Professional Documents
Culture Documents
MRI Magnetom Trio syngoMR-pages-4
MRI Magnetom Trio syngoMR-pages-4
Uploaded by
Omar SalahCopyright:
Available Formats
You might also like
- VersaLink C405 Service Manual PDFDocument862 pagesVersaLink C405 Service Manual PDFAbrahan Castro75% (4)
- VersaLink C405 Service ManualDocument858 pagesVersaLink C405 Service ManualAlex Rodriguez BarronNo ratings yet
- DRS - Installation GuideDocument26 pagesDRS - Installation GuideEduNo ratings yet
- XEROX WorkCentre 5945 5955 Service Manual PDFDocument1,366 pagesXEROX WorkCentre 5945 5955 Service Manual PDFJJ JJ50% (6)
- IBM WebSphere Application Server Interview Questions You'll Most Likely Be AskedFrom EverandIBM WebSphere Application Server Interview Questions You'll Most Likely Be AskedNo ratings yet
- Cybersecurity Information Gathering Using Kali LinuxDocument93 pagesCybersecurity Information Gathering Using Kali LinuxWanderJunior100% (4)
- Service Programme: Volvo Construction EquipmentDocument4 pagesService Programme: Volvo Construction Equipmentp_jankoNo ratings yet
- Xerox Workcentre 5790 Family 5735 5740 5745 5755 5775 Service ManualDocument1,634 pagesXerox Workcentre 5790 Family 5735 5740 5745 5755 5775 Service ManualLuis Alberto70% (30)
- Lesson 8: Implementing Identity and Account Management ControlsDocument38 pagesLesson 8: Implementing Identity and Account Management ControlsPhan Sư ÝnhNo ratings yet
- Avaya Solution & Interoperability Test LabDocument65 pagesAvaya Solution & Interoperability Test LabRaghavendra BhatNo ratings yet
- CalibrationDocument28 pagesCalibrationPatriciaAraujo100% (1)
- Workforce AES71Document37 pagesWorkforce AES71Vicky NicNo ratings yet
- Eng GB SP A60h Stage IV V DDocument8 pagesEng GB SP A60h Stage IV V DYudha SetiawanNo ratings yet
- Cyberoam V 10.01 Build 0472Document27 pagesCyberoam V 10.01 Build 0472CharnwatNo ratings yet
- AltaLink8090 Family SMDocument1,859 pagesAltaLink8090 Family SManon_14517322783% (6)
- Asset Management - Caliberation ProcessingDocument23 pagesAsset Management - Caliberation ProcessingsundargowdaNo ratings yet
- Acuson x300 Syngo Service Software IntroductionDocument51 pagesAcuson x300 Syngo Service Software IntroductionCarlos MoraNo ratings yet
- BEMsl 0108 enDocument344 pagesBEMsl 0108 enCarlos Roberto SantosNo ratings yet
- 7694 Headspace Preventive Maintenance ChecklistDocument5 pages7694 Headspace Preventive Maintenance ChecklistRafael CovaNo ratings yet
- Anjali FinalDocument51 pagesAnjali Final7974patillsNo ratings yet
- OLA (18) 001 eduTEAMS CESNETDocument9 pagesOLA (18) 001 eduTEAMS CESNEThallarmemon100% (1)
- SPERREDocument6 pagesSPERRESalman KapoorNo ratings yet
- Element Management System User Manual V1 4 1Document159 pagesElement Management System User Manual V1 4 1htrejos15923No ratings yet
- Impact AACC62 PDFDocument78 pagesImpact AACC62 PDFShobhit TiwariNo ratings yet
- A Guide For Service TechniciansDocument70 pagesA Guide For Service Techniciansapi-3756430No ratings yet
- Vision WFMRTACTIDocument36 pagesVision WFMRTACTIRohan MaradiaNo ratings yet
- Ecma-354 (Csta Pase III)Document29 pagesEcma-354 (Csta Pase III)jean-phileNo ratings yet
- Simbolo de Cancelación Avaya Communication ManagerDocument4 pagesSimbolo de Cancelación Avaya Communication Managerclobo94No ratings yet
- Portable Filters mf90 SeriesDocument34 pagesPortable Filters mf90 SeriesMaya Surya MirantiNo ratings yet
- Wc5945f Service ManualDocument1,448 pagesWc5945f Service Manualmorrison1981No ratings yet
- eng-GB20019092F HDocument4 pageseng-GB20019092F HVinod SekharNo ratings yet
- CBLM-Solano 1Document8 pagesCBLM-Solano 1Tyron Rex SolanoNo ratings yet
- ControlsDocument34 pagesControlsmikeincognito100% (1)
- 5 Programming and Testing: Service RoutinesDocument3 pages5 Programming and Testing: Service RoutinesCebrail GüzelNo ratings yet
- SAGDocument63 pagesSAGdyodenNo ratings yet
- User's Manual Servo-S Ventilator System V7.0Document185 pagesUser's Manual Servo-S Ventilator System V7.0abdessamaNo ratings yet
- 11xx12xx SMDocument44 pages11xx12xx SMfanticelliNo ratings yet
- LEAN - TPM - Autonomous Maintenance Steps - Step 0: EducationDocument3 pagesLEAN - TPM - Autonomous Maintenance Steps - Step 0: EducationkeshunaNo ratings yet
- User S Manual Servo-S Ventilator System V7.0Document183 pagesUser S Manual Servo-S Ventilator System V7.0Karan JejurkarNo ratings yet
- EMC Centera 4.0 GlobalServices Release Notes Rev.a37Document94 pagesEMC Centera 4.0 GlobalServices Release Notes Rev.a37Eero AhoNo ratings yet
- Bizhub 350 250 Ineo 350 250 SM SecurityDocument21 pagesBizhub 350 250 Ineo 350 250 SM SecurityCristian BobaruNo ratings yet
- Unitronics Remote Operator AppQuickStartDocument6 pagesUnitronics Remote Operator AppQuickStartjuan miguelNo ratings yet
- WC6655 Service ManualDocument528 pagesWC6655 Service ManualMapsonNo ratings yet
