Professional Documents
Culture Documents
Lecture 3 Classical Symmetric Cryptography
Lecture 3 Classical Symmetric Cryptography
Uploaded by
Abdlruhman sheerif0 ratings0% found this document useful (0 votes)
20 views20 pageslecture about classical symmetric cryptography
Original Title
lecture 3 classical symmetric cryptography
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this Documentlecture about classical symmetric cryptography
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
Download as pdf or txt
0 ratings0% found this document useful (0 votes)
20 views20 pagesLecture 3 Classical Symmetric Cryptography
Lecture 3 Classical Symmetric Cryptography
Uploaded by
Abdlruhman sheeriflecture about classical symmetric cryptography
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
Download as pdf or txt
You are on page 1of 20
Computer Security
Prepared by: Assistant Prof. Eman Sanad
Faculty of computers and Artificial Intelligence
Cairo University 1
Lecture 3
• Symmetric cipher Model
• Cryptography
• Cryptanalysis and Brute-force attack
• Substitution techniques
Dr. Eman Sanad, faculty of computers and
2
Artificial Intelligence , Cairo University
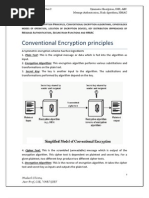
Symmetric cipher Model
A symmetric encryption (conventional encryption) scheme has five ingredients:
■ Plaintext:
This is the original intelligible message or data that is fed into the algorithm as
input.
■ Encryption algorithm:
The encryption algorithm performs various substitutions and transformations on
the plaintext.
■ Secret key:
The secret key is also input to the encryption algorithm. The key is a value
independent of the plaintext and of the algorithm. The algorithm will produce a
different output depending on the specific key being used at the time. The exact
substitutions and transformations performed by the algorithm depend on the key.
Dr. Eman Sanad, faculty of computers and
3
Artificial Intelligence , Cairo University
Symmetric cipher Model cont…
■ Ciphertext:
This is the scrambled message produced as output. It depends on
the plaintext and the secret key. For a given message, two different
keys will produce two different ciphertexts. The ciphertext is an
apparently random stream of data and, as it stands, is unintelligible.
■ Decryption algorithm:
This is essentially the encryption algorithm run in reverse. It takes
the ciphertext and the secret key and produces the original
plaintext.
Dr. Eman Sanad, faculty of computers and
4
Artificial Intelligence , Cairo University
Symmetric cipher Model cont…
Dr. Eman Sanad, faculty of computers and
5
Artificial Intelligence , Cairo University
Symmetric cipher Model cont…
• With the message X and the encryption key K as input,
the encryption algorithm forms the ciphertext
We can write this as
Y = E(K, X)
• This notation indicates that Y is produced by using
encryption algorithm E as a function of the plaintext X,
with the specific function determined by the value of the
key K.
• The intended receiver, in possession of the key, is able to
invert the transformation:
X = D(K, Y)
Dr. Eman Sanad, faculty of computers and
6
Artificial Intelligence , Cairo University
Symmetric cipher Model cont…
• An opponent, observing Y but not having access to K or X,
may attempt to recover X or K or both X and K.
It is assumed that the opponent knows the encryption (E) and
decryption (D) algorithms.
• If the opponent is interested in only this particular
message, then the focus of the effort is to recover X by
generating a plaintext estimate X
• However, the opponent is interested in being able to read
future messages as well, in which case an attempt is made
to recover K by generating an estimate K.
Dr. Eman Sanad, faculty of computers and
7
Artificial Intelligence , Cairo University
Symmetric cipher Model cont…
Dr. Eman Sanad, faculty of computers and
8
Artificial Intelligence , Cairo University
Cryptography
Cryptographic systems are characterized along three independent
dimensions:
1. The type of operations used for transforming
plaintext to ciphertext.
Substitution:
each element in the plaintext (bit, letter, group of bits or letters) is mapped
into another element.
Transposition:
which elements in the plaintext are rearranged
Most systems, referred to as product systems, involve multiple stages of
substitutions and transpositions.
Dr. Eman Sanad, faculty of computers and
9
Artificial Intelligence , Cairo University
Cryptography cont…
2. The number of keys used.
• If both sender and receiver use the same key,
the system is referred to as symmetric, single-
key, secret-key, or conventional encryption.
• If the sender and receiver use different keys,
the system is referred to as asymmetric, two-
key, or public-key encryption.
Dr. Eman Sanad, faculty of computers and
10
Artificial Intelligence , Cairo University
Cryptography cont…
3. The way in which the plaintext is processed.
• A block cipher processes the input one block of
elements at a time, producing an output block for each
input block.
• A stream cipher processes the input elements
continuously, producing output one element at a time,
as it goes along.
Dr. Eman Sanad, faculty of computers and
11
Artificial Intelligence , Cairo University
Cryptanalysis and Brute-Force Attack
The objective of attacking an encryption system is to
recover the key in use rather than simply to recover the
plaintext of a single ciphertext.
Cryptanalysis:
This type of attack exploits the characteristics of the
algorithm to attempt to deduce a specific plaintext or to
deduce the key being used.
