Professional Documents
Culture Documents
SE Reprt 2023
SE Reprt 2023
Uploaded by
Spoorthi JCopyright:
Available Formats
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5825)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1093)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (852)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (590)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (903)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (541)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (349)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (823)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (122)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (403)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- II PUC EconomicsDocument137 pagesII PUC EconomicsSpoorthi J89% (9)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Notes Module1Document14 pagesNotes Module1Spoorthi JNo ratings yet
- Feia 1Document6 pagesFeia 1Spoorthi JNo ratings yet
- CADocument17 pagesCASpoorthi JNo ratings yet
- ADA Lab Programs Consolidated 15-4-16Document41 pagesADA Lab Programs Consolidated 15-4-16Spoorthi JNo ratings yet
- CA Blue Book 02Document8 pagesCA Blue Book 02Spoorthi JNo ratings yet
- SM in Python Lab Programs 2020Document20 pagesSM in Python Lab Programs 2020Spoorthi JNo ratings yet
SE Reprt 2023
SE Reprt 2023
Uploaded by
Spoorthi JCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
SE Reprt 2023
SE Reprt 2023
Uploaded by
Spoorthi JCopyright:
Available Formats
About The GTTC-Siemens Center for Excellence
GTTC was established in 1972 at Bangalore with the participation of the Karnataka State
Government, in collaboration with the Government of Denmark under the Bilateral
Development Co-operation Agreement. The excellent performance of GTTC Bangalore,
proactive Government of Karnataka which saw the need for expansion, got second unit of
GTTC started in 1992 with DANIDA assistance.
Proliferation of technology for development of the industries with supply of skilled
manpower is the key to meet the needs of the global requirement. With this Government of
Karnataka encouraged GTTC to start 10 more sub-centres to train in the area of tool and
die making in various parts of Karnataka.
GTTC is an autonomous society, and a recognised Scientific and Research Organisation
by the Government of India. Govt. Tool Room and Training Centre (GTTC), is serving
industry by way of precision tooling and providing in well trained craftsmen the area of
tool and die making.
Today, the GTTC has acquired mastery in Mould and Die making technology and have
blossomed into an epitome of precision and quality in the development and manufacture of
sophisticated moulds, dies and tools.
Fully aware of the rapid advancement in technology the world over, the GTTC is
periodically adding new technologies to the existing set of advanced equipment like CAD /
CAM, CNC machines for tooling, Precision Components, Laser for Industries, Rapid
prototyping, vacuum casting etc.
GTTC is concentrating on the Integrated Development of the related segments of
industries by way of providing international quality tools, trained personnel and
consultancy in tooling and related areas. In future, the focus would be more on turnkey
projects in Tooling, Aerospace components & their assemblies, and also to support the
development of small and medium scale enterprises.
Achievements:
Rover wheels for chandrayana projects
Hydraulic system line replacement units like Shuttle Valves, Non-Return values
sampling valves for LCA Aircraft (Tejas).
Import substitution of precision components for packaging industries.
Prototype Laparoscopic Surgical tools.
Dept of MCA, VVIET 1
Design & Development of precision tooling for medical application.
Reverse engineering components and developments of parts for import
substitutions.
Fuel system line replacement units like inward/outward relief valves, two piston
flap valves for LCA Aircraft (Tejas).
Environmental control system like Primary heat exchanger, secondary heat
exchanger, Re-heater heat exchanger, Gimbal assembly with venture and Gimbal
Joints for LCA Aircraft (Tejas).
Aircraft mounted accessories gear box (AMAGB) for LCA Aircraft (Tejas).
Fire Extinguisher bottle for LCA Aircraft (Tejas).
Flow switch assembly for LCA Aircraft (Tejas).
Camera mounting fixture for HAL.
Parking Brake fixture for M/s. Toyota Kirloskar.
Fins for NAL.
GTTC-Siemens Center for Excellence
GTTC-Siemens Center for Excellence is a state of art Robotics and Product design
engineering lab and development center in Mysuru.
