Professional Documents
Culture Documents
Networks Protocols
Networks Protocols
Uploaded by
nyashamagutsa930 ratings0% found this document useful (0 votes)
5 views15 pagesNetwork protocols allow devices to communicate over a network by establishing rules and procedures for transmission of data. Common network protocols include HTTP for transferring web pages, FTP for file transfers but no encryption, SMTP for email transmission, and TCP/IP as the core internet protocol suite which includes IP for addressing and packet transmission and TCP for reliable data delivery. Other protocols include POP and IMAP for accessing email on servers, and VoIP for voice calls over internet.
Original Description:
Original Title
NetworksProtocols
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentNetwork protocols allow devices to communicate over a network by establishing rules and procedures for transmission of data. Common network protocols include HTTP for transferring web pages, FTP for file transfers but no encryption, SMTP for email transmission, and TCP/IP as the core internet protocol suite which includes IP for addressing and packet transmission and TCP for reliable data delivery. Other protocols include POP and IMAP for accessing email on servers, and VoIP for voice calls over internet.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
Download as pdf or txt
0 ratings0% found this document useful (0 votes)
5 views15 pagesNetworks Protocols
Networks Protocols
Uploaded by
nyashamagutsa93Network protocols allow devices to communicate over a network by establishing rules and procedures for transmission of data. Common network protocols include HTTP for transferring web pages, FTP for file transfers but no encryption, SMTP for email transmission, and TCP/IP as the core internet protocol suite which includes IP for addressing and packet transmission and TCP for reliable data delivery. Other protocols include POP and IMAP for accessing email on servers, and VoIP for voice calls over internet.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
Download as pdf or txt
You are on page 1of 15
NETWORK PROTOCOLS
A protocol is a set of communication rules and
procedures that all communicating devices must agree
to confirm in order to establish a meaningful
transmission of data.
So when two computers connect with a particular
protocol, they can talk to each other no matter what
operating system they are using.
Benefits of protocols:
i) Hardware devices from different manufactures can
work together
ii) Manufactures of different networking devices can
concentrate certain hardware devices
HYPER TEXT TRANSFER PROTOCOL (HTTP)
-Hypertext is the programming language that
is used for creating web pages.
-Http is used for transferring web pages to
your browser.
- When you type in a web address, it is
preceded by http://www.uz.ac.zw.
- The http tells the remote-computer that you
want to connect to its web-server.
FILE TRANSFER PROTOCOL (FTP)
-This is used to upload or download files
from another computer.
- FTP has no security to data as the data is not
encrypted prior to its transmission.
SIMPLE MAIL TRANSFER PROTOCOL (SMTP)
- Used to transfer e-mail messages between
computers.
- When you request your e-mail using your
mail-client such as Microsoft Outlook, it
connects to the mail server using the mail-
protocol.
- This enables e-mail to be delivered.
TERMINAL EMULATION LOCAL NETWORK
(TELNET)
- It allows a computer user to gain access to
another computer and use its software and
data as if it were a normal terminal on its
local network.
- Once the PC has initiated the emulation,
the user can log onto the remote computer
and view anything on the remote computer
that s/he has privileges to do.
INTERNET CONTROL MESSAGE PROTOCOL
(ICMP)
- It provides troubleshooting, control and
error messages when devices on a network
communicate.
- For example, routers generate error
messages to the source address when
network problems prevent delivery of
packets of data.
POINT –TO-POINT PROTOCOL
- It is usedbetween individual users and their
internet service provider, when using a
telephone line.
- Used for dialing in to your service provider
and defines communication between two
computers to see how they are connected
directly.
- The internet service provider will access the
internet on the user's behalf using the
TCP/IP.
POST OFFICE PROTOCOL (POP)
- A standard email protocol mainly used to
receive emails from a server to an email client.
- POP3 allows users to download emails to their
- computers and have them read later. POP3
uses transport layer (4) ports
- 110 (default non-encrypted port) and 995
(secure).
INTERNET MESSAGE ACCESS PROTOCOL (IMAP)
- This email protocol is used for accessing email
on a remote web server from a client.
