Professional Documents
Culture Documents
3 MAC - Illustrations
3 MAC - Illustrations
Uploaded by
amonOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
3 MAC - Illustrations
3 MAC - Illustrations
Uploaded by
amonCopyright:
Available Formats
1502346 - Computer Communications and
Networks
Dr. Mohamed Saad
Department of Computer Engineering
University of Sharjah
msaad@sharjah.ac.ae
Chapter 4: The Medium Access Control Sublayer
M. Saad
The Medium Access Control Sublayer
• We have seen that networks can be divided into 2 categories: those using
point-to-point links, and those using broadcast channels.
• In broadcast networks, the key issue is how to determine who gets to use
the channel when there is competition for it → multiple access
• The protocols used to resolve the multiple access issue belong to a
sublayer of the data link layer called the medium access control (MAC)
sublayer.
1502346 - Computer Communications & Networks 1
M. Saad
Static Channel Allocation
• Frequency Division Multiplexing (FDM):
– If there are N users, divide the bandwidth into N equal-sized bands
(portions), and assign each user to a frequency band.
– Works well if the number of users N is small and constant, and each
user has a heavy load of traffic.
– Inefficient if the number of users is large → if the spectrum is divided
into N bands and more than N users are interested in communicating,
some users will be denied access even if some of the users who have
been assigned a frequency band are not transmitting.
– Inefficient even if the number of users is held constant at N → if some
users are idle, their frequency bands are simply lost.
1502346 - Computer Communications & Networks 2
M. Saad
Static Channel Allocation (contd.)
• Time Division Multiplexing (TDM):
– Divide the time into N slots, each user is assigned a slot.
– Inefficient if a user has nothing to transmit during its assigned slot.
• Solution → Dynamic Channel allocation
– ALOHA
– CSMA
1502346 - Computer Communications & Networks 3
M. Saad
ALOHA
• Introduced by Norman Abramson and his colleges at the University of
Hawaii.
• We will discuss 2 versions of ALOHA: pure ALOHA and slotted ALOHA.
1502346 - Computer Communications & Networks 4
M. Saad
ALOHA
• Users transmit whenever they have a frame to send.
• If collision occurred, the sender waits a random amount of time and
sends the same frame again.
– Note that a collision can be detected either by listening to the channel,
or by the use of acknowledgement.
1502346 - Computer Communications & Networks 5
M. Saad
Performance of Pure ALOHA
• Offered load G: Average number of frames (new and retransmissions)
generated per frame time.
• Throughput S: Average number of frames successfully delivered per
frame time.
• It can be shown that S = Ge−2G.
1502346 - Computer Communications & Networks 6
M. Saad
Performance (contd.)
S (throughput per frame time) 0.40
Slotted ALOHA: S = Ge–G
0.30
0.20
0.10 Pure ALOHA: S = Ge–2G
0 0.5 1.0 1.5 2.0 3.0
G (attempts per packet time)
• The maximum throughput of pure ALOHA occurs at G = 0.5, with
S = 1/2e ≃ 0.184.
• The best channel utilization we can hope for is 18%.
1502346 - Computer Communications & Networks 7
M. Saad
Slotted ALOHA
• Time is divided into discrete time slots.
• A user is allowed to transmit only at the beginning of a time slot.
• Sender algorithm:
– When a user has a frame to send, it waits until the beginning of the
next time slot and transmits the frame.
– If collision occurs, the user waits for a random number of time slots
and sends the same frame again.
• It can be shown that, for slotted ALOHA, S = Ge−G .
• The maximum throughput of slotted ALOHA occurs at G = 1, with
S = 1/e ≃ 0.368 (double the capacity of pure ALOHA).
1502346 - Computer Communications & Networks 8
M. Saad
Carrier Sense Multiple Access (CSMA)
• The best channel utilization that can be achieved with ALOHA is 36%.
• This is not surprising → users transmit without paying attention to what
the other users are doing.
• Improvement → listen for ongoing transmissions and act accordingly →
carrier sense protocols.
1502346 - Computer Communications & Networks 9
M. Saad
1-persistent CSMA
• If a station has data to send, it first listens to the channel to see if
anyone else is transmitting at the moment.
