Professional Documents
Culture Documents
Certificacion Ad Forensics 5-Day Parte 2 de 2
Certificacion Ad Forensics 5-Day Parte 2 de 2
Uploaded by
Elmer Quispia asteteCopyright:
Available Formats
You might also like
- FTK ToolKitDocument4 pagesFTK ToolKitMaria Eugenia Casco100% (1)
- PE & COFF Specification v8.2Document97 pagesPE & COFF Specification v8.2Crend King100% (1)
- Computer Forensics FinalDocument34 pagesComputer Forensics FinalPrathima Prahalad100% (1)
- Infsci 2150: Introduction To Security and Privacy Lab: Operating Systems and Access ControlDocument20 pagesInfsci 2150: Introduction To Security and Privacy Lab: Operating Systems and Access ControlWu Yuqiao0% (1)
- SRS - How to build a Pen Test and Hacking PlatformFrom EverandSRS - How to build a Pen Test and Hacking PlatformRating: 2 out of 5 stars2/5 (1)
- FTK101 Syllabus 2022Document4 pagesFTK101 Syllabus 2022Alan SmithNo ratings yet
- AccessData FTK Intermediate Course SyllabusDocument3 pagesAccessData FTK Intermediate Course SyllabusdumkoliveiraNo ratings yet
- Disk Tools and Data Capture: Name From DescriptionDocument10 pagesDisk Tools and Data Capture: Name From Descriptionoh ohoNo ratings yet
- What Is Forensic Toolkit (FTK) ?Document7 pagesWhat Is Forensic Toolkit (FTK) ?Shaban MahekulaNo ratings yet
- Using PowerShell To Capture and Compare Windows Registry and Live Memory Artifacts With Online Databases To Identify Suspect FilesDocument12 pagesUsing PowerShell To Capture and Compare Windows Registry and Live Memory Artifacts With Online Databases To Identify Suspect Filesrohto1945No ratings yet
- Free Computer Forensic SoftwareDocument18 pagesFree Computer Forensic SoftwarehypnnusNo ratings yet
- Top 10 FTK Features WP FinalDocument7 pagesTop 10 FTK Features WP FinalerikafuentesNo ratings yet
- Breakup of SyllabusDocument5 pagesBreakup of SyllabusVishwanath ITINo ratings yet
- 140 Herramientas Gratuitas para Análisis ForenseDocument14 pages140 Herramientas Gratuitas para Análisis ForenseMaria Del Carmen ChableNo ratings yet
- Access Data FTK ImagerDocument4 pagesAccess Data FTK Imagerpesan97384No ratings yet
- Most Used Digital Forensics ToolsDocument9 pagesMost Used Digital Forensics Toolsprathimapesaru7No ratings yet
- 1 s2.0 S1742287610000575 MainDocument5 pages1 s2.0 S1742287610000575 MainBNo ratings yet
- Windows Operating Systems Agnostic Memory Analysis: James Okolica, Gilbert L. PetersonDocument9 pagesWindows Operating Systems Agnostic Memory Analysis: James Okolica, Gilbert L. PetersonsulisNo ratings yet
- DF 5994 Paper IeeeDocument6 pagesDF 5994 Paper Ieeelucas caicedoNo ratings yet
- 2 SoftwareDevelopmentDocument14 pages2 SoftwareDevelopmentThanh Võ Thị HoàiNo ratings yet
- Practical No 01 Title: Working With Windows Forensic Toolkit (Accessdata FTK) TheoryDocument14 pagesPractical No 01 Title: Working With Windows Forensic Toolkit (Accessdata FTK) TheoryyatharthNo ratings yet
- Windows Registry: A Complete Guide To Examining The Windows RegistryDocument11 pagesWindows Registry: A Complete Guide To Examining The Windows RegistryKarina GomezNo ratings yet
- Mini Documentation Hardware InformationDocument37 pagesMini Documentation Hardware Informationmatangi_88No ratings yet
- Forensic Toolkit: Sales and Promotional SummaryDocument8 pagesForensic Toolkit: Sales and Promotional Summaryclu5t3rNo ratings yet
- SYLLBUS COPA2014reviesed PDFDocument16 pagesSYLLBUS COPA2014reviesed PDFcniraj743566No ratings yet
- 20 Herramientas de Forense - Win - LinuxDocument24 pages20 Herramientas de Forense - Win - LinuxAlma YaritzaNo ratings yet
- IAEA SpecificationDocument13 pagesIAEA Specificationswapnil koleNo ratings yet
- 05-Computer Forensic ToolsDocument53 pages05-Computer Forensic ToolsAnonymous Rn7azW100% (1)
- Dynamic Analysis of Firmware Components in IoT DevicesDocument23 pagesDynamic Analysis of Firmware Components in IoT DevicesEugeNo ratings yet
- UNI File Spec v1.3Document22 pagesUNI File Spec v1.3Having NeverNo ratings yet
- Lecture 6-Forensic ToolsDocument46 pagesLecture 6-Forensic ToolsTing Zhi Peng (Ethan)No ratings yet
- "TIGER" OCR Library: (For Microsoft Windows NT and Windows 98/95)Document42 pages"TIGER" OCR Library: (For Microsoft Windows NT and Windows 98/95)war lockNo ratings yet
- NIST Data Leakage 00 Env SettingDocument48 pagesNIST Data Leakage 00 Env SettingwanNo ratings yet
- Windows Registry ForesicsDocument25 pagesWindows Registry ForesicsAPRIL ELLEN DELOS REYES100% (1)
- Top 10 FTK Features WP FINAL 2023Document7 pagesTop 10 FTK Features WP FINAL 2023mahdi aghaeiNo ratings yet
- Foundation - Apple Developer DocumentationDocument4 pagesFoundation - Apple Developer DocumentationSamantha De Cárdenas100% (1)
