Professional Documents
Culture Documents
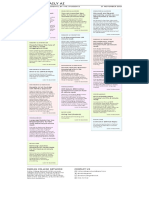
Related Works Table
Related Works Table
Uploaded by
aditya0 ratings0% found this document useful (0 votes)
16 views4 pagesThis document contains a table summarizing 20 research papers on cyberbullying detection. For each paper, it lists the year published, technologies and algorithms used, and potential future work. The technologies used include various deep learning models like CNNs, RNNs, LSTMs, BERT as well as traditional algorithms like SVM, KNN and ensemble methods. Future work suggested includes using newer models, multimodal data, handling bias and under-resourced languages.
Original Description:
related work table
Original Title
Related works table
Copyright
© © All Rights Reserved
Available Formats
DOCX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThis document contains a table summarizing 20 research papers on cyberbullying detection. For each paper, it lists the year published, technologies and algorithms used, and potential future work. The technologies used include various deep learning models like CNNs, RNNs, LSTMs, BERT as well as traditional algorithms like SVM, KNN and ensemble methods. Future work suggested includes using newer models, multimodal data, handling bias and under-resourced languages.
Copyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
Download as docx, pdf, or txt
0 ratings0% found this document useful (0 votes)
16 views4 pagesRelated Works Table
Related Works Table
Uploaded by
adityaThis document contains a table summarizing 20 research papers on cyberbullying detection. For each paper, it lists the year published, technologies and algorithms used, and potential future work. The technologies used include various deep learning models like CNNs, RNNs, LSTMs, BERT as well as traditional algorithms like SVM, KNN and ensemble methods. Future work suggested includes using newer models, multimodal data, handling bias and under-resourced languages.
Copyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
Download as docx, pdf, or txt
You are on page 1of 4
Name- Aditya Reg no 19BIT0139
Sl. Paper name Year Technologies used Future work
No published
.
1 A Bi-GRU with 2021 Self-attention Bi- Use transformer-based models
attention and GRU encoder like BERT
CapsNet hybrid Capsule network Fine grain classification into
model cyberbullying categories
for cyberbullying
detection on social
media
2 A multi-platform 2020 Convolutional Use this model on multi-
dataset for Neural Network platform incorporating data
detecting XGBoost like images and video
cyberbullying in SVM
social media
3 Automatic Cyber 2019 Corpus based N/A
Bullying Detection approach
in Arabic Social Java environment
Media
4 Cyberbullying 2016 Word embeddings Improve the robustness of
Detection based Semantic learned representation by
on enhanced considering word order in text
Semantic- marginalized
Enhanced denoising auto
Marginalized encoder
Denoising
Auto-Encoder
5 Cyberbullying 2020 RNN integrate deep learning
detection solutions LSTM approach with automatic
based on deep GRU detection by tracking and
learning Bi-LSTM object identification
Architectures mechanism
6 Cyberbullying 2021 Social media Create data sets belonging to
detection: Utilizing features like re- different countries that use
social media share, likes the same language to compare
features Crowdsourcing the effects of social media
web annotation features demographically.
