Professional Documents
Culture Documents
Cyber Security Alignment
Cyber Security Alignment
Uploaded by
bcadept0 ratings0% found this document useful (0 votes)
8 views1 pageThis document outlines the syllabus for a cyber security course with 5 units covering key topics. The course is classified as core, carries 4 credits, and has prerequisites in basic internet and data security knowledge. The 5 units cover: 1) introduction to cyber security concepts, 2) security in operating systems and networks, 3) security countermeasures like cryptography and firewalls, 4) privacy concepts in cyberspace, and 5) security management and incident handling. The course involves 90 lecture hours over the 5 units and recommends a reference book on security in computing.
Original Description:
Original Title
cyber-security-alignment
Copyright
© © All Rights Reserved
Available Formats
DOC, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThis document outlines the syllabus for a cyber security course with 5 units covering key topics. The course is classified as core, carries 4 credits, and has prerequisites in basic internet and data security knowledge. The 5 units cover: 1) introduction to cyber security concepts, 2) security in operating systems and networks, 3) security countermeasures like cryptography and firewalls, 4) privacy concepts in cyberspace, and 5) security management and incident handling. The course involves 90 lecture hours over the 5 units and recommends a reference book on security in computing.
Copyright:
© All Rights Reserved
Available Formats
Download as DOC, PDF, TXT or read online from Scribd
Download as doc, pdf, or txt
0 ratings0% found this document useful (0 votes)
8 views1 pageCyber Security Alignment
Cyber Security Alignment
Uploaded by
bcadeptThis document outlines the syllabus for a cyber security course with 5 units covering key topics. The course is classified as core, carries 4 credits, and has prerequisites in basic internet and data security knowledge. The 5 units cover: 1) introduction to cyber security concepts, 2) security in operating systems and networks, 3) security countermeasures like cryptography and firewalls, 4) privacy concepts in cyberspace, and 5) security management and incident handling. The course involves 90 lecture hours over the 5 units and recommends a reference book on security in computing.
Copyright:
© All Rights Reserved
Available Formats
Download as DOC, PDF, TXT or read online from Scribd
Download as doc, pdf, or txt
You are on page 1of 1
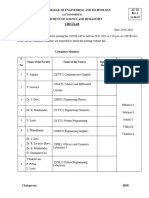
Course Code CYBER SECURITY L T P C
Core/elective/Supportive Core :10 5 0 0 4
Basic knowledge in Internet and Syllabus 2023-24
Pre- requisite
data crimes. version Onwards
Course Objectives
• Students should be able to understand.
• The transformation between threat, risk, attack and vulnerability.
• How threats materialize into attacks.
• To find information about threats, vulnerabilities and attacks.
Unit I INTRODUCTION TO CYBER SECURITY 17
Introduction -Computer Security - Threats -Harm - Vulnerabilities - Controls - Authenticat Access Control and
Cryptography - Web—User Side - Browser Attacks - Web At Targeting Users - Obtaining User or Website Data -
Email Attacks
Unit II SECURITY IN OPERATING SYSTEM & NETWORKS 17
Security in Operating Systems - Security in the Design of Operating Systems -Rootkit - Network security attack-
Threats to Network Communications - Wireless Network Security - Denial of Service - Distributed Denial-of-
Service.
Unit III DEFENCES: SECURITY COUNTERMEASURES 16
Cryptography in Network Security - Firewalls - Intrusion Detection and Prevention Systems - Network Management
- Databases - Security Requirements of Databases - Reliability and Integrity - Database Disclosure - Data Mining
and Big Data.
Unit IV PRIVACY IN CYBERSPACE 20
Privacy Concepts -Privacy Principles and Policies -Authentication and Privacy – Data Mining - Privacy on
the Web - Email Security - Privacy Impacts of Emerging Technologies- Where the Field Is Headed.
Unit V MANAGEMENT AND INCIDENTS 20
Security Planning - Business Continuity Planning - Handling Incidents - Risk Analysis - Dealing with Disaster -
Emerging Technologies - The Internet of Things - Economics - Electronic Voting - Cyber Warfare- Cyberspace and
the Law - International Laws - Cyber crime - Cyber Warfare and Home Land Security.
