Professional Documents
Culture Documents
Computer Intrusions and Attacks
Computer Intrusions and Attacks
Uploaded by
John GacheruOriginal Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Computer Intrusions and Attacks
Computer Intrusions and Attacks
Uploaded by
John GacheruCopyright:
Available Formats
Computer intrusions and attacks TECHNOLOGY
Many library computers are now connected to each other through networks and to the rest of the world CORNER
through the Internet. Current information of unprecedented scope and scale is now available on the com-
puter screen. There is, however, a dark side to all this computer interconnectivity, since it increases the pos-
sibility of deliberate unsolicited intrusion into library computers.
When such an intrusion occurs, it may come in the form of a computer virus playfully invented by some
computer hacker, or it may come as an uninvited e-mail message from an eager online salesman. There are
even some spiteful, vengeful, paranoid attackers who aim to cause destruction. Some intrusions can dam-
age valuable computer-stored information; others may simply divert the attention of a computer user.
Protective measures should be taken to avoid some intrusions; others can simply be ignored. In this article,
we take a look at some frequently encountered computer intrusions.
1. Viruses Infected disks contain an invisible application file in
their root directory. When the infected disk is
A computer virus is a computer program that can mounted on a suitable MAC system, the worm is
reproduce itself and may cause undesired effects in automatically launched. It then copies itself to the
computers where it is active. For example, a virus extensions folder of the active system and changes
may simply pop up a window containing unkind the name of the copy to ‘Desktop Print Spooler’.
words, or it may destroy files stored on the comput- The worm file is invisible, and when running is not
er’s hard drive. shown in the applications menu.
To do its malevolent work, the virus program has to The AutoStart worm is able to corrupt certain
run (execute its code). Usually viruses are located graphic files. It is intentionally destructive, overwrit-
together with other code that is likely to be execut- ing portions of the files with random data. This dam-
ed. For example, the virus could be placed in a disk age is not repairable, so the files must be reinstalled
with code that must be executed whenever the disk or restored from a backup. The response of
is started up. When the disk code is executed, the antivirus vendors to this worm has been reasonably
virus is also activated. rapid. Nevertheless, the worm has created serious
problems even without unleashing its full destruc-
A virus may also be attached to a macro. Macros tiveness. In 1998-99, several companies that use
are programs that can be executed in word proces- MACs for graphic applications in the St Louis area
sors, spreadsheets and other packages whenever a spent thousands of dollars to clean out the
document is opened. When a word processing doc- AutoStart worm.
ument infected with a macro virus is received and
opened, the infection can immediately affect not
only word processing at that computer, but also the 3. Java applications
operation of the entire system. As long as the virus
is active on the computer, it can copy itself to other Java is a computer language designed to run on vir-
files or disks when they are used. tually any computer. You may have heard that pro-
grams called applets, written in the Java language,
Viruses are frequently spread via floppy disks or cannot be used to spread viruses. That appears to
other media that users can exchange, or in software be true. However, in addition to applets, the Java
obtained from untrustworthy sources. Although it is language can also be used to write application pro-
impossible for a virus to exist in normal e-mail text, grams and these can carry virus infection. For
viruses can be spread via e-mail because the virus example, when a Java application program infected
can be carried in a file attached to the e-mail, and with a virus known as Strange Brew is run, it looks
the virus spreads when the file is opened. for other, uninfected Java files in the computer’s
directory. The virus then copies itself into these files,
modifying them so that, when they are run, the virus
2. Worms will take control. This virus can cause damage to
some of the files it infects so that they no longer run
A worm is a type of virus that does not change any properly.
existing program or file to spread itself. Instead, it
makes copies of itself within an infected computer
and spreads to become active on other systems. The 4. Trojan horses
latest example of a widespread worm is AutoStart
9805, which affects certain types of MAC computers. Sometimes called vandals, trojan horses are pieces
This particular worm can be transmitted via almost of computer code that may be downloaded to a
any disk, including floppy disks, most removable car- computer while Internet sites are being accessed.
tridge drives, hard disks, and even disk images. The The code may be in the portable Java computer
worm also spreads across networks. language or in the equally portable Microsoft
The Electronic Library, Vol. 17, No. 2, April 1999 115
ActiveX language. It may be harmless, but it could WhoWhere, American Directory Assistance, Bigfoot,
possibly delete an important file from the computer, Internet Address Finder, SearchAmerica,
TECHNOLOGY plant a harmful virus, or even steal users’ pass- Switchboard and World Email Directory. These ser-
CORNER words. Unlike viruses and worms, a Trojan horse vices will remove your e-mail address if you request
cannot replicate itself. them to do so. However, if your organisation wants to
encourage e-mail contact with colleagues and
Several hundred trojan horses are believed to cur- patrons, it may be more important to advertise the e-
rently be in circulation, and the number of trojan mail address as widely as possible than to conceal it.
horses capable of stealing passwords appears to
be increasing. When an e-mail password is stolen, Software that offers some defence against e-mail
the attacker can send out e-mail as if it came from spamming is available. For example, the Novasoft
the victim. This makes all sorts of fraudulent SpamKiller package ($30 from
schemes possible. www.spamkiller.com) comes with a list of 3000
spam sources that it screens from incoming e-mail.
