Professional Documents
Culture Documents
Cdi Ass Ni Max
Cdi Ass Ni Max
Uploaded by
Julius Evia Pajotea0 ratings0% found this document useful (0 votes)
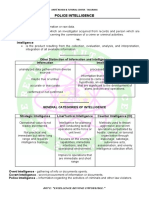
9 views5 pages1. Police intelligence involves collecting, analyzing, and interpreting information from various sources to aid in law enforcement efforts like arrests and preventing crimes.
2. Important historical figures that advanced the field of intelligence include Hannibal who gathered information in Rome by disguising himself, Alexander the Great who intercepted letters to gain intelligence, and Sir Francis Walsingham who established the first national intelligence service in England.
3. There are different types of intelligence like criminal intelligence, counterintelligence, strategic intelligence, and line intelligence which is tactical information on people, weather, the enemy, and terrain used for planning operations. Intelligence can be collected through overt means like open sources or covert methods using secret sources.
Original Description:
Original Title
CDI-ASS-NI-MAX
Copyright
© © All Rights Reserved
Available Formats
DOCX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this Document1. Police intelligence involves collecting, analyzing, and interpreting information from various sources to aid in law enforcement efforts like arrests and preventing crimes.
2. Important historical figures that advanced the field of intelligence include Hannibal who gathered information in Rome by disguising himself, Alexander the Great who intercepted letters to gain intelligence, and Sir Francis Walsingham who established the first national intelligence service in England.
3. There are different types of intelligence like criminal intelligence, counterintelligence, strategic intelligence, and line intelligence which is tactical information on people, weather, the enemy, and terrain used for planning operations. Intelligence can be collected through overt means like open sources or covert methods using secret sources.
Copyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
Download as docx, pdf, or txt
0 ratings0% found this document useful (0 votes)
9 views5 pagesCdi Ass Ni Max
Cdi Ass Ni Max
Uploaded by
Julius Evia Pajotea1. Police intelligence involves collecting, analyzing, and interpreting information from various sources to aid in law enforcement efforts like arrests and preventing crimes.
2. Important historical figures that advanced the field of intelligence include Hannibal who gathered information in Rome by disguising himself, Alexander the Great who intercepted letters to gain intelligence, and Sir Francis Walsingham who established the first national intelligence service in England.
3. There are different types of intelligence like criminal intelligence, counterintelligence, strategic intelligence, and line intelligence which is tactical information on people, weather, the enemy, and terrain used for planning operations. Intelligence can be collected through overt means like open sources or covert methods using secret sources.
Copyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
Download as docx, pdf, or txt
You are on page 1of 5
1.
Police Intelligence According to him, "one spy in the right
It is the end product resulting from the place is equivalent to 20,000 men in the
collection, evaluation, analysis, integration, field." He maintained military intelligence
and interpretation of all available and secret political police service all over
information regarding the activities of Europe.
criminals and other law violators for the
purpose of affecting their arrest, obtaining 7. Frederick the Great
evidence, and forestalling them to commit Father of organized military espionage. This
crime. Prussian master was able to classify his
agents into four classes: common spies,
2. Delilah double spies, spies of consequence, and
She is a biblical personality, she was able to persons which are involuntarily led to
gain information by using her beauty and undertake espionage.
charm, she was responsible for the fall of
Samson, a known Israelite leader and enemy 8. Hannibal
of the Philistines. Known as one of the greatest Roman
enemies who ruled and conquered Rome for
3. Sun Tzu 15 years by obtaining common street
The author of the art of war. A Chinese knowledge by posing as a beggar to gather
philosopher who takes into account practical first hand information on the pulse of the
views in battle. According to him people. His famous feat was at the outbreak
foreknowledge cannot be elicited from of the Second Punic War when he marched
spirits nor from gods nor from analogy with an army which included elephants from
past events nor from calculations. He further Iberia to Northern Italy. Military historians
asserted that if you know thy enemy and consider Hannibal as the "father of strategy"
know thyself, you need not fear the results because his greatest enemy, Rome, came to
of a hundred battles. adopt the elements of his military tactics in
its own strategic arsenal.
