Professional Documents
Culture Documents
Lab 5.4.1 Implementing EIGRP
Lab 5.4.1 Implementing EIGRP
Uploaded by
Ajith PathiranaOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Lab 5.4.1 Implementing EIGRP
Lab 5.4.1 Implementing EIGRP
Uploaded by
Ajith PathiranaCopyright:
Available Formats
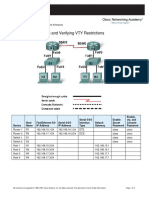
CCNA Discovery Introducing Routing and Switching in the Enterprise
Lab 5.4.1 Implementing EIGRP
Device
Router1
Host Name
Gateway
Loopback Interfaces / Subnet Masks
N/A Lo0 172.16.0.1/24 Lo1 172.16.1.1/24 Lo2 172.16.2.1/24 Lo3 172.16.3.1/24 Lo0 172.17.0.1/24 Lo1 172.17.1.1/24 Lo2 172.17.2.1/24 Lo3 172.17.3.1/24
Interface S0/0/0 / Subnet Mask
10.0.0.1/30
Serial Interface Type
DCE
Interface S0/0/1 / Subnet Mask
10.0.0.5/30
Serial Interface Type
DCE
Enable Secret Password
class
vty, Console Password
cisco
Router2
Branch1
10.0.0.2/30
DTE
10.0.0.9/30
DCE
class
cisco
Router3
Branch2
10.0.0.6/30
DTE
10.0.0.10/30
DTE
class
cisco
All contents are Copyright 19922007 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information.
Page 1 of 4
CCNA Discovery Introducing Routing and Switching in the Enterprise
Objectives
Configure a three-router topology with EIGRP and MD5 authentication. Verify EIGRP configuration and route table population.
Background / Preparation
This lab presents a three router corporate network using variably subnetted private IP addressing. On Branch1and Branch2, loopback interfaces simulate LANs attached to those routers. The design creates discontiguous subnets on the routers which will be "hidden" when EIGRP is configured with automatic summarization as the default. You will enable EIGRP MD5 authentication to protect your routing updates. The following resources are required: Three Cisco 1841 routers or comparable routers At least one PC with a terminal emulation program At least one RJ-45-to-DB-9 connector console cable Three serial cables to connect R1 to both R2 and R3, and to connect R2 to R3 NOTE: Make sure that the routers and the switches have been erased and have no startup configurations. Instructions for erasing both switch and router are provided in the Lab Manual, located on Academy Connection in the Tools section. NOTE: SDM Enabled Routers If the startup-config is erased in an SDM enabled router, SDM will no longer come up by default when the router is restarted. It will be necessary to build a basic router configuration using IOS commands. The steps provided in this lab use IOS commands and do not require the use of SDM. If you wish to use SDM, refer to the instructions in the Lab Manual, located on the Academy Connection in the Tools section or contact your instructor if necessary.
Step 1: Connect the equipment
a. Connect Router1 to Router2 and Router3 using serial cables. b. Connect Router2 to Router3 using serial cables. c. Connect a PC with a console cable to perform configurations on the routers.
Step 2: Perform basic configurations on the routers
a. Establish a console session with Router1 and configure hostname, passwords, and interfaces as described in the table. Save the configuration. b. Establish a console session with Router2 and perform a similar configuration, using the addresses and other information from the table. Save the configuration. c. Establish a console session with Router3. Configure hostname, passwords, and interfaces according to the table. Save the configuration.
Step 3: Configure EIGRP routing with default commands
a. On Gateway, configure EIGRP as the routing protocol with an autonomous system number of 100, and advertise the appropriate networks. Gateway(config)#router eigrp 100 Gateway(config-router)#network 10.0.0.0 Gateway(config-router)#network 10.0.0.4
All contents are Copyright 19922007 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information.
Page 2 of 4
CCNA Discovery Introducing Routing and Switching in the Enterprise
Predict: How will EIGRP report these subnets in the routing table? _______________________________________________________________________________ _______________________________________________________________________________ b. On Branch1, configure EIGRP as the routing protocol with an autonomous system number of 100, and advertise the appropriate networks: Branch1(config)#router eigrp 100 Branch1(config-router)#network 10.0.0.0 Branch1(config-router)#network 10.0.0.8 Branch1(config-router)#network 172.16.0.0 Branch1(config-router)#network 172.16.1.0 Branch1(config-router)#network 172.16.2.0 Branch1(config-router)#network 172.16.3.0 c. Perform a similar configuration on Branch2, using EIGRP 100 and advertising the appropriate networks.