– If the channel is idle, the station transmits.
– If the channel is busy, the station waits until it becomes idle, then
transmits.
• If a collision occurs, the station waits a random amount of time and
starts over again.
• Intuitively, this protocol performs better than ALOHA.
• Collisions occur if 2 stations are waiting for the channel to become idle at
the same time. Once the channel becomes idle they will send together.
1502346 - Computer Communications & Networks 10
M. Saad
Nonpersistent CSMA
• If a station has data to send, it first listens to the channel to see if
anyone else is transmitting at the moment.
– If the channel is idle, the station transmits.
– If the channel is busy, the station does not continuously sense it with
the purpose of seizing it immediately upon detecting the end of the
previous transmission. Instead, it waits a random period of time and
repeats the algorithm.
• This algorithm leads to better channel utilization but longer delays than
1-persistent CSMA.
1502346 - Computer Communications & Networks 11
M. Saad
p-persistent CSMA
• it applies to slotted channels, and works as follows:
• When a station becomes ready, it senses the channel.
– If the channel is idle, the station transmits with probability p. With
probability 1 − p, it defers until the next time slot and tries again. This
process is repeated until the frame has been transmitted, or another
stations starts transmitting. In the latter case, the station waits a
random time and tries again.
– If the channel is busy, it waits until the next time slot and tries again.
1502346 - Computer Communications & Networks 12
M. Saad
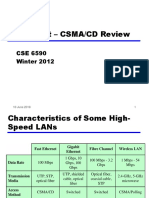
CSMA with Collision Detection (CSMA/CD)
• In CSMA protocols, if 2 stations sense the channel idle at the same time,
they may begin transmitting simultaneously.
• Collision detection → station continues sensing the channel after
beginning to transmit, stop transmitting as soon as a collision is detected
(rather than finishing transmission).
1502346 - Computer Communications & Networks 13
M. Saad
Performance of Multiple Access Techniques
0.01-persistent CSMA
1.0
0.9 Nonpersistent CSMA
S (throughput per packet time)
0.8 0.1-persistent CSMA
0.7
0.6 0.5-persistent
CSMA
0.5
Slotted
0.4 ALOHA
0.3 1-persistent
Pure CSMA
0.2
ALOHA
0.1
0
0 1 2 3 4 5 6 7 8 9
G (attempts per packet time)
1502346 - Computer Communications & Networks 14
M. Saad
Wireless LAN Protocols
• Consider a number of mobile devices (e.g., laptop computers) that can communicate
with each other using the radio (wireless) channel as the shared medium.
• The above configuration is known as wireless LAN. RX
TX
• Two users can communicate if they are in radio range of each other.
• Collision happens when a receiver is in radio range of 2 active transmitters. TX
1502346 - Computer Communications & Networks 15
M. Saad
The Hidden Station Problem
• We will see that CSMA cannot be used in wireless LANs.
A B C D A B C D
Radio range
(a) (b)
• Assume that A and B are within each other’s range and can potentially interfere with
each other. C can also interfere with B and D, but not with A.
• Let A be transmitting to B.
• If C senses the medium, it will not hear A because A is out of range, and thus will
falsely conclude that it can transmit to B → collision will occur.
• The problem of a station not being able to detect a potential competitor for the medium
because the competitor is too far away is called the hidden station problem.
1502346 - Computer Communications & Networks 16
M. Saad
The Exposed Station Problem
A B C D A B C D
Radio range
(a) (b)
• Consider the reverse situation: B is transmitting to A.
• If C senses the medium it will hear an ongoing transmission, and will falsely conclude
that it cannot send to D.
• Such transmission (from C to D) would not interfere with the transmission from b to
A, because C’s transmission cannot reach A.
• In wireless LANs, what matters is the interference at the receiver, not at the sender.
1502346 - Computer Communications & Networks 17
M. Saad
Multiple Access with Collision Avoidance (MACA)
Range of A's transmitter Range of B's transmitter
C A RTS B D C A CTS B D
E E
(a) (b)
• Consider how A sends a frame to B.
