Professional Documents
Culture Documents
Trend Micro Deep Discovery Inspector
Trend Micro Deep Discovery Inspector
Uploaded by
haivadiCopyright:
Available Formats
You might also like
- Case Study CyberDocument6 pagesCase Study CyberMuhammad Sardaar100% (2)
- Sean Jones and Bryce Webster Jackson - Beyond Encryption - Exploring The Tactics Ransomware Operators Use During Negotiation and Their ImpactDocument10 pagesSean Jones and Bryce Webster Jackson - Beyond Encryption - Exploring The Tactics Ransomware Operators Use During Negotiation and Their ImpactFranklin CordeiroNo ratings yet
- Artificial Intelligence Ai Elementary To Advanced Practices Cyber Defense Mechanisms Security PrivacyDocument231 pagesArtificial Intelligence Ai Elementary To Advanced Practices Cyber Defense Mechanisms Security Privacyalexander kessyNo ratings yet
- Deception Solution Overview: Deceive. Detect. DefendDocument4 pagesDeception Solution Overview: Deceive. Detect. DefendJimmy Alfaro HernandezNo ratings yet
- 4.electronic Evidence - Collection, Preservation and Appreciation PDFDocument108 pages4.electronic Evidence - Collection, Preservation and Appreciation PDFRohanPuthalathNo ratings yet
- Deep Discovery Inspector DatasheetDocument2 pagesDeep Discovery Inspector DatasheetHumberto BautistaNo ratings yet
- Deep Discovery Inspector DatasheetDocument2 pagesDeep Discovery Inspector DatasheetHumberto BautistaNo ratings yet
- Ds DD InspectorDocument2 pagesDs DD Inspectorzain_zedanNo ratings yet
- Trend Micro Deep Discovery AnalyzerDocument2 pagesTrend Micro Deep Discovery AnalyzerhaivadiNo ratings yet
- Ds-Apex-One 2021Document2 pagesDs-Apex-One 2021HenryNo ratings yet
- Zscaler DeceptionDocument7 pagesZscaler DeceptionLENIN HITLER RAMIREZ SANTA CRUZNo ratings yet
- Cyber SecurityDocument14 pagesCyber SecurityManish ChoudhuryNo ratings yet
- Data Security PracticesDocument5 pagesData Security Practicessukeerthi bmeNo ratings yet
- Trend Micro Apex One: Endpoint Security RedefinedDocument2 pagesTrend Micro Apex One: Endpoint Security Redefinedpier Aguilar RamirezNo ratings yet
- Seguridad P1Document54 pagesSeguridad P1Andres CandoNo ratings yet
- Compromise Assessment - Datasheet - ControlledDocument2 pagesCompromise Assessment - Datasheet - Controlleddigitlabs.marketingNo ratings yet
- SG MDR Service PresentationDocument17 pagesSG MDR Service PresentationDasha DeckwerthNo ratings yet
- Network Monitor Data SheetDocument2 pagesNetwork Monitor Data SheetTaha KhanNo ratings yet
- 10-21 NDR BuyersGuide V6.disarmedDocument7 pages10-21 NDR BuyersGuide V6.disarmedramramNo ratings yet
- Firewall EmbaDocument32 pagesFirewall EmbaMd.Ahnaf AkifNo ratings yet
- Group Ib Ti enDocument5 pagesGroup Ib Ti entahamesbahi123No ratings yet
- CNPT 3220 Network SecurityDocument21 pagesCNPT 3220 Network SecurityJingyu LiNo ratings yet
- Cisco Stealthwatch® Threat Intelligence (TI) LicenseDocument3 pagesCisco Stealthwatch® Threat Intelligence (TI) LicenseNikola PetrovNo ratings yet
- Securing Your Organization From Modern Ransomware: Ransomware Attacks Are Now A Team EffortDocument11 pagesSecuring Your Organization From Modern Ransomware: Ransomware Attacks Are Now A Team EfforttiagouebemoraisNo ratings yet
- Mageni - Groundbreaking Vulnerability Scanning and Vulnerability Management SolutionDocument2 pagesMageni - Groundbreaking Vulnerability Scanning and Vulnerability Management SolutionLucas MartinezNo ratings yet
- 03.bobak Group IB Portfolio UpdateDocument32 pages03.bobak Group IB Portfolio Updateericstevens77777No ratings yet
- MDR Flyer - Threat ManagementDocument2 pagesMDR Flyer - Threat ManagementDasha DeckwerthNo ratings yet
- Extending Security Intelligence With Big Data SolutionsDocument8 pagesExtending Security Intelligence With Big Data SolutionsYashNo ratings yet
- SB - Trend Micro XDRDocument3 pagesSB - Trend Micro XDRSixaxiSNo ratings yet
- Homework 1Document3 pagesHomework 1tojy.m12No ratings yet
- Intrusion Detection and Prevention Systems: Name: Md. Matiur Rahman Student ID: 000646848Document7 pagesIntrusion Detection and Prevention Systems: Name: Md. Matiur Rahman Student ID: 000646848Sonia Sultana100% (1)
