Professional Documents
Culture Documents
SPS 6.0 OktaMulti-FactorAuthentication-Overview
SPS 6.0 OktaMulti-FactorAuthentication-Overview
Uploaded by
Zoumana DiomandeOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
SPS 6.0 OktaMulti-FactorAuthentication-Overview
SPS 6.0 OktaMulti-FactorAuthentication-Overview
Uploaded by
Zoumana DiomandeCopyright:
Available Formats
One Identity Safeguard for Privileged
Sessions 6.0
Okta Multi-Factor Authentication -
Overview
Copyright 2019 One Identity LLC.
ALL RIGHTS RESERVED.
This guide contains proprietary information protected by copyright. The software described in this guide
is furnished under a software license or nondisclosure agreement. This software may be used or copied
only in accordance with the terms of the applicable agreement. No part of this guide may be reproduced
or transmitted in any form or by any means, electronic or mechanical, including photocopying and
recording for any purpose other than the purchaser’s personal use without the written permission of
One Identity LLC .
The information in this document is provided in connection with One Identity products. No license,
express or implied, by estoppel or otherwise, to any intellectual property right is granted by this
document or in connection with the sale of One Identity LLC products. EXCEPT AS SET FORTH IN THE
TERMS AND CONDITIONS AS SPECIFIED IN THE LICENSE AGREEMENT FOR THIS PRODUCT,
ONE IDENTITY ASSUMES NO LIABILITY WHATSOEVER AND DISCLAIMS ANY EXPRESS, IMPLIED OR
STATUTORY WARRANTY RELATING TO ITS PRODUCTS INCLUDING, BUT NOT LIMITED TO, THE
IMPLIED WARRANTY OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE, OR NON-
INFRINGEMENT. IN NO EVENT SHALL ONE IDENTITY BE LIABLE FOR ANY DIRECT, INDIRECT,
CONSEQUENTIAL, PUNITIVE, SPECIAL OR INCIDENTAL DAMAGES (INCLUDING, WITHOUT
LIMITATION, DAMAGES FOR LOSS OF PROFITS, BUSINESS INTERRUPTION OR LOSS OF
INFORMATION) ARISING OUT OF THE USE OR INABILITY TO USE THIS DOCUMENT, EVEN IF
ONE IDENTITY HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. One Identity makes no
representations or warranties with respect to the accuracy or completeness of the contents of this
document and reserves the right to make changes to specifications and product descriptions at any
time without notice. One Identity does not make any commitment to update the information
contained in this document.
If you have any questions regarding your potential use of this material, contact:
One Identity LLC.
Attn: LEGAL Dept
4 Polaris Way
Aliso Viejo, CA 92656
Refer to our Web site (http://www.OneIdentity.com) for regional and international office information.
Patents
One Identity is proud of our advanced technology. Patents and pending patents may apply to this
product. For the most current information about applicable patents for this product, please visit our
website at http://www.OneIdentity.com/legal/patents.aspx.
Trademarks
One Identity and the One Identity logo are trademarks and registered trademarks of One Identity
LLC. in the U.S.A. and other countries. For a complete list of One Identity trademarks, please visit
our website at www.OneIdentity.com/legal. All other trademarks are the property of their
respective owners.
Legend
WARNING: A WARNING icon highlights a potential risk of bodily injury or property
damage, for which industry-standard safety precautions are advised. This icon is
often associated with electrical hazards related to hardware.
CAUTION: A CAUTION icon indicates potential damage to hardware or loss of data if
instructions are not followed.
SPS Okta Multi-Factor Authentication - Overview
Updated - December 2019
Version - 6.0
Contents
Introduction 4
How SPS and Okta MFA work together 7
Technical requirements 9
Supported factors and scenarios 11
About us 12
Contacting us 12
Technical support resources 12
SPS 6.0 Okta Multi-Factor Authentication - Overview
3
1
Introduction
This document describes how you can use the services of multi-factor authentication
provider Okta to authenticate the sessions of your privileged users with One Identity
Safeguard for Privileged Sessions (SPS).