– A starts by sending an RTS (Request to Send) frame to B. This short frame (30
bytes) contains the length of the data frame that will eventually follow.
– Then B replies with a CTS (Clear to send) frame. The CTS frame contains the data
length (copied from the RTS frame)
– Upon receipt of the CTS frame, A begins transmission.
1502346 - Computer Communications & Networks 18
M. Saad
Collision Avoidance
• Any other station hearing the RTS is clearly close to A and must remain
silent long enough for the CTS to be transmitted back to A without
conflict.
• Any station hearing the CTS is clearly close to B and must remain silent
during the upcoming data transmission (length of data transmission can
be obtained by examining the CTS frame).
• Note that any station hearing the RTS but not the CTS is close to the
sender, but far away from the receiver, and can transmit.
1502346 - Computer Communications & Networks 19
M. Saad
Example
Range of A's transmitter Range of B's transmitter
C A RTS B D C A CTS B D
E E
(a) (b)
• C is within range of A but not within range of B ⇒ C hears RTS from A but does not
hear CTS from B ⇒ C is free to transmit.
• D is within range of B but not A ⇒ D does not hear the RTS but does hear the CTS
⇒ D cannot transmit.
• E hears both RTS and CTS ⇒ E cannot transmit.
1502346 - Computer Communications & Networks 20
M. Saad
Collision Can Still Happen . . .
• For example, B and C could both send an RTS to A at the same time.
These will collide and be lost.
• A transmitter will know about the collision of an RTS frame if it does
not receive a CTS within a time out interval.
• In the case of a collision of an RTS, the transmitter waits a random
amount of time and tries again.
1502346 - Computer Communications & Networks 21
M. Saad
Ethernet (revisited)
• We have now finished our general discussion of channel allocation
(multiple access) protocols, so it is time to have a look at the real
systems that use them.
• Ethernet (now IEEE 802.3 standard) is an important networking
technology that uses CSMA.
• We have introduced Ethernet in the Introduction and will add some
details here.
1502346 - Computer Communications & Networks 22
M. Saad
Classic Ethernet
Transceiver
Interface
cable
Ether
• Transmission medium is a coaxial cable (not vacuum) called “the ether”, up to 2.5 km
long, with repeaters every 500 m.
• Up to 256 machines connected to the cable.
• Transmission rate 2.94 Mbps.
• In 1978: DEC, Intel and Xerox standardized a 10 Mbps Ethernet.
• Now 100 Mbps and 1 Gbps Ethernet’s exist.
1502346 - Computer Communications & Networks 23
M. Saad
Switched Ethernet
• Switched Ethernets can be built using hubs or switches.
1502346 - Computer Communications & Networks 24
M. Saad
Repeaters, Hubs, Bridges, Switches, Routers and
Gateways
Application layer Application gateway
Transport layer Transport gateway Packet (supplied by network layer)
Frame Packet TCP User
Network layer Router CRC
header header header data
Data link layer Bridge, switch Frame (built by data link layer)
Physical layer Repeater, hub
(a) (b)
• Repeaters: analog devices connecting two cable segments; a signal appearing on one
cable is amplified and put out on the other one. Repeaters are physical layer devices,
i.e., they do not examine any address. They do not understand frames, packets or
headers; they understand volts.
Repeater
1502346 - Computer Communications & Networks 25
M. Saad
Hubs, Switches and Bridges
A B C D A B C D A B C D
Host
Hub Bridge Switch
LAN
E F G H E F G H E F G H
(a) (b) (c)
• Hubs:
– Each machine is connected to the hub by a separate twisted pair cable.
– Frames arriving on any of the hub’s lines are sent out (without buffering, and without
examining any address) on all other lines.
– If two frames arrive at the same time, they will collide, just as on coaxial cable. In
other words, the entire hub forms a single collision domain.
1502346 - Computer Communications & Networks 26
M. Saad
Hubs, Switches and Bridges (contd.)
A B C D A B C D A B C D
Host
Hub Bridge Switch
LAN
E F G H E F G H E F G H
(a) (b) (c)
• Switches: frames arriving at an input port/line are forwarded to the right output
port/line by reading the MAC address (in the Ethernet frame header), then looking up
a table to see where to send the frame.
