples of nonmalicious program errors.
16.How does a Ransomware attack work?
17. What are the drawbacks and Limitations of Using AI for Cybersecurity?
18.Explain how AI-powered threat detection works?
19.How AI is applicable in Cybersecurity, explain with real-time example.
20. What Is Machine Learning and How Is it Used in Cybersecurity?
---------------------------------------------********************-------------------------------
You might also like
- 300 Interview Questions For Cyber Security RolesDocument9 pages300 Interview Questions For Cyber Security Rolesmeetsudhar100% (1)
- The Threat Environment: Attackers and Their AttacksDocument8 pagesThe Threat Environment: Attackers and Their AttacksbseosNo ratings yet
- Cyber Security All Unit ImportantDocument5 pagesCyber Security All Unit Importantsinghnutan16novNo ratings yet
- Cyber Security Question For ReferenceDocument3 pagesCyber Security Question For ReferenceIsha ThakreNo ratings yet
- Cyber Security Some Sample Question Bank 2023 24Document2 pagesCyber Security Some Sample Question Bank 2023 24sanskarsatwik100No ratings yet
- Question Bank Cyber Security and Intellectual Property RightsDocument2 pagesQuestion Bank Cyber Security and Intellectual Property RightsmasumiNo ratings yet
- Cyber Security QuestionsDocument1 pageCyber Security QuestionsJulius E. CatiponNo ratings yet
- Interview Question P - 2Document1 pageInterview Question P - 2manishsamrat2905No ratings yet
- Review Questions / Module 1 / Unit 1 / Indicators of CompromiseDocument1 pageReview Questions / Module 1 / Unit 1 / Indicators of CompromiseDarlene Serrano LoweNo ratings yet
- Cybersecurity - 1ST Ia Question BankDocument1 pageCybersecurity - 1ST Ia Question BankAbdul Latheef NawasNo ratings yet
- Questuin Bank CSDocument1 pageQuestuin Bank CSrohitsharma30454545No ratings yet
- Cyber Security - AssessmentDocument1 pageCyber Security - Assessmentrakshita rajappaNo ratings yet
- Is Important QuestionsDocument64 pagesIs Important QuestionsNivithaNo ratings yet
- GK On Cyber Security - Cyber Crime, Cyber Attack (Question and Answer)Document16 pagesGK On Cyber Security - Cyber Crime, Cyber Attack (Question and Answer)Tang Kumar SovanNo ratings yet
- Cyber Security BCC301 Assignment 3 & 4Document6 pagesCyber Security BCC301 Assignment 3 & 4abhi.k.kashyap786No ratings yet
- 34735.question Bank CS501Document4 pages34735.question Bank CS501Akshay SinghNo ratings yet
- Cybersecurity - 1st Ia Question BankDocument1 pageCybersecurity - 1st Ia Question Bankaztec.sapphire11No ratings yet
- Interview Questions P - 1Document1 pageInterview Questions P - 1manishsamrat2905No ratings yet
- Interview QuestionsDocument3 pagesInterview Questionssivapavani4245No ratings yet
- Module 3Document44 pagesModule 3Shubham SarkarNo ratings yet
- Question Bank-InfoSecDocument1 pageQuestion Bank-InfoSecwast9197No ratings yet
- Fundamentals of Networking Assignemnt CDocument1 pageFundamentals of Networking Assignemnt Cabelcreed1994No ratings yet
- Cryptography AssignmentDocument4 pagesCryptography Assignmentmulugeta haileNo ratings yet
- QuestionsDocument1 pageQuestionsAarti jhaNo ratings yet
- Week2 ExerciseDocument2 pagesWeek2 ExerciseUmer Mushtaq GujjarNo ratings yet
- Computer System SecurityDocument1 pageComputer System Securityaditya2021cs081No ratings yet
- Internet Security 2004Document1 pageInternet Security 2004anon_584064050No ratings yet
