Professional Documents
Culture Documents
WebCTRL v7.0 Security
WebCTRL v7.0 Security
Uploaded by
Mc EswaranOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
WebCTRL v7.0 Security
WebCTRL v7.0 Security
Uploaded by
Mc EswaranCopyright:
Available Formats
WebCTRL® v7.
0 Security
Rev. 6/8/2018
The WebCTRL server application provides a very high level of security to protect against unauthorized access.
This memorandum briefly outlines design, security, configuration, and implementation aspects of your
WebCTRL Building Automation System server application.
• WebCTRL source code is subjected to source code analysis and independent third-party penetration
testing as part of our software development lifecycle process.
• All third-party libraries are scanned for known vulnerabilities.
• WebCTRL web server engine:
○ The WebCTRL server application uses its own built-in web server engine based on a locked-down
version of Apache Tomcat. This greatly reduces the chance of an undiscovered Apache Tomcat
vulnerability.
○ The WebCTRL server application does NOT use Microsoft’s IIS web server.
○ The web server renders only WebCTRL pages. It cannot be used as a general-purpose web server to
render pages from other systems on the building network.
○ All database queries use a single internal interface that protects against common SQL injection
attacks. As of v6.0, this includes Write to Database alarm actions.
○ As of v6.0, the WebCTRL server application no longer uses Java® Applets or Java Web Start which
have been the source of Java vulnerabilities to desktop computers. While the WebCTRL server
application no longer uses Applets or Web Start, we do recommend that customers keep their Java
Runtime Environment up to date at all times.
○ As of v7.0, the WebCTRL server application will, by default, allow only add-on applications provided
and signed by Automated Logic®. You can removed this restriction, but any add-on application not
provided by Automated Logic® should be carefully reviewed for source and content before using with
the WebCTRL server application.
ALC Proprietary and Confidential © 2018 Automated Logic Corporation
All rights reserved
1
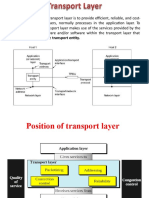
• WebCTRL communications:
○ The WebCTRL server application uses the ports and protocols listed in the following table. In the Use
column, Client/Server is communication between the end user’s computer and the WebCTRL server
application. Server/Gateway is communications between the WebCTRL server application and the
Ethernet network interface on an Automated Logic IP controller. If a firewall exists between the Client
and Server or the Server and Gateway, you will need to open the following ports to enable
communication.
Port Transfer Protocol/User Use
80 (default) TCP http (Web server) Client/Server
443 (default) TCP https (Web server) Client/Server
47806 (default) TCP Alarm Notification Client Client/Server
47808 UDP BACnet/IP Server/Gateway
47808 TCP Diagnostic Telnet * Client/Server
47806 UDP Legacy CMnet Server/Gateway
* This functionality is off by default. You can start it using the telnetd console command.
You can edit the default http and https ports in SiteBuilder and the default Alarm Pop-up Client port in
the WebCTRL interface (System Settings > General > Alarms).
The WebCTRL server application does not require open ports for standard Telnet, FTP, Windows file
sharing, or other applications that can increase the vulnerability of the system. The Diagnostic Telnet
protocol used on port 47808 is a password-protected plain text only user interface that is limited to
WebCTRL server application functions. This functionality is ONLY used for Tech Support purposes and
should be firewalled. It is turned off by default. You can start it using the telnetd console
command.
○ Built-in support for Secure Socket Layer (SSL) communications provides 128-bit encryption for all
communications to ensure unauthorized 'eavesdroppers' cannot obtain passwords or other sensitive
information passed between the web server and server. If needed, you can increase the encryption
level to 256-bit. (See "Network Security" in WebCTRL Help for information on configuring SSL.) All
network traffic between the WebCTRL server application and the browser can be encrypted using a
locally created certificate. The WebCTRL software suite offers tools to recreate these self-signed
certificates at any time, export to a third-party Certificate Authority (CA) and re-import the signed
certificate. After you receive and install a signed certificate, be sure to back up the certificate and
keystore for future WebCTRL installs.
○ IPV6 is supported between the WebCTRL server application and browser.
○ A WebCTRL server with two NICs can provide additional security and easier system diagnostics. One
NIC is dedicated to web page traffic, and the other to unencrypted BACnet traffic to field controllers.
This separation of physical networks is the recommended best practice for building security. In this
configuration, it is impossible for BACnet traffic to cross between the two networks.