- Technical Service Bulletin: ConditionDocument3 pagesTechnical Service Bulletin: ConditionJustinas RackauskasNo ratings yet
- Application Notes For Xima Chronicall 4.0 With Avaya IP Office 11.0 - Issue 1.0Document27 pagesApplication Notes For Xima Chronicall 4.0 With Avaya IP Office 11.0 - Issue 1.0guillermo granadosNo ratings yet
- Configuring Cybertech Pro With Avaya CM and AESDocument48 pagesConfiguring Cybertech Pro With Avaya CM and AESIsaac PinheiroNo ratings yet
- Alu Asm61 CS1KDocument47 pagesAlu Asm61 CS1KAdrian KumarNo ratings yet
- 1040M Control CNC Num Manual PDFDocument390 pages1040M Control CNC Num Manual PDFEdgar A Bernal100% (1)
- TelephoneDocument11 pagesTelephonevarun naikNo ratings yet
- Optical Line Terminal Equipment Element Management System User ManualDocument19 pagesOptical Line Terminal Equipment Element Management System User ManualCesar PallaresNo ratings yet
- Mobile TV ViewerDocument6 pagesMobile TV ViewerJekBrionesNo ratings yet
- Optical Line Terminal Equipment Element Management System User ManualDocument19 pagesOptical Line Terminal Equipment Element Management System User ManualCesar PallaresNo ratings yet
- Avaya ConfDocument42 pagesAvaya ConfGroWBusiness SMDNo ratings yet
- Exacq Hardening GuideDocument11 pagesExacq Hardening GuideunstrainNo ratings yet
- OUT Serial Uniqueness Errors v1.2Document58 pagesOUT Serial Uniqueness Errors v1.2StefanGarnetNo ratings yet
- Call Recovery TRDocument14 pagesCall Recovery TRStocktube lohNo ratings yet
- Sd10752 Revit External Services Arnost Lobel HandoutDocument37 pagesSd10752 Revit External Services Arnost Lobel HandoutAugusto SchiapatiNo ratings yet
- Event ID 7009 - Basic Service OperationsDocument1 pageEvent ID 7009 - Basic Service OperationsdhruvNo ratings yet
- Application Notes For The Grandstream Networks SIP Telephones With Avaya Communication Manager 4.0.1 and Avaya SIP Enablement Services 4.0Document30 pagesApplication Notes For The Grandstream Networks SIP Telephones With Avaya Communication Manager 4.0.1 and Avaya SIP Enablement Services 4.0playplaypspNo ratings yet
- SERVOi Operman 6691512 R00 V7dot0 120604 EN ALL LRDocument273 pagesSERVOi Operman 6691512 R00 V7dot0 120604 EN ALL LRKaran JejurkarNo ratings yet
- Oracle Enterprise Manager Grid Control 11g R1: Business Service ManagementFrom EverandOracle Enterprise Manager Grid Control 11g R1: Business Service ManagementNo ratings yet
- Middleware Management with Oracle Enterprise Manager Grid Control 10g R5From EverandMiddleware Management with Oracle Enterprise Manager Grid Control 10g R5No ratings yet
- Thayer Cyber Hacking in Southeast Asia BibliographyDocument2 pagesThayer Cyber Hacking in Southeast Asia BibliographyCarlyle Alan ThayerNo ratings yet
- Andrew Secure RPC ProtocolDocument10 pagesAndrew Secure RPC ProtocolanjanaNo ratings yet
- What Is DLP?: Data Loss PreventionDocument3 pagesWhat Is DLP?: Data Loss PreventionSancheetNo ratings yet
- Incidentrequest Closed Monthly AugDocument305 pagesIncidentrequest Closed Monthly Augأحمد أبوعرفهNo ratings yet
- Pen Testing BasicsDocument153 pagesPen Testing BasicsChristopher C. Cheng100% (2)
- Nozomi Networks CMC Data SheetDocument10 pagesNozomi Networks CMC Data SheetMunawar BhuttoNo ratings yet
- Advances in NW and DSSDocument218 pagesAdvances in NW and DSSGaurav GRNo ratings yet
- Paket 5000 Up 531 08.25.22 25 08 2022Document7 pagesPaket 5000 Up 531 08.25.22 25 08 2022pathul azizNo ratings yet
- DarazDocument24 pagesDarazshresthakrishna231No ratings yet
- Assignment - 8 SolutionDocument5 pagesAssignment - 8 SolutionGnaneswar reddyNo ratings yet
- Installing and Configuring SpanVADocument81 pagesInstalling and Configuring SpanVAAlfredo Martin100% (1)
- AWS+SAA C03+Exam+Guide+Mapped+to+VideosDocument29 pagesAWS+SAA C03+Exam+Guide+Mapped+to+VideosAmit KumarNo ratings yet
- Kentico CMS 7.0 Security GuideDocument67 pagesKentico CMS 7.0 Security GuidefojtkfNo ratings yet
- Ethical Hacking and Countermeasures Threats and Defense Mechanisms PDFDocument2 pagesEthical Hacking and Countermeasures Threats and Defense Mechanisms PDFJonathan0% (1)
- Ipsec Between SRX and VyosDocument6 pagesIpsec Between SRX and VyosSon Tran Hong Nam100% (1)
- Websmp230.sap-Ag - de Sap (bD1lbiZjPTAwMQ ) BC BSP SPN Ne PDFDocument1 pageWebsmp230.sap-Ag - de Sap (bD1lbiZjPTAwMQ ) BC BSP SPN Ne PDFCarlosNo ratings yet
- CCNA Security: Chapter Two Securing Network DevicesDocument70 pagesCCNA Security: Chapter Two Securing Network DevicesNicole Alejandra Pérez TapiaNo ratings yet
- Cloud Spec Final ProjectsDocument10 pagesCloud Spec Final ProjectsKavi GuruNo ratings yet
- Cybersecurity AOAO PDFDocument172 pagesCybersecurity AOAO PDFharassmeNo ratings yet
- EssayDocument13 pagesEssayT1911No ratings yet
- Digital Forensik PDFDocument29 pagesDigital Forensik PDFChyntia D. RahadiaNo ratings yet
- Rules of Netiquette (G2)Document12 pagesRules of Netiquette (G2)Abdul Jakeem CastanosNo ratings yet
