Professional Documents
Culture Documents
Vetrivendan.L Publication1
Vetrivendan.L Publication1
Uploaded by
SonyCopyright:
Available Formats
You might also like
- Curling v. Raffensperger Transcript, Volume 11Document322 pagesCurling v. Raffensperger Transcript, Volume 11The FederalistNo ratings yet
- Governmnet Lesson Notes For SS1, SS2, SS3Document52 pagesGovernmnet Lesson Notes For SS1, SS2, SS3Oladejo kabir94% (71)
- Case Digest For Sanidad Vs COMELECDocument2 pagesCase Digest For Sanidad Vs COMELECDivineDionne100% (4)
- Kabataan Party-List Et Al. vs. ComelecDocument3 pagesKabataan Party-List Et Al. vs. ComelecJemarie ArisgaNo ratings yet
- Smart Voting System Support Through Face Recognition: April 2018Document6 pagesSmart Voting System Support Through Face Recognition: April 2018Kishore SmartNo ratings yet
- Voting MachineDocument18 pagesVoting Machinevivekanand_bonalNo ratings yet
- Smart Voting System Through Face Recognition UsingDocument6 pagesSmart Voting System Through Face Recognition UsingUnknown PersonNo ratings yet
- Handwritten Signature Verification Using Instance Based LearningDocument4 pagesHandwritten Signature Verification Using Instance Based Learningsurendiran123No ratings yet
- Online Voting Using Face Recognition and Password Based Security SystemDocument9 pagesOnline Voting Using Face Recognition and Password Based Security SystemGeremu TilahunNo ratings yet
- Project Report Facial RecognitionDocument11 pagesProject Report Facial RecognitionAbhinav SharmaNo ratings yet
- Literature Review 1Document12 pagesLiterature Review 1Abhinav SharmaNo ratings yet
- Mobile Based Facial Recognition Using OTP Verification For Voting SystemDocument6 pagesMobile Based Facial Recognition Using OTP Verification For Voting SystemAkash MauryaNo ratings yet
- Review and Comparison of Face Detection Algorithms: Kirti Dang Shanu SharmaDocument5 pagesReview and Comparison of Face Detection Algorithms: Kirti Dang Shanu SharmaKevin EnriquezNo ratings yet
- (IJETA-V8I5P3) :sujith Krishna B, Priyanka BasavaDocument3 pages(IJETA-V8I5P3) :sujith Krishna B, Priyanka BasavaIJETA - EighthSenseGroupNo ratings yet
- Emotion Classification of Facial Images Using Machine Learning ModelsDocument6 pagesEmotion Classification of Facial Images Using Machine Learning ModelsIJRASETPublicationsNo ratings yet
- A Biometric Fusion Based On Face and Fingerprint Recognition Using ANNDocument5 pagesA Biometric Fusion Based On Face and Fingerprint Recognition Using ANNEditor IJRITCCNo ratings yet
- Criminal Face Recognition System: Alireza Chevelwalla, Ajay Gurav, Sachin Desai, Prof. Sumitra SadhukhanDocument4 pagesCriminal Face Recognition System: Alireza Chevelwalla, Ajay Gurav, Sachin Desai, Prof. Sumitra SadhukhanMuhammad HamzaNo ratings yet
- Seminar Project - Face - RecognitionDocument58 pagesSeminar Project - Face - RecognitionItaliya BhaktiNo ratings yet
- Design A Biometric Identification System Based On The Fusion of Hand Geometry and Backhand Patterns Raid R. Al-NimaDocument12 pagesDesign A Biometric Identification System Based On The Fusion of Hand Geometry and Backhand Patterns Raid R. Al-Nimamais taherNo ratings yet
- Real-Time Face Detection From One Camera: 1. Research TeamDocument6 pagesReal-Time Face Detection From One Camera: 1. Research TeamMuhammad UlumNo ratings yet
- Automatic Attendance System Using MatlabDocument4 pagesAutomatic Attendance System Using MatlabIJRASETPublicationsNo ratings yet
- How To Write Thesis Proposal On Face RecognitionDocument5 pagesHow To Write Thesis Proposal On Face RecognitionRahajul Amin RajuNo ratings yet
- (IJCST-V7I2P7) :mary Celin AX, KM Fathima Farzana, Lija Jude, Sherwin J Vellayil, Abeera VPDocument4 pages(IJCST-V7I2P7) :mary Celin AX, KM Fathima Farzana, Lija Jude, Sherwin J Vellayil, Abeera VPEighthSenseGroupNo ratings yet
- Information Fusion in BiometricsDocument6 pagesInformation Fusion in BiometricsMeenakshi Nehra PooniaNo ratings yet
- Smart Voting System With Face RecognitionDocument3 pagesSmart Voting System With Face RecognitionInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- An Effective Technique For Expressing and Recognizing FeelingsDocument4 pagesAn Effective Technique For Expressing and Recognizing FeelingsWeb ResearchNo ratings yet
- Face Recognition Based Attendance Management System: Smitha, Pavithra S Hegde, AfshinDocument3 pagesFace Recognition Based Attendance Management System: Smitha, Pavithra S Hegde, AfshinZubia FNo ratings yet
- Designing of Face Recognition SystemDocument3 pagesDesigning of Face Recognition SystemMuzammil NaeemNo ratings yet
- Emotion Based Music Player Using CNNDocument5 pagesEmotion Based Music Player Using CNNIJRASETPublicationsNo ratings yet
- Face Recognition Using Gabor Filters: Muhammad SHARIF, Adeel KHALID, Mudassar RAZA, Sajjad MOHSINDocument5 pagesFace Recognition Using Gabor Filters: Muhammad SHARIF, Adeel KHALID, Mudassar RAZA, Sajjad MOHSINYuri BrasilkaNo ratings yet