• Bridges: switches used to interconnect several LANs (Ethernets), as to create extended
LANs.
1502346 - Computer Communications & Networks 27
M. Saad
Ethernet Frame Format
• Frame formats: (a)DIX (DEC, Intel, Xerox) Ethernet. (b) IEEE 802.3.
Bytes 8 6 6 2 0-1500 0-46 4
Destination Source Check-
(a) Preamble Type Data Pad
address address sum
Destination Source Check-
(b) Preamble Length Data Pad
address address sum
1502346 - Computer Communications & Networks 28
M. Saad
DIX Ethernet Frame Format
• Preamble: 8 bytes containing the pattern 10101010 (repeated 8 times); used for
synchronization purposes (extracting the clock with the use of Manchester encoding).
• Source and destination addresses: 48-bit data link layer (MAC) addresses. Every
manufactured Ethernet board comes with a globally unique 48-bit MAC address.
• Type: tells the receiver which network layer protocol to hand the frame to.
• Data: up to 1500 bytes of data.
• Pad: frames with fewer than 64 bytes are padded out to 64 bytes. Having a minimum
frame length is important to allow senders to keep transmitting for long enough so that
they can detect a collision during transmission.
• Checksum: used for error detection.
1502346 - Computer Communications & Networks 29
M. Saad
Bridges and LAN Switches
• Switches can be used to forward packets between shared-media LANs such as Ethernets.
Such switches are sometimes known as LAN switches; historically they have been
referred to as bridges.
• If a frame arrives at one of the ports, it is forwarded along the other ports.
1502346 - Computer Communications & Networks 30
M. Saad
Learning Bridges
• A frame sent from A to B will be received by the bridge at port 1. The bridge, however,
does not need to forward this frame along port 2 (to the other LAN).
• Question: how does the bridge learn on which port the various hosts reside?
• Answer: the bridge maintains a forwarding table that specifies the port on which each
host resides. If the destination of a frame that arrives at port 1 resides also on port 1
(according to the table), the frame is not forwarded.
1502346 - Computer Communications & Networks 31
M. Saad
Learning Bridges (contd.)
Host Port
A 1
B 1
C 1
X 2
Y 2
Z 2
• The bridge dynamically creates the table as follows:
– When the bridge first boots, the table is empty.
– The bridge inspects the source address of all frames it receives.
– Thus when host A sends a frame to any other host, this frame will be received by
the bridge at port 1. The bridge will create the first entry of the table above.
1502346 - Computer Communications & Networks 32
M. Saad
Learning Bridges (contd.)
• To protect against the situation in which hosts may move from one
network to the other, every table entry is associated with a timeout; after
timeout the entry is deleted.
• At any time, the table is not necessarily complete. Completeness of the
table is not required for correctness of the operation. The table is an
optimization.