- ED600 SyllabusDocument9 pagesED600 SyllabusVenkat EshwariNo ratings yet
- Exterro FTK 7.5.1-Release NotesDocument17 pagesExterro FTK 7.5.1-Release NotesMuhammad ZulkhairiNo ratings yet
- Party Toonz: Media Player and Database LibraryDocument5 pagesParty Toonz: Media Player and Database Libraryapi-27070090No ratings yet
- Cisco Endpoint IOC AttributesDocument10 pagesCisco Endpoint IOC AttributesKiril PetkovNo ratings yet
- 2 It302g Linux OsDocument8 pages2 It302g Linux OsAmit DeshaiNo ratings yet
- IPXACT-Based RTL Generation ToolDocument4 pagesIPXACT-Based RTL Generation ToolQi JiaNo ratings yet
- Course 70-210Document5 pagesCourse 70-210KamalGhazaliNo ratings yet
- Lab 7 Examining The Windws RegistryDocument6 pagesLab 7 Examining The Windws RegistryMuhammad Badrul AzharNo ratings yet
- M-2 SoftwareDevelopmentDocument12 pagesM-2 SoftwareDevelopmentywq885233326No ratings yet
- How Registry Is Helpful in Managing Security.: Term Paper OnDocument13 pagesHow Registry Is Helpful in Managing Security.: Term Paper OnAshish VaniyaNo ratings yet
- FTK DataSheet - AccessDataDocument2 pagesFTK DataSheet - AccessDataaccessdataNo ratings yet
- Diploma in I.T Technical Support: Assignment Title: The Boot Process in Windows and UbuntuDocument14 pagesDiploma in I.T Technical Support: Assignment Title: The Boot Process in Windows and Ubuntuصفوان قشقري100% (1)
- FortiAnalyzer Course Description-Online-NEWDocument2 pagesFortiAnalyzer Course Description-Online-NEWCarlosDavidTorresNo ratings yet
- CNS 320 Week4 LectureDocument74 pagesCNS 320 Week4 Lecturealb3rtlinNo ratings yet
- Interview QuestionDocument9 pagesInterview Questionsonupawar8883No ratings yet
- Memor X3 SDK Readme PDFDocument3 pagesMemor X3 SDK Readme PDFpigueloNo ratings yet
- A Practitioners Guide To The Forensic Investigation of Xbox 360 Gaming ConsolesDocument23 pagesA Practitioners Guide To The Forensic Investigation of Xbox 360 Gaming Consolesmav87th-1No ratings yet
- PE File HeaderDocument128 pagesPE File HeaderQuốc TuấnNo ratings yet
- File Hawk SpecificationsDocument2 pagesFile Hawk SpecificationsCity VilleNo ratings yet
- CHFI Crash Study GuideDocument9 pagesCHFI Crash Study Guidecyber forensicNo ratings yet
- Exterro FTK and FTK Lab 8.0-Release NotesDocument35 pagesExterro FTK and FTK Lab 8.0-Release NotesIlham AdzieNo ratings yet
- BCD EditDocument22 pagesBCD EditpedrokaulsNo ratings yet
- Tutorial To Install 3D AikidoDocument2 pagesTutorial To Install 3D AikidoDexter JamesNo ratings yet
- RegrunlogDocument91 pagesRegrunlogPaijo BantulNo ratings yet
- Trend Micro Endpoint Agent - Installation ManualDocument14 pagesTrend Micro Endpoint Agent - Installation Manualsse contractNo ratings yet
- UsbFix ReportDocument2 pagesUsbFix ReportBourama DIAKITENo ratings yet
- Oracle R12 Form 10G CustomizationDocument8 pagesOracle R12 Form 10G CustomizationrameshibmNo ratings yet
- Hacking With Experts by Anurag Dwivedi PDFDocument156 pagesHacking With Experts by Anurag Dwivedi PDFKeshav VermaNo ratings yet
- Windows NT Startup ProcessDocument8 pagesWindows NT Startup ProcessSaravanan MohanNo ratings yet
- RSLogix Emulate 5000 - Internal Error! Failed To Install RSLogix Emulate 5000 in Slot!Document2 pagesRSLogix Emulate 5000 - Internal Error! Failed To Install RSLogix Emulate 5000 in Slot!Álvaro HernándezNo ratings yet
- DOCDocument114 pagesDOCElving MendozaNo ratings yet
- Errors and StepsDocument7 pagesErrors and StepssudharaghavanNo ratings yet
- Anti Forensics GuideDocument9 pagesAnti Forensics GuideDelin BardhiNo ratings yet
- Reference Guide The Open Distribution System Simulator (Opendss)Document232 pagesReference Guide The Open Distribution System Simulator (Opendss)TerrorTricolorFCNo ratings yet
- Win 76 LinkDocument2 pagesWin 76 LinkSam Djjs NileshNo ratings yet
- Ncs DummyDocument45 pagesNcs DummyAdyNo ratings yet
- 192 168 0 187Document5 pages192 168 0 187Thuy TaNo ratings yet
- Speed Up Your PCDocument8 pagesSpeed Up Your PCvaibhav420100% (1)
- All VB6 CommandsDocument10 pagesAll VB6 CommandskhonelNo ratings yet
- SysInternals DocsDocument191 pagesSysInternals DocsGuillan Pascual100% (1)
- Alstom BcuDocument560 pagesAlstom BcuGuru Mishra100% (2)
- Detailed User Guide For TRF 01 FormDocument23 pagesDetailed User Guide For TRF 01 Formm_adil_211359No ratings yet
- Manual Oracle Express PDFDocument18 pagesManual Oracle Express PDFjjose3No ratings yet
- Windows 7 Help & Advice - October 2014-P2P PDFDocument100 pagesWindows 7 Help & Advice - October 2014-P2P PDFCarlos PocinhoNo ratings yet
- Fabrication: Machine Setup in CAM: Learning ObjectivesDocument43 pagesFabrication: Machine Setup in CAM: Learning ObjectivesJohn ContrerasNo ratings yet
