Professional Documents
Culture Documents
Handson Syllabus CSCS 441-Fundamentals of Cyber Security.
Handson Syllabus CSCS 441-Fundamentals of Cyber Security.
Uploaded by
punam kumariCopyright:
Available Formats
You might also like
- In The Name of Love Sara AhmedDocument16 pagesIn The Name of Love Sara AhmedexistencialibreNo ratings yet
- PA VOCA Funding - Overview of The Victims of Crime Act Funding StreamDocument2 pagesPA VOCA Funding - Overview of The Victims of Crime Act Funding StreamDefendAChildNo ratings yet
- IV Year I Semester L T P C Subject Code: 4 0 0 3 Cryptography and Network Security SyllabusDocument3 pagesIV Year I Semester L T P C Subject Code: 4 0 0 3 Cryptography and Network Security SyllabuspragatiNo ratings yet
- Information Security and Cryptography Updated SyllabusDocument4 pagesInformation Security and Cryptography Updated SyllabusShivani DimriNo ratings yet
- BLOCKCHAI SyllabusDocument27 pagesBLOCKCHAI SyllabusChennamadhavuni SahithiNo ratings yet
- Course Objectives: This Course Will Enable Students ToDocument4 pagesCourse Objectives: This Course Will Enable Students Tomanchala anudeepNo ratings yet
- CSE329 - CS CIF NBA FormatDocument3 pagesCSE329 - CS CIF NBA FormatHAQNo ratings yet
- Cryptography and Network SecurityDocument4 pagesCryptography and Network SecurityNithyasri ArumugamNo ratings yet
- 21CS602-CNS-UNIT-1 UpdatedDocument64 pages21CS602-CNS-UNIT-1 UpdatedADUSUMALLI LAKSHMI PRIYANo ratings yet
- Computer Security and Audit Assurance SyllabusDocument23 pagesComputer Security and Audit Assurance Syllabus20-6214 Nani DandaNo ratings yet
- Open Electives Cse SyllabusDocument27 pagesOpen Electives Cse Syllabusyamini seshakalaNo ratings yet
- Final Year BTech CSE Syllabus 2022-23Document59 pagesFinal Year BTech CSE Syllabus 2022-23Utkarsha SutarNo ratings yet
- Introduction To Information SecurityDocument5 pagesIntroduction To Information SecurityjamesNo ratings yet
- CS8792 CNS Unit 1 - R1Document89 pagesCS8792 CNS Unit 1 - R1Loner VishalNo ratings yet
- Pg-Diploma in Cyber Security PDFDocument15 pagesPg-Diploma in Cyber Security PDFKang DedeNo ratings yet
- Network Security Protocols - S8 CSE-2019 Scheme-SyllabusDocument9 pagesNetwork Security Protocols - S8 CSE-2019 Scheme-SyllabusASHNA ANo ratings yet
- Fundamental of Cyber SecurityDocument2 pagesFundamental of Cyber Securitymanoj998620No ratings yet
- Syllabus-Cryptography and Network SecurityDocument2 pagesSyllabus-Cryptography and Network Securitychaithanyasgowda10No ratings yet
- Fundamental of Computers & Networks - 22MBAR0380Document16 pagesFundamental of Computers & Networks - 22MBAR0380Nalin SNo ratings yet
- English Preparation Guide Cisef 201805Document18 pagesEnglish Preparation Guide Cisef 201805Matheus ArudaNo ratings yet
- Bca III Year 2021-22Document36 pagesBca III Year 2021-22GSM XairixNo ratings yet
- 6th Sem SyllabusDocument33 pages6th Sem SyllabusAsli AccountNo ratings yet
- 28785ITC Course OutlineDocument3 pages28785ITC Course OutlineAtkah khanNo ratings yet
- 11B1WCI836-Network Management - Couirse DescriptionDocument4 pages11B1WCI836-Network Management - Couirse DescriptionjagpreetsidhuNo ratings yet
- 5th Sem Syllabus Iem 2023Document17 pages5th Sem Syllabus Iem 2023ransom3009No ratings yet
- Sms Intruder AlarmDocument15 pagesSms Intruder AlarmOjobo BlessingNo ratings yet
