Professional Documents
Culture Documents
Cambridge Assessment International Education: Computer Science 0478/13 October/November 2017
Cambridge Assessment International Education: Computer Science 0478/13 October/November 2017
Uploaded by
AwadOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Cambridge Assessment International Education: Computer Science 0478/13 October/November 2017
Cambridge Assessment International Education: Computer Science 0478/13 October/November 2017
Uploaded by
AwadCopyright:
Available Formats
Cambridge Assessment International Education
Cambridge International General Certificate of Secondary Education
COMPUTER SCIENCE 0478/13
Paper 1 October/November 2017
MARK SCHEME
Maximum Mark: 75
Published
This mark scheme is published as an aid to teachers and candidates, to indicate the requirements of the
examination. It shows the basis on which Examiners were instructed to award marks. It does not indicate the
details of the discussions that took place at an Examiners’ meeting before marking began, which would have
considered the acceptability of alternative answers.
bestexamhelp.com
Mark schemes should be read in conjunction with the question paper and the Principal Examiner Report for
Teachers.
Cambridge International will not enter into discussions about these mark schemes.
Cambridge International is publishing the mark schemes for the October/November 2017 series for most
Cambridge IGCSE®, Cambridge International A and AS Level components and some Cambridge O Level
components.
® IGCSE is a registered trademark.
This syllabus is approved for use in England, Wales and Northern Ireland as a Cambridge International Level 1/Level 2 Certificate.
This document consists of 10 printed pages.
© UCLES 2017 [Turn over
0478/13 Cambridge IGCSE – Mark Scheme October/November
PUBLISHED 2017
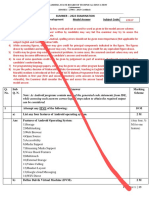
Question Answer Marks
1(a) Output 1
1(b) 1 mark for each correct conversion 3
E 0 4
1 1 1 0 0 0 0 0 0 1 0 0
1(c) Any one from: 1
– Hexadecimal codes can fit in a smaller display rather than a full text based message
– Smaller amount of memory needed to store the hex error messages than text based
1(d) 1 mark for correct sensor, 1 mark for corresponding use 6
Possible examples could include:
– Temperature (sensor)
– To monitor the temperature of the water
– Pressure (sensor)
– To monitor the level of water in the washing machine
– Motion (sensor)
– To monitor whether the drum is still in motion
– pH (sensor)
– To monitor the level of water hardness/detergent present in the water
© UCLES 2017 Page 2 of 10
0478/13 Cambridge IGCSE – Mark Scheme October/November
PUBLISHED 2017
Question Answer Marks
2 1 mark for each correct file format e.g. 3
File type File format
Pictures .JPEG
.doc, .txt, .rtf,
Text
.docx, .odt .pdf
.mp3, .wav, .aif,
Sound
.flac, .mid
Video .mp4, .flv, .wmv
Question Answer Marks
3(a) – Part 1 (access) protocol 3
– Part 2 domain (name)
– Part 3 filename
3(b) Four from: 4
– IP address is used to identify a device (on the Internet / network)
– IP address is allocated by the network/ ISP
– Can be used in place of URL
– IP addresses can be IPv4 or IPv6
– IP address can be static «
– ... meaning it doesn’t change each time it is connected to the Internet
– IP address can be dynamic «.