- Honeypots & Honeynets: Tech TalkDocument16 pagesHoneypots & Honeynets: Tech Talkthaidt229No ratings yet
- CEH Exam Blueprint 3.0: EC-CouncilDocument5 pagesCEH Exam Blueprint 3.0: EC-CouncilYONIWO EDWARD TSEMINo ratings yet
- Ethical Hacking UpdtedDocument15 pagesEthical Hacking UpdtedvamshimatangiNo ratings yet
- Cybersecurity: It Specialist Exam ObjectivesDocument3 pagesCybersecurity: It Specialist Exam ObjectivesMercy EbiojoNo ratings yet
- Cortex XDR For Network Traffic Analysis PDFDocument2 pagesCortex XDR For Network Traffic Analysis PDFfabioccnpNo ratings yet
- Interscan Web Security Virtual Appliance: Trend MicroDocument4 pagesInterscan Web Security Virtual Appliance: Trend MicroriyasathsafranNo ratings yet
- 05 Network ForensicsDocument33 pages05 Network ForensicsMohammed LajamNo ratings yet
- By Palo Alto Networks - PA-7000 Series - DatasheetDocument4 pagesBy Palo Alto Networks - PA-7000 Series - DatasheetAbel De Los SantosNo ratings yet
- Trend Micro Apex One: Endpoint Security RedefinedDocument2 pagesTrend Micro Apex One: Endpoint Security RedefinedtestNo ratings yet
- Raj Agrawal - Expt-1 - VAPTDocument13 pagesRaj Agrawal - Expt-1 - VAPTraj.maNo ratings yet
- Ds Mobile SecurityDocument2 pagesDs Mobile Securitynugroho adiNo ratings yet
- Threat Intelligence ModuleDocument2 pagesThreat Intelligence Moduleandini eldanantyNo ratings yet
- Ds XDR For NetworksDocument3 pagesDs XDR For Networkslarry linaresNo ratings yet
- Quickly Respond To Attacks Across Your NetworkDocument4 pagesQuickly Respond To Attacks Across Your Networkhieule.mktNo ratings yet
- Summit Newsweek România Dedicat Securității CiberneticeDocument20 pagesSummit Newsweek România Dedicat Securității CiberneticeNewsweek RomaniaNo ratings yet
- XDR For Users: Trend MicroDocument3 pagesXDR For Users: Trend MicroriyasathsafranNo ratings yet
- Cybersecurity - Industry PerspectiveDocument81 pagesCybersecurity - Industry PerspectivejayantascribeNo ratings yet
- Sourcefire BRKSEC-1030Document112 pagesSourcefire BRKSEC-1030Raja AthiNo ratings yet
- Security Analytics: Big Data Analytics For Cybersecurity: A Review of Trends, Techniques and ToolsDocument6 pagesSecurity Analytics: Big Data Analytics For Cybersecurity: A Review of Trends, Techniques and ToolsHimanshu GoelNo ratings yet
- CISCO Cybersecurity Final Exam Solution by PariDocument6 pagesCISCO Cybersecurity Final Exam Solution by Paribc160200544 Mah JabeenNo ratings yet
- 3part Series Dress For Success Cybersecurity Training - Phase 1Document21 pages3part Series Dress For Success Cybersecurity Training - Phase 1Mokka EbuNo ratings yet
- The CERT Guide To System and Network Security Practices: January 2001Document19 pagesThe CERT Guide To System and Network Security Practices: January 2001JRonald85No ratings yet
- Types of Cyber Attacks E Book PDFDocument10 pagesTypes of Cyber Attacks E Book PDFDwaipayan MojumderNo ratings yet
- Cyber Threat IntelligenceDocument41 pagesCyber Threat Intelligencekt06121999No ratings yet
- Network & Network SecurityDocument14 pagesNetwork & Network SecurityDAVID MGAYANo ratings yet
- Lightcyber Behavioral AnalyticsDocument4 pagesLightcyber Behavioral AnalyticsasadaNo ratings yet
- Sed Eps PB105Document5 pagesSed Eps PB105Stefano Bbc RossiNo ratings yet
- Information Security Issues, Threats, Solution & StandradsDocument46 pagesInformation Security Issues, Threats, Solution & StandradsmasteranshulNo ratings yet
- Latest AntivirusesDocument12 pagesLatest Antivirusesplease readNo ratings yet
- National Awareness Nepal 2015Document118 pagesNational Awareness Nepal 2015A M Chandra DhamiNo ratings yet
- At A Glance - EDRDocument6 pagesAt A Glance - EDRahmed gaafarNo ratings yet
- Juan Manuel Corchado - 3 - Presentación DeepSIEMDocument13 pagesJuan Manuel Corchado - 3 - Presentación DeepSIEMfelgamNo ratings yet
- CYBER SECURITY HANDBOOK Part-2: Lock, Stock, and Cyber: A Comprehensive Security HandbookFrom EverandCYBER SECURITY HANDBOOK Part-2: Lock, Stock, and Cyber: A Comprehensive Security HandbookNo ratings yet
- 4-Port Analog Dial BoardDocument1 page4-Port Analog Dial BoardhaivadiNo ratings yet