- A Novel Approach For Content Retrieval From Recognition AlgorithmDocument5 pagesA Novel Approach For Content Retrieval From Recognition AlgorithmInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- A Robust, Low-Cost Approach To Face Detection and Face RecognitionDocument6 pagesA Robust, Low-Cost Approach To Face Detection and Face RecognitionNirmalendu KumarNo ratings yet
- Webcam Based Facial Recognition Using OTDocument6 pagesWebcam Based Facial Recognition Using OTlawalkehinde1919No ratings yet
- Seminar Report: Facial Recognition Systems and AlgorithmsDocument31 pagesSeminar Report: Facial Recognition Systems and AlgorithmsNithin O JacobNo ratings yet
- Face Recognition: Identifying Facial Expressions Using Back PropagationDocument5 pagesFace Recognition: Identifying Facial Expressions Using Back PropagationInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Chapter No Title Page - No List of Figures List of Tables IDocument47 pagesChapter No Title Page - No List of Figures List of Tables Ishanmugaraja85No ratings yet
- B F M G R S: Rightness Actor Atching For Esture Ecognition Ystem Using Scaled NormalizationDocument12 pagesB F M G R S: Rightness Actor Atching For Esture Ecognition Ystem Using Scaled NormalizationAnonymous Gl4IRRjzNNo ratings yet
- Research Paper Final - FRASDocument4 pagesResearch Paper Final - FRASpijowac169No ratings yet
- 2013 FaceRecognition Review IJCTADocument4 pages2013 FaceRecognition Review IJCTADharmavarapu indhujaNo ratings yet
- Age Gender and Emotion Identification Using Face RecognitionDocument3 pagesAge Gender and Emotion Identification Using Face RecognitionAnil Kumar BNo ratings yet
- Facial Expression Recognition System Using Haar Cascades ClassifierDocument9 pagesFacial Expression Recognition System Using Haar Cascades ClassifierIJRASETPublicationsNo ratings yet
- DigiVoter-Smart Voting System Using Biometrics-Based Facial FeaturesDocument8 pagesDigiVoter-Smart Voting System Using Biometrics-Based Facial FeaturesIJRASETPublicationsNo ratings yet
- Face Recognition PaperDocument7 pagesFace Recognition PaperPuja RoyNo ratings yet
- Automated Attendance Using Open CVDocument6 pagesAutomated Attendance Using Open CVManikyam HemalathaNo ratings yet
- Facial RecognitionDocument23 pagesFacial RecognitionChaithanya MannepalliNo ratings yet
- FRT KDocument20 pagesFRT KKaushik JaiswalNo ratings yet
- Seminar ShivaniDocument58 pagesSeminar ShivaniItaliya BhaktiNo ratings yet
- Implementation of Face Recognition Based Attendance System Using LBPHDocument3 pagesImplementation of Face Recognition Based Attendance System Using LBPHManikyam HemalathaNo ratings yet
- Handwritten Digit Recognition Using Image Processing and Neural NetworksDocument4 pagesHandwritten Digit Recognition Using Image Processing and Neural Networksibtesam2No ratings yet
- Ijaiem 2014 02 28 088Document4 pagesIjaiem 2014 02 28 088International Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Biometric Images Attacks Detecting Using Convolutional Neural NetworksDocument15 pagesBiometric Images Attacks Detecting Using Convolutional Neural NetworkscmgarciasilvaNo ratings yet
- 10 23919@mipro 2019 8756700Document6 pages10 23919@mipro 2019 8756700Prince KumarNo ratings yet
- IJIPVCV1I102Document4 pagesIJIPVCV1I102Journal Home e-PublicationNo ratings yet
- A Matlab Based Electronic Voting MachineDocument7 pagesA Matlab Based Electronic Voting MachineIJRASETPublicationsNo ratings yet
- A Real-Time Face Recognition System Using Eigenfaces: Daniel GeorgescuDocument12 pagesA Real-Time Face Recognition System Using Eigenfaces: Daniel GeorgescuAlex SisuNo ratings yet
- Face Detection and Recognition - A ReviewDocument8 pagesFace Detection and Recognition - A ReviewHenry MagdayNo ratings yet
- Face RecDocument25 pagesFace RecSahilaKhanNo ratings yet
- Andwritten Ignature Erification: ECE 533 - Project byDocument18 pagesAndwritten Ignature Erification: ECE 533 - Project byYukti KhuranaNo ratings yet
- Face Recognition Based Attendance System Using Haar Cascade and Local Binary Pattern Histogram AlgorithmDocument4 pagesFace Recognition Based Attendance System Using Haar Cascade and Local Binary Pattern Histogram AlgorithmShri RaamNo ratings yet
- 2013 FaceRecognition Review IJCTADocument4 pages2013 FaceRecognition Review IJCTAMohit SNo ratings yet
- Face Recognition Technology Seminar ReportDocument26 pagesFace Recognition Technology Seminar ReportParampreet Singh71% (7)
- Geometric Feature Learning: Unlocking Visual Insights through Geometric Feature LearningFrom EverandGeometric Feature Learning: Unlocking Visual Insights through Geometric Feature LearningNo ratings yet
- VTU Question Paper of 20MCA23 Web Technologies Feb-2022Document1 pageVTU Question Paper of 20MCA23 Web Technologies Feb-2022SonyNo ratings yet
- Time, Speed & DistanceDocument3 pagesTime, Speed & DistanceSonyNo ratings yet
- PHP IntroDocument18 pagesPHP IntroSonyNo ratings yet
- VTU Exam Question Paper With Solution of 18MCA51 Programming Using C#.NET Jan-2021-Ms Uma BDocument37 pagesVTU Exam Question Paper With Solution of 18MCA51 Programming Using C#.NET Jan-2021-Ms Uma BSonyNo ratings yet
- PartnershipDocument2 pagesPartnershipSonyNo ratings yet