ALC Proprietary and Confidential © 2018 Automated Logic Corporation
All rights reserved
2
○ The WebCTRL server application is compatible with standard external security provisions such as
firewalls and Virtual Private Networks (VPNs). VPNs can limit access to specific computer IDs, provide
an additional layer of login/password protection, and offer alternative encryption schemes.
○ Remote sites that connect to the WebCTRL server application through modems use an LGR as a
BACnet dial-up half-router. These routers are inherently protected by their limited functionality, since
they only respond to BACnet commands to local field controllers. They do not provide access to other
Ethernet or IP networks within the building, even if they share the same physical wires.
○ Sites that have security concerns but cannot physically secure their environment should disable
controllers’ Local Access ports to prevent non-authenticated access through Field Assistant
connected to the Rnet. See "To disable a controller’s Local Access" in WebCTRL Help. This setting can
also be changed using global modify.
○ The 6-02 and later drivers support BACnet whitelist functionality. You can restrict traffic to all private
IP adresses and/or a list of specific IP addresses. This can also be used on an isolated network to
restrict traffic to only designated BACnet devices and workstation(s) to ensure no other IP devices can
tamper with BACnet controllers.
• Operator access to the WebCTRL server application:
○ WebCTRL password security allows operator access based on privileges set by the administrator. The
advanced security policy provides further security through password character/expiration
requirements and user lockouts.
○ Access to the WebCTRL server application can be restricted based on geographic assignment of
operator privileges. For example, this allows persons with the same operator privileges access to
different geographic areas of the system ( i.e. two different rooms, floors, or buildings).
○ The WebCTRL audit log provides a detailed list of all operator actions and can be searched by
operator name, date, and geography.
○ In a 21CFR Part 11 Pharmaceutical/Biotech validated facility, the WebCTRL server application can
require an operator to record the reason for a change to operating conditions before accepting the
change.
○ As of v6.0, operator passwords are "salted" and "hashed" using SHA512 and therefore cannot be
reversed-engineered and are not exposed if the WebCTRL database is compromised. This also means
that Automated Logic® cannot help recover lost passwords.
○ As of v6.0, passwords that the WebCTRL server application uses to access other systems use
AES-128 bit encryption. This includes database passwords, hierarchical server passwords, and Email
and Write to Database alarm action passwords.
• As of v7.0, all patches to the WebCTRL software are signed for authentication and to prevent tampering.
ALC Proprietary and Confidential © 2018 Automated Logic Corporation
All rights reserved
3
• After installing the WebCTRL software using administrator access, you can minimize risk to the server by
running the software using a second non-administrator account. For Windows this non-administrator
account must be given "Full Control" to the installation directory so that the software may run properly and
apply patches. This account should also be used when run as a service. This can be specified in the "Log
On" properties dialog for the WebCTRL service inside the "services" application in the Windows Control
Panel. Linux should also be similarly configured to not run as "root". If other accounts are used to run the
software (e.g. engineering tools), those accounts must also be granted full permissions to the installation
directory.
• Database servers should be configured to allow access only by the WebCTRL server application and tools.
This can be done through firewall protection and any other database-specific mechanism that limits
access to specific hosts. As of v7.0, SQL Server with SSL is supported.
• See our Security Best Practices document for additional best practices and a security checklist.