Dept of MCA, VVIET 2
The students of 2nd sem MCA of Vidya Vikas Institute of Engineering and Technology have
visited the development center on 20 september 2023.As an academic visit students
learned the process of product development,SDLC`s,design patterns ,product life cycle
model used and test standards at the center.
Dept of MCA, VVIET 3
Abstract
The primary goal is to expose students to the practice of software development, that is,
programming at a reasonably large scale. While the principal way of learning to develop
software is to develop software, this course teaches how the program design principles of
the prerequisite courses scale to a large code base. Indeed, without relying on such
fundamental design principles, a large code base may quickly become prohibitively
complex and incomprehensible.
Students present their solutions to their peers (in class), and student panels act as
reviewers. Both presenting code and understanding such presentations are critical skills
for the modern software developer.
Dept of MCA, VVIET 4
Introduction to Software Engineering
Software Engineering is the process of designing, developing, testing, and maintaining
software. It is a systematic and disciplined approach to software development that aims to
create high-quality, reliable, and maintainable software. Software engineering includes a
variety of techniques, tools, and methodologies, including requirements analysis, design,
testing, and maintenance.
Introduction to Software Development Life Cycle (SDLC)
The Software Development Life Cycle (SDLC) is a structured process that enables the
production of high-quality, low-cost software, in the shortest possible production time. The
goal of the SDLC is to produce superior software that meets and exceeds all customer
expectations and demands. The SDLC defines and outlines a detailed plan with stages, or
phases, that each encompass their own process and deliverables. Adherence to the SDLC
enhances development speed and minimizes project risks and costs associated with
alternative methods of production.
In the 1950s and 1960s, computer science progressed rapidly. This swift evolution sparked
the beginnings of a production framework that eventually grew into the SDLC we know
today.
Prior to the 1950s, computing was not elaborate enough to necessitate a detailed approach
like the SDLC. As the complexity and scale of programming grew, the concept of structured
programming emerged. Over time, structured programming demanded more tactical
development models, thus sparking the beginnings of the SDLC.
Why is the SDLC important?
It provides a standardized framework that defines activities and deliverables
It aids in project planning, estimating, and scheduling
It makes project tracking and control easier
It increases visibility on all aspects of the life cycle to all stakeholders involved in the
development process
It increases the speed of development
It improves client relations
It decreases project risks
It decreases project management expenses and the overall cost of production
Dept of MCA, VVIET 5
The role of security in the SDLC
The initial concept and creation of the SDLC only addressed security activities as a separate
and singular task, performed as part of the testing phase. The shortcomings of this after-
the-fact approach were the inevitably high number of vulnerabilities or bugs discovered
too late in the process, or in certain cases, not discovered at all. Today, it is understood that
security is critical to a successful SDLC, and that integrating security activities throughout
the SDLC helps create more reliable software. By incorporating security practices and
measures into the earlier phases of the SDLC, vulnerabilities are discovered and mitigated
earlier, thereby minimizing overall time involved, and reducing costly fixes later in the life
cycle.
This idea of ‘baking-in’ security provides a ‘Secure SDLC’- a concept widely recognized and
adopted in the software industry today. A secure SDLC is achieved by conducting security
assessments and practices during ALL phases of software development.
With modern application security testing tools, it is easy to integrate security throughout
the SDLC. In keeping with the ‘secure SDLC’ concept, it is vital that security assurance
activities such as penetration testing, threat modeling, code review, and architecture
analysis are an integral part of development efforts.
The primary advantages of pursuing a secure SDLC approach include
More secure software as security is a continuous concern
Awareness of security considerations by stakeholders
Early detection of flaws in the system
Cost reduction as a result of early detection and resolution of issues
Overall reduction of intrinsic business risks for the organization
SDLC working
Planning phase
The planning phase encompasses all aspects of project and product management. This
typically includes resource allocation, capacity planning, project scheduling, cost
estimation, and provisioning.