- PipelineStudio Installation GuideDocument27 pagesPipelineStudio Installation GuideRodrigo MadariagaNo ratings yet
- PSCADDocument10 pagesPSCADkaran976No ratings yet
- How To Install XP On An External Hard Drive: Jason GordonDocument6 pagesHow To Install XP On An External Hard Drive: Jason Gordonsaman369No ratings yet
- Interviews DraftDocument187 pagesInterviews DraftSaverio GrisorioNo ratings yet
- Zabbix Documentation 6.2.enDocument1,602 pagesZabbix Documentation 6.2.enpenNo ratings yet
- SAP Router Installation Step by StepDocument20 pagesSAP Router Installation Step by StepIrwin Cruize MhendozaNo ratings yet
Certificacion Ad Forensics 5-Day Parte 2 de 2
Certificacion Ad Forensics 5-Day Parte 2 de 2
Uploaded by
Elmer Quispia asteteOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Certificacion Ad Forensics 5-Day Parte 2 de 2
Certificacion Ad Forensics 5-Day Parte 2 de 2
Uploaded by
Elmer Quispia asteteCopyright:
Available Formats
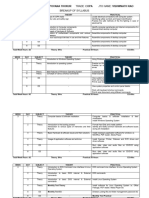
AccessData Advanced Forensics
Forensic Toolkit / FTK Imager / Registry Viewer / Password Recovery Toolkit
Intermediate • Five-Day Instructor-Led Course
This advanced five-day course provides the knowledge and skills necessary to install, configure and effectively use
Forensic Toolkit® (FTK™), FTK Imager™ Password Recovery Toolkit™ (PRTK™) and Registry Viewer™. Participants
will also use AccessData products to conduct forensic investigations on Microsoft® Windows® systems, learning where
and how to locate Windows system artifacts.
During this five-day, hands-on class, participants will perform the following tasks:
Install and configure FTK, FTK Imager, PRTK, and Registry Viewer.
Use FTK Imager to preview evidence, export evidence files, create forensic images and convert existing images.
Use the Registry Viewer to locate evidentiary information in Windows 2K and XP registry files.
Create a case in FTK.
Use FTK to process and analyze documents, metadata, graphics and e-mail.
Use bookmarks and check marks to efficiently manage and process case data.
Update and customize the KFF database.
Create and apply file filters to manage evidence in FTK.
Create regular expressions.
Import search lists for indexed searches in FTK.
Use the FTK Data Carving feature to recover files from unallocated disk space.
Use custom dictionaries and dictionary profiles to recover passwords in PRTK.
Use a FTK word list to create a custom dictionary in PRTK.
Create a user profile and biographical dictionary in PRTK.
Add SAM and Syskey values to PRTK to recover passwords and decrypt encrypted files.
Recover forensic information from Recycle Bin INFO2 files.
Recover forensic information from the following Windows XP artifacts:
o Thumbs.db files
o Metadata
o Link and Spool Files
o Alternate Data Streams
o Windows XP Prefetch
Recover EFS encrypted files on Windows 2000 and XP systems.
Create and customize reports.
The class includes multiple hands-on labs that allow students to apply what they have learned in the workshop.
Prerequisites
This hands-on class is intended for new users, particularly forensic professionals and law enforcement personnel, who
use AccessData forensic software to examine, analyze and classify digital evidence.
To obtain the maximum benefit from this class, you should meet the following requirements:
Read and understand the English language.
Perform basic operations on a personal computer.
Have a basic knowledge of computer forensic investigations and acquisition procedures.
Be familiar with the Microsoft Windows environment.
Class Materials and Software
You will receive the student training manual and CD containing the training material, lab exercises and class-related
information.
For a complete listing of scheduled courses, visit http://www.accessdata.com/training/calendar-and-syllabi
©July 8, 2013 AccessData Group, LLC. – All rights reserved.
Some topics and items in this class syllabus are subject to change. This document is for information purposes only. AccessData makes no warranties, express or implied, in this document. AccessData, AccessData Certified Examiner, ACE, AD, AD
Summation, CaseScan, CaseVantage, CaseVault, Discovery Cracker, Distributed Network Attack, DNA, Forensic Toolkit, FTK, FTK Imager, iBlaze, Mobile Phone Examiner Plus, Password Recovery Toolkit, PRTK, Registry Viewer, SilentRunner,
Summation, Summation Blaze, Summation Legal Technologies, Summation WebBlaze, The Key To Cracking It, Transender PLUS, Ultimate Toolkit, UTK, ViewerRT, and WebBlaze are trademarks of AccessData Group, LLC.in the United States
and/or other countries. Other trademarks referenced are property of their respective owners.