4. Alexander the Great
A Greek Conqueror, was able to identify 9. Classification of Police Intelligence
those who are disloyal to him by ordering ● Criminal Intelligence (CRIMINT)-
the opening of communication letters of his production of intelligence essential
men and was successful in uplifting the to the prevention of crimes and the
esprit de corps and morale of his men. He investigation, arrests, and
devised the first letter sorting and opening to prosecution of criminal offenders.
obtain information. ● Internal Security Intelligence
(INSINT)- refers to the knowledge
5. Sir Francis Walsingham essential to the maintenance of peace
In England, Sir Francis Walsingham, under and order. Keeping peace within the
Queen Elizabeth, organized the first borders of a sovereign state or other
National Intelligence Service. He employed self-governing territories, generally
spies on the staff of the Admiral in by upholding the national law and
Command of the Spanish Army and was defending against internal security
able to obtain information regarding the threats.
Spanish Army as to their ships, equipment, ● Public Safety Intelligence
forces and stores. He protected Queen (PUSINT)- refers to the knowledge
Elizabeth I from countless assassins. essential to ensure the protection of
lives and properties.
6. Napoleon Bonaparte
10. Forms of Intelligence
➔ Sociological Intelligence- deals with Intelligence information to be determined
the demographic and psychological in Line Intelligence are:
aspects of groups of people. It
includes the population and People- living condition of the people,
manpower and the characteristics of sources of income, education of the people,
the people, public opinion-attitude of government livelihood projects, extent of
the majority of the people towards enemy influence to the people.
matters of public policy and
education. Weather - visibility, cloudy, temperature,
➔ Biographical Intelligence - deals precipitation (rain), wind.
with individual's personalities who
have actual possession of power. Enemy - location of the enemy, strength of
➔ Armed Force Intelligence- deals with the enemy, disposition, tactical capability,
the armed forces of the nation. It enemy vulnerability.
includes the position of the armed
forces, the constitutional and legal Terrain- relief and drainage system,
basis of its creation and actual role, vegetation, surface material, man made
the organizational structure and features. There are military aspects of terrain
territorial disposition, and the which includes cover and concealment,
military manpower recruitment and obstacles, critical key terrain features,
Order of Battle. observation and fields of fire, and avenues
➔ Geographical Intelligence deals with of approach.
the progress of research and
development as it affects the ➔ Counter Intelligence (CI) - this kind
economic and military potential of a of intelligence covers the activity
nation. devoted to destroying the
effectiveness of hostile foreign
11. Kinds of Intelligence activities and to the protection of
➔ Strategic Intelligence - as defined info against espionage, subversion
earlier, it is an intelligence data that and sabotage. Hence, the three
is not of an immediate value. It is activities of CI are; protection of
usually descriptive in nature, information against espionage;
accumulation of physical description protection of personnel against
of personalities, modus operandi. It subversion, and protection of
does not have immediate operational installations and material against
value but rather long range that may sabotage.
become relevant to future police
operations. Counter Intelligence is also known as
➔ Line Intelligence - It is the kind of Negative Intelligence - a generic term
intelligence required by the meaning three different things;
commander to provide for planning
and conduct tactical and Security Intelligence- means that the total
administrative operations in counter sum of efforts to counsel the national
insurgency. This pertains to policies, diplomatic decisions, military data,
knowledge of People, Weather, and any other information of a secret nature
Enemy and Terrain (PWET) used in affecting the security of the nation form
planning and conducting tactical and unauthorized persons. It is an effort to deny
administrative operations in a information to unauthorized persons by
counter insurgency. restricting to those who are explicitly
authorized to possess it.
agencies and type of information the
Counter-Intelligence- counter intelligence is latter can provide.
the organized effort to protect specific data Priority Intelligence Requirement- an
that might be of value to the opponent's own item of intelligence or information of
intelligence organization. Some of its the characteristics of the area of
functions are Censorship of the following: operations and the enemy which the
correspondence, broadcast. telecast, commander feels he needs before he
telephone conversations, telegrams and can reasonably arrive at a decision.
cables, etc., prevention of the dissemination Also known as the Essential Element
of any information that might aid an of Information.
opponent; maintenance of files of suspect, ➔ Collection- The intelligence officer
surveillance of suspects, mail reading, must have thorough knowledge of
wiretapping and recording; infiltration of the the available sources of information
enemy intelligence organized to procure and collecting agencies and the type
information about its method, personal, of information they can provide.
specific operations and interest. Methods of Collection (overt and covert
intelligence)
Counter-Espionage - In counter-espionage, ● Overt-open sources. 99% of the
negative intelligence becomes a dynamic information collected is coming from
and active effort. Its purpose is to investigate open sources.
actual or theoretical violation of espionage ● Covert-closed/secret sources. Only
laws, to enforce those laws and to apprehend 1% of information is obtained from
any violators. covert operation.
