Professional Documents
Culture Documents
0 ratings0% found this document useful (0 votes)
18 viewsGaining Access
Gaining Access
Uploaded by
KlausThe gaining access phase involves exploiting identified vulnerabilities to access systems or networks. This may include using known or custom exploits, privilege escalation, installing backdoors for persistent access, and potentially exfiltrating data. Throughout this phase, the penetration tester documents actions and findings to provide a detailed report and help the organization understand the impact of vulnerabilities and how to strengthen security.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You might also like
- EX FINAL 5 - IBM Cybersecurity Analyst Professional Certificate Assessment Exam - CourseraDocument28 pagesEX FINAL 5 - IBM Cybersecurity Analyst Professional Certificate Assessment Exam - CourseraPaul Bances SeverinoNo ratings yet
- How To Use Cain & Abel To Get Local Passwords PDFDocument3 pagesHow To Use Cain & Abel To Get Local Passwords PDFStoica Claudiu Mihail100% (1)
- Maintaining AccessDocument1 pageMaintaining AccessKlausNo ratings yet
- Pen Test PhasesDocument1 pagePen Test PhasesKlausNo ratings yet
- Slide 3Document20 pagesSlide 3kisituNo ratings yet
- Penetration TestingDocument3 pagesPenetration Testingneelima_sriramNo ratings yet
- Ethical Hacking Chap - 1Document17 pagesEthical Hacking Chap - 12021ci13fNo ratings yet
- Information Security MidDocument2 pagesInformation Security MidAqsa NoumanNo ratings yet
- Security FA1Document7 pagesSecurity FA1Nnosie Khumalo Lwandile SaezoNo ratings yet
- Web Security Audit BasicsDocument20 pagesWeb Security Audit Basicsrzpjck6xrmNo ratings yet
- Eth CHP1Document17 pagesEth CHP1Liladhar VanjoleNo ratings yet
- Final It-Semis-NotesDocument9 pagesFinal It-Semis-NotesJasmine GabianaNo ratings yet
- Penetration TestingDocument4 pagesPenetration TestingsipraNo ratings yet
- IntrudersDocument36 pagesIntrudersSmily TheresaNo ratings yet
- CHapter - 4netwrokDocument16 pagesCHapter - 4netwrokQusay IsmailNo ratings yet
- Chapter 7Document4 pagesChapter 7VENICE HOSMILLONo ratings yet
- Study Paper On Penetration Testing - FinalDocument20 pagesStudy Paper On Penetration Testing - FinalrontechtipsNo ratings yet
- Effective Penetration TestingDocument8 pagesEffective Penetration TestingflaviodemenezesNo ratings yet
- Privilege Escalation and Executing ApplicationsDocument7 pagesPrivilege Escalation and Executing ApplicationsAjit PawarNo ratings yet
- CEH Notes Cybrary PDFDocument34 pagesCEH Notes Cybrary PDFJashan Singh100% (1)
- Unit 5 SolsDocument10 pagesUnit 5 SolsHafsa LateefNo ratings yet
- Sic Notes VickyDocument73 pagesSic Notes Vickyspeedyrohan8No ratings yet
- CHPT 4Document9 pagesCHPT 4shoaibmirani007No ratings yet
- UNIT 1 - The Technical Foundations of HackingDocument8 pagesUNIT 1 - The Technical Foundations of HackingNithish KumarNo ratings yet
- EasyChair Preprint 11719Document16 pagesEasyChair Preprint 11719phbck.up.kbNo ratings yet
- Unit 4 - Lecture Protection and SecurityDocument27 pagesUnit 4 - Lecture Protection and SecurityNishant NalawadeNo ratings yet
- IS Auditing - 4Document27 pagesIS Auditing - 4Wuiss AgonyNo ratings yet
- SSE AssignmentDocument5 pagesSSE Assignment1.22E11 PASUMARTHI SOWMYANo ratings yet
- Session 6 Incident ResponseDocument6 pagesSession 6 Incident Responsedrelm7399No ratings yet
- Vulnerability Assessment and Penetration TestingDocument6 pagesVulnerability Assessment and Penetration Testingseventhsensegroup100% (1)
- Intrusion and Tools....Document35 pagesIntrusion and Tools....saqlain abbasNo ratings yet
- Definitive Guide To Penetration TestingDocument19 pagesDefinitive Guide To Penetration Testing[]No ratings yet