- 8-Port Analog Dial BoardDocument1 page8-Port Analog Dial BoardhaivadiNo ratings yet
- 4-Port Digital Dial BoardDocument1 page4-Port Digital Dial BoardhaivadiNo ratings yet
- Ds Apex OneDocument2 pagesDs Apex OnehaivadiNo ratings yet
- Trend Micro Deep Discovery AnalyzerDocument2 pagesTrend Micro Deep Discovery AnalyzerhaivadiNo ratings yet
- XDR For DummiesDocument51 pagesXDR For Dummiesmbuyujean35No ratings yet
- CrowdStrike2023GlobalThreatReport UpdatedDocument42 pagesCrowdStrike2023GlobalThreatReport UpdatedSarayuth Sae-tungNo ratings yet
- NSE1 Key Cybersecurity Terms-ENDocument6 pagesNSE1 Key Cybersecurity Terms-ENitachi uchihaNo ratings yet
- Cyber and Information Security (Assignment2)Document57 pagesCyber and Information Security (Assignment2)Himanshu Sharma0% (1)
- Seminar ReportDocument19 pagesSeminar ReportSahil Sethi100% (1)
- Cyber Security at SeaDocument30 pagesCyber Security at SeaJoseph GraciousNo ratings yet
- 15: Security and Cyber LawsDocument49 pages15: Security and Cyber LawsPixelNo ratings yet
- IAS Pre FiDocument4 pagesIAS Pre FiGela SiaNo ratings yet
- Fortinet - Pre .NSE5 EDR-5.0.30q-DEMODocument14 pagesFortinet - Pre .NSE5 EDR-5.0.30q-DEMOkely.alcantara.96No ratings yet
- Grazelyn Rabe BSIT-CDocument9 pagesGrazelyn Rabe BSIT-CGrazelyn RabeNo ratings yet
- What Is An Exploit Kit (With Examples) How Do Cybercriminals Use ThemDocument11 pagesWhat Is An Exploit Kit (With Examples) How Do Cybercriminals Use ThemsetyabudhiNo ratings yet
- Exclusive GA Refresher For SBI PO Main May 2017Document43 pagesExclusive GA Refresher For SBI PO Main May 2017Jyoti SukhijaNo ratings yet
- Major-1 MCQSDocument14 pagesMajor-1 MCQSaniltimes13No ratings yet
- CyberArk EPM Overview 1Document31 pagesCyberArk EPM Overview 1Quan TranNo ratings yet
- Cyber SecurityDocument16 pagesCyber SecuritykarthikNo ratings yet
- Investor Presentation Company UpdateDocument44 pagesInvestor Presentation Company UpdatePrasad KshirsagarNo ratings yet
- Module 4: Internet ThreatsDocument10 pagesModule 4: Internet ThreatsKzy ayanNo ratings yet
- Top 10 Cyber Security Solution Providers 2020Document40 pagesTop 10 Cyber Security Solution Providers 2020The CEO ViewsNo ratings yet
- Ransomware Detection PreviewDocument46 pagesRansomware Detection Previewakhmad ismail100% (2)
- Deep Instinct Making Sense of Fileless Malware PDFDocument21 pagesDeep Instinct Making Sense of Fileless Malware PDFOsiris PHNo ratings yet
- BIT324 Networkand Information Security ExamDocument4 pagesBIT324 Networkand Information Security ExamqwztjiorxsNo ratings yet
- Ransomware CTEP Situation Manual 092023 508Document22 pagesRansomware CTEP Situation Manual 092023 508Cyril EsedoNo ratings yet
- Cybersecurity Report For SMBsDocument20 pagesCybersecurity Report For SMBsAndi Tri Jati100% (1)
- Resolving Security and Data Concerns in Cloud Computing by Utilizing A Decentralized Cloud Computing OptionDocument6 pagesResolving Security and Data Concerns in Cloud Computing by Utilizing A Decentralized Cloud Computing OptionGopala Krishna SriramNo ratings yet
- Question Bank 1Document6 pagesQuestion Bank 1siri chandanaNo ratings yet
- Cyber Security Policy For MSCB LTDDocument32 pagesCyber Security Policy For MSCB LTDthongphetlamphayphanNo ratings yet
Trend Micro Deep Discovery Inspector
Trend Micro Deep Discovery Inspector
Uploaded by
haivadiCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Trend Micro Deep Discovery Inspector
Trend Micro Deep Discovery Inspector
Uploaded by
haivadiCopyright:
Available Formats
Datasheet
Trend Micro™
Deep Discovery™ Inspector
Network-wide detection of targeted attacks, advanced threats, and ransomware
Targeted attacks and advanced threats are customized to evade your conventional Key Benefits
security defenses, and remain hidden while stealing your corporate data, intellectual
Better Detection
property, and communications, or encrypting critical data until ransom demands are
met. To detect targeted attacks and advanced threats, analysts and security experts • Multiple detection techniques
agree that organizations should utilize advanced detection technology as part of an • Monitors all network traffic
expanded strategy.