- CV Pentester Nguyễn Phúc HảiDocument1 pageCV Pentester Nguyễn Phúc HảiHải Nguyễn PhúcNo ratings yet
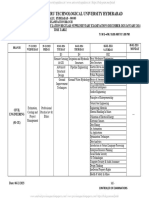
- FN B.Tech IV - I R18Document9 pagesFN B.Tech IV - I R18VigneshNo ratings yet
- Microsoft - Building A Holistic Insider Risk Management ProgramDocument52 pagesMicrosoft - Building A Holistic Insider Risk Management ProgramTruong DuyNo ratings yet
- Nozomi Networks Oil Gas Producer Case StudyDocument4 pagesNozomi Networks Oil Gas Producer Case Studymario calderonNo ratings yet
- K012581 8.0 Manage Information Technology (IT) 0Document42 pagesK012581 8.0 Manage Information Technology (IT) 0tewehaNo ratings yet
- US DOT FY22-26 Strategic PlanDocument51 pagesUS DOT FY22-26 Strategic Planlilikwbs9334No ratings yet
MRI Magnetom Trio syngoMR-pages-4
MRI Magnetom Trio syngoMR-pages-4
Uploaded by
Omar SalahOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
MRI Magnetom Trio syngoMR-pages-4
MRI Magnetom Trio syngoMR-pages-4
Uploaded by
Omar SalahCopyright:
Available Formats
CHAPTER
A.4 Service Functions A.4
The system provides a range of service functions for mainte-
nance, checking, and configuring the system for authorized
users, i.e. system administrators. A.4
➭ For technical reasons, the user interface of the service func-
tions is always in English independent of the national lan-
guage selected.
0.0
syngo MR 2006T A.4–1
Service Functions Basics
Displaying the maintenance status A.4
To ensure smooth operation, your system must be maintained
at certain intervals. A.4
The system contains a dialog box which shows you when your
system must be inspected again. A.4
✧ Call up Options > Maintenance....
The Maintenance Status dialog box is displayed. A.4
➭ On monochrome monitors, it might be difficult to see the
progress bar.
0.0
A.4–2 Operator Manual
Basics Service Functions
The progress bar shows you when the next maintenance of
your system is due by means of a colored display. A.4
As long as the display is in the green range, you can close the
window again with OK. If the bar moves into the red range, you
can only close this window again after maintenance has been
performed. A.4
➭ In that case, move the window to one side, finish off the exam-
ination, and contact Siemens Service.
➭ For further information, please contact your Siemens Service
or your system administrator.
0.0
syngo MR 2006T A.4–3
Service Functions Basics
Local service A.4
In addition to the user-specific configuration, there is a configu-
ration level for authorized users which is protected by a pass-
word. A.4
✧ Select Options > Service > Local Service... to call up the
Authentication window.
Depending on the configuration access rights in your system
several service levels are available. A.4
➭ For further information, please contact your Siemens Service
or your system administrator.
0.0
A.4–4 Operator Manual
Basics Service Functions
Remote service access A.4
Your system can also be serviced by Siemens Service via
modem. A.4
In the Remote Service Access Control window, you can grant
access rights to service so that service personnel can perform
maintenance. A.4
✧ Call up Options > Service > Remote Service... to display
the Remote Service Access Control dialog box.
0.0
syngo MR 2006T A.4–5
Service Functions Basics
A.4
NOTE
As long as you have assigned full access rights to service,
i.e. maintenance is in progress, you cannot continue
working with your system. A.4
✧ Select Limited Access or No Access and click OK or
Apply to continue.
➭ When switched on, remote service access is only possible
from trusted systems (systems with which your syngo MR
system has exchanged proved certificates).
A.4
C AU T I O N
Source of danger: Terminating remote service without
consultation with the service engineers. A.4
Consequence: Terminating the remote service ends all
service processes and causes system malfunctions. A.4
Remedy: Always consult with a service engineer before
terminating remote service. A.4
➭ For further information, please contact your Siemens Service
or your system administrator.
0.0
A.4–6 Operator Manual
Basics Service Functions
Logbook A.4
Your system has a logbook that records all system and applica-
tion-relevant events, for example error messages. A.4
✧ Call up Options > Service > Event Log... to display the
Event Log dialog box.
You can select the type and date of the messages that you want
to display. A.4
➭ For further information, please contact your Siemens Service
or your system administrator.
0.0
syngo MR 2006T A.4–7
Service Functions Basics
Configuring the MR system A.4
As an authorized user or system administrator you can set
syngo MR to the exact configuration of your MAGNETOM. This
includes, for example, specifying the MAGNETOM type, the
optional system components and environmental conditions. A.4
✧ Call up Options > Service > Local Service.
✧ Enter a new password and click on the button OK in the
Authentication dialog window.