Trojan horses are often sent out as part of programs The vendor adds new sources to the list via the
that Internet users download in hopes of getting Internet without charge.
better access, free access time, or enhancements
for viewing online services. Trojan horses may also By the way, you may want to take care not to
be distributed with e-mail. Another distribution become an inadvertent spammer yourself. That can
method is to embed a trojan horse in a word pro- happen if you get in the habit of circulating chain
cessing file. When the user opens one of these files, letters, or of overusing the ‘reply to all’ option of
the trojan horse enters the user’s computer system. your own e-mail service.
Once inside a computer the trojan horse can access
passwords, screen names and other personal infor-
mation and then distribute this confidential data to 6. Hoaxes
the attacker. This kind of attack can be prevented
by avoiding any use of programs from untrusted or Of the tens of millions of computer users who use
unknown sources. Programs that have been posted the Internet, many are novices who have little
to an Internet newsgroup are particularly risky. knowledge of computers, networks or software and
are vulnerable to unfounded hoax rumours.
Increasing numbers of virus hoaxes are propagating
5. E-mail spamming across the Internet. Hoaxes have become so com-
mon that users are more likely to bothered by these
Spam is unsolicited and unwanted e-mail. It is the false rumours than by actual viruses.
Internet equivalent of junk mail. Some e-mail ser-
vices use filters to screen out spam. These services A hoax is typically propagated through a phoney e-
try to keep track of active spammers’ addresses mail message that warns of a virus that can accom-
and then exclude any mail from those addresses. pany e-mail messages and will cause damage to
This is never fully effective because recalcitrant recipients’ computers. The message urges users to
spammers continue to find new ways to evade forward the warning to all their friends and col-
these filters, and new spammers are constantly leagues. In fact, this virus does not exist. However,
appearing. the hoax message can take on virus-like character-
istics as it spreads from user to user via e-mail.
If your organisation is using e-mail, and the amount
of spam received becomes a problem, there are Remember, the only way it is possible for viruses to
some steps that can be taken to minimise the spam. spread via e-mail messages is through files
For example, you can send polite e-mail asking the attached to the e-mail, not through the messages
spammers to remove you from their e-mailing lists. themselves. However, any real viruses are far out-
If that doesn’t work, try sending e-mail to the numbered by the growing number of hoax warn-
Internet Service Provider the spammers are using. ings.
Thus, if the spam comes from mrspammer@the-
mall.net, try sending a polite complaint to
abuse@themall.net. Unfortunately, spammers don’t 7. Cookies
always give their actual return e-mail address.
A cookie is a small text file that may be placed in a
There are some e-mail practices that tend to invite computer when an Internet site is contacted. The
spamming. For example, spammers often raid mail- ostensible purpose of a cookie is to facilitate com-
ing lists to obtain e-mail addresses for new victims. If munications between the computer and the Internet
you or your organisation are on any mailing lists, and site. Thus, a cookie may be used to record items
you are experiencing spamming problems, contact put into a shopping cart at an Internet shopping
the list keepers and inform them of the problem. site, or it may be used to keep track of user prefer-
Remind the list keepers that lists may be kept private ences at a site that offers choices such as location
or public, but only the public lists can be easily raid- of weather information.
ed for addresses. To avoid spam, give your e-mail
address only to those who need to use it. Keep the Internet browsers can be easily set to refuse cookies,
address out of Internet directories like Four11, or to notify the user before each cookie is accepted.
116 The Electronic Library, Vol. 17, No. 2, April 1999
However, if cookies are refused, users may find it 100% of the viruses currently known to be publicly
inconvenient to fully access certain sites, and it can circulating.
be quite annoying to be confronted with cookie noti- TECHNOLOGY
fication displays while surfing the Internet. New viruses appear all the time and the only way to CORNER
protect against them is to keep your antivirus soft-
Cookies can be used to collect information on how ware up-to-date. Fortunately, most antivirus pack-
individuals use their computers. For example, cook- age vendors maintain Web sites from which their
ies can record an audit trail of the Internet sites users can download free antivirus updates. Some
accessed by a computer. Cookies can be used to packages also offer e-mail notification to users
direct advertising to likely consumers. They can whenever they are recommending updates.
also be used to collect personal information on indi-
vidual users by keeping and interpreting records of 9.1. Network antivirus software
Internet use, and later matching this data to existing
public and private database information on the indi- When individual computers are protected by
viduals. Information items such as name, address, antivirus software, a separate software package
phone number, health, salary, eating habits and must be purchased for each computer. However,
mortgage status have been gleaned in this manner. when computers are connected by a local network,
it is possible to purchase network antivirus software
that will protect every computer in the network.