Brute-force attack:
The attacker tries every possible key on a piece of ciphertext
until an intelligible translation into plaintext is obtained
Dr. Eman Sanad, faculty of computers and
12
Artificial Intelligence , Cairo University
Types of Attacks on Encrypted Message
Dr. Eman Sanad, faculty of computers and
13
Artificial Intelligence , Cairo University
Encryption Scheme Security
• Unconditionally secure
No matter how much time an opponent has, it is
impossible for him or her to decrypt the ciphertext
simply because the required information is not there.
• Computationally secure
■ The cost of breaking the cipher exceeds the value of
the encrypted information.
■ The time required to break the cipher exceeds the
useful lifetime of the information.
Dr. Eman Sanad, faculty of computers and
14
Artificial Intelligence , Cairo University
Brute-force Attack
Involves trying all possible key until an
intelligible translation of the ciphertext into
plaintext is obtained
On average, half of all possible keys must be
tried to achieve success
to supplement the brute-force approach, some degree of
knowledge about the expected plaintext is needed, and
some means of automatically distinguishing plaintext from
garble is also needed.
Dr. Eman Sanad, faculty of computers and
15
Artificial Intelligence , Cairo University
Substitution Techniques
each element in the plaintext (bit, letter, group of bits or letters) is
mapped into another element.
Caesar Cipher
• The earliest known, and the simplest, use of a substitution
cipher was by Julius Caesar.
• The Caesar cipher involves replacing each letter of the
alphabet with the letter standing three places further down
the alphabet.
Dr. Eman Sanad, faculty of computers and
16
Artificial Intelligence , Cairo University
Caesar Cipher
Note that the alphabet is wrapped around, so that the letter following Z
is A.
We can define the transformation by listing all possibilities, as follows:
Dr. Eman Sanad, faculty of computers and
17
Artificial Intelligence , Cairo University
Caesar cipher cont…
For each plaintext letter p, substitute the ciphertext letter C:
A shift may be of any amount, so that the general Caesar
algorithm is:
where k takes on a value in the range 1 to 25. The decryption
algorithm is simply
Dr. Eman Sanad, faculty of computers and
18
Artificial Intelligence , Cairo University
Brute-force Attack of Caesar cipher
Dr. Eman Sanad, faculty of computers and
19
Artificial Intelligence , Cairo University
Thank you
Dr. Eman Sanad, faculty of computers and
20
Artificial Intelligence , Cairo University
You might also like
- Cryptanalysis of Classical Ciphers: ObjectivesDocument5 pagesCryptanalysis of Classical Ciphers: Objectiveskochi jerryNo ratings yet
- Information Systems Security LAB: Eng. Christine ZeniehDocument11 pagesInformation Systems Security LAB: Eng. Christine ZeniehAbdullah Al-HallakNo ratings yet
- Classical Encryption TechniquesDocument12 pagesClassical Encryption Techniquessushantluitel39No ratings yet
- Chapter Two - Fundamentals of CryptographyDocument107 pagesChapter Two - Fundamentals of CryptographyJONAS J JONASNo ratings yet
- Encryption StandardsDocument76 pagesEncryption Standardsbhasker7100% (1)
- UNIT - I (Part 2)Document109 pagesUNIT - I (Part 2)asdadsaNo ratings yet
- CH 2 ISDocument12 pagesCH 2 IStiwarisapana036No ratings yet
- Symmetric Encryption, DES, AES, MAC, Hash Algorithms, HMACDocument76 pagesSymmetric Encryption, DES, AES, MAC, Hash Algorithms, HMACMukesh86% (7)
- Unit 3Document47 pagesUnit 3Andualem BegunoNo ratings yet
- IAS Chapter TwoDocument80 pagesIAS Chapter TwodigafeeyuelNo ratings yet
- CryptographyDocument23 pagesCryptographyAnubhav KumarNo ratings yet
- Computer Security: Computer Threats and EncryptionDocument21 pagesComputer Security: Computer Threats and EncryptionPro NebyuNo ratings yet
- Symmetric Ciphers: Data Encryption & Security (CEN-451) Spring 2020, BUKCDocument26 pagesSymmetric Ciphers: Data Encryption & Security (CEN-451) Spring 2020, BUKCMuhammad RehanNo ratings yet
- CRYPTO Mod1@AzDOCUMENTS - inDocument24 pagesCRYPTO Mod1@AzDOCUMENTS - insasindhur rNo ratings yet
- Computer Security Chapter 2-3-4-1Document72 pagesComputer Security Chapter 2-3-4-1guta lamessaNo ratings yet