0.0
A.4–8 Operator Manual
PART
B Security Package B.0
B.1 Introduction
Terms and definitions in security ............................... B.1–5
B.2 Information for Administrators
Configuration of the security system .............................. B.2–2
Preparatory steps .................................................... B.2–12
Workflow for the configuration of
the security system .................................................. B.2–16
Configuration of user accounts ................................ B.2–25
Configuration of groups and roles ........................... B.2–35
Access control ......................................................... B.2–44
Audit trail and log files .................................................. B.2–71
Opening the configuration for audit trail storing ....... B.2–75
Configuring the storage of the audit trail .................. B.2–77
Opening the Audit Trail Filter and Viewer ................ B.2–86
Defining events to be recorded in the audit trail ...... B.2–88
Viewing log files ....................................................... B.2–91
Storing and deleting log files ................................... B.2–94
What to do when the audit trail blocks
the system ............................................................... B.2–97
Secure transfer of data ................................................ B.2–99
B.3 Information for Users
User management and access control .......................... B.3–2
Logging on and off ..................................................... B.3–5
Emergency access....................................................... B.3–11
Failed log on ................................................................ B.3–12
Protecting data from unauthorized access ................... B.3–13
Service access ............................................................. B.3–15
Generating a service password for local access ..... B.3–17
0.0
syngo MR 2006T B–1
Contents Safety standards in syngo MR
Recorded user transactions (audit trail) ....................... B.3–20
B.4 Information for Service Technicians
Service access ............................................................... B.4–2
Local access .............................................................. B.4–3
Remote access .......................................................... B.4–5
Backup & restore ............................................................ B.4–7
0.0
B–2 Operator Manual
CHAPTER
B.1 Introduction B.1
Data and Function Based on diagnostic images and medical reports decisions are
Security B.1 made that affect the health of patients. Therefore, in modern
health care it is necessary to protect such sensitive documents
from unauthorized access and to record all actions on the
data. B.1
The Health Insurance Portability and Accountability Act
(HIPAA) is a legal requirement to ensure the privacy, integrity
and consistency of patient data in health care. B.1
In supporting HIPAA, syngo MR provides competent user man-
agement and highly configurable access control to implement
privacy, integrity and consistency of patient data in health care
which may be required by country specific regulatory. B.1
❏ Access to functions as well as to data is only permitted to
authenticated and authorized users. Each user is identifiable
at all times.
❏ Logon and action on data such as creation, read, update and
deletion are recorded in an audit trail. The audit trail can only
be viewed by authorized users.
❏ syngo MR only accepts DICOM Query/Retrieve requests
from trusted hosts. Requests from unknown hosts are
rejected.
❏ Communication during secured remote service sessions is
encrypted.
❏ If the computer is unused for a specific period of time, the
screen is automatically locked.
0.0
syngo MR 2006T B.1–1
Introduction Safety standards in syngo MR
B.1 B.1
NOTE
Security has to be set up on every workstation except for
satellite consoles, which take the security settings from
their main console. Therefore, you cannot configure the
security system on satellite consoles. B.1
Furthermore, if the computer is connected to a hospital
network, all partner workstations have to be set up for
security, otherwise a security gap will exist. B.1
Scope B.1 Security in syngo MR provides the infrastructure that is neces-
sary to protect patient data from unauthorized access. Only
persons who need to see certain data will have access to it, and
only persons with the necessary data access rights will be able
to modify data. B.1
The security system consists of the following parts: B.1
❏ Authentication of users who are working on the system
❏ Access protection to patient data with user specific permis-
sions
❏ Protection for execution of application functionality with user-
specific privileges
❏ Logging the access to patient data in an AuditTrail
0.0
B.1–2 Operator Manual
Safety standards in syngo MR Introduction
Use Cases B.1 The following use cases show you some benefits of the syngo
MR user management and security system. B.1
❏ To ensure high throughput of patients, two assistants work
on one system at the same time. While one assistant pre-
pares a patient for the next examination at the modality, the
other assistant sends the images from the previous examina-
tion to the store. The assistants can take over and log on
without a restart of the application or a significant delay being
caused due to a patient data unload.
❏ A system can be shared between wards or hospitals, and
patient data is only visible to the staff of the ward/hospital
that has acquired the data.
❏ A radiologist working in a radiology department of a hospital
can also have his or her own practice and use the hospital’s
systems for examinations of own patients. For example,
depending on the current role (“radiologist in hospital“ or
“radiologist for private patients“) he/she has access to a
wider or more restricted range of functions for post-process-
ing images.
❏ The presence of a VIP patient in the hospital is kept confi-
dential. Data acquisition is carried out by the departmental
head and one assistant. The acquired images and even the
existence of the patient’s records is hidden from all other
users of the system.
0.0
syngo MR 2006T B.1–3
Introduction Safety standards in syngo MR
Structure of the This documentation distinguishes between three types of
Documentation B.1 users. B.1
❏ Information for Administrators
In this part of the documentation, administrators find all the
information they need to manage the security system, from
activating the security package, through managing users
and access control to configuring the audit trail.
→ Chapter B.2, Information for Administrators
❏ Information for Users
This part of the documentation shows the user how to log on
and off, how to work efficiently and what to do when he/she
forgot the password. It also shows how to enable access to
a service technician (local and remote access).
→ Chapter B.3, Information for Users
❏ Information for Service Technicians
Service technicians can enter the system locally or remotely.
This documentation part is restricted to the most common
service issues.
A special source of information aimed at service technicians
is available in the Service Software Online Help.
→ Chapter B.4, Information for Service Technicians
0.0
B.1–4 Operator Manual
Safety standards in syngo MR Introduction
Terms and definitions in security B.1
Access Rights B.1 In syngo MR security, rights protect the access to patient
health information (data) with group/user specific permissions.
B.1
Authentication B.1 Authentication of users who are working with syngo MR is the
underlying basis of all security measures. A user account is cre-
ated for every person who will be working with syngo MR. To
log on to the system, the user enters his/her user account and
password. By this, a user is identifiable.
B.1
Audit Trail B.1 On a secure system, all actions on data are logged. syngo uses
auditing to track which user account was used to access files or
other objects, as well as logon attempts, system shutdowns or
restarts, and similar events. B.1
Only authorized users can track auditing activity by viewing the
log files of the audit trail. B.1
The log files of the audit trail need to be stored on a regular
schedule.
B.1
Authorization B.1 Authorization means: B.1
❏ Data Access: Only users who need access to certain patient
data can view it (for example, all medical personnel on
Ward A).
❏ Functional Privileges: Only users with the necessary autho-
rization can modify the data (for example, only doctors would
have the right to change the work status).
0.0
syngo MR 2006T B.1–5
Introduction Safety standards in syngo MR
Data Access and Groups B.1 The data access security check is based on groups and users:B.1
❏ Users need to have access to patient data within their sphere
of influence (for example, their ward).