One Identity Safeguard for Privileged Sessions:
One Identity Safeguard for Privileged Sessions (SPS) controls privileged access to remote
IT systems, records activities in searchable, movie-like audit trails, and prevents malicious
actions. SPS is a quickly deployable enterprise device, completely independent from clients
and servers — integrating seamlessly into existing networks. It captures the activity data
necessary for user profiling and enables full user session drill down for forensic
investigations.
SPS acts as a central authentication gateway, enforcing strong authentication before users
access sensitive IT assets. SPS can integrate with remote user directories to resolve the
group memberships of users who access nonpublic information. Credentials for accessing
information systems can be retrieved transparently from SPS's local credential store or a
third-party password management system. This method protects the confidentiality of
passwords as users can never access them. When used together with Okta (or another
multi-factor authentication provider), SPS directs all connections to the authentication tool,
and upon successful authentication, it permits the user to access the information system.
Okta Adaptive Multi-factor Authentication:
To support multi-factor authentication, SPS integrates with the identity management
service Okta. This enables you to leverage an additional out-of-band factor (typically
through the user’s registered smartphone) when authenticating the user. The additional
factor is processed in-line with the connection, so users do not have to switch to an
external application to process the additional factor. This results in an efficient user
experience that is readily accepted by the users.
The One Identity Safeguard for Privileged Sessions can interact with your Okta account and
can automatically request multi-factor authentication for your privileged users who are
accessing the servers and services protected by SPS.
SPS 6.0 Okta Multi-Factor Authentication - Overview
4
Introduction
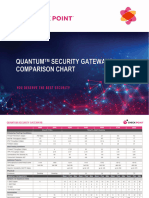
Figure 1: How SPS and Okta work together
Solution benefits
Matt Magleby, Sr. Computer Scientist at Adobe
One Identity Safeguard for Privileged Sessions helps us meet a portion of our
compliance and internal security requirements related to access management.
Using SPS together with Okta provides the following benefits.
l Easy-to-use multi-factor authentication to secure your privileged users who
access your business-critical servers. The enforcement of a second-factor
authentication and the availability of session recordings make the access of high-
risk users more secure.
l Out-of-band authentication to protect against privileged identity theft
l Logs and audits administrative network traffic
l Integrates with existing LDAP user directory
l Easy and fast deployment and implementation: a network-level solution that does
not require installing agents on clients or servers
l Can forward user logs into Splunk for long-term storage and analysis
l Supports SSH and RDP protocols to access both Linux and Windows servers,
without disrupting the daily workflow of your system administrators and other
privileged users
l Supports strong authentication methods, including SSH keys and certificates
SPS 6.0 Okta Multi-Factor Authentication - Overview
5
Introduction
Meet compliance requirements
ISO 27001, ISO 27018, SOC 2, and other regulations and industry standards include
authentication-related requirements, for example, multi-factor authentication (MFA) for
accessing production systems, and the logging of all administrative sessions. In addition to
other requirements, using SPS and Okta helps you comply with the following requirements:
l PCI DSS 8.3: Secure all individual non-console administrative access and all access
to the cardholder data environment (CDE) using multi-factor authentication.
l PART 500.12 Multi-Factor Authentication: Covered entities are required to apply
multi-factor authentication for:
l Each individual accessing the covered entity’s internal systems.
l Authorized access to database servers that allow access to nonpublic
information.
l Third parties accessing nonpublic information.
l NIST 800-53 IA-2, Identification and Authentication, network access to privileged
accounts: The information system implements multi-factor authentication for
network access to privileged accounts
To read about the experiences of Adobe Experience Cloud business unit using SPS and
Okta, download our case study.