- 18MCA51 - Nirupama B KDocument109 pages18MCA51 - Nirupama B KSonyNo ratings yet
- Ajax TutorialDocument2 pagesAjax TutorialSonyNo ratings yet
- PHP Patter MatchingDocument5 pagesPHP Patter MatchingSonyNo ratings yet
- InstantRails WorkingDocument10 pagesInstantRails WorkingSonyNo ratings yet
- Ajax ExamplesDocument1 pageAjax ExamplesSonyNo ratings yet
- VTU Question Paper of 18MCA51 Programming Using C# .Net Jan-2021Document2 pagesVTU Question Paper of 18MCA51 Programming Using C# .Net Jan-2021SonyNo ratings yet
- Ajaxapplicaion CreatingDocument62 pagesAjaxapplicaion CreatingSonyNo ratings yet
- VTU Question Paper of 16-17MCA52 Programming Using C# and .Net Jan-2021Document1 pageVTU Question Paper of 16-17MCA52 Programming Using C# and .Net Jan-2021SonyNo ratings yet
- Reviewer in CONSTI REV Part1Document4 pagesReviewer in CONSTI REV Part1bam zeppeleinNo ratings yet
- Perez vs. COMELECDocument7 pagesPerez vs. COMELECRaniel MirandaNo ratings yet
- Conversation Flashcards2Document14 pagesConversation Flashcards2Marie Thelma Benolirao RomarateNo ratings yet
- DH 0519Document10 pagesDH 0519The Delphos HeraldNo ratings yet
- Sec. 32 Subic Bay Metropolitan Authority v. COMELEC - DigestDocument2 pagesSec. 32 Subic Bay Metropolitan Authority v. COMELEC - DigestLorenzo Elegio IIINo ratings yet
- Aytona V Castillo GR L-19313Document27 pagesAytona V Castillo GR L-19313LalaLanibaNo ratings yet
- Fingerprint Voting SystemDocument6 pagesFingerprint Voting SystemKathleen CornejoNo ratings yet
- QUINN 4th Edition Computer ReliabilityDocument53 pagesQUINN 4th Edition Computer ReliabilityViveekdeep SinghNo ratings yet
- Shifter, 2011Document16 pagesShifter, 2011anotheruntoldstoryNo ratings yet
- 09-29-15 EditionDocument28 pages09-29-15 EditionSan Mateo Daily JournalNo ratings yet
- Catarman, CamiguinDocument2 pagesCatarman, CamiguinSunStar Philippine NewsNo ratings yet
- ABS-CBN Broadcasting Group vs. COMELEC, G.R. No. 133486Document9 pagesABS-CBN Broadcasting Group vs. COMELEC, G.R. No. 133486Inez Monika Carreon PadaoNo ratings yet
- Business Statistic Linear Programming ExerciseDocument3 pagesBusiness Statistic Linear Programming ExerciseSimon Gee0% (2)
- Libanan V HRETDocument2 pagesLibanan V HRETAnsai CaluganNo ratings yet
- 031 - Miranda v. AguirreDocument3 pages031 - Miranda v. Aguirrergtan3No ratings yet
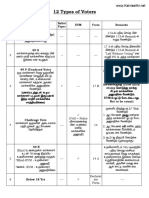
- 12 Types of VotersDocument13 pages12 Types of VotersAshok KumarNo ratings yet
- 2012 217Document88 pages2012 217Jaja Ordinario Quiachon-AbarcaNo ratings yet
- Germania, Proiect Iulia CraciunDocument5 pagesGermania, Proiect Iulia CraciunElenaNo ratings yet
- 2019 Indian General ElectionDocument24 pages2019 Indian General Electionharshika guptaNo ratings yet
- Bondoc Vs PinedaDocument3 pagesBondoc Vs PinedaMa Gabriellen Quijada-TabuñagNo ratings yet
- Assignment Malaysian StudiesDocument16 pagesAssignment Malaysian StudiesStephanny Sylvester100% (1)
- Election of Directors or Trustees.: Election and Voting Sec. 24Document25 pagesElection of Directors or Trustees.: Election and Voting Sec. 24markuslagan06No ratings yet
- Political Law.2Document120 pagesPolitical Law.2Rengie GaloNo ratings yet
- Labo vs. ComelecDocument3 pagesLabo vs. ComelecNico Delos TrinosNo ratings yet
- Travis Prete - Mini Unit WDDocument20 pagesTravis Prete - Mini Unit WDapi-298016754No ratings yet
Vetrivendan.L Publication1
Vetrivendan.L Publication1
Uploaded by
SonyOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Vetrivendan.L Publication1
Vetrivendan.L Publication1
Uploaded by
SonyCopyright:
Available Formats
ISSN (Online) 2394-2320
International Journal of Engineering Research in Computer Science and Engineering
(IJERCSE)
Vol 5, Issue 4, April 2018
Smart Voting System Support through Face
Recognition
[1]
L.Vetrivendan, [2]Dr.R.Viswanathan, [3]J.AngelinBlessy
[2]
Associate Professor, [1][3] Assistant Professor
[1][2][3]
Galgotias University
Abstract: In this paper a new authentication technique in online voting system using facial recognition of the voter is used. In
India, currently there are two types of voting system in practice. They are secret Ballet paper and Electronic Voting Machines
(EVM), but both of the process have some limitation or demerits. In India online voting has not been yet implemented. The current
voting system is not safe and secure too. The voters need to go to distributed places like polling booths and stand in a long queue to
cast their vote, because of these reasons most of the people misses their chance of voting. The voter who is not eligible can also cast
its vote by fake means which may leads to many problems. That’s why in this project we have to propose a system or way for
voting which is very effective or useful in voting. In our approach we have three level of security in voting process. The first level is
the verification of unique id number (UID), second level is the verification of election id number (EID) and third level is face
recognition or face matching. The security level of our system is greatly improved by the new application method for each voter.