❏ Users are assigned to groups that correspond with their
sphere of influence; these groups are allowed access to the
corresponding patient data.
It is easier to manage permissions for groups than for individ-
ual users.
Access to patient data is secured through the needed permis-
sions: In order to reduce complexity, only the following permis-
sion levels are implemented: B.1
❏ NO ACCESS
❏ FULL CONTROL
0.0
B.1–6 Operator Manual
Safety standards in syngo MR Introduction
Everyone (Group and syngo MR security makes use of the “Everyone” group and a
Role) B.1 “Everyone” role. B.1
❏ The “Everyone” group is the default group for setting up
access to data. If the “Everyone” group is configured to have
access to all data within the hospital, all users will have
access to all data (regardless of any group or individual set-
tings).
It is therefore essential that the “Everyone” group is restricted
to patient data that everyone must have access to (for exam-
ple, emergency patients).
❏ The “Everyone” role is the default level for granting privileges
to users. If all privileges are assigned to “Everyone”, the con-
figuration of other roles or individuals will not have any actual
effect.
It is therefore essential to limit the privileges of the “Every-
one” role to those that everyone must have.
All users potentially have full access to data and functions
because the default settings of the “Everyone” group and role
allow full access. The effective rights for a user depend on the
configuration of this group and role. B.1
0.0
syngo MR 2006T B.1–7
Introduction Safety standards in syngo MR
B.1
NOTE
Because it is not possible to deny rights, the “Everyone”
group and role have but the user shall not, we recommend
to take special care when configuring the data access
permission and the functional privileges. B.1
You can follow two different strategies for the “Everyone”
setup: B.1
❏ Following the “Allow nothing” strategy, you would withdraw
almost all rights from the “Everyone” group and role and then
set up the user groups and the roles. In this case, even com-
mon rights would have to be assigned to every group and
role.
❏ Following the “Common rights” strategy, you would only with-
draw critical rights that are not needed by all users.
A useful procedure could be to set up the desired permis-
sions, and then check the effective permissions. When you
are finished, you can remove any unnecessary privileges
from the “Everyone” group. You must then re-check the effec-
tive permissions.
0.0
B.1–8 Operator Manual
Safety standards in syngo MR Introduction
❏ Please take care not to configure “No Access” for all groups,
because then even fall-back data objects are can no longer
be accessed.
We recommend to allow Full Control, for example, for the
STANDARD patient group at the “Everyone” configuration
level. This would allow all users access to the “standard”
patients (for example, any patients who have not yet been
assigned to a ward).
Groups B.1 Groups are assigned to users which are members of a team or
a department. All members of a group receive the same data
access rights (permission, for example, to view or to process
data). B.1
Establishing groups helps to efficiently assign data access
rights to users and reduces the time needed for configuration.
B.1
Permissions B.1 Data access rights. The right to create, read, update, delete or
protect data is granted via permissions. The following permis-
sion levels are available: B.1
❏ NO ACCESS
❏ FULL CONTROL
0.0
syngo MR 2006T B.1–9
Introduction Safety standards in syngo MR
Privileges B.1 The right to execute functions is granted via privileges. The
functional security check is based on roles and users: B.1
❏ Users need to perform functions that correspond with their
role in the hospital, for example, nurse, physician, office
desk, …
❏ Privileges are managed by roles.
It is easier to manage privileges for roles than for individual
users.
❏ Users are associated with roles and inherit the correspond-
ing privileges.
Roles B.1 Users having the same tasks are assigned a role (for example,
radiologists, administrators, or technicians). Then all users of a
role have the same right to execute functions, such as storing
data. B.1
Establishing roles helps to efficiently assign execution rights to
users and reduces the time needed for configuration. B.1
0.0
B.1–10 Operator Manual
Safety standards in syngo MR Introduction
Trusted Hosts B.1 Trusted hosts is a principle for a secure exchange of data
between systems in a network. The trusted host functionality
can be switched on in the Local Service Software. Switching
on has the following consequences: B.1
❏ Basically, all trusted systems must have knowledge about
each other.
❏ At your local workstation, all systems you “trust“ must be set
up as such.
❏ Received data is only accepted from trusted systems.
❏ Data will only be sent to trusted systems.
❏ Queries on data are only allowed from other trusted systems.
Your trusted zone must contain only network nodes with the
security system installed so that you can receive and send data
without worrying about data security. B.1
0.0
syngo MR 2006T B.1–11
Introduction Safety standards in syngo MR
0.0
B.1–12 Operator Manual
CHAPTER Information for
B.2 Administrators B.2
Administrator’s tasks B.2 Once the syngo MR security system has been installed,
Administrators are responsible for establishing and maintaining
competent user management, and for ensuring that the system
remains secure. This includes the following main tasks: B.2
❏ Creation and maintenance of user and group accounts and
role definitions
❏ Definition of data access rights (permissions)
❏ Assignment of functional privileges
❏ Handling of the audit trail
❏ Regularly backing up the audit trail
NOTE
User management has to be set up on every computer,
except for satellite consoles, which take the security
settings from their main console. B.2
0.0
syngo MR 2006T B.2–1
Information for Administrators Safety standards in syngo MR
Configuration of the security
system B.2
Principles of the syngo MR Patient data is sensitive information that has to be protected
User Management B.2 from unauthorized access, modification, transfer or deletion.
B.2
User Authentication B.2 A user account has to be created for every person who will be
working with syngo MR. To log on to the system, the user
enters his/her user account and password.
B.2
User Authorization B.2 The syngo MR user management and security system pro-
vides a highly configurable access control and ensures that
users obtain access only to application functions and patient
data they are authorized to work with. B.2
❏ The right to execute functions is granted via privileges.
❏ The right to create, read, update, delete or protect data is
granted via permissions.
Permissions can be set on at the patient or the study level.
Series and instances inherit their permissions from the study
they belong to.
0.0
B.2–2 Operator Manual
Safety standards in syngo MR Information for Administrators
Example: Doctor Stern wants to send a study of the patient Mr.