AccessData Advanced Forensics
Forensic Toolkit / FTK Imager / Registry Viewer / Password Recovery Toolkit
Intermediate • Five-Day Instructor-Led Course
(Continued)
Module 1: Introduction Module 3: Windows Registry
Topics Windows Registry 101
Identify the FTK components. Objectives
List the FTK and PRTK system requirements.
Describe how to receive upgrades and support for Describe the function of the Windows registry
AccessData tools. Identify the files that make up the Windows registry
Install required applications and drivers. Describe how the registry is organized
Identify forensic issues associated with multiple
Lab profiles on Windows systems
Participants will install the UTK components—FTK,
KFF Library, FTK Imager, Registry Viewer, and PRTK. Windows 2000 and XP Registries
Objectives
Module 2: Working with FTK Imager Identify the files that make up the Windows 2000
Objectives and XP registry, list their locations, and describe the
information they contain.
Describe standard data storage devices.
Identify reasons to resolve a user to a SID.
Identify some common software and hardware
acquisition tools. Identify notable tracking differences in the registry
List some common forensic image formats. on FAT and NTFS systems including a look a
tracking mounted devices.
Use FTK Imager to perform the following functions:
o Preview evidence
o Export data files Module 4: Registry Viewer
o Create a hash to benchmark your case evidence
Working with Registry Viewer
o Acquire an image of evidence data
o Convert existing images to other formats Objectives
Use dockable windows in FTK Imager. Identify the menu and toolbar options in Registry
Navigate evidence items. Viewer.
Use the properties and interpreters windows. Describe how Registry Viewer displays MRU lists.
Validate forensic images. Describe the function of the Registry Viewer's
Create Custom Content Images. common areas.
Mount images. Describe different methods to search the registry.
Capture active RAM. Create a report in Registry Viewer.
Create a Summary report in Registry Viewer.
Labs Utilize Registry Viewer help.
During the practical, participants acquire an image of a
thumb drive, then explore the FTK Imager features Lab
and functions discussed in the module, including Review the Registry Viewer interface.
converting an image to a different image format,
Harvest and view registry files.
creating a Custom Content Image, and mounting an
image.
For a complete listing of scheduled courses, visit http://www.accessdata.com/training/calendar-and-syllabi
© July 8, 2013 AccessData Group, LLC. – All rights reserved.
Some topics and items in this class syllabus are subject to change. This document is for information purposes only. AccessData makes no warranties, express or implied, in this document. AccessData, AccessData Certified Examiner, ACE, AD,
AD Summation, CaseScan, CaseVantage, CaseVault, Discovery Cracker, Distributed Network Attack, DNA, Forensic Toolkit, FTK, FTK Imager, iBlaze, Mobile Phone Examiner Plus, Password Recovery Toolkit, PRTK, Registry Viewer,
SilentRunner, Summation, Summation Blaze, Summation Legal Technologies, Summation WebBlaze, The Key To Cracking It, Transender PLUS, Ultimate Toolkit, UTK, ViewerRT, and WebBlaze are trademarks of AccessData Group, LLC.in the
United States and/or other countries. Other trademarks referenced are property of their respective owners.
AccessData Advanced Forensics
Forensic Toolkit / FTK Imager / Registry Viewer / Password Recovery Toolkit
Intermediate • Five-Day Instructor-Led Course
(Continued)
Module 4: Working with FTK—Part 1 Lab
The labs in this module guide participants through
Objectives
more advanced functions in processing case evidence.
Effectively use the Case Manager. During the practical, participants will bookmark
Create and administer users. evidence, view metadata and compound files, examine
Back up, delete, and restore cases. registry files, recover deleted files from the Recycle
Bin, export case files and folders, create custom
Identify the evidence processing options.
column settings, decrypt files, and use the data
Create a case. carving feature to recover evidence items from file
Identify the basic FTK interface components, slack and unallocated space.
including the menu and toolbar options as well as
the program tabs.
Obtain basic analysis data. Module 6: Processing the Case
Objectives
Lab Identify the elements of a graphics case.
During the practical, participants go through the introductory
Navigate the FTK Graphics tab.
steps of processing a case, including creating a case,
adding evidence to the case, and processing case evidence. Export graphics files and hash sets.
Students will also perform basic system functions such as Tag graphics files using the Bookmarks feature.
creating user accounts and defining different levels of Identify the elements of an email case.
permissions to a case, managing shared objects, and Identify supported email types.
customizing the FTK interface.
Navigate the FTK Email tab.
Sort email.
Module 5: Working with FTK—Part 2 Find a word or phrase in an email message or
attachment.
Objectives
Export email items.
Change time zone display.
Create and manage bookmarks.
Lab
View compound files.
During the practical, participants explore FTK features to
Export files and folders. view, sort, and export email and graphic artifacts from the
Create custom column settings to manage the case. Students will also create custom columns for graphics
information that appears in the FTK file list. and email, export email and graphics files, and create a
Use the Copy Special and Export File List Info hash list.
features.
Create and manage bookmarks.
Perform additional analysis, such as full text
indexing, after evidence has been added to the
case.
Perform automatic and manual data carving
functions.
For a complete listing of scheduled courses, visit http://www.accessdata.com/training/calendar-and-syllabi
© July 8, 2013 AccessData Group, LLC. – All rights reserved.
