Professional Documents
Culture Documents
D2 Watermark
D2 Watermark
Uploaded by
Samdani ShaikCopyright:
Available Formats
You might also like
- Durst Caldera: Application GuideDocument70 pagesDurst Caldera: Application GuideClaudio BasconiNo ratings yet
- Radio Frequency Identification Access Control System - Toll GateDocument2 pagesRadio Frequency Identification Access Control System - Toll GateJadeNo ratings yet
- Cape Notes Unit1 Module 2 Content 15Document5 pagesCape Notes Unit1 Module 2 Content 15Tyrick MinottNo ratings yet
- EP P1 UM Rev001Document1,013 pagesEP P1 UM Rev001Chin FattNo ratings yet
- C108 BurkeyDocument26 pagesC108 Burkeytovih27684No ratings yet
- D3 WatermarkDocument6 pagesD3 WatermarkSamdani ShaikNo ratings yet
- Ttkransomwareprotection 202309141694655795096Document62 pagesTtkransomwareprotection 202309141694655795096kucaisoftNo ratings yet
- 3. Ông Phạm Hoàng Linh, HPE Việt Nam - Bảo vệ dữ liệu và giải pháp phục hồi RansomwareDocument24 pages3. Ông Phạm Hoàng Linh, HPE Việt Nam - Bảo vệ dữ liệu và giải pháp phục hồi RansomwarethethuybnNo ratings yet
- DLP Sales Play DLP Sales 4 Common Use Cases FeaturesDocument10 pagesDLP Sales Play DLP Sales 4 Common Use Cases FeaturesJaime MoralesNo ratings yet
- 335041-TIS TD CCCv2Document27 pages335041-TIS TD CCCv2Vijju Vijayendra PSNo ratings yet
- Advanced APT Hunting Workshop 26012021 ReduxDocument136 pagesAdvanced APT Hunting Workshop 26012021 ReduxGenestapowerNo ratings yet
- Matrix 1Document7 pagesMatrix 1ashishNo ratings yet
- CISSP - Domain 1 Part 1Document21 pagesCISSP - Domain 1 Part 1ezechrissNo ratings yet
- ITS OD 102 Network SecurityDocument2 pagesITS OD 102 Network Securitynemezis86No ratings yet
- CH 01Document24 pagesCH 01Nam NguyenNo ratings yet
- Virtual Metaverse Project Proposal by Slidesgo 2Document5 pagesVirtual Metaverse Project Proposal by Slidesgo 2AGS INFOTECHNo ratings yet
- DLP Sales Play - SE - DLP Customer Deck-2022Document17 pagesDLP Sales Play - SE - DLP Customer Deck-2022Jaime MoralesNo ratings yet
- CISSP - AllDocument530 pagesCISSP - Alltoyeve4326No ratings yet
- PPS ManwinDocument38 pagesPPS ManwinzenhtNo ratings yet
- Fasoo Brochure Fasoo Enterprise DRMDocument2 pagesFasoo Brochure Fasoo Enterprise DRMsarontomiguelNo ratings yet
- Information Security ManagementDocument7 pagesInformation Security ManagementVineet KakkarNo ratings yet
- Leveraging Centralized Threat IntelligenceDocument16 pagesLeveraging Centralized Threat Intelligenceknow_idea8867No ratings yet
- Data TheftDocument7 pagesData TheftAtinuke OweteNo ratings yet
- Cloud 2Document1 pageCloud 2Abhishek DangolNo ratings yet
- Forcepoint Security Solutions Reference GuideDocument1 pageForcepoint Security Solutions Reference Guidehoangtruc.ptitNo ratings yet
- How To Use Splunk For Automated Regulatory Compliance PDFDocument74 pagesHow To Use Splunk For Automated Regulatory Compliance PDFDennis DubeNo ratings yet
- NSA Sharkseer PDFDocument12 pagesNSA Sharkseer PDFJuan100% (1)
- Computer Security 1Document18 pagesComputer Security 1Nguyen Thien Bang (K17 HL)No ratings yet
- InDefend Data SheetDocument3 pagesInDefend Data Sheetabhijit379No ratings yet
- Revisionary NotesDocument15 pagesRevisionary Notesvarchasvini malhotraNo ratings yet