- Chapter 09 IntrudersDocument38 pagesChapter 09 IntrudershajerpcNo ratings yet
- Attack Phases: 1 - Explain Each Phase of A System Attack According To CEHDocument3 pagesAttack Phases: 1 - Explain Each Phase of A System Attack According To CEHAlumno: María del Carmen Fernández ArrebolaNo ratings yet
- Research PlanDocument6 pagesResearch PlanPrince OpokuNo ratings yet
- HAHADocument4 pagesHAHAnutwoNo ratings yet
- Operating System SecurityDocument4 pagesOperating System SecuritymakamafortunateNo ratings yet
- Planning and ReconDocument1 pagePlanning and ReconKlausNo ratings yet
- Case Study On VerticalScope Data Breach PDF FormatDocument5 pagesCase Study On VerticalScope Data Breach PDF Formatkritika.negi45No ratings yet
- Penetration Test Process and Types FactsDocument5 pagesPenetration Test Process and Types FactsKimberly PinedaNo ratings yet
- Cyber Security and Ethical HackingDocument58 pagesCyber Security and Ethical HackingAkashNo ratings yet
- Controls For Information Security Instructor's Manual Learning ObjectivesDocument11 pagesControls For Information Security Instructor's Manual Learning Objectivesym5c2324No ratings yet
- Compusoft, 3 (4), 752-757 PDFDocument6 pagesCompusoft, 3 (4), 752-757 PDFIjact EditorNo ratings yet
- Week6 KillChainDocument17 pagesWeek6 KillChainFrozoneNo ratings yet
- PrintoutDocument14 pagesPrintoutShalini ChintalaNo ratings yet
- Unit 9 Penetration TestingDocument29 pagesUnit 9 Penetration Testingzalak.desaiNo ratings yet
- Cyber Attack Kill ChainDocument23 pagesCyber Attack Kill ChainAgaje O. KelvinNo ratings yet
- An Overview of Penetration TestingDocument20 pagesAn Overview of Penetration TestingAIRCC - IJNSANo ratings yet
- OS Material Protection Security AIML UNIT V 2023Document17 pagesOS Material Protection Security AIML UNIT V 2023Ganesh DegalaNo ratings yet
- Lecture 01 - Introduction To Information SecurityDocument22 pagesLecture 01 - Introduction To Information SecurityS t a r D u s tNo ratings yet
- Ethical OverviewDocument17 pagesEthical OverviewdaphneygitNo ratings yet
- Security: Interruption vs. Interception vs. Modification vs. FabricationDocument8 pagesSecurity: Interruption vs. Interception vs. Modification vs. Fabricationcharysahith528No ratings yet
- Unit - I Classical Cryptosystem 9Document26 pagesUnit - I Classical Cryptosystem 9Manish RawatNo ratings yet
- Computer SecurityDocument37 pagesComputer SecurityEmmanuel RichardNo ratings yet
- Chapter OneDocument38 pagesChapter Onesohad aldeekNo ratings yet
- Ais Chapter 8Document16 pagesAis Chapter 8Anonymous cmPu24wNo ratings yet
- Assignment CSFDocument12 pagesAssignment CSFGOLDEN BIRDNo ratings yet
- Digital ForensicDocument23 pagesDigital ForensicReena GharatNo ratings yet
- Penetration Testing: Process and Procedures: ENG202CDocument6 pagesPenetration Testing: Process and Procedures: ENG202Capi-356224290No ratings yet
- Is Audit RevisionDocument14 pagesIs Audit RevisionsheecncNo ratings yet
- Ccna Security Ch1 Networking Security ConceptsDocument10 pagesCcna Security Ch1 Networking Security Conceptsflorinn81No ratings yet
- Cybersecurity and Ethical Hacking: Exploring the Dark Art of Ethical Hacking and Penetration TestingFrom EverandCybersecurity and Ethical Hacking: Exploring the Dark Art of Ethical Hacking and Penetration TestingNo ratings yet
- RfidDocument27 pagesRfidwineyarddeeNo ratings yet
- Module 5Document55 pagesModule 5ouia iooNo ratings yet
- A Physical Layer Security Scheme With Compressed Sensing in Ofdm-Based Iot SystemsDocument6 pagesA Physical Layer Security Scheme With Compressed Sensing in Ofdm-Based Iot SystemsKanwal HabibNo ratings yet