SPS 6.0 Okta Multi-Factor Authentication - Overview
6
Introduction
2
How SPS and Okta MFA work
together
Figure 2: How SPS and Okta work together
1. A user attempts to log in to a protected server.
2. Gateway authentication on SPS
SPS receives the connection request and authenticates the user. SPS can
authenticate the user to a number of external user directories, for example, LDAP,
Microsoft Active Directory, or RADIUS. This authentication is the first factor.
SPS 6.0 Okta Multi-Factor Authentication - Overview
7
How SPS and Okta MFA work together
3. Outband authentication on Okta
If gateway authentication is successful, SPS connects the Okta server to check which
authentication factors are available for the user. Then SPS requests the second
authentication factor from the user.
l For OTP-like authentication factors, SPS requests the one-time password (OTP)
from the user, and sends it to the Okta server for verification.
l For the Okta push notification factor, SPS asks the Okta server to check if the
user successfully authenticated on the Okta server.
4. If multi-factor authentication is successful, the user can start working, while SPS
records the user's activities. (Optionally, SPS can retrieve credentials from a local or
external credential store or password vault, and perform authentication on the
server with credentials that are not known to the user.)
SPS 6.0 Okta Multi-Factor Authentication - Overview
8
How SPS and Okta MFA work together
3
Technical requirements
In order to successfully connect SPS with Okta, you need the following components.
In Okta:
l A valid Okta subscription that permits multi-factor authentication.
l An Okta API key. You will need it to configure the SPS plugin.
l Your users must be available in Okta.
l The users must activate their Okta accounts, and be able to perform the
authentication required for the factor (for example, install the Okta mobile app,
possess the required hardware token, and so on).
l A factor that the SPS plugin supports must be enabled in Okta. Note that this is a
global setting, you cannot selectively enable factors. For a list of factors that SPS
supports, see Supported factors and scenarios.
In SPS:
l A One Identity Safeguard for Privileged Sessions appliance (virtual or physical), at
least version 5 F1.
l A copy of the SPS Okta plugin. This plugin is an Authentication and Authorization (AA)
plugin customized to work with the Okta multi-factor authentication service.
l SPS must be able to access the Internet (at least the services on
https://www.okta.com). Since Okta is a cloud-based service provider, SPS must be
able to access its web services to authorize the user.
l Depending on the factor you use to authenticate your users, your users might need
Internet access as well, for example, to use the Okta Verify Push Notification factor.
Note that the Okta app generates one-time passwords (OTPs) offline.
l SPS supports AA plugins in the RDP, SSH, and Telnet protocols.
l In RDP, using an AA plugin together with Network Level Authentication in a
Connection Policy has the same limitations as using Network Level Authentication
without domain membership. For details, see "Network Level Authentication without
domain membership" in the Administration Guide.
SPS 6.0 Okta Multi-Factor Authentication - Overview
9
Technical requirements
l In RDP, using an AA plugin requires TLS-encrypted RDP connections. For details,
see "Enabling TLS-encryption for RDP connections" in the Administration Guide.
Availability and support of the plugin
The SPS Okta plugin is available as-is, free of charge to every SPS customer from the
Plugin Page. In case you need any customizations or additional features, contact our
Professional Services Team.
You can use the plugin on SPS 5 F3 and later. If you need to use the plugin on SPS 5 LTS,
contact our Professional Services Team.
SPS 6.0 Okta Multi-Factor Authentication - Overview
10
Technical requirements
4
Supported factors and scenarios
The SPS Okta plugin can provide multi-factor authentication in the Remote Desktop (RDP),
Secure Shell (SSH), and TELNET protocols. In RDP, using push notifications (when the user
authenticates using the Okta mobil app) is the most convenient method. You can use
another factor, but in this case the user must encode the OTP password into the username
used in the connection, before trying to connect to the server.
Okta supports several different authentication backends ("factor types" in Okta
terminology). When using one-time passwords (OTP-like factors), your users can specify
which factor they use (from the ones available for them in Okta).
You can also set a default factor in the Okta configuration, it defaults to Okta Verify (One-
Time Password).