- Forcepoint - Data Protection WhiteboardDocument11 pagesForcepoint - Data Protection WhiteboardHenrique OliveiraNo ratings yet
- Lab 1Document4 pagesLab 1akadapanda25No ratings yet
- DNN DPCS Webinar (4) Security 101Document12 pagesDNN DPCS Webinar (4) Security 101Chen MichaelNo ratings yet
- 1.1 - Introduction and Technical Overview - PresentationDocument27 pages1.1 - Introduction and Technical Overview - PresentationMohannad DawoudNo ratings yet
- Deep Dive SOAR 2Document22 pagesDeep Dive SOAR 2jesusmaitaNo ratings yet
- GravityZone OnPremise-1Document162 pagesGravityZone OnPremise-1Irina NastasescuNo ratings yet
- Ensuring Database Compliance With Real-Time Database Monitoring, Security & AuditingDocument39 pagesEnsuring Database Compliance With Real-Time Database Monitoring, Security & AuditingmohitsportNo ratings yet
- Windows SecurityDocument31 pagesWindows Securityhussien100% (1)
- Core PAS-DS-Mar-2019-2Document2 pagesCore PAS-DS-Mar-2019-2Trinh Hoang LongNo ratings yet
- Ptima XR X: Security, Backup/Restore & LFCDocument19 pagesPtima XR X: Security, Backup/Restore & LFCSyarif AlfathNo ratings yet
- Document 3Document1 pageDocument 3zoeijfoizjefNo ratings yet
- INTRO TO ICT NotesDocument9 pagesINTRO TO ICT Notesnabihah zaidiNo ratings yet
- CS NotesDocument36 pagesCS NotesJ2XNo ratings yet
- 5 - McAfee - Endpoint DLP Overview PDFDocument32 pages5 - McAfee - Endpoint DLP Overview PDFtestNo ratings yet
- ScaleProtect Competitive Battlecard - DELLDocument2 pagesScaleProtect Competitive Battlecard - DELLLucho VillamilNo ratings yet
- Ciso Workshop 3 Identity and Zero Trust User Access PDFDocument26 pagesCiso Workshop 3 Identity and Zero Trust User Access PDFHigino Domingos de Almeida JoãoNo ratings yet
- CyberArk EPM Overview 1Document31 pagesCyberArk EPM Overview 1Quan TranNo ratings yet
- Howtomakeyourcloudsase 200611211429Document17 pagesHowtomakeyourcloudsase 200611211429manishNo ratings yet
- Mcafee Professional Services Building Security Into ProjectsDocument24 pagesMcafee Professional Services Building Security Into Projectsvalliappan alNo ratings yet
- MS-Defender-endpoint Competitive Cheatsheet - CleanedDocument3 pagesMS-Defender-endpoint Competitive Cheatsheet - CleanedHugo GarciaNo ratings yet
- Cyber Recovery Workshop 2024 - Protecting Using PPDM and CyberSense Analysis, Reports and SyslogDocument54 pagesCyber Recovery Workshop 2024 - Protecting Using PPDM and CyberSense Analysis, Reports and SyslogMurad SultanzadehNo ratings yet
- Maximum Security Architecture: Securing Data at Its SourceDocument9 pagesMaximum Security Architecture: Securing Data at Its SourceSneha PednekarNo ratings yet
- Threat Analysis Report: Hash Values File Details EnvironmentDocument28 pagesThreat Analysis Report: Hash Values File Details Environmenttodo nothingNo ratings yet
- TNC Briefing 2013 12 10Document31 pagesTNC Briefing 2013 12 10threatsource2023No ratings yet
- DigiSAFE Data Diode & FCS (2018-06-27)Document15 pagesDigiSAFE Data Diode & FCS (2018-06-27)Tuan MANo ratings yet
- DLP PresentationDocument59 pagesDLP PresentationnagarjunaNo ratings yet
- Jay Identity-First Security TechExDocument30 pagesJay Identity-First Security TechExJayavignesh ZohoNo ratings yet