During the planning phase, the development team collects input from stakeholders
involved in the project; customers, sales, internal and external experts, and developers.
This input is synthesized into a detailed definition of the requirements for creating the
Dept of MCA, VVIET 6
desired software. The team also determines what resources are required to satisfy the
project requirements, and then infers the associated cost.
Expectations are clearly defined during this stage as well; the team determines not only
what is desired in the software, but also what is NOT. The tangible deliverables produced
from this phase include project plans, estimated costs, projected schedules, and
procurement needs.
Coding phase
The coding phase includes system design in an integrated development environment. It
also includes static code analysis and code review for multiple types of devices.
Building Phase
The building phase takes the code requirements determined earlier and uses those to begin
actually building the software.
Testing Phase
The phase entails the evaluation of the created software. The testing team evaluates the
developed product(s) in order to assess whether they meet the requirements specified in
the ‘planning’ phase.
Assessments entail the performance of functional testing: unit testing, code quality testing,
integration testing, system testing, security testing, performance testing and acceptance
testing, as well as nonfunctional testing. If a defect is identified, developers are notified.
Validated (actual) defects are resolved, and a new version of the software is produced.
The best method for ensuring that all tests are run regularly and reliably, is to implement
automated testing. Continuous integration tools assist with this need.
Release Phase
The release phase involves the team packaging, managing and deploying releases across
different environments.
Deploy Phase
In the deployment phase, the software is officially released into the production
environment.
Operate Phase
The operate phase entails the use of the software in the production environment.
Dept of MCA, VVIET 7
Monitor Phase
In the monitor phase, various elements of the software are monitored. These could include
the overall system performance, user experience, new security vulnerabilities, an analysis
of bugs or errors in the system.
SDLC models/methodologies
Waterfall
Waterfall represents the oldest, simplest, and most structured methodology. Each phase
depends on the outcome of the previous phase, and all phases run sequentially. This model
provides discipline and gives a tangible output at the end of each phase. However, this
model doesn’t work well when flexibility is a requirement. There is little room for change
once a phase is deemed complete, as changes can affect the cost, delivery time, and quality
of the software.
Agile
The agile methodology produces ongoing release cycles, each featuring small, incremental
changes from the previous release. At each iteration, the product is tested. The agile model
helps teams identify and address small issues in projects before they evolve into more
significant problems. Teams can also engage business stakeholders and get their feedback
throughout the development process.
Lean
The lean methodology for software development is inspired by lean manufacturing
practices and principles. The lean principles encourage creating better flow in work
processes and developing a continuous improvement culture. The seven lean principles
are:
Eliminate waste
Amplify learning
Make decisions as late as possible
Deliver as fast as possible
Empower your team
Build integrity in
Build holistically
Dept of MCA, VVIET 8
Iterative
In the iterative process, each development cycle produces an incomplete but deployable
version of the software. The first iteration implements a small set of the software
requirements, and each subsequent version adds more requirements. The last iteration
contains the complete requirement set.
Spiral
In the spiral development model, the development process is driven by the unique risk
patterns of a project. The development team evaluates the project and determines which
elements of the other process models to incorporate.
V-Shaped
In the V-shaped model, verification phases and validation phases are run in parallel. Each
verification phase is associated with a validation phase, and the model is run in a V-shape,
where each phase of development has an associated phase of testing.
SDLC best practices
The most important best practice to implement into your SDLC is effective communication
across the entire team. The more alignment, the greater the chances for success.
Signs of a well-implemented SDLC include:
The successful deployment of a comprehensive application security program
Code quality standards
Effective collaboration across teams
Streamlined workflows
Cross-involvement of teams throughout the life cycle
SDLC common mistakes and challenges
There are several pitfalls that threaten to negatively impact an SDLC implementation.
Perhaps the most problematic mistake is a failure to adequately account for and
accommodate customer and stakeholder needs in the process. This results in a
misunderstanding of system requirements, and inevitable disappointment with the end-
product.