The SPS Okta plugin supports the following authentication factors:
l Google Authenticator (One-Time Password)
l Okta Push Authentication
l Okta Verify (One-Time Password)
l RSA token
l Symantec token (One-Time Password)
l YubiKey token (One-Time Password)
You can also configure SPS to require multi-factor authentication only from selected users
or usergroups. You can also specify exceptions, that is, require multi-factor authentication
from everyone except the specified users. This allows you to have emergency or break-
glass users who can access your servers even if the Okta services are not available. For
details, see "[auth]" in the Okta Multi-Factor Authentication - Tutorial.
SPS 6.0 Okta Multi-Factor Authentication - Overview
11
Supported factors and scenarios
About us
About us
One Identity solutions eliminate the complexities and time-consuming processes often
required to govern identities, manage privileged accounts and control access. Our solutions
enhance business agility while addressing your IAM challenges with on-premises, cloud and
hybrid environments.
Contacting us
For sales and other inquiries, such as licensing, support, and renewals, visit
https://www.oneidentity.com/company/contact-us.aspx.
Technical support resources
Technical support is available to One Identity customers with a valid maintenance contract
and customers who have trial versions. You can access the Support Portal at
https://support.oneidentity.com/.
The Support Portal provides self-help tools you can use to solve problems quickly and
independently, 24 hours a day, 365 days a year. The Support Portal enables you to:
l Submit and manage a Service Request
l View Knowledge Base articles
l Sign up for product notifications
l Download software and technical documentation
l View how-to videos at www.YouTube.com/OneIdentity
l Engage in community discussions
l Chat with support engineers online
l View services to assist you with your product
SPS 6.0 Okta Multi-Factor Authentication - Overview
12
About us
You might also like
- Okta Certified Professional DemoDocument5 pagesOkta Certified Professional DemoZoumana DiomandeNo ratings yet
- The New Accounts Payable ToolkitDocument269 pagesThe New Accounts Payable ToolkitThùy Vân Nguyễn100% (1)
- VeriSign OTP Credential Provisioning Protocol For Trusted Devices Technical Specification v6Document29 pagesVeriSign OTP Credential Provisioning Protocol For Trusted Devices Technical Specification v6maheshsharmapNo ratings yet
- Cisco ISE Design and ArchitectureDocument69 pagesCisco ISE Design and ArchitectureMike Van Kleef100% (1)
- PI SQL Data Access Server (OLE DB) 2018 Administrator GuideDocument40 pagesPI SQL Data Access Server (OLE DB) 2018 Administrator Guidezongcheng jinNo ratings yet
- Administrator Study GuideDocument20 pagesAdministrator Study GuidesachinkoenigNo ratings yet
- Req LogicDocument172 pagesReq Logicadriana_e_sosaNo ratings yet
- Oaam Device Identification - 10.1.4.5Document32 pagesOaam Device Identification - 10.1.4.5davidmm81No ratings yet
- Cisco Identity Services EngineDocument8 pagesCisco Identity Services EngineZakarieya AbdurahmanNo ratings yet
- IAM - OKTA Without User Onboarding ProcessDocument11 pagesIAM - OKTA Without User Onboarding ProcessNapster KingNo ratings yet
