Professional Documents
Culture Documents
Exam 1.1. Assess Cybersecurity Concepts and Security Principles Learned - Coursera
Exam 1.1. Assess Cybersecurity Concepts and Security Principles Learned - Coursera
Uploaded by
RopTox YTCopyright:
Available Formats
You might also like
- EJPTv2 Exam ReviewDocument11 pagesEJPTv2 Exam Reviewtanjidhasan0077No ratings yet
- Final Exam AnswersDocument27 pagesFinal Exam AnswersWaktole GenatiNo ratings yet
- IBM Security Verify Privilege Level 2 Quiz Attempt ReviewDocument9 pagesIBM Security Verify Privilege Level 2 Quiz Attempt ReviewBBMNo ratings yet
- Lesson Plan - Day 1.Document4 pagesLesson Plan - Day 1.Jocelyn Baculi AutenticoNo ratings yet
- Basic Signal CommunicationDocument3 pagesBasic Signal Communicationhumanupgrade100% (3)
- QuizDocument6 pagesQuizJames PodlewskiNo ratings yet
- AU5800 Online Specification For Version 5.0 or LaterDocument61 pagesAU5800 Online Specification For Version 5.0 or LaterRubi Kauneus MørkeNo ratings yet
- Huawei DWDM SDHDocument31 pagesHuawei DWDM SDHKevin SalvatierraNo ratings yet
- Week 1 Quiz - CourseraDocument1 pageWeek 1 Quiz - CourseraSarang PotdarNo ratings yet
- IBM Security Verify Access Level 2 Quiz Attempt Review PDFDocument10 pagesIBM Security Verify Access Level 2 Quiz Attempt Review PDFJustice MapangaNo ratings yet
- 11.1 Class Tasks Suggested AnswersDocument6 pages11.1 Class Tasks Suggested Answersgemote6096No ratings yet
- Final Exam - Evaluación Final - Cybersecurity EssentialsDocument32 pagesFinal Exam - Evaluación Final - Cybersecurity EssentialsVicente Romero46% (50)
- Module Quiz - Interactive CSS - CourseraDocument1 pageModule Quiz - Interactive CSS - CourseraRopTox YTNo ratings yet
- Chapter 7 Quiz - Attempt Review-22 PDFDocument1 pageChapter 7 Quiz - Attempt Review-22 PDFShaharyar AhmedNo ratings yet
- Post-Quiz: Attempt ReviewDocument3 pagesPost-Quiz: Attempt ReviewNikhil SahlotNo ratings yet
- Post-Quiz: Attempt ReviewDocument3 pagesPost-Quiz: Attempt ReviewNikhil SahlotNo ratings yet
- ECCU 501 Syllabus 2021Document12 pagesECCU 501 Syllabus 2021hatfiodNo ratings yet
- Syllabus PCLU FE 1Document4 pagesSyllabus PCLU FE 1Maestro CabadoNo ratings yet
- Cyber Security - A Promising PathDocument12 pagesCyber Security - A Promising PathVinnySha SelvarajahNo ratings yet
- Chapter 1 Quiz - Cybersecurity EssentialsDocument8 pagesChapter 1 Quiz - Cybersecurity EssentialsbmkvsrNo ratings yet
- Chapter 4 Quiz - Evidence7 PC4.1-PC4.4 Attempt ReviewDocument1 pageChapter 4 Quiz - Evidence7 PC4.1-PC4.4 Attempt ReviewKhaled Al AliNo ratings yet
- Info Assurance Security Syll 2 2022-2023Document7 pagesInfo Assurance Security Syll 2 2022-2023beverly arevaloNo ratings yet
- CEHDocument5 pagesCEHanil0% (1)
- Key Concepts On Deep Neural Networks - CourseraDocument1 pageKey Concepts On Deep Neural Networks - CourseracgchydtrainingNo ratings yet
- Quiz 5 - CS690 A1 Network ..Document7 pagesQuiz 5 - CS690 A1 Network ..Nishant KawaNo ratings yet
- Lesson Plan - Day 1.Document4 pagesLesson Plan - Day 1.Jocelyn Baculi AutenticoNo ratings yet
- Chapter 1 Quiz - Cybersecurity Essentials - EN 0118Document7 pagesChapter 1 Quiz - Cybersecurity Essentials - EN 0118Jenny Marcela Perez BolivarNo ratings yet
- Final Quiz PDFDocument37 pagesFinal Quiz PDFB.Deepak CR7No ratings yet
- Case 3 - An Organization That Wanted To Secure Acce...Document4 pagesCase 3 - An Organization That Wanted To Secure Acce...Muhammad FrazNo ratings yet
- Final Quiz - Cybersecurity Essentials - en 0118Document32 pagesFinal Quiz - Cybersecurity Essentials - en 0118Zulkipli0% (2)
- Ungraded Test On Modules 1 and 2Document7 pagesUngraded Test On Modules 1 and 2Hanzhi -No ratings yet
- Background/Overview: Student Name: Tetyana Hyde Student ID: E0972688Document21 pagesBackground/Overview: Student Name: Tetyana Hyde Student ID: E0972688tetyanaNo ratings yet
- CyberOps Associate (Version 1.0) - FINAL Exam (Answers)Document90 pagesCyberOps Associate (Version 1.0) - FINAL Exam (Answers)coba yudNo ratings yet
- Important Instructions To Examiners:: What Is Computer Security & Its Need?Document40 pagesImportant Instructions To Examiners:: What Is Computer Security & Its Need?Gaurang NakumNo ratings yet
- Risk Based Test PlanningDocument1 pageRisk Based Test PlanningPatriciaGarcesNo ratings yet
- Career Path Syllabus - Cyber Security EngineerDocument3 pagesCareer Path Syllabus - Cyber Security EngineerKhushiNo ratings yet
- Take Test: Vulnerability Scanning, Ethics, Privacy, and The ...Document4 pagesTake Test: Vulnerability Scanning, Ethics, Privacy, and The ...Suman ShahNo ratings yet
- Lesson Plan - TemplateDocument3 pagesLesson Plan - Template303906No ratings yet