1502346 - Computer Communications & Networks 33
M. Saad
Example: Building LAN Using Hubs and a Switch
Cable
duct
Hub
Corri dor
Switch
Hub
Twisted pair Office
to a hub
1502346 - Computer Communications & Networks 34
M. Saad
Thanks
1502346 - Computer Communications & Networks 35
You might also like
- RADCOM - 5G Core Network PosterDocument1 pageRADCOM - 5G Core Network PosterFaustoLasernaSantiago100% (1)
- Automated Broad and Narrow Band Impedance Matching for RF and Microwave CircuitsFrom EverandAutomated Broad and Narrow Band Impedance Matching for RF and Microwave CircuitsNo ratings yet
- CN U3Document106 pagesCN U3NAMAN JAISWALNo ratings yet
- Medium Access ControlDocument37 pagesMedium Access ControlRekha V RNo ratings yet
- Lecture #14: Local Area Networks: Aloha Ethernet Token Ring Token BusDocument43 pagesLecture #14: Local Area Networks: Aloha Ethernet Token Ring Token BusDhruvik ViraniNo ratings yet
- Medium Access Control Sub LayerDocument41 pagesMedium Access Control Sub LayerhariharankalyanNo ratings yet
- Chapter Five - NewDocument45 pagesChapter Five - NewEthio DotNetDeveloperNo ratings yet
- MAC SublayerDocument92 pagesMAC SublayerAlready ATracerNo ratings yet
- The Medium Access ControlDocument71 pagesThe Medium Access ControlfarhanaNo ratings yet
- ALOHA Class of Multiple Access Protocols: ThroughputDocument12 pagesALOHA Class of Multiple Access Protocols: ThroughputGehendraSubediNo ratings yet
- EthernetDocument73 pagesEthernetRaheel MahmoodNo ratings yet
- Medium Access Control ProtocolDocument146 pagesMedium Access Control ProtocolAbhiRamNo ratings yet
- The Medium Accesscontrol SublayerDocument69 pagesThe Medium Accesscontrol Sublayerj srisai sekharNo ratings yet
- Merged CNDocument257 pagesMerged CNYuvaraj TankalaNo ratings yet
- Part 6 - Local Area Network TechnologyDocument35 pagesPart 6 - Local Area Network TechnologyRoberaNo ratings yet
- Medium Access Control PDFDocument47 pagesMedium Access Control PDFTadesse DestawNo ratings yet
- CN - Chapter 4 - Class 1, 2Document4 pagesCN - Chapter 4 - Class 1, 2himanshuajaypandeyNo ratings yet
- 4 MacDocument81 pages4 MacKunal ChitkaraNo ratings yet
- Chapter 5 - Local Area Network TechnologyDocument35 pagesChapter 5 - Local Area Network Technologyfnata AiNo ratings yet
- Mac SblayerDocument69 pagesMac SblayerAmbika SharmaNo ratings yet
- Medium Access Control (MAC)Document79 pagesMedium Access Control (MAC)Saurabh SharmaNo ratings yet
- 21CS52 PPT 2Document26 pages21CS52 PPT 2Manju p sNo ratings yet
- CE257 Data Communication and Networking: By: Dr. Ritesh Patel Ce Dept, Cspit, Charusat Riteshpatel - Ce@charusat - Ac.inDocument71 pagesCE257 Data Communication and Networking: By: Dr. Ritesh Patel Ce Dept, Cspit, Charusat Riteshpatel - Ce@charusat - Ac.inDHRUVNo ratings yet
- Computer Communication and NetworkingDocument32 pagesComputer Communication and NetworkingVankesh MathraniNo ratings yet
- Chapter 2.2.1Document32 pagesChapter 2.2.1Aarush KashyapNo ratings yet
- Hihg Level Datalink Control Protocol (HDLC)Document6 pagesHihg Level Datalink Control Protocol (HDLC)suneelkluNo ratings yet
- Share DCNPPTDocument25 pagesShare DCNPPTAkhil MishraNo ratings yet
- EE206A Lecture #5 Sharing The Wireless Link: Part II: Mani SrivastavaDocument29 pagesEE206A Lecture #5 Sharing The Wireless Link: Part II: Mani SrivastavaGopi MgNo ratings yet
- Online - Class 11 MACDocument22 pagesOnline - Class 11 MACAshNo ratings yet
- Unit 2Document198 pagesUnit 2Manish NagarNo ratings yet
