Professional Documents
Culture Documents
402 Information Tech MS
402 Information Tech MS
Uploaded by
eeshaanbehera2008Original Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
402 Information Tech MS
402 Information Tech MS
Uploaded by
eeshaanbehera2008Copyright:
Available Formats
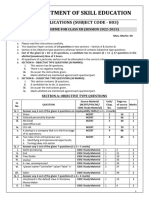
CBSE | DEPARTMENT OF SKILL EDUCATION
INFORMATION TECHNOLOGY (SUBJECT CODE - 402)
MARKING SCHEME FOR CLASS X (SESSION 2023-2024)
Max. Time: 2 Hours Max. Marks: 50
General Instructions:
1. Please read the instructions carefully.
2. This Question Paper consists of 21 questions in two sections – Section A & Section B.
3. Section A has Objective type questions whereas Section B contains Subjective type questions.
4. Out of the given (5 + 16 =) 21 questions, a candidate has to answer (5 + 10 =) 15 questions in the
allotted (maximum) time of 2 hours.
5. All questions of a particular section must be attempted in the correct order.
6. SECTION A - OBJECTIVE TYPE QUESTIONS (24 MARKS):
i. This section has 05 questions.
ii. There is no negative marking.
iii. Do as per the instructions given.
iv. Marks allotted are mentioned against each question/part.
7. SECTION B – SUBJECTIVE TYPE QUESTIONS (26 MARKS):
i. This section contains 16 questions.
ii. A candidate has to do 10 questions.
iii. Do as per the instructions given.
iv. Marks allotted are mentioned against each question/part.
SECTION A: OBJECTIVE TYPE QUESTIONS
Page
Source Material
no. of
Q. (NCERT/PSSCIVE/
QUESTION Unit/ Chap. No. source Marks
No. CBSE Study
materia
Material)
l
Q. 1 Answer any 4 out of the given 6 questions on Employability Skills (1 x 4 = 4 marks)
i. b. Interpersonal Barrier NCERT Communication Pg-72 1
Skills
ii. b. Ishan : Install reliable antivirus NCERT Unit 3 Pg-77 1
software and update
iii. b. Stress Management NCERT Unit-2 Self- Pg-42 1
Management
Skills
iv. c. Mental NCERT Unit-2 Self- Pg-17 1
Management
Skills
v. d. All of these Employability Study Entrepreneurial Pg-55 1
Material Skills
vi. c. United Nations NCERT Green Skills Pg-63 1
Q. 2 Answer any 5 out of the given 6 questions (1 x 5 = 5 marks)
i. d. Row CBSE Study Material Unit 1 Session 4 Pg – 30 1
ii. a. Black CBSE Study Material Unit 1 Session 4 Pg – 17 1
402 – Information Technology – Class X Page 1 of 6
iii. a. Wraptaext CBSE Study Material Unit 1 Pg - 13 1
iv. a. Data source CBSE Study Material Unit 1 Session 5 Pg – 41 1
v. b. Sharpen CBSE Study Material Unit 4 Session 2 Pg – 172 1
vi. b. DSL CBSE Study Material 1
Q. 3 Answer any 5 out of the given 6 questions (1 x 5 = 5 marks)
i. b. Scenario CBSE Study Material Unit 1 Pg - 17 1
ii. b. Linksheet CBSE Study Material Unit 2 Session 2 Pg - 74 1
iii. c. Solver CBSE Study Material Unit 2 Session 1 Pg – 1
67,68
iv. a. Sheet tab CBSE Study Material Unit 2 session 2 Pg - 72 1
v. b. Sharpen CBSE Study Material Unit 1 Session 2 Pg - 13 1
vi. b. Comparing CBSE Study Material Unit 2 Pg -94 1
Q. 4 Answer any 5 out of the given 6 questions (1 x 5 = 5 marks)
i. c. Form CBSE Study Material Unit 3 Pg - 155 1
ii. b. 3 CBSE Study Material Unit 3 Pg – 1
135
iii. c. SQL CBSE Study Material Unit 2 Pg - 72 1
iv. b. Varchar CBSE Study Material Unit 3 Pg - 124 1
v. d. F5 CBSE Study Material Unit 3 Session 4 Pg - 143 1
vi. a. 1 CBSE Study Material Unit 3 Pg - 113 1
Q. 5 Answer any 5 out of the given 6 questions (1 x 5 = 5 marks)
i. c. Serial CBSE Study Material Unit 4 Session 1 Pg - 168 1
ii. a. Blog CBSE Study Material Unit 4 Session 5 Pg - 183 1
iii. c. Google CBSE Study Material Unit 4 Pg - 177 1
iv. b. 14Hd{]$_Sb10 CBSE Study Material Unit 4 Session 5 Pg - 184 1
v. a. LAN CBSE Study Material Unit 4 Session 2 Pg - 170 1
vi. b. IP Protcol CBSE Study Material Unit 4 Pg - 170 1
Session 11
SECTION B: SUBJECTIVE TYPE QUESTIONS
Source
Page
Material
Unit/ no. of
Q. (NCERT/
QUESTION Chap. source Marks
No. PSSCIVE/
No. materia
CBSE Study
l