- EHF M01 C01 PPT IntroductionDocument37 pagesEHF M01 C01 PPT IntroductionDÀRK么SØUŁ GAMINGNo ratings yet
- Kaspersky Security Awareness Datasheet GAT 0322 ENDocument6 pagesKaspersky Security Awareness Datasheet GAT 0322 ENghNo ratings yet
- Career Path Syllabus - Penetration TesterDocument2 pagesCareer Path Syllabus - Penetration TesterjansonhushNo ratings yet
- EX FINAL 2 - IBM Cybersecurity Analyst Professional Certificate Assessment Exam - CourseraDocument33 pagesEX FINAL 2 - IBM Cybersecurity Analyst Professional Certificate Assessment Exam - CourseraPaul Bances SeverinoNo ratings yet
- 2020 11 16 TVET Trades Session3Document27 pages2020 11 16 TVET Trades Session3Santosh KatkarNo ratings yet
- Expert Veri Ed, Online, Free.: Custom View SettingsDocument2 pagesExpert Veri Ed, Online, Free.: Custom View SettingsxaninNo ratings yet
- Lecture0 Into IsrafilDocument6 pagesLecture0 Into IsrafilVictor ImehNo ratings yet
- Analysis of Superstructure Using Midas CivilDocument21 pagesAnalysis of Superstructure Using Midas CivilBadri NathNo ratings yet
- 50 Cyber Security Interview Question & Answers For Sure Shot Success - Networking and SecurityDocument34 pages50 Cyber Security Interview Question & Answers For Sure Shot Success - Networking and SecurityC GNo ratings yet
- CPTE CourseDocument11 pagesCPTE CourseGudden GuptaNo ratings yet
- Iot Security 1.1 Chapter 6 Quiz: Attempt HistoryDocument11 pagesIot Security 1.1 Chapter 6 Quiz: Attempt HistoryJaime QuishpeNo ratings yet
- Chapter 8 Quiz - Attempt Review-2 PDFDocument1 pageChapter 8 Quiz - Attempt Review-2 PDFShaharyar AhmedNo ratings yet
- Cloud Tech Associate Advanced Email Security 2022Document79 pagesCloud Tech Associate Advanced Email Security 2022Juntos PodCastNo ratings yet
- Module 4 QuizDocument1 pageModule 4 QuizNasar KhanNo ratings yet
- Final Quiz - Ui Cybersecurityessen CV 9no Sis 2018 2019Document28 pagesFinal Quiz - Ui Cybersecurityessen CV 9no Sis 2018 2019Juan Carlos Carrillo50% (4)
- Module 4 QuizDocument1 pageModule 4 QuizNasar KhanNo ratings yet
- Information Assurance and Security Prelim ExamDocument14 pagesInformation Assurance and Security Prelim ExamAwan LangNo ratings yet
- Io Midterm ReviewerDocument5 pagesIo Midterm ReviewerMargarita Dave MendozaNo ratings yet
- QuizChapter 1Document6 pagesQuizChapter 1Yoga SaputraNo ratings yet
- Study Plan Cisco CCNA Security 210 260 IINSDocument8 pagesStudy Plan Cisco CCNA Security 210 260 IINSMr RCodeNo ratings yet
- Saint Leo University Introduction To Security Information COM-416 July 26, 2014Document7 pagesSaint Leo University Introduction To Security Information COM-416 July 26, 2014SaravananNo ratings yet
- PCNSE 10.1 Domain #1 - Planning and Core ConceptsDocument107 pagesPCNSE 10.1 Domain #1 - Planning and Core ConceptsFernala Sejmen-Banjac0% (1)
- MCTS Windows SharePoint Services 3.0 Configuration Study Guide: Exam 70-631From EverandMCTS Windows SharePoint Services 3.0 Configuration Study Guide: Exam 70-631No ratings yet
- CISA Exam-Testing Concept-Knowledge of Logical Access ControlFrom EverandCISA Exam-Testing Concept-Knowledge of Logical Access ControlRating: 2.5 out of 5 stars2.5/5 (3)
- Hassdac 720p SystemDocument4 pagesHassdac 720p SystemNeelam sihagNo ratings yet
- Page 1Document6 pagesPage 1langbotNo ratings yet
- 300-135 Exam Dumps With PDF and VCE Download (21-40)Document32 pages300-135 Exam Dumps With PDF and VCE Download (21-40)Metuzalem De Oliveira ZalemNo ratings yet
- MME Technical OverviewDocument568 pagesMME Technical OverviewAndreea TrenteaNo ratings yet
- 4CAE000433 XMC22 XMC23 XMC25 EnglishDocument3 pages4CAE000433 XMC22 XMC23 XMC25 Englishmarija.bandic1No ratings yet
- Vmware Validated Design 20 Introduction GuideDocument30 pagesVmware Validated Design 20 Introduction GuideninodjukicNo ratings yet
- Cambium Networks PMP 450 Subscriber Module SpecificationDocument2 pagesCambium Networks PMP 450 Subscriber Module SpecificationthenioNo ratings yet
- Cisco Voip/Ccme: Introduction To Cisco Unified Communication Manager Express (Callmanager Express - Cme)Document28 pagesCisco Voip/Ccme: Introduction To Cisco Unified Communication Manager Express (Callmanager Express - Cme)Ministere EdificeNo ratings yet
- MOP Integration and Protocol Activation 7705 at LPG-TLS-EN1-SAR8 v1.1Document25 pagesMOP Integration and Protocol Activation 7705 at LPG-TLS-EN1-SAR8 v1.1Diksi KalisNo ratings yet
- TOPFLYtech Product - April 2023 - 4GDocument56 pagesTOPFLYtech Product - April 2023 - 4GmosorioNo ratings yet
- Usw E48pDocument3 pagesUsw E48pMohamed Shaffaf Ali RasheedNo ratings yet