• Custom sandbox analysis
Trend Micro™ Deep Discovery™ Inspector is a physical or virtual network appliance
• Standards–based threat intelligence
that monitors 360 degrees of your network to create complete visibility into all aspects
sharing
of targeted attacks, advanced threats, and ransomware. By using specialized detection
engines and custom sandbox analysis, Deep Discovery Inspector identifies advanced • Increased detection with machine
and unknown malware, ransomware, zero-day exploits, command and control (C&C) learning
communications, and evasive attacker activities that are invisible to standard security
defenses. Detection is enhanced by monitoring all physical, virtual, north-south, and
east-west traffic.
Key Capabilities
Inspects all network content. Deep Discovery Inspector monitors all
traffic across physical and virtual network segments, all network ports, and
over 100 network protocols to identify targeted attacks, advanced threats, Tangible ROI
and ransomware. Our agnostic approach to network traffic enables Deep • Enhance existing investments
Discovery Inspector to detect targeted attacks, advanced threats, and
ransomware from inbound and outbound network traffic as well as lateral • Flexible deployment options
movement, C&C, and other attacker behavior across all phases of the • Automation of manual tasks
attack lifecycle. • Graphical analysis of attacks
Extensive detection techniques utilize file, web, IP, mobile application
reputation, heuristic analysis, advanced threat scanning, custom sandbox
analysis, and correlated threat intelligence to detect ransomware, zero-day
exploits, advanced malware, and attacker behavior.
Custom sandbox analysis uses virtual images that are tuned to precisely
match an organization’s system configurations, drivers, installed
applications, and language versions. This approach improves the detection WAVE
rate of advanced threats and ransomware that are designed to evade LEADER 2023
Network Analysis And
standard virtual images. Visibility
Managed detection and response. Let Trend Micro security experts and
industry–leading artificial intelligence help monitor and prioritize threats
detected by Deep Discovery Inspector.
Turn unknown threats into known threats. Leverage standards–based
advanced threat intelligence sharing to keep ahead of threats (STIX/
TAXII and YARA). Deep Discovery Inspector automates the sharing of
threat information across Trend and third-party security solutions, which
strengthens multiple links in the security chain simultaneously.
Network Analytics. Security professionals are flooded with threat data
from numerous sources. Network analytics help prioritize threats and
provide visibility into an attack. By looking back at months of historical
data, you will be able to see what the first point of entry was, who else in
the organization is impacted, and with whom the threat is communicating
(for example, C&C).