- HW - Uds - Cyber - RecoveryDocument29 pagesHW - Uds - Cyber - Recoveryl00pback63No ratings yet
- Information AssuranceDocument7 pagesInformation Assurancelols14029No ratings yet
- SecurityDocument57 pagesSecurityYovxy MaNo ratings yet
- HKPM OFFICIAL Rules & PunishmentsDocument10 pagesHKPM OFFICIAL Rules & PunishmentsIvan LauNo ratings yet
- Conveying Equipment Product Handbook PDFDocument78 pagesConveying Equipment Product Handbook PDFAscencio Ruben100% (1)
- User Manual - TAD110(排版)Document78 pagesUser Manual - TAD110(排版)Anirudha Singh ThakurNo ratings yet
- Assignment: Internet of ThingsDocument26 pagesAssignment: Internet of ThingsArslan MukhtarNo ratings yet
- As-525 Axtrax Software Manual 190409Document108 pagesAs-525 Axtrax Software Manual 190409VolvoxdjNo ratings yet
- Memorandum Memorandum Circular No. 2023 133 Regarding Barangay at Kalinisan Day BarKaDaDocument1 pageMemorandum Memorandum Circular No. 2023 133 Regarding Barangay at Kalinisan Day BarKaDahermanos belen100% (1)
- WalltzDocument10 pagesWalltzPreeti Kumari SharmaNo ratings yet
- Logcat Prev CSC LogDocument218 pagesLogcat Prev CSC Logdeiby colinaNo ratings yet
- The Information Technology Act 2000Document9 pagesThe Information Technology Act 2000Birendra PushpakarNo ratings yet
- Cryptosummary PDFDocument2 pagesCryptosummary PDFMichelleNo ratings yet
- Lect 2Document27 pagesLect 2abhs82No ratings yet
- Computer Ethics RevisedDocument19 pagesComputer Ethics RevisedNaitsirhc RelloNo ratings yet
- Cold City Quickplay DemoDocument5 pagesCold City Quickplay DemofsultanaNo ratings yet
- Reverse Reach SettingDocument2 pagesReverse Reach SettingAashwinAndeNo ratings yet
- Unity of Command ManualDocument21 pagesUnity of Command ManualNewMaxxNo ratings yet
- Fisher HF340 Filter HARTDocument4 pagesFisher HF340 Filter HARTpgarces86No ratings yet
- Cisco Unified IP Phone 9971Document8 pagesCisco Unified IP Phone 9971amartins2011No ratings yet
- Calculate PIN Block For ISO8583 PaymentsDocument4 pagesCalculate PIN Block For ISO8583 Paymentssajad salehiNo ratings yet
- Guru Jee 2Document2 pagesGuru Jee 2Abhinav RanjanNo ratings yet
- Chapter 3 Public Key Crypto Digital Sign and CertDocument78 pagesChapter 3 Public Key Crypto Digital Sign and CertNurlign YitbarekNo ratings yet
- Define Accrual Plan Element and Accrual Plan Part 2 PDFDocument22 pagesDefine Accrual Plan Element and Accrual Plan Part 2 PDFppnsankarNo ratings yet
- 2000-06 The Computer Paper - Ontario EditionDocument140 pages2000-06 The Computer Paper - Ontario EditionthecomputerpaperNo ratings yet
- SiteDocument2 pagesSitealiNo ratings yet
- TIS Security AgreementDocument2 pagesTIS Security AgreementRick YaoNo ratings yet
- Net - ST - Security Protocols XXIV 24th International Workshop - BrnoDocument242 pagesNet - ST - Security Protocols XXIV 24th International Workshop - BrnoKulqedraNo ratings yet
- What Is A Digital SignatureDocument11 pagesWhat Is A Digital SignatureMohitNo ratings yet
- Paper Concept The Importance of Cybersecurity Education in SchoolDocument17 pagesPaper Concept The Importance of Cybersecurity Education in Schoolapi-444048246No ratings yet
- Manual Minero SP20 - JacksonDocument23 pagesManual Minero SP20 - JacksonajrandisiNo ratings yet
D2 Watermark
D2 Watermark
Uploaded by