- Multiple Access Techniques For 5G Wireless Networks and Beyond PDFDocument692 pagesMultiple Access Techniques For 5G Wireless Networks and Beyond PDFTarek GARANo ratings yet
- ILS (Glide Path) - System Part Training BookDocument25 pagesILS (Glide Path) - System Part Training BookChiranjivi KuthumiNo ratings yet
- FortiOS 7.0 PortsDocument6 pagesFortiOS 7.0 Portsvedant vedNo ratings yet
- Dell Storage Center SC4020 Storage System OwnerManualDocument41 pagesDell Storage Center SC4020 Storage System OwnerManualfarrukh_meNo ratings yet
- CCIE V5.0 LAB小凡实验室-H1Document40 pagesCCIE V5.0 LAB小凡实验室-H1Song XiuheNo ratings yet
- Ken HollaydayDocument3 pagesKen HollaydaySonia ElouedNo ratings yet
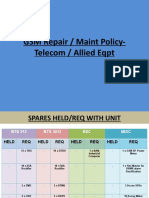
- GSM Repair / Maint Policy-Telecom / Allied EqptDocument9 pagesGSM Repair / Maint Policy-Telecom / Allied EqptImran AzizNo ratings yet
- Skip To ContentDocument18 pagesSkip To ContentFikru TesefayeNo ratings yet
- 5G Mficd: Supported RF Trace MessagesDocument7 pages5G Mficd: Supported RF Trace MessagesJózsef HoffmannNo ratings yet
- Experiment No. 01 Experiment Name-ASK ModulationDocument47 pagesExperiment No. 01 Experiment Name-ASK ModulationmuskanNo ratings yet
- V6.4.0 Technical Update: SAN Volume Controller and Storwize V7000Document58 pagesV6.4.0 Technical Update: SAN Volume Controller and Storwize V7000ecorradiNo ratings yet
- ERD97P21-U Receiver: Product SpecificationDocument2 pagesERD97P21-U Receiver: Product SpecificationSakerhetsNo ratings yet
- MDE-4820H 8 Port Commverter Operation and Installation ManualDocument129 pagesMDE-4820H 8 Port Commverter Operation and Installation ManualJ LUIS AGUILARNo ratings yet
- Amphenol CATV ConnectorsDocument28 pagesAmphenol CATV ConnectorsCARLOSNo ratings yet
- Chapter 8-Fault ToleranceDocument30 pagesChapter 8-Fault ToleranceMohamedsultan AwolNo ratings yet
- WIMAX Throughput CalculationDocument3 pagesWIMAX Throughput Calculationarzaman100% (1)
Exam 1.1. Assess Cybersecurity Concepts and Security Principles Learned - Coursera
Exam 1.1. Assess Cybersecurity Concepts and Security Principles Learned - Coursera
Uploaded by
RopTox YTOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Exam 1.1. Assess Cybersecurity Concepts and Security Principles Learned - Coursera
Exam 1.1. Assess Cybersecurity Concepts and Security Principles Learned - Coursera
Uploaded by
RopTox YTCopyright:
Available Formats
Exam 1.1.
Assess Cybersecurity Concepts and Security Principles Learned English Due Dec 3, 11:59 PM -05
Back Graded Quiz • 42 min
Hide menu
Try again once you are ready
Exam 1.1. Assess Cybersecurity Concepts and Security Principles Learned
Course Overview Try again
Grade Latest Submission To pass 80% or
Vulnerability and Threat received 52.38% Grade 52.38% higher
MOM: Method, Opportunity, Motive
CIA: Confidentiality, Integrity, Availability
Review Learning Objectives
Risk, Risk Assessment and Method of Defense
Security Principles: Defense in Depth, Defense with Diversity, Cyber Resilience 1. 2016 DNC was hacked by Russian Hackers. What are the MOM involved? 0.6666666666666666
/ 1 point
Video: Security Principles: Defense in Depth, Defense with Diversity, Cyber Resilience
6 min
Submit your assignment
The methods are to use the hacking tool to break in the insecure/unpatched DNC server and to launch Try again
Reading: Defense in Depth
Due Dec 3, 11:59 PM -05 Attempts 3 every 8 hours phishing emails to get login credential from DNC staff.
10 min
Discussion Prompt: Security Principles: Defense in Depth, Defense with Diversity, Cyber Resilience
Correct
5 min
Receive grade Correct. The tools for phishing credential through emails and for penetrating the insecure servers are Your grade
Quiz: Exam 1.1. Assess Cybersecurity Concepts and Security Principles Learned ready available on internet. View Feedback
42 min To Pass 80% or higher 52.38% We keep your highest score
The main motive is to steal credit card info of donors in DNC server.
The opportunity will not be there if the DNS staff are well trained with cybersecurity awareness on phishing
attacks and how to handle it and if DNS hire qualified IT security professionals with tools patching the
Like Dislike Report an issue
server and protecting the data.
You didn’t select all the correct answers
2. The three basic security services with the CIA acronym can be used as a triage tool to analyze cyber incidents and 1 / 1 point
suggest solutions. Which of the following is an application of CIA?
Brian Kreb of Krebonsecurity was attacked by DDoS with more than 600 Gbps 9/20/2016. Such an attack
could have been prevented by encrypting his documents on the hosting web server.