- Module-3 Practical ExerciseDocument81 pagesModule-3 Practical Exerciserakshitt10No ratings yet
- SyllabusDocument2 pagesSyllabusRama ChandranNo ratings yet
- Ethical Hacking Syllabus FinalDocument2 pagesEthical Hacking Syllabus FinalTraining DeskNo ratings yet
- CSS (Computer System Security)Document162 pagesCSS (Computer System Security)Ashmit JaiswalNo ratings yet
- Syllabus For Cyber Security.Document3 pagesSyllabus For Cyber Security.Roushan GiriNo ratings yet
- Fundamental of Computers & Networks - 22MBAR0069 - ArunDocument33 pagesFundamental of Computers & Networks - 22MBAR0069 - ArunNalin SNo ratings yet
- 22620-Network and Information Security 241219Document8 pages22620-Network and Information Security 241219darshit rupareliyaNo ratings yet
- MTech - Syllabus - Final 2.0Document23 pagesMTech - Syllabus - Final 2.0prasathNo ratings yet
- Web Security (CAT-309) - Unit 1 Lecture 1Document10 pagesWeb Security (CAT-309) - Unit 1 Lecture 120BCA1382 GYAN VARDHANNo ratings yet
- SyllabyusDocument6 pagesSyllabyusRama ChandranNo ratings yet
- KTU S7 Elective: CST433 Security in ComputingDocument8 pagesKTU S7 Elective: CST433 Security in ComputingJishnu ManikkothNo ratings yet
- B.Tech Third Year Syllabus - EMBEDDED SYSTEMSDocument6 pagesB.Tech Third Year Syllabus - EMBEDDED SYSTEMSMAHESWARY SREENATH ECNo ratings yet
- Information Assurance and SecurityDocument2 pagesInformation Assurance and Securityfikru tesefayeNo ratings yet
- 01 Ad8602 Dis Unit 1Document78 pages01 Ad8602 Dis Unit 1BRINDHANo ratings yet
- CSC340 CN CDF V3.1Document2 pagesCSC340 CN CDF V3.1Faizan KhanNo ratings yet
- Mba Ba Semii El DMSQLP LTPDocument4 pagesMba Ba Semii El DMSQLP LTPselladurai designNo ratings yet
- Computer System Security QuantumDocument158 pagesComputer System Security QuantumVarshika Gangwar100% (2)
- Alliance College of Engineering and DesignDocument8 pagesAlliance College of Engineering and Designpunam kumariNo ratings yet
- 05 Ad8602 Dis Unit 5Document70 pages05 Ad8602 Dis Unit 5BRINDHANo ratings yet
- Program Name Program Code: Co/Cm/If/Cw Course Title Course Code 22620 1. RationaleDocument8 pagesProgram Name Program Code: Co/Cm/If/Cw Course Title Course Code 22620 1. Rationaleyourname sofarNo ratings yet
- Part C: Course Specific: 40 (As Prescribed by AKTU) 4 Jyotirmay - Patel@srms - Ac.inDocument17 pagesPart C: Course Specific: 40 (As Prescribed by AKTU) 4 Jyotirmay - Patel@srms - Ac.inShubhamNo ratings yet
- Blockchain Essentials & DappsDocument125 pagesBlockchain Essentials & DappsBharath Kumar T V100% (1)
- FoW - Network Security - Unit No 1Document33 pagesFoW - Network Security - Unit No 1Savi AkolkarNo ratings yet
- Syllabus - CRYPTOGRAPHY AND SECURITYDocument4 pagesSyllabus - CRYPTOGRAPHY AND SECURITYnaresh2004.sNo ratings yet
- 04 Ad8602 Dis Unit 4Document95 pages04 Ad8602 Dis Unit 4BRINDHANo ratings yet
- SCADA Attack Trees FinalDocument9 pagesSCADA Attack Trees FinalNelsonNo ratings yet
- MCA - II SEMESTER Syllabus and Bridge CourseDocument33 pagesMCA - II SEMESTER Syllabus and Bridge Coursevishalsinghsoft62No ratings yet
- MCSCB Cyber SecurityDocument16 pagesMCSCB Cyber SecurityKrishna Kumaran ThampiNo ratings yet
- Department of Computer Science and EngineeringDocument22 pagesDepartment of Computer Science and EngineeringNishitha PriyankaNo ratings yet