- Evaluation of The Role of Encryption Techniques in E CommerceDocument10 pagesEvaluation of The Role of Encryption Techniques in E CommerceLame Segokgo100% (2)
- Nis MicroprojectDocument21 pagesNis MicroprojectNitesh Gowardhan BorlaNo ratings yet
- AI-Enhanced LSB Steganography Interface Concealed Data Embedding FrameworkDocument4 pagesAI-Enhanced LSB Steganography Interface Concealed Data Embedding Frameworkstark pantherNo ratings yet
- About SOCDocument29 pagesAbout SOCRizal BachtiarNo ratings yet
- Aadhaar Ekyc Api 2 0Document11 pagesAadhaar Ekyc Api 2 0deepiiitbhuNo ratings yet
- Chapter 4-Connecting To DatabasesDocument20 pagesChapter 4-Connecting To Databasesወንድወሰን እርገጤNo ratings yet
- Rainbow Crack v1.0 TutorialDocument5 pagesRainbow Crack v1.0 TutorialJunior SanzNo ratings yet
- Dutch & English & EstonianDocument4 pagesDutch & English & EstonianAsh WinNo ratings yet
- Howtodecrypt802.11: How To Decrypt 802.11Document4 pagesHowtodecrypt802.11: How To Decrypt 802.11m.hadi sobhaniNo ratings yet
- A Note On Some Algebraic Trapdoors For Block CiphersDocument10 pagesA Note On Some Algebraic Trapdoors For Block CiphersBertha Catalina RostroNo ratings yet
- EAP Authentication With RADIUS ServerDocument13 pagesEAP Authentication With RADIUS ServerlancethNo ratings yet
- Course Policy DocumentDocument9 pagesCourse Policy DocumentTulsi PatelNo ratings yet
- Cryptography and Information TheoryDocument31 pagesCryptography and Information TheoryShorya KumarNo ratings yet
- Idirect Transec Advanced Overview PDF FreeDocument13 pagesIdirect Transec Advanced Overview PDF FreeAhmadHambaliNo ratings yet
- Devoir SecuDocument4 pagesDevoir SecuGlen TchoumbaNo ratings yet
- APIspecCLASSIC-3 0 1-RRDocument420 pagesAPIspecCLASSIC-3 0 1-RR奇刘No ratings yet
- SSL V/S Set: By-Neelu DeviDocument12 pagesSSL V/S Set: By-Neelu DeviKhushi GuptaNo ratings yet
- 254 Cascadable and Reconfigurable Photonic Logic GatesDocument15 pages254 Cascadable and Reconfigurable Photonic Logic Gatesfsd fsdfdsNo ratings yet
- Download ebook Science Of Cyber Security Third International Conference Scisec 2021 Virtual Event August 13 15 2021 Revised Selected Papers Lecture Notes In Computer Science Wenlian Lu Editor Kun Sun Editor Moti Yun online pdf all chapter docx epubDocument70 pagesDownload ebook Science Of Cyber Security Third International Conference Scisec 2021 Virtual Event August 13 15 2021 Revised Selected Papers Lecture Notes In Computer Science Wenlian Lu Editor Kun Sun Editor Moti Yun online pdf all chapter docx epubchristopher.zimmerebner674100% (8)
- Assignment 3, Fa17-Bse-073-BDocument19 pagesAssignment 3, Fa17-Bse-073-BFaisal QayyumNo ratings yet
- Digital Signature Schemes: Maria AlabbadiDocument13 pagesDigital Signature Schemes: Maria AlabbadiMARIA AL-ABBADINo ratings yet
- 3DES Triple DESDocument14 pages3DES Triple DESVijay AgrahariNo ratings yet
- 08 Chapter 3Document35 pages08 Chapter 3Jashanpreet SinghNo ratings yet
- Applications of Group Theory in CryptographyDocument5 pagesApplications of Group Theory in CryptographyMajid KhanNo ratings yet
- Fromdev: Ethical Hacking BooksDocument7 pagesFromdev: Ethical Hacking BooksMorgado_JsNo ratings yet
Gaining Access
Gaining Access
Uploaded by
Klaus0 ratings0% found this document useful (0 votes)
18 views1 pageThe gaining access phase involves exploiting identified vulnerabilities to access systems or networks. This may include using known or custom exploits, privilege escalation, installing backdoors for persistent access, and potentially exfiltrating data. Throughout this phase, the penetration tester documents actions and findings to provide a detailed report and help the organization understand the impact of vulnerabilities and how to strengthen security.