- IAM - OKTA Without User Onboarding ProcessDocument11 pagesIAM - OKTA Without User Onboarding ProcessNapster KingNo ratings yet
- Cisco Identity Services Engine: How To BuyDocument8 pagesCisco Identity Services Engine: How To BuyUmAiR ANo ratings yet
- Securing Web Apis With Oauth 2.0: ArticleDocument13 pagesSecuring Web Apis With Oauth 2.0: Articlephan trungNo ratings yet
- OpenAM PDFDocument5 pagesOpenAM PDFNilabja SahaNo ratings yet
- Dot1x Dep Guide - CiscoDocument37 pagesDot1x Dep Guide - CiscoJh0n Fredy HNo ratings yet
- Oracle Advanced Security New Features Oracle8i Release 8.1.6Document8 pagesOracle Advanced Security New Features Oracle8i Release 8.1.6anilp20055148No ratings yet
- PKI Deployment - Business Issues: An Oasis White PaperDocument15 pagesPKI Deployment - Business Issues: An Oasis White Papersaryus2012No ratings yet
- Addendum oAuthExtensibilityDocument8 pagesAddendum oAuthExtensibilityDanny DawsonNo ratings yet
- SAP Leonardo IoT Bridge - Security - GuideDocument12 pagesSAP Leonardo IoT Bridge - Security - GuidePau TorregrosaNo ratings yet
- Oracle Software Licensing Basics Sep20Document35 pagesOracle Software Licensing Basics Sep20Sandeep ChatterjeeNo ratings yet
- Sec User Services 15 1 BookDocument1,291 pagesSec User Services 15 1 BookEnis ByciNo ratings yet
- 3-30552 SharePointSecurityBestPractices FINALDocument4 pages3-30552 SharePointSecurityBestPractices FINALljrojas2011No ratings yet
- Cyber Ark Questions and AnswersDocument93 pagesCyber Ark Questions and AnswersYayathi AmpoluNo ratings yet
- PIWorld 2019 Beginning Administration and Management of The PI System - FinalDocument80 pagesPIWorld 2019 Beginning Administration and Management of The PI System - FinalRommel RiosNo ratings yet
- Implementing Access Control, Authentication, and Account ManagementDocument7 pagesImplementing Access Control, Authentication, and Account Managementoutplayer65No ratings yet
- DigiCert SSLTools API Reference v1.0Document22 pagesDigiCert SSLTools API Reference v1.0Prüfer SPANo ratings yet
- Net Banking Mini ProjectDocument65 pagesNet Banking Mini ProjectTrupti SuryawanshiNo ratings yet
- AuthenticationServices 4.0 SiebelSecurityAdapter PDFDocument40 pagesAuthenticationServices 4.0 SiebelSecurityAdapter PDFSparkle HemaNo ratings yet
- Srs 1Document13 pagesSrs 1Suraj PandeyNo ratings yet
- Ibm Filenet P8 Platform and Architecture: Reprinted For Supriya Kapoor, Tata Consultancy SvcsDocument30 pagesIbm Filenet P8 Platform and Architecture: Reprinted For Supriya Kapoor, Tata Consultancy SvcsVinod KapoorNo ratings yet
- Access Management Vision DocumentDocument16 pagesAccess Management Vision DocumentvicadeNo ratings yet
- SWL 1.2 2848bhbhDocument5 pagesSWL 1.2 2848bhbh19bcs2856No ratings yet
- Why Choose Otka Rather Than Microsoft Azure ADDocument7 pagesWhy Choose Otka Rather Than Microsoft Azure ADPeterNo ratings yet
- The Public Key InfrastructureDocument6 pagesThe Public Key InfrastructurekajulovNo ratings yet
- 2016-Mw-Subhajit Das Chaudhuri-Deep Dive Into SSL Implementation Scenarios For Oracle Apps-Praesentation PDFDocument52 pages2016-Mw-Subhajit Das Chaudhuri-Deep Dive Into SSL Implementation Scenarios For Oracle Apps-Praesentation PDFmaleemNo ratings yet
- IT ProDocument4 pagesIT ProAlthaf BashaNo ratings yet