ALC Proprietary and Confidential © 2018 Automated Logic Corporation
All rights reserved
4
You might also like
- CCNAv7 - Enterprise Networking, Security, and Automation Final ExamDocument66 pagesCCNAv7 - Enterprise Networking, Security, and Automation Final ExamsinkuNo ratings yet
- PaloAltoNetworks Designs Guide RevB PDFDocument110 pagesPaloAltoNetworks Designs Guide RevB PDFsatya28100% (2)
- Aviatrix ACEDocument25 pagesAviatrix ACEDavid Patterson100% (1)
- Building A Powerful FreeBSD Firewall Based On PF and IPFWDocument13 pagesBuilding A Powerful FreeBSD Firewall Based On PF and IPFWIan100% (17)
- Cisco S380 and Cisco S680 Web Security Appliance: Uick Tart UideDocument28 pagesCisco S380 and Cisco S680 Web Security Appliance: Uick Tart UidefregolikventinNo ratings yet
- Perimeta Network Integration Guide: PMC-008 - Version 4.7.20 - Issue 1-406Document78 pagesPerimeta Network Integration Guide: PMC-008 - Version 4.7.20 - Issue 1-406nergal19100% (1)
- Ecostruxure Plant: Hybrid & Discrete IndustriesDocument33 pagesEcostruxure Plant: Hybrid & Discrete IndustriesbkarakoseNo ratings yet
- Pca Exadata Direct Connect-TpDocument19 pagesPca Exadata Direct Connect-TpKesava ReddyNo ratings yet
- Torch System Requirements1Document3 pagesTorch System Requirements1NaveenKumarNo ratings yet
- Dot1x Dep Guide - CiscoDocument37 pagesDot1x Dep Guide - CiscoJh0n Fredy HNo ratings yet
- Transport Security Specification 61Document12 pagesTransport Security Specification 61Pedro MarquesNo ratings yet
- Puertos, Protocolos y Requerimientos de FirewallDocument9 pagesPuertos, Protocolos y Requerimientos de FirewallJoeNo ratings yet
- Network Security AssignmentDocument24 pagesNetwork Security AssignmentSagar PaudelNo ratings yet
- Embedded Web ServerDocument17 pagesEmbedded Web ServerAmma C sNo ratings yet
- NI Tutorial 12402 enDocument6 pagesNI Tutorial 12402 enMisael Castillo CamachoNo ratings yet
- Specific Instructional Objectives: Encryption/decryption Technique For Transfer of Data Between Two SecureDocument8 pagesSpecific Instructional Objectives: Encryption/decryption Technique For Transfer of Data Between Two SecureGanesh MoteNo ratings yet
- Cisco S390 Web Security Appliance Quick Start GuideDocument22 pagesCisco S390 Web Security Appliance Quick Start GuidefregolikventinNo ratings yet
- WedgeARP AMB v2.1 Training - Module F - Deployment and ConfigurationDocument84 pagesWedgeARP AMB v2.1 Training - Module F - Deployment and Configurationahmed gaafarNo ratings yet
- Flow Matrix TutorialDocument23 pagesFlow Matrix TutorialbabasexNo ratings yet
- FAQ SecurityCenterPorts5.8Document9 pagesFAQ SecurityCenterPorts5.8etronmanNo ratings yet
- Transparent Proxy Solution22Document13 pagesTransparent Proxy Solution22mNo ratings yet
- Designing Ethernet/Ip Machine/Skid Level Networks: Rev 5058-Co900DDocument33 pagesDesigning Ethernet/Ip Machine/Skid Level Networks: Rev 5058-Co900DdroncanciomNo ratings yet
- Netsupport Manager Gateway: Netsupport Ltd. All Rights ReservedDocument17 pagesNetsupport Manager Gateway: Netsupport Ltd. All Rights ReservedimpeesaNo ratings yet
- CTERA Portal Installation Guide CentOS Edition Over VMWareDocument74 pagesCTERA Portal Installation Guide CentOS Edition Over VMWarejanet johnNo ratings yet
- SX-SRVR Security Expert - Networking Administrator Guide - Reference GuideDocument13 pagesSX-SRVR Security Expert - Networking Administrator Guide - Reference GuideErick DiazNo ratings yet
- 0722 Proxy Server Based FirewallsDocument100 pages0722 Proxy Server Based FirewallsSanthosh SNo ratings yet
- Broadcom NetXtremeII Server T7.8Document332 pagesBroadcom NetXtremeII Server T7.8Thiago PHNo ratings yet
- MANUALrevADocument67 pagesMANUALrevAJenn BellNo ratings yet
- Network Management For Labs GROUP CDocument5 pagesNetwork Management For Labs GROUP CisaacNo ratings yet