Some topics and items in this class syllabus are subject to change. This document is for information purposes only. AccessData makes no warranties, express or implied, in this document. AccessData, AccessData Certified Examiner, ACE, AD,
AD Summation, CaseScan, CaseVantage, CaseVault, Discovery Cracker, Distributed Network Attack, DNA, Forensic Toolkit, FTK, FTK Imager, iBlaze, Mobile Phone Examiner Plus, Password Recovery Toolkit, PRTK, Registry Viewer,
SilentRunner, Summation, Summation Blaze, Summation Legal Technologies, Summation WebBlaze, The Key To Cracking It, Transender PLUS, Ultimate Toolkit, UTK, ViewerRT, and WebBlaze are trademarks of AccessData Group, LLC.in the
United States and/or other countries. Other trademarks referenced are property of their respective owners.
AccessData Advanced Forensics
Forensic Toolkit / FTK Imager / Registry Viewer / Password Recovery Toolkit
Intermediate • Five-Day Instructor-Led Course
(Continued)
Module 7: Narrowing Your Focus Module 8: Filtering the Case
Objectives Objectives
Narrow evidence items using the Known File Filter, Explain basic concepts of rule-based filtering in FTK.
checked items, and filtered/ignored items. Design a basic filter and use it to filter data.
Perform an indexed search. Manage shared filters.
Perform a live search. Discuss the use of compound filters.
Import search terms from text files. Explain the difference between global and tab filters.
Perform a regular expression search. Import and export filters.
Lab Lab
During the practical, participants learn how to During the labs, participants create filters to locate
effectively sort through case evidence to locate items specific items of interest. Students will further refine
of interest. Students will use the KFF database to filter results using compound filters. Finally, students
ignore or flag known files, perform keyword searches, will have a change to import and export filters so they
use dtSearch options to customize a search, and use can share filters with co-workers and colleagues.
regular expressions to search case evidence for
pattern data such as credit card numbers or IP Module 6: The Recycle Bin
addresses.
Objectives
Describe the function of the Windows Recycle Bin.
Module 2: Regular Expressions Identify the differences in the Recycle Bin on FAT
Objectives and NTFS systems.
Understand basic Operators and Literals in RegEx. List what information can be recovered from the
Learn 10 very useful characters and concepts of INFO2 file.
RegEx++, enabling you to write hundreds of Describe how FTK parses and displays INFO2 files.
expressions. Describe what happens when a file is deleted or
Create and interpret a basic regular expression that removed from the Recycle Bin.
includes Function Groups and Repeat Values. Explain what happens when a user empties the
Integrate a new RegEx into FTK for use. Recycle Bin.
Integrate a new TR1 Expression into FTK for use. Identify how information can still be retrieved when
items are removed from the Recycle Bin.
Lab Describe the forensic implications of files located in
Create a regular expression and add it to the list of the Recycle Bin.
expressions in the FTK Live Search tab. Describe the function of the Orphan folder.
Perform a live search using the regular expression Create a regular expression to recover unallocated
you created. INFO2 file records.
For a complete listing of scheduled courses, visit http://www.accessdata.com/training/calendar-and-syllabi
© July 8, 2013 AccessData Group, LLC. – All rights reserved.
Some topics and items in this class syllabus are subject to change. This document is for information purposes only. AccessData makes no warranties, express or implied, in this document. AccessData, AccessData Certified Examiner, ACE, AD,
AD Summation, CaseScan, CaseVantage, CaseVault, Discovery Cracker, Distributed Network Attack, DNA, Forensic Toolkit, FTK, FTK Imager, iBlaze, Mobile Phone Examiner Plus, Password Recovery Toolkit, PRTK, Registry Viewer,
SilentRunner, Summation, Summation Blaze, Summation Legal Technologies, Summation WebBlaze, The Key To Cracking It, Transender PLUS, Ultimate Toolkit, UTK, ViewerRT, and WebBlaze are trademarks of AccessData Group, LLC.in the
United States and/or other countries. Other trademarks referenced are property of their respective owners.
AccessData Advanced Forensics
Forensic Toolkit / FTK Imager / Registry Viewer / Password Recovery Toolkit
Intermediate • Five-Day Instructor-Led Course
(Continued)
Lab Alternate Data Streams
Retrieve deleted evidence from the Recycle Bin. Objectives
Use a regular expression to locate INFO2 files. Identify the differences between named and
Retrieve the following information from INFO2 files: alternate data streams.
o Deleted File Path Identify forensic issues associated with alternate
o Deleted File Index data streams.
o Deleted File Drive Number Identify how Forensic Toolkit® (FTK®) displays
o Deleted File Date and Time alternate data streams.
Describe how alternate data streams impact file
Module 7: Common Windows XP Artifacts size, disk space, and file creation date.
Thumbs.db Files Lab
Identify alternate data stream files in your case.
Objectives
Define the Thumbs.db file. Windows Prefetch
Define Thumbs.db behavior.
Objectives
Identify thumbnail graphics. Accurately define Prefetch, Superfetch, and their
Define EFS file changes and Thumbs.db behavior. related functions.
Lab Define the forensic importance of Prefetch Registry
entries, Prefetch files, and the Layout.ini file.
Use FTK to recover graphics information from
View and analyze pertinent Prefetch artifacts as
Thumbs.db files.
they relate to case analysis and user behavior.
Link and Spool Files Lab
View Prefetch settings in the Registry.
Objectives
View Prefetch entries in FTK to find the last date
Define the function of a link file. and time an application was launched.
Identify what evidentiary information is contained in View Prefetch entries in FTK to determine the
link files. number of times an application was launched.
Describe how FTK parses and displays link files.
Define the function of a spool file and its related Module 9: Working with PRTK
files. Objectives
Identify what evidentiary information is contained in Navigate within the PRTK interface.
spool files.
Identify the available password recovery modules
Lab and their associated attack types.