The user authentication process of the system is improved by adding face recognition in an application which will identify whether
the particular user is authenticated user or not.
I. INTRODUCTION 2.NECESSITY: -
Now a day in India two types of method are used for
voting. [1] The first method is secret ballot paper, in
which lots of paper are used and [2] second method is
EVM (electronic voting machine) which is used since
2003. we have to propose a method or way for online
voting that is more secure than the existing system. In this
proposed project face detection and recognition concept is
used to identify the exact person. There are three levels of
verification were used for the voters in our proposed
system.
The first one is Unique id number verification, second
level of verification is election commission id or voter
card number, if your election commission id number is
correct then you have to go for third level of security
which is the main security level where the system
recognize the face of the real voter from the current
database of face images given by the election
commission. If the captured image is matched with the
respective image of the voter in the database, then a voter
can cast their vote in the election.as you have to know that
in existing system is not much more secure because in
existing system security level is only voter card so any
one can give other person vote with voter card but here
we proposed a way for voting which is more secure than
existing system.
In India people don’t Vote [3] for following reason as
shown in fig
All Rights Reserved © 2018 IJERCSE 203
ISSN (Online) 2394-2320
International Journal of Engineering Research in Computer Science and Engineering
(IJERCSE)
Vol 5, Issue 4, April 2018
used to capture the variation in a collection of face images
3. EXISTING SYSTEM: - and this information is use to encode the particular images
of individual faces. Then the encoded images of
In the current voting system, [3] the ballet machines individual faces are compared with the collection of face
where used in which the symbols of various political images in a holistic manner. The Eigen faces itself form a
parties are displayed. When we press the button with the basis set of all images used to construct the covariance
respective party’s (political party) symbol the voting is matrix. The formed smaller set of basis images are used to
done. The chance of fake person casting their vote is more represent the original training images which produces
in the existing system. The voting person may use the dimension reduction. By comparing how faces are
fake voting card and cast his vote, this may cause represented by the basis set, the classification can be
problem. In the existing system, the person has to travel achieved.
long places to his constituency to cast his vote. Therefore, Face Images are projected into a feature space (“Face
we need an effective method to identify the fake voters Space”) that best encodes the variation among known face
during voting. So, the images.
The face space is defined by the “eigenfaces”, which are
the eigenvectors of the set of faces.
Working of Eigen face algorithm:
Steps in Face Recognition
•Initialization:
Acquire the training set and calculate Eigen faces (using
PCA projections) which define Eigen space.
• When a new face is encountered, calculate its weight.
Fig.1 Exiting Voting Process scenario • Determine if the image is face.
•If yes, classify the weight pattern as known or unknown.
facial authentication process is used for detecting the right • (Learning) If the same unknown face is seen several
person and also making the system to work in online, times incorporate it into known faces.
which will help the voters to cast their vote from their Principal Component Analysis [7]
place itself. •Eigen face follows the Principal Component Analysis
approach, in which face space forms a cluster in image
4. PROPOSSED SYSTEM: - space.
In this project we are working with three different- PCA gives suitable representation
different security levels Calculation of Eigen faces
Level1: -Unique id number (UID) [4]. (1) Calculate average face: v.
At the time of voter registration system will request for (2) Collect difference between training images and
the unique id from the voter. The entered unique id is average face in matrix A (M by N), where M is the
verified from the database provide by the election number of pixels and N is the number of images.
commission. (3) The eigenvectors of covariance matrix C (M by M)
Level2: Election commission id card number. [5] give the Eigen faces.
In the second level of verification, the voter has to enter
the election commission id or voter’s id number. The
entered id number is verified from the database provide M is usually big, so this process would be time
by the election commission. consuming.
Level3: - Face recognition with respective election C AAT
commission id number.
•Calculation of Eigenvectors of C
In this level, Eigen face algorithm is used to verify the
If the number of data points is smaller than the
facial image of the voters from the database provided by
dimension (N<M), then there will be only N-1 meaningful
the election commission.
eigenvectors.
Eigen Face Algorithm:
Instead of directly calculating the eigenvectors of
The main concept of Eigen Face algorithm is to follow the
C, we can calculate the eigenvalues and the corresponding
appearance –based approach to face recognition [6]. It is
eigenvectors of a much smaller matrix L (N by N).