Material)
Answer any 3 out of the given 5 questions on Employability Skills in 20 – 30 words each (2 x 3 = 6 marks)
Q. 6 Learning objectives of Effective communication are : Employabilit Chap. Pg – 1,2 2
1. Sending, receiving and understanding y Study No. 1
the message or information Material
2. Development of Interposal Skills
3. To express effectively with maximum efficiency
Q. 7 The smartest and most successful people welcome NCERT Chap. Pg - 13 2
new ideas and diverse perspectives, allowing them No. 1
to see more opportunities ahead of them and better
solutions to problems. Open-minded entrepreneurs
are able to strategize better because they can listen
to varying and look at a problem through multiple
lenses.
402 – Information Technology – Class X Page 2 of 6
Q. 8 The ability to work independently can be enhanced NCERT Unit 2 Pg - 43 2
by being self-regulated. Self-regulation guides
independent individuals as it help them to consider
long term consequences rather than just transient
feelings. It leads to a responsible and a value driven
behavior. It teaches self-control and well-directed
efforts to reach the goal. Self-regulated includes
discipline that helps in consistent efforts to move
towards the goal.
Q. 9 We can prevent the computer against attack of NCERT Unit 3 Pg - 81 2
viruses by installing proper antivirus, enabling the
firewall, scan external devices before using on other
computer, by avoiding emails that are suspicious or
not known to us, should be very careful while
downloading files or any programs from the internet
etc.
Q. 10 The focus of green growth strategies is ensuring that STUDY Entrepre Pg – 63 2
natural assets can deliver their full economic MATERIAL -
potential on a sustainable basis. That potential neurship
includes the provision of critical life support services Skills
– clean air and water, and the resilient biodiversity
needed to support food production and human
health.
Answer any 4 out of the given 6 questions in 20 – 30 words each (2 x 4 = 8 marks)
Q. 11 Anchoring refers to the reference point for the CBSE Study Unit 1 Pg-21 2
graphics. This point could be the page, or frame Material Session 2
where the object is, paragraph, or even a character.
An image always has an anchor point.
(Answer in Libre Office and Open Office both are
acceptable.)
Q. 12 Sorting is the process of arranging data into CBSE Study Unit 2 Pg-104 2
meaningful order so that you can analyze it more Material Session 4
effectively. For example , you might want to arrange
sales data by calendar month so that you can
produce a graph of sales performance.
(Answer in Libre Office and Open Office both are
acceptable.)
Q. 13 The etiquettes to be followed while chatting on the CBSE Study Unit 3 Pg-130 2
internet are : Material Session 3
i. Message should be short and to the point.
ii. Always introduce yourself by name if your screen
name doesn’t reflect it.
iii. Always ask if the other person has time to chat
first, regardless of how important you think what
you have to say is, it’s not going to be well received
if the recipient is busy.
Q. 14 Goal seek determines what values needs to be input CBSE Study Unit 2 Pg-66 2
in a cell to achieve the described result in a formula Material Session 1
402 – Information Technology – Class X Page 3 of 6
cell as it allows varying the value for one cell
whereas
Solver can solve equations that uses several
variables, so it can be used to determine what
values need to be entered in multiple-input cells to
achieve the described result.
Q. 15 A primary key is a unique value that identifies a row CBSE Study Unit 3 Pg-113 2
in a table, whereas a foreign key identifies a column Material Session 1
or set of columns in one (referencing) table that
refers to a column or set of column in another
(referenced. table. A table can have only Primary
Key but a table can have multiple foreign keys.
