Professional Documents
Culture Documents
DSA Sample2
DSA Sample2
Uploaded by
armirshadh22Original Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
DSA Sample2
DSA Sample2
Uploaded by
armirshadh22Copyright:
Available Formats
lOMoARcPSD|20224103
DSA - E130941 - Assignment with answers
HND in Computing (ESOFT Metro Campus)
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
Studocu is not sponsored or endorsed by any college or university
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
Higher Nationals
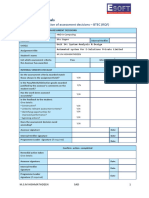
Internal verification of assessment decisions – BTEC (RQF)
INTERNAL VERIFICATION – ASSESSMENT DECISIONS
Programme title Higher National Diploma in Computing
Assessor Internal Verifier
Unit 19 – Data Structures and Algorithms
Unit(s)
Specification, Implementation, and Assessment of Data Structures for a sample
Assignment title scenario.
M.S. MARYAM RUQSHA
Student’s name
List which assessment criteria Pass Merit Distinction
the Assessor has awarded.
INTERNAL VERIFIER CHECKLIST
Do the assessment criteria awarded match
those shown in the assignment brief?
Y/N
Is the Pass/Merit/Distinction grade awarded
justified by the assessor’s comments on the
Y/N
student work?
Has the work been assessed accurately?
Y/N
Is the feedback to the student:
Give details:
• Constructive?
• Linked to relevant assessment criteria?
Y/N
• Identifying opportunities for improved
Y/N Y/N
performance?
Y/N
• Agreeing actions?
Does the assessment decision need
amending? Y/N
Assessor signature Date
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
Internal Verifier signature Date
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 1
Programme Leader signature (if required)
Date
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 2
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
Confirm action completed
Remedial action taken
Give details:
Assessor signature Date
Internal Verifier
signature Date
Programme Leader
signature (if required) Date
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 3
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
Higher Nationals - Summative
Assignment Feedback Form
Student Name/ID M.S. MARYAM RUQSHA / E130941
Unit Title Unit 19: Data Structures and Algorithms
Assignment Number 1 Assessor
04/04/2023 Date Received 1st
Submission Date submission
Date Received 2nd
Re-submission Date submission
Assessor Feedback:
LO1 Examine different concrete data structures and it’s valid operations.
Pass, Merit & P1 P2 M1 M2 D1
Distinction Descripts
LO2 Discuss the advantages, complexity of Abstract Data Type and importance concepts of Object
orientation.
Pass, Merit & P3 M3 D2
Distinction Descripts
LO3 Implement, Demonstrate and evaluate complex ADT algorithm.
Pass, Merit & P4 P5 M4 D3
Distinction Descripts
LO4 Examine the advantages of Independent data structures and discuss the need of asymptotic
analysis to assess the effectiveness of an algorithm.
Pass, Merit & P6 P7 M5 D4
Distinction Descripts
Grade: Assessor Signature: Date:
Resubmission Feedback:
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 4
Grade: Assessor Signature: Date:
Internal Verifier’s Comments:
Signature & Date:
* Please note that grade decisions are provisional. They are only confirmed once internal and external moderation has taken place and grades
decisions have been agreed at the assessment board.
Assignment Feedback
Formative Feedback: Assessor to Student
Action Plan
Summative feedback
Feedback: Student to Assessor
Assessor signature Date
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
Student signature Date
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 5
Pearson Higher Nationals in
Computing
Unit 19: Data Structures & Algorithms
Assignment 01
M.S. MARYAM RUQSHA - COL00088920
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 6 General Guidelines
• A Cover page or title page – You should always attach a title page to your assignment. Use
previous page as your cover sheet and make sure all the details are accurately filled.
• Attach this brief as the first section of your assignment.
• All the assignments should be prepared using a word processing software.
• All the assignments should be printed on A4 sized papers. Use single side printing.
• Allow 1” for top, bottom , right margins and 1.25” for the left margin of each page. Word
Processing Rules
• The font size should be 12 point, and should be in the style of Time New Roman.
• Use 1.5 line spacing. Left justify all paragraphs.
• Ensure that all the headings are consistent in terms of the font size and font style.
• Use footer function in the word processor to insert Your Name, Subject, Assignment No, and
Page Number on each page. This is useful if individual sheets become detached for any reason.
• Use word processing application spell check and grammar check function to help editing your
assignment.
Important Points:
• It is strictly prohibited to use textboxes to add texts in the assignments, except for the
compulsory information. eg: Figures, tables of comparison etc. Adding text boxes in the body
except for the before mentioned compulsory information will result in rejection of your work.
• Carefully check the hand in date and the instructions given in the assignment. Late submissions
will not be accepted.
• Ensure that you give yourself enough time to complete the assignment by the due date.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
• Excuses of any nature will not be
accepted for failure to hand in the work
on time.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 7
• You must take responsibility for managing your own time effectively.
• If you are unable to hand in your assignment on time and have valid reasons such as illness, you
may apply (in writing) for an extension.
• Failure to achieve at least PASS criteria will result in a REFERRAL grade .
• Non-submission of work without valid reasons will lead to an automatic RE FERRAL. You will
then be asked to complete an alternative assignment.
• If you use other people’s work or ideas in your assignment, reference them properly using
HARVARD referencing system to avoid plagiarism. You have to provide both in-text citation and a
reference list.
• If you are proven to be guilty of plagiarism or any academic misconduct, your grade could be
reduced to A REFERRAL or at worst you could be expelled from the course
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 8 Student Declaration
I hereby, declare that I know what plagiarism entails, namely to use another’s work and to present it as my
own without attributing the sources in the correct form. I further understand what it means to copy
another’s work.
• I know that plagiarism is a punishable offence because it constitutes theft.
• I understand the plagiarism and copying policy of Edexcel UK.
• I know what the consequences will be if I plagiarize or copy another’s work in any of the
assignments for this program.
• I declare therefore that all work presented by me for every aspect of my program, will be my
own, and where I have made use of another’s work, I will attribute the source in the correct way.
• I acknowledge that the attachment of this document signed or not, constitutes a binding
agreement between myself and Pearson, UK.
• I understand that my assignment will not be considered as submitted if this document is not
attached to the assignment.
maryamruqsha16@gmail.com 04/04/2023 Student’s
Signature: Date:
(Provide E-mail ID) (Provide Submission Date)
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 9
Higher National Diploma in Business
Assignment Brief
Student Name /ID Number M.S. MARYAM RUQSHA / E130941
Unit Number and Title Unit 19 : Data Structures and Algorithms
Academic Year 2021/22
Unit Tutor
Assignment Title Specification, Implementation, and Assessment of Data Structures for a
sample scenario.
Issue Date
Submission Date 04/04/2023
IV Name & Date
Submission format
The submission should be in the form of a report, which contains code snippets (which must be
described well), text-based descriptions, and diagrams where appropriate. References to external
sources of knowledge must be cited (reference list supported by in-text citations) using the Harvard
Referencing style.
Unit Learning Outcomes:
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
LO1. Examine abstract data types, concrete data structures and algorithms.
LO2. Specify abstract data types and algorithms in a formal notation.
LO3. Implement complex data structures and algorithms.
LO4. Assess the effectiveness of data structures and algorithms.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 10
Assignment Brief and Guidance:
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
Scenario
ABC Pvt Ltd organizing Car Racing event across western province and they decided to have maximum
of 6 cars(participants) to compete.
There are totally 3 Rounds and at the end of each round lowest rank car will be eliminated from the
Race.
Each car has unique number, brand, sponsor and driver details.
In order to manage this particular event ABC Pvt Ltd decided to develop an Application.
Application functions are listed down.
1.Register Car Details
2.Delete a car
3.Insert 3 Rounds Results.
4.Find out the winners (1st,2nd,3rd)
5.Search for a particular car
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 11
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
Task 1: Examine and create data structure by simulating the above scenario and explain the valid
operations that can be carried out on this data structure.
Determine the operations of a queue and critically review how it is used to implement function calls
related to the above scenario.
Task 2: Implement the above scenario using the selected data structure and its valid operations for
the design specification given in task 1 by using java programming. Use suitable error handling and
Test the application using suitable test cases and illustrate the system. Provide evidence of the test
cases and the test results.
Task 3 : Registered Car details are stored from oldest to newest. Management of ABC Pvt Ltd should
be able to find from the newest to oldest registered car details. Using an imperative definition,
specify the abstract data type for the above scenario and implement specified ADT using java
programming and briefly discuss the complexity of chosen ADT algorithm. List down the advantages
of Encapsulation and Information hiding when using an ADT selected for the above scenario.
“Imperative ADTs are basis for object orientation.” Discuss the above view stating whether you agree
or not. Justify your answer.
Task 4: ABC Pvt Ltd plans to visit all of these participants through the shortest path within a day.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 12
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
Analyse the above operation by using illustrations, of two shortest path algorithms, specify how it
operates using a sample graph diagram. Sort the cars based on numbers with two different sorting
algorithms and critically review the performances of those two algorithms by comparing them.
Task 5: Evaluate how Asymptotic analysis can be used to assess the effectiveness of an algorithm
and critically evaluate the different ways in which the efficiency of an algorithm can be measured.
Critically review the sort of trade-offs exists when you use an ADT for implementing programs. You
also need to evaluate the benefits of using independent data structures for implementing programs.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 13
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
Grading Rubric
Grading Criteria Achieved Feedback
LO1. Examine abstract data types, concrete
data structures and algorithms.
P1 Create a design specification for data
structures explaining the valid operations
that can be carried out on the structures.
P2 Determine the operations of a memory
stack and how it is used to implement
function calls in a computer.
M1 Illustrate, with an example, a concrete
data structure for a First In First out (FIFO)
queue.
M2 Compare the performance of two sorting
algorithms.
D1 Analyse the operation, using illustrations,
of two network shortest path algorithms,
providing an example of each.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 14
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
LO2. Specify abstract data types and
algorithms in a formal notation.
P3 Using an imperative definition, specify
the abstract data type for a software stack.
M3 Examine the advantages of
encapsulation and information hiding
when using an ADT.
D2 Discuss the view that imperative ADTs are
a basis for object orientation and, with
justification, state whether you agree.
LO3. Implement complex data structures
and algorithms.
P4 Implement a complex ADT and algorithm
in an executable programming language to
solve a well-defined problem.
P5 Implement error handling and report test
results.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 15
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M4 Demonstrate how the implementation of
an ADT/algorithm solves a well-defined
problem.
D3 Critically evaluate the complexity of an
implemented ADT/algorithm.
LO4. Assess the effectiveness of data
structures and algorithms.
P6 Discuss how asymptotic analysis can be
used to assess the effectiveness of an
algorithm.
P7 Determine two ways in which the
efficiency of an algorithm can be measured,
illustrating your answer with an example.
M5 Interpret what a trade-off is when
specifying an ADT using an example to
support your answer.
D4 Evaluate three benefits of using
implementation independent data
structures.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 16
Table of Contents
Acknowledgement.............................................................................................................................22
1. Data Structure and Algorithm.......................................................................................................23
1.1 Design Specifications for Data Structure..............................................................................23
1.2 Fundamental kinds of Data Structures..................................................................................25
1.3 Algorithms............................................................................................................................. 26
1.4 The accompanying PC issues can be settled using Data Structures.......................................28
2. Create data structure by simulating the above scenario and explain the valid operations that
can be carried out on this data structure............................................................................................29
2.1 Data structure for given scenario...........................................................................................29
2.1.1 Linked list Data structure.................................................................................................29
2.1.1.1 Linked List Representation.......................................................................................30
2.1.1.2 Uses of Linked list....................................................................................................30
2.1.1.3 Types of Linked list..................................................................................................31
2.1.1.4 Performing various operations on linked list............................................................32
2.1.2 LIFO principle of Stack....................................................................................................34
2.1.2.1 Basic operation of stack............................................................................................36
2.1.2.2 Flowchart for implementing stack using array..........................................................39
2.1.2.3 Representation of stack.............................................................................................42
2.1.3 Stack memory implementation for PCs............................................................................43
3. Illustrate, with an example, a concrete data structure for a First in First out (FIFO) queue........47
3.1 Queue Data Structure.............................................................................................................47
4. Illustrate, with an example, a concrete data structure for a First in First out (FIFO) queue........52
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 17
4.1 Software Stack.....................................................................................................................
52
4.2 Abstract Data Type (ADT) ..................................................................................................
53
4.2.1 Common Examples of ADTs .......................................................................................
55
4.2.1.1 List ADT ................................................................................................................ 55
4.2.1.2 Stack ADT ............................................................................................................. 57
4.2.1.3 Queue ADT ............................................................................................................ 58
4.2.2 Stack, Queue and List Abstract Data Type Comparison ..............................................
59
4.3 Selecting the suitable ADT for the scenario and implementing it ......................................
60
5. Implement a complex ADT and algorithm in an executable programming language to solve
a well-defined problem. ................................................................................................................
61
5.1 Describe the scenario and design the system ......................................................................
61
5.2 Implementation the system..................................................................................................
62
5.2.1 Full functionable code which I used in my application ................................................
69
5.3 Implementation of the fully commented code.....................................................................
77
5.4 Output of the codes .............................................................................................................
83
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
5.5 Complexity of Stack
ADT ............................................................
...................................... 89
5.6 Encapsulation ......................................................................................................................
90
5.6.1 Advantages of using Encapsulation ..............................................................................
92
6. Implement Error Handling and Report Test Results. ............................................................
94
6.1 Error Handling.....................................................................................................................
94
6.1.1 Option and Unwrap ......................................................................................................
96
6.1.2 Panic .............................................................................................................................
99
6.1.3 Result ..........................................................................................................................
100
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 18
6.1.4 Multiple error type ......................................................................................................
102
6.1.5 Iterative over results ...................................................................................................
103
6.1.6 Handling Errors using Do-Catch ................................................................................
107
6.1.7 Changing Error over to Option values ........................................................................
108
6.1.8 Bugs Versus exceptions ..............................................................................................
109
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
6.1.9 Error handling
implementation .......................................
............................................ 109
6.2 Test report .........................................................................................................................
112
6.2.1 Why test report is important. ......................................................................................
113
6.2.2 What does test report contain .....................................................................................