8. How much intrusion protection is
needed? When only a few computers are involved, it is prob-
ably most sensible to purchase an individual
E-mail spamming and hoaxes can be annoying and antivirus package for each machine. Single-com-
time-wasting, but they appear to offer little threat to puter antivirus packages generally cost less than
basic library operations and can usually be safely $50 each.
ignored.
If there are more than a half dozen computers on
Cookies seem to be more beneficial than harmful. the network, it probably makes sense to consider a
Cookies may pose a potential threat to some busi- network antivirus package. This may save some
nesses on the Internet, and they are certainly of money but, even if there is no cost reduction, net-
concern to individuals who use the Internet from work packages offer the advantage of central man-
their own computers. However, the ability of cook- agement. With single-computer packages, antivirus
ies to monitor Internet use at libraries does not operations and updating have to be performed sep-
seem to have any threatening implications. arately at each computer. With the network pack-
age, antivirus control and updating can be per-
Computer viruses, worms, and trojan horses may formed once, at one computer, to keep all the net-
indeed pose serious threats to library computer net- work computers protected.
works because they can spread from one computer
to another and may damage files. With increasing
amounts of paperwork now performed on library 9.1.1. Command AntiVirus
computers, destruction of files can be measured in
loss of hours of intellectual and clerical effort. As This package provides automatic notification if a
computer storage assumes its place as one of the virus infection is found. Discovered viruses are
regular repositories for library collections, loss of files automatically isolated to a quarantine folder and e-
becomes as important as loss of physical materials. mail notification can be specified. Protection from
Protection against such losses seems prudent. Office 97 macro viruses is provided. Virus protec-
tion updates from the vendor’s Web site can be
received automatically and then installed on users’
9. Virus protection software network-connected computers from a shared cen-
tralised directory.
Antivirus software can continuously examine all
computer activity for signs of viruses, worms and Command AntiVirus allows network administrators
trojan horses. Scanning a large number of files can to display virus scan statistics and a log of scanning
take a long time so most packages allow antivirus events. Antivirus scans can be set for a single user,
scanning to take place in the background when no a group of users, or throughout the entire network.
other work is being processed by the computer. Groups and users are displayed in a tree view.
Antivirus software may also operate in an on- Scans can also be scheduled by logged-on users
demand mode where users initiate the examination for their own machines. Scanning can be set up on
of files for viruses. Most antivirus packages allow a scheduled, on-demand and on-access basis.
the user to define a set of antivirus procedures, save Specific file types can be included or excluded.
that combination of procedures, and execute them
on a schedule set by the user. Command AntiVirus for one network server lists for
$239 (for NetWare) or $170 (for NT). Also required is
Virus protection software can be certified by the Command AntiVirus for user workstations, which
International Computer Security Association (ISCA). lists at $49.95 each. A single-user version also lists
To receive ICSA certification, packages must detect at $49.95. The vendor is Command Software
The Electronic Library, Vol. 17, No. 2, April 1999 117
Systems Inc., Jupiter, FL. Tel.: +1 561 575 3200. files. Groups of files can, however, be selected by
www.commandcom.com. file type and then scanned. Also, groups of files can
TECHNOLOGY be excluded. The vendor’s Web site makes month-
CORNER ly updates to the package available.
9.1.2. Dr Solomon’s Management Edition
A network version of the package with automated
This is a network antivirus package that provides network deployment and management is available
support and central administration for a variety of at prices starting at $49.95 per user for up to 10
different computers connected to a network. users. A single-user version of eSafe lists for $49.
Whether the individual computers use Windows 95, The vendor is eSafe Technologies Inc., Seattle, WA.
NT, 3.1 or 3.11, this package will supply antivirus Tel.: +1 206 524 9159. www.esafe.com.
protection to all of them.
The Dr Solomon central management software is 9.1.4. InocuLAN
installed onto a Windows NT computer. Computers
that are identified as antivirus protected get their With this antivirus package, users can select any
updates from directories that store management and combination of drives, folders or files for scanning.
antivirus toolkits and components. Remote installa- There is detailed control over which items are to be
tion and updating of software on Windows 3.1 com- excluded from scanning. Regularly scheduled scans
puters is handled by supplying a custom computer are set up with the help of a wizard. The software
name for each 3.1 machine when the Management detects many virus types, including macro viruses.