12. Major Intelligence service in the ➔ Processing/Analysis- The stage in
Philippines which the collected information is
The National Intelligence Coordinating subjected to review in order to
Agency or NICA is the primary intelligence satisfy significant facts and derive
collection and analysis arm of the Philippine conclusions there from.
government in charge of carrying out overt, ➔ Dissemination- Processed
covert, and clandestine intelligence information or intelligence data are
programs. The current head of the Agency is disseminated to end users, common
General Cesar Garcia. Its motto is Ang methods of disseminating Intel data
Karunungan ay Kaligtasan (translated are conferences, briefing and person
"Knowledge is Security"). Presently, NICA to person exchanges. In this process,
is in close coordination with the CIA, consider the factors of timeliness,
Mossad and intelligence services of ASEAN correctness and security.
countries to counter the threat of terrorism.
14. Four Categories of classified
EXECUTIVE ORDER NO. 246 matters
JULY 24, 1987, PROVIDING FOR THE ● Top Secret- calls for the utmost
CREATION OF THE NATIONAL degree of protection. Unauthorized
INTELLIGENCE COORDINATING revelation of these materials and
AGENCY AND FOR OTHER PURPOSES. information will cause extremely
severe damage to the nation,
13. Intelligence Cycle politically, economically, or
➔ Planning and direction -The militarily.
intelligence officer must have a Examples: political negotiations, military
thorough knowledge of the available defense, war strategic plans, etc.
sources of information, the collecting
● Secret- unauthorized disclosure of ➔ False Informant - reveals information
these documents or things may put of no consequences or value.
national security at risk and cause ➔ Self-Aggrandizing - moves around
serious injury to the reputation of the the center of criminals delight in
nation. surprising the police about bits of
Examples: info about intelligence information.
operations, troop movements, order of ➔ Double Crosser - wants to get more
battle, etc. information from the police more
● Confidential-Unauthorized than what he gives.
revelation of which may be injurious ➔ Special/legitimate informant- those
to the reputation of the nation or who give information concerning
governmental activity or will cause specialized cases. Usually they are
administrative humiliation or regarded with special treatment by
unnecessary injury. the operatives.
Examples: plans of government projects, ➔ Voluntary informant-gives
routine intelligence reports information freely and willfully as a
● Restricted - this is information which witness to a certain act.
should not be published or ➔ Recruited informant- a person who is
communicated to anyone except for selected, cultivated, and developed
official purposes. These records are into a continuous source of
daily files, routine in nature even if information.
lost or destroyed will not affect ➔ Rival elimination informant-
operation, informant who gives information to
Examples: blotters, daily logbook file, etc. eliminate rivalry.
➔ Mercenary informant-informant who
15. Informant (assets)- gives gives Information for remuneration
information without any or compensation.
consideration.
17. Types of surveillance
Other meanings of "Informants": a. According to Intensity and
1. Obnoxious - the view of the public to Sensitivity
a person selling information to ● Discrete- Discreet surveillance of
another or money motivated. people and facilities is defined as
2. Stool Pidgeon - the view of the secret monitoring and surveillance of
underworld to a person who exposes people, facilities and vehicles for the
their activities and Identities. purpose of collecting findings and
3. Savior - the view of the police to a evidence related to specific
person who gives information, activities, people's identities and
without his valuable reports or meetings, previously defined by the
revelations the crime would remain client requesting the surveillance.
unsolved. ● Close- surveillance maintained
where the prevention of loss of the
Informer- gives information in exchange subject is paramount.
for a reward or a price. ● Loose- involves the exercise of
caution, preferring to lose the subject
16. Types of informant rather than risk detection or
➔ Anonymous- those who give exposure.
information through telephone with
the hope that the informant cannot be b. According to Methods
identified.
● Stationary Surveillance - also 19. Method of foot surveillance
referred to as Fixed or Stakeout ➔ One man- Extremely difficult and
Surveillance - is used when you should be avoided, if unavoidable
know or suspect that a person is at or keep the subject in view at all times.
will come to a known location, when ➔ Two-man- two agents are employed
you suspect that stolen goods are to to follow the subject.
be dropped or when informants have ➔ ABC method or Three-man- reduces
told you that a crime is going to be the risk of losing the subject, affords
committed. greater security agents detection
● Technical- surveillance by the use of ➔ Progressive/Leap frog method- poor
communications and electronic chances of obtaining good results,
hardware, gadgets, etc. agents are stationed at a fixed point
● Moving Surveillance/ Shadowing/ assuming that subject followed the
Tailing - simply the act of following same general route each day.
a person. ➔ Combined foot-auto surveillance-
employment of surveillant on foot
18. Kinds of surveillant and agents in an automobile.
The Following are the Kinds of Surveillance
(UST): 20. Common tricks of the subject in
surveillance
1. Undercover or roping – Is a form of 1. Test For Tailing = When the subject is
investigation in which the investigator conscious that he is being tailed while about
assumes a different and unofficial identity in to board a public conveyance, is to jump off
order to obtain information; an investigative the vehicle. If somebody also jumps off, he
technique in which the agent’s/investigator’s then recognizes the shadower, which will be
official identity is concealed to accomplish his basis for future recognition.
an investigative mission.