114
6.2.3 Test results screen shot for given scenario. ................................................................
115
7. Discuss how asymptotic analysis can be used to assess the effectiveness of an algorithm. 118
7.1 Asymptotic analysis ..........................................................................................................
118
7.2 Most pessimistic scenario and Average-Case Analysis .................................................... 119
7.3 Calculation Efficiency and Asymptotic Analysis ............................................................. 120
7.3.1 Issue with timing code ................................................................................................
122
7.3.2 Analysis Framework ...................................................................................................
123
7.3.3 Asymptotic notation ...................................................................................................
125
8. Determine two ways in which the efficiency of an algorithm can be measured, illustrating
your answer with an example. ....................................................................................................
128
8.1 Algorithm Efficiency.........................................................................................................
128
8.1.1 Time complexity .........................................................................................................
128
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
8.1.2 Space
complexity .....................................
................................................................... 129
9. Conclusion ...........................................................................................................................
140
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 19
List of Figures
Figure 1: LIFO ..............................................................................................................................................
34 Figure 2: Flowchart for Push ()
Operation .................................................................................................. 39 Figure 3: Flowchart for Pop ()
Operations .................................................................................................. 40
Figure 4: Flowchart for Peek () Operations .................................................................................................
41 Figure 5: Stack
Representation ................................................................................................................... 42 Figure 6:
Stack functioning Principle ........................................................................................................... 45 Figure
7: Car class........................................................................................................................................ 62
Figure 8: Main Class ....................................................................................................................................
63 Figure 9:
Function ....................................................................................................................................... 63 Figure
10: Case 1 ......................................................................................................................................... 64
Figure 11: Case 2 .........................................................................................................................................
65 Figure 12: Case
3 ......................................................................................................................................... 66 Figure 13:
Case 4 ......................................................................................................................................... 67 Figure
14: Case 5 ......................................................................................................................................... 68
Figure 15: Function list ................................................................................................................................
83 Figure 16: Case 1
Output ............................................................................................................................ 83 Figure 17: Case
1 Output 2.......................................................................................................................... 84 Figure 18:
Delete a car Case 2 ..................................................................................................................... 85 Figure
19: Case 3 ......................................................................................................................................... 86
Figure 20: Case 4 .........................................................................................................................................
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
87 Figure 21: Case
5 ......................................................................................................................................... 88 Figure 22:
Case 6 ......................................................................................................................................... 88 Figure
23: Encapsulation example .............................................................................................................. 91
Figure 24: Error Handling ............................................................................................................................
94 Figure 25: Error log ...................................................................................................................................
109 Figure 26: Try
catch1 ................................................................................................................................. 110 Figure 27:
Try catch 2 ................................................................................................................................ 111 Figure
28: Test cycle .................................................................................................................................. 115
Figure 29: Functions ..................................................................................................................................
116 M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 20 Figure 30:
Defect density .......................................................................................................................... 116 Figure
31: Defect Fixed Ratio .................................................................................................................... 117
Figure 32: Θ Notation (theta) ....................................................................................................................
132 Figure 33: Ω
Notation................................................................................................................................ 133 Figure 34:
Big O notation .......................................................................................................................... 135
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 21
Acknowledgement
First and foremost I wish to thank my lord and my parents who is my constant source of help,
strength and support and who is truly is my all in all. A very big thank you to our course
Coordinator Miss. Chathurika and Our Data Structure & Algorithms module Lecturer Miss.
Navodi and all the other lecturers for all the support, patience guidance and valuable advice
they gave me throughout this assignment, without them this project would not have been
possible. I sincerely acknowledge and thank my mother, my father and my friends who gave
moral support for me to complete the project duly. I am thankful and fortunate enough to get
constant encouragement, support and guidance from my family who sacrificed their works and
helped me in successfully my project work. I would also like to take this opportunity to thank
Esoft for giving me such a great opportunity. Thank you all.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 22
1. Data Structure and Algorithm
The usage of a data structure allows for the efficient organization and storage of data in a
computer. Hash tables, trees, graphs, linked lists, and arrays are examples of common data
structures. Data structures offer a way to efficiently manage massive volumes of data for a
variety of applications, including databases, search engines, and video games.
A set of instructions or procedures used to solve a problem or carry out a task is known as an
algorithm. In computer programming, algorithms are used to process data, carry out calculations,
and reach decisions. They can be used in a variety of programming languages and are an
essential component of computer science. Effective algorithms are crucial for tackling
complicated issues and can considerably boost the speed of computer applications. The study of
algorithms involves understanding their properties such as correctness, efficiency, and
complexity.
1.1 Design Specifications for Data Structure
Design specifications for a data structure typically include:
1. Purpose and Functionality: The purpose and functionality of the data structure should be
clearly defined. This includes what types of data it will store, how it will be accessed, and
what operations can be performed on it.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 23
2. Implementation Details: Implementation details should be provided, including the
programming language to be used, the platform it will run on, and any specific memory
or performance requirements.
3. Performance Requirements: The data structure should be designed to meet performance
requirements such as memory usage, time complexity of operations, and scalability.
4. Error Handling: Error handling should be defined for situations such as invalid input or
overflow of data.
5. Security: Any security requirements such as access control or data encryption should be
defined.
6. Extensibility: The data structure should be designed with extensibility in mind, so that it
can be easily modified or extended in the future.
7. Testing and Verification: Test cases should be specified to verify that the data structure
functions as intended, and that it meets performance requirements.
8. Documentation: Documentation should be provided to explain how to use the data
structure, its limitations, and any assumptions made during design.
The design specifications for a data structure should, in general, give a clear and comprehensive
understanding of how the data structure is meant to operate as well as how it should be
implemented and evaluated.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 24
1.2 Fundamental kinds of Data Structures
There are several fundamental kinds of data structures. Here are some of the most common:
1. Arrays: An array is a collection of elements of the same data type that are stored in
contiguous memory locations. It is used for storing and accessing a fixed number of
elements efficiently.
2. Linked Lists: A linked list is a collection of elements, where each element (node) contains
a value and a reference (pointer) to the next node. It is used for storing and accessing a
variable number of elements efficiently.
3. Stacks: A stack is a collection of elements that allows access only to the last element
inserted (LIFO – last in, first out). It is used for keeping track of the state of a program or
for solving problems that can be solved using the LIFO principle.
4. Queues: A queue is a collection of elements that allows access only to the first element
inserted (FIFO – first in, first out). It is used for managing resources, handling
interruptions, and scheduling tasks.
5. Trees: A tree is a collection of nodes connected by edges. It is used for representing
hierarchical data, such as a file system or the structure of a web page.
6. Graphs: A graph is a collection of vertices (nodes) connected by edges. It is used for
representing complex relationships between objects, such as social networks or road
networks.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
7. Hash Tables: A hash table is a
collection of key-value pairs that allows access to elements in
constant time on average. It is used for efficient searching and indexing of data.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 25
Many algorithms and computer programs use these data structures as their basic building
elements. Choosing the appropriate data structure for a given issue is essential for creating
effective algorithms and programs because each data structure has strengths and weaknesses.
1.3 Algorithms
An algorithm is a set of clear instructions for resolving a dilemma or carrying out a particular
job. Algorithms are the fundamental units of computer programs and are crucial for effectively
tackling challenging computational issues.
Algorithms are a collection of rules intended to solve a particular issue or carry out a particular
job. They are an essential component of computer science and are widely used in data
processing, programming, and other technological fields.
Sorting algorithms, searching algorithms, graph algorithms, optimization algorithms, and many
other kinds of algorithms can all be categorized. They can be represented in a variety of ways,
such as programming languages, flowcharts, and pseudo code.
An algorithm's accuracy, running time, and memory utilization are just a few examples of the
factors that affect an algorithm's efficiency and effectiveness. Algorithm design is therefore a
fundamental component of computer science, and researchers are constantly trying to create new
and improved algorithms to address ever-more-complex issues.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
The binary search algorithm, bubble sort,
quicksort, and Dijkstra's algorithm for shortest route problems are a few of
the most well-known algorithms. Here are some common types of algorithms:
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 26
1. Sorting algorithms: Sorting algorithms are used to rearrange a collection of elements in
a specific order, such as ascending or descending order. Some popular sorting algorithms
include bubble sort, quicksort, and merge sort.
2. Searching algorithms: Searching algorithms are used to find a specific element or value
in a collection of elements. Some popular search algorithms include linear search and
binary search.
3. Path finding algorithms: Path finding algorithms are used to find the shortest path
between two points in a graph or a grid. Some popular path finding algorithms include
Dijkstra's algorithm and A* algorithm.
4. Compression algorithms: Compression algorithms are used to reduce the size of a file
or data without losing significant information. Some popular compression algorithms
include Huffman coding and Lempel-Ziv-Welch (LZW) algorithm
5. Cryptographic algorithms: Cryptographic algorithms are used to ensure the security
and confidentiality of data by encrypting or decrypting it. Some popular cryptographic
algorithms include RSA, AES, and SHA.
6. Machine learning algorithms: Machine learning algorithms are used to make
predictions or decisions based on large amounts of data. Some popular machine learning
algorithms include decision trees, neural networks, and support vector machines.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
In many disciplines, including computer
science, mathematics, engineering, and economics, algorithms are used. It
is essential to comprehend algorithms and how they are used in order to effectively solve
complex problems and create successful software systems.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 27
1.4 The accompanying PC issues can be settled using Data Structures
A key idea in computer science and programming, data structures are used to arrange and store
data in a way that makes it easy to handle and retrieve it later. Although data structures can be
employed to address a variety of computing issues, they are not frequently employed to address
hardware or system-level issues with computers. However, data structures can be used to
enhance the efficiency of computer software programs and algorithms, which tangentially aids in
the resolution of some computer-related problems. For instance, if a computer application is
sluggish or unresponsive as a result of ineffective data storing and retrieval, using the right data
structure can enhance performance and fix the problem.
Data structures can also be used to effectively manage and process vast amounts of data, which
can help with problems with data management and storage. For instance, utilizing a hash table
data structure can facilitate quicker data retrieval and searching, which can assist in resolving
issues with slow database searches or ineffective data storage. In conclusion, even though data
structures themselves might not be able to handle some common computer issues directly, they
can be used to enhance the functionality of software programs and algorithms, which might be
able to do so. Data Structures can be used to solve the following PC concerns
• Fibonacci number series
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
• Backpack issue
• Pinnacle of Hanoi
• All pair most limited way by Floyd-Warshall
• Most limited way by Dijkstra
• Venture booking
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 28
2. Create data structure by simulating the above scenario and explain the
valid operations that can be carried out on this data structure
2.1 Data structure for given scenario.
Stack data structures and linked list data structures were utilized by the author to create the application for
ABC Pvt Ltd. Stacks are linear data structures that adhere to the Last in First out rule (LIFO). This
suggests that the final item to be removed from the stack does so first. When it comes to managing
dynamic data items, a linked list is the most desired data structure. A node is a type of data element found
in linked lists. Moreover, each node has two fields: one field contains data, and the other field contains an
address that maintains a link to the node after it.
2.1.1 Linked list Data structure.
A linked list is a group of links that includes stuff. There is a relationship between each link and
another link. The second most used data structure is the linked list, behind the array. The key
words for understanding the concept of a linked list are listed below.
Link − Each link of a linked list can store data called an element.
Next − Each link of a linked list contains a link to the next link called Next.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
Linked List − A Linked List contains the
connection link to the first link called First
(Anon., n.d.).
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 29
2.1.1.1 Linked List Representation
Linked list can be visualized as a chain of nodes, where every node points to the next node.
As per the above illustration, the following are the important points to be considered.
• Linked List contains a link element called first.
• Each link carries a data field(s) and a link field called next.
• Each link is linked with its next link using its next link.
• Last link carries a link as null to mark the end of the list (Anon., n.d.).
2.1.1.2 Uses of Linked list
Linked lists are a fundamental data structure in computer science and are commonly used in
programming and software development. Here are some of the most common uses of linked lists:
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
1. Implementing stacks and queues:
Linked lists are used to implement stacks and queues because they
support efficient insertion and deletion at one end of the list.
2. Dynamic memory allocation: Linked lists are used to allocate and deallocate memory
dynamically at run-time. For example, in C programming language, the malloc and free
functions are used to allocate and deallocate memory for linked lists.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 30
3. Implementing hash tables: Linked lists are used to resolve collisions in hash tables. In a
hash table, if two keys hash to the same index, they are stored in a linked list at that
index.
4. Representing sparse matrices: A sparse matrix is a matrix that contains mostly zeros.
Linked lists are used to represent sparse matrices because they can efficiently store only
the non-zero elements.
5. Music and video playlists: Linked lists can be used to implement music and video
playlists. Each node in the linked list represents a song or a video, and the links represent
the order in which they are played.
6. Navigation systems: Linked lists are used in navigation systems to represent the sequence
of directions to reach a destination. Each node in the linked list represents a direction, and
the links represent the order in which they are followed.
7. Graphs: Linked lists are used to represent graphs, where each node represents a vertex,
and the links represent the edges connecting the vertices.
Overall, linked lists are a versatile data structure that can be used in many different applications,
making them an essential tool for software developers and computer scientists.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
2.1.1.3 Types of Linked list
There are several types of linked lists, including:
1. Singly linked list: In a singly linked list, each node has only one link pointing to the next
node in the list.
2. Doubly linked list: In a doubly linked list, each node has two links: one pointing to the
next node and another pointing to the previous node in the list. This allows for efficient
traversal in both directions.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 31
3. Circular linked list: In a circular linked list, the last node points to the first node in the list,
creating a circular structure. This allows for efficient traversal from the last node back to
the first node.
4. Singly linked list with a tail pointer: In this type of linked list, there is an additional pointer
to the last node in the list, which allows for efficient insertion at the end of the list. A
doubly linked list with a tail pointer combines two linked lists: a single linked list with a
tail pointer and a doubly linked list. With a tail pointer, it combines the advantages of a
doubly linked list and a single linked list.
2.1.1.4 Performing various operations on linked list
Here are some common operations that can be performed on a linked list:
1. Traversing the linked list: This involves visiting each node in the list sequentially, starting
from the head node and following the links until the end of the list is reached.