Samdani ShaikOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
D2 Watermark
D2 Watermark
Uploaded by
Samdani ShaikCopyright:
Available Formats
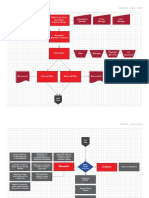
Domain 2: Asset Security Saved Comment 0 Export as PNG Share
Topic Subtopic Connection Icon Note Link 50% Theme Tips
Top secret - grave image Owner - info classifying, control selection, identify
Laws - OECD guideline, GDPR, EU-US standard, set rules of protection by senior management
Secret - serious image Privacy shield
Business owner - balance need of security control (CBA)
Government
Confidential - damage
System owner - responsible for the
Unclassified - Available to anyone system on protection the data
with free of info act (FOIA)
Data Classifcation Controller - decide what&how data process
Confidential/Proprietary - grave
image [trade secret] Data Roles Processor - third party handling data as
behalf of owner, cloud, healthcare, bank
Private - serious damange [PII,PHI]
Non-government
Custodian - day2day responsibilities
Sensitive - damage [internal network] of protection data, IT department
Public - no damage [website] Auditor - evaluate security controls
1. Create an Asset Inventory - HW (barcode, User - responsible protection of data in use, due care
RFID), SW(Software Configuration, AD,LDAP,
nmap, software license, DLP), network logs Administrator - grant access
2. Assign Ownership 1. collection - min sensitive info
Asset Classification Process
3. Classify based on value. Tips: MIX At rest - db, hard drive AES encryption (TPM, self
classification use highest level security encryption drive SED, file level encryption)
4. Protect based on classification 2. location - store In motion - tls/ssl, VPN, link encryption
(routing point), end-to-end encryption
5. Assess and Review Domain 2:
Asset
In use - RAM, caches, registers
Security
Cloud access security broker (CASB) -
monitor user activity and central 3. maintenance - use and share, scrub
control to enforce security data and remove data
Data Loss Prevention (DLP) - EOL - no new product
endpoint, network, states (rest, 4. retention - archive. Period based (prepare to discontinue)
transit, use) on regulatory, policy. Don't keep it
if don't need it EOS - no more support
Digital right management (DRM) - (end life of product)
copyright, watermark Data protection
Data lifecyle 5. remanence - destroy. Tips: get a new
Pseudonymization - alias represents data drive is more cost effective and data
remanence is hard to get rid sometime
Tokenization - random string represents data
Erasing/Delete file (recoverable) - least
Anonymization - remove all PII data effective, data remain on drive
until can't identify subject
(Irréversible) Clearing/Sanitization - prepare for
reuse. Overwrite with random bits
marking - physical marking of asset in
human readable form Purging (not recoverable) - intensive form of
Asset handling clearing for resuse in lower security level. E.g
6. destruction zeroization, crypto shredding, degaussing
labelling - associate with security
attributes. Metadata help DLP to flag
Degaussing - tapes, magnetic disk. Not
Scoping (which) - select part of control apply to optical disk, SSD
Tailoring (fit)- modify control to Requirements Destruction (cannot reuse) - SSD acidic