application Additionally, a fuzzy rule-
SVM, LR, KNN, based system can be
NBM, AdaBoost, implemented to the current
RF approaches using the analysis
of social media futures
7 Early detection of 2021 Random Forest, Use of heterogeneous
cyberbullying on AdaBoost, Extra combination of ML algorithms
social media tree, Linear
networks Support Vector
Classification,
Logistic Regression
Applied other
features on
baseline models
Name- Aditya Reg no 19BIT0139
like profile owners
features,
Comments
features, LDA,
BoW
8 Predicting 2019 Random Forest, N/A
Cyberbullying on AdaBoost, Extra
Social Media in the tree, Linear
Big Data Era Using Support Vector
Machine Learning machine, Logistic
Algorithms:
Regression, Naïve
Review of
Bayes
Literature and
Open Challenges
9 Social Media 2019 SVM and Neural Use of larger size dataset
Cyberbullying network for
Detection using classification
Machine Learning TF-IDF and
sentimental
analysis for
feature extraction
10 Multi-input 2020 CapsNet, CNN, Use of embeddings from
integrative MLP, Bi-LSTM, Language Models (ELMo) and
learning using Multi-input bidirectional encoder
deep neural integrative representations from
networks learning using transformers (BERT)
and transfer deep neural
learning for networks
cyberbullying
detection in
real-time
code-mix data
11 A Multilingual 2017 Hybrid training Use of deep learning methods
System for models, such as
Cyberbullying combinations of
Detection: Arabic Distance
Content Detection Functions, NB and
using Machine SVM
Learning Weka for pre-
processing
12 DEA-RNN: A Hybrid 2022 Dolphin Use proposed model for other
Deep Learning Echolocation data types like audio, video
Approach Algorithm and images
for Cyberbullying Recurrent Neural
Detection in Network
Social Media
Platform
13 Cyberbullying 2020 DistilBERT for combining proposed approach
Detection with feature extraction with other bias mitigation
Fairness 3-layered Deep methods and establishing a
Name- Aditya Reg no 19BIT0139
Constraints neural network comprehensive framework for
unbiased machine learning
algorithms in cyber-social
health applications
14 Cyberbullying 2021 RNN-LSTM and Use of Ensemble methods
detection: RNN-BiLSTM Incorporation of context-
advanced pre- specific features and handling
processing of morphological variations
techniques & deep
learning
architecture for
Roman Urdu data
15 Cyberbullying 2022 2DCNN, VGG16, Use of proposed methodology
detection using Inception V3 on textual data
deep transfer
learning
16 An Application to 2022 CNN-BiLSTM, Analysis of image and video
Detect LSTM, GRU
Cyberbullying Combination of
Using Machine different
Learning activation
and Deep Learning
Techniques
17 Multilingual hope 2022 SVM, LR and Use of larger dataset
speech detection ensemble with further fine-grained
in English and CNN + BiLSTM classification and content
Dravidian m-BERT, Indic- analysis
languages BERT, XLNet and
XLM-R
18 COVID-19 and 2021 MLP, CNN, Use of multimodal fusion in
cyberbullying: BiLSTM, BERT order to predict the instances
deep ensemble of cyberbully in a more fine-
model grained way
to identify Model capable of
cyberbullying from understanding sarcasm
code-switched
languages
during the
pandemic
19 Keeping Children 2021 CASPER N/A
Safe Online With
Limited
Resources:
Analyzing What is
Seen and Heard
20 Machine Learning 2021 KNN, Naïve Bayes, explore into larger variety of
and feature Random forest, pre-processing methods for
engineering-based SVM linear, CNN sarcasm and irony detection
study into sarcasm
and irony
classification with
Name- Aditya Reg no 19BIT0139
application to
cyberbullying
detection
You might also like
- Learn IoT Programming Using Node-RED: Begin to Code Full Stack IoT Apps and Edge Devices with Raspberry Pi, NodeJS, and GrafanaFrom EverandLearn IoT Programming Using Node-RED: Begin to Code Full Stack IoT Apps and Edge Devices with Raspberry Pi, NodeJS, and GrafanaNo ratings yet
- SOPDocument5 pagesSOPKarthik V KalyaniNo ratings yet