Q. 16 A healthy lifestyle helps to keep and improve NCERT Unit 4 Pg-211 2
people’s health and well-being. A healthy lifestyle Session
includes : 11
i. Healthy eating habits.
ii. Physical activities.
iii. Stress management
v. Sound sleep
vi.
Answer any 3 out of the given 5 questions in 50– 80 words each (4 x 3 = 12 marks)
Q. 17 The table of contents is a snapshot of the headings CBSE Study Unit 1 Pg-21 4
and page numbers in your document and does not Material Session 2
automatically updates itself as you make changes. It
acts as a map for the users.
A good table of content has the following
characteristics:
• It should be easy to read and simple to use.
• It should be organised and formatted
properly.
• It must be accurate and easily accessible.
• It should be given after the title and copyright
page.
(Answer in Libre Office and Open Office both are
acceptable.)
Q. 18 Scenarios are a tool to test “What-if” questions. CBSE Study Unit 2 Pg-65 4
Each scenario is names and can be edited and Material Session 1
formatted separately. When you print the
spreadsheet, only the content of the currently active
scenario is printed. A scenario is essentially a saved
set of cell values for your calculations. You can easily
switch between these sets using the navigator or a
drop-down list which can be shown beside the
changing cells. For example, if you wanted to
calculate the effect of different interest rates on
investment, you could add a scenario for each
interest rate and quickly view the results. Formulas
that rely on the values changed by your scenario are
updated when the scenario is opened. If all your
402 – Information Technology – Class X Page 4 of 6
sources of income used scenarios, you could
efficiently build a complex model of your possible
income.
Q. 19 There are different kinds of online threads: CBSE Study Unit 4 Pg-195 4
i. Phishing: Phishing attacks use fack Material Session 8
communication, such as an email, to trick the
receiver into opening it and carrying out the
instructions inside, such as providing a credit card
number.
ii. Malware: Malware is malicious software such as
spyware, ransomware, viruses, and worms.
Malware is activated when a user clicks on a
malicious link or attachment, which leads to
installing harmful software.
iii. Password Attacks: With the right password, a
cyber attacker has access to a wealth of
information. Social engineering is a type of
password attack that data insider defines as
“a strategy cyber attackers use that relies
heavily on human interaction and often
involves tricking people into breaking
standard security practices.”
iv. Email spoofing: It is the forgery of an email
header so that the message appears to have
originated from someone or somewhere other than
the actual source.
Q. 20 Referential Integrity is used to maintain the accuracy CBSE Study Unit 3 Pg-135 4
and consistency of data in a relationship. In Base, Material Session 3
data can be linked between two or more tables with
the help of primary key and foreign key constrains.
Referential Integrity is important in DBMS as:
• It prevents the entry of duplicate data.
• It prevents one table from pointing to a
nonexistent field in another table.
• It prevents consistency between “Partnered”
tables.
• It prevents the deletion of a record that
contains a value referred to by a foreign key
in another table.
• It prevents the addition of a record to a table
that contains a foreign key unless key unless
there is primary key in the linked table.
402 – Information Technology – Class X Page 5 of 6
Q. 21 i. Select*from Datesheet order by DateofExam CBSE Study Unit 3 Pg - 142 4
Material Session 4
ii. Select*from Datesheet
iii. Select Sub_Name, DateofExam from Datesheet
where Days= ‘Monday’
iv. Select Sub_Name, Date of Exam from Datesheet
where Sub_Name = ‘Science’
For visually impaired candidates.
i) A database management system is a software package CBSE Study Unit 3 Pg - 108
with computer programs that controls the creation, Material Session 1
maintenance, and use of a database. It allows
organizations to conveniently develop databases for
various applications. A database is an integrated
collection of data records, files, and other objects. A
DBMS allows different user application programs to
concurrently access the same database. Well known
DBMSs include Oracle, IBM DB2, Microsoft SQL Server,
Microsoft Access, PostgreSQL, MySQL, FoxPro, and
SQLite.
ii) Database servers are dedicated computers that hold CBSE Study Unit 3 Pg –
the actual databases and run only the DBMS and related Material Session 1 109
software. Typically databases available on the database
servers are accessed through command line or graphic
user interface tools referred to as Frontends; database
servers are referred to as Back-ends. Such type of data
access is referred to as a client-server model.