Total Lecture Hours 90 Hours
Reference Book(s)
1 Charles P. Pfleeger Shari Lawrence Pfleeger Jonathan Margulies, Security in computing
You might also like
- Cyber Security - I.ravi KumarDocument38 pagesCyber Security - I.ravi KumarMr. RAVI KUMAR INo ratings yet
- Lecture 3 Country Specific StrategyDocument21 pagesLecture 3 Country Specific StrategyShilukaNo ratings yet
- Renewable 1.0Document8 pagesRenewable 1.073035537rishubrother95827594No ratings yet
- Digital Notes ON Cyber Security (R18A0521) : B.Tech Iii Year - Ii Sem (R18)Document38 pagesDigital Notes ON Cyber Security (R18A0521) : B.Tech Iii Year - Ii Sem (R18)Shyam Sulbhewar100% (1)
- Cp5291 SP Syllabus1Document1 pageCp5291 SP Syllabus1Elanchezhiyan TNo ratings yet
- Cyber SecurityDocument39 pagesCyber SecurityprateekguptadelNo ratings yet
- IT Sec Net Sec Cyber Sec IT LawDocument27 pagesIT Sec Net Sec Cyber Sec IT LawCha DechavezNo ratings yet
- MCSCB Cyber SecurityDocument16 pagesMCSCB Cyber SecurityKrishna Kumaran ThampiNo ratings yet
- Lecture 3 Country Specific StrategyDocument18 pagesLecture 3 Country Specific StrategyR BNo ratings yet
- (R17A0526) Information Security Digital NotesDocument143 pages(R17A0526) Information Security Digital NotesPrafulla Durgadhar GawandeNo ratings yet
- Cyber Security NotesDocument106 pagesCyber Security NotesBhure Vedika100% (1)
- Int407:Information Security and Privacy: Session 2020-21 Page:1/1Document1 pageInt407:Information Security and Privacy: Session 2020-21 Page:1/1ayushiNo ratings yet
- Final Report v2Document21 pagesFinal Report v2KesavaNo ratings yet
- Network Security: Seminar Report OnDocument31 pagesNetwork Security: Seminar Report Onabhishek100% (1)
- IEEE DL Survey ExactDocument82 pagesIEEE DL Survey ExactArthee PandiNo ratings yet
- CNCS2004-Cybersecurity SyllabusDocument3 pagesCNCS2004-Cybersecurity SyllabusZoyaNo ratings yet
- Unit 1 Cs 191cse046jDocument21 pagesUnit 1 Cs 191cse046jTRB hubNo ratings yet
- Essentials of Cyber SecurityDocument1 pageEssentials of Cyber Securityravikumar rayala100% (1)
- Lecture 1Document34 pagesLecture 1Rimsha MukhtiarNo ratings yet
- Why You Need Cyber Security:-The Protection of Data, Networks and Computing Power. The Protection of DataDocument4 pagesWhy You Need Cyber Security:-The Protection of Data, Networks and Computing Power. The Protection of DataSainbu GuptaNo ratings yet
- Overview of University of Tennessee at ChattanoogaDocument41 pagesOverview of University of Tennessee at ChattanoogaLongNguyenNo ratings yet
- W.E.F Academic Year 2012-13 G' SchemeDocument5 pagesW.E.F Academic Year 2012-13 G' SchemeSanket bhosaleNo ratings yet
- Cyber SecurityDocument53 pagesCyber SecurityAnvesha SharmaNo ratings yet
- Network Security History Importance and FutureDocument13 pagesNetwork Security History Importance and FutureBandarAlHarbiNo ratings yet
- Cyber SecurityDocument3 pagesCyber SecuritySAMAY N. JAINNo ratings yet
- CNS Theory Syllabus PDFDocument3 pagesCNS Theory Syllabus PDFnootiNo ratings yet
- Cyber Law Cyber Crime & IPR NotesDocument33 pagesCyber Law Cyber Crime & IPR NotesPRAVEEN M RNo ratings yet
- Cyber Law Cyber Crime & IPR NotesDocument68 pagesCyber Law Cyber Crime & IPR Notespoornir9972No ratings yet
- AI 403 Cyber Security and ForensicsDocument2 pagesAI 403 Cyber Security and Forensicssomnath.sinhaNo ratings yet
- ManagementDocument16 pagesManagementAbhishek KhandekarNo ratings yet
- CF SyllabusDocument1 pageCF SyllabusSindhuja ManoharNo ratings yet
- Cyber Security Notes 4-1Document81 pagesCyber Security Notes 4-1Sripriya BellaryNo ratings yet