- AAA Administration For Clouds Unit 4Document35 pagesAAA Administration For Clouds Unit 4sambangialekhya846No ratings yet
- Shaik Khaja Muneer Resume LatestDocument6 pagesShaik Khaja Muneer Resume LatestShaik MunnaNo ratings yet
- Identity Service Engine User GuideDocument1,200 pagesIdentity Service Engine User GuidearuninbaNo ratings yet
- Configuring PI System SecurityDocument30 pagesConfiguring PI System SecurityDimo DimoNo ratings yet
- Highly Confidential Security SystemDocument6 pagesHighly Confidential Security SystemVenkat ChowdaryNo ratings yet
- Opensso Ds 129530Document2 pagesOpensso Ds 129530necrombiNo ratings yet
- Integration Guide: Safenet Authentication ServiceDocument26 pagesIntegration Guide: Safenet Authentication ServicepyxpdrlviqddcbyijuNo ratings yet
- Microsoft SLP Services Getting Started User GuideDocument15 pagesMicrosoft SLP Services Getting Started User GuideLoi DoanNo ratings yet
- 5 Operational RequirementsDocument2 pages5 Operational RequirementsHakimuddin AttarwalaNo ratings yet
- IPM Admin GuideDocument638 pagesIPM Admin GuideHanna CruzNo ratings yet
- "Vehicle Information System": Gitarattan International Business SchoolDocument6 pages"Vehicle Information System": Gitarattan International Business SchoolRajni_Pathania_1874No ratings yet
- Eap-Fast Admin GuideDocument64 pagesEap-Fast Admin GuideMatías ArgüelloNo ratings yet
- How To Enable Authorization Relevance On A Navigation AttributeDocument12 pagesHow To Enable Authorization Relevance On A Navigation AttributeKalyanaraman ParthasarathyNo ratings yet
- Pci DSSDocument5 pagesPci DSSAtanasije Zlatousti100% (1)
- Oracle Banking Microservices Architecture Installer GuideDocument45 pagesOracle Banking Microservices Architecture Installer Guidebr0k3n.s0ul44No ratings yet
- 12 IdentityAI Activation GuideDocument8 pages12 IdentityAI Activation GuideSrinivas SeenuNo ratings yet
- Complete IT and InfoSec RFP For HRMSDocument22 pagesComplete IT and InfoSec RFP For HRMSshwetank sharmaNo ratings yet
- Integration of GCP With OKTADocument22 pagesIntegration of GCP With OKTANapster KingNo ratings yet
- Ebilling SDKDocument414 pagesEbilling SDKWilfred MbithiNo ratings yet
- Ignition 21 CFR Part 11 Compliance - Panacea TechnologiesDocument7 pagesIgnition 21 CFR Part 11 Compliance - Panacea TechnologiesglmazNo ratings yet
- Cisco Secure Desktop Configuration Guide: For Cisco ASA 5500 Series AdministratorsDocument82 pagesCisco Secure Desktop Configuration Guide: For Cisco ASA 5500 Series Administratorsvolero tristeNo ratings yet
- Enhancing Password Manager Chrome Extension Through Multi Authentication and Device LogsDocument7 pagesEnhancing Password Manager Chrome Extension Through Multi Authentication and Device LogsEditor IJTSRDNo ratings yet
- Oracle Banking Digital Experience Installer ManualDocument68 pagesOracle Banking Digital Experience Installer ManualAlem MezgeboNo ratings yet
- Oracle Banking Microservices Platform Foundation Installation GuideDocument56 pagesOracle Banking Microservices Platform Foundation Installation Guidebr0k3n.s0ul44No ratings yet
- Smarttools Project Preparation PrerequisitesDocument15 pagesSmarttools Project Preparation PrerequisitesnithyaNo ratings yet