2. Use of Convoy = The subject employs
2. Surveillance of place (fixed/ stake-out) – other partners to detect if he is being tailed.
careful survey of the surrounding area The convoy which may employ the ABC
should be made. The character of the method would be very easy to detect
neighborhood, residents and transients shadowers. If the subject uses this, the
should be noted. The observation point shadower must be behind the convoy and
should be selected properly. When follow them instead.
observation is conducted from a ‘plant’,
surveillance agents must be extremely
careful not to reveal their true activity.
Observation may be made through a window
or other aperture so as to be unnoticed from
the outside. Venetian blinds afford the best
coverage, but may appear to be out of place
in some buildings.
3.Tailing or shadowing – Is the act of
following a person, depending on the
number of surveillant available, volume of
pedestrian traffic and importance of
concealing the surveillance.
You might also like
- Police Intelligence ReviewerDocument12 pagesPolice Intelligence ReviewerBimboy Cueno100% (8)
- Historical Setting of IntelligenceDocument35 pagesHistorical Setting of IntelligenceHarrison sajor100% (3)
- Police Intelligence LECTURESDocument7 pagesPolice Intelligence LECTURESSänä ÄĺĺNo ratings yet
- Cdi Ass Ni MaxDocument9 pagesCdi Ass Ni MaxJulius Evia PajoteaNo ratings yet
- Cdi Ass Ni MaxDocument9 pagesCdi Ass Ni MaxJulius Evia PajoteaNo ratings yet
- Week 10Document25 pagesWeek 10Eduardo FriasNo ratings yet
- Cdin 1 ReviewerDocument165 pagesCdin 1 ReviewerNicko SalinasNo ratings yet
- Police Intelligence GANDER FCDocument84 pagesPolice Intelligence GANDER FCAngel King RelativesNo ratings yet
- Complete Reviewer For IntelligenceDocument30 pagesComplete Reviewer For IntelligenceJuan TowTowNo ratings yet
- Lea Police Intelligence FinalDocument9 pagesLea Police Intelligence FinalLloyd Rafael EstabilloNo ratings yet
- Police Intel CeltechDocument116 pagesPolice Intel CeltechMark Allen PulidoNo ratings yet
- Police Intelligence: Dynamic Edge Learning SolutionsDocument82 pagesPolice Intelligence: Dynamic Edge Learning Solutionsdynamic_edge80% (5)
- Police IntelligenceDocument16 pagesPolice IntelligenceroxanneNo ratings yet
- IntelDocument9 pagesIntelJulia Rose Fabia febreoNo ratings yet
- Review Police IntelligenceDocument116 pagesReview Police IntelligenceKristine Joy100% (1)
- IntelligenceDocument92 pagesIntelligenceJeneva Castillo Abadilla100% (1)
- Review in Intel 2009Document25 pagesReview in Intel 2009Bernard AyudaNo ratings yet
- CDI FINAL Part 1Document14 pagesCDI FINAL Part 1Reyjun GulleNo ratings yet
- Police Intelligence BAGODocument14 pagesPolice Intelligence BAGOJudy Ann AciertoNo ratings yet
- Lea Intelligence Review NotesDocument9 pagesLea Intelligence Review NotesAnne MacarioNo ratings yet
- Memorandom FOR PNPDocument199 pagesMemorandom FOR PNPjudy an maquisoNo ratings yet
- Law Enforcement Administration Police IntelligenceDocument15 pagesLaw Enforcement Administration Police IntelligenceHanimah DimaocorNo ratings yet
- Police IntelligenceDocument94 pagesPolice IntelligenceSeagal Umar67% (3)
- Intel RevDocument3 pagesIntel RevLianne DarauayNo ratings yet
- Introduction To IntelligenceDocument7 pagesIntroduction To IntelligenceJudilyn RavilasNo ratings yet
- Intel Finals ModDocument11 pagesIntel Finals ModbnalibhanNo ratings yet
- (Lea) Police IntelligenceDocument30 pages(Lea) Police IntelligenceShania MadridondoNo ratings yet