- IMAP can be thought of as a remote file server.
- It uses transport layer (4) ports 143 (default non
encrypted port) and 993 (secure).
SIMPLE MAIL TRANSFER PROTOCOL (SMTP)
- A protocol for transferring e-mail across
the Internet.
- You send e-mail with SMTP then the mail
is read using POP or IMAP.
WIRELESS APPLICATION PROTOCOL (WAP)
- It is a standard for mobile phones rules for
connecting mobile phone users to the
internet.
- It allows users to access information
instantly via hand-held wireless devices like
mobile phones, smartphones, pagers etc.
- WAP mobile phones can use e-mail, access
pages to get information etc.
VOICE OVER INTERNET PROTOCOL (VoIP)
-A technology that allows one to make voice
calls using a broadband Internet
connection instead of a regular (or analog)
phone line.
- VoIP runs both voice and data
communications over a single network,
which can significantly reduce
infrastructure costs.
- The advantage is that as the internet carries
the actual voice traffic , VoIP can be free or
cost much less than a telephone call
especially over long distances.
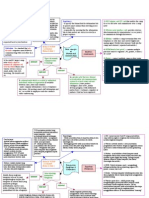
INTERNET PROTOCOL SUITE
- It is made up of the following:
i) TRANSMISSION CONTROL PROTOCOL (TCP)
ii) INTERNET PROTOCOL (IP)
- It is a suite of communication protocols
used to interconnect network devices on the
internet.
- TCP/IP can also be used as a
communications protocol in a private
network (intranet or extranet)
- Provides the services of exchanging data
directly between two networked computers.
- It sends data as packets across a network to its
correct destination.
- It checks for and resend lost packets, and
reassemble packets in the correct sequence.
- It contain addresses that identify the sending
computer and the receiving computer
- IP packet contains a self-destructive counter
that limits its lifetime so that the Internet
doesn't get overloaded with broken packets
wandering aimlessly in the channel.
USER DATAGRAM PROTOCOL (UDP)
- Performs the same function as the TCP but
sends messages called datagrams instead of
individual packets like the TCP does.
- In addition, UDP does not provides error
and flow control mechanism as TCP does.
RESEARCH WORK
- Explain the 7 layers of the Open System Interconnection
(OSI) model
Layer 7 - Application Layer, Layer 6 - Presentation
Layer 5 - Session Layer, Layer 4 - Transport Layer
Layer 3 - Network Layer, Layer - Data Link Layer
Layer 1 - Physical Layer
- Identify the layers in which the above protocols are found.
- Make a detailed comparison between the OSI model and
the TCP/IP suite.
You might also like
- Packet Sniffer Project DocumentDocument90 pagesPacket Sniffer Project DocumentAshish Katlam70% (10)
- CCNP ENARSI 300 410 v5.2 Dumps ITExamAnswersDocument214 pagesCCNP ENARSI 300 410 v5.2 Dumps ITExamAnswersDOMINGOS MASSISSANo ratings yet
- KonelabDocument61 pagesKonelabАндрей Сырчин100% (1)
- Gateway ProConOSDocument32 pagesGateway ProConOSNorbertoNo ratings yet
- Kendriya Vidyalya School R.B.N.M Salboni: Name-Niraj Kumar Class - Xii Science Sub - Computer ScienceDocument13 pagesKendriya Vidyalya School R.B.N.M Salboni: Name-Niraj Kumar Class - Xii Science Sub - Computer ScienceSourav SinghNo ratings yet