- Pe - Iv - Wireless and Mobile NetworksDocument2 pagesPe - Iv - Wireless and Mobile Networkssivasankari.csbsNo ratings yet
- CNS SyllabusDocument5 pagesCNS Syllabussaru priyaNo ratings yet
- III Year 2nd Semester Syllabus2022Document17 pagesIII Year 2nd Semester Syllabus2022Ecell FarewellNo ratings yet
- Dbms Lab ManualDocument60 pagesDbms Lab Manualbadrujamashaik08No ratings yet
- Computer Networks & Security, BSC (Hons) - UCLanDocument18 pagesComputer Networks & Security, BSC (Hons) - UCLanMike MikkelsenNo ratings yet
- Module 1 DCNDocument150 pagesModule 1 DCNrakshitt10No ratings yet
- Alliance University: Course Delivery and Assessment PlanDocument7 pagesAlliance University: Course Delivery and Assessment Planpunam kumariNo ratings yet
- CS Sample Syllabus FormatDocument3 pagesCS Sample Syllabus Formatpunam kumariNo ratings yet
- Syllabus CSE Fundamentals of Cyber SecurityDocument2 pagesSyllabus CSE Fundamentals of Cyber Securitypunam kumariNo ratings yet
- Alliance College of Engineering and DesignDocument8 pagesAlliance College of Engineering and Designpunam kumariNo ratings yet
- Text Book: Let Us Python - 4th Edition Yashavant Kanetkar, Aditya KanetkarDocument93 pagesText Book: Let Us Python - 4th Edition Yashavant Kanetkar, Aditya Kanetkarpunam kumariNo ratings yet
- Government Accounting ProblemsDocument4 pagesGovernment Accounting ProblemsApril ManjaresNo ratings yet
- Presentation On Insider TradingDocument8 pagesPresentation On Insider TradingCA Gaurav KanudawalaNo ratings yet
- Manese V Jollibee (SUN)Document5 pagesManese V Jollibee (SUN)Peter Joshua OrtegaNo ratings yet
- BugkalotDocument3 pagesBugkalotADMIN OFFICERNo ratings yet
- Human Loyal Traits QualitiesDocument6 pagesHuman Loyal Traits QualitiesAnonymous oTtlhPNo ratings yet
- MPRA Paper 74730Document15 pagesMPRA Paper 74730soundarya mahalingamNo ratings yet
- Siy vs. NLRC G.R. No. 158971, August 25, 2005Document4 pagesSiy vs. NLRC G.R. No. 158971, August 25, 2005MykaNo ratings yet
- CIR Vs St. Paul DigestDocument2 pagesCIR Vs St. Paul DigestElise Marie BertosNo ratings yet
- SIMI Fictions Tehelka PDFDocument68 pagesSIMI Fictions Tehelka PDFgaurav ghoshNo ratings yet
- Electrotel Spectracell WRFDocument41 pagesElectrotel Spectracell WRFLaurentiu CatalinNo ratings yet
- History of The English Languge and Globe EnglishDocument167 pagesHistory of The English Languge and Globe EnglishglanNo ratings yet
- Data Processing Agreement - MillionVerifierDocument7 pagesData Processing Agreement - MillionVerifierDorian Joel ZúñigaNo ratings yet
- Yukata Onsen Ryokan: Shrine KamiDocument12 pagesYukata Onsen Ryokan: Shrine KamiRonalyn ColladoNo ratings yet
- Profile Company Bhavana Bonafide IndonesiaDocument11 pagesProfile Company Bhavana Bonafide IndonesiaathaadiwidyaludfiNo ratings yet
- Unit 6Document10 pagesUnit 6Prachi UpadhyayNo ratings yet
- Debat Bahasa InggrisDocument4 pagesDebat Bahasa Inggrisnadela981No ratings yet
- Sha DM 0910Document2 pagesSha DM 0910shashank guptaNo ratings yet
- CS Unitec - ATEX - Working in Ex ZonesDocument2 pagesCS Unitec - ATEX - Working in Ex Zonesmate_matic34No ratings yet
- Reservation Confirmation Sample: Guest NameDocument2 pagesReservation Confirmation Sample: Guest NameNabin ShakyaNo ratings yet
- Alamag, B.O. - Rizal's BiographyDocument3 pagesAlamag, B.O. - Rizal's BiographyResel O. GalloNo ratings yet