- Clarin, Jean Rai-Anne S. - Cdi - 1Document8 pagesClarin, Jean Rai-Anne S. - Cdi - 1Camille ClarinNo ratings yet
- Police Intel LectureDocument185 pagesPolice Intel LectureRoxanne CalabonNo ratings yet
- Review Notes On Law Enforcement Administration Sjit Criminology Cl-Mabikas 2014Document30 pagesReview Notes On Law Enforcement Administration Sjit Criminology Cl-Mabikas 2014hamlet DanucoNo ratings yet
- Brief of Lea - Polc IntelDocument95 pagesBrief of Lea - Polc IntelJimmySyNo ratings yet
- Police Intelligence Review Notes-DONEDocument14 pagesPolice Intelligence Review Notes-DONEMariz Altizo ParconNo ratings yet
- Cdin 1Document7 pagesCdin 1Bea SalazarNo ratings yet
- Notes LEA 2.2Document30 pagesNotes LEA 2.2JabbarNo ratings yet
- CDI IntelligenceDocument51 pagesCDI Intelligencenasmyr.salisip85No ratings yet
- Cri169 Mod10-16Document9 pagesCri169 Mod10-16potchi devsNo ratings yet
- Police Intelligence Reviewer - BigwasDocument35 pagesPolice Intelligence Reviewer - BigwasRile NyleveNo ratings yet
- Article Byzantine IntelligenceDocument8 pagesArticle Byzantine Intelligencerajcic66No ratings yet
- IntelligenceDocument51 pagesIntelligenceMelanie HadiNo ratings yet
- CDI 101 Hand-Outs FinalsDocument23 pagesCDI 101 Hand-Outs FinalsEugene YuNo ratings yet
- Espionage: Espionage (Colloquially, Spying) Is The ObtainingDocument10 pagesEspionage: Espionage (Colloquially, Spying) Is The ObtainingRonaldNo ratings yet
- Cdi101 IntelDocument110 pagesCdi101 IntelNatores Palangga JoyNo ratings yet
- Police IntelligenceDocument12 pagesPolice IntelligenceRandy OboNo ratings yet
- Police IntelligenceDocument11 pagesPolice IntelligencePaul Espinosa75% (4)
- LEA 4 Police IntelDocument6 pagesLEA 4 Police IntelTerrencio Reodava100% (2)
- Fundamentals of Criminal Investigation and Intelligence CDI 121Document6 pagesFundamentals of Criminal Investigation and Intelligence CDI 121Jamaica Vacalares BugsahanNo ratings yet
- Pre-Final Examination MurilloooDocument3 pagesPre-Final Examination MurilloooPrincess Mae QuinoNo ratings yet
- Police IntelligenceDocument12 pagesPolice IntelligenceGeb Galagala100% (1)
- Exit AssessmentDocument5 pagesExit AssessmentSaybel Nangcas EsguerraNo ratings yet
- V Police IntelligenceDocument7 pagesV Police IntelligenceGaudia CdtNo ratings yet
- Notes For Intel LectureDocument10 pagesNotes For Intel LectureOcyub Avlas OdnamraNo ratings yet
- Lea 4 ReviewDocument116 pagesLea 4 ReviewJaden Fate SalidaNo ratings yet
- Police Intel WordDocument68 pagesPolice Intel WordAnonymous 9URsQ281xNo ratings yet
- Jess Intelligence OctagonDocument31 pagesJess Intelligence OctagonSilver LisingNo ratings yet
- History of Surveillance: From Espionage to Cyber Intelligence in Military OperationsFrom EverandHistory of Surveillance: From Espionage to Cyber Intelligence in Military OperationsNo ratings yet
- Espionage: Clandestine Tactics, Unveiling the Shadows of WarfareFrom EverandEspionage: Clandestine Tactics, Unveiling the Shadows of WarfareNo ratings yet
- My Friends, The Enemy: Life in Military Intelligence During the Falklands WarFrom EverandMy Friends, The Enemy: Life in Military Intelligence During the Falklands WarNo ratings yet
- A Brief Theory of Spycraft: Weaving the Tangled WebFrom EverandA Brief Theory of Spycraft: Weaving the Tangled WebNo ratings yet
- Audax ResultDocument8 pagesAudax ResultMoises CalastravoNo ratings yet
- Data Spare Part DatangDocument7 pagesData Spare Part DatangThaufan WijayaNo ratings yet
- Korean WarDocument6 pagesKorean WarDaniel AhnNo ratings yet