- Ch3 NISDocument37 pagesCh3 NIS410 Sarang JagdaleNo ratings yet
- Cryptography TechknowxpressDocument28 pagesCryptography TechknowxpressMeet SindhalNo ratings yet
- CryptographyDocument7 pagesCryptographyHaile MelakuNo ratings yet
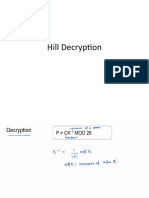
- Hill DecryptionDocument49 pagesHill DecryptionDhamodaran SrinivasanNo ratings yet
- Computer Security AsDocument4 pagesComputer Security AsHagos gebreslasieNo ratings yet
- Cryptography Using Automata TheoryDocument8 pagesCryptography Using Automata TheoryAbdullah AlahdalNo ratings yet
- Lect 4 Cryptographic System Trust ModelDocument15 pagesLect 4 Cryptographic System Trust ModelDipanshu sharmaNo ratings yet
- Varios Cryptography TechnicsDocument11 pagesVarios Cryptography TechnicsSuinNo ratings yet
- Lecture#02 - Classical Encryption TechniquesDocument57 pagesLecture#02 - Classical Encryption TechniquesfasihNo ratings yet
- Lecture#02 Part 1 - Classical Encryption TechniquesDocument30 pagesLecture#02 Part 1 - Classical Encryption TechniquesfasihNo ratings yet
- Chapter 2 IAS)Document41 pagesChapter 2 IAS)Abduu MizaabNo ratings yet
- CB3491 QBankDocument27 pagesCB3491 QBankjesusjeeva1995No ratings yet
- Chapter 3 FinalDocument80 pagesChapter 3 FinalMihretu BekeleNo ratings yet
- Chapter 3 Encryption Principles and AlgorithmsDocument25 pagesChapter 3 Encryption Principles and AlgorithmsHiziki TareNo ratings yet
- Ch3 NISDocument37 pagesCh3 NISshrey6346No ratings yet
- CB3491 NotesDocument192 pagesCB3491 NotesANITHARANI KNo ratings yet
- VTU Network Security (10ec832) Unit-2 Notes..Document91 pagesVTU Network Security (10ec832) Unit-2 Notes..jayanthdwijesh h p100% (3)
- Chapter 2 & 3Document20 pagesChapter 2 & 3Yakubu AliuNo ratings yet
- CryptographyDocument5 pagesCryptographyJoelNo ratings yet
- Chapter 3Document95 pagesChapter 3Soll HaileNo ratings yet
- CryptanalysisDocument13 pagesCryptanalysisRahmatullah MehrabiNo ratings yet
- Cs8792 Notes CnsDocument277 pagesCs8792 Notes CnsMathioli SenthilNo ratings yet
- Unit 1 - 2022Document177 pagesUnit 1 - 2022Ghetiya NirajNo ratings yet
- Unit IIDocument27 pagesUnit II20AD022 KAMALI PRIYA SNo ratings yet
- Chapter 2Document91 pagesChapter 2Destaye Sole WonideNo ratings yet
- CryptographyDocument30 pagesCryptographychelesani ngwenyaNo ratings yet
- New Encryption AlgorithmDocument5 pagesNew Encryption AlgorithmcheintNo ratings yet
- Ch3 CryptoDocument90 pagesCh3 CryptoArif AbdulelamNo ratings yet
- Network Design and Security ManagementDocument52 pagesNetwork Design and Security ManagementmehraDpaNo ratings yet
- Classical Encryption CipherDocument164 pagesClassical Encryption CipherShahriarNo ratings yet
- Symmetric Cryptography Using Nural NetworksDocument59 pagesSymmetric Cryptography Using Nural NetworksNAVEENA.VEMPADANo ratings yet
- IJETR2217Document6 pagesIJETR2217anil kasotNo ratings yet
- Exploring Polymorphic Algorithmsandtheirusein Cryptography CCWC2024Document8 pagesExploring Polymorphic Algorithmsandtheirusein Cryptography CCWC2024Dương Trần Mỹ LinhNo ratings yet
- Lecture 1Document54 pagesLecture 1sottathalaNo ratings yet
- 2.chapter - 9 - Public Key Cryptography and RSADocument40 pages2.chapter - 9 - Public Key Cryptography and RSAtt hhNo ratings yet
- Cryptography - PsDocument25 pagesCryptography - Psumti29No ratings yet
- ZCh1 Introduction To CryptographyDocument18 pagesZCh1 Introduction To Cryptographyawnimm99No ratings yet
- Advanced Encryption Standards (Aes)Document13 pagesAdvanced Encryption Standards (Aes)pulikondaNo ratings yet
- Public Key Cryptosystems With ApplicationsDocument21 pagesPublic Key Cryptosystems With ApplicationsChalo ChaleNo ratings yet
- SACA: A Study of Symmetric and Asymmetric Cryptographic AlgorithmsDocument8 pagesSACA: A Study of Symmetric and Asymmetric Cryptographic Algorithmsghada sayedNo ratings yet
- Is PTSSSS: AxssanboyDocument3 pagesIs PTSSSS: AxssanboyCabdi Fitaax KulmiyeNo ratings yet
- CryptoDocument24 pagesCryptoshivani.cs1995No ratings yet
- U21CS601 CT Unit 123 Part B QADocument13 pagesU21CS601 CT Unit 123 Part B QASanthosh kannaNo ratings yet
- CSS Chapter 1Document20 pagesCSS Chapter 1VIDIT SHAHNo ratings yet