All Rights Reserved © 2018 IJERCSE 204
ISSN (Online) 2394-2320
International Journal of Engineering Research in Computer Science and Engineering
(IJERCSE)
Vol 5, Issue 4, April 2018
L AT A - Test set contains 16×3 images.
if λi are the eigenvectors of L then A λi are the Save average coefficients for each person. Classify new
eigenvectors for C. face as the person with the closest average.
The eigenvectors are in the descent order of the
corresponding eigenvalues.
Representation of Face Images using Eigen faces [8]:
The training face images and new face images can be
represented as linear combination of the Eigen faces.
When we have a face image u:
u aii
i
Since the eigenvectors are orthogonal:
ai u T i
First three Eigen faces:
Recognition accuracy increases with number of
eigenfaces till 15.
Later eigenfaces do not help much with recognition.
Best recognition rates
Training set - 99%
Test set - 89%
Overview over the Eigen Face algorithm:
Fig: High level functioning principle of the Eigen face-
based facial recognition algorithm
5. COMPARISONS OF BOTH THE SYSTEM: -
Classification Using Nearest Neighbor
Here we can say that our proposed system is more secure
EXPERIMENT AND RESULTS than existing system. In existing system, we have seen
that no security level available any one can give fake vote
Data used here are from the ORL database of faces. Facial with voter card. But in our approach we have seen that we
images of 16 persons each with 10 views are used. are using three level of security. If a voter fails in any
- Training set contains 16×7 images. level of security, then voter cannot cast their vote.
All Rights Reserved © 2018 IJERCSE 205
ISSN (Online) 2394-2320
International Journal of Engineering Research in Computer Science and Engineering
(IJERCSE)
Vol 5, Issue 4, April 2018
i). Every New User in the India is first register for Voting.
6. PROPOSED FRAMEWORK ARCHITECTURE: - So, our first step is registration
ii). At that time of Registration System Capture, the Face
7. SCOPE: - of the user by using Web Camera and
Store the Face sample in the Server Database for Security
Purpose.
iii). At the time of election, we will use three level of
security first one is unique id verification second one is
voter id verification third one is face recognition.
iv). System will be checking whatever unique id and voter
id entered by the voter is correct or not.
v). If unique id or voter id is correct than system will take
image of voter and compare with the respective image of
database or server.
vi). If the image in database is matching with the captured
image of the voter, then he/she is allowed to cast is vote.
vii). On the voting page all the party whatever party
contest in the election symbols /buttons will be there.
Voter can cast his /her vote in the election.
viii). As soon as voter will give vote the id of voter logout
automatically so we can say that a voter can give only one
1. Highly secured because in this project we have to use vote.
face recognition [7]. And face comparison. Tech. so false ix). On counting form only election commission
user can’t give votes.
authorized user can login with the secure id and password
2. We can access result (counting) faster than existing
if both id and password is correct then voting process will
system. Because ballet system [8] takes much more time
be continuing.
for counting process.
3. Online voting system increase voting percentage in
9. CONCLUSION: -
India. Because lots of people don’t give vote. they think
that the voting process is to lengthy but in our approach
As we see that existing voting system has many defects
any one can give vote from home easily.
such as lengthy process, time taking, not secure, bogus
voting, no security level but now we can say that our
8. WORKING FLOW OF THE SYSTEM: - approach is more useful and secure from the existing
Steps of Working Flow: - system. Since, we are using three level of security in this
Fig: Working flow of proposed system
proposed system the false voters can be easily identified.
The facial authentication technique is very much useful in
identifying the fraud voters, so we can avoid the bogus
votes during election commission. The voters can cast
their voting from anywhere by login to our proposed
smart voting system through internet. As every operation
is performed through internet connectivity so, it is one-
time investment for government. Voters’ location is not
important but their voting is important. As data is stored
in centralized repository so, data is accessible at any time
as well as backup of the data is possible. Smart voting
system provides updated result at each and every minute.
Also requires less man power and resources. The database
needs to be updated every year or before election so that
new eligible citizens may be enrolled and those who are
dead are removed from the voter list.
All Rights Reserved © 2018 IJERCSE 206
ISSN (Online) 2394-2320
International Journal of Engineering Research in Computer Science and Engineering
(IJERCSE)
Vol 5, Issue 4, April 2018
10. References: -
1. Pandit, Varad, Prathamesh Majgaonkar, Pratik Meher,
Shashank Sapaliga, and Sachin Bojewar. "Intelligent
security lock." In Trends in Electronics and Informatics
(ICEI), 2017 International Conference on, pp. 713-716.
IEEE, 2017.
2. Chauhan, C. U., Abhishek Kalnawat, Akshay Aswale,
Ujwal Gautam, and Roshan Nemad. "Survey Paper on a
Novel Approach: Web Based Technique for Vote
Casting." International Journal of Engineering and
Management Research (IJEMR) 7, no. 5 (2017): 71GER,
BARRY. "CONTENTIOUS POLITICS AND URBAN
DESIGN: TOWARD A NEW ARCHITECTURAL
THEORY." International Journal of Architecture and
Urban Studies (2017): 18
4. Sundaram, Ravi. "The Postcolonial City in India. From
Planning to Information?." Techniques & Culture. Revue
semestrielle d’anthropologie des techniques (2017).
5. Warghade, Shrikant Subhash, and B. Karthikeyan.
"Voting System for India." In Intelligent Embedded
Systems, pp. 59-65. Springer, Singapore, 2018.
6. Shah, Syed Afaq Ali, Uzair Nadeem, Mohammed
Bennamoun, Ferdous Sohel, and Roberto Togneri.