– « meaning that it can change each time a device is connected to the Internet
– Any valid example (e.g. xxx.xxx.xxx.xxx or xxxx:xxxx:xxxx:xxxx:xxxx:xxxx:xxxx:xxxx)
© UCLES 2017 Page 3 of 10
0478/13 Cambridge IGCSE – Mark Scheme October/November
PUBLISHED 2017
Question Answer Marks
4 1 mark for each correct line up to a total of 5 marks 5
© UCLES 2017 Page 4 of 10
0478/13 Cambridge IGCSE – Mark Scheme October/November
PUBLISHED 2017
Question Answer Marks
5(a) 1 mark for each correct logic gate 4
© UCLES 2017 Page 5 of 10
0478/13 Cambridge IGCSE – Mark Scheme October/November
PUBLISHED 2017
Question Answer Marks
5(b) 1 mark for correct logic gate symbol: 5
Any four from:
– similar to an OR gate
– It has (at least) two inputs
– Output will be high/1 if both inputs are different
– Output will be high/1 if either input is high
– Output will be low/0 if both inputs are high
– Output will be low/0 if both inputs are low
Question Answer Marks
6 Any six from: 6
2D
– (Scanner) shines a light onto the surface of a document // Light moves across document
– Reflected light is captured
– Uses mirrors and lenses
– Captured image is converted into a digital file
– Produces a 2D digital image
3D
– Scanners shines a laser (or light) over the surface of a 3D object
– Records measurements of the geometry/dimensions of the object
– Measurements are converted to digital file
– Produces a 3D digital model
© UCLES 2017 Page 6 of 10
0478/13 Cambridge IGCSE – Mark Scheme October/November
PUBLISHED 2017
Question Answer Marks
7 1 mark for each correct tick 6
true false
Statement
(9) (9)
Firewalls can monitor incoming and outgoing traffic. 9
Firewalls operate by checking traffic against a set of rules. 9
Firewalls cannot block access to a certain website. 9
Firewalls can be software and hardware. 9
Firewalls can act as intermediary servers. 9
Firewalls can block unauthorised traffic. 9
Question Answer Marks
8(a) Any three from: 3
– Human error (e.g. deleting/overwriting data)
– Physical damage
– Power failure/surge
– Hardware failure
– Software crashing
8(b) Any three from: 3
– Online shopping // Online payment systems // Online booking
– Cloud based storage
– Intranet/extranet
– VPN
– VoIP // video conferencing
– Instant messaging (IM) // social networking // online gaming
© UCLES 2017 Page 7 of 10
0478/13 Cambridge IGCSE – Mark Scheme October/November
PUBLISHED 2017
Question Answer Marks
8(c) 1 mark for identifying, 1 mark for description 6
– Strong password
– To make it difficult to hack an account
– Biometric device
– To use data that is difficult to fake as a password
– TLS // Encryption
– To make data meaningless if intercepted
– To encrypt data that is exchanged (TLS only)
– More secure than SSL (TLS only)
– Anti-spyware (software)
– To find and remove any spyware that is installed on a computer
– To help stop key loggers recording key presses
– Firewall
– To help prevent unauthorised access to an account
– Blocks any requests that do not meet/match the criteria
– Authentication (card reader at home)/mobile security code app/two-step verification
– To add another level of identification of the user
– Use of drop-down boxes (or equivalent)
– So key loggers cannot record the key presses
– Proxy server
– To divert an attack away from the main system
© UCLES 2017 Page 8 of 10
0478/13 Cambridge IGCSE – Mark Scheme October/November
PUBLISHED 2017
Question Answer Marks
9(a) Any four from: 4
– (Red) laser is used
– (Laser beams) shines onto surface of the disk
– It is rotated (at a constant speed) to be read
– Surface is covered in a track (that spirals from the centre)
– Data is represented on the surface using pits and lands
– Pits and lands represent binary values
– Pits reflect light back differently (to the area in between/land)
– Optical device can determine the binary value from the light reflection
9(b) 1 mark for calculation, 1 mark for correct answer: 2
– 1000 × 16
– 16000/8
– Answer is 2000 bytes
9(c) Four from: (Max 2 for either primary or secondary) 4
– Primary RAM and ROM
– Secondary HDD and SSD
– Primary is directly accessible by CPU
– Secondary is not directly accessible by CPU
– Primary is internal to computer
– Secondary can be internal or external to the computer
– Primary stores boot up instructions and can hold data whilst being processed
– Secondary stores files/software
– Primary has faster access speed
– Secondary has a slower access speed
– Primary has both volatile and non-volatile