Brian Kreb of Krebonsecurity was attacked by DDoS attacks with more
than 600 Gbps 9/20/2016. Such an attack could have been prevented by requiring each visitor of his web site
to login and present the password.
Brian Kreb of Krebonsecurity was attacked by DDoS attacks with more
than 600 Gbps 9/20/2016. Such an attack could have been prevented by moving his web site to a hosting
company that is capable of dealing with the kind of DDoS bandwidth attacks.
Correct
Correct. Brian Kreb was kicked out of the hosting companies twice due to the availability capability of
companies not able to deal with the amount of attack bandwidth. Finally Google Shield takes him in and
provide capable availability service to defeat the attacks. See the related presentation at USENIX Enigama
2017 conference.
3. Select the correct match based on classifying the attack according to the basic type of threats. 1 / 1 point
North Korea launched DDoS Attacks on FTC, White House, and Dept of Commerce. This is considered as
fabrication threat.
North Korea launched DDoS Attacks on FTC, White House, and Dept of Commerce. This is considered as
interruption threat.
North Korea launched DDoS Attacks on FTC, White House, and Dept of Commerce. This is considered as
Interception threat.
North Korea launched DDoS Attacks on FTC, White House, and Dept of Commerce. This is considered as
modification threat.
Correct
Correct. They intend to interrupt the access to those US web sites.
4. Ashley Madison Web Site got hacked 7/2015. Results in 32M accounts and usernames released on the dark web. 0.5 / 1 point
Since their web site does not verify the email address when users registered, many were framed, users
impersonated e.t.c. How do you design the web site registration process to prevent such abuse (using others'
email addresses as login) from happening?
Click on link for more information.
The abuser is attacking vulnerability and incorrect implementation of the integrity service of the Ashley
Madison site.
The registration will require the user to confirm their registration by sending secure confirmation email with
unique one time pass (OTP) code to the mail account and only when the user hit the link attached in the
email, the registration will be completed.
Correct
Correct. This will work. A person tries to use other's email will not know the OTP to confirm the
registration. The OTP needs to be saved with the registration request for verifcation though. The OTP
need to be sent over secure email to avoid packet sniffing.
The registration will require the user to confirm their registration by
sending secure confirmation email with an url containing the email address and a token encrypted with the
email address and a secret string.
The registration will require the user to confirm their registration by sending an email and ask user to send
a simple email back to the site with their email on subject field.
You didn’t select all the correct answers
5. Assessing the risk of a secure network system allow us to make wise decision in investing our resources to address 0 / 1 point
the critical impact areas and to improve the "security posture" of our system.
Prevent is one of the method of the defense. we can prevent
the intrusion from arriving or
happening.
Deter can not often effective achieve, since we often do not know who attack us. Therefore it is not a
method of defense to be considered.
Risk can never be eliminated so it is futile to perform any risk analysis.
Risk can be assessed by the summation of all impacts of security events and their probability of
occurrence.
Correct
Correct. That is the basic formula we use to estimate or calculate the risks.
You didn’t select all the correct answers
6. To reduce the risk we can deploy various methods of defense. They deals with different stages of attacks. 0 / 1 point
By deploying the five different methods of defense, we follow the layer of defense or defense in depth
paradigm and reduce the system risk.
Correct
Correct. Each method of defense deals with different stage of attacks.
Detection is an often deployed method of defense.
Honeypot is considered as a method of deterrence.
Recover is an important method of defense. Fast recovery from disasters increase the availability of the
system.
You didn’t select all the correct answers
7. 0.5 / 1 point
Security controls are the
safeguards or countermeasures prescribed for an information system to protect
the confidentiality, integrity, and availability of the system and its
information.
NIST 800-18 defines a list of security controls.
Awareness
and Training is listed as one of the top security controls in NIST 800-53.
Access control is listed as one of the top security controls in NIST 800-53.
Audit
and accountability is listed as one of the top security controls in NIST 800-53.
Correct
Correct. It is a critical one. Audit
and accountability can be used to reveal insider attacks and external
intrusion.
You didn’t select all the correct answers
8. Risk Management Framework (RMF) is the unified information security framework for the entire federal 0 / 1 point
government that is replacing the legacy Certification and Accreditation (C&A) processes within federal
government departments and agencies, the Department of Defense (DOD) and the Intelligence Community (IC).
RMF has six steps. The first is to categorize information system and assessing the related risks.
Step
5 of RMF is to authorize the use of security control
in Information system.
Correct
Correct. This is done after the security control mechanisms are carefully assessed.
Second step of RMF deal with implementing the security control
After we authorized the use of security control of information system, we just left it run without monitoring.
You didn’t select all the correct answers
9. Security principles are collections 0 / 1 point
of
desirable system
properties,
behaviors, designs and implementation practices that can reduce the risk. Follow these principles, we
can beware
of threats to
our
system and ultimately
derive a set of protection requirements.
Currently most of the computer processing unit are using same mono instruction set architecture (ISA).
Hackers developed a malware can exploit device using the same x8t6/64 instruction set archiecture. The
defend in depth security principle can be deployed to remedy this.
The most often cited security principles is defense in depth. It provide layered security mechansims to
increase security of the system as a whole.
Correct
Correct. If an attack causes one security mechanism to fail, other mechanisms may still provide the
necessary security to protect the system.
In insider attack, the first line of defense is to perform regular audit.
To defend the network & infrastructure, we need first line defense to protect the local area network and
wide area network from DDoS attacks, as a second line of defense, we provide
confidentiality and integrity protection for data transmitted over networks to
resist passive monitoring.
You didn’t select all the correct answers
10. Cyber Resilience is a new security principle where we design systems to support the functions necessary for 0.3333333333333333
mission success in spite of hostile action or adverse conditions. / 1 point
The constrain, reconstitute, transform, and re-architecture are the new cyber resilience techniques
proposed.