- Eeswar Babu Banala: Associate Professor Vidya Jyothi Institute of Technology Hyderabad TelanganaDocument77 pagesEeswar Babu Banala: Associate Professor Vidya Jyothi Institute of Technology Hyderabad Telanganakarna_lokeshNo ratings yet
- Ethernet - CSMA/CD Review: CSE 6590 Winter 2012Document22 pagesEthernet - CSMA/CD Review: CSE 6590 Winter 2012azamNo ratings yet
- Unit 2 Medium Access Sub Layer: Q2.Write A Short Note On Static and Dynamic Channel Allocation?Document24 pagesUnit 2 Medium Access Sub Layer: Q2.Write A Short Note On Static and Dynamic Channel Allocation?santhipriyasunkaraNo ratings yet
- Media Access ControlDocument25 pagesMedia Access ControlPIXEL Is LiveNo ratings yet
- Unit2A FinalDocument74 pagesUnit2A FinalAkhila VeerabommalaNo ratings yet
- The Medium Access SublayerDocument80 pagesThe Medium Access SublayerVimal KumarNo ratings yet
- Module 2 Part 4Document53 pagesModule 2 Part 4leemong335No ratings yet
- R16 4-1 CN Unit 4Document18 pagesR16 4-1 CN Unit 4rahaman mahamadNo ratings yet
- Computer Networks-MACDocument10 pagesComputer Networks-MACRani MuraliNo ratings yet
- CHP 2 CNNDDocument14 pagesCHP 2 CNNDaditipatil2404No ratings yet
- Chapter4 MediumAccessControlSublayerDocument159 pagesChapter4 MediumAccessControlSublayersunilsmcsNo ratings yet
- Data Link Control and Multiple AccessDocument42 pagesData Link Control and Multiple AccessmigadNo ratings yet
- Computer NetworksDocument15 pagesComputer NetworksJeena Mol AbrahamNo ratings yet
- Multiple Access Protocols: Multiple Access Method Allows Several Terminals Connected To The SameDocument31 pagesMultiple Access Protocols: Multiple Access Method Allows Several Terminals Connected To The Samemanish saraswatNo ratings yet
- Computer Networks UNIT-4 Syllabus: The Medium Access Control Sublayer-The Channel Allocation Problem-StaticDocument47 pagesComputer Networks UNIT-4 Syllabus: The Medium Access Control Sublayer-The Channel Allocation Problem-StaticCDTP G.P. NARENDRANAGARNo ratings yet
- 9.d CN Unit 4Document47 pages9.d CN Unit 4SK Endless SoulNo ratings yet
- Chapter Five: Local Area Networking TechnologyDocument38 pagesChapter Five: Local Area Networking TechnologyAbera BrhanuNo ratings yet
- Medium Access ControlDocument10 pagesMedium Access ControlVijay ParuchuriNo ratings yet
- The Medium Access Control SublayerDocument159 pagesThe Medium Access Control SublayerAlaa Dawood SalmanNo ratings yet
- CN - Unit II MACDocument57 pagesCN - Unit II MACbd29012004No ratings yet
- 15-Local Area NetworksDocument63 pages15-Local Area Networkskks_82No ratings yet
- Ch12 Multiple AccessDocument56 pagesCh12 Multiple Accessvishalmishra271bNo ratings yet
- CH - 04 - 1 MAC Sub Layer-AlohaDocument16 pagesCH - 04 - 1 MAC Sub Layer-Alohayoutube premiumNo ratings yet
- The Medium Access Control SublayerDocument70 pagesThe Medium Access Control Sublayerayushi vermaNo ratings yet
- Multiplexing and Multiple AccessDocument82 pagesMultiplexing and Multiple AccessharshadaNo ratings yet
- Lec2 Local Area NetworksDocument60 pagesLec2 Local Area Networksapi-26404571No ratings yet
- Unit - Iii - PPT-2 Mca-20-14Document26 pagesUnit - Iii - PPT-2 Mca-20-14amaubedwalNo ratings yet
- MAC Protocols For Ad-Hoc Wireless NetworksDocument55 pagesMAC Protocols For Ad-Hoc Wireless NetworksIqra HanifNo ratings yet
- MAC ProtocolDocument36 pagesMAC ProtocolHrithik ReignsNo ratings yet
- Unit 5Document18 pagesUnit 5ManaswiniNo ratings yet
- SAS Protocol LayerDocument1,059 pagesSAS Protocol LayerEmily WangNo ratings yet