iii) Data integrity means that the data is accurate and CBSE Study Unit 1
consistent in the database. Data Integrity is very Material Session 3 Pg - 109
important as there are multiple databases in a DBMS. All
of these databases contain data that is visible to multiple
users.
iv) A record is a set of information (made up of fields) CBSE Study Unit 1
stored in your database about one of the items. Material Session 3 Pg - 110
402 – Information Technology – Class X Page 6 of 6
You might also like
- 402 Information Tech MSDocument7 pages402 Information Tech MSaltxd1313No ratings yet
- 402 Information Tech MSDocument7 pages402 Information Tech MSKomalNo ratings yet
- 802 - Information - Technology - MS (2) - 231223 - 090825Document7 pages802 - Information - Technology - MS (2) - 231223 - 090825manmarvellous1337No ratings yet
- 802 Information Technology MsDocument6 pages802 Information Technology MsPradeep R SNo ratings yet
- 802 Information Technology MsDocument6 pages802 Information Technology MsMannatdeep Kaur ToorNo ratings yet
- 802 - Information - Technology - MS (3) - 231223 - 091112Document7 pages802 - Information - Technology - MS (3) - 231223 - 091112manmarvellous1337No ratings yet
- 803 - Web - Application - MS 22-23Document4 pages803 - Web - Application - MS 22-23Hridish GoswamiNo ratings yet
- 819 Electrical Technology MSDocument9 pages819 Electrical Technology MSfunwanderersNo ratings yet
- 812 Marketing MsDocument12 pages812 Marketing MsHiten ChaudharyNo ratings yet
- 843 Ai MSDocument5 pages843 Ai MSHitarth ShahNo ratings yet
- 412 Marketing Sales MSDocument12 pages412 Marketing Sales MSrp278706No ratings yet
- Class X - Media - Ms QP, 23-24Document5 pagesClass X - Media - Ms QP, 23-24srishtiNo ratings yet
- 405 Introduction Financial Markets MSDocument9 pages405 Introduction Financial Markets MSVidhit VermaNo ratings yet
- 809 - FOOD - PRODUCTION - MS 12thDocument8 pages809 - FOOD - PRODUCTION - MS 12thpallavijoshivisNo ratings yet
- 835 Mass Media Studies MSDocument7 pages835 Mass Media Studies MSsndschoolmedia.dptNo ratings yet
- 808 Agriculture MSDocument15 pages808 Agriculture MSnavresi97No ratings yet
- 409 - FOOD - PRODUCTION - MS 10thDocument7 pages409 - FOOD - PRODUCTION - MS 10thpallavijoshivisNo ratings yet
- 807 Beauty Wellness SQP MSDocument16 pages807 Beauty Wellness SQP MSnirmalabehera8No ratings yet
- 805 Financial Market Management MSDocument8 pages805 Financial Market Management MSanshrathoreanshrathore5No ratings yet
- Ans Q1Document5 pagesAns Q1MOHAMMED RASHIDNo ratings yet
- UGC NET Management Exam 2021 - Teaching and Research Aptitude - Paper I & II - 10 Full-Length Mock Tests (Solved) - Latest Pattern Kit by EduGorilla - NodrmDocument329 pagesUGC NET Management Exam 2021 - Teaching and Research Aptitude - Paper I & II - 10 Full-Length Mock Tests (Solved) - Latest Pattern Kit by EduGorilla - NodrmRoshan SahuNo ratings yet
- 417 Ai MSDocument8 pages417 Ai MSSwarnajit SarkarNo ratings yet
- Assignment 10: Unit 12 - Week 10Document6 pagesAssignment 10: Unit 12 - Week 10reddy1984No ratings yet
- 418 Pat SQPDocument7 pages418 Pat SQPSameer SachdevaNo ratings yet
- DLL - MATHEMATICS-5 - Q1 - W1 FinalDocument7 pagesDLL - MATHEMATICS-5 - Q1 - W1 FinalFrancis Anthony EspesorNo ratings yet
- MObq 8 HT K8 F OJi KEcj BN LDocument13 pagesMObq 8 HT K8 F OJi KEcj BN LRohith Sivakumar0% (1)
- 803 Web Application SQPDocument8 pages803 Web Application SQPHardik NarangNo ratings yet
