Professional Documents
Culture Documents
Malware Analysis Syllabus
Malware Analysis Syllabus
Uploaded by
kunalsisodiacseOriginal Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Malware Analysis Syllabus
Malware Analysis Syllabus
Uploaded by
kunalsisodiacseCopyright:
Available Formats
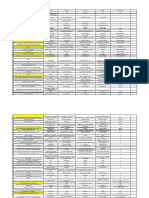
INT251:MALWARE ANALYSIS AND CYBER DEFENCE
L:2 T:0 P:2 Credits:3
Course Outcomes: Through this course students should be able to
CO1 :: understand major defense strategies to secure operation centers
CO2 :: analyze the behavior of the malware and its interaction with the system
CO3 :: gain the basics of assembly Language and the necessary skills required to perform code
analysis
CO4 :: analyze the stealth techniques used by advanced malware to hide from Forensic tools
CO5 :: apply the malware forensic techniques to investigate advanced malware
CO6 :: identify major defense strategies to secure operation centers
Unit I
Introduction to malware analysis : introduction to malware, types of malware, malware analysis,
types of malware analysis
Static Analysis : determining file type, fingerprinting malware, multiple anti-virus scanning,
extracting strings, determining file obfuscation, Inspecting PE header information, Comparing and
classifying malware
Unit II
Dynamic Analysis : dynamic analysis steps, analysing malware, DLL analysis
Assembly language and disassembly primer : introduction to assembly language basics,
registers, data transfer instructions, arithmetic operations, bitwise operations, branching and
conditionals,, loops and Functions, arrays and strings, structures and x64 architecture
Unit III
Disassembly using IDA : static code analysis, dissembling Windows API
Debugging malicious Binaries : general concepts of debugging, debugging binaries
Unit IV
Malware functionalities and persistence : malware functionalities, malware persistence methods
Code Injection and Hooking : virtual memory, user mode and kernel mode, code injection
techniques, hooking techniques
Unit V
Malware Obfuscation Techniques : simple encoding, malware encryption, custom encoding,
malware unpacking
Hunting Malware using Malware Forensics : memory forensics steps, memory acquisition,
volatility overview, enumerating processes, listing process handles, dumping executable and DLL,
listing network connections and Sockets, inspecting registry, investigating service, extracting
command history, listing DLL’s
Unit VI
Detecting advanced malware using memory forensics : detecting code injection, investigating
hollow process injection, detecting API hooks, kernel mode rootkits, listing kernel modules, I/O
processing, display device tress, detecting kernel space hooking, kernel call-backs and timers
Security Operation Center : Major defense strategies, Importance of SOC, SIEM, Importance of
SIEM, Case studies pertaining to SOC
List of Practicals / Experiments:
Identifying file type using manual method
• manual file identification using various methods
Identifying file type using tools
• CFF explorer
• Determining file type using python
Session 2023-24 Page:1/3
Fingerprinting the malware
• Generating cryptographic hash using tools
• Determining cryptographic hash in python
String extraction using tools
• Decoding obfuscated strings using FLOSS
Determining file obfuscation
• packers and cryptors
Detecting and inspecting pe and exports
• Detecting inspectingpe header information file obfuscation using exeinfo pe
• inspecting file dependencies and imports
• inspecting exports
• examining pe sectiontable and sections
• examining the compilation timestamp
• examining pe resources
Comparing and classifying the malware
• classifying malware using fuzzy hashing
• classifying malware using import hash
• classifying malware using section hash
• classifying malware using yara
Dynamic analysis method