- Training Methods of TigerDocument7 pagesTraining Methods of TigerSalvador PerazaNo ratings yet
- L/epublic of Tue Flbilippine.s': $upreme (!j:ourtDocument31 pagesL/epublic of Tue Flbilippine.s': $upreme (!j:ourtKarl Rigo AndrinoNo ratings yet
- Triggers of Internationalisation - UOLDocument17 pagesTriggers of Internationalisation - UOLMarlena DrzewskaNo ratings yet
- Introduction of BriberyDocument10 pagesIntroduction of BriberyAnonymous cOdJm4OAMmNo ratings yet
- A Maqāma Collection by A Mamlūk Historian: Mu Ammad Al - Afadī (Fl. First Quarter of The 8th/14th C.)Document33 pagesA Maqāma Collection by A Mamlūk Historian: Mu Ammad Al - Afadī (Fl. First Quarter of The 8th/14th C.)mpomeranNo ratings yet
- Earthquake HazardsDocument2 pagesEarthquake HazardsDexter Jimenez ResullarNo ratings yet
- Was Imam Ali A MisogynistDocument32 pagesWas Imam Ali A MisogynistJosé AntônioNo ratings yet
- Puente Temburong, Brunei - Diseño de Dos Puentes AtirantadosDocument7 pagesPuente Temburong, Brunei - Diseño de Dos Puentes AtirantadosRONALD ABRAHAM SAMCA MONTAÑONo ratings yet
Handson Syllabus CSCS 441-Fundamentals of Cyber Security.
Handson Syllabus CSCS 441-Fundamentals of Cyber Security.
Uploaded by
punam kumariOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Handson Syllabus CSCS 441-Fundamentals of Cyber Security.
Handson Syllabus CSCS 441-Fundamentals of Cyber Security.
Uploaded by
punam kumariCopyright:
Available Formats
COURSE
Fundamentals of Cyber Security CREDITS 3
TITLE
COURSE COURSE
CSCS 441 Core/PE/OE/Minor L-T-P 3-0-0
CODE CATEGORY
LEARNING
Version Approval Details BTL-3
LEVEL
ASSESSMENT SCHEME
Semester End
During Semester Assessment (DSA)
Examination
MSE-1 MSE-2 DSA Components Attendance SEE
10% 10% 25% 5% 50%
In this Fundamental of Cyber security, you will be given an extensive overview of the various branches of computing
security. You will learn cybersecurity concepts, issues, and tools that are critical in solving problems in the computing
Course security domain.
Description You will have opportunities to learn essential techniques in protecting systems and network infrastructures, analyzing
and monitoring potential threats and attacks, devising and implementing security solutions for organizations large or
small.
1. Exhibit knowledge to secure corrupted systems, protect personal data, and secure computer networks in an
organization.
2. Practice with an expertise in academics to design and implement security solutions.
Course
3. Understand key terms and concepts in Cryptography, Governance and Compliance.
Objective
4. Develop cyber security strategies and policies
5. Understand principles of web security and to guarantee a secure network by monitoring and analyzing the nature
of attacks through cyber/computer forensics software/tools.
Upon completion of this course, the students will be able to
1. Analyze and evaluate the cyber security needs of an organization.
2. Determine and analyze software vulnerabilities and security solutions to reduce the risk of exploitation.
Course 3. Measure the performance and troubleshoot cyber security systems.
Outcome 4. Implement cyber security solutions and use of cyber security, information assurance, and cyber/computer forensics
software/tools.
5. Comprehend and execute risk management processes, risk treatment methods, and key risk and performance
indicators.