Dept of MCA, VVIET 9
Additionally, the complexity of the SDLC often causes a project to derail or teams to lose
sight of specifics and requirements. Without strict adherence to all aspects of the
parameters and design plans, a project can easily miss the mark.
Agile Software Development Life Cycle
Agile SDLC methodology is based on collaborative decision making between requirements
and solutions teams, and a cyclical, iterative progression of producing working software.
Work is done in regularly iterated cycles, known as sprints, that usually last two to four
weeks. In Agile, you often don’t design for needs that could come up in the future, even if
they seem obvious. This is a point where development teams and security teams tend to
struggle. Security teams aim to anticipate and risks. As needs emerge and are refined over
time, security requirements can emerge that weren’t anticipated at the beginning of the
process. This is normal and natural in Agile, but it can be disorienting to security people
who aren’t able to secure against various likely attacks. A key takeaway from a security
perspective is that Agile is all about the sprint. If a security requirement isn’t in the backlog,
it won’t be scheduled for delivery in a sprint. If it isn’t scheduled in a sprint, it won’t get
done. When security needs are articulated in the backlog, they’re prioritized alongside
everything else.
How does Agile drive secure development?
Fifteen years after the Agile Manifesto was released, similar inefficiencies still plague
application security efforts in software development. Security is often seen as something
separate from—and external to—software development. It’s time to change the approach
to building secure software using the Agile methodology.
When building secure software in an Agile environment, it’s essential to focus on four
principles. These principles are patterned after those in the original Agile Manifesto: while
we value the things on the right, we must value the things on the left more.
The goal is to guide the development of new activities and make adjustments to existing
activities to make it natural and efficient to build security into an agile process. These four
principles are meant to inspire us to build secure software in an agile way:
Rely on developers and testers more than security specialists.
Secure while we work more than after we’re done.
Implement features securely more than adding on security features.
Mitigate risks more than fix bugs.
Dept of MCA, VVIET 10
Building secure software in an agile way is fundamentally the same as building software in
an agile way. The Agile SDLC train
Agile SDLC works a lot like a train. Each rotation of the train wheels represents a sprint.
During each sprint rotation, new needs are coming in from the backlog, rolling through the
planning, implementation, testing, evaluation, and deployment phases of the Agile software
development life cycle (SDLC).
Each Agile phase within each sprint rotation meets the software security tracks through a
series of security activities tailored to each phase. There’s no need to stop the train to think
about security. If a vulnerability is identified, treat it like any other bug and resolve it along
the way.
Dept of MCA, VVIET 11
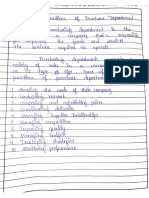
Real Time scenario of how a product is developed in software industry with robotics and AI
technology using Agile SDLC.
Dept of MCA, VVIET 12
Conclusion
Students learned the real-time implementation of SDLCs in software development in
various robotics and AI based products that are developed in GTTC-Siemens Center for
Excellence, Mysuru.
Dept of MCA, VVIET 13
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5825)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1093)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (852)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (590)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (903)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (541)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (349)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (823)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (122)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (403)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- II PUC EconomicsDocument137 pagesII PUC EconomicsSpoorthi J89% (9)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Notes Module1Document14 pagesNotes Module1Spoorthi JNo ratings yet
- Feia 1Document6 pagesFeia 1Spoorthi JNo ratings yet
- CADocument17 pagesCASpoorthi JNo ratings yet
- ADA Lab Programs Consolidated 15-4-16Document41 pagesADA Lab Programs Consolidated 15-4-16Spoorthi JNo ratings yet
- CA Blue Book 02Document8 pagesCA Blue Book 02Spoorthi JNo ratings yet
- SM in Python Lab Programs 2020Document20 pagesSM in Python Lab Programs 2020Spoorthi JNo ratings yet