- Unit 1 NotesDocument24 pagesUnit 1 Notessonal rajNo ratings yet
- TCP IpDocument36 pagesTCP IpMonisha MoniNo ratings yet
- Importance: How Its Work: Protocol TCP/IP (Or Internet Protocol Suite)Document2 pagesImportance: How Its Work: Protocol TCP/IP (Or Internet Protocol Suite)aisyahjadinNo ratings yet
- Importance: How Its Work: Protocol TCP/IP (Or Internet Protocol Suite)Document2 pagesImportance: How Its Work: Protocol TCP/IP (Or Internet Protocol Suite)Aidaa AzmanNo ratings yet
- Final Test SieteDocument4 pagesFinal Test SieteOmokoNo ratings yet
- Network Protocols7Document12 pagesNetwork Protocols7nitashach22No ratings yet
- Lesson 3 Internet ProtocolsDocument37 pagesLesson 3 Internet ProtocolsReign Jay FerrerNo ratings yet
- Network Protocols7Document12 pagesNetwork Protocols7nitashach22No ratings yet
- TCP/IP Protocols: Ibrahim I. Banat, Computer Science, AL-Hussein Bin Talal University, Maan-JordanDocument10 pagesTCP/IP Protocols: Ibrahim I. Banat, Computer Science, AL-Hussein Bin Talal University, Maan-JordanDer1991ChefNo ratings yet
- Internet WorkingDocument3 pagesInternet WorkingGoutami ChNo ratings yet
- Class XII (As Per CBSE Board) : Computer ScienceDocument18 pagesClass XII (As Per CBSE Board) : Computer ScienceSuchit KumarNo ratings yet
- Packet Switching: GROUP 2: Understanding Network Protocols I. Definition of Network ProtocolsDocument18 pagesPacket Switching: GROUP 2: Understanding Network Protocols I. Definition of Network ProtocolsLiezl LagrimasNo ratings yet
- Unit-2 Study Material Part-2Document10 pagesUnit-2 Study Material Part-2Himadri BhardwajNo ratings yet
- Unit 2 - Advance Computer Networks - WWW - Rgpvnotes.inDocument21 pagesUnit 2 - Advance Computer Networks - WWW - Rgpvnotes.inprince keshriNo ratings yet
- Lesson 3Document35 pagesLesson 3Bhon-Bhon AgcaoiliNo ratings yet
- Tcp/Ip Protocol SuiteDocument17 pagesTcp/Ip Protocol Suitemadhavi gulhaneNo ratings yet
- Unit 5 (CSS)Document9 pagesUnit 5 (CSS)hasansyedamanNo ratings yet
- Assignment 1Document18 pagesAssignment 1Kushal BajracharyaNo ratings yet
- Questions and Answers - ProtocolsDocument4 pagesQuestions and Answers - ProtocolsVishal PaupiahNo ratings yet
- Email SMTP: Protocol E-Mail Servers Internet E-Mail Client POP Imap Configure ApplicationDocument11 pagesEmail SMTP: Protocol E-Mail Servers Internet E-Mail Client POP Imap Configure ApplicationIrish Bianca Usob LunaNo ratings yet
- Network Protocols: Presented By: Ns-Sarah Shiraz Ns-Sabaina HaroonDocument40 pagesNetwork Protocols: Presented By: Ns-Sarah Shiraz Ns-Sabaina HaroonSamin AfnanNo ratings yet
- Notes e CommerceDocument83 pagesNotes e CommerceSawmya ShanmuganathanNo ratings yet
- Computer Network Protocols and IPaddressDocument44 pagesComputer Network Protocols and IPaddressolive tabernaNo ratings yet
- Is Unit2Document63 pagesIs Unit2002Aadika BhatiaIT1No ratings yet
- Network Protocols6Document17 pagesNetwork Protocols6Rohan ManeNo ratings yet
- CCNA by HiwotDocument35 pagesCCNA by Hiwothiwot kebedeNo ratings yet
- Network ProtocolsDocument6 pagesNetwork ProtocolsAnne Margaret EscobalNo ratings yet
- Network Protocols7Document18 pagesNetwork Protocols7malathiNo ratings yet
- IncredibleDocument2 pagesIncredibleDemixNo ratings yet