2. Inserting a node: This involves creating a new node and inserting it into the list at a
specific position. The node can be inserted at the beginning of the list (as the new head
node), at the end of the list, or in the middle of the list (before or after a specific node).
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
3. Deleting a node: This involves
removing a specific node from the list. The node can be deleted
from the beginning of the list (as the head node), from the end of the list, or from the
middle of the list (after locating the node).
4. Searching for a node: This involves locating a specific node in the list based on a given
value or key. The search can start from the head node and continue until the end of the list
is reached or the node is found.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 32
5. Reversing the linked list: This involves reversing the order of the nodes in the list, so that
the last node becomes the head node and vice versa.
6. Concatenating two linked lists: This involves joining two linked lists together, so that the
last node of the first list points to the head node of the second list.
7. Sorting the linked list: This involves arranging the nodes in the list in a specific order,
such as ascending or descending order based on the node values.
8. Splitting the linked list: This involves dividing a linked list into two separate lists based
on a specific condition or position. For example, a list can be split into two lists with odd
and even values.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 33
2.1.2 LIFO principle of Stack
Figure 1: LIFO
The LIFO principle, or "Last In, First Out," is the fundamental concept behind a stack data
structure. A stack is a linear data structure that allows elements to be added and removed from
one end only, which is called the top of the stack.
In a stack, elements are added to the top of the stack, and the most recently added element is
always at the top of the stack. Similarly, elements are removed from the top of the stack, so the
element that was most recently added is the first one to be removed.
The LIFO principle can be thought of as a stack of plates in a cafeteria. When plates are added to
the stack, they are placed on top of the other plates. When a customer wants a plate, they take the
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 34
top plate off the stack, which is the last plate that was added. As plates are used, they are
removed from the top of the stack in the reverse order that they were added.
In a computer program, stacks are often used to keep track of function calls, where each function
call creates a new stack frame that is added to the top of the call stack. When the function returns,
its stack frame is removed from the top of the call stack, allowing the program to continue
executing from the previous point in the program.
Here's an example to illustrate the LIFO principle of a stack:
Suppose you are at a cafeteria, and you need to stack a set of plates. The LIFO principle would
mean that you would place the most recently used plate at the top of the stack, and when a plate
is needed, it would be taken from the top of the stack, which is the last plate that was placed.
For example, imagine you have the following sequence of plate stacking and plate usage:
1. You place a blue plate on the table.
2. You place a red plate on top of the blue plate.
3. You place a green plate on top of the red plate.
4. You take a plate from the top of the stack, which is the green plate.
5. You place a yellow plate on top of the stack.
6. You take a plate from the top of the stack, which is the yellow plate.
7. You take a plate from the top of the stack, which is the red plate.
In this example, the LIFO principle ensures that the most recently used plate is always at the top
of the stack. When a plate is needed, it is taken from the top of the stack, which is the last plate
that was placed. This is like how a stack data structure works in computer programming, where
elements are added to the top of the stack and removed from the top of the stack in reverse order
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 35
2.1.2.1 Basic operation of stack
The basic operations of a stack are as follows:
1. Push: This operation adds an element to the top of the stack. When an element is pushed
onto the stack, it becomes the new top element.
2. Pop: This operation removes the top element from the stack. When an element is popped
from the stack, the element just below it becomes the new top element.
3. Peek/Top: This operation returns the top element of the stack without removing it. It
simply returns the value of the element at the top of the stack.
4. Is Empty: This operation checks whether the stack is empty or not. It returns a Boolean
value (true or false) based on whether the stack is empty or not.
These four basic operations are sufficient to implement any other operations or algorithms that
may be required using a stack data structure. Here's an example implementation of a stack data
structure using these basic operations in Java:
import java.util.*; public class
StackExample { private
ArrayList<Integer> stack; public
StackExample() { stack = new
ArrayList<>();
}
public void push(int value)
{ stack.add(value);
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 36
}
public int pop() {
if (!isEmpty()) {
int topIndex = stack.size() - 1;
int topValue = stack.get(topIndex);
stack.remove(topIndex); return
topValue;
}
return -1; // Or throw an exception
}
public int peek() {
if (!isEmpty()) {
int topIndex = stack.size() - 1;
return stack.get(topIndex);
}
return -1; // Or throw an exception
}
public boolean isEmpty()
{ return stack.isEmpty();
}
}
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 37
In this implementation, we have defined the basic operations of push, pop, peek/top, and isEmpty
for a stack data structure using an ArrayList. The push operation adds an element to the end of
the list, while the pop operation removes and returns the last element of the list if the list is not
empty.
The peek operation returns the last element of the list without removing it if the list is not empty.
Finally, the isEmpty operation returns a boolean value based on whether the list is empty or not.
Position of top Status of stack
-1 Stack is Empty
0 Only one element in Stack
N-1 Stack is Full
N Overflow state of Stack
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 38
2.1.2.2 Flowchart for implementing stack using array.
Flowchart for Push () Operation
Figure 2: Flowchart for Push () Operation
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 39
Flowchart for Pop () Operation
Figure 3: Flowchart for Pop () Operations
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 40
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
Flowchart for Peek () Operation
Figure 4: Flowchart for Peek () Operations
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 41
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
2.1.2.3 Representation of stack
A stack may be represented in the memory in various ways. There are two main ways: using a
onedimensional array and a single linked list. Array Representation of Stacks: First we have to
allocate a memory block of sufficient size to accommodate the full capacity of the stack. Then,
starting from the first location of the memory block, the items of the stack can be stored in a
sequential fashion. In Figure, Itemi denotes the ith item in the stack; l and u denote the index
range of the array in use; usually the values of these indices are 1 and SIZE respectively. TOP is
a pointer to point the position of the array up to which it is filled with the items of the stack. With
this representation, the following two ways can be stated:
EMPTY: TOP < l FULL: TOP ≥ u
Figure 5: Stack Representation
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 42
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
Linked List Representation of Stacks:
Although array representation of stacks is very easy and convenient, it
allows the representation of only fixed sized stacks. In several applications, the size of the stack
may vary during program execution. An obvious solution to this problem is to represent a stack
using a linked list. A single linked list structure is sufficient to represent any stack. Here, the
DATA field is for the ITEM, and the LINK field is, as usual, to point to the next' item. Above
Figure b depicts such a stack using a single linked list. In the linked list representation, the first
node on the list is the current item that is the item at the top of the stack and the last node is the
node containing the bottom-most item. Thus, a PUSH operation will add a new node in the front
and a POP operation will remove a node from the front of the list.
2.1.3 Stack memory implementation for PCs.
Each running PC software makes use of a section of memory known as the stack to enable
certain functions to function properly. The stack is used by the machine to carry work
contentions, store return data, reserve registers for later reclamation, and for close-by variables. A
stack outline is the area of the stack reserved for a single capacity call. As a result, a new space
(i.e., stack outline) is created on the stack for each capacity call.
The stack of the computer resides in memory's very top regions. Stack is a stack information
structure, as suggested by its name, with the "top" of the stack moving from high value locations
towards poor quality addresses. We employ pop D to remove the top value from the stack and
place it into a destination, and we employ push S to push the source into the stack (for example a
register or memory area). As a pointer to the top of the stack, which is also the top of the topmost
stack outline, we use the stack register, %esp.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 43
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
Stack memory is a special type of memory
that is used for temporary data storing when we need to read data exactly
the opposite way from how it was written in, without thinking about getting sorted out
information tending.
Stack memory is a sequential memory with clear access restrictions that only allow writing to
and reading from one location in the memory, known as the top of the stack. A shift of all data
stored in subsequent regions by one scenario down inside and out of this line is made
concurrently by the stack memory, which serves as a line to which information can be assembled
at the top of the stack.
Only looking at the top of the stack, the readout from the stack is plausible.
The readout causes data from the top of the stack to be removed, and new data from the depth of
the stack is created in its place, shifting all previously stored data one position upward. The line
then switches to a Last-In-First-Out format.
The stack memory operates similarly to a rifle's magazine in that presenting a new cartridge
causes the magazine's normally-remaining cartridges to move to the inside and outside, and
firing a cartridge (a shot) causes the top cartridge to be removed and replaced by the first
cartridge that was previously stored beneath the used one.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 44
Figure 6: Stack functioning Principle
In the memory of a computer, information is kept in linear information structures called memory
stacks. They could also be referred to as lines. A stack of information should regularly contain
similar types of information. Every function on your computer, including the main() function,
creates temporary variables that are stored in a unique region of memory. The stack is a "LIFO"
(last in, first out) data structure that the CPU carefully monitors and advances. Another variable
is "pushed" into the stack every time a capacity declares another one. Then, at that point, every
variable that was added to the stack by a capacity is released whenever that capacity exists (in
other words, they are erased).
This region of memory becomes available for other stack variables after a stack variable is
released. Using the stack to hold variables has the advantage of managing memory for you.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 45
Memory doesn't need to be allocated manually or released if you no longer require it. Also,
reading from and writing to stack variables happen very quickly because of how efficiently the
CPU organizes stack memory. The idea that when a capacity exists, each of its variables is
popped off of the stack (and subsequently lost till the end of time) is essential to comprehending
the stack. Stack variables are consequently close in nature. This is related to a previous concept
we discussed, factor extension, or local vs global variables. Trying to access a variable that was
created on the stack inside of a capacity from a location in your program outside of that capacity
(for example, after that capacity has left) is a common error in C programming. Another aspect of
the stack to keep in mind is that the maximum size of variables that can be stored on it has a
cutoff (which varies with OS). Variables allotted on the heap are an exception to this rule.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 46
3. Illustrate, with an example, a concrete data structure for a First in
First out (FIFO) queue.
3.1 Queue Data Structure
A queue is a linear data structure that follows the First in First out (FIFO) principle. It is an
ordered collection of elements in which an element is added to the end of the queue and removed
from the front of the queue.
The two basic operations of a queue are:
1. Enqueue - adding an element to the end of the queue.
2. Dequeue - removing the element from the front of the queue.
Queues are used in a variety of applications such as scheduling, resource allocation, and
breadthfirst search algorithms.
Some of the key properties of a queue are:
• FIFO: The first element added to the queue is the first one to be removed.
• Linear: The elements are stored in a linear sequence.
• Dynamic size: The size of the queue can be changed dynamically as elements are added
or removed.
• Limited access: The only way to access elements in the middle of the queue is to dequeue
elements until the desired element is reached.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 47
Queues can be implemented using different data structures such as arrays, linked lists, or circular
buffers. The choice of data structure depends on the specific use case and performance
requirements.
Common operations on a queue include enqueue, dequeue, peek (viewing the element at the front
of the queue without removing it), checking if the queue is empty or full, and getting the size of
the queue.
Here's an example implementation of a First in First out (FIFO) queue in Java using an array-
based circular buffer:
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 48
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 49
In this implementation, we define a Queue class with four methods:
• isEmpty(): Returns true if the queue is empty, false otherwise.
• isFull(): Returns true if the queue is full, false otherwise.
• enqueue(int value): Adds an element to the end of the queue by incrementing rear and
adding the new element to the buffer array.
• dequeue(): Removes and returns the element at the front of the queue by incrementing
front and returning the value at the corresponding index of the buffer array.
• peek(): Returns the element at the front of the queue without removing it.
• size(): Returns the current size of the queue.
The circular buffer allows for efficient use of memory and avoids the need to shift elements in
the array when the front pointer changes.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 50
Here's an example of how to use this implementation:
In this example, I create a new Queue object with a maximum capacity of 3, add three elements
to the queue using enqueue, remove the first element using dequeue, and then peek at the front
element and get the current size of the queue using peek and size, respectively
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 51
4. Illustrate, with an example, a concrete data structure for a First in
First out (FIFO) queue.
4.1 Software Stack
A software stack refers to a set of software components and technologies that are used to create
and operate a software application or system. A typical software stack includes several layers of
software that work together to provide a complete solution.
For example, a web application software stack could include the following layers:
1. Operating system: The lowest layer of the stack that provides the foundation for running
the application. Examples of popular operating systems include Linux, Windows, and
macOS.
2. Server software: This layer includes software such as web servers, application servers,
and database servers. Examples of server software include Apache, Nginx, Tomcat, and
MySQL.
3. Frameworks and libraries: These are software components that provide pre-built
functionality to the application. Examples of frameworks include React, Angular, and
Django, while popular libraries include jQuery, React Native, and NumPy.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 52
4. Application code: This is the custom code that is written to provide
the specific functionality of
the application. It is typically written in programming languages such as Python, Java, or
JavaScript.
5. User interface: This layer includes the graphical user interface
(GUI) of the application, which allows users to interact with the
application.
Overall, a software stack represents the complete set of technologies and software components
required to build, run, and manage a software application. It usually consists of several layers of
software, each of which provides a different level of functionality and interacts with the layers
above and below it
4.2 Abstract Data Type (ADT)
An abstract data type (ADT) is a high-level data type that is defined by its behavior and
operations, independent of its implementation details. It is an abstraction of a data structure that
describes what operations can be performed on it and what their behavior and properties are,
without specifying how those operations are implemented.
The definition of an ADT includes the set of operations that can be performed on it, their input
and output parameters, and any preconditions or postconditions that apply to those operations.
The behavior and properties of an ADT are defined by the behavior of its operations and any
constraints or invariants that apply to its data.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
ADTs are useful because they provide a level
of abstraction that enables software designers and developers to think
about data structures and algorithms at a higher level, without being concerned
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 53
with their low-level details. This allows for modular, reusable, and extensible software design, as
ADTs can be used as building blocks to construct more complex data structures and algorithms.
Stacks are a useful abstract data type with a variety of applications in computer science and
programming. Here are some common employment of ADT Stack:
1. Function call stack: One of the most common employment of the stack is in the
implementation of function calls in a program. Each function call is pushed onto the
stack, and when the function completes, it is popped from the stack, allowing the program
to return to the previous point of execution.
2. Expression evaluation: Stacks can be used in expression evaluation, where operators and
operands are pushed onto the stack and then popped off in the correct order to evaluate
the expression.
3. Undo/redo functionality: Stacks can be used to implement undo/redo functionality in a
text editor or other applications. Each operation performed by the user is pushed onto the
stack, and the most recent operation can be undone by popping it from the stack.