- BACnet Advanced Workstation BACnet Operator WorkstationDocument2 pagesBACnet Advanced Workstation BACnet Operator WorkstationAhmed AbdullaNo ratings yet
- Broadcom Netxtreme Adapters Owner's Manual en UsDocument175 pagesBroadcom Netxtreme Adapters Owner's Manual en UsMihai ZamfirNo ratings yet
- Chapter 10Document39 pagesChapter 10AbhiNo ratings yet
- GlobalProtect Configuration Rev IDocument54 pagesGlobalProtect Configuration Rev IJimmy Alfaro HernandezNo ratings yet
- NetBackup102 Network Ports Reference GuideDocument21 pagesNetBackup102 Network Ports Reference Guidedixade1732No ratings yet
- CCNA Security v20 Chapter 3 Exam AnswersDocument5 pagesCCNA Security v20 Chapter 3 Exam AnswersJonathanNo ratings yet
- Proxy ServerDocument12 pagesProxy ServerambroseNo ratings yet
- Application Note 3ADR010650Document33 pagesApplication Note 3ADR010650Mohamed MOUCHRIFNo ratings yet
- User Manual: G G Internet Access DeviceDocument24 pagesUser Manual: G G Internet Access DeviceEtzael Martínez FloresNo ratings yet
- SOL PROJECT REPORT 15062021 083527pmDocument11 pagesSOL PROJECT REPORT 15062021 083527pmEiman WahabNo ratings yet
- Broadcom NetXtremeII Server T7.0Document292 pagesBroadcom NetXtremeII Server T7.0cristiancca123No ratings yet
- C 70 LwapDocument126 pagesC 70 LwapKundan PrasadNo ratings yet
- Net TunnelDocument14 pagesNet TunnelChris NordNo ratings yet
- Cisco CCNA Security Chapter 3 ExamDocument6 pagesCisco CCNA Security Chapter 3 ExamPaulina EcheverríaNo ratings yet
- A Wireless LAN Hot SpotDocument8 pagesA Wireless LAN Hot SpotMugluuNo ratings yet
- Development of An Embedded Web Server System For Controlling and Monitoring of Remote Devices Based On ARM and Win CEDocument6 pagesDevelopment of An Embedded Web Server System For Controlling and Monitoring of Remote Devices Based On ARM and Win CEIndu MandwiNo ratings yet
- Carel Webgate PDFDocument6 pagesCarel Webgate PDFOky LimNo ratings yet
- 01-02 Classic EditionDocument598 pages01-02 Classic EditionnrNo ratings yet
- Integration Into Networks: 4.1 Network ParametersDocument2 pagesIntegration Into Networks: 4.1 Network ParametersMihai PopescuNo ratings yet
- Edge To Cloud ProtocolDocument21 pagesEdge To Cloud ProtocolMuzammil BalochNo ratings yet
- Case StudyDocument33 pagesCase StudyLeo F. Thomas Jr.100% (1)
- ExtremeControl With WiNG 5.8Document42 pagesExtremeControl With WiNG 5.8manelnaboNo ratings yet
- AnswerDocument5 pagesAnswerVIKRAM KUMARNo ratings yet
- Răspunsuri Test Final NetacadDocument26 pagesRăspunsuri Test Final NetacadLarisa DumitracheNo ratings yet
- Ethernet Broadband Router: User's ManualDocument47 pagesEthernet Broadband Router: User's ManualCondo EastNo ratings yet
- Cisco Intersight Onpremises DeploymentDocument20 pagesCisco Intersight Onpremises Deploymentsalist3kNo ratings yet
- CCNA Final Exam 4.0Document16 pagesCCNA Final Exam 4.0rasheeccnaNo ratings yet
- Configuration of Microsoft ISA Proxy Server and Linux Squid Proxy ServerFrom EverandConfiguration of Microsoft ISA Proxy Server and Linux Squid Proxy ServerNo ratings yet
- Set Up Your Own IPsec VPN, OpenVPN and WireGuard Server: Build Your Own VPNFrom EverandSet Up Your Own IPsec VPN, OpenVPN and WireGuard Server: Build Your Own VPNRating: 5 out of 5 stars5/5 (1)
- Kw-Multiprog DSDocument1 pageKw-Multiprog DSMc EswaranNo ratings yet
- ABB M1M Modbus Map V1.2Document32 pagesABB M1M Modbus Map V1.2Mc EswaranNo ratings yet
- Installsheet - 77 - 629c 01 CH p1 E1 s1Document4 pagesInstallsheet - 77 - 629c 01 CH p1 E1 s1Mc EswaranNo ratings yet
- Enhancing Energy Efficiency in MalaysiaDocument35 pagesEnhancing Energy Efficiency in MalaysiaMc Eswaran100% (2)
- Instructions !!!Document1 pageInstructions !!!Mc EswaranNo ratings yet
- User Manual: Bacnet/Ip Slave / Modbus Slave - Converter Bacnet MS/TP Slave / Modbus Slave - ConverterDocument32 pagesUser Manual: Bacnet/Ip Slave / Modbus Slave - Converter Bacnet MS/TP Slave / Modbus Slave - ConverterMc EswaranNo ratings yet