- SSL VPN : Understanding, evaluating and planning secure, web-based remote accessFrom EverandSSL VPN : Understanding, evaluating and planning secure, web-based remote accessNo ratings yet
- Qualys Container Security User GuideDocument54 pagesQualys Container Security User GuideZoumana DiomandeNo ratings yet
- Qualys Cloud Platform WhitepaperDocument40 pagesQualys Cloud Platform WhitepaperZoumana DiomandeNo ratings yet
- AI Revolutionizing Public Relations_ A Path to Enhanced CommDocument18 pagesAI Revolutionizing Public Relations_ A Path to Enhanced CommZoumana DiomandeNo ratings yet
- Danilobanjac - Bash Scripting Language Cheat SheetDocument5 pagesDanilobanjac - Bash Scripting Language Cheat SheetZoumana DiomandeNo ratings yet
- cyberark-customer-success-overview-ebookDocument9 pagescyberark-customer-success-overview-ebookZoumana DiomandeNo ratings yet
- SEC1729CDocument25 pagesSEC1729CZoumana DiomandeNo ratings yet
- Cyberark Shortcuts For Common CommandsDocument3 pagesCyberark Shortcuts For Common CommandsZoumana DiomandeNo ratings yet
- 8.4 IdentityIQ Advanced AnalyticsDocument44 pages8.4 IdentityIQ Advanced AnalyticsZoumana DiomandeNo ratings yet
- IT1227Document21 pagesIT1227Zoumana DiomandeNo ratings yet
- Co Branded - Splunk ITSI Product BriefDocument3 pagesCo Branded - Splunk ITSI Product BriefZoumana DiomandeNo ratings yet
- Fortinet FortiGate - EAL4 - ST - V1.5.pdf (320893) - TMPDocument82 pagesFortinet FortiGate - EAL4 - ST - V1.5.pdf (320893) - TMPZoumana DiomandeNo ratings yet
- Check Point Appliance Comparison ChartDocument5 pagesCheck Point Appliance Comparison ChartZoumana DiomandeNo ratings yet
- Security Gateway DatasheetDocument5 pagesSecurity Gateway DatasheetZoumana DiomandeNo ratings yet
- Logger QuickStart HyperV 5.3SP1Document42 pagesLogger QuickStart HyperV 5.3SP1Zoumana DiomandeNo ratings yet
- Small Business Appliance BrochureDocument7 pagesSmall Business Appliance BrochureZoumana DiomandeNo ratings yet
- LC ACADEMIC Tips For CandidatesDocument11 pagesLC ACADEMIC Tips For CandidatesZoumana DiomandeNo ratings yet
- Okta Mfa-DatasheetDocument1 pageOkta Mfa-DatasheetZoumana DiomandeNo ratings yet
- WPR - How Okta Integrates Apps ArchitectureDocument12 pagesWPR - How Okta Integrates Apps ArchitectureZoumana DiomandeNo ratings yet
- Logger RelNotes 5.3SP1Document32 pagesLogger RelNotes 5.3SP1Zoumana DiomandeNo ratings yet
- Datasheet ArcSight ConnectorsDocument4 pagesDatasheet ArcSight ConnectorsZoumana DiomandeNo ratings yet
- The Splunk It Service Intelligence Itsi Top 20 KpisDocument48 pagesThe Splunk It Service Intelligence Itsi Top 20 KpisZoumana DiomandeNo ratings yet
- Splunk It Service Intelligence Keep Your Boss and Their Bosses Informed and Happy and Still Have Time To Sleep at NightDocument34 pagesSplunk It Service Intelligence Keep Your Boss and Their Bosses Informed and Happy and Still Have Time To Sleep at NightZoumana DiomandeNo ratings yet
- Forward-Looking StatementsDocument20 pagesForward-Looking StatementsZoumana DiomandeNo ratings yet
- Ansible SecurityDocument133 pagesAnsible SecurityZoumana DiomandeNo ratings yet
- IT2184 TunningDocument36 pagesIT2184 TunningZoumana DiomandeNo ratings yet
- Ansible Rhel 90Document72 pagesAnsible Rhel 90Zoumana DiomandeNo ratings yet
- Forward-Looking StatementsDocument14 pagesForward-Looking StatementsZoumana DiomandeNo ratings yet