• process inspection with process hacker
• determining system interaction with process monitor
• logging system activities using noriben
• capturing network traffic with wireshark
• simulating services with inetsim
Analyzing a malware executable
• static analysis of the sample
• dynamic analysis of the sample
Dynamic-Link Library (DLL) analysis
• analyzing the dll using rundll32.exe
• analyzing a dll with no exports
• analyzing a dll with exports
• analyzing a dll accepting export arguments
• analyzing a dll with process checks
Assembly and disassembly on disk
• analyzing the program on disk
• program disassembly(from machine code to assembly code)
• analyzing 32-bit executable on 64bit windows
Static code analysis disassembly using IDA
• loading binary in ida
• improving disassembly using ida
Session 2023-24 Page:2/3
Disassembling windows API
• understanding windows api
• windows api 32-bit and 64-bit comparison
Patching binary using IDA
• patching program bytes
• patching instructions
IDA scripting and plugins
• executing ida scripts
• ida python
• ida plugin
Malicious binaries dubugging
• debugging a binary using x64dbg
• debugging a malicious dll using x64dbg
Debugging a binary using IDA
• debugging malware executables
• debugging a malicious dll using ida
• debugger scripting using idapython
• determining files accessed by malware
References:
1. LEARNING MALWARE ANALYSIS by MONNAPPA K A, PACKT PUBLISHING
Session 2023-24 Page:3/3
You might also like
- The CSI Linux - Certified Investigator (CSIL-CI)Document2 pagesThe CSI Linux - Certified Investigator (CSIL-CI)rafaelmarcelocarmona100% (1)
- Malware SyllabusDocument2 pagesMalware SyllabusTri TrangNo ratings yet
- Syllabus - Malware Analysis and DevelopmentDocument4 pagesSyllabus - Malware Analysis and DevelopmentBhargav RajNo ratings yet
- Prakash Yadav: Ethical Hacker - Red Team SpecialistDocument2 pagesPrakash Yadav: Ethical Hacker - Red Team Specialistbinaryglitch008No ratings yet
- Int242 Cyber Security EssentialsDocument2 pagesInt242 Cyber Security EssentialsJenish ButaniNo ratings yet
- Malware AnalysisDocument35 pagesMalware AnalysisMansi SharmaNo ratings yet
- Gujarat Technological University Branch: Cyber Security (59) Subject Name: Malware Analysis SUBJECT CODE: 2725908 Semester: IiDocument3 pagesGujarat Technological University Branch: Cyber Security (59) Subject Name: Malware Analysis SUBJECT CODE: 2725908 Semester: IiRenugadevi NavaneethakrishnanNo ratings yet
- FRM Course Syllabus IPDownloadDocument2 pagesFRM Course Syllabus IPDownloadutsav mandalNo ratings yet
- Malware AnalysisDocument33 pagesMalware AnalysispjaironNo ratings yet
- Malware AnalysisDocument5 pagesMalware AnalysisRavi KumarNo ratings yet
- Certified Ethical Hacker: Course SpecificationsDocument6 pagesCertified Ethical Hacker: Course SpecificationsvarpaliaNo ratings yet
- 03 Behavioral 2023-24Document86 pages03 Behavioral 2023-24lorel17157No ratings yet
- Kaspersky Security TrainingDocument4 pagesKaspersky Security TrainingALEJANDRO GUTIERREZNo ratings yet
- Introduction To MalwareDocument86 pagesIntroduction To Malwareيُ يَNo ratings yet
- 01 IntroDocument41 pages01 IntroPrinceNo ratings yet
- Malware Analysis 27112023 055948pmDocument39 pagesMalware Analysis 27112023 055948pmAkhtar HussainNo ratings yet
- Basic MalwareDocument15 pagesBasic MalwareRin TohsakaNo ratings yet
- Blue Team ToolDocument72 pagesBlue Team ToolMurat100% (1)
- Malware AnalysisDocument2 pagesMalware AnalysisTariq MahmoodNo ratings yet
- Whitelisting 2018 Io TDocument27 pagesWhitelisting 2018 Io TTzi-cker ChiuehNo ratings yet
- Tilbury ISSA 2013Document36 pagesTilbury ISSA 2013trueholymindsNo ratings yet
- Awesome Penetration Testing DocumentationDocument32 pagesAwesome Penetration Testing DocumentationRizam Ali JavedNo ratings yet