- Network-Protocols and StandardsDocument17 pagesNetwork-Protocols and StandardsMuñoz, Jian Jayne O.No ratings yet
- Network Protocols PDFDocument25 pagesNetwork Protocols PDFDhruv MishraNo ratings yet
- Networking Data Link Protocol Networking Nodes Authentication Encryption CompressionDocument9 pagesNetworking Data Link Protocol Networking Nodes Authentication Encryption CompressionAdit LalNo ratings yet
- Research Work It301Document9 pagesResearch Work It301Jr Gadiano GallardoNo ratings yet
- Network LabDocument8 pagesNetwork LabTanusri GhoshNo ratings yet
- CHAPTER 04 (Network)Document40 pagesCHAPTER 04 (Network)Mihirete BantegegnNo ratings yet
- Newtwork Terms QuizDocument2 pagesNewtwork Terms Quiznur celonNo ratings yet
- E Commerce Chap 2Document21 pagesE Commerce Chap 2CloudKitNo ratings yet
- MDU Ist Sem - Explain TCP/IP ModelDocument2 pagesMDU Ist Sem - Explain TCP/IP ModelSandeep RathiNo ratings yet
- Internet Server Management L1Document7 pagesInternet Server Management L1chamunorwa100% (1)
- Internet PresentationDocument27 pagesInternet Presentationkamolideen07026No ratings yet
- IPT Communications FatmuscleDocument30 pagesIPT Communications Fatmusclecicelly linneNo ratings yet
- Iv Ecom Questions & AnswereDocument10 pagesIv Ecom Questions & AnswereSaratha Anbu ArasuNo ratings yet
- Inernet and IntranetDocument26 pagesInernet and IntranetHimal BhattaraiNo ratings yet
- 1 StudyDocument7 pages1 StudyAman GoyalNo ratings yet
- Bao-Idang, Chaermalyn D.Document5 pagesBao-Idang, Chaermalyn D.Chaermalyn Bao-idangNo ratings yet
- Interfaces: Medium Access ControlDocument6 pagesInterfaces: Medium Access ControlnaziaNo ratings yet
- DCN TCP AssignmentDocument11 pagesDCN TCP Assignmenttalwandi bhindranNo ratings yet
- Network ProtocolsDocument13 pagesNetwork ProtocolspallaB ghoshNo ratings yet
- How Internet WorksDocument27 pagesHow Internet Worksnfhs_anaNo ratings yet
- Intranet Extranet: Layer Packet Internet Protocol AddressDocument1 pageIntranet Extranet: Layer Packet Internet Protocol AddresssindhuponnusamyNo ratings yet
- Assignment 2 NDaMDocument3 pagesAssignment 2 NDaMKenneth SentillasNo ratings yet
- Chapter OneDocument13 pagesChapter OnemenbereNo ratings yet
- Network Protocols: Dr. Ahmed MusaDocument16 pagesNetwork Protocols: Dr. Ahmed MusaAkram TaNo ratings yet
- Cyber Security Module 1 Lesson 1 NotesDocument11 pagesCyber Security Module 1 Lesson 1 NotesAnshpreet SinghNo ratings yet
- Network Layer Samia'Document10 pagesNetwork Layer Samia'Dark GardianNo ratings yet
- Communication and Internet TechnologiesDocument9 pagesCommunication and Internet Technologiesmuhammad hussainNo ratings yet
- IoT EndsemDocument151 pagesIoT EndsemAdyasha mishraNo ratings yet
- Hacking Network Protocols: Unlocking the Secrets of Network Protocol AnalysisFrom EverandHacking Network Protocols: Unlocking the Secrets of Network Protocol AnalysisNo ratings yet
- 6383 13501 1 PBDocument5 pages6383 13501 1 PBnyashamagutsa93No ratings yet
- NETWORKINGDocument9 pagesNETWORKINGnyashamagutsa93No ratings yet
- Pricing Strategies in Business Teacher InstructionsDocument2 pagesPricing Strategies in Business Teacher Instructionsnyashamagutsa93No ratings yet
- Networking PresentationDocument8 pagesNetworking Presentationnyashamagutsa93No ratings yet