Page 1 of 3 Datasheet • Trend Micro™ Deep Discovery™ Inspector
Datasheet
A Key Part of Trend Vision One™ Detect and Protect Against
The XDR capabilities in Trend Vision One break down the silos between email, endpoints, • Targeted attacks and advanced threats
servers, cloud workloads, and networks. It offers broader visibility and expert security
analytics, leading to fewer alerts and more higher-confidence detections for an earlier, • Targeted and known ransomware attacks
faster response. With XDR, you can identify and respond more effectively and efficiently • Zero-day malware and document exploits
to threats, minimizing the severity and scope of an attack on the organization. Deep • Attacker behavior and other
Discovery Inspector and Trend Vision One™ – XDR for Network are valuable parts of network activity
the XDR solution, providing critical logs and visibility into unmanaged systems, such as
• Web threats, including exploits and
contractor/third-party systems, internet of things (IoT) and industrial internet of things
(IIoT) devices, printers, and bring-your-own-device (BYOD) systems. drive-by downloads
• Phishing, spear phishing, and other
email threats
• Data exfiltration
• Bots, Trojans, worms, keyloggers
• Disruptive applications
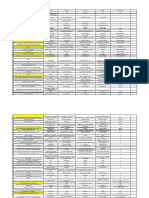
DEEP DISCOVERY INSPECTOR HARDWARE SPECIFICATIONS
Series 500/1000 Series 4000 Series 9000
Throughput 500 Mbps / 1 Gbps 4 Gbps 10 Gbps
Sandboxes Supported 2/4 20 30
Form Factor 1U rack-mount, 48.26 cm (19”) 2U rack-mount, 48.26 cm (19”) 2U rack-Mount, 48.26 cm (19”)
Weight 18.62kg (41.05 lbs) 28.6 kg (63.05 lbs) 28.6 kg (63.05 lbs)
Dimensions (WxDxH) 48.2 cm (18.98”) x 74.9 cm 48.2 cm (18.98”) x 71.55 cm (28.17”) 48.2 cm (18.98”) x 71.55 cm
(29.48”) x 4.28 cm (1.68”) x 8.68 cm (3.42”) (28.17”) x 8.68 cm (3.42”)
Management Ports 10/100/1000 base-T RJ45 port x 1 10/100/1000 base-T RJ45 10/100/1000 base-T RJ45
iDrac enterprise RJ45 x 1 port x 1 port x 1
iDrac enterprise RJ45 x 1 iDrac enterprise RJ45 x 1
Data Ports 10/100/1000 base-T RJ45 10 Gb SFP+ SR transceiver x 4 10 Gb SFP+ SR transceiver x 4
port x 5 10/100/1000 base-T RJ45 10/100/1000 Base-T RJ45
port x 5 port x 5
AC Input Voltage 100 to 240 VAC 100 to 240 VAC 100 to 240 VAC
AC Input Current 9.2A to 4.7A 10A to 5A 12A to 6.5A
Hard Drives 2 x 2 TB 3.5” SATA 4 x 1 TB 3.5” SATA 4 x 1 TB 3.5” SATA
RAID Configuration RAID 1 RAID 10 RAID 10
Power Supply 800W redundant 750W redundant 1,100W redundant
Power Consumption (Max.) 899W (max.) 847W (max.) 1,202W (max.)
Heat 3,000 BTU/hr. (max.) 2,891 BTU/hr. (max.) 4,100 BTU/hr. (max.)
Frequency 50/60 Hz 50/60HZ 50/60HZ
Operating Temp. 10 to 35 °C (50-95 °F) 10 to 35 °C (50-95 °F) 10–35 °C (50–95 °F)
Hardware Warranty 3 years 3 years 3 years
Deep Discovery Inspector virtual appliances are available at 100/250/500/1000 Mbps capacities and are deployable on VMware
vSphere 5 and above, as well as KVM. Cloud sandboxing can be added to the virtual Deep Discovery Inspector through the Trend
Micro™ Deep Discovery™ Analyzer as a Service add–on.
Page 2 of 3 Datasheet • Trend Micro™ Deep Discovery™ Inspector
Datasheet
Other network security products
Trend network security solutions provide a layered security solution to protect you from
known, unknown, and undisclosed threats.
• Deep Discovery Analyzer provides advanced sandbox analysis to extend the value
of security products such as endpoint protection, web and email gateways, network
security, and other Trend Micro™ Deep Discovery™ solutions. Deep Discovery
Analyzer can detect ransomware, advanced malware, zero-day exploits, command
and control, and multi–stage downloads resulting from malicious payloads or URLs on
Microsoft Windows and Mac operating systems.
• Trend Micro™ TippingPoint™ provides high-speed, inline intrusion prevention
system (IPS) inspection, offering comprehensive threat protection against known and
undisclosed vulnerabilities with high accuracy and low latency.
• Trend Micro™ Deep Discovery™ Director. In addition to providing central
management, data deduplication, log aggregation, and more for the Deep Discovery
family, it provides advanced threat sharing via an indicators of compromise (IoC)
exchange. It uses standards–based formats and transfers like YARA, STIX, and TAXII to
share advanced threat intelligence across your security ecosystem.
For more information, please visit
trendmicro.com
©2023 by Trend Micro Incorporated. All rights reserved. Trend Micro, Deep Discovery, TippingPoint, Trend Vision One, the Trend Micro logo, and the t-ball logo are
trademarks or registered trademarks of Trend Micro Incorporated. All other company and/or product names may be trademarks or registered trademarks of their
owners. Information contained in this document is subject to change without notice. Trend Micro, the Trend Micro logo, and the t-ball logo Reg. U.S. Pat. & Tm. Off.