- NO Paper / Year Method/tool Concept ApplicationDocument2 pagesNO Paper / Year Method/tool Concept Applicationmindworkz proNo ratings yet
- Predicting Cyberbullying in Social Media Using Machine LearningDocument7 pagesPredicting Cyberbullying in Social Media Using Machine Learningvinoth1128No ratings yet
- A41369 Tracking Objects Across Multiple Cameras Made Easy With Metropolis MicroservicesDocument25 pagesA41369 Tracking Objects Across Multiple Cameras Made Easy With Metropolis MicroservicesEduardo OrtizNo ratings yet
- PW - 4 - Litt. SurveyDocument6 pagesPW - 4 - Litt. SurveyTARA TARANNUMNo ratings yet
- IEEE Conference Template 1Document4 pagesIEEE Conference Template 1iqra muzaffarNo ratings yet
- A Comprehensive Survey On Machine Learning Techniques For Android Malware DetectionDocument12 pagesA Comprehensive Survey On Machine Learning Techniques For Android Malware DetectionAbhinandan BanikNo ratings yet
- A Hybrid / Novel Approach To Analyse Vulnerabilities in Software Applications Using Deep Learning MethodsDocument13 pagesA Hybrid / Novel Approach To Analyse Vulnerabilities in Software Applications Using Deep Learning Methodsafrin.anjum2020No ratings yet
- Resume - ComprehensiveDocument1 pageResume - Comprehensivemd sajid samiNo ratings yet
- Face Recognition Attendance System Based On Real-Time VideoDocument23 pagesFace Recognition Attendance System Based On Real-Time Videoshriramrs24No ratings yet
- Electronics 11 01044 v2Document26 pagesElectronics 11 01044 v2paulestephan76No ratings yet
- Vehicular Data Cloud PlatformDocument2 pagesVehicular Data Cloud PlatformPulin ChaudhariNo ratings yet
- Deep LearningINAF With MATLABDocument80 pagesDeep LearningINAF With MATLABTrieu Do MinhNo ratings yet
- Augmenting High-Performance Mobile Cloud Computations ForDocument13 pagesAugmenting High-Performance Mobile Cloud Computations FormunwarNo ratings yet
- Project SynopsisDocument12 pagesProject SynopsisShivam ThakurNo ratings yet
- Ai and AppplicationsDocument3 pagesAi and AppplicationsRezkie RezkieNo ratings yet
- Smart Home Security System Using Iot, Face Recognition and Raspberry PiDocument4 pagesSmart Home Security System Using Iot, Face Recognition and Raspberry PiBhanu B PrakashNo ratings yet
- Digits ClassifierDocument33 pagesDigits ClassifierSIVA BALANNo ratings yet
- Literature SurveyDocument3 pagesLiterature Surveykpalanivel123No ratings yet
- Explainability in IDS, Read Just After IntrosDocument6 pagesExplainability in IDS, Read Just After IntrosMango PeterNo ratings yet
- XiNOS Introduction & Cases 2017 Rev3cDocument21 pagesXiNOS Introduction & Cases 2017 Rev3cPraveen DubeyNo ratings yet
- 1-S2.0-S0925231223004502-Main 24Document24 pages1-S2.0-S0925231223004502-Main 24kacharnabil1No ratings yet
- Projectt EC IDeasDocument10 pagesProjectt EC IDeasJaydeep SNo ratings yet
- Catch Them Alive: Malware DetectionDocument19 pagesCatch Them Alive: Malware DetectionYolgezer İsviçre'deNo ratings yet
- ProfileDocument3 pagesProfileDebrup PaulNo ratings yet
- # Approach Authors (Year) Type Applicability Strategy Result & Granularity 1Document2 pages# Approach Authors (Year) Type Applicability Strategy Result & Granularity 1Marriam ijazNo ratings yet
- Cyberbullying DetectionDocument12 pagesCyberbullying DetectionRupesh SanagalaNo ratings yet
- 1 - Ai-Ml-Dl-HpcDocument11 pages1 - Ai-Ml-Dl-Hpcpedrovasrocha1No ratings yet
- Devansh Dixit 20BCS5590Document1 pageDevansh Dixit 20BCS5590Warriors NeoNo ratings yet
- Summer Training 2020 PDFDocument23 pagesSummer Training 2020 PDFInsideBest10No ratings yet
- Final ReviewDocument32 pagesFinal ReviewK AnirudhNo ratings yet
- Client 3 - Tech Symposia - Heterogeneous AI On Arm (Taiwan Version v2)Document27 pagesClient 3 - Tech Symposia - Heterogeneous AI On Arm (Taiwan Version v2)Andy WuNo ratings yet
- Abhinav JainDocument2 pagesAbhinav Jainknightark007No ratings yet