The cyber resilience adds anticipate, withstand (to deal with hostile attacks), evolve to adapt to the
new hostile and degraded system
condition.
The new cyber resilience objectives such as coordinate
defense, Deception , diversity, Dynamic
positioning, realignment, unpredictability are added.
This should not be selected
Incorrect. They are new cyber resilience techniques, not objectives.
11. 0.6666666666666666
What is proper control on the vulnerabilities in the case of Taiwan First Bank ATM Heist? / 1 point
Install a firewall device that blocks traffic to ATM machines except from authorized servers.
Require users to present another credential, i.e., multi-factor authentication
A sound security policy "Patches must be verified and can only be
download from specific authorized servers" with proper enforcement.
Correct
Correct. If this security policy is properly enforced, the hacker will not be able to download the malicious
software
You didn’t select all the correct answers
12. 0.5 / 1 point
What are Known DDoS Facts?
Only small number of IoT devices are compromised and use as Botnet devices for DDoS attacks.
Not just Government (White House), big companies (Sony) got attacked, small and medium size companies
got attacked too.
Correct
Correct. Based on UCSD report, those small and medium
size companies got DDoS attacks too. But compared with large
organization, they donot have enough IT or dedicated person to handle
such DDoS incidence response. Therefore they suffer longer.
Murai botnet does not require those lease their botnet to install DDoS software to
launch the attacks.
Murai botnet web site advertised 50k IoT bots for $4600.
You didn’t select all the correct answers
13. 0.75 / 1 point
What are differences between Integrity and Authenticity?
Authenticity deals with verifying the documents are from specific authors
Correct
Correct. It deals with including additional
information such as signed hash of a document where the hash of the
document is signed with the private key of the author.
To verify the signed hash in a secure email, we just extract the public
key from attached sender certificate to decrypt the signed hash without
having to verify integrity of the attached sender certificate.
An email is received with its message digest attached. If the message
digest we compute from the email content is the same as those attached,
it means the email was not modified after it was sent.
Integrity deals with making sure the documents are not modified un-authorized person.
You didn’t select all the correct answers
14. 0 / 1 point
How do we efficiently defend against DDoS attack?
Duplicate our servers on different regions of a public cloud or multi-cloud.
Trace back or push back the DDoS attacks by contacting FBI or our ISP
Utilize multi-homing or proxy-based indirect routes
Incorrect
Incorrect. The multi-homing gateways or the wide area proxy servers are subjected to further attacks.
15. What factors are included in the method for a cyber attack? 1 / 1 point
The skill, knowledge, tools and other things with which to be able to pull off the attack
The reason a hacker/cracker to want to perform the cyber attack against this syste.
The time and access to accomplish attack.
Correct
Correct.
16. Why MOM is useful in security analysis? 1 / 1 point
It is just an eye-catching term no special meaning.
They are the important factors of an attack.
It focuses solely on the vulnerabilities of the victim of an attack.
Correct
Correct. By denying any of these factors the attacks will not occur.
17. In Taiwan First Bank ATM Heist case, what are the MOM factors? 0.3333333333333333
/ 1 point
The ATM machines and First Bank servers are connected and can be accessed through Internet easily
Correct
Correct. The hacker first compromised the First Bank Answering server in its London branch and then use
it to access the ATM machines in Taipei that are vulnerable.
The ATM machines of this bank in Taipei city contains large volume of cashes for their customers even at
night.
First Bank uses the same vulnerable ATM software which the hacker has exploit before.
You didn’t select all the correct answers
18. In Taiwan First Bank ATM Heist case, what are the MOM factors caused the robbers got caught? Hint. From defense 1 / 1 point
point of view.
The robber thinks no body will witness the peculiar money drawn at night.
The citizen/taxi drives do not care about the behavior of their passenger.
It is difficult to launder money, or carry such a large lump sum of money through airport.
Correct
Correct. This is the method factors that was not carefully consider. Taiwan is an island. Not easy to get in
and out.
19. In case study: Taiwan First Bank ATM Heist 7/2016. What are the main threats? Related Story: 0 / 1 point
First Bank in Taiwan 7/2016.http://www.reuters.com/article/us-taiwan-banks-theft-idUSKCN0ZX0N7
The security policy may not be restrictive enough to limit where the software updates come from.
ATM machine does not verify the integrity of the software patch or the identity of download server.
Hackers from East Europe.
Incorrect
Incorrect. That is one of vulnerabilities, not threat. The threat comes from Hackers that break in to the
First Bank's London Server and utilize the vulnerability of the ATM system to replace with their malware to
spit out cashes in the compromised ATM machines on their demand.
20. In 2016 Russian hack of Clinton Campaign incidence, the main vulnerability is 0.75 / 1 point
Related story:
https://www.nytimes.com/2016/12/13/us/politics/russia-hack-election-dnc.html?_r=0
DNC server contains valuable political emails.
The DNC server was not secure and was compromised earlier 2015
Correct
Correct. DNS servers was compromised and detected by FBI for sending emails to Russian. Security policy
does/may not exist for urgently following up FBI alerts or their enforcement procedures were not strictly
followed.
Super cyber attack skill of Russian hackers Fancy Bear and Cozy Bear
The staff of Mr. Podesta (Clintons Campaign Chairman) believe the emails from gmail to him were legitimate
and change the password accordingly.
You didn’t select all the correct answers
21. As a receiver, why do we need to compute the hash of received signed document ourselves and then compare that 1 / 1 point
with decrypted signed hash?
This is to prevent a hacker from change part of the content.
This is to ensure no message collision.
This is just to make the computation longer to convince the receiver the crypto library program has done a
lot of work.
Correct
Correct. For example, a hacker can just change the public key or subject field of a certificate without
changing the signed hash of the certificate. If we just verify that the signed hash can be decrypted by the
public key of sender, we may accept altered content.