align org's mission, better address spoil, shredding, incineration (burnt),
with org's environment disintegration (pieces), most secure
You might also like
- Durst Caldera: Application GuideDocument70 pagesDurst Caldera: Application GuideClaudio BasconiNo ratings yet
- Radio Frequency Identification Access Control System - Toll GateDocument2 pagesRadio Frequency Identification Access Control System - Toll GateJadeNo ratings yet
- Cape Notes Unit1 Module 2 Content 15Document5 pagesCape Notes Unit1 Module 2 Content 15Tyrick MinottNo ratings yet
- EP P1 UM Rev001Document1,013 pagesEP P1 UM Rev001Chin FattNo ratings yet
- C108 BurkeyDocument26 pagesC108 Burkeytovih27684No ratings yet
- D3 WatermarkDocument6 pagesD3 WatermarkSamdani ShaikNo ratings yet
- Ttkransomwareprotection 202309141694655795096Document62 pagesTtkransomwareprotection 202309141694655795096kucaisoftNo ratings yet
- 3. Ông Phạm Hoàng Linh, HPE Việt Nam - Bảo vệ dữ liệu và giải pháp phục hồi RansomwareDocument24 pages3. Ông Phạm Hoàng Linh, HPE Việt Nam - Bảo vệ dữ liệu và giải pháp phục hồi RansomwarethethuybnNo ratings yet
- DLP Sales Play DLP Sales 4 Common Use Cases FeaturesDocument10 pagesDLP Sales Play DLP Sales 4 Common Use Cases FeaturesJaime MoralesNo ratings yet
- 335041-TIS TD CCCv2Document27 pages335041-TIS TD CCCv2Vijju Vijayendra PSNo ratings yet
- Advanced APT Hunting Workshop 26012021 ReduxDocument136 pagesAdvanced APT Hunting Workshop 26012021 ReduxGenestapowerNo ratings yet
- Matrix 1Document7 pagesMatrix 1ashishNo ratings yet
- CISSP - Domain 1 Part 1Document21 pagesCISSP - Domain 1 Part 1ezechrissNo ratings yet
- ITS OD 102 Network SecurityDocument2 pagesITS OD 102 Network Securitynemezis86No ratings yet
- CH 01Document24 pagesCH 01Nam NguyenNo ratings yet
- Virtual Metaverse Project Proposal by Slidesgo 2Document5 pagesVirtual Metaverse Project Proposal by Slidesgo 2AGS INFOTECHNo ratings yet
- DLP Sales Play - SE - DLP Customer Deck-2022Document17 pagesDLP Sales Play - SE - DLP Customer Deck-2022Jaime MoralesNo ratings yet
- CISSP - AllDocument530 pagesCISSP - Alltoyeve4326No ratings yet
- PPS ManwinDocument38 pagesPPS ManwinzenhtNo ratings yet
- Fasoo Brochure Fasoo Enterprise DRMDocument2 pagesFasoo Brochure Fasoo Enterprise DRMsarontomiguelNo ratings yet
- Information Security ManagementDocument7 pagesInformation Security ManagementVineet KakkarNo ratings yet
- Leveraging Centralized Threat IntelligenceDocument16 pagesLeveraging Centralized Threat Intelligenceknow_idea8867No ratings yet
- Data TheftDocument7 pagesData TheftAtinuke OweteNo ratings yet
- Cloud 2Document1 pageCloud 2Abhishek DangolNo ratings yet
- Forcepoint Security Solutions Reference GuideDocument1 pageForcepoint Security Solutions Reference Guidehoangtruc.ptitNo ratings yet
- How To Use Splunk For Automated Regulatory Compliance PDFDocument74 pagesHow To Use Splunk For Automated Regulatory Compliance PDFDennis DubeNo ratings yet
- NSA Sharkseer PDFDocument12 pagesNSA Sharkseer PDFJuan100% (1)
- Computer Security 1Document18 pagesComputer Security 1Nguyen Thien Bang (K17 HL)No ratings yet
- InDefend Data SheetDocument3 pagesInDefend Data Sheetabhijit379No ratings yet
- Revisionary NotesDocument15 pagesRevisionary Notesvarchasvini malhotraNo ratings yet