"Efficient image set classification using linear regression
based image reconstruction." arXiv preprint
arXiv:1701.02485 (2017).
7. Bhimanwar, Chinmay, Rupesh Biradar, Nikhil Bhole,
and Milind Rane. "Face Identification." International
Journal of Engineering Science 11923 (2017).
8. Bhukuth, Augendra, Jérôme Ballet, and Isabelle
Guérin. "Social capital and the brokerage system: the
formation of debt bondage in South India." Journal of
Economic Studies34, no. 4 (2007): 311-323
All Rights Reserved © 2018 IJERCSE 207
You might also like
- Curling v. Raffensperger Transcript, Volume 11Document322 pagesCurling v. Raffensperger Transcript, Volume 11The FederalistNo ratings yet
- Governmnet Lesson Notes For SS1, SS2, SS3Document52 pagesGovernmnet Lesson Notes For SS1, SS2, SS3Oladejo kabir94% (71)
- Case Digest For Sanidad Vs COMELECDocument2 pagesCase Digest For Sanidad Vs COMELECDivineDionne100% (4)
- Kabataan Party-List Et Al. vs. ComelecDocument3 pagesKabataan Party-List Et Al. vs. ComelecJemarie ArisgaNo ratings yet
- Smart Voting System Support Through Face Recognition: April 2018Document6 pagesSmart Voting System Support Through Face Recognition: April 2018Kishore SmartNo ratings yet
- Voting MachineDocument18 pagesVoting Machinevivekanand_bonalNo ratings yet
- Smart Voting System Through Face Recognition UsingDocument6 pagesSmart Voting System Through Face Recognition UsingUnknown PersonNo ratings yet
- Handwritten Signature Verification Using Instance Based LearningDocument4 pagesHandwritten Signature Verification Using Instance Based Learningsurendiran123No ratings yet
- Online Voting Using Face Recognition and Password Based Security SystemDocument9 pagesOnline Voting Using Face Recognition and Password Based Security SystemGeremu TilahunNo ratings yet
- Project Report Facial RecognitionDocument11 pagesProject Report Facial RecognitionAbhinav SharmaNo ratings yet
- Literature Review 1Document12 pagesLiterature Review 1Abhinav SharmaNo ratings yet
- Mobile Based Facial Recognition Using OTP Verification For Voting SystemDocument6 pagesMobile Based Facial Recognition Using OTP Verification For Voting SystemAkash MauryaNo ratings yet
- Review and Comparison of Face Detection Algorithms: Kirti Dang Shanu SharmaDocument5 pagesReview and Comparison of Face Detection Algorithms: Kirti Dang Shanu SharmaKevin EnriquezNo ratings yet
- (IJETA-V8I5P3) :sujith Krishna B, Priyanka BasavaDocument3 pages(IJETA-V8I5P3) :sujith Krishna B, Priyanka BasavaIJETA - EighthSenseGroupNo ratings yet
- Emotion Classification of Facial Images Using Machine Learning ModelsDocument6 pagesEmotion Classification of Facial Images Using Machine Learning ModelsIJRASETPublicationsNo ratings yet
- A Biometric Fusion Based On Face and Fingerprint Recognition Using ANNDocument5 pagesA Biometric Fusion Based On Face and Fingerprint Recognition Using ANNEditor IJRITCCNo ratings yet
- Criminal Face Recognition System: Alireza Chevelwalla, Ajay Gurav, Sachin Desai, Prof. Sumitra SadhukhanDocument4 pagesCriminal Face Recognition System: Alireza Chevelwalla, Ajay Gurav, Sachin Desai, Prof. Sumitra SadhukhanMuhammad HamzaNo ratings yet
- Seminar Project - Face - RecognitionDocument58 pagesSeminar Project - Face - RecognitionItaliya BhaktiNo ratings yet
- Design A Biometric Identification System Based On The Fusion of Hand Geometry and Backhand Patterns Raid R. Al-NimaDocument12 pagesDesign A Biometric Identification System Based On The Fusion of Hand Geometry and Backhand Patterns Raid R. Al-Nimamais taherNo ratings yet
- Real-Time Face Detection From One Camera: 1. Research TeamDocument6 pagesReal-Time Face Detection From One Camera: 1. Research TeamMuhammad UlumNo ratings yet
- Automatic Attendance System Using MatlabDocument4 pagesAutomatic Attendance System Using MatlabIJRASETPublicationsNo ratings yet
- How To Write Thesis Proposal On Face RecognitionDocument5 pagesHow To Write Thesis Proposal On Face RecognitionRahajul Amin RajuNo ratings yet
- (IJCST-V7I2P7) :mary Celin AX, KM Fathima Farzana, Lija Jude, Sherwin J Vellayil, Abeera VPDocument4 pages(IJCST-V7I2P7) :mary Celin AX, KM Fathima Farzana, Lija Jude, Sherwin J Vellayil, Abeera VPEighthSenseGroupNo ratings yet
- Information Fusion in BiometricsDocument6 pagesInformation Fusion in BiometricsMeenakshi Nehra PooniaNo ratings yet
- Smart Voting System With Face RecognitionDocument3 pagesSmart Voting System With Face RecognitionInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- An Effective Technique For Expressing and Recognizing FeelingsDocument4 pagesAn Effective Technique For Expressing and Recognizing FeelingsWeb ResearchNo ratings yet