- Cyber Security Interview PreparationDocument3 pagesCyber Security Interview Preparationsureshmenonpk692No ratings yet
- Ôn tập TACNDocument42 pagesÔn tập TACNKhánh MinhNo ratings yet
- Nis Qbank Final ExamDocument2 pagesNis Qbank Final ExamShrutiNo ratings yet
- QnbankDocument2 pagesQnbankBhartiNo ratings yet
- CSF Asgmt 1Document1 pageCSF Asgmt 1aapmklhguNo ratings yet
- Thergaon Pune Question Bank For Final Examination: Marathwada Mitra Mandal's PolytechnicDocument2 pagesThergaon Pune Question Bank For Final Examination: Marathwada Mitra Mandal's Polytechnicshruti gaware100% (1)
- Cyber SecurityDocument3 pagesCyber SecuritySAMAY N. JAINNo ratings yet
- Nis Qbank Final ExamDocument4 pagesNis Qbank Final Exam974-Abhijeet MotewarNo ratings yet
- Important QuestionsDocument6 pagesImportant QuestionsVivek DangiNo ratings yet
- Chapter 1 QuestionDocument1 pageChapter 1 Questionvrushabhb8055No ratings yet
- Mca QB ISDocument1 pageMca QB ISSRC ExamNo ratings yet
- Cyber Security-Unit-1&2Document2 pagesCyber Security-Unit-1&2RohitNo ratings yet
- 19cse304-Cybersecurity Answer KeyDocument19 pages19cse304-Cybersecurity Answer KeyabhiNo ratings yet
- Question Paper of Cryptography and Network SecurityDocument5 pagesQuestion Paper of Cryptography and Network SecurityAnkita Dwivedi100% (1)
- QB Cyber ScurityDocument3 pagesQB Cyber ScurityAnjan UtkarshNo ratings yet
- Assignment 2 Date of Allotment Date of Submission: 09-Sep-19 23-Sep-19Document3 pagesAssignment 2 Date of Allotment Date of Submission: 09-Sep-19 23-Sep-19Sunny SandhuNo ratings yet
- INS IMP QB (E-Next - In)Document3 pagesINS IMP QB (E-Next - In)LAPPY HUBNo ratings yet
- Cyber Crime & LawDocument2 pagesCyber Crime & LawShravani SalunkheNo ratings yet
- Cyber Security AssignmentDocument29 pagesCyber Security AssignmentDusk LightNo ratings yet
- Revision QuestionsDocument1 pageRevision QuestionsViktor InfinityNo ratings yet
- Unit 1 2 MarksDocument2 pagesUnit 1 2 Markssaranyaksr92No ratings yet
- Is SampleQuesDocument2 pagesIs SampleQuesaparna chinnarajNo ratings yet
- Cyber Security ApponixDocument4 pagesCyber Security ApponixAshokNo ratings yet
- Sic Prelim AssignmentDocument1 pageSic Prelim Assignmentwawet10014No ratings yet
- TEST DE NIVEAU DU COURS DE CyberOpsDocument5 pagesTEST DE NIVEAU DU COURS DE CyberOpsArnaud Semevo AhouandjinouNo ratings yet
- Lbti LTD Cybersecurity - 073153Document5 pagesLbti LTD Cybersecurity - 073153LIGHTHOUSE BUSINESS AND TECHNOLOGY INTEGRATION LTDNo ratings yet
- SyllabusDocument6 pagesSyllabusmanomahe0287No ratings yet
- Security Questions Interview QuestionsDocument11 pagesSecurity Questions Interview QuestionsSaurabh VashistNo ratings yet
- MCQ Questions CybersecurityDocument5 pagesMCQ Questions CybersecurityAakanksha NNo ratings yet
- SIC - VIVA QuestionsDocument3 pagesSIC - VIVA Questionsrohit rohitNo ratings yet
- Gujarat Technological UniversityDocument1 pageGujarat Technological UniversityCode AttractionNo ratings yet
- AICS - Assignment No-1Document14 pagesAICS - Assignment No-1Swapnil RautkhedkarNo ratings yet
- Syllabus - Applications of AI For CSFileDocument5 pagesSyllabus - Applications of AI For CSFileSwapnil RautkhedkarNo ratings yet
- Applications of AI in Cyber SecurityDocument89 pagesApplications of AI in Cyber SecuritySwapnil RautkhedkarNo ratings yet
- Advanced AIDocument4 pagesAdvanced AISwapnil RautkhedkarNo ratings yet