Step 4: Configure MD5 Authentication a. Create a keychain named discchain. b. Configure a key 1 that has a key string of san-fran. c. Enable the Branch1 router to utilize EIGRP MD5 authentication with each of the EIGRP neighbors and to use the keychain discchain.
Branch1(config)#key chain discchain Branch1(config-keychain)#key 1 Branch1(config-keychain-key)#key-string san-fran Branch1(config-keychain-key)#end Branch1#configure terminal Branch1(config)#interface serial 0/0/0 Branch1(config-if)#ip authentication mode eigrp 100 md5 Branch1(config-if)#ip authentication key-chain eigrp 100 discchain Branch1(config-if)#exit Branch1(config)#interface serial 0/0/1 Branch1(config-if)#ip authentication mode eigrp 100 md5 Branch1(config-if)#ip authentication key-chain eigrp 100 discchain
d. Repeat the MD5 authentication configuration for the Branch2 and Gateway routers. e. View the contents of the Gateway, Branch1, and Branch2 routing tables to ensure all routing updates are still being accepted.
Gateway#show ip route List the routes that are shown: _______________________________________________________________________________ _______________________________________________________________________________ _______________________________________________________________________________ _______________________________________________________________________________
All contents are Copyright 19922007 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information.
Page 3 of 4
CCNA Discovery Introducing Routing and Switching in the Enterprise
Step 5: Reflection
a. What is the importance of enabling authentication on the routing updates? _______________________________________________________________________________ _______________________________________________________________________________ _______________________________________________________________________________
All contents are Copyright 19922007 Cisco Systems, Inc. All rights reserved. This document is Cisco Public Information.
Page 4 of 4
You might also like
- 6.2.3.8 Lab - Configuring Multiarea OSPFv2 - ILM PDFDocument23 pages6.2.3.8 Lab - Configuring Multiarea OSPFv2 - ILM PDFMaksim Korsakov98% (51)
- PLC Programming from Novice to Professional: Learn PLC Programming with Training VideosFrom EverandPLC Programming from Novice to Professional: Learn PLC Programming with Training VideosRating: 5 out of 5 stars5/5 (1)
- SUITPlus Protocol Description v4.0Document58 pagesSUITPlus Protocol Description v4.0amr sabry100% (1)
- Cisco CCNA Command Guide: An Introductory Guide for CCNA & Computer Networking Beginners: Computer Networking, #3From EverandCisco CCNA Command Guide: An Introductory Guide for CCNA & Computer Networking Beginners: Computer Networking, #3No ratings yet
- 9.2.2.7 Lab - Configuring and Verifying Standard ACLs - ILMDocument18 pages9.2.2.7 Lab - Configuring and Verifying Standard ACLs - ILMJohann Neethling72% (18)
- 3.4.1.5 Lab - Troubleshooting Basic PPP With AuthenticationDocument8 pages3.4.1.5 Lab - Troubleshooting Basic PPP With AuthenticationLarry Abisaí17% (6)
- Lab 2.3.2 Configuring OSPF With Loopback Addresses: ObjectiveDocument8 pagesLab 2.3.2 Configuring OSPF With Loopback Addresses: ObjectivepitR2d2No ratings yet
- 6.5.1.2 Lab - Building A Switch and Router Network - Isaiah WhitenerDocument6 pages6.5.1.2 Lab - Building A Switch and Router Network - Isaiah WhitenerSpectre EtherealNo ratings yet
- Lab 6.2.2 Configuring OSPF Authentication: CCNA Discovery Introducing Routing and Switching in The EnterpriseDocument4 pagesLab 6.2.2 Configuring OSPF Authentication: CCNA Discovery Introducing Routing and Switching in The Enterprisemohammad_shahzad_iiuiNo ratings yet