Edition software is installed. Depending on the size Files found to be infected can be moved into a quar-
and structure of the network there are different antine area where they can be safely examined, and
strategies for setting up the antivirus software. The files in this area are excluded from antivirus scans,
user manuals explain the options. so they will not trigger further alarms. Level of pro-
tection can be set by clicking on a button. When any
Management Edition gives network administrators a virus infection is detected, the package automatical-
vehicle for installing, configuring and updating ly goes to the highest level of protection.
antivirus software throughout Microsoft and Novell
networks. From the central management computer, The network versions of this software allow for
the administrator can distribute antivirus software, Windows-based grouping of servers and worksta-
make updates, receive antivirus event messages, tions. The software keeps a virus scanning history,
and schedule antivirus events for the individual net- including files checked, viruses found, responses
work computers. taken and updates. InocuLAN is available for
Windows NT and NetWare servers and Windows
Dr Solomon’s Management Edition prices are: 10 3.x, Windows 95, Windows NT, DOS and Macintosh
nodes, $1159; 25 nodes, $2843. In other words, workstations.
about $115 per user. Single-computer versions list
at $39.95 to $69.95. The vendor is Dr Solomon, The list price for InocuLAN for a single computer is
www.drsolomon.com. $69.For network workstations the price is about $40
each. Versions for network servers are more expen-
sive. The vendor is Computer Associates
9.1.3. eSafe Protect International Inc., Islandia, NY. Tel.: +1 516 342
5224. www.cai.com/cheyenne.
This package is designed to control viruses, trojan
horses, Java applets, ActiveX controls, and even
modem dialler intrusions that can dial unwanted 9.1.5. McAfee NetShield for Windows NT
long-distance numbers. eSafe lets Java applet and
ActiveX control programs enter the computer but This package detects virus-infected files moving to
they are isolated in a protected area on the hard disk and from an NT server to prevent viruses from
called a sandbox. eSafe then runs the programs and spreading through the local network. When an
checks their activity to determine whether they may infected file is detected, it is automatically logged
cause harm. eSafe has compiled a list of untrustwor- and either isolated or deleted. NetShield displays
thy Internet sites, and users can add to that list. The provide point and click administration of virus scan-
package will prevent contact with sites that appear ning tasks, including notification and reporting.
on the untrustworthy list. The package can also stop
selected words from being accessed. The eSafe NetShield for Windows NT lists at $190, for use with
manual is an Acrobat file that can be downloaded 10 nodes. The single-user version lists for $49. The
from the eSafe Web site. The manual provides step vendor is Network Associates Inc., Santa Clara, CA.
by step instructions on configuring the package for Tel.: +1 408 988 3832. www.networkassociates.
individual needs. The package also comes with a com.
well-organised and useful help file.
One shortcoming is that real-time scanning for 9.1.6. Norton AntiVirus
viruses is difficult to disable. eSafe lets users scan
drives and folders on demand but not individual This package has an on-demand virus scanner that
118 The Electronic Library, Vol. 17, No. 2, April 1999
lets users control the scan using many options. Guard Dog Deluxe is priced at $59.95. The vendor
Folders, file types and individual files can be includ- is CyberMedia Inc., Santa Monica, CA. Tel.: +1 310
ed or excluded. Within a safe environment for start- 664 5000. www.cybermedia.com. TECHNOLOGY
ing program files, Norton AntiVirus uses a search CORNER
technology from IBM to locate virtually any virus-
like files. A scan and deliver feature lets users e-mail 9.2.2. Integrity Master
a safely wrapped virus to Symantec’s AntiVirus Lab.
In many cases the process is automated, so the Most antivirus packages operate by identifying the
response can be 30 minutes or less. Also in this ver- various viruses that are known to be in circulation.
sion, users can incrementally update virus definition Integrity Master takes an entirely different approach,
files with new information from Symantec, but free based on the characteristics of the files that are
updates are limited to a year. After that, an annual stored on the computer. During installation, this
subscription to updates costs $4.95. The package package scans all files for viruses. If none are found,
comes with a scheduler that automates the updat- the package sets up a coded description of each
ing process. Running of programs and virus scan- stored file. Any change to a file will alter this signa-
ning can also be scheduled. ture. If the signature changes unexpectedly, this
alerts the package to possible infection or tamper-
NT server, NT workstation and Windows 95/98 ver- ing. This approach not only detects changes due to
sions of Norton AntiVirus each list for $39.95 The viruses, but it can also discover file changes that
vendor is Symantec Corp., Cupertino, CA. Tel.: +1 may be due to other types of invasions, or even due
541 334 6054. www.symantec.com. to hardware malfunctions. The package generates
detailed reports that list all changed files and the
errors found by the package, along with possible
9.1.7. Vet AntiVirus reasons for these errors. The Integrity Master man-
ual includes considerable material on viruses and
Vet performs rapid antivirus scanning. Users can the strengths and weaknesses of various antivirus
select as many folders and files for scanning as they approaches. Unfortunately, this package is unable
see displayed in the current Windows Explorer dis- to remove the viruses it finds. Although it is intend-
play. The package scans either all files or only ed for PCs, it does not function smoothly under
selected file types. It has no scan scheduling capa- Microsoft Windows.
bility and it checks files only as they open and close.