- Forcepoint - Data Protection WhiteboardDocument11 pagesForcepoint - Data Protection WhiteboardHenrique OliveiraNo ratings yet
- Lab 1Document4 pagesLab 1akadapanda25No ratings yet
- DNN DPCS Webinar (4) Security 101Document12 pagesDNN DPCS Webinar (4) Security 101Chen MichaelNo ratings yet
- 1.1 - Introduction and Technical Overview - PresentationDocument27 pages1.1 - Introduction and Technical Overview - PresentationMohannad DawoudNo ratings yet
- Deep Dive SOAR 2Document22 pagesDeep Dive SOAR 2jesusmaitaNo ratings yet
- GravityZone OnPremise-1Document162 pagesGravityZone OnPremise-1Irina NastasescuNo ratings yet
- Ensuring Database Compliance With Real-Time Database Monitoring, Security & AuditingDocument39 pagesEnsuring Database Compliance With Real-Time Database Monitoring, Security & AuditingmohitsportNo ratings yet
- Windows SecurityDocument31 pagesWindows Securityhussien100% (1)
- Core PAS-DS-Mar-2019-2Document2 pagesCore PAS-DS-Mar-2019-2Trinh Hoang LongNo ratings yet
- Ptima XR X: Security, Backup/Restore & LFCDocument19 pagesPtima XR X: Security, Backup/Restore & LFCSyarif AlfathNo ratings yet
- Document 3Document1 pageDocument 3zoeijfoizjefNo ratings yet
- INTRO TO ICT NotesDocument9 pagesINTRO TO ICT Notesnabihah zaidiNo ratings yet
- CS NotesDocument36 pagesCS NotesJ2XNo ratings yet
- 5 - McAfee - Endpoint DLP Overview PDFDocument32 pages5 - McAfee - Endpoint DLP Overview PDFtestNo ratings yet
- ScaleProtect Competitive Battlecard - DELLDocument2 pagesScaleProtect Competitive Battlecard - DELLLucho VillamilNo ratings yet
- Ciso Workshop 3 Identity and Zero Trust User Access PDFDocument26 pagesCiso Workshop 3 Identity and Zero Trust User Access PDFHigino Domingos de Almeida JoãoNo ratings yet
- CyberArk EPM Overview 1Document31 pagesCyberArk EPM Overview 1Quan TranNo ratings yet
- Howtomakeyourcloudsase 200611211429Document17 pagesHowtomakeyourcloudsase 200611211429manishNo ratings yet
- Mcafee Professional Services Building Security Into ProjectsDocument24 pagesMcafee Professional Services Building Security Into Projectsvalliappan alNo ratings yet
- MS-Defender-endpoint Competitive Cheatsheet - CleanedDocument3 pagesMS-Defender-endpoint Competitive Cheatsheet - CleanedHugo GarciaNo ratings yet
- Cyber Recovery Workshop 2024 - Protecting Using PPDM and CyberSense Analysis, Reports and SyslogDocument54 pagesCyber Recovery Workshop 2024 - Protecting Using PPDM and CyberSense Analysis, Reports and SyslogMurad SultanzadehNo ratings yet
- Maximum Security Architecture: Securing Data at Its SourceDocument9 pagesMaximum Security Architecture: Securing Data at Its SourceSneha PednekarNo ratings yet
- Threat Analysis Report: Hash Values File Details EnvironmentDocument28 pagesThreat Analysis Report: Hash Values File Details Environmenttodo nothingNo ratings yet
- TNC Briefing 2013 12 10Document31 pagesTNC Briefing 2013 12 10threatsource2023No ratings yet
- DigiSAFE Data Diode & FCS (2018-06-27)Document15 pagesDigiSAFE Data Diode & FCS (2018-06-27)Tuan MANo ratings yet
- DLP PresentationDocument59 pagesDLP PresentationnagarjunaNo ratings yet
- Jay Identity-First Security TechExDocument30 pagesJay Identity-First Security TechExJayavignesh ZohoNo ratings yet