Original Description:
Gaining Access in Penetration Testing.
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThe gaining access phase involves exploiting identified vulnerabilities to access systems or networks. This may include using known or custom exploits, privilege escalation, installing backdoors for persistent access, and potentially exfiltrating data. Throughout this phase, the penetration tester documents actions and findings to provide a detailed report and help the organization understand the impact of vulnerabilities and how to strengthen security.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
Download as pdf or txt
0 ratings0% found this document useful (0 votes)
18 views1 pageGaining Access
Gaining Access
Uploaded by
KlausThe gaining access phase involves exploiting identified vulnerabilities to access systems or networks. This may include using known or custom exploits, privilege escalation, installing backdoors for persistent access, and potentially exfiltrating data. Throughout this phase, the penetration tester documents actions and findings to provide a detailed report and help the organization understand the impact of vulnerabilities and how to strengthen security.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
Download as pdf or txt
You are on page 1of 1
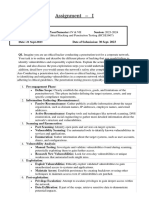
Gaining access is the third phase of the penetration testing process.
Once vulnerabilities have
been identified in the scanning phase, the penetration tester attempts to exploit them to gain
access to the target system or network. This may involve using known exploits or developing
custom exploits to take advantage of specific vulnerabilities.
Here are some details about the gaining access phase of penetration testing:
1. Exploitation: The penetration tester attempts to exploit the vulnerabilities that were
identified in the scanning phase. This may involve using known exploits, developing
custom exploits, or using social engineering techniques to trick users into divulging
sensitive information.
2. Privilege escalation: Once initial access has been gained, the penetration tester may
attempt to escalate their privileges to gain greater access to the target system or
network. This may involve using additional exploits or techniques such as password
cracking to gain administrative privileges.
3. Persistence: Once access has been gained and privileges escalated, the penetration
tester may attempt to maintain persistence by installing backdoors or other persistent
access mechanisms that allow them to access the target system or network even after
the penetration testing engagement is complete.
4. Data exfiltration: Depending on the goals of the penetration testing engagement, the
penetration tester may attempt to exfiltrate sensitive data from the target system or
network. This can include stealing passwords, stealing intellectual property, or
accessing financial or personal information.
5. Reporting: Throughout the gaining access phase, the penetration tester documents
their actions and findings in order to provide a detailed report of the vulnerabilities
that were exploited and the methods used to gain access. This report is used to help
the organization understand the impact of the vulnerabilities and to develop a plan for
remediation.
Overall, the gaining access phase of penetration testing is critical for understanding the
impact of vulnerabilities and identifying potential threats to the target system or network. By
exploiting vulnerabilities and gaining access to the target environment, the penetration tester
can demonstrate the potential impact of a real-world attack and help the organization develop
a plan for improving their security posture.