Smith to the archive. To do so, he needs the permission to
access the study of Mr. Smith and he needs the privilege to
send data to the archive. B.2
B.2
Grouping of Users: Roles Setting up the access rights for each user individually would
and Groups B.2 take a long time and would inevitably lead to inconsistent rights
for “similar” users. B.2
Scenario: Every doctor in the hospital shall be allowed to invoke
the 3-D functions, but nurses shall not be allowed to do so. Also,
patient data shall only be visible in the ward where the patient
is being treated. B.2
0.0
syngo MR 2006T B.2–3
Information for Administrators Safety standards in syngo MR
As the scenario shows, users can be grouped under certain
aspects: B.2
❏ According to his/her profession or duties, a user may have
assigned one or several roles, such as radiologist, nurse, or
administrator.
Roles can be assigned certain function execution rights
(= privileges), such as sending data, correcting data or set-
ting a work status. These rights extend to all users who
assume a certain role (or several roles). B.2
❏ According to the department(s) a user belongs to, a user
may also be assigned to one or several groups, such as the
radiology department or a ward.
For groups, you can configure data access rights (= permis-
sions), which are granted to all group members. B.2
❏ You can also set up permissions and privileges for each user
individually.
0.0
B.2–4 Operator Manual
Safety standards in syngo MR Information for Administrators
Typically, a user belongs to at least one group and has at least
one role. A user can also be assigned to more than one group
or role. See (→ Page B.2–44) for more information about access
control and how conflicting permissions and privileges are han-
dled if a user belongs to more than one group or role.
B.2
Special User Accounts B.2 The syngo MR security system knows the following special
user accounts: B.2
❏ Administrator
By default, the security system is installed with a general
“Administrator” user account assigned to the groups “Admin-
istrators” and “SecurityAdmins” and having assigned a role
called “SecurityAdmins”. B.2
Use this system account only to set up user management.
You then have to create a separate user account for every
administrator and assign these user accounts both to the
groups “Administrators” and “SecurityAdmins”. From now on,
log on to the system only under your personal administrator
user name. B.2
By default, the system is delivered with a setup that allows all
administrators full access to the system as long as an admin-
istrator does not remove these settings, the system is acces-
sible for him. B.2
0.0
syngo MR 2006T B.2–5
Information for Administrators Safety standards in syngo MR
❏ LocalServiceUser
This account usually is set up to have restricted access to
patient data, but full functional privileges for checking and
maintaining the system. B.2
To allow local service activities, an authorized user gets the
system to generate a temporary service password that auto-
matically expires after a configurable number of days. The
user then gives the password to the service technician, so
that the technician has access to the system under the
“LocalServiceUser” account. B.2
By default, this account is assigned both to the built-in group
and role called “syngoServiceUsers”. It also inherits rights
from the “Everyone” group and role (like all other accounts). B.2
In the default settings, the “syngoServiceUsers“ group and
role have full access to all data. We therefore recommend
that you as administrator disable the rights for the “syngoS-
erviceUsers“ group and role that are not essential for service
activities. B.2
0.0
B.2–6 Operator Manual
Safety standards in syngo MR Information for Administrators
❏ RemoteServiceUser
This account is used for remote service sessions. B.2
By default, the security system is installed with a “Remote-
ServiceUser” account assigned to the group “syngoService-
Users” and the role “syngoServiceUsers”. B.2
Depending on national and local regulations, remote access
to patient data is prohibited. Keep in mind that the “Remote-
ServiceUser“inherits the rights of the “Everyone“ group and
role and the “syngoServiceUsers“ group and role. It is there-
fore necessary that the data access rights for these groups
and roles do not allow the violation of remote data access.
B.2
❏ Emergency Access
To ensure emergency access to the system at all times, you
should create at least one special user account for common
emergency logon. B.2
Typically, the emergency user account(s) are assigned to an
“Emergency_Access” group and assigned the “Emergen-
cy_Access” role, which are already built in by the security
configuration. B.2
0.0
syngo MR 2006T B.2–7
Information for Administrators Safety standards in syngo MR
Depending on national and local regulations and the hospi-
tal’s security policies, the administrator has to define the cor-
rect permissions and privileges of the emergency access.
For example, emergency access should not allow modifica-
tion, deletion or transfer of data. If this is in accordance with
the security policy, you may think about creating an emer-
gency account without password. B.2
To make this emergency logon information available for the
users, we suggest to give this information to the desk officer
or deposited in a safe place. Also, the users have to be
informed about the correct usage of this account and the
consequences of abuse.