- Face Recognition Based Attendance Management System: Smitha, Pavithra S Hegde, AfshinDocument3 pagesFace Recognition Based Attendance Management System: Smitha, Pavithra S Hegde, AfshinZubia FNo ratings yet
- Designing of Face Recognition SystemDocument3 pagesDesigning of Face Recognition SystemMuzammil NaeemNo ratings yet
- Emotion Based Music Player Using CNNDocument5 pagesEmotion Based Music Player Using CNNIJRASETPublicationsNo ratings yet
- Face Recognition Using Gabor Filters: Muhammad SHARIF, Adeel KHALID, Mudassar RAZA, Sajjad MOHSINDocument5 pagesFace Recognition Using Gabor Filters: Muhammad SHARIF, Adeel KHALID, Mudassar RAZA, Sajjad MOHSINYuri BrasilkaNo ratings yet
- A Novel Approach For Content Retrieval From Recognition AlgorithmDocument5 pagesA Novel Approach For Content Retrieval From Recognition AlgorithmInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- A Robust, Low-Cost Approach To Face Detection and Face RecognitionDocument6 pagesA Robust, Low-Cost Approach To Face Detection and Face RecognitionNirmalendu KumarNo ratings yet
- Webcam Based Facial Recognition Using OTDocument6 pagesWebcam Based Facial Recognition Using OTlawalkehinde1919No ratings yet
- Seminar Report: Facial Recognition Systems and AlgorithmsDocument31 pagesSeminar Report: Facial Recognition Systems and AlgorithmsNithin O JacobNo ratings yet
- Face Recognition: Identifying Facial Expressions Using Back PropagationDocument5 pagesFace Recognition: Identifying Facial Expressions Using Back PropagationInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Chapter No Title Page - No List of Figures List of Tables IDocument47 pagesChapter No Title Page - No List of Figures List of Tables Ishanmugaraja85No ratings yet
- B F M G R S: Rightness Actor Atching For Esture Ecognition Ystem Using Scaled NormalizationDocument12 pagesB F M G R S: Rightness Actor Atching For Esture Ecognition Ystem Using Scaled NormalizationAnonymous Gl4IRRjzNNo ratings yet
- Research Paper Final - FRASDocument4 pagesResearch Paper Final - FRASpijowac169No ratings yet
- 2013 FaceRecognition Review IJCTADocument4 pages2013 FaceRecognition Review IJCTADharmavarapu indhujaNo ratings yet
- Age Gender and Emotion Identification Using Face RecognitionDocument3 pagesAge Gender and Emotion Identification Using Face RecognitionAnil Kumar BNo ratings yet
- Facial Expression Recognition System Using Haar Cascades ClassifierDocument9 pagesFacial Expression Recognition System Using Haar Cascades ClassifierIJRASETPublicationsNo ratings yet
- DigiVoter-Smart Voting System Using Biometrics-Based Facial FeaturesDocument8 pagesDigiVoter-Smart Voting System Using Biometrics-Based Facial FeaturesIJRASETPublicationsNo ratings yet
- Face Recognition PaperDocument7 pagesFace Recognition PaperPuja RoyNo ratings yet
- Automated Attendance Using Open CVDocument6 pagesAutomated Attendance Using Open CVManikyam HemalathaNo ratings yet
- Facial RecognitionDocument23 pagesFacial RecognitionChaithanya MannepalliNo ratings yet
- FRT KDocument20 pagesFRT KKaushik JaiswalNo ratings yet
- Seminar ShivaniDocument58 pagesSeminar ShivaniItaliya BhaktiNo ratings yet
- Implementation of Face Recognition Based Attendance System Using LBPHDocument3 pagesImplementation of Face Recognition Based Attendance System Using LBPHManikyam HemalathaNo ratings yet
- Handwritten Digit Recognition Using Image Processing and Neural NetworksDocument4 pagesHandwritten Digit Recognition Using Image Processing and Neural Networksibtesam2No ratings yet
- Ijaiem 2014 02 28 088Document4 pagesIjaiem 2014 02 28 088International Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Biometric Images Attacks Detecting Using Convolutional Neural NetworksDocument15 pagesBiometric Images Attacks Detecting Using Convolutional Neural NetworkscmgarciasilvaNo ratings yet
- 10 23919@mipro 2019 8756700Document6 pages10 23919@mipro 2019 8756700Prince KumarNo ratings yet
- IJIPVCV1I102Document4 pagesIJIPVCV1I102Journal Home e-PublicationNo ratings yet
- A Matlab Based Electronic Voting MachineDocument7 pagesA Matlab Based Electronic Voting MachineIJRASETPublicationsNo ratings yet
- A Real-Time Face Recognition System Using Eigenfaces: Daniel GeorgescuDocument12 pagesA Real-Time Face Recognition System Using Eigenfaces: Daniel GeorgescuAlex SisuNo ratings yet
- Face Detection and Recognition - A ReviewDocument8 pagesFace Detection and Recognition - A ReviewHenry MagdayNo ratings yet
- Face RecDocument25 pagesFace RecSahilaKhanNo ratings yet
- Andwritten Ignature Erification: ECE 533 - Project byDocument18 pagesAndwritten Ignature Erification: ECE 533 - Project byYukti KhuranaNo ratings yet