You might also like
- EX FINAL 5 - IBM Cybersecurity Analyst Professional Certificate Assessment Exam - CourseraDocument28 pagesEX FINAL 5 - IBM Cybersecurity Analyst Professional Certificate Assessment Exam - CourseraPaul Bances SeverinoNo ratings yet
- How To Use Cain & Abel To Get Local Passwords PDFDocument3 pagesHow To Use Cain & Abel To Get Local Passwords PDFStoica Claudiu Mihail100% (1)
- Maintaining AccessDocument1 pageMaintaining AccessKlausNo ratings yet
- Pen Test PhasesDocument1 pagePen Test PhasesKlausNo ratings yet
- Slide 3Document20 pagesSlide 3kisituNo ratings yet
- Penetration TestingDocument3 pagesPenetration Testingneelima_sriramNo ratings yet
- Ethical Hacking Chap - 1Document17 pagesEthical Hacking Chap - 12021ci13fNo ratings yet
- Information Security MidDocument2 pagesInformation Security MidAqsa NoumanNo ratings yet
- Security FA1Document7 pagesSecurity FA1Nnosie Khumalo Lwandile SaezoNo ratings yet
- Web Security Audit BasicsDocument20 pagesWeb Security Audit Basicsrzpjck6xrmNo ratings yet
- Eth CHP1Document17 pagesEth CHP1Liladhar VanjoleNo ratings yet
- Final It-Semis-NotesDocument9 pagesFinal It-Semis-NotesJasmine GabianaNo ratings yet
- Penetration TestingDocument4 pagesPenetration TestingsipraNo ratings yet
- IntrudersDocument36 pagesIntrudersSmily TheresaNo ratings yet
- CHapter - 4netwrokDocument16 pagesCHapter - 4netwrokQusay IsmailNo ratings yet
- Chapter 7Document4 pagesChapter 7VENICE HOSMILLONo ratings yet
- Study Paper On Penetration Testing - FinalDocument20 pagesStudy Paper On Penetration Testing - FinalrontechtipsNo ratings yet
- Effective Penetration TestingDocument8 pagesEffective Penetration TestingflaviodemenezesNo ratings yet
- Privilege Escalation and Executing ApplicationsDocument7 pagesPrivilege Escalation and Executing ApplicationsAjit PawarNo ratings yet
- CEH Notes Cybrary PDFDocument34 pagesCEH Notes Cybrary PDFJashan Singh100% (1)
- Unit 5 SolsDocument10 pagesUnit 5 SolsHafsa LateefNo ratings yet
- Sic Notes VickyDocument73 pagesSic Notes Vickyspeedyrohan8No ratings yet
- CHPT 4Document9 pagesCHPT 4shoaibmirani007No ratings yet
- UNIT 1 - The Technical Foundations of HackingDocument8 pagesUNIT 1 - The Technical Foundations of HackingNithish KumarNo ratings yet
- EasyChair Preprint 11719Document16 pagesEasyChair Preprint 11719phbck.up.kbNo ratings yet
- Unit 4 - Lecture Protection and SecurityDocument27 pagesUnit 4 - Lecture Protection and SecurityNishant NalawadeNo ratings yet
- IS Auditing - 4Document27 pagesIS Auditing - 4Wuiss AgonyNo ratings yet
- SSE AssignmentDocument5 pagesSSE Assignment1.22E11 PASUMARTHI SOWMYANo ratings yet
- Session 6 Incident ResponseDocument6 pagesSession 6 Incident Responsedrelm7399No ratings yet
- Vulnerability Assessment and Penetration TestingDocument6 pagesVulnerability Assessment and Penetration Testingseventhsensegroup100% (1)
- Intrusion and Tools....Document35 pagesIntrusion and Tools....saqlain abbasNo ratings yet
- Definitive Guide To Penetration TestingDocument19 pagesDefinitive Guide To Penetration Testing[]No ratings yet
- Chapter 09 IntrudersDocument38 pagesChapter 09 IntrudershajerpcNo ratings yet
- Attack Phases: 1 - Explain Each Phase of A System Attack According To CEHDocument3 pagesAttack Phases: 1 - Explain Each Phase of A System Attack According To CEHAlumno: María del Carmen Fernández ArrebolaNo ratings yet