[DS15_Deep_Discovery_Inspector_230725US]
For details about what personal information we collect and why, please see our Privacy Notice on our website at: trendmicro.com/privacy
Page 3 of 3 Datasheet • Trend Micro™ Deep Discovery™ Inspector
You might also like
- Case Study CyberDocument6 pagesCase Study CyberMuhammad Sardaar100% (2)
- Sean Jones and Bryce Webster Jackson - Beyond Encryption - Exploring The Tactics Ransomware Operators Use During Negotiation and Their ImpactDocument10 pagesSean Jones and Bryce Webster Jackson - Beyond Encryption - Exploring The Tactics Ransomware Operators Use During Negotiation and Their ImpactFranklin CordeiroNo ratings yet
- Artificial Intelligence Ai Elementary To Advanced Practices Cyber Defense Mechanisms Security PrivacyDocument231 pagesArtificial Intelligence Ai Elementary To Advanced Practices Cyber Defense Mechanisms Security Privacyalexander kessyNo ratings yet
- Deception Solution Overview: Deceive. Detect. DefendDocument4 pagesDeception Solution Overview: Deceive. Detect. DefendJimmy Alfaro HernandezNo ratings yet
- 4.electronic Evidence - Collection, Preservation and Appreciation PDFDocument108 pages4.electronic Evidence - Collection, Preservation and Appreciation PDFRohanPuthalathNo ratings yet
- Deep Discovery Inspector DatasheetDocument2 pagesDeep Discovery Inspector DatasheetHumberto BautistaNo ratings yet
- Deep Discovery Inspector DatasheetDocument2 pagesDeep Discovery Inspector DatasheetHumberto BautistaNo ratings yet
- Ds DD InspectorDocument2 pagesDs DD Inspectorzain_zedanNo ratings yet
- Trend Micro Deep Discovery AnalyzerDocument2 pagesTrend Micro Deep Discovery AnalyzerhaivadiNo ratings yet
- Ds-Apex-One 2021Document2 pagesDs-Apex-One 2021HenryNo ratings yet
- Zscaler DeceptionDocument7 pagesZscaler DeceptionLENIN HITLER RAMIREZ SANTA CRUZNo ratings yet
- Cyber SecurityDocument14 pagesCyber SecurityManish ChoudhuryNo ratings yet
- Data Security PracticesDocument5 pagesData Security Practicessukeerthi bmeNo ratings yet
- Trend Micro Apex One: Endpoint Security RedefinedDocument2 pagesTrend Micro Apex One: Endpoint Security Redefinedpier Aguilar RamirezNo ratings yet
- Seguridad P1Document54 pagesSeguridad P1Andres CandoNo ratings yet
- Compromise Assessment - Datasheet - ControlledDocument2 pagesCompromise Assessment - Datasheet - Controlleddigitlabs.marketingNo ratings yet
- SG MDR Service PresentationDocument17 pagesSG MDR Service PresentationDasha DeckwerthNo ratings yet
- Network Monitor Data SheetDocument2 pagesNetwork Monitor Data SheetTaha KhanNo ratings yet
- 10-21 NDR BuyersGuide V6.disarmedDocument7 pages10-21 NDR BuyersGuide V6.disarmedramramNo ratings yet
- Firewall EmbaDocument32 pagesFirewall EmbaMd.Ahnaf AkifNo ratings yet
- Group Ib Ti enDocument5 pagesGroup Ib Ti entahamesbahi123No ratings yet
- CNPT 3220 Network SecurityDocument21 pagesCNPT 3220 Network SecurityJingyu LiNo ratings yet
- Cisco Stealthwatch® Threat Intelligence (TI) LicenseDocument3 pagesCisco Stealthwatch® Threat Intelligence (TI) LicenseNikola PetrovNo ratings yet
- Securing Your Organization From Modern Ransomware: Ransomware Attacks Are Now A Team EffortDocument11 pagesSecuring Your Organization From Modern Ransomware: Ransomware Attacks Are Now A Team EfforttiagouebemoraisNo ratings yet
- Mageni - Groundbreaking Vulnerability Scanning and Vulnerability Management SolutionDocument2 pagesMageni - Groundbreaking Vulnerability Scanning and Vulnerability Management SolutionLucas MartinezNo ratings yet
- 03.bobak Group IB Portfolio UpdateDocument32 pages03.bobak Group IB Portfolio Updateericstevens77777No ratings yet
- MDR Flyer - Threat ManagementDocument2 pagesMDR Flyer - Threat ManagementDasha DeckwerthNo ratings yet
- Extending Security Intelligence With Big Data SolutionsDocument8 pagesExtending Security Intelligence With Big Data SolutionsYashNo ratings yet