B.2
Internal Users B.2 Internal user accounts are essential for the system. They con-
sist of built-in users of the Windows operating system and
syngo MR internal users. B.2
The symbol “user with exclamation mark” indicates internal
users. B.2
NOTE
Although it is possible to change the password of these
internal accounts, we strongly recommend not to modify
any of the internal users. B.2
0.0
B.2–8 Operator Manual
You might also like
- VersaLink C405 Service Manual PDFDocument862 pagesVersaLink C405 Service Manual PDFAbrahan Castro75% (4)
- VersaLink C405 Service ManualDocument858 pagesVersaLink C405 Service ManualAlex Rodriguez BarronNo ratings yet
- DRS - Installation GuideDocument26 pagesDRS - Installation GuideEduNo ratings yet
- XEROX WorkCentre 5945 5955 Service Manual PDFDocument1,366 pagesXEROX WorkCentre 5945 5955 Service Manual PDFJJ JJ50% (6)
- IBM WebSphere Application Server Interview Questions You'll Most Likely Be AskedFrom EverandIBM WebSphere Application Server Interview Questions You'll Most Likely Be AskedNo ratings yet
- Cybersecurity Information Gathering Using Kali LinuxDocument93 pagesCybersecurity Information Gathering Using Kali LinuxWanderJunior100% (4)
- Service Programme: Volvo Construction EquipmentDocument4 pagesService Programme: Volvo Construction Equipmentp_jankoNo ratings yet
- Xerox Workcentre 5790 Family 5735 5740 5745 5755 5775 Service ManualDocument1,634 pagesXerox Workcentre 5790 Family 5735 5740 5745 5755 5775 Service ManualLuis Alberto70% (30)
- Lesson 8: Implementing Identity and Account Management ControlsDocument38 pagesLesson 8: Implementing Identity and Account Management ControlsPhan Sư ÝnhNo ratings yet
- Avaya Solution & Interoperability Test LabDocument65 pagesAvaya Solution & Interoperability Test LabRaghavendra BhatNo ratings yet
- CalibrationDocument28 pagesCalibrationPatriciaAraujo100% (1)
- Workforce AES71Document37 pagesWorkforce AES71Vicky NicNo ratings yet
- Eng GB SP A60h Stage IV V DDocument8 pagesEng GB SP A60h Stage IV V DYudha SetiawanNo ratings yet
- Cyberoam V 10.01 Build 0472Document27 pagesCyberoam V 10.01 Build 0472CharnwatNo ratings yet
- AltaLink8090 Family SMDocument1,859 pagesAltaLink8090 Family SManon_14517322783% (6)
- Asset Management - Caliberation ProcessingDocument23 pagesAsset Management - Caliberation ProcessingsundargowdaNo ratings yet
- Acuson x300 Syngo Service Software IntroductionDocument51 pagesAcuson x300 Syngo Service Software IntroductionCarlos MoraNo ratings yet
- BEMsl 0108 enDocument344 pagesBEMsl 0108 enCarlos Roberto SantosNo ratings yet
- 7694 Headspace Preventive Maintenance ChecklistDocument5 pages7694 Headspace Preventive Maintenance ChecklistRafael CovaNo ratings yet
- Anjali FinalDocument51 pagesAnjali Final7974patillsNo ratings yet
- OLA (18) 001 eduTEAMS CESNETDocument9 pagesOLA (18) 001 eduTEAMS CESNEThallarmemon100% (1)
- SPERREDocument6 pagesSPERRESalman KapoorNo ratings yet
- Element Management System User Manual V1 4 1Document159 pagesElement Management System User Manual V1 4 1htrejos15923No ratings yet
- Impact AACC62 PDFDocument78 pagesImpact AACC62 PDFShobhit TiwariNo ratings yet
- A Guide For Service TechniciansDocument70 pagesA Guide For Service Techniciansapi-3756430No ratings yet
- Vision WFMRTACTIDocument36 pagesVision WFMRTACTIRohan MaradiaNo ratings yet
- Ecma-354 (Csta Pase III)Document29 pagesEcma-354 (Csta Pase III)jean-phileNo ratings yet
- Simbolo de Cancelación Avaya Communication ManagerDocument4 pagesSimbolo de Cancelación Avaya Communication Managerclobo94No ratings yet
- Portable Filters mf90 SeriesDocument34 pagesPortable Filters mf90 SeriesMaya Surya MirantiNo ratings yet
- Wc5945f Service ManualDocument1,448 pagesWc5945f Service Manualmorrison1981No ratings yet
- eng-GB20019092F HDocument4 pageseng-GB20019092F HVinod SekharNo ratings yet
- CBLM-Solano 1Document8 pagesCBLM-Solano 1Tyron Rex SolanoNo ratings yet
- ControlsDocument34 pagesControlsmikeincognito100% (1)
- 5 Programming and Testing: Service RoutinesDocument3 pages5 Programming and Testing: Service RoutinesCebrail GüzelNo ratings yet
- SAGDocument63 pagesSAGdyodenNo ratings yet
- User's Manual Servo-S Ventilator System V7.0Document185 pagesUser's Manual Servo-S Ventilator System V7.0abdessamaNo ratings yet
- 11xx12xx SMDocument44 pages11xx12xx SMfanticelliNo ratings yet
- LEAN - TPM - Autonomous Maintenance Steps - Step 0: EducationDocument3 pagesLEAN - TPM - Autonomous Maintenance Steps - Step 0: EducationkeshunaNo ratings yet
- User S Manual Servo-S Ventilator System V7.0Document183 pagesUser S Manual Servo-S Ventilator System V7.0Karan JejurkarNo ratings yet
- EMC Centera 4.0 GlobalServices Release Notes Rev.a37Document94 pagesEMC Centera 4.0 GlobalServices Release Notes Rev.a37Eero AhoNo ratings yet
- Bizhub 350 250 Ineo 350 250 SM SecurityDocument21 pagesBizhub 350 250 Ineo 350 250 SM SecurityCristian BobaruNo ratings yet
- Unitronics Remote Operator AppQuickStartDocument6 pagesUnitronics Remote Operator AppQuickStartjuan miguelNo ratings yet
- WC6655 Service ManualDocument528 pagesWC6655 Service ManualMapsonNo ratings yet
- Technical Service Bulletin: ConditionDocument3 pagesTechnical Service Bulletin: ConditionJustinas RackauskasNo ratings yet
- Application Notes For Xima Chronicall 4.0 With Avaya IP Office 11.0 - Issue 1.0Document27 pagesApplication Notes For Xima Chronicall 4.0 With Avaya IP Office 11.0 - Issue 1.0guillermo granadosNo ratings yet