- Research PlanDocument6 pagesResearch PlanPrince OpokuNo ratings yet
- HAHADocument4 pagesHAHAnutwoNo ratings yet
- Operating System SecurityDocument4 pagesOperating System SecuritymakamafortunateNo ratings yet
- Planning and ReconDocument1 pagePlanning and ReconKlausNo ratings yet
- Case Study On VerticalScope Data Breach PDF FormatDocument5 pagesCase Study On VerticalScope Data Breach PDF Formatkritika.negi45No ratings yet
- Penetration Test Process and Types FactsDocument5 pagesPenetration Test Process and Types FactsKimberly PinedaNo ratings yet
- Cyber Security and Ethical HackingDocument58 pagesCyber Security and Ethical HackingAkashNo ratings yet
- Controls For Information Security Instructor's Manual Learning ObjectivesDocument11 pagesControls For Information Security Instructor's Manual Learning Objectivesym5c2324No ratings yet
- Compusoft, 3 (4), 752-757 PDFDocument6 pagesCompusoft, 3 (4), 752-757 PDFIjact EditorNo ratings yet
- Week6 KillChainDocument17 pagesWeek6 KillChainFrozoneNo ratings yet
- PrintoutDocument14 pagesPrintoutShalini ChintalaNo ratings yet
- Unit 9 Penetration TestingDocument29 pagesUnit 9 Penetration Testingzalak.desaiNo ratings yet
- Cyber Attack Kill ChainDocument23 pagesCyber Attack Kill ChainAgaje O. KelvinNo ratings yet
- An Overview of Penetration TestingDocument20 pagesAn Overview of Penetration TestingAIRCC - IJNSANo ratings yet
- OS Material Protection Security AIML UNIT V 2023Document17 pagesOS Material Protection Security AIML UNIT V 2023Ganesh DegalaNo ratings yet
- Lecture 01 - Introduction To Information SecurityDocument22 pagesLecture 01 - Introduction To Information SecurityS t a r D u s tNo ratings yet
- Ethical OverviewDocument17 pagesEthical OverviewdaphneygitNo ratings yet
- Security: Interruption vs. Interception vs. Modification vs. FabricationDocument8 pagesSecurity: Interruption vs. Interception vs. Modification vs. Fabricationcharysahith528No ratings yet
- Unit - I Classical Cryptosystem 9Document26 pagesUnit - I Classical Cryptosystem 9Manish RawatNo ratings yet
- Computer SecurityDocument37 pagesComputer SecurityEmmanuel RichardNo ratings yet
- Chapter OneDocument38 pagesChapter Onesohad aldeekNo ratings yet
- Ais Chapter 8Document16 pagesAis Chapter 8Anonymous cmPu24wNo ratings yet
- Assignment CSFDocument12 pagesAssignment CSFGOLDEN BIRDNo ratings yet
- Digital ForensicDocument23 pagesDigital ForensicReena GharatNo ratings yet
- Penetration Testing: Process and Procedures: ENG202CDocument6 pagesPenetration Testing: Process and Procedures: ENG202Capi-356224290No ratings yet
- Is Audit RevisionDocument14 pagesIs Audit RevisionsheecncNo ratings yet
- Ccna Security Ch1 Networking Security ConceptsDocument10 pagesCcna Security Ch1 Networking Security Conceptsflorinn81No ratings yet
- Cybersecurity and Ethical Hacking: Exploring the Dark Art of Ethical Hacking and Penetration TestingFrom EverandCybersecurity and Ethical Hacking: Exploring the Dark Art of Ethical Hacking and Penetration TestingNo ratings yet
- RfidDocument27 pagesRfidwineyarddeeNo ratings yet
- Module 5Document55 pagesModule 5ouia iooNo ratings yet