Prerequisites:
CO, PO AND PSO MAPPING
PO PO- PO- PO- PO- PO- PO- PO- PO- PO - PO- PO- PSO- PSO- PSO-
CO
-1 2 3 4 5 6 7 8 9 10 11 12 1 2 3
CO-1 1 - - - - - - - - - - - -
CO-2 2 3 2 - - 2 2 - - - - - - - -
CO-3 2 3 2 - 3 2 2 - - 2 - - 1 - -
CO-4 2 3 2 2 3 3 2 - 2 2 2 3 2 2 2
CO-5 2 2 2 3 3 3 2 2 2 3 2 3 2 2 2
1: Weakly related, 2: Moderately related and 3: Strongly related
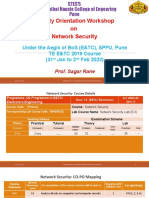
MODULE 1: Introduction to Computer Security(9hrs)
How Seriously Should You Take Threats to Network Security? - Identifying Types of Threats - Assessing the
Likelihood of an Attack on Your Network - Networks and the Internet - Network Basics - How the internet Works -
History of the Internet - Basic Network Utilities – Other Network Devices - Advanced Network Communications CO-1
Topics
Hands ON: Network Interfaces on the Kali Linux, Identify the Network Routes in the System ,DNS Lookup and
reverse lookup
Network Analysis using tcpdump
MODULE 2: Cyber Stalking, Fraud, and Abuse(9hrs)
- How Internet Fraud Works - Identity Theft –Cyber Stalking - Protecting Yourself against Cyber Crime - Denial of
Service Attacks -Denial of Service - Illustrating an Attack - Common Tools Used for DoS .- DoS Weaknesses - CO-2
Specific DoS attacks - Land Attack-Distributed Denial of Service (DDoS)
Hands On: Identify Open Port using telnet, Network Scanning using Hping3 ,Scanning TCP services using NMAP
MODULE 3: Malware - Viruses(9hrs)
Unit – III
- How a Virus Spreads - Trojan Horses - The Buffer-Overflow Attack- The Sasser Virus/Buffer Overflow - Spyware -
Other Forms of Malware – Detecting and Eliminating Viruses and Spyware - Techniques Used by Hackers - Basic CO-3
Terminology - The Reconnaissance Phase - Actual Attacks
Hands On: Capturing Session Tokens with Burp Suite
MODULE 4: Industrial Espionage in Cyberspace(9hrs)
What Is Industrial Espionage? - Information as an Asset - Real-World Examples of Industrial Espionage - How Does
Espionage Occur? - Phone Taps and Bugs - Protecting against Industrial Espionage - Industrial Espionage Act - Spear CO-4
Phishing - Encryption - Cryptography Basics- History of Encryption- Modern Methods - Legitimate Versus Fraudulent
Encryption Methods
MODULE 5: Computer Security Software (9hrs)
Virus Scanners - Firewalls - Antispyware - Intrusion-Detection Software - Network Scanning and Vulnerability
Scanning -Basics of Assessing a System - Securing Computer Systems - Cyber Terrorism and Information Warfare
Actual Cases of Cyber Terrorism -China Eagle Union- Economic Attacks -Military Operations Attacks- General CO-5
Attacks - Supervisory Control and Data Acquisitions - Information Warfare- Actual Cases.
Cyber Security using Machine Learning: Cyber Threat Identification, A.I in Cyber security, Future Machine Learning,
and cyber security,
Project : Spam detection using ML
TEXT BOOKS
1. Chuck Easttom, “Computer Security Fundamentals” Second edition, Pearson education, 2012
REFERENCE BOOKS
Charles J. Brooks, Christopher Grow, Philip Craig, Donald Short, “Cyber Security Essentials, Wiley publication
1.
2. Erdal Ozkaya, “Cybersecurity: the Beginner's Guide”, Packet publication 2019.
E BOOKS
1. https://uou.ac.in/sites/default/files/slm/Introduction-cyber-security.pdf
MOOC
1. https://www.youtube.com/watch?v=w9dkh1cfB6Y
You might also like
- In The Name of Love Sara AhmedDocument16 pagesIn The Name of Love Sara AhmedexistencialibreNo ratings yet
- PA VOCA Funding - Overview of The Victims of Crime Act Funding StreamDocument2 pagesPA VOCA Funding - Overview of The Victims of Crime Act Funding StreamDefendAChildNo ratings yet