- OSPF Route SummarizationDocument5 pagesOSPF Route SummarizationrupeshNo ratings yet
- Lab 3.2.5 Configuring Message-of-the-Day (MOTD) : Background/PreparationDocument4 pagesLab 3.2.5 Configuring Message-of-the-Day (MOTD) : Background/PreparationHamzaSpahijaNo ratings yet
- Lab 2.3.2 Configuring OSPF With Loopback Addresses: ObjectiveDocument8 pagesLab 2.3.2 Configuring OSPF With Loopback Addresses: ObjectiveAdityo Prabhaswara HaryantoNo ratings yet
- Lab 4 - Configuring Multi-Area OSPFv2Document7 pagesLab 4 - Configuring Multi-Area OSPFv2Alex TienNo ratings yet
- 6.4.3.5 Lab - Building A Switch and Router NetworkDocument6 pages6.4.3.5 Lab - Building A Switch and Router NetworkKennetGONo ratings yet
- Lab 11.2.1a Configuring Standard Access Lists: ObjectiveDocument45 pagesLab 11.2.1a Configuring Standard Access Lists: ObjectivetieuphapsNo ratings yet
- Lab 2 Configuring Basic Routing and Switching PDFDocument11 pagesLab 2 Configuring Basic Routing and Switching PDFDennis Masuku MacfeeNo ratings yet
- A Lab1acceslistDocument5 pagesA Lab1acceslistveracespedesNo ratings yet
- Week 6 Lab - Configuring IPv4 Static and Default RoutesDocument7 pagesWeek 6 Lab - Configuring IPv4 Static and Default RoutesAhmedNo ratings yet
- Lab 5.2.3 Configuring Ripv2 With VLSM, and Default Route PropagationDocument4 pagesLab 5.2.3 Configuring Ripv2 With VLSM, and Default Route Propagationmohammad_shahzad_iiuiNo ratings yet
- Lab 4 1 6Document6 pagesLab 4 1 6HamzaSpahijaNo ratings yet
- 7.2.2.5 Lab - Configuring Basic EIGRP For IPv4 - ILM PDFDocument16 pages7.2.2.5 Lab - Configuring Basic EIGRP For IPv4 - ILM PDFMaksim Korsakov97% (35)
- Lab 6.3.1 Configuring and Propagating An OSPF Default RouteDocument5 pagesLab 6.3.1 Configuring and Propagating An OSPF Default Routemohammad_shahzad_iiuiNo ratings yet
- Add Devices and Connect Cables Configure Pcs Configure R1 Configure R2 Save The Packet Tracer FileDocument12 pagesAdd Devices and Connect Cables Configure Pcs Configure R1 Configure R2 Save The Packet Tracer FileMeme222No ratings yet
- 3.3.2.8 Lab - Configuring Basic PPP With AuthenticationDocument17 pages3.3.2.8 Lab - Configuring Basic PPP With AuthenticationLarry Abisaí0% (2)
- Lab 1.2.5 Verifying RIP v2 Configuration: ObjectiveDocument7 pagesLab 1.2.5 Verifying RIP v2 Configuration: ObjectiveHà TrầnNo ratings yet
- Lab 3.2.3 Verifying Basic EIGRP Configuration: ObjectiveDocument6 pagesLab 3.2.3 Verifying Basic EIGRP Configuration: Objectivevf3nixNo ratings yet
- Lab 3.1 - Configuring and Verifying Standard ACLsDocument9 pagesLab 3.1 - Configuring and Verifying Standard ACLsRas Abel BekeleNo ratings yet
- Lab For Extended AclsDocument5 pagesLab For Extended Aclscasilan_90No ratings yet
- Lab 2.3.5 Configuring Basic Routing and SwitchingDocument12 pagesLab 2.3.5 Configuring Basic Routing and SwitchingPanic Teuku Ryan Francis100% (1)
- LabDocument11 pagesLableonora KrasniqiNo ratings yet
- E2 Lab 5 6 3 InstructorDocument12 pagesE2 Lab 5 6 3 InstructorDayana VelasquezNo ratings yet
- Lab 4.2.6 Troubleshooting IP Address Issues: ObjectiveDocument4 pagesLab 4.2.6 Troubleshooting IP Address Issues: ObjectiveHamzaSpahijaNo ratings yet
- Switching LabDocument17 pagesSwitching LabGabby100% (1)
- 4.3.1.6 Lab - Troubleshooting Basic Frame RelayDocument6 pages4.3.1.6 Lab - Troubleshooting Basic Frame Relayzadeli6381No ratings yet
- Data Com TestDocument11 pagesData Com Testkinabapaul49No ratings yet
- Le Quang Vu - SE160967 - Lab 1Document12 pagesLe Quang Vu - SE160967 - Lab 1Le Quang Vu (K16HCM)No ratings yet
- Configuring and Verifying VTY RestrictionsDocument4 pagesConfiguring and Verifying VTY RestrictionsAnatoli ParhinNo ratings yet