- Critical Path Analysis (MR Kaybee)Document7 pagesCritical Path Analysis (MR Kaybee)nyashamagutsa93No ratings yet
- Acc P1 2022 A QPDocument9 pagesAcc P1 2022 A QPnyashamagutsa93No ratings yet
- Acc A N11 p3 MsDocument4 pagesAcc A N11 p3 Msnyashamagutsa93No ratings yet
- Acc p3 J2023 A Level MsDocument8 pagesAcc p3 J2023 A Level Msnyashamagutsa93No ratings yet
- OSI ModelDocument2 pagesOSI ModelJoshNo ratings yet
- Mvi56e MCMMCMXT User ManualDocument217 pagesMvi56e MCMMCMXT User ManualJason PerezNo ratings yet
- Printed Manual: © 1999-2011 AGG SoftwareDocument54 pagesPrinted Manual: © 1999-2011 AGG Softwareนายธีรพงษ์ บุญพาNo ratings yet
- C122 ImVision User Guide Jul 12Document17 pagesC122 ImVision User Guide Jul 12Josel ArevaloNo ratings yet
- SAP IDOC InformationDocument23 pagesSAP IDOC Informationyalamanchili111No ratings yet
- TView WinDiags User ManualDocument32 pagesTView WinDiags User ManualMARIANANo ratings yet
- Rip, Eigrp, Ospf and AclDocument105 pagesRip, Eigrp, Ospf and AclCharu Mathur0% (1)
- COMP1406 Ch12 NetworkProgrammingDocument22 pagesCOMP1406 Ch12 NetworkProgrammingainnNo ratings yet
- Iec 61850 SepamDocument104 pagesIec 61850 Sepamnotsag001No ratings yet
- IBM Storwize V7000 and SANSlide Implementation PDFDocument52 pagesIBM Storwize V7000 and SANSlide Implementation PDFAnton SoNo ratings yet
- Excelerator Example OoxmlDocument30 pagesExcelerator Example OoxmlMiguel Ángel Macías MartínezNo ratings yet
- Avaya Hardware InstalationDocument146 pagesAvaya Hardware InstalationMidhun PvNo ratings yet
- SP5050 S v2 ManualDocument70 pagesSP5050 S v2 ManualkalabendaNo ratings yet
- Logic Controller - Modicon M241 - TM241CE24RDocument13 pagesLogic Controller - Modicon M241 - TM241CE24RGameONNo ratings yet
- Panasonic KX TDE100 200 600 Programming Virtual SIP CardDocument60 pagesPanasonic KX TDE100 200 600 Programming Virtual SIP CardAndres H. AcevedoNo ratings yet
- 3.3.3.3 Packet Tracer - Explore A Network (Answer)Document5 pages3.3.3.3 Packet Tracer - Explore A Network (Answer)magesswary100% (1)
- B Qos Cg43xasrDocument230 pagesB Qos Cg43xasrbeletraNo ratings yet
- PeopleCert ExamShield Technical Details PDFDocument11 pagesPeopleCert ExamShield Technical Details PDFfranciscoNo ratings yet
- Teldat Dm702-I TCP IPDocument64 pagesTeldat Dm702-I TCP IPTeodoro SosaNo ratings yet
- IP Active Performance Measurement (SRAN10.1 - 04)Document64 pagesIP Active Performance Measurement (SRAN10.1 - 04)Pragati VatsaNo ratings yet
- Esp 8266 Reference SheetDocument24 pagesEsp 8266 Reference Sheethmgp1975100% (4)
- Unit-II 21CSC202J OperatingSystemDocument156 pagesUnit-II 21CSC202J OperatingSystemramhacker2004No ratings yet
- Chapter 3 - VLANs Part 1Document53 pagesChapter 3 - VLANs Part 1Fasy AwanNo ratings yet
- Quantify Admin Guide - System Management - 2018Document103 pagesQuantify Admin Guide - System Management - 2018shaun_okeefe_1No ratings yet
- Iscp RCV 103Document22 pagesIscp RCV 103monismsantosNo ratings yet
- P 1 UsermDocument350 pagesP 1 UsermElliotNo ratings yet
- Cisco TAC Entry Training - 9 - Network Address Translation (NAT)Document40 pagesCisco TAC Entry Training - 9 - Network Address Translation (NAT)FerasHamdanNo ratings yet