4. Backtracking: Stacks can be used in backtracking algorithms, where a sequence of
choices are made and then potentially reversed if the choices lead to a dead end.
5. Parsing: Stacks can be used in parsing, where tokens are pushed onto the stack and then
popped off as the parser processes them.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
6. Memory allocation: Stacks can be
used in memory allocation, where memory is allocated in a stack-
like fashion and then deallocated in the reverse order.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 54
Overall, stacks are a versatile and powerful tool with many practical applications in computer
science and programming.
4.2.1 Common Examples of ADTs
4.2.1.1 List ADT
List ADT (Abstract Data Type) is a data structure that allows storage and manipulation of a
collection of elements. It provides a set of operations that can be used to insert, delete, and
retrieve elements from the list. The list ADT does not specify how the elements are stored in
memory or how the operations are implemented; it only defines the interface for accessing and
manipulating the elements.
The basic operations of the list ADT include:
1. Insertion: This operation adds an element to the list at a specified position.
2. Deletion: This operation removes an element from the list at a specified position.
3. Retrieval: This operation retrieves an element from the list at a specified position.
4. Traversal: This operation allows the user to traverse the list from the beginning to the
end, accessing each element in turn.
5. Size: This operation returns the number of elements in the list.
6. Search: This operation searches for a specific element in the list.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 55
The list ADT can be implemented using different data structures such as arrays, linked lists, and
dynamic arrays. The choice of data structure depends on the specific requirements of the
application. The list ADT is widely used in many applications such as databases, file systems,
and programming languages, making it a fundamental concept in computer science.
Here are some common operations that are typically supported by the List ADT:
1. Append: Adds an element to the end of the list.
2. Prepend: Adds an element to the beginning of the list.
3. Insert: Adds an element at a specified position within the list.
4. Remove: Removes an element from the list at a specified position.
5. Get: Returns the element at a specified position within the list.
6. Set: Changes the value of the element at a specified position within the list.
7. Length: Returns the number of elements in the list.
8. Find: Searches for an element within the list and returns its position.
9. Concatenate: Combines two lists into a single list.
10. Slice: Extracts a subset of elements from the list, based on a specified range of indices.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
Lists are used extensively in programming
and computer science, and they serve as a fundamental building block for
many other data structures, such as stacks, queues, and trees. They are implemented using arrays
or linked lists, and the choice of implementation depends on the requirements of the application
and the performance characteristics of the data structure.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 56
4.2.1.2 Stack ADT
The Stack abstract data type (ADT) is a collection of elements that follows the Last-In-First-Out
(LIFO) principle. It supports two main operations: push, which adds an element to the top of the
stack, and pop, which removes the most recently added element from the top of the stack. In
addition, the stack ADT typically includes a third operation, peek, which returns the element at
the top of the stack without removing it.
The basic operations of the stack ADT include:
1. Push: Adds an element to the top of the stack.
2. Pop: Removes the most recently added element from the top of the stack.
3. Peek: Returns the element at the top of the stack without removing it.
4. IsEmpty: Determines whether the stack is empty.
5. Size: Returns the number of elements in the stack.
Stacks are used extensively in programming and computer science, and they serve as a
fundamental building block for many other data structures, such as queues, trees, and graphs.
They are implemented using arrays or linked lists, and the choice of implementation depends on
the requirements of the application and the performance characteristics of the data structure.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
Stack ADT is useful in a wide variety of
applications, including function call management, expression evaluation,
backtracking, parsing, undo/redo functionality, and memory allocation.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 57
4.2.1.3 Queue ADT
The First-In-First-Out (FIFO) concept is applied to the elements in the Queue abstract data type
(ADT). Enqueue, which adds an element to the back of the queue, and dequeue, which removes
the element at the front of the queue, are the two primary actions that it supports. A third action,
known as peek, is frequently included in the queue ADT as well. It returns the element at the
front of the queue without removing it.
Here are some common operations that are typically supported by the Queue ADT:
1. Enqueue: Adds an element to the back of the queue.
2. Dequeue: Removes the element at the front of the queue.
3. Peek: Returns the element at the front of the queue without removing it.
4. IsEmpty: Determines whether the queue is empty.
5. Size: Returns the number of elements in the queue.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
In programming and computer science,
queues are widely used and act as a basic building block for a variety of
other data structures, including stacks, trees, and graphs. Depending on the needs of the program
and the performance characteristics of the data structure, they are implemented using arrays or
linked lists.
The queue ADT is useful in a wide variety of applications, including task scheduling, message
passing, network packet routing, and event handling.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 58
4.2.2 Stack, Queue and List Abstract Data Type Comparison
Three of the most popular abstract data types (ADTs) in computing and computer science are
stacks, queues, and lists. While there are some parallels between them, there are also some
significant differences.
1. Structure: Stacks and queues are both linear data structures, meaning that their elements
are arranged in a linear sequence. Lists can also be linear, but they can also be
implemented as linked lists, which are more flexible in terms of their structure.
2. Principle of operation: Stacks follow the Last-In-First-Out (LIFO) principle, meaning that
the most recently added element is the first one to be removed. Queues follow the FirstIn-
First-Out (FIFO) principle, meaning that the first element added is the first one to be
removed. Lists do not have a fixed principle of operation.
3. Main operations: The main operations supported by stacks are push, pop, and peek. The
main operations supported by queues are enqueue, dequeue, and peek. The main
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
operations supported by lists are
append, prepend, insert, remove, get, set, and slice.
4. Use cases: Stacks are often used in applications that require backtracking, expression
evaluation, undo/redo functionality, or function call management. Queues are often used
in applications that require task scheduling, message passing, or network packet routing.
Lists are often used in applications that require the storage and manipulation of ordered
collections of elements.
Stacks, queues, and lists are intended to serve different purposes and have different qualities that
make them more suitable for certain types of applications, even though they have some
similarities.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 59
4.3 Selecting the suitable ADT for the scenario and implementing it
If stack data structures use the phrase "first in, last out," we can use them in our application.
Therefore, if we are entering the car's details from oldest to newest and need the results in
reverse chronological sequence, we can use stack data structure as our ADT. Consequently, we
can use a linked list in this instance for the Java version. Because the count that the corporation
gets cannot be measured and must be arranged dynamically, the answer should be implemented
as a linked list.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 60
5. Implement a complex ADT and algorithm in an executable
programming language to solve a well-defined problem.
5.1 Describe the scenario and design the system
In the aforementioned situation, we need an object array to store the relevant data about each car,
then an object. When registering a car, we can quickly retrieve the array index and fill in the
required data inside the object. I decide to use an object array because it is effective and simple to
apply the program. We can quickly delete an automobile by assigning null to the array index,
which will cause the object to be deleted automatically. We can sort the array by rank after
entering the data to get rid of the last car from the list. The first record entered will be the first
record exited in a queue data structure. If we arrange the array in that manner, the winners can be
readily distinguished from all other competitors. A queue can be used in the aforementioned
scenario to input race results, eliminate the final competitor based on those results, and choose
the winners.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 61
5.2 Implementation the system
In accordance with the task description, I first established a class, then I created the main class,
and I carried out the corresponding tasks.
Figure 7: Car class
The process of importing libraries, making the Car class, and adding class properties like number,
brand, sponsor, and driver is illustrated by this snippet of code. And using this class, I created
objects to hold the data about the cars. When objects are made, initializing the properties of cars
is easier. This is the primary class, and it is in this class that I have all of the program's features.
Here, I made a collection of Car objects with the name "c" and a size of 6. Because there are only
six cars entered in the competition consequently, there can be a limit of 6 cars.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 62
Figure 8: Main Class
I created a scanner object to enter all user inputs with the name "input." I also initialized the
numbers select, I, and r at this location. I counts the number of registered cars, R counts the
number of rounds in the competition out of three, and "select" refers to the menu.
Figure 9: Function
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 63
This code snippet displays the program's menu as well as the switch statement that selects
choices on a case-by-case basis. I'll talk about the code snippets I used to apply the
functionalities in the following paragraphs.
Figure 10: Case 1
This code snippet shows the way I register a car using the car object array. So, I will be
representing the count of the cars that registered. So, with that we can see if the car count
increases by 6. It will display an error, saying, “You can only register 6 cars for the race!”
I used the functionalities here itself is there is no repetition of the functionality.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 64
Figure 11: Case 2
This instance is where I got the delete car functionality. The vehicle number is being entered in
this box. That is followed by the reviewing phase. It will be removed from the array if any of the
registry numbers match the car number that we put there. As a result, the object array's index will
be changed to NULL. The quantity of cars will drop by one, as indicated by "i—." The next
action should be to fill the array starting at the deleted position if it is in the array's middle.
Therefore, I created a for loop to populate the null index in the array while preserving the
hierarchy of the registry's other information. And if there is no such a car like that I entered to the
search tool, it will output the result, as “No car found to delete!”
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 65
Figure 12: Case 3
In this case, I developed the functionality for the round outcomes, and following one round, it
will be sorted by the car's rating. Additionally, it will reduce the range of the ongoing for loop by
1. After a round has concluded, the final car is unable to fight against the other vehicles. I applied
the solution for the race's rounds with rankings in this specific case in the same manner.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 66
Figure 13: Case 4
In this case, this shows the winners of the race. It is going to happen, only if they complete all 3
rounds. If we were not completed all 3 rounds and asks for the winners, it will show the current
ranking after with the round rounds.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 67
Figure 14: Case 5
Therefore, this snippet of code illustrates the "search car" feature. So, in this case, we input the
car's number and use a for loop to find the car. And in the for loop, if any object numbers match
the number that we entered, all information about the car that number possesses will be
displayed. And if there isn't a car matching that description, it will say "No car found." And if
there isn't a vehicle listed, it will say so in the prints.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 68
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
5.2.1 Full functionable code which I used in
my application
import java.util.Scanner;
import java.util.*; class
Car { int number;
String brand;
String sponsor;
String driver;
} public class main { public static void
main(String[] args) { Car c[]=new Car[6]; int
choose=0,i=0,r=0;
System.out.println("\t***ABC PVT LTD. car race***\t");
Scanner input = new Scanner(System.in); while(choose!
=7) {
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 69
System.out.println("1. Register a car ");
System.out.println("2. Delete a car ");
System.out.println("3. Insert 3 rounds details ");
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
System.out.println("4.
Find out winners ");
System.out.println("5. Search a car ");
System.out.println("6.Display registered
cars"); System.out.println("7. Exit ");
choose=input.nextInt(); switch(choose) { case 1:
if(i<6) { c[i]=new
Car();
System.out.print("enter car number: ");
c[i].number=input.nextInt();
input.nextLine();
System.out.print("enter car brand: ");
c[i].brand=input.nextLine();
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 70
System.out.print("enter car sponsor:
"); c[i].sponsor=input.nextLine();
System.out.print("enter car driver: ");
c[i].driver=input.nextLine(); i++;
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
} else {
System.out.println("you only can register 6 cars
for the race!");
break; case 2:
System.out.println("enter the car number to delete:
"); int carNum=input.nextInt(); for(int m=0; m<i; m+
+) { if(carNum==c[m].number) {
System.out.println("Car deleted!"); c[m]=null;
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 71
i--;
for(int k=m; k<i; k++) { if(k!
=6) { c[k]=c[k+1];
} else if(m+1==i) {
System.out.println("No car found to delete!");
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
break;
case 3:
System.out.println("enter round"+(++r)+" results:
"); Car temp=new Car(); int num,a=0; for(int k=0;
k<6-(r-1); k++) {
System.out.print("place "+(k+1)+": ");
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 72
num=input.nextInt(); for(int
m=0; m<i; m++)
{ if(num==c[m].number)
{ temp=c[m]; c[m]=c[a]; c[a+
+]=temp;
break;
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
case 4:
if(r==3) {
System.out.println("1st place: "+c[0].number+"
"+c[0].driver);
System.out.println("2nd place: "+c[1].number+"
"+c[1].driver);
System.out.println("3rd place: "+c[2].number+"
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 73
"+c[2].driver);
} else {
System.out.println("Race is still going on, current results are: ");
System.out.println("End of round"+r+": "); for(int k=0; k<6; k+
+){
System.out.println((k+1)+" place:"+c[k].number);
break;
case 5:
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
System.out.print("Enter the car number:
"); int n=input.nextInt(); for(int k=0; k<i;
k++) { if(n==c[k].number) {
System.out.println("Brand: "+c[k].brand);
System.out.println("Sponsor: "+c[k].sponsor);
System.out.println("Driver: "+c[k].driver);
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 74
} else if(k+1==i) {
System.out.println("No car found!");
} else if(k==0) {
System.out.println("No car in registry!");
break; case 6:
System.out.println("---------------Car registry----------------"); for(int
m=0; m<i; m++) {
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
System.out.println(c[m].number+"\
t"+c[m].brand+"\t"+c[m].spons or+"\t"+c[m].driver);
break; case 7:
System.out.println("Exit!");
break;
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 75
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 76
5.3 Implementation of the fully commented code
import java.util.Scanner; import java.util.*; import static
java.lang.System.exit;// import package class
CarRegistryStack {// Create Stack Using Linked list
private class Node {// A linked list node int carNum;
String brand;
String sponsor;
String driver;
Node next; // reference variable Node type
Node top;
CarRegistryStack(){// Constructor this.top
= null;
} public void push(int x, String br, String sp, String dr) // enter in the
beginning.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 77
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
Node tmp = new Node();// create new node tmp and allocate memory if
(tmp == null) {
System.out.print("\nHeap Overflow");// check whether stack (heap) is full or not.
return;
} tmp.carNum = x; // initialize carNum into tmp carNum
field tmp.brand = br; // initialize brand tmp.sponsor = sp; //
initialize sponsor tmp.driver = dr; // initialize driver
tmp.next = top; // put top reference into tmp next top = tmp;
// update top reference
} public boolean isEmpty(){// Utility function to check if the stack is empty or
not return top == null;
} public String peek(){ // Utility function to return top element in a
stack
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 78
if (!isEmpty()) { // check for empty stack return top.carNum+"
"+top.brand+" "+top.sponsor+" "+top.driver;
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
else
System.out.println("Stack is empty"); return
null;
} } public void pop() // remove at
the beginning
// check whether stack is underflow or not.
if (top == null) {
System.out.print("\nStack
Underflow"); return; } top = (top).next;
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 79
public void display()
// check whether stack is underflow or not.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
if (top == null) {
System.out.printf("\nStack Underflow"); exit(1);
else
Node tmp = top; while
(tmp != null) {
System.out.printf("%d->", tmp.carNum);// print node carNum tmp
= tmp.next;// assign tmp next to tmp
} } public
class atd {
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 80
public static void main(String[] args){
CarRegistryStack obj = new CarRegistryStack();// create Object of
Implementing class
int choose=0;
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
System.out.println("\t***ABC
PVT LTD. car race***\t"); Scanner input = new
Scanner(System.in); while(choose!=3){
System.out.println("1. Register a car ");
System.out.println("2. get car details
"); choose=input.nextInt();
switch(choose){ case 1:
System.out.print("enter car num: ");
int n=input.nextInt();
input.nextLine();
System.out.print("enter car brand: ");
String brand=input.nextLine();
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 81
System.out.print("enter car sponsor: ");
String sponsor=input.nextLine();
System.out.print("enter car driver:
"); String driver=input.nextLine();
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
obj.push(n,brand,sponsor,driver); break;
case 2:
System.out.println(obj.peek())
; obj.pop(); break; case 3:
System.out.println("Exit!");
break;
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 82
5.4 Output of the codes
Figure 15: Function list
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
The Function wants to be performed by the
ABC Company.