- Brosur Rectiverter Dan Battery (48Vdc 24Vdc 220vac)Document6 pagesBrosur Rectiverter Dan Battery (48Vdc 24Vdc 220vac)Andri SupartoNo ratings yet
- MSOFTX3000 Unified Maintenance Manual - Baic Call Service-V3.1.0Document68 pagesMSOFTX3000 Unified Maintenance Manual - Baic Call Service-V3.1.0haytham_501100% (1)
- Notifier Nca2/Nfs2-3030: Fieldserver Protocol Driver SheetDocument3 pagesNotifier Nca2/Nfs2-3030: Fieldserver Protocol Driver SheetLuis KaaNo ratings yet
- How To Configure Power Stack Switch Power ParametersDocument2 pagesHow To Configure Power Stack Switch Power ParametersCassandra ShafferNo ratings yet
- WiresharkDocument21 pagesWiresharkLavi JainNo ratings yet
- A Comparison Between LDPC Block and Convolutional CodesDocument5 pagesA Comparison Between LDPC Block and Convolutional CodesnxtxxxNo ratings yet
- Draytek Vigor 2910 & GreenBow IPSec VPN Software ConfigurationDocument17 pagesDraytek Vigor 2910 & GreenBow IPSec VPN Software Configurationgreenbow100% (2)
- How Internet Works On Mobile DevicesDocument6 pagesHow Internet Works On Mobile DevicesBiruk BirhanuNo ratings yet
- Network Mind MapDocument2 pagesNetwork Mind Mapanita Kumari100% (1)
- Flashwave 4 1 0 0: Multiservice Provisioning PlatformDocument8 pagesFlashwave 4 1 0 0: Multiservice Provisioning PlatformAugtron Anders100% (1)
- Transmission Control Protocol (TCP)Document100 pagesTransmission Control Protocol (TCP)nabeel hasanNo ratings yet
- Configuration Guide - Ethernet Switching: Cloudengine 8800, 7800, 6800, and 5800 V200R003C00Document7 pagesConfiguration Guide - Ethernet Switching: Cloudengine 8800, 7800, 6800, and 5800 V200R003C00Yerly MancipeNo ratings yet
- TS 36.211 LTE Physical Channels and ModulationDocument138 pagesTS 36.211 LTE Physical Channels and ModulationRoberto TRNo ratings yet
- CMU200 TrainingDocument61 pagesCMU200 TrainingJason RobinsonNo ratings yet
- Modem ATCmd RefDocument48 pagesModem ATCmd RefmaxonetNo ratings yet
- Queclink Product Catalog - ENDocument24 pagesQueclink Product Catalog - ENmohamed.khalidNo ratings yet
- VLSM ExampleDocument4 pagesVLSM ExampleRafayetNo ratings yet
- Spread Spectrum Modulation: UNIT-3 PART-2Document40 pagesSpread Spectrum Modulation: UNIT-3 PART-2Sudheer KumarNo ratings yet
- Computer Assignment: BS2 SS2:Assignment No1Document12 pagesComputer Assignment: BS2 SS2:Assignment No1ShahrozNo ratings yet
- ASTM Host Simulator User Manual V5-6Document23 pagesASTM Host Simulator User Manual V5-6Rol PositivoNo ratings yet
- Teleprotection Scheme With SIPROTEC 5 DevicesDocument12 pagesTeleprotection Scheme With SIPROTEC 5 DevicesCarlos Roberto Hernandez FerrerNo ratings yet
- Dell Networking RoCE ConfigurationDocument11 pagesDell Networking RoCE Configurationnaja manNo ratings yet
- Suricata User Guide: Release 4.1.0-DevDocument260 pagesSuricata User Guide: Release 4.1.0-DevErnesto GuevarNo ratings yet
- 2G&3G Planning & Optimization - Part-1Document80 pages2G&3G Planning & Optimization - Part-1Rituraj Biswanath100% (1)
- Tecspg 3001Document402 pagesTecspg 3001TrkNo ratings yet
- Nova-233 - OD - FDD-TDD - eNB - Data - Sheet (SRv1.2 - 15-Feb-2018)Document2 pagesNova-233 - OD - FDD-TDD - eNB - Data - Sheet (SRv1.2 - 15-Feb-2018)Wan Mohd GhazaliNo ratings yet
- Extreme Routing Student Guide v2.0 (Ebook)Document319 pagesExtreme Routing Student Guide v2.0 (Ebook)Hrvoje SilovNo ratings yet
- Muhummad Tutorial Ipv6 BasicsDocument78 pagesMuhummad Tutorial Ipv6 BasicsSatyapriya PanigrahiNo ratings yet