- Reversing With Ghidra-InFILTRATE2020Document3 pagesReversing With Ghidra-InFILTRATE2020IVONo ratings yet
- CEH v9 NotesDocument39 pagesCEH v9 NotesGAMETICGUYNo ratings yet
- Updated ZeroLecture INT251Document22 pagesUpdated ZeroLecture INT251kunalsisodiacseNo ratings yet
- 2022 Cyber Defenders PlaybookDocument22 pages2022 Cyber Defenders PlaybookPathum Fernando100% (2)
- Certified Information Security Expert (CISE Level 1 v2) Detailed Course ModuleDocument18 pagesCertified Information Security Expert (CISE Level 1 v2) Detailed Course ModuleAmila KulathungaNo ratings yet
- How To Perform Long Term Monitoring of Careless Threat ActorsDocument40 pagesHow To Perform Long Term Monitoring of Careless Threat ActorsremremkNo ratings yet
- Malware Analyst Professional - Level 1 SyllabusDocument3 pagesMalware Analyst Professional - Level 1 SyllabusBhargav RajNo ratings yet
- Question Bank 1Document6 pagesQuestion Bank 1siri chandanaNo ratings yet
- CSL Module-3Document23 pagesCSL Module-3Gaurav WankhedeNo ratings yet
- Ethical Hacking Proactive TrainingDocument16 pagesEthical Hacking Proactive TrainingMarcelo JuniorNo ratings yet
- ChatGPT For Cybersecurity 3 1673855733Document40 pagesChatGPT For Cybersecurity 3 1673855733RuiNo ratings yet
- Chatgpt For Cybersecurity #2: Joas Antonio Dos SantosDocument40 pagesChatgpt For Cybersecurity #2: Joas Antonio Dos Santosshehriyar khanNo ratings yet
- Android MalwareDocument21 pagesAndroid MalwareTotuNo ratings yet
- Black Duck DatasheetDocument4 pagesBlack Duck DatasheetNguyễn LinhNo ratings yet
- Ceh V10Document97 pagesCeh V10Sachjith MNo ratings yet
- Certified Information Security Expert (CISE Level 1 v2) Detailed Course ModuleDocument18 pagesCertified Information Security Expert (CISE Level 1 v2) Detailed Course ModuleAkhil SreenadhNo ratings yet
- IA 400 Malware Analysis SyllabusDocument5 pagesIA 400 Malware Analysis SyllabusGowtham SadasivamNo ratings yet
- Chapter 2Document30 pagesChapter 2Dr. Myat Mon KyawNo ratings yet
- Ethical HackingDocument9 pagesEthical HackingobedNo ratings yet
- Malware DetectionDocument29 pagesMalware DetectionShahab KarimNo ratings yet
- Double-Layer Detection Model of Malicious PDF DocuDocument19 pagesDouble-Layer Detection Model of Malicious PDF DocunaybproductordeoroNo ratings yet
- Bai 3 Hoc May Va ATTTDocument25 pagesBai 3 Hoc May Va ATTTNguyễn ThànhNo ratings yet
- MIT6 858F14 q14 2 Review1Document16 pagesMIT6 858F14 q14 2 Review1jarod_kyleNo ratings yet
- Institute: Uie Department: Cse: Bachelor of Engineering (Computer Science & Engineering)Document29 pagesInstitute: Uie Department: Cse: Bachelor of Engineering (Computer Science & Engineering)sukhpreet singhNo ratings yet
- Hack IT Security Through Penetration TestingDocument575 pagesHack IT Security Through Penetration TestingRaja Mustafa0% (1)
- ch0 1Document75 pagesch0 1pjaironNo ratings yet
- Emerging Threats AkiraDocument27 pagesEmerging Threats AkiraShagy Agustin Reyes Palacios OroscoNo ratings yet
- Cyber Defenders Playbook 2023 (CyberProof) - 31pgDocument31 pagesCyber Defenders Playbook 2023 (CyberProof) - 31pgNewReaderNo ratings yet
- ch0 1Document78 pagesch0 1Yazan Al-NirabNo ratings yet
- ch0 1Document72 pagesch0 1Jayesh ShindeNo ratings yet
- Cyber Threat IntelligenceDocument41 pagesCyber Threat Intelligencekt06121999No ratings yet
- CT-19005 - Lab 3 - Malware AnalysisDocument5 pagesCT-19005 - Lab 3 - Malware AnalysisRAMESH KUMARNo ratings yet
- Web SOPDocument17 pagesWeb SOPhellomarty1221No ratings yet
- Unit 5 OffescDocument8 pagesUnit 5 OffescSathvik KunaNo ratings yet
- Hacker Tools, Techniques, Exploits, and Incident Handling Duration: 5 DaysDocument6 pagesHacker Tools, Techniques, Exploits, and Incident Handling Duration: 5 DaysRon Karl PalmaNo ratings yet
- 5 Days WorkshopDocument3 pages5 Days WorkshopVani SivaNo ratings yet