22. How we can strengthen the authentication of users in the login process? 0.75 / 1 point
Require the use of multi-factor authentication
Correct
Correct. Requiring more that one means of identifications is an excellent approach for authentication.
****
Ask the user to send in their private key.
Ask the user to present their public key.
Require the user to use stronger password.
You didn’t select all the correct answers
23. Which of the following are methods of defense that deal with risks? 0.6666666666666666
/ 1 point
Recover
Correct
Correct. After the system being hacked, use contingent/disaster recovery plan to restore system or
mitigate the damages.
Deflect
Deter
Obfuscate
Detect
Correct
Correct. Use IDS to provide early detection of intrusion. Give response team longer time to act or call for
help.
Prevent
Correct
Correct. Preemption and External deference are corresponding external prevention and internal
prevention. Reducing the number of network ports/services (attack surface) belongs to such a method.
You didn’t select all the correct answers
24. What are the steps of RMF? 1 / 1 point
Select the Security Control to reduce the vulnerabilities and threats.
Correct
Correct.
Implement the selected security controls
Correct
Correct.
Authorize the use of security control in Information system
Correct
Correct. Really turn in on.
Assess the effectiveness the security controls.
Correct
Correct.
Continuously monitor the security state of the system.
Correct
Correct.
Categorize information system
Correct
Correct.
25. Which of the following are part of the Security Control Family of document? 0.5 / 1 point
Auditing and Accountability is one of the important security control listed in NIST 800-53.
Correct
Correct.
Access Control is one of the Security Control listed in NIST 800-53
NIST special publication 800-30 deals with Security Control Families
Configuration Management is one of the important security control listed in NIST 800-53.
You didn’t select all the correct answers
26. What is the first line of defense for insider attacks? 0 / 1 point
The first line of defense for insider attacks is Authenticated Access Control and Audit
The first line of defense for insider attacks is Physical and Personnel Security
Incorrect
Incorrect. This is 2nd line of defense for insider attacks.
27. What is Defense With Diversity? 0.75 / 1 point
We should encourage the development of diverse system architecture, OS', crucial libraries/software
packages, and programming languges.
Correct
Systems with dynamic changing ISA exist but incur 100% performance degradation
Mono instruction architectures, such as Intel x86/64, make it easier for attackers to develop one malicious
software to attack vulnerabilities in all systems with the same architecture.
Framework for allowing real-time seamless service/app migration from one system to another remote
system is too difficult. So do not try it.
You didn’t select all the correct answers
28. What are Cyber Resilience Facts? 0 / 1 point
An architecture is more resilient if it can provide these functions with higher probability, shorter periods of
reduced capability, and across a wider range of scenarios, conditions and threats.
Resilience may leverage cross-domain or alternative government, commercial, or international capabilities
The cyber resilience objectives include Transform, Reconstitute, and Re-Architect.
It is the same concept of fault tolerance and high available systems
This should not be selected
Incorrect. It introduces the new concepts of performing while being attacks. Fault tolerance and high
availability deal with more benigh system component failure. Cyber resilience deals with adversary and
tenacious attacks after system components compromised.
You might also like
- EJPTv2 Exam ReviewDocument11 pagesEJPTv2 Exam Reviewtanjidhasan0077No ratings yet
- Final Exam AnswersDocument27 pagesFinal Exam AnswersWaktole GenatiNo ratings yet
- IBM Security Verify Privilege Level 2 Quiz Attempt ReviewDocument9 pagesIBM Security Verify Privilege Level 2 Quiz Attempt ReviewBBMNo ratings yet
- Lesson Plan - Day 1.Document4 pagesLesson Plan - Day 1.Jocelyn Baculi AutenticoNo ratings yet
- Basic Signal CommunicationDocument3 pagesBasic Signal Communicationhumanupgrade100% (3)
- QuizDocument6 pagesQuizJames PodlewskiNo ratings yet
- AU5800 Online Specification For Version 5.0 or LaterDocument61 pagesAU5800 Online Specification For Version 5.0 or LaterRubi Kauneus MørkeNo ratings yet
- Huawei DWDM SDHDocument31 pagesHuawei DWDM SDHKevin SalvatierraNo ratings yet
- Week 1 Quiz - CourseraDocument1 pageWeek 1 Quiz - CourseraSarang PotdarNo ratings yet
- IBM Security Verify Access Level 2 Quiz Attempt Review PDFDocument10 pagesIBM Security Verify Access Level 2 Quiz Attempt Review PDFJustice MapangaNo ratings yet
- 11.1 Class Tasks Suggested AnswersDocument6 pages11.1 Class Tasks Suggested Answersgemote6096No ratings yet