- SB - Trend Micro XDRDocument3 pagesSB - Trend Micro XDRSixaxiSNo ratings yet
- Homework 1Document3 pagesHomework 1tojy.m12No ratings yet
- Intrusion Detection and Prevention Systems: Name: Md. Matiur Rahman Student ID: 000646848Document7 pagesIntrusion Detection and Prevention Systems: Name: Md. Matiur Rahman Student ID: 000646848Sonia Sultana100% (1)
- Honeypots & Honeynets: Tech TalkDocument16 pagesHoneypots & Honeynets: Tech Talkthaidt229No ratings yet
- CEH Exam Blueprint 3.0: EC-CouncilDocument5 pagesCEH Exam Blueprint 3.0: EC-CouncilYONIWO EDWARD TSEMINo ratings yet
- Ethical Hacking UpdtedDocument15 pagesEthical Hacking UpdtedvamshimatangiNo ratings yet
- Cybersecurity: It Specialist Exam ObjectivesDocument3 pagesCybersecurity: It Specialist Exam ObjectivesMercy EbiojoNo ratings yet
- Cortex XDR For Network Traffic Analysis PDFDocument2 pagesCortex XDR For Network Traffic Analysis PDFfabioccnpNo ratings yet
- Interscan Web Security Virtual Appliance: Trend MicroDocument4 pagesInterscan Web Security Virtual Appliance: Trend MicroriyasathsafranNo ratings yet
- 05 Network ForensicsDocument33 pages05 Network ForensicsMohammed LajamNo ratings yet
- By Palo Alto Networks - PA-7000 Series - DatasheetDocument4 pagesBy Palo Alto Networks - PA-7000 Series - DatasheetAbel De Los SantosNo ratings yet
- Trend Micro Apex One: Endpoint Security RedefinedDocument2 pagesTrend Micro Apex One: Endpoint Security RedefinedtestNo ratings yet
- Raj Agrawal - Expt-1 - VAPTDocument13 pagesRaj Agrawal - Expt-1 - VAPTraj.maNo ratings yet
- Ds Mobile SecurityDocument2 pagesDs Mobile Securitynugroho adiNo ratings yet
- Threat Intelligence ModuleDocument2 pagesThreat Intelligence Moduleandini eldanantyNo ratings yet
- Ds XDR For NetworksDocument3 pagesDs XDR For Networkslarry linaresNo ratings yet
- Quickly Respond To Attacks Across Your NetworkDocument4 pagesQuickly Respond To Attacks Across Your Networkhieule.mktNo ratings yet
- Summit Newsweek România Dedicat Securității CiberneticeDocument20 pagesSummit Newsweek România Dedicat Securității CiberneticeNewsweek RomaniaNo ratings yet
- XDR For Users: Trend MicroDocument3 pagesXDR For Users: Trend MicroriyasathsafranNo ratings yet
- Cybersecurity - Industry PerspectiveDocument81 pagesCybersecurity - Industry PerspectivejayantascribeNo ratings yet
- Sourcefire BRKSEC-1030Document112 pagesSourcefire BRKSEC-1030Raja AthiNo ratings yet
- Security Analytics: Big Data Analytics For Cybersecurity: A Review of Trends, Techniques and ToolsDocument6 pagesSecurity Analytics: Big Data Analytics For Cybersecurity: A Review of Trends, Techniques and ToolsHimanshu GoelNo ratings yet
- CISCO Cybersecurity Final Exam Solution by PariDocument6 pagesCISCO Cybersecurity Final Exam Solution by Paribc160200544 Mah JabeenNo ratings yet
- 3part Series Dress For Success Cybersecurity Training - Phase 1Document21 pages3part Series Dress For Success Cybersecurity Training - Phase 1Mokka EbuNo ratings yet
- The CERT Guide To System and Network Security Practices: January 2001Document19 pagesThe CERT Guide To System and Network Security Practices: January 2001JRonald85No ratings yet
- Types of Cyber Attacks E Book PDFDocument10 pagesTypes of Cyber Attacks E Book PDFDwaipayan MojumderNo ratings yet
- Cyber Threat IntelligenceDocument41 pagesCyber Threat Intelligencekt06121999No ratings yet
- Network & Network SecurityDocument14 pagesNetwork & Network SecurityDAVID MGAYANo ratings yet
- Lightcyber Behavioral AnalyticsDocument4 pagesLightcyber Behavioral AnalyticsasadaNo ratings yet
- Sed Eps PB105Document5 pagesSed Eps PB105Stefano Bbc RossiNo ratings yet
- Information Security Issues, Threats, Solution & StandradsDocument46 pagesInformation Security Issues, Threats, Solution & StandradsmasteranshulNo ratings yet
- Latest AntivirusesDocument12 pagesLatest Antivirusesplease readNo ratings yet