- IV Year I Semester L T P C Subject Code: 4 0 0 3 Cryptography and Network Security SyllabusDocument3 pagesIV Year I Semester L T P C Subject Code: 4 0 0 3 Cryptography and Network Security SyllabuspragatiNo ratings yet
- Information Security and Cryptography Updated SyllabusDocument4 pagesInformation Security and Cryptography Updated SyllabusShivani DimriNo ratings yet
- BLOCKCHAI SyllabusDocument27 pagesBLOCKCHAI SyllabusChennamadhavuni SahithiNo ratings yet
- Course Objectives: This Course Will Enable Students ToDocument4 pagesCourse Objectives: This Course Will Enable Students Tomanchala anudeepNo ratings yet
- CSE329 - CS CIF NBA FormatDocument3 pagesCSE329 - CS CIF NBA FormatHAQNo ratings yet
- Cryptography and Network SecurityDocument4 pagesCryptography and Network SecurityNithyasri ArumugamNo ratings yet
- 21CS602-CNS-UNIT-1 UpdatedDocument64 pages21CS602-CNS-UNIT-1 UpdatedADUSUMALLI LAKSHMI PRIYANo ratings yet
- Computer Security and Audit Assurance SyllabusDocument23 pagesComputer Security and Audit Assurance Syllabus20-6214 Nani DandaNo ratings yet
- Open Electives Cse SyllabusDocument27 pagesOpen Electives Cse Syllabusyamini seshakalaNo ratings yet
- Final Year BTech CSE Syllabus 2022-23Document59 pagesFinal Year BTech CSE Syllabus 2022-23Utkarsha SutarNo ratings yet
- Introduction To Information SecurityDocument5 pagesIntroduction To Information SecurityjamesNo ratings yet
- CS8792 CNS Unit 1 - R1Document89 pagesCS8792 CNS Unit 1 - R1Loner VishalNo ratings yet
- Pg-Diploma in Cyber Security PDFDocument15 pagesPg-Diploma in Cyber Security PDFKang DedeNo ratings yet
- Network Security Protocols - S8 CSE-2019 Scheme-SyllabusDocument9 pagesNetwork Security Protocols - S8 CSE-2019 Scheme-SyllabusASHNA ANo ratings yet
- Fundamental of Cyber SecurityDocument2 pagesFundamental of Cyber Securitymanoj998620No ratings yet
- Syllabus-Cryptography and Network SecurityDocument2 pagesSyllabus-Cryptography and Network Securitychaithanyasgowda10No ratings yet
- Fundamental of Computers & Networks - 22MBAR0380Document16 pagesFundamental of Computers & Networks - 22MBAR0380Nalin SNo ratings yet
- English Preparation Guide Cisef 201805Document18 pagesEnglish Preparation Guide Cisef 201805Matheus ArudaNo ratings yet
- Bca III Year 2021-22Document36 pagesBca III Year 2021-22GSM XairixNo ratings yet
- 6th Sem SyllabusDocument33 pages6th Sem SyllabusAsli AccountNo ratings yet
- 28785ITC Course OutlineDocument3 pages28785ITC Course OutlineAtkah khanNo ratings yet
- 11B1WCI836-Network Management - Couirse DescriptionDocument4 pages11B1WCI836-Network Management - Couirse DescriptionjagpreetsidhuNo ratings yet
- 5th Sem Syllabus Iem 2023Document17 pages5th Sem Syllabus Iem 2023ransom3009No ratings yet
- Sms Intruder AlarmDocument15 pagesSms Intruder AlarmOjobo BlessingNo ratings yet
- Module-3 Practical ExerciseDocument81 pagesModule-3 Practical Exerciserakshitt10No ratings yet
- SyllabusDocument2 pagesSyllabusRama ChandranNo ratings yet
- Ethical Hacking Syllabus FinalDocument2 pagesEthical Hacking Syllabus FinalTraining DeskNo ratings yet
- CSS (Computer System Security)Document162 pagesCSS (Computer System Security)Ashmit JaiswalNo ratings yet
- Syllabus For Cyber Security.Document3 pagesSyllabus For Cyber Security.Roushan GiriNo ratings yet
- Fundamental of Computers & Networks - 22MBAR0069 - ArunDocument33 pagesFundamental of Computers & Networks - 22MBAR0069 - ArunNalin SNo ratings yet