Users must perform occasional full scans manually The list price for Integrity Master is $49.50. The ven-
in order to ensure the safety of their systems. Vet dor is Stiller Research, Colorado Springs, CO. Tel.:
detects and cleans conventional file and boot sec- +1 719 533 1879. Fax: +1 719 533 1728.
tor viruses as well as macro viruses. Vet AntiVirus www.stiller.com.
lists for 595 Australian dollars for one network serv-
er (NT, NetWare or DEC Alpha). The list price for
workstations is 99 Australian dollars. The vendor is 9.2.3. ThunderByte
Cybec Pty Ltd, Melbourne, Victoria, Australia. Tel.:
+61 3 9825 5600. www.vet.com.au. Users of this package can define antivirus scanning
to cover the boot disk drive, all local hard disks, all
9.2. Single-user packages CD-ROM drives and all drives on an editing screen.
However, the package does not allow users to
schedule scanning in advance. ThunderByte Anti-
9.2.1. Guard Dog Deluxe Virus Utilities list for $99. The vendor is NovaStor-
Authentex Software Corp., Kanata, Ontario,
This package keeps computers from downloading Canada. Tel.: +1 613 930 4444.
ActiveX controls, Java applets, cookies and viruses. www.authentex.com.
It has an interface that makes it very easy to use. A
single dialogue box provides for the available set-up
options, which are explained briefly yet clearly. It is 9.2.4. Panda AntiVirus
easy to determine and select the precise level of
protection that is desired and the package alerts This package has a scanning system that can
users to any downloaded program that exhibits any examine an entire hard disk in a few seconds.
suspicious activity. Users can schedule virus Panda detects more than 13,000 viruses. It scans
checks automatically for specific file types. There is compressed files, and it detects and removes virus-
a cookie-blocking module that allows users to es. The vendor provides updates and a hotline ser-
selectively accept cookies only from trusted or use- vice. The package uses a heuristic scanning
ful sites and reject all others. There is a feature that method that is said to be capable of detecting new
automatically blocks search requests entered at viruses not yet recognised by conventional scan
popular search engines from being forwarded to systems. Panda’s virtual driver feature oversees file
other sites that track such behaviour. Another fea- traffic, and it can detect viruses while the user per-
ture alerts the user whenever a program attempts to forms other tasks. Panda AntiVirus sells for $45 to
connect to the Internet. The package will clean out $100. The vendor is Panda Software. Tel.: +1 415
the browser’s cache, and the list of sites visited, and 392 5950. www.pandasoftware.com.
the history file of Web pages.
The Electronic Library, Vol. 17, No. 2, April 1999 119
You might also like
- Introduction To Computer VirusesDocument31 pagesIntroduction To Computer Virusesaafy92% (12)
- My Seminar Report Computer, Cellphone Virus and SecurityDocument49 pagesMy Seminar Report Computer, Cellphone Virus and SecurityRijy LoranceNo ratings yet
- Section B Writing - 15 MarksDocument4 pagesSection B Writing - 15 MarksArjita SrivastavaNo ratings yet
- Computer Viruses and MalwaresDocument76 pagesComputer Viruses and MalwaresHazel Karen CaguinginNo ratings yet
- A Computer Worm Is A Type of Malware That Spreads Copies of Itself From Computer To ComputerDocument10 pagesA Computer Worm Is A Type of Malware That Spreads Copies of Itself From Computer To ComputerAbdul LateefNo ratings yet
- Virus and TrojansDocument3 pagesVirus and TrojansSaiful KaderNo ratings yet
- AbstractDocument24 pagesAbstractVijay Kumar0% (1)
- Computer Virus and Penetration Technique: Mayej - S@yahoo - Co.inDocument5 pagesComputer Virus and Penetration Technique: Mayej - S@yahoo - Co.inJournal of Computer ApplicationsNo ratings yet
- By: Abd Rashid Bin HJ Shafie Penyelaras Bestari SMK Gunung Rapat, IpohDocument4 pagesBy: Abd Rashid Bin HJ Shafie Penyelaras Bestari SMK Gunung Rapat, IpohEiza AliasNo ratings yet
- Computer Virus TypesDocument7 pagesComputer Virus TypesmohanakalaiselviNo ratings yet
- 03 Computer VirusDocument3 pages03 Computer VirusDjamesNo ratings yet