- Ansible Smart MGMTDocument46 pagesAnsible Smart MGMTZoumana DiomandeNo ratings yet
- Ansible f5Document89 pagesAnsible f5Zoumana DiomandeNo ratings yet
- Rahul Sisodiya Resume1Document2 pagesRahul Sisodiya Resume1Rahul Sisodiya100% (1)
- Guide To Using Seller PicksDocument18 pagesGuide To Using Seller PicksAftab AhmedNo ratings yet
- Proposal 111Document6 pagesProposal 111ConillyMwaleNo ratings yet
- DASM Study Guide-2Document7 pagesDASM Study Guide-2MILTON CÉSAR AGUILAR DE AZAMBUJANo ratings yet
- Ho So San Pham BRAVO 8 - Catalog - E PDFDocument52 pagesHo So San Pham BRAVO 8 - Catalog - E PDFTrung NguyenNo ratings yet
- Civil Rico Prac Manual FORMSDocument154 pagesCivil Rico Prac Manual FORMSD.W. SmithNo ratings yet
- How To Build An Activity Based Sales Strategy LevelElevenDocument14 pagesHow To Build An Activity Based Sales Strategy LevelElevenRogerNo ratings yet
- Laptop Price PredictionDocument25 pagesLaptop Price Predictionvtu19362No ratings yet
- Miscellaneous Receipt PDFDocument1 pageMiscellaneous Receipt PDFMukesh KewlaniNo ratings yet
- Product Management For BAsDocument11 pagesProduct Management For BAsKevin BrennanNo ratings yet
- Vulnerability Management Policy Template For Control 7Document17 pagesVulnerability Management Policy Template For Control 7Ivan Ninan100% (1)
- SYBMS Sample Questions-MinDocument63 pagesSYBMS Sample Questions-MinParmanand GiriNo ratings yet
- BH Session Task 1Document4 pagesBH Session Task 1RajNo ratings yet
- Banks Core Technology Conundrum Reaches An Inflection PointDocument9 pagesBanks Core Technology Conundrum Reaches An Inflection Pointjuliae.delacourNo ratings yet
- FxExtractor OperationDocument6 pagesFxExtractor OperationMirevStefanNo ratings yet
- SAP Data Replication Customer MasterDocument21 pagesSAP Data Replication Customer MasterSankara GanapathyNo ratings yet
- Project Report On UPIDocument52 pagesProject Report On UPI538Mansi Chaurasia67% (3)
- Rder Anagement Ystems: Chris Cook Electronic Trading Sales 214-978-4736Document26 pagesRder Anagement Ystems: Chris Cook Electronic Trading Sales 214-978-4736Pinaki MishraNo ratings yet
- APTAVIS - Presentation For Hotels (New May 2022)Document18 pagesAPTAVIS - Presentation For Hotels (New May 2022)Rianto BarnasNo ratings yet
- AZ 305T00A ENU TrainerCaseStudiesDocument37 pagesAZ 305T00A ENU TrainerCaseStudiesjicih27380No ratings yet
- Bam 006 Sas 7Document9 pagesBam 006 Sas 7Shanice Rose Mercado LandayanNo ratings yet
- John Snow: Project Manager / Scrum MasterDocument3 pagesJohn Snow: Project Manager / Scrum MasterMariia HoncharovaNo ratings yet
- Kinder GardenDocument29 pagesKinder GardenMayur DhawleNo ratings yet
- Harita Corporate ProfileDocument11 pagesHarita Corporate ProfileSwaminathan PrabaharanNo ratings yet
- Advances in Apparel Production Technology PDFDocument15 pagesAdvances in Apparel Production Technology PDFzinabu girmaNo ratings yet
- 06 Handout 1 (Pre-Finals)Document4 pages06 Handout 1 (Pre-Finals)Emmanuel DelarosaNo ratings yet
- Automated Threat Detection and Response (ATDR) : Customer PresentationDocument16 pagesAutomated Threat Detection and Response (ATDR) : Customer PresentationAyyansh&Amyrah MasurkarNo ratings yet
- Adaptive ManagementDocument32 pagesAdaptive ManagementEbrenonNo ratings yet