Figure 16: Case 1 Output
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 83
Register Car details.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
Figure 17: Case 1 Output 2
As per Scenario only 6 people can register to the Race if more then 6 people are join to the even
can get this message.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 84
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
Figure 18: Delete a car Case 2
Above Image we can see Car details after deleted and before delete by entering car number can
delete particular car.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 85
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
Figure 19: Case 3
Above image is the way of inserting places of every end of each round this is help to know
finally who the winner is
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 86
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
Figure 20: Case 4
As I said earlier by inserting places to end of each round finally can identify who is the winner
and that is shown on above picture.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 87
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
Figure 21: Case 5
Search car by car‟s Number this is very helpful for identify the details of car brand,sponsor and
Driver‟s Name.
Figure 22: Case 6
In the above picture can find the details of all registered car.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 88
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
5.5 Complexity of Stack ADT
The complexity of the Stack ADT (Abstract Data Type) operations depends on the
implementation of the stack.
1. Array-based implementation:
• Push: O(1) amortized time complexity, O(n) worst-case time complexity when the array
needs to be resized.
• Pop: O(1) time complexity.
• Peek: O(1) time complexity.
• Search: O(n) time complexity.
2. Linked list-based implementation:
• Push: O(1) time complexity.
• Pop: O(1) time complexity.
• Peek: O(1) time complexity.
• Search: O(n) time complexity.
3. Dynamic Array-based implementation (such as std::vector in C++):
• Push: O(1) amortized time complexity, O(n) worst-case time complexity when the
dynamic array needs to be resized.
• Pop: O(1) time complexity.
• Peek: O(1) time complexity.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 89
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
Search: O(n) time complexity.
In general, the stack operations have a time complexity of O(1) for push, pop, and peek.
However, the search operation has a time complexity of O(n) for all implementations.
5.6 Encapsulation
In object-oriented programming (OOP), the term "encapsulation" refers to the grouping of data
and the methods that act on it into a single entity, such as a class. Encapsulation is a technique
used to provide a clearly specified interface for interacting with an object while keeping the
implementation details of the object hidden from the outside world.
Encapsulation is the process of containing data and behavior within a singular entity and
allowing controlled access to that entity, to put it another way. By forbidding direct access to an
object's data and methods and requiring access through clearly defined interfaces, it allows the
developer to create reliable and secure software systems.
This approach ensures that the implementation details of an object are not exposed to the outside
world and that the object is responsible for maintaining its own integrity.
Encapsulation helps in achieving data hiding, which means that the internal representation of an
object is hidden from the outside world. This allows the developer to modify the internal
implementation of an object without affecting the code that uses it. Encapsulation also facilitates
code reuse and modularity by providing a clear separation between the interface and the
implementation of an object.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 90
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
Encapsulation provides several benefits,
including:
• Improved maintainability: Changes to the internal implementation of an object do not
affect the external code that uses the object.
• Improved security: Encapsulated data cannot be modified or accessed directly from
outside the class.
• Improved usability: Encapsulation allows developers to define a clear and concise
interface to an object, making it easier to use and understand.
Overall, encapsulation is a crucial concept in object-oriented programming and plays a
significant role in designing software systems that are modular, reusable, and maintainable.
Below I have mentioned example for encapsulation using java language.
Figure 23: Encapsulation example
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 91
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
In this case, the account number and balance
information are confidential and enclosed within the BankAccount class.
This indicates that the only place from which to obtain these variables is the BankAccount class.
By returning the contents of the secret variables, the getAccountNumber() and getBalance()
methods allow for controlled access to the data that is encapsulated. Other classes may use these
methods to get the account number and amount.
There are two ways to change the account balance: transfer() and withdraw(). These methods are
used to guarantee that the balance is updated in a controlled and consistent way and can only be
called from within the BankAccount class.
By encapsulating the data and methods within the BankAccount class, the developer can ensure
that the account information is accessed and modified in a controlled and secure way, reducing
the risk of errors and vulnerabilities in the software system
5.6.1 Advantages of using Encapsulation
There are several advantages to using encapsulation in programming:
1. Security: By concealing an object's internal implementation details, encapsulation aids in
keeping the security and integrity of data. This minimizes the danger of unauthorized
access by ensuring that the data can only be accessed using the methods offered by the
object.
2. Modularity: By clearly separating an object's interface and execution, encapsulation
encourages modularity. This makes it simpler to update and expand the code without
having an adverse effect on other system components.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 92
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
3. Code Reusability: By producing self-
contained objects that can be used in various system components
without change, encapsulation facilitates code reuse. As a result, less code needs to be
created, tested, and managed.
4. Maintenance: Encapsulation reduces the scope of changes to an object's internal
implementation, which makes the code simpler to manage and debug. This lowers the
possibility of causing unintended adverse effects or damaging other system components.
5. Abstraction: Through the provision of a clearly specified interface for interacting with an
object, encapsulation makes abstraction easier. Because of this notion, it is simpler to
comprehend an object's behavior without having to comprehend how it is implemented
internally.
Overall, encapsulation is a powerful technique that promotes security, modularity, code
reusability, maintainability, and abstraction in programming. By encapsulating data and methods
within objects, developers can create more robust and secure software systems that are easier to
modify, maintain and extend.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 93
6. Implement Error Handling and Report Test Results.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
6.1 Error Handling
Figure 24: Error Handling
The procedure used to deal with the possibility for disappointment is called error handling. For
instance, it would be risky to use a paper even after realizing it was terrible and choosing to
disregard it. Recognizing and fixing those issues right away shields the remainder of the software
from additional pitfalls.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 94
The accompanying subchapters illustrate various approaches to error handling in Rust. They all
have a variety of use cases and rather unpretentious contrasts. As a general guideline:
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
The most effective use of unambiguous panic
is in handling testing and unrecoverable errors. It may be helpful for
prototyping, for example, when dealing with yet-to-be-performed tasks, but in those
circumstances, the more illustrative the unimplemented, the better. It makes sense to panic during
testing as a surefire method to fail.
The Option type should be used when a value is optional or when the absence of a value is not an
error circumstance. For example, neither C: nor -/ have a parent directory. Unwrap works well
when managing Options for experimentation and situations where there is unquestionably going
to be a benefit. The ability to define an error message with expect, should something go wrong,
makes it more useful.
There are several techniques for error handling, including:
1. Exception handling: This technique involves detecting errors and throwing exceptions to
handle them. It allows developers to control the flow of the program and handle errors
gracefully without crashing the application.
2. Logging: Logging is the process of recording events, errors, and other information that
occurs during the execution of an application. It helps developers identify errors and
troubleshoot issues that occur during runtime.
3. Defensive programming: Defensive programming is a technique that involves writing
code that anticipates potential errors and handles them proactively. It includes techniques
such as input validation, boundary checking, and data sanitization.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 95
4. Graceful degradation: graceful degradation is a technique used in web development that
allows a website or application to continue functioning even when some features or
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
components are not working correctly.
This technique ensures that users can still use the application even
if some features are unavailable.
Overall, error handling is an essential part of software development, and developers should
implement robust error handling techniques to ensure that their applications are reliable and
resilient.
6.1.1 Option and Unwrap
In the prior model, we demonstrated how simple it is for us to start a disappointing program. If
we consume sugary lemonade, we instructed our program to panic. But contemplate the
possibility that we might ask for a drink but not get one. It's important to handle that
circumstance because the consequences would be terrible.
Similarly to a lemonade, we could compare this to the invalid text. (""). We would prefer to have
the compiler flag cases when there isn't a drink because we are using Rust.
When nonattendance is reasonable, the sexually transmitted disease library's Option<T> Enum is
used. It manifests as one of two possible "options":
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 96
These situations can be dealt with either categorically using coordinate or tangibly using unwind.
Either the internal part will be returned or there will be a panic.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
Keep in mind that it is possible to physically
alter fear with anticipation, but doing so results in a less important outcome
than express handling. In the accompanying model, unambiguous management produces a more
controlled outcome while retaining the ability to panic at any time.
// The adult has seen it all, and can handle any drink well.
// All drinks are handled explicitly using `match`.
fn give_adult(drink: Option<&str>) {
// Specify a course of action for each case. match
drink {
Some("lemonade") => println!("Yuck! Too sugary."),
Some(inner) => println!("{}? How nice.", inner),
None => println!("No drink? Oh well."),
// Others will `panic` before drinking sugary drinks.
// All drinks are handled implicitly using `unwrap`.
fn drink(drink: Option<&str>) {
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 97
// `unwrap` returns a `panic` when it receives a
`None`. let inside = drink.unwrap(); if inside ==
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
"lemonade" { panic!
("AAAaaaaa!!!!"); } println!("I love {}s!!!!!", inside);
} fn main() { let water = Some("water");
let lemonade = Some("lemonade"); let
void = None; give_adult(water);
give_adult(lemonade); give_adult(void);
let coffee = Some("coffee"); let nothing =
None; drink(coffee); drink(nothing);
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 98
6.1.2 Panic
Panic is the error management feature that is the easiest to understand. It usually exits the
program after printing an error message and starting to free up the stack. Here, we categorically
declare that our error state is panic:
fn drink(beverage: &str) {
// You shouldn't drink too much sugary beverages.
if beverage == "lemonade" { panic!("AAAaaaaa!!!!"); } println!
("Some refreshing {} is all I need.", beverage);
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
} fn main()
{ drink("water");
drink("lemonade");
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 99
6.1.3 Result
Result is a more extravagant form of the Option type that portrays conceivable error rather than
conceivable nonappearance. (Anon., n.d)
That is, Result<T, E> could have one of two results:
• Ok(T): An element T was found
• Err(E): An error was found with element E
By show, the expected result is Ok while the unexpected result is Err.
Similar to Option, Result also has a variety of connected strategies. For instance, unwind () either
produces the element T or panics. There are many combinators available for case processing.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
between the cross-overing Results and
Options. (Anon., n.d)
You will undoubtedly come across strategies that yield the Result type while working with Rust,
such as the parse () strategy. Since it might not typically be possible to imagine parsing a string
into the other sort, parse () gives a Result indicating potentially disappointing expectations.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 100
We should see what happens when we effectively and fruitlessly parse () a string:
fn multiply(first_number_str: &str, second_number_str: &str) -> i32 { //
Let's try using `unwrap()` to get the number out. Will it bite us? let
first_number = first_number_str.parse::<i32>().unwrap(); let
second_number = second_number_str.parse::<i32>().unwrap();
first_number * second_number
} fn main() { let twenty =
multiply("10", "2"); println!("double is
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
{}",
twenty); let tt = multiply("t", "2");
println!("double is {}", tt);
When parse() fails, an error is left behind for unwrap() to worry on. Additionally, the panic exits
our application and issues an awful error message. (Anon., n.d)
We should consider handling the error explicitly and being more clear about the return type in
order to improve the nature of our error message.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 101
6.1.4 Multiple error type
The past models have consistently been extremely advantageous; Results communicate with
different Results and Options associate with different Options.
Sometimes an Option needs to interface with a Result, or a Result<T, Error1> needs to
communicate with a Result<T, Error2>. In those cases, we need to deal with our distinctive error
types such that makes them composable and simple to interface with.
In the accompanying code, two cases of unwrap create distinctive error types. Vec::first returns
an Option, while parse::<i32> returns a Result<i32, ParseIntError>:
fn double_first(vec: Vec<&str>) -> i32 { let first =
vec.first().unwrap(); // Generate error 1
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
2 * first.parse::<i32>().unwrap() //
Generate error 2
fn main() { let numbers = vec!["42", "93", "18"]; let empty =
vec![]; let strings = vec!["tofu", "93", "18"]; println!
("The first doubled is {}", double_first(numbers));
println!("The first doubled is {}", double_first(empty));
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 102
// Error 1: the input vector is empty println!("The first
doubled is {}", double_first(strings));
// Error 2: the element doesn't parse to a number
6.1.5 Iterative over results
An Iter::map operation might fail, for example:
fn main() { let strings = vec!["tofu", "93",
"18"]; let numbers: Vec<_> = strings
.into_iter()
.map(|s| s.parse::<i32>())
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
.collect(); println!("Results: {:?}",
numbers);
Ingore the failes items with filter_map() filter_map calls a function
and filters out the results that are None.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 103
fn main() { let strings = vec!["tofu", "93",
"18"]; let numbers: Vec<_> = strings
.into_iter()
.filter_map(|s| s.parse::<i32>().ok())
.collect(); println!("Results: {:?}",
numbers);
Fail the entire operation with collect()
Result implements FromIter so that a vector of results (Vec<Result<T, E>>) can be
turned into a result with a vector (Result<Vec<T>, E>). Once an Result::Err is found, the
iteration will terminate.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
fn main() { let
strings = vec!["tofu", "93", "18"]; let
numbers: Result<Vec<_>, _> = strings
.into_iter()
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 104
.map(|s| s.parse::<i32>())
.collect(); println!("Results: {:?}",
numbers);
Collect all valid and failures with partition fn main() { let
strings = vec!["tofu", "93", "18"]; let (numbers, errors):
(Vec<_>, Vec<_>) = strings
.into_iter()
.map(|s| s.parse::<i32>())
.partition(Result::is_ok); println!