- Module 5 - MalwareDocument5 pagesModule 5 - MalwareJamara Pucan100% (1)
- Haramaya University: Institute of TechnologyDocument3 pagesHaramaya University: Institute of TechnologyKalebNo ratings yet
- Chapter Five Computer Security: How Infections OccurDocument7 pagesChapter Five Computer Security: How Infections OccurErmiasNo ratings yet
- Differences Between Worms and VirusesDocument9 pagesDifferences Between Worms and VirusesChe Andrea Arandia AbarraNo ratings yet
- Day - 1Document19 pagesDay - 1Sivakumar RavichandranNo ratings yet
- Anti Virus Best Practices PDFDocument8 pagesAnti Virus Best Practices PDFkprasad_mlNo ratings yet
- The Difference Between A Virus, Worm and Trojan Horse?Document3 pagesThe Difference Between A Virus, Worm and Trojan Horse?joshidpalNo ratings yet
- Virus and Its TypesDocument7 pagesVirus and Its TypesrajNo ratings yet
- Virus Worms TrojenhorseDocument3 pagesVirus Worms TrojenhorseAltaf KarediaNo ratings yet
- Computer WormDocument3 pagesComputer WormChina FonNo ratings yet
- VirusDocument5 pagesVirusarunNo ratings yet
- Virus Definition and Manual RemovalDocument6 pagesVirus Definition and Manual RemovalJerrymae OboNo ratings yet
- Malware: Online Threats: Presented By: Ramil L. Kaharian ICT TeacherDocument16 pagesMalware: Online Threats: Presented By: Ramil L. Kaharian ICT TeacherShielina Mae CosejoNo ratings yet
- System Software (Csd-224) : Assignment: 01Document4 pagesSystem Software (Csd-224) : Assignment: 01Prateek SharmaNo ratings yet
- Trojan and Email ForgingDocument20 pagesTrojan and Email ForgingAnurag GoelNo ratings yet
- VirusDocument3 pagesVirusspanda5734009No ratings yet
- Computer Worm: Causal Connection RelationshipDocument5 pagesComputer Worm: Causal Connection RelationshipfeisalNo ratings yet
- Report Computervirus 190303140330Document16 pagesReport Computervirus 190303140330auadm1311No ratings yet
- Internet Security NotesDocument7 pagesInternet Security Notescool.tbaNo ratings yet
- What Is A Computer Security RiskDocument10 pagesWhat Is A Computer Security Riskhantu malamNo ratings yet
- System Software (Csd-224) : Assignment: 01Document4 pagesSystem Software (Csd-224) : Assignment: 01Prateek SharmaNo ratings yet
- Computer VirusDocument11 pagesComputer VirusAbhay AnantNo ratings yet
- Lecture4-Malicious and Antivirus SoftwareDocument25 pagesLecture4-Malicious and Antivirus SoftwareTACN-2C-19ACN Nguyen Tung AnhNo ratings yet
- Getting Ill Sucks.Document3 pagesGetting Ill Sucks.Subhajit KunduNo ratings yet
- Antivirus UpdatedDocument40 pagesAntivirus UpdatedkhadijaNo ratings yet
- Threats of Computer System and Its PreveDocument4 pagesThreats of Computer System and Its Prevedubeza2008No ratings yet
- Ethical - Hacking-1 (Islamic University of Science and Technology Pulwama)Document37 pagesEthical - Hacking-1 (Islamic University of Science and Technology Pulwama)cse 20 42Syed TawqeerNo ratings yet
- 2.3network SecurityDocument22 pages2.3network Securitybrought to inspire - faith silvaNo ratings yet
- Computer Worm ReportDocument6 pagesComputer Worm Reportapi-345209108No ratings yet
- Comprog1 - SLK Q1 4Document10 pagesComprog1 - SLK Q1 4emmanuel simNo ratings yet
- Computer VirusesDocument26 pagesComputer VirusesMahe KotaNo ratings yet
- Threats To Sys SecurityDocument3 pagesThreats To Sys SecurityPoornima SinghNo ratings yet
- Definition of VirusDocument3 pagesDefinition of Virusunknown.JackNo ratings yet
- Computer ProjectDocument6 pagesComputer ProjectPiyush RanjanNo ratings yet
- Project ReportDocument6 pagesProject Reportsharrmaa0% (1)
- Attack VectorsDocument5 pagesAttack VectorsJay Mehta100% (1)
- IntroductionDocument4 pagesIntroductionLG star coreNo ratings yet
- Malware Classification & DamagesDocument7 pagesMalware Classification & Damagesnusha2907No ratings yet
- Computer VirusDocument4 pagesComputer VirusJohn GacheruNo ratings yet
- Trojan Horse: Computer Viruses Typically Attach To An Executable Host FileDocument3 pagesTrojan Horse: Computer Viruses Typically Attach To An Executable Host FileReena CorreaNo ratings yet
- The History of Computer VirusDocument5 pagesThe History of Computer VirusDrRohitKumarMDHomNo ratings yet