- CBSE - X Biology Phase - III Session Wise Q.P PatternDocument1 pageCBSE - X Biology Phase - III Session Wise Q.P PatterncopynvrmNo ratings yet
- DLL - Mathematics 5 - Q1 - W2Document8 pagesDLL - Mathematics 5 - Q1 - W2Luisa GarcillanNo ratings yet
- 11 A - Term 2 Assessment Date SheetDocument2 pages11 A - Term 2 Assessment Date SheetHarshith TNo ratings yet
- 809 Food Production SQPDocument9 pages809 Food Production SQPpallavijoshivisNo ratings yet
- English Core SrSec 2022-23Document8 pagesEnglish Core SrSec 2022-23Khuch BhiNo ratings yet
- Sample Paper AI 2notDocument16 pagesSample Paper AI 2notAmar AryanNo ratings yet
- 417 - AI - SQP Simpal PaperDocument8 pages417 - AI - SQP Simpal PaperAVN SchoolNo ratings yet
- Biology 2023 Set - 9Document14 pagesBiology 2023 Set - 9alizabeath9292No ratings yet
- Cbse - Department of Skill Education: Artificial Intelligence (Subject Code 417)Document9 pagesCbse - Department of Skill Education: Artificial Intelligence (Subject Code 417)Spoorthi KumbhaNo ratings yet
- AnsKey+Ques CBSE SamplePaper 20-21Document12 pagesAnsKey+Ques CBSE SamplePaper 20-21RESULTNo ratings yet
- Data Base Management System - Unit 7 - Week 4Document6 pagesData Base Management System - Unit 7 - Week 4Bhoomika B RNo ratings yet
- Sample Paper 10: Biology (044) Class XII Session 2022-23Document14 pagesSample Paper 10: Biology (044) Class XII Session 2022-23DhruviNo ratings yet
- Sample 10Document14 pagesSample 10avanthighathenmozhi12No ratings yet
- 802 Information Technology SQPDocument7 pages802 Information Technology SQPaespamaoNo ratings yet
- Biology 2023 Set - 6Document10 pagesBiology 2023 Set - 6Aniket RajanNo ratings yet
- Physical FitnessDocument4 pagesPhysical Fitnessayikoyoroy10No ratings yet
- (LASER) survival8-DM An DSAD-2-print PendingDocument29 pages(LASER) survival8-DM An DSAD-2-print PendingJohn WickNo ratings yet
- Week 10: Assignment 10: (Https://swayam - Gov.in)Document4 pagesWeek 10: Assignment 10: (Https://swayam - Gov.in)ARUN KUMARNo ratings yet
- Grade 5 DLL MATH 5 Q1 Week 2Document8 pagesGrade 5 DLL MATH 5 Q1 Week 2Charmayne DatorNo ratings yet
- Week 4Document14 pagesWeek 4padmaNo ratings yet
- CO1 September 19Document6 pagesCO1 September 19ronald malicdemNo ratings yet
- 402 Information Tech SQPDocument7 pages402 Information Tech SQPTeam gore100% (1)
- It SQP and SolutionsDocument14 pagesIt SQP and SolutionsShaheer HaiderNo ratings yet
- Assignment 1Document7 pagesAssignment 1teju rajputNo ratings yet
- 417 Ai SQPDocument9 pages417 Ai SQPPeta SureshNo ratings yet
- BscphysyllDocument49 pagesBscphysyll22f2000478No ratings yet
- DLL Mathematics 5 q1 w2Document7 pagesDLL Mathematics 5 q1 w2Jom Mar Baroquillo100% (2)
- AI 2020 21 Samplepaper AnswerkeyDocument19 pagesAI 2020 21 Samplepaper Answerkeynnhcn5cj8sNo ratings yet
- 417 Ai SQPDocument8 pages417 Ai SQPPooja KukrejaNo ratings yet
- Introduction To Internet of Things - Unit 10 - Week 7Document5 pagesIntroduction To Internet of Things - Unit 10 - Week 7vasudevchalla8No ratings yet
- DLL - Mathematics 5 - Q1 - W2Document7 pagesDLL - Mathematics 5 - Q1 - W2NASH RENZO JUDIEL NADALNo ratings yet
- Introduction To Machine Learning - IITKGP - Unit 5 - Week 3Document4 pagesIntroduction To Machine Learning - IITKGP - Unit 5 - Week 3Priya VenkadachalamNo ratings yet
- PaperCut MF - Toshiba Embedded ManualDocument32 pagesPaperCut MF - Toshiba Embedded ManualJustin RossNo ratings yet