- 22620-Network and Information Security 241219Document8 pages22620-Network and Information Security 241219darshit rupareliyaNo ratings yet
- MTech - Syllabus - Final 2.0Document23 pagesMTech - Syllabus - Final 2.0prasathNo ratings yet
- Web Security (CAT-309) - Unit 1 Lecture 1Document10 pagesWeb Security (CAT-309) - Unit 1 Lecture 120BCA1382 GYAN VARDHANNo ratings yet
- SyllabyusDocument6 pagesSyllabyusRama ChandranNo ratings yet
- KTU S7 Elective: CST433 Security in ComputingDocument8 pagesKTU S7 Elective: CST433 Security in ComputingJishnu ManikkothNo ratings yet
- B.Tech Third Year Syllabus - EMBEDDED SYSTEMSDocument6 pagesB.Tech Third Year Syllabus - EMBEDDED SYSTEMSMAHESWARY SREENATH ECNo ratings yet
- Information Assurance and SecurityDocument2 pagesInformation Assurance and Securityfikru tesefayeNo ratings yet
- 01 Ad8602 Dis Unit 1Document78 pages01 Ad8602 Dis Unit 1BRINDHANo ratings yet
- CSC340 CN CDF V3.1Document2 pagesCSC340 CN CDF V3.1Faizan KhanNo ratings yet
- Mba Ba Semii El DMSQLP LTPDocument4 pagesMba Ba Semii El DMSQLP LTPselladurai designNo ratings yet
- Computer System Security QuantumDocument158 pagesComputer System Security QuantumVarshika Gangwar100% (2)
- Alliance College of Engineering and DesignDocument8 pagesAlliance College of Engineering and Designpunam kumariNo ratings yet
- 05 Ad8602 Dis Unit 5Document70 pages05 Ad8602 Dis Unit 5BRINDHANo ratings yet
- Program Name Program Code: Co/Cm/If/Cw Course Title Course Code 22620 1. RationaleDocument8 pagesProgram Name Program Code: Co/Cm/If/Cw Course Title Course Code 22620 1. Rationaleyourname sofarNo ratings yet
- Part C: Course Specific: 40 (As Prescribed by AKTU) 4 Jyotirmay - Patel@srms - Ac.inDocument17 pagesPart C: Course Specific: 40 (As Prescribed by AKTU) 4 Jyotirmay - Patel@srms - Ac.inShubhamNo ratings yet
- Blockchain Essentials & DappsDocument125 pagesBlockchain Essentials & DappsBharath Kumar T V100% (1)
- FoW - Network Security - Unit No 1Document33 pagesFoW - Network Security - Unit No 1Savi AkolkarNo ratings yet
- Syllabus - CRYPTOGRAPHY AND SECURITYDocument4 pagesSyllabus - CRYPTOGRAPHY AND SECURITYnaresh2004.sNo ratings yet
- 04 Ad8602 Dis Unit 4Document95 pages04 Ad8602 Dis Unit 4BRINDHANo ratings yet
- SCADA Attack Trees FinalDocument9 pagesSCADA Attack Trees FinalNelsonNo ratings yet
- MCA - II SEMESTER Syllabus and Bridge CourseDocument33 pagesMCA - II SEMESTER Syllabus and Bridge Coursevishalsinghsoft62No ratings yet
- MCSCB Cyber SecurityDocument16 pagesMCSCB Cyber SecurityKrishna Kumaran ThampiNo ratings yet
- Department of Computer Science and EngineeringDocument22 pagesDepartment of Computer Science and EngineeringNishitha PriyankaNo ratings yet
- Pe - Iv - Wireless and Mobile NetworksDocument2 pagesPe - Iv - Wireless and Mobile Networkssivasankari.csbsNo ratings yet
- CNS SyllabusDocument5 pagesCNS Syllabussaru priyaNo ratings yet
- III Year 2nd Semester Syllabus2022Document17 pagesIII Year 2nd Semester Syllabus2022Ecell FarewellNo ratings yet
- Dbms Lab ManualDocument60 pagesDbms Lab Manualbadrujamashaik08No ratings yet
- Computer Networks & Security, BSC (Hons) - UCLanDocument18 pagesComputer Networks & Security, BSC (Hons) - UCLanMike MikkelsenNo ratings yet
- Module 1 DCNDocument150 pagesModule 1 DCNrakshitt10No ratings yet
- Alliance University: Course Delivery and Assessment PlanDocument7 pagesAlliance University: Course Delivery and Assessment Planpunam kumariNo ratings yet
- CS Sample Syllabus FormatDocument3 pagesCS Sample Syllabus Formatpunam kumariNo ratings yet