- E1 LAB 11-5-1 SolutionDocument20 pagesE1 LAB 11-5-1 SolutionChris GirouardNo ratings yet
- Lab 1.5.2: Basic Router Configuration: (Instructor Version)Document9 pagesLab 1.5.2: Basic Router Configuration: (Instructor Version)abu abo100% (1)
- Lab 8.3.4 Planning, Configuring and Verifying Extended AclsDocument5 pagesLab 8.3.4 Planning, Configuring and Verifying Extended AclsFery ArdiansyahNo ratings yet
- Lab 3.2.1 Configuring EIGRP Routing: ObjectiveDocument5 pagesLab 3.2.1 Configuring EIGRP Routing: ObjectiveguijjouNo ratings yet
- Module4 (LAB) - Serial ConfigurationDocument15 pagesModule4 (LAB) - Serial ConfigurationJoyce Ann Rufino100% (1)
- 5.1.2.13 Lab - Configuring OSPFv2 On A Multiaccess Network - ILM PDFDocument13 pages5.1.2.13 Lab - Configuring OSPFv2 On A Multiaccess Network - ILM PDFMaksim Korsakov95% (20)
- CCNA2 Lab Inst 3 1 5 enDocument18 pagesCCNA2 Lab Inst 3 1 5 enblahblah2331No ratings yet
- CCNA2 Lab 7 2 7 enDocument6 pagesCCNA2 Lab 7 2 7 enapi-3809703No ratings yet
- Lab 6-1-6Document6 pagesLab 6-1-6Chullachat_Chu_1486No ratings yet
- 5.1.3.7 Lab - Configuring 802.1Q Trunk-Based Inter-VLAN RoutingDocument7 pages5.1.3.7 Lab - Configuring 802.1Q Trunk-Based Inter-VLAN RoutingJochemJochem0% (2)
- 05 - Raziq - w1 - Configuring Basic Router Settings With IOS CLIDocument9 pages05 - Raziq - w1 - Configuring Basic Router Settings With IOS CLIrazqkimi2022No ratings yet
- Lab4-4.1.4.6 - Configuring Basic Router SettingsDocument19 pagesLab4-4.1.4.6 - Configuring Basic Router SettingsAdmiral210% (2)
- Lab 5.6.2: Advanced RIP Configuration: Topology DiagramDocument7 pagesLab 5.6.2: Advanced RIP Configuration: Topology DiagramPaintMeAnEpicNo ratings yet
- Laporan Praktik Lab 2 - Securing The Router For Administrative Access - CompressedDocument57 pagesLaporan Praktik Lab 2 - Securing The Router For Administrative Access - CompressedRizky RismadhantiNo ratings yet
- Lab 3.2.5 Configuring Message-of-the-Day (MOTD) : Background/PreparationDocument4 pagesLab 3.2.5 Configuring Message-of-the-Day (MOTD) : Background/PreparationNawaz Ali100% (2)
- CISCO PACKET TRACER LABS: Best practice of configuring or troubleshooting NetworkFrom EverandCISCO PACKET TRACER LABS: Best practice of configuring or troubleshooting NetworkNo ratings yet
- CompTIA A+ Complete Review Guide: Core 1 Exam 220-1101 and Core 2 Exam 220-1102From EverandCompTIA A+ Complete Review Guide: Core 1 Exam 220-1101 and Core 2 Exam 220-1102Rating: 5 out of 5 stars5/5 (2)
- Network with Practical Labs Configuration: Step by Step configuration of Router and Switch configurationFrom EverandNetwork with Practical Labs Configuration: Step by Step configuration of Router and Switch configurationNo ratings yet
- WAN TECHNOLOGY FRAME-RELAY: An Expert's Handbook of Navigating Frame Relay NetworksFrom EverandWAN TECHNOLOGY FRAME-RELAY: An Expert's Handbook of Navigating Frame Relay NetworksNo ratings yet
- C Programming for the Pc the Mac and the Arduino Microcontroller SystemFrom EverandC Programming for the Pc the Mac and the Arduino Microcontroller SystemNo ratings yet
- Cisco Packet Tracer Implementation: Building and Configuring Networks: 1, #1From EverandCisco Packet Tracer Implementation: Building and Configuring Networks: 1, #1No ratings yet
- PLC: Programmable Logic Controller – Arktika.: EXPERIMENTAL PRODUCT BASED ON CPLD.From EverandPLC: Programmable Logic Controller – Arktika.: EXPERIMENTAL PRODUCT BASED ON CPLD.No ratings yet
- Mail Scanner - Community Ubuntu DocumentationDocument4 pagesMail Scanner - Community Ubuntu DocumentationAjith PathiranaNo ratings yet