- 16CS2E56 Cyber Security SyllabusDocument1 page16CS2E56 Cyber Security SyllabuskrishnakumarNo ratings yet
- Network Security & Cryptography BookDocument204 pagesNetwork Security & Cryptography BookYash Bhardwaj100% (1)
- 1 - Introduction - Week 1 - NSDocument46 pages1 - Introduction - Week 1 - NSnasir jaanNo ratings yet
- Zero Trust Architecture - Protection Against Cyber AttacksDocument17 pagesZero Trust Architecture - Protection Against Cyber AttacksVidyun lambaNo ratings yet
- Common Subjects-5Document1 pageCommon Subjects-5varsha guptaNo ratings yet
- Cyber Security SyllabusDocument1 pageCyber Security Syllabusshubh1996sriNo ratings yet
- NIS Project Final PMV 23Document3 pagesNIS Project Final PMV 23Pooja AbhangNo ratings yet
- Soniya Hariramani (CYBERSECURITY ReportDocument39 pagesSoniya Hariramani (CYBERSECURITY Reportsoniya hariramaniNo ratings yet
- Cyber Security NotesDocument51 pagesCyber Security NotesBhure VedikaNo ratings yet
- Lecture#01 - Introduction To Information Security COnceptsDocument54 pagesLecture#01 - Introduction To Information Security COnceptsawsdNo ratings yet
- Network Security and Anti HackingDocument8 pagesNetwork Security and Anti Hackingnewlog6303No ratings yet
- Network Security: Dr. Imran RashidDocument83 pagesNetwork Security: Dr. Imran RashidhafeezNo ratings yet
- Adobe Scan Jan 17, 2024Document1 pageAdobe Scan Jan 17, 2024SWARUP SAMANTANo ratings yet
- Introduction To IT SecurityDocument32 pagesIntroduction To IT SecurityDilshanNo ratings yet
- Chapter 4Document39 pagesChapter 4Soll HaileNo ratings yet
- Cyber SecurityDocument68 pagesCyber SecuritymoisertarienNo ratings yet
- Cyber Security - (R20a898896202)Document75 pagesCyber Security - (R20a898896202)anketsarkar964No ratings yet
- Cyber Security ResearchDocument9 pagesCyber Security Researchdagy36444No ratings yet
- Cyber Security (R18A0521) Lecture Notes: Department of CseDocument37 pagesCyber Security (R18A0521) Lecture Notes: Department of CseSRAVANTHI SALLARAM100% (2)
- CS1p IntroductionDocument60 pagesCS1p IntroductionjoshuaNo ratings yet
- Cybersecuritypresentation 220328172438Document88 pagesCybersecuritypresentation 220328172438Arifin ChowdhuryNo ratings yet
- Cyber Security 06012022Document3 pagesCyber Security 06012022Nilesh Waikar 2No ratings yet
- Information Security Privacy SyllabusDocument1 pageInformation Security Privacy SyllabusANUPMA PRITYNo ratings yet
- Cyber Security (R20a6202)Document75 pagesCyber Security (R20a6202)Anacademy FreeNo ratings yet
- Cybersecurity AU SyllabusDocument2 pagesCybersecurity AU SyllabusAjay MukundNo ratings yet
- Network Security Traceback Attack and React in the United States Department of Defense NetworkFrom EverandNetwork Security Traceback Attack and React in the United States Department of Defense NetworkNo ratings yet
- Data VisualizationDocument1 pageData VisualizationbcadeptNo ratings yet
- 1st CCM Cir IT-BDocument1 page1st CCM Cir IT-BbcadeptNo ratings yet
- Digital 01Document2 pagesDigital 01bcadeptNo ratings yet
- ReactnativeDocument1 pageReactnativebcadeptNo ratings yet
- Ijcrt2108014 - 2021Document5 pagesIjcrt2108014 - 2021bcadeptNo ratings yet
- Brief Introduction To SSL: SSL Connection Using Tlsv1.2 SSL Connection Using Jks SSL Connection Using Oracle WalletsDocument23 pagesBrief Introduction To SSL: SSL Connection Using Tlsv1.2 SSL Connection Using Jks SSL Connection Using Oracle WalletspradeepNo ratings yet
- MIT - Design and Feasibility ReportsDocument3 pagesMIT - Design and Feasibility ReportsMuhamad Andri KurniawanNo ratings yet