- Types of VirusDocument3 pagesTypes of ViruschepimancaNo ratings yet
- Qn.1.What Is A Printer? A Printer Is A Peripheral DeviceDocument11 pagesQn.1.What Is A Printer? A Printer Is A Peripheral Devicechachuo0% (1)
- I Jcs It 2013040325Document6 pagesI Jcs It 2013040325Charles SandersNo ratings yet
- Malicious SoftwareDocument38 pagesMalicious SoftwareAkshay KothariNo ratings yet
- Virus On Computer22 - 1Document17 pagesVirus On Computer22 - 1Bharath ChinuNo ratings yet
- VirusDocument8 pagesVirusRavula KartheekNo ratings yet
- Comparing Passive and Active Worm DefensesDocument10 pagesComparing Passive and Active Worm DefensesJohn GacheruNo ratings yet
- Computer Viruses - Legal OptionsDocument2 pagesComputer Viruses - Legal OptionsJohn GacheruNo ratings yet
- Computer Viruses A Global PerspectiveDocument20 pagesComputer Viruses A Global PerspectiveJohn GacheruNo ratings yet
- Computer Viruses - The Current State in ItalyDocument2 pagesComputer Viruses - The Current State in ItalyJohn GacheruNo ratings yet
- Computer Viruses - A Form of Artificial LifeDocument22 pagesComputer Viruses - A Form of Artificial LifeJohn GacheruNo ratings yet
- Attitude Adjustment Trojans and Malware On The InternetDocument26 pagesAttitude Adjustment Trojans and Malware On The InternetJohn GacheruNo ratings yet
- Combating Computer VirusesDocument2 pagesCombating Computer VirusesJohn GacheruNo ratings yet
- Broadband Network Virus Detection System Based On Bypass MonitorDocument4 pagesBroadband Network Virus Detection System Based On Bypass MonitorJohn GacheruNo ratings yet
- Chapter Five The Body Electr (On) Ic Catches Cold Viruses and ComputersDocument54 pagesChapter Five The Body Electr (On) Ic Catches Cold Viruses and ComputersJohn GacheruNo ratings yet
- Computer Insecurity and Viral AttacksLiability Issues Regarding Unsafe Computer Systems Under Quebec LawDocument15 pagesComputer Insecurity and Viral AttacksLiability Issues Regarding Unsafe Computer Systems Under Quebec LawJohn GacheruNo ratings yet
- Biologically Inspired Defenses Against Computer VirusesDocument12 pagesBiologically Inspired Defenses Against Computer VirusesJohn GacheruNo ratings yet
- As Japanese Bring Work Home, Virus Hitches A RideDocument2 pagesAs Japanese Bring Work Home, Virus Hitches A RideJohn GacheruNo ratings yet
- Catch Me, If You Can Evading Network Signatures With Web-Based Polymorphic WormsDocument9 pagesCatch Me, If You Can Evading Network Signatures With Web-Based Polymorphic WormsJohn GacheruNo ratings yet
- Artificial Immune Systems and The Grand Challenge For Non-Classical ComputationDocument12 pagesArtificial Immune Systems and The Grand Challenge For Non-Classical ComputationJohn GacheruNo ratings yet
- Classification of Packed Executables For Accurate Computer Virus DetectionDocument15 pagesClassification of Packed Executables For Accurate Computer Virus DetectionJohn GacheruNo ratings yet
- Computer Doctor Busy Fighting 'Viruses'Document1 pageComputer Doctor Busy Fighting 'Viruses'John GacheruNo ratings yet
- Comments On A Paper by Voas, Payne & Cohen%3A %80%9CA Model For Detecting The Existence of Software Corruption in Real Time %80%9DDocument6 pagesComments On A Paper by Voas, Payne & Cohen%3A %80%9CA Model For Detecting The Existence of Software Corruption in Real Time %80%9DJohn GacheruNo ratings yet
- Computer Viruses Demystified, 2Document4 pagesComputer Viruses Demystified, 2John GacheruNo ratings yet
- Computer Viruses and Electronic MailDocument13 pagesComputer Viruses and Electronic MailJohn GacheruNo ratings yet
- Computer Viruses A Very Real ThreatDocument14 pagesComputer Viruses A Very Real ThreatJohn GacheruNo ratings yet
- Can Cryptography Prevent Computer VirusesDocument12 pagesCan Cryptography Prevent Computer VirusesJohn GacheruNo ratings yet
- Computer Malware What You Don't Know Can Hurt YouDocument2 pagesComputer Malware What You Don't Know Can Hurt YouJohn GacheruNo ratings yet
- Computer Virus Cover WithdrawnDocument1 pageComputer Virus Cover WithdrawnJohn GacheruNo ratings yet
- Computer Viruses and What To Do About ThemDocument9 pagesComputer Viruses and What To Do About ThemJohn GacheruNo ratings yet