- Configuring Cybertech Pro With Avaya CM and AESDocument48 pagesConfiguring Cybertech Pro With Avaya CM and AESIsaac PinheiroNo ratings yet
- Alu Asm61 CS1KDocument47 pagesAlu Asm61 CS1KAdrian KumarNo ratings yet
- 1040M Control CNC Num Manual PDFDocument390 pages1040M Control CNC Num Manual PDFEdgar A Bernal100% (1)
- TelephoneDocument11 pagesTelephonevarun naikNo ratings yet
- Optical Line Terminal Equipment Element Management System User ManualDocument19 pagesOptical Line Terminal Equipment Element Management System User ManualCesar PallaresNo ratings yet
- Mobile TV ViewerDocument6 pagesMobile TV ViewerJekBrionesNo ratings yet
- Optical Line Terminal Equipment Element Management System User ManualDocument19 pagesOptical Line Terminal Equipment Element Management System User ManualCesar PallaresNo ratings yet
- Avaya ConfDocument42 pagesAvaya ConfGroWBusiness SMDNo ratings yet
- Exacq Hardening GuideDocument11 pagesExacq Hardening GuideunstrainNo ratings yet
- OUT Serial Uniqueness Errors v1.2Document58 pagesOUT Serial Uniqueness Errors v1.2StefanGarnetNo ratings yet
- Call Recovery TRDocument14 pagesCall Recovery TRStocktube lohNo ratings yet
- Sd10752 Revit External Services Arnost Lobel HandoutDocument37 pagesSd10752 Revit External Services Arnost Lobel HandoutAugusto SchiapatiNo ratings yet
- Event ID 7009 - Basic Service OperationsDocument1 pageEvent ID 7009 - Basic Service OperationsdhruvNo ratings yet
- Application Notes For The Grandstream Networks SIP Telephones With Avaya Communication Manager 4.0.1 and Avaya SIP Enablement Services 4.0Document30 pagesApplication Notes For The Grandstream Networks SIP Telephones With Avaya Communication Manager 4.0.1 and Avaya SIP Enablement Services 4.0playplaypspNo ratings yet
- SERVOi Operman 6691512 R00 V7dot0 120604 EN ALL LRDocument273 pagesSERVOi Operman 6691512 R00 V7dot0 120604 EN ALL LRKaran JejurkarNo ratings yet
- Oracle Enterprise Manager Grid Control 11g R1: Business Service ManagementFrom EverandOracle Enterprise Manager Grid Control 11g R1: Business Service ManagementNo ratings yet
- Middleware Management with Oracle Enterprise Manager Grid Control 10g R5From EverandMiddleware Management with Oracle Enterprise Manager Grid Control 10g R5No ratings yet
- Thayer Cyber Hacking in Southeast Asia BibliographyDocument2 pagesThayer Cyber Hacking in Southeast Asia BibliographyCarlyle Alan ThayerNo ratings yet
- Andrew Secure RPC ProtocolDocument10 pagesAndrew Secure RPC ProtocolanjanaNo ratings yet
- What Is DLP?: Data Loss PreventionDocument3 pagesWhat Is DLP?: Data Loss PreventionSancheetNo ratings yet
- Incidentrequest Closed Monthly AugDocument305 pagesIncidentrequest Closed Monthly Augأحمد أبوعرفهNo ratings yet
- Pen Testing BasicsDocument153 pagesPen Testing BasicsChristopher C. Cheng100% (2)
- Nozomi Networks CMC Data SheetDocument10 pagesNozomi Networks CMC Data SheetMunawar BhuttoNo ratings yet
- Advances in NW and DSSDocument218 pagesAdvances in NW and DSSGaurav GRNo ratings yet
- Paket 5000 Up 531 08.25.22 25 08 2022Document7 pagesPaket 5000 Up 531 08.25.22 25 08 2022pathul azizNo ratings yet
- DarazDocument24 pagesDarazshresthakrishna231No ratings yet
- Assignment - 8 SolutionDocument5 pagesAssignment - 8 SolutionGnaneswar reddyNo ratings yet
- Installing and Configuring SpanVADocument81 pagesInstalling and Configuring SpanVAAlfredo Martin100% (1)
- AWS+SAA C03+Exam+Guide+Mapped+to+VideosDocument29 pagesAWS+SAA C03+Exam+Guide+Mapped+to+VideosAmit KumarNo ratings yet
- Kentico CMS 7.0 Security GuideDocument67 pagesKentico CMS 7.0 Security GuidefojtkfNo ratings yet
- Ethical Hacking and Countermeasures Threats and Defense Mechanisms PDFDocument2 pagesEthical Hacking and Countermeasures Threats and Defense Mechanisms PDFJonathan0% (1)
- Ipsec Between SRX and VyosDocument6 pagesIpsec Between SRX and VyosSon Tran Hong Nam100% (1)
- Websmp230.sap-Ag - de Sap (bD1lbiZjPTAwMQ ) BC BSP SPN Ne PDFDocument1 pageWebsmp230.sap-Ag - de Sap (bD1lbiZjPTAwMQ ) BC BSP SPN Ne PDFCarlosNo ratings yet
- CCNA Security: Chapter Two Securing Network DevicesDocument70 pagesCCNA Security: Chapter Two Securing Network DevicesNicole Alejandra Pérez TapiaNo ratings yet
- Cloud Spec Final ProjectsDocument10 pagesCloud Spec Final ProjectsKavi GuruNo ratings yet
- Cybersecurity AOAO PDFDocument172 pagesCybersecurity AOAO PDFharassmeNo ratings yet
- EssayDocument13 pagesEssayT1911No ratings yet
- Digital Forensik PDFDocument29 pagesDigital Forensik PDFChyntia D. RahadiaNo ratings yet
- Rules of Netiquette (G2)Document12 pagesRules of Netiquette (G2)Abdul Jakeem CastanosNo ratings yet
- CV Pentester Nguyễn Phúc HảiDocument1 pageCV Pentester Nguyễn Phúc HảiHải Nguyễn PhúcNo ratings yet
- FN B.Tech IV - I R18Document9 pagesFN B.Tech IV - I R18VigneshNo ratings yet
- Microsoft - Building A Holistic Insider Risk Management ProgramDocument52 pagesMicrosoft - Building A Holistic Insider Risk Management ProgramTruong DuyNo ratings yet
- Nozomi Networks Oil Gas Producer Case StudyDocument4 pagesNozomi Networks Oil Gas Producer Case Studymario calderonNo ratings yet
- K012581 8.0 Manage Information Technology (IT) 0Document42 pagesK012581 8.0 Manage Information Technology (IT) 0tewehaNo ratings yet
- US DOT FY22-26 Strategic PlanDocument51 pagesUS DOT FY22-26 Strategic Planlilikwbs9334No ratings yet