– Secondary is non-volatile
© UCLES 2017 Page 9 of 10
0478/13 Cambridge IGCSE – Mark Scheme October/November
PUBLISHED 2017
Question Answer Marks
10 1 mark for each correct tick 6
true false
Statement
(9) (9)
Assembly language uses mnemonic codes. 9
Assembly language programs do not need a translator to be executed. 9
Assembly language is a low-level programming language. 9
Assembly language is specific to the computer hardware. 9
Assembly language is machine code. 9
Assembly language is often used to create drivers for hardware. 9
© UCLES 2017 Page 10 of 10
You might also like
- Practical Psychic Self Defense For Home & Office (Latest Edition) (Pranic Healing)Document5 pagesPractical Psychic Self Defense For Home & Office (Latest Edition) (Pranic Healing)Sanju Satheesh50% (2)
- DBMS LAB Manual - 3136Document47 pagesDBMS LAB Manual - 3136santhoshkarthika100% (1)
- The New NormalDocument46 pagesThe New NormalMapapG100% (1)
- Cambridge Assessment International Education: Computer Science 2210/13 October/November 2017Document10 pagesCambridge Assessment International Education: Computer Science 2210/13 October/November 2017pighonNo ratings yet
- Computer ScienceDocument316 pagesComputer ScienceFSFC7477No ratings yet
- Cambridge International Examinations: This Document Consists of 11 Printed PagesDocument11 pagesCambridge International Examinations: This Document Consists of 11 Printed Pagesbkey6012No ratings yet
- Cambridge Assessment International EducationDocument8 pagesCambridge Assessment International EducationyomamathicccNo ratings yet
- Cambridge Assessment International Education: Computer Science 0478/11 October/November 2018Document12 pagesCambridge Assessment International Education: Computer Science 0478/11 October/November 2018Sol CarvajalNo ratings yet
- Cambridge International Examinations: Information and Communication Technology 0417/13 May/June 2017Document10 pagesCambridge International Examinations: Information and Communication Technology 0417/13 May/June 2017ilovefettuccineNo ratings yet
- 0417 w17 Ms 11 PDFDocument9 pages0417 w17 Ms 11 PDFMuhammad MuddassirNo ratings yet
- Cambridge International Examinations: Information and Communication Technology 0417/13 May/June 2017Document10 pagesCambridge International Examinations: Information and Communication Technology 0417/13 May/June 2017SimonaNo ratings yet
- Cambridge International AS & A Level: Computer Science 9608/31 May/June 2021Document9 pagesCambridge International AS & A Level: Computer Science 9608/31 May/June 2021Thinaya JayarathneNo ratings yet
- 1.1.2-Hexadecimal ANSWERSDocument25 pages1.1.2-Hexadecimal ANSWERSMd. Samsul Arefin ShamimNo ratings yet
- Cambridge International Examinations: Information Technology 9626/32 March 2017Document9 pagesCambridge International Examinations: Information Technology 9626/32 March 2017Mukisa BenjaminNo ratings yet
- Cambridge International Examinations: Computer Science 0478/12 March 2017Document9 pagesCambridge International Examinations: Computer Science 0478/12 March 2017Khan NurunnabiNo ratings yet
- 0417 w18 Ms 13Document10 pages0417 w18 Ms 13Moin MemonNo ratings yet
- IGCSE ICT Mark SchemeDocument10 pagesIGCSE ICT Mark Schemeanon_977221299100% (1)
- Cambridge International AS & A Level: Computer Science 9608/13 May/June 2020Document9 pagesCambridge International AS & A Level: Computer Science 9608/13 May/June 2020Zaki JrNo ratings yet
- Cambridge International Examinations Cambridge International General Certificate of Secondary EducationDocument6 pagesCambridge International Examinations Cambridge International General Certificate of Secondary EducationabdNo ratings yet
- Cambridge International Examinations Cambridge Ordinary LevelDocument10 pagesCambridge International Examinations Cambridge Ordinary LevelpighonNo ratings yet
- Cambridge International Examinations Cambridge International Advanced Subsidiary and Advanced LevelDocument10 pagesCambridge International Examinations Cambridge International Advanced Subsidiary and Advanced Level2025naldo.sNo ratings yet
- Cambridge Assessment International Education: Information and Communication Technology 0417/13 May/June 2018Document10 pagesCambridge Assessment International Education: Information and Communication Technology 0417/13 May/June 2018Thein Zaw MinNo ratings yet
- Cambridge Assessment International Education: Computer Science 9608/12 October/November 2019Document10 pagesCambridge Assessment International Education: Computer Science 9608/12 October/November 2019omerNo ratings yet