- Final Exam - Evaluación Final - Cybersecurity EssentialsDocument32 pagesFinal Exam - Evaluación Final - Cybersecurity EssentialsVicente Romero46% (50)
- Module Quiz - Interactive CSS - CourseraDocument1 pageModule Quiz - Interactive CSS - CourseraRopTox YTNo ratings yet
- Chapter 7 Quiz - Attempt Review-22 PDFDocument1 pageChapter 7 Quiz - Attempt Review-22 PDFShaharyar AhmedNo ratings yet
- Post-Quiz: Attempt ReviewDocument3 pagesPost-Quiz: Attempt ReviewNikhil SahlotNo ratings yet
- Post-Quiz: Attempt ReviewDocument3 pagesPost-Quiz: Attempt ReviewNikhil SahlotNo ratings yet
- ECCU 501 Syllabus 2021Document12 pagesECCU 501 Syllabus 2021hatfiodNo ratings yet
- Syllabus PCLU FE 1Document4 pagesSyllabus PCLU FE 1Maestro CabadoNo ratings yet
- Cyber Security - A Promising PathDocument12 pagesCyber Security - A Promising PathVinnySha SelvarajahNo ratings yet
- Chapter 1 Quiz - Cybersecurity EssentialsDocument8 pagesChapter 1 Quiz - Cybersecurity EssentialsbmkvsrNo ratings yet
- Chapter 4 Quiz - Evidence7 PC4.1-PC4.4 Attempt ReviewDocument1 pageChapter 4 Quiz - Evidence7 PC4.1-PC4.4 Attempt ReviewKhaled Al AliNo ratings yet
- Info Assurance Security Syll 2 2022-2023Document7 pagesInfo Assurance Security Syll 2 2022-2023beverly arevaloNo ratings yet
- CEHDocument5 pagesCEHanil0% (1)
- Key Concepts On Deep Neural Networks - CourseraDocument1 pageKey Concepts On Deep Neural Networks - CourseracgchydtrainingNo ratings yet
- Quiz 5 - CS690 A1 Network ..Document7 pagesQuiz 5 - CS690 A1 Network ..Nishant KawaNo ratings yet
- Lesson Plan - Day 1.Document4 pagesLesson Plan - Day 1.Jocelyn Baculi AutenticoNo ratings yet
- Chapter 1 Quiz - Cybersecurity Essentials - EN 0118Document7 pagesChapter 1 Quiz - Cybersecurity Essentials - EN 0118Jenny Marcela Perez BolivarNo ratings yet
- Final Quiz PDFDocument37 pagesFinal Quiz PDFB.Deepak CR7No ratings yet
- Case 3 - An Organization That Wanted To Secure Acce...Document4 pagesCase 3 - An Organization That Wanted To Secure Acce...Muhammad FrazNo ratings yet
- Final Quiz - Cybersecurity Essentials - en 0118Document32 pagesFinal Quiz - Cybersecurity Essentials - en 0118Zulkipli0% (2)
- Ungraded Test On Modules 1 and 2Document7 pagesUngraded Test On Modules 1 and 2Hanzhi -No ratings yet
- Background/Overview: Student Name: Tetyana Hyde Student ID: E0972688Document21 pagesBackground/Overview: Student Name: Tetyana Hyde Student ID: E0972688tetyanaNo ratings yet
- CyberOps Associate (Version 1.0) - FINAL Exam (Answers)Document90 pagesCyberOps Associate (Version 1.0) - FINAL Exam (Answers)coba yudNo ratings yet
- Important Instructions To Examiners:: What Is Computer Security & Its Need?Document40 pagesImportant Instructions To Examiners:: What Is Computer Security & Its Need?Gaurang NakumNo ratings yet
- Risk Based Test PlanningDocument1 pageRisk Based Test PlanningPatriciaGarcesNo ratings yet
- Career Path Syllabus - Cyber Security EngineerDocument3 pagesCareer Path Syllabus - Cyber Security EngineerKhushiNo ratings yet
- Take Test: Vulnerability Scanning, Ethics, Privacy, and The ...Document4 pagesTake Test: Vulnerability Scanning, Ethics, Privacy, and The ...Suman ShahNo ratings yet
- Lesson Plan - TemplateDocument3 pagesLesson Plan - Template303906No ratings yet
- EHF M01 C01 PPT IntroductionDocument37 pagesEHF M01 C01 PPT IntroductionDÀRK么SØUŁ GAMINGNo ratings yet
- Kaspersky Security Awareness Datasheet GAT 0322 ENDocument6 pagesKaspersky Security Awareness Datasheet GAT 0322 ENghNo ratings yet
- Career Path Syllabus - Penetration TesterDocument2 pagesCareer Path Syllabus - Penetration TesterjansonhushNo ratings yet
- EX FINAL 2 - IBM Cybersecurity Analyst Professional Certificate Assessment Exam - CourseraDocument33 pagesEX FINAL 2 - IBM Cybersecurity Analyst Professional Certificate Assessment Exam - CourseraPaul Bances SeverinoNo ratings yet
- 2020 11 16 TVET Trades Session3Document27 pages2020 11 16 TVET Trades Session3Santosh KatkarNo ratings yet
- Expert Veri Ed, Online, Free.: Custom View SettingsDocument2 pagesExpert Veri Ed, Online, Free.: Custom View SettingsxaninNo ratings yet
- Lecture0 Into IsrafilDocument6 pagesLecture0 Into IsrafilVictor ImehNo ratings yet
- Analysis of Superstructure Using Midas CivilDocument21 pagesAnalysis of Superstructure Using Midas CivilBadri NathNo ratings yet
- 50 Cyber Security Interview Question & Answers For Sure Shot Success - Networking and SecurityDocument34 pages50 Cyber Security Interview Question & Answers For Sure Shot Success - Networking and SecurityC GNo ratings yet
- CPTE CourseDocument11 pagesCPTE CourseGudden GuptaNo ratings yet
- Iot Security 1.1 Chapter 6 Quiz: Attempt HistoryDocument11 pagesIot Security 1.1 Chapter 6 Quiz: Attempt HistoryJaime QuishpeNo ratings yet
- Chapter 8 Quiz - Attempt Review-2 PDFDocument1 pageChapter 8 Quiz - Attempt Review-2 PDFShaharyar AhmedNo ratings yet