- Phishing, Pharming, Vishing and SmishingDocument2 pagesPhishing, Pharming, Vishing and SmishingHussain100% (1)
- BPOS Standard Deployment Guide February2010 PDFDocument100 pagesBPOS Standard Deployment Guide February2010 PDFRuben Dario Pinzón ErasoNo ratings yet
- Hyperion SSL ModuleDocument32 pagesHyperion SSL ModuleGabriel GutierrezNo ratings yet
- GartnerDocument2 pagesGartnersusNo ratings yet
- Ccsa - 156-215.80 V18.75Document142 pagesCcsa - 156-215.80 V18.75mikos84187No ratings yet
- Zimbra Desktop Installation and Setup GuideDocument28 pagesZimbra Desktop Installation and Setup GuideRandy GullickNo ratings yet
- Long Term Project Based EngagementsDocument4 pagesLong Term Project Based EngagementsIko JaroNo ratings yet
- CNR-BR2 ManualDocument77 pagesCNR-BR2 ManualCristian SerbanoiuNo ratings yet
- Paket 5000 Up 531 08.25.22 25 08 2022Document7 pagesPaket 5000 Up 531 08.25.22 25 08 2022pathul azizNo ratings yet
- Ewan Ptact 5 2 8Document6 pagesEwan Ptact 5 2 8Muhammad HudzaifahNo ratings yet
- வாடகை ஒப்பந்த பத்திரம் Rental Agreement Format In Tamil Font (q6ng7mdeyjnv)Document2 pagesவாடகை ஒப்பந்த பத்திரம் Rental Agreement Format In Tamil Font (q6ng7mdeyjnv)ÂaryanArun0% (1)
- Cisco: Security Architecture For Systems EngineerDocument5 pagesCisco: Security Architecture For Systems EngineerAhmedin abukiaNo ratings yet
- Digital Learning ToolsDocument40 pagesDigital Learning ToolsJaver BorngoNo ratings yet
- Motorola ST v1.5Document85 pagesMotorola ST v1.5László SzabóNo ratings yet
- Lecture 2 - Introduction: Information Assurance AND SecurityDocument23 pagesLecture 2 - Introduction: Information Assurance AND SecurityApril VasquezNo ratings yet
- Advantages and Disadvantages of InternetDocument2 pagesAdvantages and Disadvantages of InternetABDELHAKIM ELHANINo ratings yet
- SIP Presentation 17599 NurhakimahDocument24 pagesSIP Presentation 17599 NurhakimahSyazana RosliNo ratings yet
- Converting APs To Instant APsDocument2 pagesConverting APs To Instant APsAsnake TegenawNo ratings yet
- Session Management: 7.1. What Is Session and How It Works?Document5 pagesSession Management: 7.1. What Is Session and How It Works?Prince JuttNo ratings yet
- Your Guide To Free Website TrafficDocument75 pagesYour Guide To Free Website TrafficJoe DestinyNo ratings yet
- A Component Of: Microsoft WindowsDocument4 pagesA Component Of: Microsoft WindowsVishal KumarNo ratings yet
- What Is The Jira Family of Products - Jira Software Cloud - Atlassian SupportDocument5 pagesWhat Is The Jira Family of Products - Jira Software Cloud - Atlassian Supporteduard diezNo ratings yet
- Cybersecurity MidtermsDocument13 pagesCybersecurity Midtermsinbox.privvellyNo ratings yet
- 20m Triangle High Mast With Foundation - Manufactured Goods - NatureDocument5 pages20m Triangle High Mast With Foundation - Manufactured Goods - NatureEr Mahavir MiyatraNo ratings yet
- My Activities in Module 2Document7 pagesMy Activities in Module 2Devine Gabat100% (6)
- Integration Suite Managed Gateway - Cloud Connector ConfigurationDocument28 pagesIntegration Suite Managed Gateway - Cloud Connector ConfigurationrafaelmajorNo ratings yet
- List of Engineering Colleges in PuneDocument4 pagesList of Engineering Colleges in PunesaurabhNo ratings yet
- Gmail - Your Plastiq Payment ID #Pny9emp Has Been Approved (Ref - 00D61alVC. - 5004N1LhgXK - Ref)Document3 pagesGmail - Your Plastiq Payment ID #Pny9emp Has Been Approved (Ref - 00D61alVC. - 5004N1LhgXK - Ref)Zearl ClarkNo ratings yet