- Face Recognition Based Attendance System Using Haar Cascade and Local Binary Pattern Histogram AlgorithmDocument4 pagesFace Recognition Based Attendance System Using Haar Cascade and Local Binary Pattern Histogram AlgorithmShri RaamNo ratings yet
- 2013 FaceRecognition Review IJCTADocument4 pages2013 FaceRecognition Review IJCTAMohit SNo ratings yet
- Face Recognition Technology Seminar ReportDocument26 pagesFace Recognition Technology Seminar ReportParampreet Singh71% (7)
- Geometric Feature Learning: Unlocking Visual Insights through Geometric Feature LearningFrom EverandGeometric Feature Learning: Unlocking Visual Insights through Geometric Feature LearningNo ratings yet
- VTU Question Paper of 20MCA23 Web Technologies Feb-2022Document1 pageVTU Question Paper of 20MCA23 Web Technologies Feb-2022SonyNo ratings yet
- Time, Speed & DistanceDocument3 pagesTime, Speed & DistanceSonyNo ratings yet
- PHP IntroDocument18 pagesPHP IntroSonyNo ratings yet
- VTU Exam Question Paper With Solution of 18MCA51 Programming Using C#.NET Jan-2021-Ms Uma BDocument37 pagesVTU Exam Question Paper With Solution of 18MCA51 Programming Using C#.NET Jan-2021-Ms Uma BSonyNo ratings yet
- PartnershipDocument2 pagesPartnershipSonyNo ratings yet
- 18MCA51 - Nirupama B KDocument109 pages18MCA51 - Nirupama B KSonyNo ratings yet
- Ajax TutorialDocument2 pagesAjax TutorialSonyNo ratings yet
- PHP Patter MatchingDocument5 pagesPHP Patter MatchingSonyNo ratings yet
- InstantRails WorkingDocument10 pagesInstantRails WorkingSonyNo ratings yet
- Ajax ExamplesDocument1 pageAjax ExamplesSonyNo ratings yet
- VTU Question Paper of 18MCA51 Programming Using C# .Net Jan-2021Document2 pagesVTU Question Paper of 18MCA51 Programming Using C# .Net Jan-2021SonyNo ratings yet
- Ajaxapplicaion CreatingDocument62 pagesAjaxapplicaion CreatingSonyNo ratings yet
- VTU Question Paper of 16-17MCA52 Programming Using C# and .Net Jan-2021Document1 pageVTU Question Paper of 16-17MCA52 Programming Using C# and .Net Jan-2021SonyNo ratings yet
- Reviewer in CONSTI REV Part1Document4 pagesReviewer in CONSTI REV Part1bam zeppeleinNo ratings yet
- Perez vs. COMELECDocument7 pagesPerez vs. COMELECRaniel MirandaNo ratings yet
- Conversation Flashcards2Document14 pagesConversation Flashcards2Marie Thelma Benolirao RomarateNo ratings yet
- DH 0519Document10 pagesDH 0519The Delphos HeraldNo ratings yet
- Sec. 32 Subic Bay Metropolitan Authority v. COMELEC - DigestDocument2 pagesSec. 32 Subic Bay Metropolitan Authority v. COMELEC - DigestLorenzo Elegio IIINo ratings yet
- Aytona V Castillo GR L-19313Document27 pagesAytona V Castillo GR L-19313LalaLanibaNo ratings yet
- Fingerprint Voting SystemDocument6 pagesFingerprint Voting SystemKathleen CornejoNo ratings yet
- QUINN 4th Edition Computer ReliabilityDocument53 pagesQUINN 4th Edition Computer ReliabilityViveekdeep SinghNo ratings yet
- Shifter, 2011Document16 pagesShifter, 2011anotheruntoldstoryNo ratings yet
- 09-29-15 EditionDocument28 pages09-29-15 EditionSan Mateo Daily JournalNo ratings yet
- Catarman, CamiguinDocument2 pagesCatarman, CamiguinSunStar Philippine NewsNo ratings yet
- ABS-CBN Broadcasting Group vs. COMELEC, G.R. No. 133486Document9 pagesABS-CBN Broadcasting Group vs. COMELEC, G.R. No. 133486Inez Monika Carreon PadaoNo ratings yet
- Business Statistic Linear Programming ExerciseDocument3 pagesBusiness Statistic Linear Programming ExerciseSimon Gee0% (2)
- Libanan V HRETDocument2 pagesLibanan V HRETAnsai CaluganNo ratings yet
- 031 - Miranda v. AguirreDocument3 pages031 - Miranda v. Aguirrergtan3No ratings yet
- 12 Types of VotersDocument13 pages12 Types of VotersAshok KumarNo ratings yet
- 2012 217Document88 pages2012 217Jaja Ordinario Quiachon-AbarcaNo ratings yet
- Germania, Proiect Iulia CraciunDocument5 pagesGermania, Proiect Iulia CraciunElenaNo ratings yet
- 2019 Indian General ElectionDocument24 pages2019 Indian General Electionharshika guptaNo ratings yet
- Bondoc Vs PinedaDocument3 pagesBondoc Vs PinedaMa Gabriellen Quijada-TabuñagNo ratings yet
- Assignment Malaysian StudiesDocument16 pagesAssignment Malaysian StudiesStephanny Sylvester100% (1)
- Election of Directors or Trustees.: Election and Voting Sec. 24Document25 pagesElection of Directors or Trustees.: Election and Voting Sec. 24markuslagan06No ratings yet
- Political Law.2Document120 pagesPolitical Law.2Rengie GaloNo ratings yet
- Labo vs. ComelecDocument3 pagesLabo vs. ComelecNico Delos TrinosNo ratings yet
- Travis Prete - Mini Unit WDDocument20 pagesTravis Prete - Mini Unit WDapi-298016754No ratings yet