- Cambridge Assessment International Education: Computer Science 0478/12 May/June 2018Document10 pagesCambridge Assessment International Education: Computer Science 0478/12 May/June 2018NobodyNo ratings yet
- 0478 w17 Ms 22Document8 pages0478 w17 Ms 22shaliniNo ratings yet
- Cambridge International AS & A Level: Computer Science 9608/12 May/June 2020Document9 pagesCambridge International AS & A Level: Computer Science 9608/12 May/June 2020Shanbhavi ShanmugarajahNo ratings yet
- 0417 s16 Ms 11Document8 pages0417 s16 Ms 11ismat araNo ratings yet
- 1.3.5 Memory Storage Devices and Media - ANSWERSDocument30 pages1.3.5 Memory Storage Devices and Media - ANSWERSchandrshannuNo ratings yet
- Cambridge Assessment International Education: Computer Science 0478/21 October/November 2019Document8 pagesCambridge Assessment International Education: Computer Science 0478/21 October/November 2019janm23No ratings yet
- Cambridge International Examinations: Information and Communication Technology 0417/12 March 2017Document10 pagesCambridge International Examinations: Information and Communication Technology 0417/12 March 2017no oneNo ratings yet
- Bca Semester-I - 2 PDFDocument9 pagesBca Semester-I - 2 PDFThink AlienNo ratings yet
- Bca Semester-I - 2 PDFDocument9 pagesBca Semester-I - 2 PDFThink AlienNo ratings yet
- Bca Semester-I 2vvhDocument9 pagesBca Semester-I 2vvhThink AlienNo ratings yet
- Cambridge International AS & A Level: Computer Science 9608/12 May/June 2020Document9 pagesCambridge International AS & A Level: Computer Science 9608/12 May/June 2020Zaki JrNo ratings yet
- June 2021 (v1) MSDocument10 pagesJune 2021 (v1) MSDavid DavitadzeNo ratings yet
- Cambridge Assessment International EducationDocument7 pagesCambridge Assessment International EducationyomamathicccNo ratings yet
- June 2021 Mark Scheme Paper 11Document8 pagesJune 2021 Mark Scheme Paper 11Omar BilalNo ratings yet
- Cambridge Assessment International Education: Information and Communication Technology 0417/13 October/November 2017Document9 pagesCambridge Assessment International Education: Information and Communication Technology 0417/13 October/November 2017Muhammad MuddassirNo ratings yet
- 0417 w18 Ms 11Document10 pages0417 w18 Ms 11Tamer AhmedNo ratings yet
- 0417 w16 Ms 11 PDFDocument11 pages0417 w16 Ms 11 PDFAhmad BatranNo ratings yet
- Cambridge Assessment International Education: Information and Communication Technology 0417/11 May/June 2018Document10 pagesCambridge Assessment International Education: Information and Communication Technology 0417/11 May/June 2018SimonaNo ratings yet
- Cambridge Assessment International Education: English As A Second Language 0510/11 October/November 2017Document10 pagesCambridge Assessment International Education: English As A Second Language 0510/11 October/November 2017Akindamola AkinwumiNo ratings yet
- Cambridge International AS & A Level: Computer Science 9618/12Document10 pagesCambridge International AS & A Level: Computer Science 9618/12C JavaNo ratings yet
- 1.3.7 High and Low Level Languages and Their Translators ANSWERSDocument10 pages1.3.7 High and Low Level Languages and Their Translators ANSWERSPanashe ChitakunyeNo ratings yet
- Multi-Dimensional Long Short-Term Memory Networks For Artificial Arabic Text Recognition in News VideoDocument10 pagesMulti-Dimensional Long Short-Term Memory Networks For Artificial Arabic Text Recognition in News VideoFatih KüçükNo ratings yet
- 9618 s22 Ms 12 PDFDocument9 pages9618 s22 Ms 12 PDFSunnatbek Meliqo'ziyevNo ratings yet
- 0417 m17 Ms 12Document10 pages0417 m17 Ms 12Mohammed MaGdyNo ratings yet
- Cambridge International Examinations: Information Technology 9626/11 May/June 2017Document9 pagesCambridge International Examinations: Information Technology 9626/11 May/June 2017uma9sathiyakailashNo ratings yet
- 0417 w18 Ms 11Document10 pages0417 w18 Ms 11salimNo ratings yet
- Cambridge IGCSE™: Computer Science 0478/13 October/November 2021Document8 pagesCambridge IGCSE™: Computer Science 0478/13 October/November 2021sorixo9693No ratings yet
- 0478 m17 Ms 22Document5 pages0478 m17 Ms 22M.Hassan Bin AdeelNo ratings yet
- Cambridge International AS & A Level: Computer Science 9608/22 October/November 2021Document19 pagesCambridge International AS & A Level: Computer Science 9608/22 October/November 2021Lavanya GoleNo ratings yet