("Numbers: {:?}", numbers); println!("Errors:
{:?}", errors);
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 105
When you look at results, we will note that everything is still wrapped in results. A little more
boilerplate is needed for this.
fn main() { let strings = vec!["tofu", "93", "18"]; let
(numbers, errors): (Vec<_>, Vec<_>) = strings
.into_iter()
.map(|s| s.parse::<i32>())
.partition(Result::is_ok); let numbers: Vec<_> =
numbers.into_iter().map(Result::unwrap).collect(); let errors: Vec<_> =
errors.into_iter().map(Result::unwrap_err).collect(); println!("Numbers:
{:?}", numbers); println!("Errors: {:?}", errors);
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 106
6.1.6 Handling Errors using Do-Catch
You utilize a do-catch proclamation to deal with mistakes by running a square of code. Assuming
that a mistake is tossed by the code in the do provision, it's matched against the catch statements
to figure out which one of them can deal with the blunder.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
Here is the overall type of a do-catch
proclamation:
1. do {
2. try expression
3. statements
4. } catch pattern 1 {
5. statements
6. } catch pattern 2 where condition {
7. statements
8. } catch pattern 3 , pattern 4 where condition {
9. statements
10. } catch {
11. statements
12. }
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 107
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
6.1.7 Changing Error over to Option values
You use attempt? to deal with a mistake by changing it over to a discretionary worth. Assuming a
blunder is tossed while assessing the attempt? articulation, the worth of the articulation is
nothing.
For instance, in the accompanying code x and y have a similar worth and conduct.
1. func someThrowingFunction() throws -> Int {
2. // ...
3. }
4.
5. let x = try? someThrowingFunction()
6.
7. let y: Int?
8. do {
9. y = try someThrowingFunction()
10. } catch {
11. y = nil
12. }
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 108
6.1.8 Bugs Versus exceptions
It is important to decide into which of these categories a certain problem falls. For example,
consider our old power function.
function power(base, exponent) { var result = 1; for
(var count = 0; count < exponent; count++)
result *= base;
return result;
6.1.9 Error handling implementation
Figure 25: Error log
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 109
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
Figure 26: Try catch1
The code above is what it would have looked like without error handling because in the scenario
described above, a user might have accidentally entered a string value in place of an integer
when the system was asking for an integer instead. This would cause the system to malfunction
as shown in the above picture. So, let's see how I corrected this mistake.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 110
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
Figure 27: Try catch 2
So the above image can see using try catch method can avoid the error in this case we can alive
our system when user give any kind of input.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 111
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
6.2 Test report
A test report is a written account of the testing procedures and findings for a specific piece of
software or system. The report typically contains details on the testing methods employed, the
different kinds of tests carried out, the test results, and any problems or flaws found during the
testing process. An extensive grasp of the software's quality and readiness for release is what a
test report is meant to give stakeholders. Developers, testers, project managers, and other
stakeholders use test reports as a crucial component of the software development lifecycle to
make choices about the software.
Here are a few examples of what could be included in a test report:
1. Test Summary: This section provides an overview of the testing process, including the
testing objectives, scope, and key findings.
2. Testing Environment: This section describes the testing environment, including the
hardware, software, and network configurations used during the testing process.
3. Test Cases: This section provides a list of the test cases that were executed during the
testing process, including the expected and actual results.
4. Defects and Issues: This section provides a list of any defects or issues that were
identified during the testing process, including their severity, priority, and steps to
reproduce them.
5. Test Metrics: This section provides quantitative data about the testing process, including
the number of test cases executed, the number of defects identified, and the test coverage
achieved.
6. Recommendations: This section provides recommendations for addressing any defects or
issues identified during the testing process and improving the quality of the software.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 112
These are just a few examples of what could be included in a test report. The specific contents of
the report will depend on the testing objectives, the testing methodology used, and the needs of
the stakeholders who will be reviewing the report.
6.2.1 Why test report is important.
Test reports are important for several reasons:
1. Communication: Test reports give stakeholders, such as developers, testers, project
managers, and company owners, a clear and succinct method to understand the testing
results. They assist in making sure that everyone working on the software development
process is in agreement regarding the software's quality and any problems that need to be
fixed.
2. Decision-making: Stakeholders can use test reports to gather the data they need to make
knowledgeable software choices. Stakeholders can determine whether the software is
ready for release based on the results of the testing process or whether more testing or
development is necessary.
3. Quality control: Test results offer a way to monitor the software's quality evolution.
Stakeholders can spot trends and patterns in the quality of the software by comparing test
results from various stages of the development process and taking appropriate corrective
action as necessary.
4. Compliance: Regulatory agencies or business standards like ISO or CMMI frequently
demand test reports. These studies aid in proving that the software development
procedure adheres to the necessary norms and regulations.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 113
In summary, test reports are important because they provide stakeholders with the information,
they need to make informed decisions about the software, ensure the quality of the software, and
comply with regulatory and industry standards.
6.2.2 What does test report contain
A test report typically contains the following information:
1. Introduction: This section provides an overview of the testing process, including the
objectives, scope, and approach used.
2. Testing Environment: This section describes the testing environment, including the
hardware, software, and network configurations used during the testing process.
3. Test Cases: This section provides a list of the test cases that were executed during the
testing process, including the expected and actual results.
4. Defects and Issues: This section provides a list of any defects or issues that were
identified during the testing process, including their severity, priority, and steps to
reproduce them.
5. Test Metrics: This section provides quantitative data about the testing process, including
the number of test cases executed, the number of defects identified, and the test coverage
achieved.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
6. Summary of Results: This section
provides a summary of the testing results, including an analysis of
the defects and issues identified, and any recommendations for further testing or
development.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 114
7. Conclusions: This section provides a summary of the key findings of the test report, and
any conclusions or recommendations based on those findings.
Depending on the goals, scope, and methodology of the testing process as well as the
requirements of the stakeholders who will be evaluating the report, a test report's precise contents
may change. To give a thorough overview of the testing procedure and results, most test reports
will include the data listed above.
6.2.3 Test results screen shot for given scenario.
Figure 28: Test cycle
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 115
Figure 29: Functions
Figure 30: Defect density
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 116
Figure 31: Defect Fixed Ratio
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 117
7. Discuss how asymptotic analysis can be used to assess the
effectiveness of an algorithm.
7.1 Asymptotic analysis
As the size of an algorithm's input approaches infinity, asymptotic analysis is a method used in
computer science to assess an algorithm's effectiveness. It aids in assessing an algorithm's
efficiency and foretelling how it will scale as input size increases.
Analysis of an algorithm's worst-case behavior is the primary goal of asymptotic analysis. As a
result, it gives us an upper bound on the rate of growth of the algorithm's time complexity and
space complexity, which are the two major aspects that affect how effective the algorithm is.
Big O notation is used in asymptotic analysis to indicate the maximum time and space
complexity of an algorithm. The performance growth rate of an algorithm as the input size
approaches infinite can be expressed using the Big O notation.
Think about an algorithm that sorts an array with n items, for instance. As the input quantity (n)
grows, the algorithm's sorting time for the array will also grow. We can predict how fast the
amount of time needed to sort the array will increase as n grows by using asymptotic analysis.
We can state that the algorithm has an O(n2) time complexity if we observe that the amount of
time needed by the algorithm to sort an array of size n is proportional to n2. This indicates that
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
the time needed to sort the array will only
rise quadratically as n increases. We can state that the algorithm's time
complexity is O if we discover that the amount of time needed by the algorithm
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 118
to sort an array of size n is proportional to n.(n). This means that the time needed to sort the array
will only rise linearly as n increases.
Asymptotic analysis is a powerful tool for analyzing the efficiency of algorithms and comparing
the performance of different algorithms for a given problem. It helps in choosing the most
efficient algorithm for a particular use case and optimizing the performance of existing
algorithms.
7.2 Most pessimistic scenario and Average-Case Analysis
Most pessimistic scenario analysis and average-case analysis are two approaches to analyzing the
efficiency of algorithms.
Worst-case analysis is another name for the situation analysis that is the most pessimistic. It
entails examining an algorithm's behavior while assuming that the input is in the worst-case
situation. The worst-case scenario is the one in which the algorithm needs the most time or space
to finish. We can determine an upper bound on the algorithm's time and space complexity by
considering the worst-case situation. This higher bound ensures that the algorithm won't perform
worse than a specific threshold.
On the other hand, average-case analysis examines an algorithm's performance under the
presumption that the data is uniformly distributed and random. With the help of common inputs,
this method estimates how well the algorithm should work. In average-case analysis, we
determine the algorithm's typical time or area complexity across all feasible inputs. When the
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
input data are unpredictable and the spread of
the input data is unknown, this method is helpful.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 119
Most pessimistic scenario analysis is typically more conservative and offers a more solid upper
limit on the algorithm's performance. On the other hand, average-case analysis offers a more
accurate assessment of the algorithm's real performance on typical inputs.
The constraints of both worst-case and average-case analyses must be kept in mind. The
worstcase situation might not accurately depict the algorithm's typical behavior, and the best-case
scenario might not accurately depict how the algorithm responds to particular inputs. As a result,
it is frequently necessary to combine worst-case and average-case analysis to get a complete
grasp of an algorithm's effectiveness.
7.3 Calculation Efficiency and Asymptotic Analysis
To determine an algorithm's efficiency, one must determine how long and how much memory it
requires to complete a job for a specific input size. On the other hand, asymptotic analysis can be
used to forecast how an algorithm's efficiency will increase as the amount of the input increases
toward infinity.
While measuring an algorithm's efficiency for a particular input size can provide us with a
precise indication of how well it performs, it may not be very helpful to predict how the
algorithm will perform for bigger input sizes. This is where asymptotic analysis comes in, as it
gives us a method to forecast an algorithm's overall effectiveness as the input size increases.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
Big O notation is used in asymptotic analysis
to indicate the maximum time and space complexity of an algorithm. A
program's time complexity measures how long it takes to run as a function of the size of the
input, whereas its space complexity measures how much RAM it needs to run as a function of the
size of the input.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 120
Think about an algorithm that sorts an array with n items, for instance. We can state that an
algorithm has O(n2) time complexity if the amount of time it takes to sort an array is
proportional to n2. This indicates that the time needed to sort the array will only rise
quadratically as n increases. Similar to this, we can state that the algorithm's space complexity is
O if the amount of space needed by the algorithm to sort the array is proportional to n.(n).
Asymptotic analysis allows us to compare the effectiveness of various algorithms and identify
the one that is most appropriate for a particular issue. The actual performance of an algorithm
may be better or worse depending on the particular input data and the implementation of the
algorithm, and asymptotic analysis only gives an upper limit on the growth rate of an algorithm's
efficiency. Therefore, in order to obtain a more accurate estimate of an algorithm's performance,
it is always advised to also carry out real measurements of an algorithm's efficiency for a
particular input size.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 121
7.3.1 Issue with timing code
Timing code is a popular method for gauging how effective an algorithm or program is. Timing
code, however, has a number of potential pitfalls that can produce unreliable or deceptive
outcomes. Here are a few typical synchronization code problems:
1. System load: The system load, which can change based on the other processes operating
on the system, can have an impact on how well a program performs. The timing code
results may be inaccurate and deceptive if other resource-intensive operations are running
on the system at the same time.
2. Warm-up time: When timing code, it's crucial to give enough warm-up time to make sure
that any JIT (Just-in-Time) compilation has taken place and the code has been completely
loaded into memory. Inaccurate findings can result from not allowing enough warm-up
time because early executions might take longer because of compilation or memory
allocation overhead.
3. Measurement overhead: The process of determining the amount of time it takes for an
algorithm to run can add extra overhead, which can skew the results. The operating
system's time-keeping device or the measurement code itself may be the source of this
overhead.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
4. Hardware variability: The
performance of a program can also be affected by the hardware it is
running on. For example, running the same code on different processors or with different
amounts of memory can lead to different performance results.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 122
5. Input data variability: The raw data that an algorithm is processing can also affect how
well it performs. Timing code may not correctly capture an algorithm's performance for a
particular set of inputs, producing inaccurate results.
It's crucial to measure the execution time several times and average the findings in order to
address these problems. Controlling system stress, warming up the code, and reducing
measurement overhead are also essential. To better understand the code's performance
characteristics, it can also be useful to test it on various hardware and input data sets.
7.3.2 Analysis Framework
A system, process, or problem may be analyzed and evaluated using a collection of tools,
methods, and guidelines known as an analysis framework. It offers a methodical strategy to
comprehending a system's parts and behaviors and can point out areas for development or
optimization.
The following are the key components of an analysis framework:
1. Define the problem: Any analysis framework should start with a precise definition of the
issue or research topic. This entails determining the analysis's goals, objectives, and
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
requirements as well as any
restrictions or limitations that might have an effect on the analysis.
2. Gather data: The following stage is to compile pertinent data and information about the
issue. Data collection from different sources, such as surveys, interviews, or data analysis
tools, may be necessary.
3. Analyze the data: Following the collection of the data, it must be analyzed using a variety
of analytical methods, including statistical analysis, regression analysis, and machine
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 123
learning algorithms. Finding patterns, trends, and relationships in the data that can help us
better comprehend the issue is the goal of this step.
4. Identify solutions: The next stage is to find potential solutions or suggestions to deal with
the issue based on the findings of the analysis. To assess various scenarios and their
potential effects, this may entail using brainstorming, modeling, or simulation techniques.
5. Implement and monitor: The next stage after finding a solution is to put it into practice
and track its success over time. This might entail creating an execution strategy, keeping
an eye on the outcomes, and making changes as necessary.
6. Evaluate the results: Evaluating the findings of the analysis and the viability of the
solution is the last stage in the analysis framework. This entails evaluating how the
problem has been resolved in comparison to the initial goals and objectives, comparing
the results to those goals and objectives, and identifying areas that could use
improvement.