- National Awareness Nepal 2015Document118 pagesNational Awareness Nepal 2015A M Chandra DhamiNo ratings yet
- At A Glance - EDRDocument6 pagesAt A Glance - EDRahmed gaafarNo ratings yet
- Juan Manuel Corchado - 3 - Presentación DeepSIEMDocument13 pagesJuan Manuel Corchado - 3 - Presentación DeepSIEMfelgamNo ratings yet
- CYBER SECURITY HANDBOOK Part-2: Lock, Stock, and Cyber: A Comprehensive Security HandbookFrom EverandCYBER SECURITY HANDBOOK Part-2: Lock, Stock, and Cyber: A Comprehensive Security HandbookNo ratings yet
- 4-Port Analog Dial BoardDocument1 page4-Port Analog Dial BoardhaivadiNo ratings yet
- 8-Port Analog Dial BoardDocument1 page8-Port Analog Dial BoardhaivadiNo ratings yet
- 4-Port Digital Dial BoardDocument1 page4-Port Digital Dial BoardhaivadiNo ratings yet
- Ds Apex OneDocument2 pagesDs Apex OnehaivadiNo ratings yet
- Trend Micro Deep Discovery AnalyzerDocument2 pagesTrend Micro Deep Discovery AnalyzerhaivadiNo ratings yet
- XDR For DummiesDocument51 pagesXDR For Dummiesmbuyujean35No ratings yet
- CrowdStrike2023GlobalThreatReport UpdatedDocument42 pagesCrowdStrike2023GlobalThreatReport UpdatedSarayuth Sae-tungNo ratings yet
- NSE1 Key Cybersecurity Terms-ENDocument6 pagesNSE1 Key Cybersecurity Terms-ENitachi uchihaNo ratings yet
- Cyber and Information Security (Assignment2)Document57 pagesCyber and Information Security (Assignment2)Himanshu Sharma0% (1)
- Seminar ReportDocument19 pagesSeminar ReportSahil Sethi100% (1)
- Cyber Security at SeaDocument30 pagesCyber Security at SeaJoseph GraciousNo ratings yet
- 15: Security and Cyber LawsDocument49 pages15: Security and Cyber LawsPixelNo ratings yet
- IAS Pre FiDocument4 pagesIAS Pre FiGela SiaNo ratings yet
- Fortinet - Pre .NSE5 EDR-5.0.30q-DEMODocument14 pagesFortinet - Pre .NSE5 EDR-5.0.30q-DEMOkely.alcantara.96No ratings yet
- Grazelyn Rabe BSIT-CDocument9 pagesGrazelyn Rabe BSIT-CGrazelyn RabeNo ratings yet
- What Is An Exploit Kit (With Examples) How Do Cybercriminals Use ThemDocument11 pagesWhat Is An Exploit Kit (With Examples) How Do Cybercriminals Use ThemsetyabudhiNo ratings yet
- Exclusive GA Refresher For SBI PO Main May 2017Document43 pagesExclusive GA Refresher For SBI PO Main May 2017Jyoti SukhijaNo ratings yet
- Major-1 MCQSDocument14 pagesMajor-1 MCQSaniltimes13No ratings yet
- CyberArk EPM Overview 1Document31 pagesCyberArk EPM Overview 1Quan TranNo ratings yet
- Cyber SecurityDocument16 pagesCyber SecuritykarthikNo ratings yet
- Investor Presentation Company UpdateDocument44 pagesInvestor Presentation Company UpdatePrasad KshirsagarNo ratings yet
- Module 4: Internet ThreatsDocument10 pagesModule 4: Internet ThreatsKzy ayanNo ratings yet
- Top 10 Cyber Security Solution Providers 2020Document40 pagesTop 10 Cyber Security Solution Providers 2020The CEO ViewsNo ratings yet
- Ransomware Detection PreviewDocument46 pagesRansomware Detection Previewakhmad ismail100% (2)
- Deep Instinct Making Sense of Fileless Malware PDFDocument21 pagesDeep Instinct Making Sense of Fileless Malware PDFOsiris PHNo ratings yet
- BIT324 Networkand Information Security ExamDocument4 pagesBIT324 Networkand Information Security ExamqwztjiorxsNo ratings yet
- Ransomware CTEP Situation Manual 092023 508Document22 pagesRansomware CTEP Situation Manual 092023 508Cyril EsedoNo ratings yet
- Cybersecurity Report For SMBsDocument20 pagesCybersecurity Report For SMBsAndi Tri Jati100% (1)
- Resolving Security and Data Concerns in Cloud Computing by Utilizing A Decentralized Cloud Computing OptionDocument6 pagesResolving Security and Data Concerns in Cloud Computing by Utilizing A Decentralized Cloud Computing OptionGopala Krishna SriramNo ratings yet
- Question Bank 1Document6 pagesQuestion Bank 1siri chandanaNo ratings yet
- Cyber Security Policy For MSCB LTDDocument32 pagesCyber Security Policy For MSCB LTDthongphetlamphayphanNo ratings yet