Use FTK to recover forensic information from link Import user-defined dictionaries and FTK word lists
files, including the MAC address of the target to use in a password recovery attack.
machine. Create biographical dictionaries.
Use link file data to associate a file with a USB drive. Set up profiles.
Use FTK to recover forensic information from spool Explain what a PRTK profile is and how it is used.
files. Recount the AccessData Methodology.
Recover Windows logon passwords.
For a complete listing of scheduled courses, visit http://www.accessdata.com/training/calendar-and-syllabi
© July 8, 2013 AccessData Group, LLC. – All rights reserved.
Some topics and items in this class syllabus are subject to change. This document is for information purposes only. AccessData makes no warranties, express or implied, in this document. AccessData, AccessData Certified Examiner, ACE, AD,
AD Summation, CaseScan, CaseVantage, CaseVault, Discovery Cracker, Distributed Network Attack, DNA, Forensic Toolkit, FTK, FTK Imager, iBlaze, Mobile Phone Examiner Plus, Password Recovery Toolkit, PRTK, Registry Viewer,
SilentRunner, Summation, Summation Blaze, Summation Legal Technologies, Summation WebBlaze, The Key To Cracking It, Transender PLUS, Ultimate Toolkit, UTK, ViewerRT, and WebBlaze are trademarks of AccessData Group, LLC.in the
United States and/or other countries. Other trademarks referenced are property of their respective owners.
AccessData Advanced Forensics
Forensic Toolkit / FTK Imager / Registry Viewer / Password Recovery Toolkit
Intermediate • Five-Day Instructor-Led Course
(Continued)
Lab Module 9: Case Reporting
Export encrypted files from a case.
Objectives
Export a word list and create a custom dictionary.
Define a report.
Create a Biographical dictionary. o Modify the case information
Create a profile. o Include a list of bookmarked files
Recover a password. o Export bookmarked files with the report
Locate SAM and SysKey Files o Include thumbnails of bookmarked graphics
o Manage the appearance of the Bookmark section
Attack and decrypt encrypted files, then list the
o Include thumbnails of case graphics
recovered passwords.
o Link thumbnails to full-sized graphics in the report
Module 10: Encrypting File System directory
o Export and link video files
Objectives o Export rendered videos and thumbnails
Describe how EFS works. o Include a list of directories, subdirectories, files,
List the information required to recover EFS and file types
encrypted files on Windows 2000 systems. o Include a list of case files and file properties in the
List the information required to recover EFS report
encrypted files on Windows XP Professional Service o Export case files associated with specific file
Pack 1 (SP1) and later systems. categories
List potential problems associated with recovering o Append a registry report to the case report
EFS encrypted data. Generate reports in the following formats:
Lab o PDF
o HTML
Create EFS encrypted files.
o RTF
Recover EFS encrypted files in FTK. o WML
o XML
o DOCX
o ODT
Generate reports in other languages.
Lab
During the practical, participants create multiple
reports from a single case to explore all options
available from the report wizard. They build from a
very basic report to a detailed report that contains
customized report items.
Practical Skills Assessment
The Windows Forensics class includes a Practical Skills Assessment (PSA). This performance-based assessment requires
participants to apply key concepts presented during the class to complete a practical exercise. Participants who successfully
complete the exercise receive a PSA certificate of completion.
For a complete listing of scheduled courses, visit http://www.accessdata.com/training/calendar-and-syllabi
© July 8, 2013 AccessData Group, LLC. – All rights reserved.
Some topics and items in this class syllabus are subject to change. This document is for information purposes only. AccessData makes no warranties, express or implied, in this document. AccessData, AccessData Certified Examiner, ACE, AD,
AD Summation, CaseScan, CaseVantage, CaseVault, Discovery Cracker, Distributed Network Attack, DNA, Forensic Toolkit, FTK, FTK Imager, iBlaze, Mobile Phone Examiner Plus, Password Recovery Toolkit, PRTK, Registry Viewer,
SilentRunner, Summation, Summation Blaze, Summation Legal Technologies, Summation WebBlaze, The Key To Cracking It, Transender PLUS, Ultimate Toolkit, UTK, ViewerRT, and WebBlaze are trademarks of AccessData Group, LLC.in the
United States and/or other countries. Other trademarks referenced are property of their respective owners.