- A Physical Layer Security Scheme With Compressed Sensing in Ofdm-Based Iot SystemsDocument6 pagesA Physical Layer Security Scheme With Compressed Sensing in Ofdm-Based Iot SystemsKanwal HabibNo ratings yet
- Evaluation of The Role of Encryption Techniques in E CommerceDocument10 pagesEvaluation of The Role of Encryption Techniques in E CommerceLame Segokgo100% (2)
- Nis MicroprojectDocument21 pagesNis MicroprojectNitesh Gowardhan BorlaNo ratings yet
- AI-Enhanced LSB Steganography Interface Concealed Data Embedding FrameworkDocument4 pagesAI-Enhanced LSB Steganography Interface Concealed Data Embedding Frameworkstark pantherNo ratings yet
- About SOCDocument29 pagesAbout SOCRizal BachtiarNo ratings yet
- Aadhaar Ekyc Api 2 0Document11 pagesAadhaar Ekyc Api 2 0deepiiitbhuNo ratings yet
- Chapter 4-Connecting To DatabasesDocument20 pagesChapter 4-Connecting To Databasesወንድወሰን እርገጤNo ratings yet
- Rainbow Crack v1.0 TutorialDocument5 pagesRainbow Crack v1.0 TutorialJunior SanzNo ratings yet
- Dutch & English & EstonianDocument4 pagesDutch & English & EstonianAsh WinNo ratings yet
- Howtodecrypt802.11: How To Decrypt 802.11Document4 pagesHowtodecrypt802.11: How To Decrypt 802.11m.hadi sobhaniNo ratings yet
- A Note On Some Algebraic Trapdoors For Block CiphersDocument10 pagesA Note On Some Algebraic Trapdoors For Block CiphersBertha Catalina RostroNo ratings yet
- EAP Authentication With RADIUS ServerDocument13 pagesEAP Authentication With RADIUS ServerlancethNo ratings yet
- Course Policy DocumentDocument9 pagesCourse Policy DocumentTulsi PatelNo ratings yet
- Cryptography and Information TheoryDocument31 pagesCryptography and Information TheoryShorya KumarNo ratings yet
- Idirect Transec Advanced Overview PDF FreeDocument13 pagesIdirect Transec Advanced Overview PDF FreeAhmadHambaliNo ratings yet
- Devoir SecuDocument4 pagesDevoir SecuGlen TchoumbaNo ratings yet
- APIspecCLASSIC-3 0 1-RRDocument420 pagesAPIspecCLASSIC-3 0 1-RR奇刘No ratings yet
- SSL V/S Set: By-Neelu DeviDocument12 pagesSSL V/S Set: By-Neelu DeviKhushi GuptaNo ratings yet
- 254 Cascadable and Reconfigurable Photonic Logic GatesDocument15 pages254 Cascadable and Reconfigurable Photonic Logic Gatesfsd fsdfdsNo ratings yet
- Download ebook Science Of Cyber Security Third International Conference Scisec 2021 Virtual Event August 13 15 2021 Revised Selected Papers Lecture Notes In Computer Science Wenlian Lu Editor Kun Sun Editor Moti Yun online pdf all chapter docx epubDocument70 pagesDownload ebook Science Of Cyber Security Third International Conference Scisec 2021 Virtual Event August 13 15 2021 Revised Selected Papers Lecture Notes In Computer Science Wenlian Lu Editor Kun Sun Editor Moti Yun online pdf all chapter docx epubchristopher.zimmerebner674100% (8)
- Assignment 3, Fa17-Bse-073-BDocument19 pagesAssignment 3, Fa17-Bse-073-BFaisal QayyumNo ratings yet
- Digital Signature Schemes: Maria AlabbadiDocument13 pagesDigital Signature Schemes: Maria AlabbadiMARIA AL-ABBADINo ratings yet
- 3DES Triple DESDocument14 pages3DES Triple DESVijay AgrahariNo ratings yet
- 08 Chapter 3Document35 pages08 Chapter 3Jashanpreet SinghNo ratings yet
- Applications of Group Theory in CryptographyDocument5 pagesApplications of Group Theory in CryptographyMajid KhanNo ratings yet
- Fromdev: Ethical Hacking BooksDocument7 pagesFromdev: Ethical Hacking BooksMorgado_JsNo ratings yet