- Anti-Virus in The Corporate ArenaDocument18 pagesAnti-Virus in The Corporate ArenaJohn GacheruNo ratings yet
- Computer Security Analysis Through Decompilation and High-Level DebuggingDocument6 pagesComputer Security Analysis Through Decompilation and High-Level DebuggingJohn GacheruNo ratings yet
- Attack of The Killer Virus!Document7 pagesAttack of The Killer Virus!John GacheruNo ratings yet
- Computer Viruses EpisodeDocument18 pagesComputer Viruses EpisodeJohn GacheruNo ratings yet
- Computer Viruses As A Threat To Home UsersDocument12 pagesComputer Viruses As A Threat To Home UsersJohn GacheruNo ratings yet
- Biological Models of Security For Virus Propagation in Computer NetworksDocument8 pagesBiological Models of Security For Virus Propagation in Computer NetworksJohn GacheruNo ratings yet
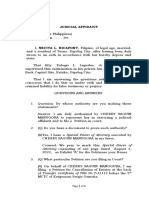
- JUDICIAL AFFIDAVIT RicafortDocument4 pagesJUDICIAL AFFIDAVIT RicafortEulogio LagudasNo ratings yet
- Lifetime StandardsDocument37 pagesLifetime StandardsLazar CristianNo ratings yet
- Date Narration Chq./Ref - No. Value DT Withdrawal Amt. Deposit Amt. Closing BalanceDocument16 pagesDate Narration Chq./Ref - No. Value DT Withdrawal Amt. Deposit Amt. Closing Balancevedhasai198No ratings yet
- Chapter 17 (Hukm Shar'i)Document16 pagesChapter 17 (Hukm Shar'i)MutyaAlmodienteCocjin100% (1)
- Pension ProposalDocument14 pagesPension ProposalprastacharNo ratings yet
- School Operational Work Plan - CompressDocument6 pagesSchool Operational Work Plan - CompressKimathi Bundi100% (2)
- 40 Values ChecklistDocument1 page40 Values ChecklistCarina LindseyNo ratings yet
- Sonic R. SystemDocument2 pagesSonic R. Systemthang 1No ratings yet
- Academic Calendar 2022-2023Document1 pageAcademic Calendar 2022-2023AssunçãoNo ratings yet
- Data InterpretationDocument44 pagesData InterpretationSwati Choudhary100% (2)
- Ojoyoshu by Genshin, Translated From Japanese by A.K. ReischauerDocument136 pagesOjoyoshu by Genshin, Translated From Japanese by A.K. ReischauerJōshō Adrian Cirlea100% (6)
- Evidence Cases IIDocument94 pagesEvidence Cases IIAiken Alagban LadinesNo ratings yet
- MPA - Policy Paper (R.simbahon)Document80 pagesMPA - Policy Paper (R.simbahon)Robert SimbahonNo ratings yet
- Practitioner Guide Georgia English 20130516Document310 pagesPractitioner Guide Georgia English 20130516OSGFNo ratings yet
- Tool 5 Steps To Building An HR StrategyDocument23 pagesTool 5 Steps To Building An HR Strategysara.algaeitiNo ratings yet
- Lawrence Connell v. Linda Ammons - Court Opinion Denying Motion To Change VenueDocument3 pagesLawrence Connell v. Linda Ammons - Court Opinion Denying Motion To Change VenueLegal InsurrectionNo ratings yet
- Blue StrategyDocument22 pagesBlue StrategyshivanthikaNo ratings yet
- Finding Our Way Again - Part 1Document10 pagesFinding Our Way Again - Part 1dscharfNo ratings yet
- Computer AssociatesDocument18 pagesComputer AssociatesRosel RicafortNo ratings yet
- Cen 01 2019 RRB NTPC RrbonlinegovinDocument71 pagesCen 01 2019 RRB NTPC RrbonlinegovinIndia Jobs Seeker75% (8)
- Voluntarism - IEPDocument1 pageVoluntarism - IEPLeandro BertoncelloNo ratings yet
- GRADE 5 AGUINALDO Numeracy Profile of LearnersDocument7 pagesGRADE 5 AGUINALDO Numeracy Profile of Learnersroel labayNo ratings yet
- Adoption by LGBTQ ParentsDocument3 pagesAdoption by LGBTQ ParentsCheuk Yin WONGNo ratings yet
- Post DevelopmentDocument35 pagesPost DevelopmentAminul QuayyumNo ratings yet
- Paint A Brighter Future PFS - 220618 - 074733Document1 pagePaint A Brighter Future PFS - 220618 - 074733Rene AliNo ratings yet
- The Conquistadors Always Start From The South in Square 28 and On The Track The Aztecs Always Start in Square 13Document9 pagesThe Conquistadors Always Start From The South in Square 28 and On The Track The Aztecs Always Start in Square 13Joshua ReyesNo ratings yet
- Combined Knitting Conversion TableDocument1 pageCombined Knitting Conversion TableKatarina Ivic-UcovicNo ratings yet
- MATH PROJECT TOPIC 2 (Income Tax)Document7 pagesMATH PROJECT TOPIC 2 (Income Tax)avinamakadiaNo ratings yet
- Bully Policy PDFDocument3 pagesBully Policy PDFLisa DouglasNo ratings yet