- Cloud Tech Associate Advanced Email Security 2022Document79 pagesCloud Tech Associate Advanced Email Security 2022Juntos PodCastNo ratings yet
- Module 4 QuizDocument1 pageModule 4 QuizNasar KhanNo ratings yet
- Final Quiz - Ui Cybersecurityessen CV 9no Sis 2018 2019Document28 pagesFinal Quiz - Ui Cybersecurityessen CV 9no Sis 2018 2019Juan Carlos Carrillo50% (4)
- Module 4 QuizDocument1 pageModule 4 QuizNasar KhanNo ratings yet
- Information Assurance and Security Prelim ExamDocument14 pagesInformation Assurance and Security Prelim ExamAwan LangNo ratings yet
- Io Midterm ReviewerDocument5 pagesIo Midterm ReviewerMargarita Dave MendozaNo ratings yet
- QuizChapter 1Document6 pagesQuizChapter 1Yoga SaputraNo ratings yet
- Study Plan Cisco CCNA Security 210 260 IINSDocument8 pagesStudy Plan Cisco CCNA Security 210 260 IINSMr RCodeNo ratings yet
- Saint Leo University Introduction To Security Information COM-416 July 26, 2014Document7 pagesSaint Leo University Introduction To Security Information COM-416 July 26, 2014SaravananNo ratings yet
- PCNSE 10.1 Domain #1 - Planning and Core ConceptsDocument107 pagesPCNSE 10.1 Domain #1 - Planning and Core ConceptsFernala Sejmen-Banjac0% (1)
- MCTS Windows SharePoint Services 3.0 Configuration Study Guide: Exam 70-631From EverandMCTS Windows SharePoint Services 3.0 Configuration Study Guide: Exam 70-631No ratings yet
- CISA Exam-Testing Concept-Knowledge of Logical Access ControlFrom EverandCISA Exam-Testing Concept-Knowledge of Logical Access ControlRating: 2.5 out of 5 stars2.5/5 (3)
- Hassdac 720p SystemDocument4 pagesHassdac 720p SystemNeelam sihagNo ratings yet
- Page 1Document6 pagesPage 1langbotNo ratings yet
- 300-135 Exam Dumps With PDF and VCE Download (21-40)Document32 pages300-135 Exam Dumps With PDF and VCE Download (21-40)Metuzalem De Oliveira ZalemNo ratings yet
- MME Technical OverviewDocument568 pagesMME Technical OverviewAndreea TrenteaNo ratings yet
- 4CAE000433 XMC22 XMC23 XMC25 EnglishDocument3 pages4CAE000433 XMC22 XMC23 XMC25 Englishmarija.bandic1No ratings yet
- Vmware Validated Design 20 Introduction GuideDocument30 pagesVmware Validated Design 20 Introduction GuideninodjukicNo ratings yet
- Cambium Networks PMP 450 Subscriber Module SpecificationDocument2 pagesCambium Networks PMP 450 Subscriber Module SpecificationthenioNo ratings yet
- Cisco Voip/Ccme: Introduction To Cisco Unified Communication Manager Express (Callmanager Express - Cme)Document28 pagesCisco Voip/Ccme: Introduction To Cisco Unified Communication Manager Express (Callmanager Express - Cme)Ministere EdificeNo ratings yet
- MOP Integration and Protocol Activation 7705 at LPG-TLS-EN1-SAR8 v1.1Document25 pagesMOP Integration and Protocol Activation 7705 at LPG-TLS-EN1-SAR8 v1.1Diksi KalisNo ratings yet
- TOPFLYtech Product - April 2023 - 4GDocument56 pagesTOPFLYtech Product - April 2023 - 4GmosorioNo ratings yet
- Usw E48pDocument3 pagesUsw E48pMohamed Shaffaf Ali RasheedNo ratings yet
- Multiple Access Techniques For 5G Wireless Networks and Beyond PDFDocument692 pagesMultiple Access Techniques For 5G Wireless Networks and Beyond PDFTarek GARANo ratings yet
- ILS (Glide Path) - System Part Training BookDocument25 pagesILS (Glide Path) - System Part Training BookChiranjivi KuthumiNo ratings yet
- FortiOS 7.0 PortsDocument6 pagesFortiOS 7.0 Portsvedant vedNo ratings yet
- Dell Storage Center SC4020 Storage System OwnerManualDocument41 pagesDell Storage Center SC4020 Storage System OwnerManualfarrukh_meNo ratings yet
- CCIE V5.0 LAB小凡实验室-H1Document40 pagesCCIE V5.0 LAB小凡实验室-H1Song XiuheNo ratings yet
- Ken HollaydayDocument3 pagesKen HollaydaySonia ElouedNo ratings yet
- GSM Repair / Maint Policy-Telecom / Allied EqptDocument9 pagesGSM Repair / Maint Policy-Telecom / Allied EqptImran AzizNo ratings yet
- Skip To ContentDocument18 pagesSkip To ContentFikru TesefayeNo ratings yet
- 5G Mficd: Supported RF Trace MessagesDocument7 pages5G Mficd: Supported RF Trace MessagesJózsef HoffmannNo ratings yet
- Experiment No. 01 Experiment Name-ASK ModulationDocument47 pagesExperiment No. 01 Experiment Name-ASK ModulationmuskanNo ratings yet
- V6.4.0 Technical Update: SAN Volume Controller and Storwize V7000Document58 pagesV6.4.0 Technical Update: SAN Volume Controller and Storwize V7000ecorradiNo ratings yet
- ERD97P21-U Receiver: Product SpecificationDocument2 pagesERD97P21-U Receiver: Product SpecificationSakerhetsNo ratings yet
- MDE-4820H 8 Port Commverter Operation and Installation ManualDocument129 pagesMDE-4820H 8 Port Commverter Operation and Installation ManualJ LUIS AGUILARNo ratings yet
- Amphenol CATV ConnectorsDocument28 pagesAmphenol CATV ConnectorsCARLOSNo ratings yet
- Chapter 8-Fault ToleranceDocument30 pagesChapter 8-Fault ToleranceMohamedsultan AwolNo ratings yet
- WIMAX Throughput CalculationDocument3 pagesWIMAX Throughput Calculationarzaman100% (1)