- The Shellcoder's Handbook: Discovering and Exploiting Security HolesFrom EverandThe Shellcoder's Handbook: Discovering and Exploiting Security HolesNo ratings yet
- Parts - Used: VendorsDocument27 pagesParts - Used: VendorsDanno NNo ratings yet
- EDFD 211: Psychological Foundations in Education First Semester SY 2016-17 Course DescriptionDocument4 pagesEDFD 211: Psychological Foundations in Education First Semester SY 2016-17 Course DescriptionLeezl Campoamor OlegarioNo ratings yet
- Lesson 2Document16 pagesLesson 2Vusani NeguyuniNo ratings yet
- Holy Family Academy of Gma, Inc.: Diocese of Imus Catholic Educational System, Inc. (DICESDocument2 pagesHoly Family Academy of Gma, Inc.: Diocese of Imus Catholic Educational System, Inc. (DICESellieneh21No ratings yet
- GrandStream GXV-3175 - User Manual EnglishDocument130 pagesGrandStream GXV-3175 - User Manual Englishซิสทูยู ออนไลน์No ratings yet
- PHP Viva QuestionsDocument8 pagesPHP Viva QuestionsFake AccountNo ratings yet
- STARS (SHE Tracking Analysis Reporting System) Plant ViewDocument18 pagesSTARS (SHE Tracking Analysis Reporting System) Plant ViewrajatNo ratings yet
- Semi-Detailed Lesson Plan: Teacher: Blessie Jean A. YbañezDocument3 pagesSemi-Detailed Lesson Plan: Teacher: Blessie Jean A. YbañezJENNIFER YBAÑEZNo ratings yet
- Final - Thesis Quantum Study Silicon NanowiresDocument154 pagesFinal - Thesis Quantum Study Silicon NanowiresChandra Bhal SinghNo ratings yet
- AREVA in NigerDocument20 pagesAREVA in Nigermushava nyokaNo ratings yet
- Enrollment FormDocument1 pageEnrollment Formvalupadasu VishvasNo ratings yet
- RelativityDocument9 pagesRelativity0hitk0No ratings yet
- Flygt Submersible Pumps: Water & WastewaterDocument2 pagesFlygt Submersible Pumps: Water & WastewaterRebeka ComercializadoraNo ratings yet
- ENVS 532: DR Assad Al-Thukair Associate ProfessorDocument16 pagesENVS 532: DR Assad Al-Thukair Associate ProfessorAbu Muhsin Al NgapakyNo ratings yet
- Jerry Goldsmith PaperDocument11 pagesJerry Goldsmith PaperKathleen Rose100% (2)
- Mobile Computing Multiple Choice Questions With Answers PDFDocument10 pagesMobile Computing Multiple Choice Questions With Answers PDFvikes singhNo ratings yet
- Pugh Method Example-2Document4 pagesPugh Method Example-2Shaikh AkhlaqueNo ratings yet
- GN No 333 Public Procurement (Amendment) Regulations, 2016Document45 pagesGN No 333 Public Procurement (Amendment) Regulations, 2016imran hameerNo ratings yet
- WHO Food Additives Series 59 2008Document479 pagesWHO Food Additives Series 59 2008jgallegosNo ratings yet
- BTS Power ManagementDocument21 pagesBTS Power ManagementSam FicherNo ratings yet
- Film ConventionsDocument9 pagesFilm ConventionsAnjali Kaur ChannaNo ratings yet
- DIY GREENHOUSE by KMS - ChangelogDocument4 pagesDIY GREENHOUSE by KMS - Changeloglm pronNo ratings yet
- A J-Protein Co-Chaperone Recruits BiP To Monomerize IRE1 and Repress The Unfolded Protein ResponseDocument27 pagesA J-Protein Co-Chaperone Recruits BiP To Monomerize IRE1 and Repress The Unfolded Protein ResponseLefan YuNo ratings yet
- Bearing Inspection SOPDocument7 pagesBearing Inspection SOPRianAwangga100% (1)
- Portable Boring MachineDocument2 pagesPortable Boring Machinesexmanijak100% (1)
- Siliporite Opx Pellets Revision 11 - 2017Document2 pagesSiliporite Opx Pellets Revision 11 - 2017Juan Victor Sulvaran Arellano100% (2)
- Impact of The New Malaysian IFSA 2013 Regulation On Takaful and ReTakaful OperatorsDocument3 pagesImpact of The New Malaysian IFSA 2013 Regulation On Takaful and ReTakaful OperatorsDilawar AheerNo ratings yet
- Streamline Modular Electronic Sounder: Model SLM700Document2 pagesStreamline Modular Electronic Sounder: Model SLM700GersonDarioOrtizReyesNo ratings yet
- Ngspice ManualDocument592 pagesNgspice ManualRommel Joshua OrtegaNo ratings yet
- Maseno Universit1Document9 pagesMaseno Universit1Simon MutuaNo ratings yet