- Sun Ray Enterprise Server Software 1.1 Advanced Administrator's GuideDocument66 pagesSun Ray Enterprise Server Software 1.1 Advanced Administrator's GuideAjith PathiranaNo ratings yet
- Network Security and PrivacyDocument8 pagesNetwork Security and PrivacyAjith PathiranaNo ratings yet
- By: Anung Muhandanu: Redhat Install Tutorial Step by StepDocument13 pagesBy: Anung Muhandanu: Redhat Install Tutorial Step by StepAjith PathiranaNo ratings yet
- RTN 950 Configuration GuideDocument1,722 pagesRTN 950 Configuration GuideWilliam Fernandes100% (2)
- PHD Thesis KLLDocument209 pagesPHD Thesis KLLdeltakio@gmail.comNo ratings yet
- OpenVox WGW1002G User ManualDocument63 pagesOpenVox WGW1002G User Manualmaple4VOIPNo ratings yet
- TL SF1008P DatasheetDocument2 pagesTL SF1008P DatasheetChristian GonzalezNo ratings yet
- Cisco ASA 5585Document8 pagesCisco ASA 5585Iwene IsraaNo ratings yet
- Data and Computer Communications: - Protocol Architecture, TCP/IP, and Internet-Based ApplicationsDocument34 pagesData and Computer Communications: - Protocol Architecture, TCP/IP, and Internet-Based ApplicationscilentNo ratings yet
- 10 NetworkDocument38 pages10 Networkapi-371092170No ratings yet
- ZXUN USPP Installation and Commissioning-Data Planning - 39Document39 pagesZXUN USPP Installation and Commissioning-Data Planning - 39kaijage kishekyaNo ratings yet
- Cisco Press Troubleshooting Ip Routing Protocols May 2002Document861 pagesCisco Press Troubleshooting Ip Routing Protocols May 2002LjubišaBrajović100% (3)
- Siebel InstallDocument3 pagesSiebel Installgrkayyappa001No ratings yet
- Perdition LdapDocument5 pagesPerdition LdapEdward Callao CortezNo ratings yet
- Iot-Book - Unit 2Document46 pagesIot-Book - Unit 2MOHIT DEO (RA2112009010004)No ratings yet
- Routing Inter Vlan - Svi - DHCPDocument20 pagesRouting Inter Vlan - Svi - DHCPĐinh TúNo ratings yet
- Fortigate 600c - Fix SSLv3 Vulnerability On FirewallDocument1 pageFortigate 600c - Fix SSLv3 Vulnerability On FirewallSerge PallaNo ratings yet
- Security Issues of Network Mobility (NEMO) With Tor ArchitectureDocument5 pagesSecurity Issues of Network Mobility (NEMO) With Tor ArchitectureUIJRT United International Journal for Research & TechnologyNo ratings yet
- SD5A445GB-HNR S0 Datasheet-20240305Document4 pagesSD5A445GB-HNR S0 Datasheet-20240305sistemasNo ratings yet
- GGC InstallationDocument46 pagesGGC InstallationWe3 NetworkNo ratings yet
- Nurul Azizah - P27838123085 - P.16 DHT22Document14 pagesNurul Azizah - P27838123085 - P.16 DHT22Nurul AzizahNo ratings yet
- Alpeta Install QuickGuide (English)Document15 pagesAlpeta Install QuickGuide (English)kalkumarmNo ratings yet
- Access The Server Using An SSH TunnelDocument3 pagesAccess The Server Using An SSH Tunnelleonard1971No ratings yet
- SMS Call Flow - BasicDocument3 pagesSMS Call Flow - BasicarunmathewleoNo ratings yet
- Lab2 Socket ProgrammingDocument9 pagesLab2 Socket Programminghussamnasser146No ratings yet
- Intro To IT by Peter Norton, MacGraw Hills Chap 07ADocument47 pagesIntro To IT by Peter Norton, MacGraw Hills Chap 07AMurtaza MoizNo ratings yet
- Cell-Outage-Analysis (RCA) - Procedure - vRANDocument47 pagesCell-Outage-Analysis (RCA) - Procedure - vRANaslam_326580186No ratings yet
- TOS-for-Grade 10 010519Document1 pageTOS-for-Grade 10 010519Jonathan CayatNo ratings yet
- ISS - FirewallDocument10 pagesISS - FirewallgferantaNo ratings yet
- Load Balanced ProxySQL in Google CloudDocument2 pagesLoad Balanced ProxySQL in Google Cloudtsultim bhutiaNo ratings yet
- DVR and NVR Network SetupDocument7 pagesDVR and NVR Network SetupVebry AndrianNo ratings yet
- Free Guide MQTT RilhevaDocument6 pagesFree Guide MQTT RilhevajeliasNo ratings yet