- PGP Machine Learning BrochureDocument21 pagesPGP Machine Learning BrochurevijayakumarvarmaNo ratings yet
- Biniyam AjawDocument1 pageBiniyam AjawBiniyam AjawNo ratings yet
- Shankar Chavan: Data ScientistDocument2 pagesShankar Chavan: Data ScientistSatyajeet RaiNo ratings yet
- Exploring and Comparing Various Machine and Deep Learning Technique Algorithms To Detect Domain Generation Algorithms of Malicious VariantsDocument10 pagesExploring and Comparing Various Machine and Deep Learning Technique Algorithms To Detect Domain Generation Algorithms of Malicious VariantsCSIT iaesprimeNo ratings yet
- Darshin Patel CVDocument1 pageDarshin Patel CVNimish TiwariNo ratings yet
- Sensors: BLAINDER-A Blender AI Add-On For Generation of Semantically Labeled Depth-Sensing DataDocument28 pagesSensors: BLAINDER-A Blender AI Add-On For Generation of Semantically Labeled Depth-Sensing DataNina MouhoubNo ratings yet
- Presentation 1Document2 pagesPresentation 1MANOJ .V 18BIR030No ratings yet
- Takeoff Edu Group CSE Title ListDocument321 pagesTakeoff Edu Group CSE Title ListTimNo ratings yet
- BeGAN Power Grid Benchmark Generation Using A Process-Portable GAN-based MethodologyDocument8 pagesBeGAN Power Grid Benchmark Generation Using A Process-Portable GAN-based Methodologyzoo50913No ratings yet
- Final Year Project Titles 2017-2018Document24 pagesFinal Year Project Titles 2017-2018Igeeks Technologies,Bangalore0% (1)
- Muskan's Resume FDocument1 pageMuskan's Resume FritwikcninjasNo ratings yet
- Cross MatchDocument11 pagesCross MatchKiên Dương NgôNo ratings yet
- ML Paper 2Document8 pagesML Paper 2lydiaNo ratings yet
- Huawei IMaster NCE Data SheetDocument11 pagesHuawei IMaster NCE Data SheetTest Test100% (1)
- Malware Detection and Classification Based On Graph Convolutional Networks and Function Call GraphsDocument11 pagesMalware Detection and Classification Based On Graph Convolutional Networks and Function Call Graphsanwarshahphd2021No ratings yet
- Special Issue May2021Document2 pagesSpecial Issue May2021Ketevani OtiashviliNo ratings yet
- IBM Cognitive Computing and Watson For AerospaceDocument19 pagesIBM Cognitive Computing and Watson For AerospaceSanjay K PrasadNo ratings yet
- Aiml Online BrochureDocument20 pagesAiml Online BrochurekarthikNo ratings yet
- Nest DNNDocument13 pagesNest DNNMilinbhadeNo ratings yet
- Deep Learning For Logo RecognitionDocument10 pagesDeep Learning For Logo RecognitionMonisha djNo ratings yet
- Sourav KumarDocument1 pageSourav Kumarprakash gangwarNo ratings yet
- AdMat A CNN-On-Matrix Approach To Android Malware Detection and ClassificationDocument15 pagesAdMat A CNN-On-Matrix Approach To Android Malware Detection and ClassificationDanh Nguyễn CôngNo ratings yet
- Articles (Zaki)Document2 pagesArticles (Zaki)godathangodathanNo ratings yet
- Ai Icn 17-Nov-2023Document1 pageAi Icn 17-Nov-2023Time PassNo ratings yet
- Image Processing and Computer Vision Systems Using MATLABDocument49 pagesImage Processing and Computer Vision Systems Using MATLABKio RoxNo ratings yet
- Shankar - Chavan - Resume - 10 08 2022 12 54 00Document2 pagesShankar - Chavan - Resume - 10 08 2022 12 54 00ALI HAIDERNo ratings yet
- 5Document1 page5MohmmedSaleemNo ratings yet
- 19mis0321 VL2022230507210 Ast04Document3 pages19mis0321 VL2022230507210 Ast04adityaNo ratings yet
- 18bce2049 VL2020210102673 Pe003Document26 pages18bce2049 VL2020210102673 Pe003adityaNo ratings yet
- TARPDocument21 pagesTARPadityaNo ratings yet
- Assignments For TarpDocument3 pagesAssignments For TarpadityaNo ratings yet
- Assignment - 3Document1 pageAssignment - 3adityaNo ratings yet
- Assignment-2: TARP Course, Winter 2022-23Document1 pageAssignment-2: TARP Course, Winter 2022-23adityaNo ratings yet
- OS LAB Assignment Q: Name - Aditya Reg No - 19BIT0139Document5 pagesOS LAB Assignment Q: Name - Aditya Reg No - 19BIT0139adityaNo ratings yet
- Tarp Rev3Document32 pagesTarp Rev3adityaNo ratings yet