Overall, an analysis framework provides a structured approach to analyzing and solving
problems and can be applied to a wide range of contexts and domains, such as business,
engineering, health care, and social sciences.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 124
7.3.3 Asymptotic notation
As the size of the input approaches infinity, asymptotic notation is a mathematical technique used
to express the growth rate of a function. To explain the effectiveness and complexity of
algorithms, it is frequently used in computer science and algorithm analysis.
There are several types of asymptotic notation, including:
1. Big O notation
• Big O notation is a type of mathematical writing used to express the maximum growth
rate of a function. It is frequently used in computer science to characterize an algorithm's
worstcase time complexity in terms of the size of its input.
• If an algorithm, for instance, has a time complexity of O(n), where n is the size of the
input, this indicates that the algorithm's worst-case running time will not increase any
faster than a linear function of n. In other words, the algorithm's running time only grows
maximally linearly with the size of the input.
• An algorithm's worst-case running time will not increase any quicker than a quadratic
function of n if it has a time complexity of O(n2). The algorithm's running time grows at
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
most quadratically as the input
amount does.
• "Order of" is what the "O" in Big O writing stands for. Therefore, when we say that an
algorithm has a time complexity of O(f(n)), we imply that as the input size approaches
infinity, the algorithm's running time grows at a rate on the order of f(n).
• It's essential to remember that Big O notation does not specify the precise running time of
an algorithm; rather, it only gives an upper bound on the growth rate of a function.
Furthermore, Big O notation does not take into account constant factors or lower-order
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 125
terms, which means that two algorithms with the same time complexity could still operate
very differently in reality.
2. Omega notation:
• The bottom limit of a function's growth rate is expressed using the mathematical notation
known as "omega notation." It is a standard practice in computer science to express an
algorithm's worst-case time complexity in terms of the size of its input.
• If an algorithm, for instance, has a time complexity of (n), where n is the size of the input,
it indicates that its best-case running time increases no more slowly than a linear function
of n. In other words, the algorithm's execution time grows at least linearly as the size of
the input rises.
• In a similar vein, if an algorithm has a time complexity of n2, it implies that its best-case
running time increases no more slowly than n's quadratic function. The algorithm's
execution time rises at least quadratically as the input size does.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
• Omega is represented by the Greek
letter "omega" in writing. Because of this, when we say that an
algorithm has a time complexity of (f(n)), we mean that the rate of increase of the
algorithm's running time is at least on the order of f(n) as the input size approaches
infinity.
• Omega notation does not specify the precise running time of an algorithm; rather, it only
gives a lower limit on the growth rate of a function. Omega notation does not take into
account constant factors or higher-order terms, which means that two algorithms with the
same time complexity could still operate very differently in practice.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 126
3. Theta notation:
• The top and lower bounds of a function's growth rate are expressed using the
mathematical notation theta. In computer science, the size of an algorithm's input is
frequently used to characterize the average-case time complexity of an algorithm.
• For instance, if an algorithm's time complexity is n, where n is the size of the input, it
implies that the algorithm's running time increases linearly with n. In other words, the
algorithm's running time increases at most linearly and at least linearly as the input size
grows.
• In a similar vein, if an algorithm's time complexity is n2, it implies that its running time
increases at the same rate as n's quadratic function. The algorithm's running time rises at
most quadratically and at least quadratically as the input size increases.
• The "Θ" in Theta notation stands for "theta". Therefore, when we say an algorithm has a
time complexity of Θ(f(n)), we mean that the growth rate of the algorithm's running time
is on the order of f(n) as the input size approaches infinity, both in the best and worst case
scenarios.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
• Compared to Big O or Omega
notation alone, theta notation more accurately describes the
development rate of a function. Theta notation, however, may not always be appropriate
because an algorithm's best-case and worst-case temporal complexities may not always
be the same.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 127
8. Determine two ways in which the efficiency of an algorithm can be
measured, illustrating your answer with an example.
8.1 Algorithm Efficiency
The term "algorithm efficiency" describes how effectively an algorithm uses resources, usually
time and space. When solving an issue, an efficient algorithm uses the least amount of resources
possible, whereas an inefficient algorithm uses more resources than are required.
The effectiveness of an algorithm is frequently assessed in terms of its space and temporal
complexity in computer science. Time complexity is the amount of time an algorithm needs to
solve a problem as the size of the input increases, whereas space complexity is the amount of
memory an algorithm needs to solve a problem as the size of the input increases.
Because they can produce results more quickly, conserve computational resources, use less
energy, and allow the processing of bigger data sets more quickly, efficient algorithms are
desirable. Many fields of computer science, such as artificial intelligence, computer graphics,
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
cryptography, database systems, network
protocols, and optimization, place a high priority on improving algorithm
efficiency
8.1.1 Time complexity
When the size of the data increases, an algorithm's time complexity measures how long it takes to
run. In other words, it explains how an algorithm's running time grows in proportion to the
amount of the input. The Big O notation is typically used to express the time complexity of an
algorithm and gives an upper bound on the rate of growth of the algorithm's running time.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 128
An algorithm's time complexity plays a significant role in deciding how effective it is. Because it
can handle larger inputs or finish tasks quicker, an algorithm with a lower time complexity will
typically be more effective than an algorithm with a higher time complexity.
For instance, the worst-case scenario for a linear search algorithm entails sequentially checking
each element of an input list until a match is discovered or the complete list is searched. This is
because a linear search algorithm has a time complexity of O(n). The target element in a sorted
list can be found using a binary search algorithm, which has a time complexity of O(log n),
which means that it can do so by splitting the search space in half at each stage. This results in a
much faster search time for big input sizes.
The time complexity of an algorithm should be taken into account when developing and
analyzing it to make sure it is suitable for the issue at hand and the anticipated input size.
Algorithms with lower time complexity are better suited for larger input sizes or when faster
performance is necessary, while algorithms with greater time complexity may be acceptable for
small input sizes or when only a small number of computations are needed.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
8.1.2 Space complexity
The quantity of memory or storage an algorithm needs to run as the size of the input increases is
referred to as space complexity. The amount of memory required by the algorithm to keep its
internal data structures and intermediate results is specified.
Similar to time complexity, space complexity is typically expressed using Big O notation, which
sets a limit on how quickly the algorithm's memory utilization will increase. The quantity of
extra
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 129
memory the algorithm needs above and beyond the size of the input itself is a common metric for
space complexity.
Since they use the least amount of memory to solve a problem, efficient algorithms generally
have low space complexity. An algorithm's ability to manage larger input sizes, use less
expensive hardware or cloud resources, and execute more quickly and reliably are just a few
advantages that can result from reducing an algorithm's space complexity.
A straightforward algorithm that adds up a list of numbers, for instance, has a space complexity
of O (1), which means that it only requires a fixed quantity of memory to store the sum as it is
computed. A recursive algorithm for computing the factorial of a number, however, has a space
complexity of O(n), which means that it must store intermediate results for each recursive call,
leading to a linear rise in memory utilization as the input size increases.
It is crucial to take space complexity into account when creating and analyzing algorithms and to
make sure that it is suitable for the issue at hand and the anticipated input size. Algorithms with
lower space complexity are better suited for larger input sizes or when memory usage must be
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
kept to a minimum, while algorithms with
greater space complexity may be acceptable for small input sizes or when
memory usage is not a concern.
There are three asymptotic notations that are utilized to address the time complexity of an
algorithm. They are:
1. Θ Notation (theta)
2. Big O Notation
3. Ω Notation
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 130
o Θ Notation (theta)
The Notation is used to visualize what is considered to be an algorithm's normal limit. For
instance, it defines an upper bound and a lower bound, and your algorithm will fall somewhere
between these two levels. This means that if a capacity is g(n), the theta portrayal will be
displayed as (g(n)) and the link will be displayed as:
Θ(g(n)) = { f(n): there exist positive constants c1, c2 and n0
such that 0 ≤ c1g(n) ≤ f(n) ≤ c2g(n) for all n ≥ n0 }
The above articulation can be perused as theta of g(n) is characterized as set of the multitude of
capacities f(n) for which there exists some certain constants c1, c2, and n0 with the end goal that
c1*g(n) is not exactly or equal to f(n) and f(n) is not exactly or equal to c2*g(n) for all n that is
more noteworthy than or equal to n0.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
For example:
if f(n) = 2n² + 3n + 1 and g(n) = n² then for c1 = 2, c2 = 6, and
n0 = 1, we can say that f(n) = Θ(n²)
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 131
Figure 32: Θ Notation (theta)
o Ω Notation
The Ω documentation signifies the lower bound of an algorithm for example the time taken by
the algorithm can't be lower than this. At the end of the day, this is the quickest time in which the
algorithm will return an outcome. Its the time taken by the algorithm when given its best-case
input. Along these lines, on the off chance that a capacity is g(n), then, at that point, the omega
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
portrayal is displayed as Ω(g(n)) and the
connection is displayed as:
Ω(g(n)) = { f(n): there exist positive constants c and n0 such
that 0 ≤ cg(n) ≤ f(n) for all n ≥ n0 }
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 132
The above articulation can be perused as omega of g(n) is characterized as set of the multitude of
capacities f(n) for which there exist a few constants c and n0 with the end goal that c*g(n) is not
exactly or equal to f(n), for all n more noteworthy than or equal to n0.
For example: if f(n) = 2n² + 3n + 1 and g(n) = n² then
for c = 2 and n0 = 1, we can say that f(n) = Ω(n²)
Figure 33: Ω Notation
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 133
o Big O notation
The Big O documentation characterizes the upper bound of any algorithm for example you
algorithm can't take additional time than this time. All in all, we can say that the big O
documentation means the most extreme time taken by an algorithm or the most pessimistic
scenario time complexity of an algorithm. Thus, big O documentation is the most utilized
documentation for the time complexity of an algorithm. In this way, assuming a capacity is g(n),
then, at that point, the big O portrayal of g(n) is displayed as O(g(n)) and the connection is
displayed as:
O(g(n)) = { f(n): there exist positive constants c and n0 such
that 0 ≤ f(n) ≤ cg(n) for all n ≥ n0 }
The above articulation can be perused as Big O of g(n) is characterized as a bunch of capacities
f(n) for which there exist a few constants c and n0 to such an extent that f(n) is more noteworthy
than or equal to 0 and f(n) is more modest than or equal to c*g(n) for all n more prominent than
or equal to n0. For example if f(n) = 2n² + 3n + 1 and g(n) = n² then for c = 6 and n0 = 1, we
can say that f(n) = O(n²)
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 134
Figure 34: Big O notation
Big O notation illustration of algorithms
The most popular notation for expressing an algorithm's temporal complexity is called Big O. We
will examine the big O notation of different algorithms in this blog section.
Example: Finding the amount of the main n numbers.
In this model, we need to observe the amount of first n numbers. For instance, assuming n = 4,
our output should be 1 + 2 + 3 + 4 = 10. Assuming n = 5, the ouput should be 1 + 2 + 3 + 4 + 5 =
15.
How about we try various solutions to this code and try to compare that large number of codes.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 135
O(1) solution
// function taking input "n" int
findSum(int n)
{ return n * (n+1) / 2; // this will take some constant time
c1 }
In the above code, there is only one articulation and we know that an assertion requires some
investment for its execution. The essential thought is that assuming the assertion is taking
constant time, then, at that point, it will set aside a similar amount of effort for all the information
size and we denote this as O(1).
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA
STRUCTURES & ALGORITHMS 136
O(n) solution int
findSum(int n)
{ int sum = 0; // -----------------> it takes some constant time "c1" for(int i = 1; i <= n; ++i)
// --> here the comparision and increment will take place
n times(c2*n) and the creation of i takes place with some constant
time
sum = sum + i; // -----------> this statement will be executed n times i.e.
c3*n return sum; // ------------------> it takes some constant time "c4" }
In this solution, we will run a loop from 1 to n and we will add these qualities to a variable
named "aggregate".
The big O notation of the above code is O(c0*n) + O(c), where c and c0 are constants. So, the
overall time complexity can be composed as O(n).
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 137
O(n²) solution
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
// function taking input "n" int
findSum(int n)
{ int sum = 0; // ---------------------> constant time
for(int i = 1; i <= n; ++i) for(int j = 1; j <= i; ++j)
sum++; // -------------------> it will run [n * (n + 1) /
2] return sum; // ----------------------> constant time
In this solution, we will augment the worth of total variable "I" times for example for I =1, the
total variable will be augmented once for example total = 1. For I = 2, the total variable will be
augmented twice. So, how about we see the solution.
The big O notation of the above algorithm is O(c1*n²) +O( c2*n) + O(c3). Since we take the
higher order of growth in big O. So, our expression will be decreased to O(n²).
So far, we have seen 3 solutions to an issue of a similar nature. Which method would you prefer
to use to find the total number of first "n" numbers? If your response is an O(1) solution, we have
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 138
one bonus part for you at the end of this blog post. Because the algorithm's execution time will be
constant regardless of the size of the information, we would lean toward the O(1) answer.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
We learned how to analyze an algorithm's
effectiveness using time and area complexity. Therefore, there is
essentially a compromise between time and space. If time is less than it usually is, room will also
be larger.
Different methods are used to evaluate algorithms. We examine the algorithm's effectiveness
through both time and space research. Sometimes it's necessary to look at how much memory or
room is being used. For instance, when managing vast amounts of data or developing embedded
devices. Furthermore, time complexity/efficiency shows that the quicker a program or function
completes a job, the better.
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 139
9. Conclusion
We summarize each module's key ideas and go over its subjects once more in these concluding
notes. You should have gained a deeper understanding of programming from this lesson, with a
focus on the item-centered approach to programming. It ought to encourage you to think about
programming in terms of what you want to do to solve a problem or illustrate a situation rather
than just the features of the programming language you're using, and then how you would go
about doing that in your chosen programming language. You "invent your own instructions," or
write methods, and you "invent your own types," or write classes, to organize a program. Most of
the time, after considering the situation you're trying to portray, you'll determine what kind of
instructions you need. You will then engage in programming on two levels: The code that gives
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
these types and instructions is known as the
implementation, whereas your own custom types and instructions are used
in the application. More intricate code can be further divided into implementation and application
components.