- Project 2 Digital LogicDocument4 pagesProject 2 Digital LogicJesusNo ratings yet
- Tsecet 2023Document5 pagesTsecet 2023naganathNo ratings yet
- Data Visualization With Python and JavaScript, 2nd Edition Kyran Dale Full ChapterDocument24 pagesData Visualization With Python and JavaScript, 2nd Edition Kyran Dale Full Chaptershoebvanoss100% (5)
- Siege of Tyre I. A. Objectives of The Study: Have An In-Depth Analysis in Presenting The StrategicDocument4 pagesSiege of Tyre I. A. Objectives of The Study: Have An In-Depth Analysis in Presenting The StrategicKim N. BurgosNo ratings yet
- ATMIS Officially Hands Over Forward Operating Bases To The Federal Government of SomaliaDocument6 pagesATMIS Officially Hands Over Forward Operating Bases To The Federal Government of SomaliaAMISOM Public Information ServicesNo ratings yet
- Grade 10 CS Year Plan 2020 - 21Document12 pagesGrade 10 CS Year Plan 2020 - 21Farhad AhmedNo ratings yet
- Parmar: Monthly Current AffairsDocument45 pagesParmar: Monthly Current AffairsSomya BansalNo ratings yet
- Comunicare StrategicaDocument55 pagesComunicare Strategicadiablero999100% (1)
- How and Why Did The Soviet Union CollapseDocument2 pagesHow and Why Did The Soviet Union CollapseRalph Ryan SilvestreNo ratings yet
- U BookFile Studies54No2 Extracts WebBook 19june PDFDocument114 pagesU BookFile Studies54No2 Extracts WebBook 19june PDFMilivoje JaukovicNo ratings yet
- Lesson PlanDocument101 pagesLesson PlanNaman MaheshwariNo ratings yet
- 06-Neither Skepticism Nor Romanticism - The ASEAN Regional Forum As A Solution For The Asia-PacifiDocument20 pages06-Neither Skepticism Nor Romanticism - The ASEAN Regional Forum As A Solution For The Asia-PacifiFadel MuhammadNo ratings yet
- C1 AMG Monthly Report December 2023Document38 pagesC1 AMG Monthly Report December 2023ferdinanNo ratings yet
- Richard Boyle: GI Revolts - The Breakdown of The US Army in VietnamDocument35 pagesRichard Boyle: GI Revolts - The Breakdown of The US Army in VietnamBloom100% (1)
- A Study On Effectiveness of Adr Methods and Mechanisms in TiruchirapalliDocument5 pagesA Study On Effectiveness of Adr Methods and Mechanisms in Tiruchirapallinivedidha arulselvamNo ratings yet
- 80 Years of Memorial Complex February 12thDocument126 pages80 Years of Memorial Complex February 12thNebojsa OzimicNo ratings yet
- Battle Masters Advanced Rulebook V1.0Document24 pagesBattle Masters Advanced Rulebook V1.0Jonathan TownsendNo ratings yet
- History 2020 Final Exam Study GuideDocument4 pagesHistory 2020 Final Exam Study GuideWill HallmarkNo ratings yet
- P222154201Document21 pagesP222154201luis alberto silva caicedoNo ratings yet
- More Truth Revealed by Bill BrockbraderDocument8 pagesMore Truth Revealed by Bill BrockbraderCharles Edward FrithNo ratings yet
- De Thi Mon CS Cong Nghe CTM FMMT330825Document7 pagesDe Thi Mon CS Cong Nghe CTM FMMT330825hoan thanhNo ratings yet
- 1Document27 pages1kororo1937No ratings yet
- Hydrophilia Rulebook 1.1Document14 pagesHydrophilia Rulebook 1.1Algan Algan100% (1)
- (Download PDF) Art of Being Human 11th Edition Janaro Test Bank Full ChapterDocument24 pages(Download PDF) Art of Being Human 11th Edition Janaro Test Bank Full Chaptertembybekie26100% (7)
- Compare and Contrast of Each of The FollowingDocument3 pagesCompare and Contrast of Each of The FollowingObrador , Munallet B.No ratings yet
- Martin Luther King. Answer KeyDocument1 pageMartin Luther King. Answer KeyOleg MuhendisNo ratings yet
- Sri Dasamgranthpart OneDocument145 pagesSri Dasamgranthpart OneGurchet singhNo ratings yet