- A Proactive 2-Stage Indoor CO2-based Demand-Controlled Ventilation Method Considering CoDocument18 pagesA Proactive 2-Stage Indoor CO2-based Demand-Controlled Ventilation Method Considering CoMariaNo ratings yet
- Covid 19 Prediction in India Using Machine LearningDocument5 pagesCovid 19 Prediction in India Using Machine LearningEditor IJTSRDNo ratings yet
- IJEST Special Issue CompleteDocument208 pagesIJEST Special Issue CompleteUkemebookieNo ratings yet
- Machine LearningDocument5 pagesMachine Learningmissbannu7350No ratings yet
- Predicting Autism Spectrum Disorder Using Machine Learning ClassifiersDocument4 pagesPredicting Autism Spectrum Disorder Using Machine Learning Classifiersahfn79No ratings yet
- Lecture04 Graph SVMDocument54 pagesLecture04 Graph SVMmasoudnateghi78No ratings yet
- Download Applications Of Artificial Intelligence In Mining And Geotechnical Geoengineering 1St Edition Hoang Nguyen Xuan Nam Bui Yosoon Choi Wengang Zhang Jian Zhou Erkan Topal online ebook texxtbook full chapter pdfDocument70 pagesDownload Applications Of Artificial Intelligence In Mining And Geotechnical Geoengineering 1St Edition Hoang Nguyen Xuan Nam Bui Yosoon Choi Wengang Zhang Jian Zhou Erkan Topal online ebook texxtbook full chapter pdfsalvador.cobb279100% (18)
- Emotion REcognition Using The Emotiv Epoc Device PDFDocument6 pagesEmotion REcognition Using The Emotiv Epoc Device PDFPaasolNo ratings yet
- hw1 Problem SetDocument8 pageshw1 Problem SetBilly bobNo ratings yet
- Demand Forecasting For Fashion ProductsDocument21 pagesDemand Forecasting For Fashion Productslishuang dengNo ratings yet
- Data Processing For Big Data ReportDocument24 pagesData Processing For Big Data ReportVarun MathurNo ratings yet
- Anomaly Detection: A TutorialDocument101 pagesAnomaly Detection: A TutorialBalajiNo ratings yet
- A Comprehensive Survey of 6G Wireless Communications: Pervasive/collective AIDocument34 pagesA Comprehensive Survey of 6G Wireless Communications: Pervasive/collective AIace.kris8117No ratings yet
- ML Notes Unit 1-2Document55 pagesML Notes Unit 1-2Mudit MattaNo ratings yet
- P P P A M L A: Rediction of Orosity and Ermeability Lteration Based On Achine Earning LgorithmsDocument19 pagesP P P A M L A: Rediction of Orosity and Ermeability Lteration Based On Achine Earning LgorithmsAbbas AlkhudafiNo ratings yet
- Content Based Image Retrieval in Peer-To-Peer NetworksDocument6 pagesContent Based Image Retrieval in Peer-To-Peer NetworksNationalinstituteDsnrNo ratings yet
- Data Mining and Machine-Learning in Time-Domain Discovery & ClassificationDocument37 pagesData Mining and Machine-Learning in Time-Domain Discovery & ClassificationZsolt BagolyNo ratings yet
- Sample Minor Project ReportDocument30 pagesSample Minor Project ReportAzhar SofiNo ratings yet
- Full Text 01Document255 pagesFull Text 01Adarsh VRNo ratings yet
- An Approach For Prediction of Crop Yield Using Machine Learning and Big Data TechniquesDocument9 pagesAn Approach For Prediction of Crop Yield Using Machine Learning and Big Data TechniquesKumara SNo ratings yet
- ADVANCED WEB DESIGN AND CONTENT MANAGEMENT ReportDocument42 pagesADVANCED WEB DESIGN AND CONTENT MANAGEMENT ReportMOHAMAD IZUDIN ABDUL RAHAMANNo ratings yet
- ML 18ai61Document2 pagesML 18ai61sharonsajan438690No ratings yet
- Machine Learning AlgorithmsDocument514 pagesMachine Learning Algorithmsbikash100% (2)
- Analysis of Common Supervised Learning Algorithms Through ApplicationDocument20 pagesAnalysis of Common Supervised Learning Algorithms Through Applicationacii journalNo ratings yet
- 4 SRFP 2023 24Document80 pages4 SRFP 2023 24am11an22thakurNo ratings yet
- MainDocument9 pagesMainrullyhimawan.tmmjNo ratings yet
- Mini Project 2 ReportDocument28 pagesMini Project 2 ReportInayat BaigNo ratings yet
- Early Detection of Epilepsy Using EEG Signals: Selvin Pradeep Kumar.S Ajitha.LDocument6 pagesEarly Detection of Epilepsy Using EEG Signals: Selvin Pradeep Kumar.S Ajitha.LPRIYANKANo ratings yet