Design specification for data structures that describes the legitimate operations that can be
carried out on the structures as well as how a memory stack functions and how it is used to
execute determined function calls in a computer. Reports on the test outcomes, error handling,
and a challenging ADT implementation are all included in the paper. This paper shows how to
assess an algorithm's effectiveness using asymptotic analysis. Finally, the author offered two
approaches for assessing an algorithm's effectiveness, using an illustration to support your
answer.
This subject covers a lot of material, so if you learn everything there is to know about it, it might
be difficult to comprehend. But since this is a practical part, you can use the executable code that
has been provided to test your own theories. That is the most efficient way to study this material,
create your own code or modify already-existing code, and see how what is covered in these
notes
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 140
is used in practice. Like many practical abilities, they become simpler the more you use them.
When you use them, what seems difficult to describe in words turns out to be much simpler.
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
lOMoARcPSD|20224103
M.S.MARYAM RUQSHA /COL00088920 – DATA STRUCTURES & ALGORITHMS 141
Downloaded by Chamika Srimantha (chamikasrimantha2002@gmail.com)
You might also like
- Transport Network Design AssignmentDocument88 pagesTransport Network Design AssignmentMOHAMED SIHAF100% (1)
- Discrete Mathematics Complete AssignmentDocument47 pagesDiscrete Mathematics Complete AssignmentCRi GB78% (9)
- FortiOS 7.2 Best - PracticesDocument40 pagesFortiOS 7.2 Best - PracticesneilNo ratings yet
- FortiAuthenticator Quiz PDFDocument3 pagesFortiAuthenticator Quiz PDFcaos probaNo ratings yet
- TADM10 - 1 Test QuestionsDocument7 pagesTADM10 - 1 Test QuestionsWilson Lima100% (1)
- Unit 02 - Networking AssignmentDocument122 pagesUnit 02 - Networking AssignmentThushan LakshithaNo ratings yet
- A-008550-1624688646968-80386-Unit 34 - System Analysis and Design.Document103 pagesA-008550-1624688646968-80386-Unit 34 - System Analysis and Design.Hansi Ranasinghe100% (1)
- Esp32 Technical Reference Manual enDocument660 pagesEsp32 Technical Reference Manual enDeepak BhagatNo ratings yet
- Ins Important QuestionsDocument3 pagesIns Important QuestionsSanjanaNo ratings yet
- Yohan Prototyping Final AssingmentDocument143 pagesYohan Prototyping Final AssingmentMadara NirmaniNo ratings yet
- 4549-1688754073246-unit-35-system-analysis-and-designDocument85 pages4549-1688754073246-unit-35-system-analysis-and-designMohammed AskarNo ratings yet
- Downstudocucom Lan Design Implementation For Syntax SolutionsDocument157 pagesDownstudocucom Lan Design Implementation For Syntax SolutionsBimsara KumarasingheNo ratings yet
- Networking Assignment 1st SemesterDocument113 pagesNetworking Assignment 1st SemesterisumkNo ratings yet
- Networking Assignment 1st SemesterDocument113 pagesNetworking Assignment 1st SemesterGK AshenNo ratings yet
- Unit 13 CRP Report 2021 2022 Digital TransformationDocument148 pagesUnit 13 CRP Report 2021 2022 Digital TransformationNipuniNo ratings yet
- Database Assignment Database AssignmentDocument73 pagesDatabase Assignment Database Assignmentrsmusical62No ratings yet
- 1164-1619624869751-40 - Advanced Programming Reworded 2021Document133 pages1164-1619624869751-40 - Advanced Programming Reworded 2021ahmedNo ratings yet
- CRP 2Document181 pagesCRP 2aruna92piyumi93No ratings yet
- SAD SampleDocument90 pagesSAD Samplearmirshadh22No ratings yet
- ABC Same Code S.piragash PDFDocument116 pagesABC Same Code S.piragash PDFRaishaNo ratings yet
- 1153 1619623108515 Unit 10 Web Design and Development RewordedDocument128 pages1153 1619623108515 Unit 10 Web Design and Development Rewordedvidura375No ratings yet
- Computing Research Project HND in Computing Computing Research Project HND in ComputingDocument59 pagesComputing Research Project HND in Computing Computing Research Project HND in Computingaruna92piyumi93No ratings yet
- WDD TestDocument69 pagesWDD Testdenuwanathauda4No ratings yet
- E126643 WDD Niluksha WDD AssignmentDocument150 pagesE126643 WDD Niluksha WDD AssignmentJoe RootNo ratings yet
- Unit 02 Networking 2020 Reworded PDFDocument116 pagesUnit 02 Networking 2020 Reworded PDFsl teachNo ratings yet
- E127670-1699812791387-361803-DSA - Jayan Perera - E127670Document80 pagesE127670-1699812791387-361803-DSA - Jayan Perera - E127670maheshikatharushi5No ratings yet
- OK - WDD Niluksha WDD AssignmentDocument150 pagesOK - WDD Niluksha WDD Assignmentudesh ishankaNo ratings yet
- ABC Different Code Premnath PDFDocument81 pagesABC Different Code Premnath PDFRaishaNo ratings yet
- E168429-1664557821200-193283-Thirukkumaran 00139198 Unit 02 Networking-Reworded 2Document78 pagesE168429-1664557821200-193283-Thirukkumaran 00139198 Unit 02 Networking-Reworded 2Gopahan HamsavarthanNo ratings yet
- E157266-1692427850039-308622-Unit 34 - System Analysis - Design - Reworded - 2021Document54 pagesE157266-1692427850039-308622-Unit 34 - System Analysis - Design - Reworded - 2021muheedhmuheedhboyNo ratings yet
- Unit 02 Networking Reworded 2022 Ahmed MushtaqDocument130 pagesUnit 02 Networking Reworded 2022 Ahmed MushtaqAhamedNo ratings yet
- Unit 5 SecurityDocument36 pagesUnit 5 SecuritySulakshi SulakshirajakarunaNo ratings yet
- AD Mohamed Shimash Siraj AD Mohamed Shimash SirajDocument145 pagesAD Mohamed Shimash Siraj AD Mohamed Shimash SirajahmedNo ratings yet
- Lan Design Implementation For Syntax SolutionsDocument157 pagesLan Design Implementation For Syntax SolutionsCool MarttNo ratings yet
- Securirty Assignment RoshenDocument89 pagesSecurirty Assignment RoshenSandun RathnayakaNo ratings yet
- Unit 34 - System AnalysisDocument72 pagesUnit 34 - System Analysistharindu roshanaNo ratings yet
- ABC Different Code Premnath PDFDocument88 pagesABC Different Code Premnath PDFRaishaNo ratings yet
- DSA AssingmentDocument79 pagesDSA AssingmentPrince RizerNo ratings yet
- 1160-1619624320093-Unit 34 - System Analysis - Design - Reworded - 2021 - E158162Document126 pages1160-1619624320093-Unit 34 - System Analysis - Design - Reworded - 2021 - E158162Charles RodrigoNo ratings yet
- MDSA AsdignmentDocument30 pagesMDSA AsdignmentRaishaNo ratings yet
- ABC Assignment PDFDocument64 pagesABC Assignment PDFRaishaNo ratings yet
- 1159 1619624003344 UNIT 19 DSA ASSIGNMENT - Reworded - 2021Document17 pages1159 1619624003344 UNIT 19 DSA ASSIGNMENT - Reworded - 2021Thushan LakshithaNo ratings yet
- CRP FinalDocument148 pagesCRP FinalNipuniNo ratings yet
- Net RishDocument74 pagesNet RishRishad JobbsNo ratings yet
- Ruzan Network Final Assignment - 082926Document65 pagesRuzan Network Final Assignment - 082926starelike002No ratings yet
- E157266-1699766836404-330779-Unit 45 - Emerging - Technologies - Reworded - 2021 - MergedDocument103 pagesE157266-1699766836404-330779-Unit 45 - Emerging - Technologies - Reworded - 2021 - MergedmuheedhmuheedhboyNo ratings yet
- A-019730-1647416754604-137865-W.M.Supun Anjana DSADocument175 pagesA-019730-1647416754604-137865-W.M.Supun Anjana DSADishan SanjayaNo ratings yet
- 1159 1619624003344 UNIT 19 DSA ASSIGNMENT - Reworded - 2021Document74 pages1159 1619624003344 UNIT 19 DSA ASSIGNMENT - Reworded - 2021Azam AkshanNo ratings yet
- Maths AssignmentDocument72 pagesMaths Assignmentimad zayan (bumblebee ..)No ratings yet
- Higher Nationals: Internal Verification of Assessment Decisions - BTEC (RQF)Document46 pagesHigher Nationals: Internal Verification of Assessment Decisions - BTEC (RQF)safras faizerNo ratings yet
- Aiyoob's NetworkingDocument168 pagesAiyoob's NetworkingAiyoob.No ratings yet
- UntitledDocument87 pagesUntitledrecoveries 1No ratings yet
- Unit 19 Dsa Assignment Reworded 2021Document38 pagesUnit 19 Dsa Assignment Reworded 2021Banuka UdayangaNo ratings yet
- Programing Assignment BriefDocument133 pagesPrograming Assignment BriefMohamed Rasul MohamedNo ratings yet
- Premnath - Jaf 1679217975465 270647 Sanjeeth Final NetworkDocument174 pagesPremnath - Jaf 1679217975465 270647 Sanjeeth Final NetworkVivekan VivekNo ratings yet
- Higher Nationals: Internal Verification of Assessment Decisions - BTEC (RQF)Document76 pagesHigher Nationals: Internal Verification of Assessment Decisions - BTEC (RQF)Rangika De silvaNo ratings yet
- #Prabin Sunuwar SITXHRM002 Assessment TaskDocument31 pages#Prabin Sunuwar SITXHRM002 Assessment TaskPravinNo ratings yet
- 1447 1628760497056 Unit 6 MSCP 2021 and 22 RWDocument56 pages1447 1628760497056 Unit 6 MSCP 2021 and 22 RWrecoveries 1No ratings yet
- 1151-1619622564463-Unit 02 Networking - Reworded - 2021Document15 pages1151-1619622564463-Unit 02 Networking - Reworded - 2021Udara BandaraNo ratings yet
- TND 2-KavishnaDocument130 pagesTND 2-KavishnaShahana RifkhanNo ratings yet
- 1151-1647580999324-Unit 02 Networking - Reworded - 2021Document90 pages1151-1647580999324-Unit 02 Networking - Reworded - 2021Nimanthika PrasadaniNo ratings yet
- E131525 1650995324013 157617 Shobikah - NWDocument133 pagesE131525 1650995324013 157617 Shobikah - NWVivekan VivekNo ratings yet
- PMI-PBA Exam Success :A Practical Guide to Ace Business Analysis QuestionsFrom EverandPMI-PBA Exam Success :A Practical Guide to Ace Business Analysis QuestionsNo ratings yet
- Configuring Snmpv3 On Huawei DevicesDocument3 pagesConfiguring Snmpv3 On Huawei DevicesHussein DhafanNo ratings yet
- AES Algorithm For Smartphone To Vehicle CommunicationDocument4 pagesAES Algorithm For Smartphone To Vehicle CommunicationAndriansyah ZakariaNo ratings yet
- Homework 2 Solutions: 1 Security ProtocolsDocument6 pagesHomework 2 Solutions: 1 Security ProtocolsneetuNo ratings yet
- Recording LogDocument314 pagesRecording LogSreenivasulu Reddy SanamNo ratings yet
- Task Meeting11 17191156Document2 pagesTask Meeting11 17191156rizki prabowoNo ratings yet
- Full Chapter Database and Application Security A Practitioners Guide 1St Edition Danturthi PDFDocument53 pagesFull Chapter Database and Application Security A Practitioners Guide 1St Edition Danturthi PDFjoey.carey681100% (7)
- Secure Medical Data Transmission Model For Iot-Based Healthcare SystemsDocument13 pagesSecure Medical Data Transmission Model For Iot-Based Healthcare Systemsrock starNo ratings yet
- Encryption TechDocument8 pagesEncryption TechsrisairampolyNo ratings yet
- Openvpn PfsenseDocument22 pagesOpenvpn PfsenseCARL JHON DURAN VARGASNo ratings yet
- Secure Socket LayerDocument27 pagesSecure Socket LayerKalpa De SilvaNo ratings yet
- Computer ScienceDocument17 pagesComputer ScienceTruptiNo ratings yet
- nlp1 SSHDocument4 pagesnlp1 SSHgojodNo ratings yet
- Unit 3 Cryptography and Public Key InfrastrucutreDocument34 pagesUnit 3 Cryptography and Public Key InfrastrucutreDarshit ChhatbarNo ratings yet
- BTEC Level 3 Organisational Systems Security Assignment 1Document6 pagesBTEC Level 3 Organisational Systems Security Assignment 1trey0% (1)
- Network Security CryptographyDocument23 pagesNetwork Security CryptographynazerNo ratings yet
- Linux Essential A 2 4Document28 pagesLinux Essential A 2 4Robin LiNo ratings yet
- Online and Payment SecurityDocument14 pagesOnline and Payment SecurityVanezz UchihaNo ratings yet
- ClaudiaDocument29 pagesClaudiaLulz CypherNo ratings yet
- cs707 Past PapersDocument5 pagescs707 Past Papersms160400042 Ashfaq Ahmad JanNo ratings yet
- Cns QBDocument3 pagesCns QBDheepak NarsimhanNo ratings yet
- Principles of Information SecurityDocument23 pagesPrinciples of Information SecurityVinu VithuNo ratings yet
- Notlogin NillreturnDocument142 pagesNotlogin NillreturnbestdealsNo ratings yet
- Improving Privacy and Security in Multi-Authority Attribute-Based EncyptionDocument12 pagesImproving Privacy and Security in Multi-Authority Attribute-Based Encyptionselva kumarNo ratings yet
- CH 3Document46 pagesCH 3አርቲስቶቹ Artistochu animation sitcom by habeshan memeNo ratings yet
- AMNA Arooj RsaDocument7 pagesAMNA Arooj RsaAmna AroojNo ratings yet