You might also like
- FTK ToolKitDocument4 pagesFTK ToolKitMaria Eugenia Casco100% (1)
- PE & COFF Specification v8.2Document97 pagesPE & COFF Specification v8.2Crend King100% (1)
- Computer Forensics FinalDocument34 pagesComputer Forensics FinalPrathima Prahalad100% (1)
- Infsci 2150: Introduction To Security and Privacy Lab: Operating Systems and Access ControlDocument20 pagesInfsci 2150: Introduction To Security and Privacy Lab: Operating Systems and Access ControlWu Yuqiao0% (1)
- SRS - How to build a Pen Test and Hacking PlatformFrom EverandSRS - How to build a Pen Test and Hacking PlatformRating: 2 out of 5 stars2/5 (1)
- FTK101 Syllabus 2022Document4 pagesFTK101 Syllabus 2022Alan SmithNo ratings yet
- AccessData FTK Intermediate Course SyllabusDocument3 pagesAccessData FTK Intermediate Course SyllabusdumkoliveiraNo ratings yet
- Disk Tools and Data Capture: Name From DescriptionDocument10 pagesDisk Tools and Data Capture: Name From Descriptionoh ohoNo ratings yet
- What Is Forensic Toolkit (FTK) ?Document7 pagesWhat Is Forensic Toolkit (FTK) ?Shaban MahekulaNo ratings yet
- Using PowerShell To Capture and Compare Windows Registry and Live Memory Artifacts With Online Databases To Identify Suspect FilesDocument12 pagesUsing PowerShell To Capture and Compare Windows Registry and Live Memory Artifacts With Online Databases To Identify Suspect Filesrohto1945No ratings yet
- Free Computer Forensic SoftwareDocument18 pagesFree Computer Forensic SoftwarehypnnusNo ratings yet
- Top 10 FTK Features WP FinalDocument7 pagesTop 10 FTK Features WP FinalerikafuentesNo ratings yet
- Breakup of SyllabusDocument5 pagesBreakup of SyllabusVishwanath ITINo ratings yet
- 140 Herramientas Gratuitas para Análisis ForenseDocument14 pages140 Herramientas Gratuitas para Análisis ForenseMaria Del Carmen ChableNo ratings yet
- Access Data FTK ImagerDocument4 pagesAccess Data FTK Imagerpesan97384No ratings yet
- Most Used Digital Forensics ToolsDocument9 pagesMost Used Digital Forensics Toolsprathimapesaru7No ratings yet
- 1 s2.0 S1742287610000575 MainDocument5 pages1 s2.0 S1742287610000575 MainBNo ratings yet
- Windows Operating Systems Agnostic Memory Analysis: James Okolica, Gilbert L. PetersonDocument9 pagesWindows Operating Systems Agnostic Memory Analysis: James Okolica, Gilbert L. PetersonsulisNo ratings yet
- DF 5994 Paper IeeeDocument6 pagesDF 5994 Paper Ieeelucas caicedoNo ratings yet
- 2 SoftwareDevelopmentDocument14 pages2 SoftwareDevelopmentThanh Võ Thị HoàiNo ratings yet
- Practical No 01 Title: Working With Windows Forensic Toolkit (Accessdata FTK) TheoryDocument14 pagesPractical No 01 Title: Working With Windows Forensic Toolkit (Accessdata FTK) TheoryyatharthNo ratings yet
- Windows Registry: A Complete Guide To Examining The Windows RegistryDocument11 pagesWindows Registry: A Complete Guide To Examining The Windows RegistryKarina GomezNo ratings yet
- Mini Documentation Hardware InformationDocument37 pagesMini Documentation Hardware Informationmatangi_88No ratings yet
- Forensic Toolkit: Sales and Promotional SummaryDocument8 pagesForensic Toolkit: Sales and Promotional Summaryclu5t3rNo ratings yet
- SYLLBUS COPA2014reviesed PDFDocument16 pagesSYLLBUS COPA2014reviesed PDFcniraj743566No ratings yet
- 20 Herramientas de Forense - Win - LinuxDocument24 pages20 Herramientas de Forense - Win - LinuxAlma YaritzaNo ratings yet
- IAEA SpecificationDocument13 pagesIAEA Specificationswapnil koleNo ratings yet
- 05-Computer Forensic ToolsDocument53 pages05-Computer Forensic ToolsAnonymous Rn7azW100% (1)
- Dynamic Analysis of Firmware Components in IoT DevicesDocument23 pagesDynamic Analysis of Firmware Components in IoT DevicesEugeNo ratings yet
- UNI File Spec v1.3Document22 pagesUNI File Spec v1.3Having NeverNo ratings yet
- Lecture 6-Forensic ToolsDocument46 pagesLecture 6-Forensic ToolsTing Zhi Peng (Ethan)No ratings yet
- "TIGER" OCR Library: (For Microsoft Windows NT and Windows 98/95)Document42 pages"TIGER" OCR Library: (For Microsoft Windows NT and Windows 98/95)war lockNo ratings yet
- NIST Data Leakage 00 Env SettingDocument48 pagesNIST Data Leakage 00 Env SettingwanNo ratings yet
- Windows Registry ForesicsDocument25 pagesWindows Registry ForesicsAPRIL ELLEN DELOS REYES100% (1)
- Top 10 FTK Features WP FINAL 2023Document7 pagesTop 10 FTK Features WP FINAL 2023mahdi aghaeiNo ratings yet
- Foundation - Apple Developer DocumentationDocument4 pagesFoundation - Apple Developer DocumentationSamantha De Cárdenas100% (1)
- ED600 SyllabusDocument9 pagesED600 SyllabusVenkat EshwariNo ratings yet
- Exterro FTK 7.5.1-Release NotesDocument17 pagesExterro FTK 7.5.1-Release NotesMuhammad ZulkhairiNo ratings yet
- Party Toonz: Media Player and Database LibraryDocument5 pagesParty Toonz: Media Player and Database Libraryapi-27070090No ratings yet
- Cisco Endpoint IOC AttributesDocument10 pagesCisco Endpoint IOC AttributesKiril PetkovNo ratings yet