- Introduction To Power Apps PortalsDocument4 pagesIntroduction To Power Apps PortalsIrwan SulistyoNo ratings yet
- Sensors and Simulation Doc For Weather Monitoring SystemDocument6 pagesSensors and Simulation Doc For Weather Monitoring SystemjainNo ratings yet
- Hds State Ed UserDocument194 pagesHds State Ed UserdupipiNo ratings yet
- En - stm32L4 Peripheral LCDDocument25 pagesEn - stm32L4 Peripheral LCDPareekshith PNo ratings yet
- By Teamlease in 2 To 3 Working Days From The Date of KYC UpdationDocument3 pagesBy Teamlease in 2 To 3 Working Days From The Date of KYC UpdationParvezNo ratings yet
- Index: S.No Name of Practical Page No SignatureDocument8 pagesIndex: S.No Name of Practical Page No SignatureVivek BhardwajNo ratings yet
- AmazonDocument198 pagesAmazonVictor UzowuruNo ratings yet
- Requirement Specification Format DocumentDocument6 pagesRequirement Specification Format DocumentRohan SinghNo ratings yet
- FILE 20210113 151059 Vdocuments - Site 01-Ua5000-Technical-Manual PDFDocument107 pagesFILE 20210113 151059 Vdocuments - Site 01-Ua5000-Technical-Manual PDFThanh LeNo ratings yet
- Dell EMC Host Connectivity Guide For VMware ESX Server (300-002-304)Document121 pagesDell EMC Host Connectivity Guide For VMware ESX Server (300-002-304)AICCNo ratings yet
- Optical Burst Switching (OBS)Document27 pagesOptical Burst Switching (OBS)adityaNo ratings yet
- Cmbs 04-Management Information SystemDocument2 pagesCmbs 04-Management Information SystemRama KrishnaNo ratings yet
- Alnaseem PasswordsDocument12 pagesAlnaseem Passwords3KA عــ كهNo ratings yet
- Ghulam HussainDocument1 pageGhulam HussainNarendraNo ratings yet
- ET203 Research Paper PDFDocument5 pagesET203 Research Paper PDFYash SonawaneNo ratings yet
- nm2100 PDFDocument22 pagesnm2100 PDFRicardi Martinelli Martins0% (1)
- Bhavik Suthar - CV - AJDocument3 pagesBhavik Suthar - CV - AJmohammed rafi shaikhNo ratings yet
- HackingDocument6 pagesHackingapi-379098611100% (1)
- Data Sheet 6AG1518-4FP00-4AB0: General InformationDocument11 pagesData Sheet 6AG1518-4FP00-4AB0: General InformationAbdallah AbdelrehimNo ratings yet
- Inflection PointDocument32 pagesInflection PointRoberto SantiagoNo ratings yet
- 1-Intro To Computer System ServicingDocument9 pages1-Intro To Computer System Servicingloida maeNo ratings yet
- 7.0inch RGB Display User Manual enDocument15 pages7.0inch RGB Display User Manual enDVTNo ratings yet
- OB52 Month EndDocument3 pagesOB52 Month EndliverredNo ratings yet
- Website: Vce To PDF Converter: Facebook: Twitter:: Hpe0-S57.Vceplus - Premium.Exam.60QDocument22 pagesWebsite: Vce To PDF Converter: Facebook: Twitter:: Hpe0-S57.Vceplus - Premium.Exam.60Qmally4dNo ratings yet
- Packet Tracer - Configure Initial Router Settings: ObjectivesDocument8 pagesPacket Tracer - Configure Initial Router Settings: ObjectivesMENDOZA GASPAR PAOLA Ingeniería en Sistemas ComputacionalesNo ratings yet
- 30.unix - Useful CommandsDocument6 pages30.unix - Useful CommandsVikram AkulaNo ratings yet
- NSE Training NSE 4 Course Updates Partner FacingDocument11 pagesNSE Training NSE 4 Course Updates Partner FacinghahaNo ratings yet
- FAQ On Printing at ComCen UTown PDFDocument3 pagesFAQ On Printing at ComCen UTown PDFrevo17No ratings yet
- UNAVCO Polar GPS System Test Procedure Appendix4 v1.2Document2 pagesUNAVCO Polar GPS System Test Procedure Appendix4 v1.2Galih Yudha Wahyu SaputraNo ratings yet