- Cambridge IGCSE™: Computer Science 0478/12 October/November 2020Document13 pagesCambridge IGCSE™: Computer Science 0478/12 October/November 2020boyredbisonNo ratings yet
- Cambridge International Examinations Cambridge Ordinary LevelDocument6 pagesCambridge International Examinations Cambridge Ordinary LevelhassanNo ratings yet
- 2210 s17 Ms 11Document8 pages2210 s17 Ms 11Muhammad UmarNo ratings yet
- 0417 m17 QP 12Document16 pages0417 m17 QP 12Mohammed MaGdyNo ratings yet
- Var 1 MSDocument10 pagesVar 1 MSamouryh2019No ratings yet
- Cambridge International AS & A Level: Computer Science 9618/13 May/June 2022Document10 pagesCambridge International AS & A Level: Computer Science 9618/13 May/June 2022sunita mungrooNo ratings yet
- The Self Assessment Report (SAR) As Part of The Accreditation ProcessDocument20 pagesThe Self Assessment Report (SAR) As Part of The Accreditation ProcessluqmanfNo ratings yet
- Cambridge IGCSE™: Information & Communication Technology 0417/12 October/November 2021Document9 pagesCambridge IGCSE™: Information & Communication Technology 0417/12 October/November 2021EffNo ratings yet
- Cambridge International AS & A Level: Computer Science 9618/33Document9 pagesCambridge International AS & A Level: Computer Science 9618/33Abiral ManandharNo ratings yet
- Mad ct2 Part 1 PDFDocument40 pagesMad ct2 Part 1 PDF550-Shivendra TiwariNo ratings yet
- User Manual For New Firmware of The 3/3.5-Inch Color Screen: Date: April 2013Document63 pagesUser Manual For New Firmware of The 3/3.5-Inch Color Screen: Date: April 2013Denny De Leon LaurencioNo ratings yet
- Outgoing Call in RoamingDocument11 pagesOutgoing Call in RoamingPrince GargNo ratings yet
- Big Data in FintechDocument21 pagesBig Data in Fintechakanksha_ambitionNo ratings yet
- Technical Doc Tristar Modbus Specification enDocument30 pagesTechnical Doc Tristar Modbus Specification enAnita FelixNo ratings yet
- MainDocument260 pagesMainapi-3726429No ratings yet
- PhilHealth ContributionsDocument19 pagesPhilHealth ContributionsRocelle IndicoNo ratings yet
- Workflow API Reference Guide PDFDocument340 pagesWorkflow API Reference Guide PDFRaghugovindNo ratings yet
- ST60 Digital Instruments Service ManualDocument36 pagesST60 Digital Instruments Service ManualLeandro ClericiNo ratings yet
- Z002E3ST ECardDocument3 pagesZ002E3ST ECardtechbhaskarNo ratings yet
- JolliCube LEDDocument18 pagesJolliCube LEDBobbyNo ratings yet
- Connect More Process Tips MBDocument31 pagesConnect More Process Tips MBRicardo PereiraNo ratings yet
- MCQ RefDocument4 pagesMCQ Refsatish.mali100% (1)
- TB194.LISRelease of LIS-Link 2.01Document4 pagesTB194.LISRelease of LIS-Link 2.01Peter KohlscheinNo ratings yet
- Apple HistoryDocument4 pagesApple HistoryAronAbadillaNo ratings yet
- International Journal of Disaster Risk ScienceDocument2 pagesInternational Journal of Disaster Risk ScienceMichael PadillaNo ratings yet
- Organux VST VST3 Audio Unit: Antique, Classic, Vintage and Modern Organs. Cathedral, Church, Baroque, Pump Reed, Harmonium, VOX, Farfisa, B3, Elka Panther EXS24 + KONTAKTDocument10 pagesOrganux VST VST3 Audio Unit: Antique, Classic, Vintage and Modern Organs. Cathedral, Church, Baroque, Pump Reed, Harmonium, VOX, Farfisa, B3, Elka Panther EXS24 + KONTAKTSyntheway Virtual Musical InstrumentsNo ratings yet
- TCS Company HistoryDocument22 pagesTCS Company HistoryManiraj Vignesh RNo ratings yet
- GTMaritime GTRAFT Brochure DigitalDocument4 pagesGTMaritime GTRAFT Brochure Digitalchen wansinNo ratings yet
- Apogee 7 Basic Tutorial enDocument170 pagesApogee 7 Basic Tutorial enMouse_L100% (1)
- SQL Group by ClauseDocument2 pagesSQL Group by ClausenellutlaramyaNo ratings yet
- "2003" Seminar Information: Volkswagen / AudiDocument7 pages"2003" Seminar Information: Volkswagen / AudiGina LópezNo ratings yet
- Legal Aspects of Cloud Security: Richard KempDocument5 pagesLegal Aspects of Cloud Security: Richard KempNéstor ZevallosNo ratings yet
- Tech Topic Local Remote Switch 525 1 PDFDocument2 pagesTech Topic Local Remote Switch 525 1 PDFkotrex_tre3No ratings yet
- Tunnel SafetyDocument77 pagesTunnel SafetyTobin Don0% (1)
- Hawkins - Complaint (JBR + MWL Edits)Document12 pagesHawkins - Complaint (JBR + MWL Edits)WXYZ-TV Channel 7 DetroitNo ratings yet
- Submit Your Application inDocument5 pagesSubmit Your Application inRakib AhasanNo ratings yet
- Effect of Temp PV - Lab 5 PDFDocument7 pagesEffect of Temp PV - Lab 5 PDFHumayun ArshadNo ratings yet