- Mini ProjectDocument6 pagesMini ProjectMc EswaranNo ratings yet
- Q2) A) Input: Original Salary B) Expected Output: Remaining SalaryDocument2 pagesQ2) A) Input: Original Salary B) Expected Output: Remaining SalaryMc EswaranNo ratings yet
- Nilai Polytechnic, Negeri Sembilan Department of Mechanical EngineeringDocument1 pageNilai Polytechnic, Negeri Sembilan Department of Mechanical EngineeringMc EswaranNo ratings yet
- Instructor DevNet Associate Packet Tracer ActivityDocument36 pagesInstructor DevNet Associate Packet Tracer ActivityindryNo ratings yet
- Cisco ME-C3750-24TE-M Command Reference 12.2.44SEDocument939 pagesCisco ME-C3750-24TE-M Command Reference 12.2.44SEscorcdNo ratings yet
- General Introduction of Smartax Ma5800: Security LevelDocument27 pagesGeneral Introduction of Smartax Ma5800: Security Levelvinh lưuNo ratings yet
- APM403 ModbusTCP ENDocument18 pagesAPM403 ModbusTCP ENMartinNo ratings yet
- DHCP Scope PropertiesDocument2 pagesDHCP Scope Propertiesavitoy23No ratings yet
- Monitor BandwidthDocument15 pagesMonitor BandwidthTaban SimonNo ratings yet
- Mobile Operator Converges Fixed and Mobile Telephony: Executive SummaryDocument6 pagesMobile Operator Converges Fixed and Mobile Telephony: Executive SummaryardhendumohantyNo ratings yet
- Siemens - Profibus and Modbus ComparisonDocument5 pagesSiemens - Profibus and Modbus Comparisonmanuela.bibescuNo ratings yet
- Networking Huynhvotrungnguyen SE06202Document34 pagesNetworking Huynhvotrungnguyen SE06202tín ngô100% (1)
- HostsaDocument259 pagesHostsaRaka Bagus PanuntunNo ratings yet
- TN 206: Network Routers and Routing ProtocolsDocument51 pagesTN 206: Network Routers and Routing ProtocolsJohnBenardNo ratings yet
- Load Balancer Interview Questions & AnswersDocument15 pagesLoad Balancer Interview Questions & Answersajay kumarNo ratings yet
- Chapter 5Document52 pagesChapter 5Pratham SuhasiaNo ratings yet
- Final Exam Solution: CSE 473 - Introduction To Computer Networks Jon TurnerDocument9 pagesFinal Exam Solution: CSE 473 - Introduction To Computer Networks Jon TurnerIngo SNo ratings yet
- What Is An E-SBC?: White PaperDocument7 pagesWhat Is An E-SBC?: White PaperYuvraj KumarNo ratings yet
- Computer NetworksDocument22 pagesComputer NetworksRISHINo ratings yet
- Addressing The DAO Insider Attack in RPL's Internet of Things NetworksDocument4 pagesAddressing The DAO Insider Attack in RPL's Internet of Things NetworksMohammed Belkheir100% (1)
- MANET: Mobile Ad Hoc NetworkDocument8 pagesMANET: Mobile Ad Hoc NetworkAravind RajNo ratings yet
- TCP IP NetworkingDocument37 pagesTCP IP NetworkingRai Kashif JahangirNo ratings yet
- Network Troubleshooting Using Packet Capture UtilitiesDocument13 pagesNetwork Troubleshooting Using Packet Capture UtilitiesAndrejNo ratings yet
- CN Unit - 1 PDFDocument137 pagesCN Unit - 1 PDFYeshwanth KrishnaNo ratings yet
- Ds 3xtend Einc LDocument20 pagesDs 3xtend Einc LMushahidNo ratings yet
- MindCert Cisco IPsec MindMap PDFDocument1 pageMindCert Cisco IPsec MindMap PDFzinzinNo ratings yet
- Duplichecker Plagiarism ReportDocument1 pageDuplichecker Plagiarism ReporthritikprabhakarNo ratings yet
- Candra 2020 IOP Conf. Ser. Mater. Sci. Eng. 725 012110Document6 pagesCandra 2020 IOP Conf. Ser. Mater. Sci. Eng. 725 012110Rudi Arif candraNo ratings yet
- Network Infrastructure of E Commerce: Where The Web Was BornDocument7 pagesNetwork Infrastructure of E Commerce: Where The Web Was Bornهمسه محمد بدرNo ratings yet
- (Instructor Version) : Packet Tracer Simulation - TCP and UDP CommunicationsDocument6 pages(Instructor Version) : Packet Tracer Simulation - TCP and UDP Communicationsadnan MengalNo ratings yet
- Supportinfo d4684d269280Document133 pagesSupportinfo d4684d269280Ahmad WahidNo ratings yet
- 01-04 IPSec ConfigurationDocument270 pages01-04 IPSec Configurationfetah baghdadNo ratings yet