- 2 It302g Linux OsDocument8 pages2 It302g Linux OsAmit DeshaiNo ratings yet
- IPXACT-Based RTL Generation ToolDocument4 pagesIPXACT-Based RTL Generation ToolQi JiaNo ratings yet
- Course 70-210Document5 pagesCourse 70-210KamalGhazaliNo ratings yet
- Lab 7 Examining The Windws RegistryDocument6 pagesLab 7 Examining The Windws RegistryMuhammad Badrul AzharNo ratings yet
- M-2 SoftwareDevelopmentDocument12 pagesM-2 SoftwareDevelopmentywq885233326No ratings yet
- How Registry Is Helpful in Managing Security.: Term Paper OnDocument13 pagesHow Registry Is Helpful in Managing Security.: Term Paper OnAshish VaniyaNo ratings yet
- FTK DataSheet - AccessDataDocument2 pagesFTK DataSheet - AccessDataaccessdataNo ratings yet
- Diploma in I.T Technical Support: Assignment Title: The Boot Process in Windows and UbuntuDocument14 pagesDiploma in I.T Technical Support: Assignment Title: The Boot Process in Windows and Ubuntuصفوان قشقري100% (1)
- FortiAnalyzer Course Description-Online-NEWDocument2 pagesFortiAnalyzer Course Description-Online-NEWCarlosDavidTorresNo ratings yet
- CNS 320 Week4 LectureDocument74 pagesCNS 320 Week4 Lecturealb3rtlinNo ratings yet
- Interview QuestionDocument9 pagesInterview Questionsonupawar8883No ratings yet
- Memor X3 SDK Readme PDFDocument3 pagesMemor X3 SDK Readme PDFpigueloNo ratings yet
- A Practitioners Guide To The Forensic Investigation of Xbox 360 Gaming ConsolesDocument23 pagesA Practitioners Guide To The Forensic Investigation of Xbox 360 Gaming Consolesmav87th-1No ratings yet
- PE File HeaderDocument128 pagesPE File HeaderQuốc TuấnNo ratings yet
- File Hawk SpecificationsDocument2 pagesFile Hawk SpecificationsCity VilleNo ratings yet
- CHFI Crash Study GuideDocument9 pagesCHFI Crash Study Guidecyber forensicNo ratings yet
- Exterro FTK and FTK Lab 8.0-Release NotesDocument35 pagesExterro FTK and FTK Lab 8.0-Release NotesIlham AdzieNo ratings yet
- BCD EditDocument22 pagesBCD EditpedrokaulsNo ratings yet
- Tutorial To Install 3D AikidoDocument2 pagesTutorial To Install 3D AikidoDexter JamesNo ratings yet
- RegrunlogDocument91 pagesRegrunlogPaijo BantulNo ratings yet
- Trend Micro Endpoint Agent - Installation ManualDocument14 pagesTrend Micro Endpoint Agent - Installation Manualsse contractNo ratings yet
- UsbFix ReportDocument2 pagesUsbFix ReportBourama DIAKITENo ratings yet
- Oracle R12 Form 10G CustomizationDocument8 pagesOracle R12 Form 10G CustomizationrameshibmNo ratings yet
- Hacking With Experts by Anurag Dwivedi PDFDocument156 pagesHacking With Experts by Anurag Dwivedi PDFKeshav VermaNo ratings yet
- Windows NT Startup ProcessDocument8 pagesWindows NT Startup ProcessSaravanan MohanNo ratings yet
- RSLogix Emulate 5000 - Internal Error! Failed To Install RSLogix Emulate 5000 in Slot!Document2 pagesRSLogix Emulate 5000 - Internal Error! Failed To Install RSLogix Emulate 5000 in Slot!Álvaro HernándezNo ratings yet
- DOCDocument114 pagesDOCElving MendozaNo ratings yet
- Errors and StepsDocument7 pagesErrors and StepssudharaghavanNo ratings yet
- Anti Forensics GuideDocument9 pagesAnti Forensics GuideDelin BardhiNo ratings yet
- Reference Guide The Open Distribution System Simulator (Opendss)Document232 pagesReference Guide The Open Distribution System Simulator (Opendss)TerrorTricolorFCNo ratings yet
- Win 76 LinkDocument2 pagesWin 76 LinkSam Djjs NileshNo ratings yet
- Ncs DummyDocument45 pagesNcs DummyAdyNo ratings yet
- 192 168 0 187Document5 pages192 168 0 187Thuy TaNo ratings yet
- Speed Up Your PCDocument8 pagesSpeed Up Your PCvaibhav420100% (1)
- All VB6 CommandsDocument10 pagesAll VB6 CommandskhonelNo ratings yet
- SysInternals DocsDocument191 pagesSysInternals DocsGuillan Pascual100% (1)
- Alstom BcuDocument560 pagesAlstom BcuGuru Mishra100% (2)
- Detailed User Guide For TRF 01 FormDocument23 pagesDetailed User Guide For TRF 01 Formm_adil_211359No ratings yet
- Manual Oracle Express PDFDocument18 pagesManual Oracle Express PDFjjose3No ratings yet
- Windows 7 Help & Advice - October 2014-P2P PDFDocument100 pagesWindows 7 Help & Advice - October 2014-P2P PDFCarlos PocinhoNo ratings yet
- Fabrication: Machine Setup in CAM: Learning ObjectivesDocument43 pagesFabrication: Machine Setup in CAM: Learning ObjectivesJohn ContrerasNo ratings yet
- PipelineStudio Installation GuideDocument27 pagesPipelineStudio Installation GuideRodrigo MadariagaNo ratings yet
- PSCADDocument10 pagesPSCADkaran976No ratings yet
- How To Install XP On An External Hard Drive: Jason GordonDocument6 pagesHow To Install XP On An External Hard Drive: Jason Gordonsaman369No ratings yet
- Interviews DraftDocument187 pagesInterviews DraftSaverio GrisorioNo ratings yet
- Zabbix Documentation 6.2.enDocument1,602 pagesZabbix Documentation 6.2.enpenNo ratings yet
- SAP Router Installation Step by StepDocument20 pagesSAP Router Installation Step by StepIrwin Cruize MhendozaNo ratings yet