- HW - Uds - Cyber - RecoveryDocument29 pagesHW - Uds - Cyber - Recoveryl00pback63No ratings yet
- Information AssuranceDocument7 pagesInformation Assurancelols14029No ratings yet
- SecurityDocument57 pagesSecurityYovxy MaNo ratings yet
- HKPM OFFICIAL Rules & PunishmentsDocument10 pagesHKPM OFFICIAL Rules & PunishmentsIvan LauNo ratings yet
- Conveying Equipment Product Handbook PDFDocument78 pagesConveying Equipment Product Handbook PDFAscencio Ruben100% (1)
- User Manual - TAD110(排版)Document78 pagesUser Manual - TAD110(排版)Anirudha Singh ThakurNo ratings yet
- Assignment: Internet of ThingsDocument26 pagesAssignment: Internet of ThingsArslan MukhtarNo ratings yet
- As-525 Axtrax Software Manual 190409Document108 pagesAs-525 Axtrax Software Manual 190409VolvoxdjNo ratings yet
- Memorandum Memorandum Circular No. 2023 133 Regarding Barangay at Kalinisan Day BarKaDaDocument1 pageMemorandum Memorandum Circular No. 2023 133 Regarding Barangay at Kalinisan Day BarKaDahermanos belen100% (1)
- WalltzDocument10 pagesWalltzPreeti Kumari SharmaNo ratings yet
- Logcat Prev CSC LogDocument218 pagesLogcat Prev CSC Logdeiby colinaNo ratings yet
- The Information Technology Act 2000Document9 pagesThe Information Technology Act 2000Birendra PushpakarNo ratings yet
- Cryptosummary PDFDocument2 pagesCryptosummary PDFMichelleNo ratings yet
- Lect 2Document27 pagesLect 2abhs82No ratings yet
- Computer Ethics RevisedDocument19 pagesComputer Ethics RevisedNaitsirhc RelloNo ratings yet
- Cold City Quickplay DemoDocument5 pagesCold City Quickplay DemofsultanaNo ratings yet
- Reverse Reach SettingDocument2 pagesReverse Reach SettingAashwinAndeNo ratings yet
- Unity of Command ManualDocument21 pagesUnity of Command ManualNewMaxxNo ratings yet
- Fisher HF340 Filter HARTDocument4 pagesFisher HF340 Filter HARTpgarces86No ratings yet
- Cisco Unified IP Phone 9971Document8 pagesCisco Unified IP Phone 9971amartins2011No ratings yet
- Calculate PIN Block For ISO8583 PaymentsDocument4 pagesCalculate PIN Block For ISO8583 Paymentssajad salehiNo ratings yet
- Guru Jee 2Document2 pagesGuru Jee 2Abhinav RanjanNo ratings yet
- Chapter 3 Public Key Crypto Digital Sign and CertDocument78 pagesChapter 3 Public Key Crypto Digital Sign and CertNurlign YitbarekNo ratings yet
- Define Accrual Plan Element and Accrual Plan Part 2 PDFDocument22 pagesDefine Accrual Plan Element and Accrual Plan Part 2 PDFppnsankarNo ratings yet
- 2000-06 The Computer Paper - Ontario EditionDocument140 pages2000-06 The Computer Paper - Ontario EditionthecomputerpaperNo ratings yet
- SiteDocument2 pagesSitealiNo ratings yet
- TIS Security AgreementDocument2 pagesTIS Security AgreementRick YaoNo ratings yet
- Net - ST - Security Protocols XXIV 24th International Workshop - BrnoDocument242 pagesNet - ST - Security Protocols XXIV 24th International Workshop - BrnoKulqedraNo ratings yet
- What Is A Digital SignatureDocument11 pagesWhat Is A Digital SignatureMohitNo ratings yet
- Paper Concept The Importance of Cybersecurity Education in SchoolDocument17 pagesPaper Concept The Importance of Cybersecurity Education in Schoolapi-444048246No ratings yet
- Manual Minero SP20 - JacksonDocument23 pagesManual Minero SP20 - JacksonajrandisiNo ratings yet