- Syllabus CSE Fundamentals of Cyber SecurityDocument2 pagesSyllabus CSE Fundamentals of Cyber Securitypunam kumariNo ratings yet
- Alliance College of Engineering and DesignDocument8 pagesAlliance College of Engineering and Designpunam kumariNo ratings yet
- Text Book: Let Us Python - 4th Edition Yashavant Kanetkar, Aditya KanetkarDocument93 pagesText Book: Let Us Python - 4th Edition Yashavant Kanetkar, Aditya Kanetkarpunam kumariNo ratings yet
- Government Accounting ProblemsDocument4 pagesGovernment Accounting ProblemsApril ManjaresNo ratings yet
- Presentation On Insider TradingDocument8 pagesPresentation On Insider TradingCA Gaurav KanudawalaNo ratings yet
- Manese V Jollibee (SUN)Document5 pagesManese V Jollibee (SUN)Peter Joshua OrtegaNo ratings yet
- BugkalotDocument3 pagesBugkalotADMIN OFFICERNo ratings yet
- Human Loyal Traits QualitiesDocument6 pagesHuman Loyal Traits QualitiesAnonymous oTtlhPNo ratings yet
- MPRA Paper 74730Document15 pagesMPRA Paper 74730soundarya mahalingamNo ratings yet
- Siy vs. NLRC G.R. No. 158971, August 25, 2005Document4 pagesSiy vs. NLRC G.R. No. 158971, August 25, 2005MykaNo ratings yet
- CIR Vs St. Paul DigestDocument2 pagesCIR Vs St. Paul DigestElise Marie BertosNo ratings yet
- SIMI Fictions Tehelka PDFDocument68 pagesSIMI Fictions Tehelka PDFgaurav ghoshNo ratings yet
- Electrotel Spectracell WRFDocument41 pagesElectrotel Spectracell WRFLaurentiu CatalinNo ratings yet
- History of The English Languge and Globe EnglishDocument167 pagesHistory of The English Languge and Globe EnglishglanNo ratings yet
- Data Processing Agreement - MillionVerifierDocument7 pagesData Processing Agreement - MillionVerifierDorian Joel ZúñigaNo ratings yet
- Yukata Onsen Ryokan: Shrine KamiDocument12 pagesYukata Onsen Ryokan: Shrine KamiRonalyn ColladoNo ratings yet
- Profile Company Bhavana Bonafide IndonesiaDocument11 pagesProfile Company Bhavana Bonafide IndonesiaathaadiwidyaludfiNo ratings yet
- Unit 6Document10 pagesUnit 6Prachi UpadhyayNo ratings yet
- Debat Bahasa InggrisDocument4 pagesDebat Bahasa Inggrisnadela981No ratings yet
- Sha DM 0910Document2 pagesSha DM 0910shashank guptaNo ratings yet
- CS Unitec - ATEX - Working in Ex ZonesDocument2 pagesCS Unitec - ATEX - Working in Ex Zonesmate_matic34No ratings yet
- Reservation Confirmation Sample: Guest NameDocument2 pagesReservation Confirmation Sample: Guest NameNabin ShakyaNo ratings yet
- Alamag, B.O. - Rizal's BiographyDocument3 pagesAlamag, B.O. - Rizal's BiographyResel O. GalloNo ratings yet
- Training Methods of TigerDocument7 pagesTraining Methods of TigerSalvador PerazaNo ratings yet
- L/epublic of Tue Flbilippine.s': $upreme (!j:ourtDocument31 pagesL/epublic of Tue Flbilippine.s': $upreme (!j:ourtKarl Rigo AndrinoNo ratings yet
- Triggers of Internationalisation - UOLDocument17 pagesTriggers of Internationalisation - UOLMarlena DrzewskaNo ratings yet
- Introduction of BriberyDocument10 pagesIntroduction of BriberyAnonymous cOdJm4OAMmNo ratings yet
- A Maqāma Collection by A Mamlūk Historian: Mu Ammad Al - Afadī (Fl. First Quarter of The 8th/14th C.)Document33 pagesA Maqāma Collection by A Mamlūk Historian: Mu Ammad Al - Afadī (Fl. First Quarter of The 8th/14th C.)mpomeranNo ratings yet
- Earthquake HazardsDocument2 pagesEarthquake HazardsDexter Jimenez ResullarNo ratings yet
- Was Imam Ali A MisogynistDocument32 pagesWas Imam Ali A MisogynistJosé AntônioNo ratings yet
- Puente Temburong, Brunei - Diseño de Dos Puentes AtirantadosDocument7 pagesPuente Temburong, Brunei - Diseño de Dos Puentes AtirantadosRONALD ABRAHAM SAMCA MONTAÑONo ratings yet