Professional Documents
Culture Documents
Continuous Container Security
Continuous Container Security
Uploaded by
Adrian des RotoursCopyright:
Available Formats
You might also like
- The Devsecops Security Checklist: 2Nd EditionDocument28 pagesThe Devsecops Security Checklist: 2Nd Editionjhon due0% (1)
- DevSecOps PresentationDocument20 pagesDevSecOps Presentationcheenu100% (4)
- Method Statement & ITP For Construction of Tunnel Retaining Wall at S10 Part 3-5 and 5-5 PDFDocument10 pagesMethod Statement & ITP For Construction of Tunnel Retaining Wall at S10 Part 3-5 and 5-5 PDFrayNo ratings yet
- Complete Guide To Enterprise Container Security: Released: February 20, 2018Document24 pagesComplete Guide To Enterprise Container Security: Released: February 20, 2018VictorNo ratings yet
- Docker Container Security in Cloud Computing: Kelly Brady, Seung Moon, Tuan Nguyen, Joel CoffmanDocument6 pagesDocker Container Security in Cloud Computing: Kelly Brady, Seung Moon, Tuan Nguyen, Joel CoffmanShubham SarohaNo ratings yet
- Devsecops Security ChecklistDocument18 pagesDevsecops Security ChecklistDigambar S TatkareNo ratings yet
- Palo Alto Networks Ebook Prisma Container Security101 PDFDocument8 pagesPalo Alto Networks Ebook Prisma Container Security101 PDFRavi KiranNo ratings yet
- Aqua Security Ebook Container Security-10 Things DevOps Need To DoDocument12 pagesAqua Security Ebook Container Security-10 Things DevOps Need To DoJulio Cesar Juan LuisNo ratings yet
- Container Security For DummiessssDocument6 pagesContainer Security For DummiessssRAMANAN MAGESHNo ratings yet
- NeuVector SP800 190 Report - Final1Document12 pagesNeuVector SP800 190 Report - Final1toxiw75730No ratings yet
- Devops Security ChecklistDocument14 pagesDevops Security ChecklistNatalie Penso100% (2)
- Container Security Going Beyond Image ScanningDocument18 pagesContainer Security Going Beyond Image ScanningnicolepetrescuNo ratings yet
- OWASPDocument226 pagesOWASPNguyen Hong PhuNo ratings yet
- Container IzationDocument5 pagesContainer IzationabcdNo ratings yet
- Container Security Best Practices Cheat SheetDocument9 pagesContainer Security Best Practices Cheat SheetmcskumarNo ratings yet
- Ai Web Report 1 1Document25 pagesAi Web Report 1 1Suraj TheekshanaNo ratings yet
- Methods To Manage and Secure The Container LifecycleContainer+Lifecycle+Security+-+WPDocument15 pagesMethods To Manage and Secure The Container LifecycleContainer+Lifecycle+Security+-+WPuserNo ratings yet
- CyBOK v1.1.0-4Document200 pagesCyBOK v1.1.0-4Adrian NNo ratings yet
- Real-Time DevOps WorkFlow by DevOps ShackDocument6 pagesReal-Time DevOps WorkFlow by DevOps ShackRohit KulkarniNo ratings yet
- Deep Security DatasheetDocument5 pagesDeep Security DatasheetDecentsmart SmartNo ratings yet
- Bitdefender Practical Container Security PDFDocument8 pagesBitdefender Practical Container Security PDFDiego OrjuelaNo ratings yet
- Experiment 10 CCLDocument20 pagesExperiment 10 CCL41Remje SiddhantPNo ratings yet
- OWASP SCP Quick Reference Guide - en-USDocument17 pagesOWASP SCP Quick Reference Guide - en-USheloNo ratings yet
- Secure Web Based System Development: Oluleke Bamodu Benson OtafuDocument4 pagesSecure Web Based System Development: Oluleke Bamodu Benson OtafuNihaNo ratings yet
- Secdevops: Description and PrimerDocument37 pagesSecdevops: Description and PrimerPeter LamarNo ratings yet
- UNIT-4 Security in CloudsDocument41 pagesUNIT-4 Security in Cloudssaradaganerchukundham45No ratings yet
- Web Application Security and StandardsDocument12 pagesWeb Application Security and StandardsReshma WawhalNo ratings yet
- Ecommerce and Web Security (Cber 705) : Assignment # 1Document5 pagesEcommerce and Web Security (Cber 705) : Assignment # 1Mohit SangwanNo ratings yet
- DevSecops AllThingsOpen 2019Document37 pagesDevSecops AllThingsOpen 2019Peter LamarNo ratings yet
- Vivian ResumeDocument4 pagesVivian Resumeashh3417No ratings yet
- Kubernetes Security Ebook Tips Tricks Best Practices PDFDocument20 pagesKubernetes Security Ebook Tips Tricks Best Practices PDFSam SonyNo ratings yet
- Abhinav SinghDocument23 pagesAbhinav SinghGouri ShankerNo ratings yet
- CloudDefense - White PaperDocument42 pagesCloudDefense - White PaperBinuNo ratings yet
- Security Risk Assessment of Project Dependencies and Counter MeasureDocument10 pagesSecurity Risk Assessment of Project Dependencies and Counter MeasurevishalNo ratings yet
- Nodejs Security HandbookDocument28 pagesNodejs Security Handbookisshin22No ratings yet
- 1 Containerized AppDocument2 pages1 Containerized AppDebojyoti MukherjeeNo ratings yet
- اربعون 40يوماDocument14 pagesاربعون 40يوماmurtida33No ratings yet
- Module 6 - Application Deployment and SecurityDocument86 pagesModule 6 - Application Deployment and SecurityDaniilNo ratings yet
- Ultimate Kubernetes Security GuideDocument30 pagesUltimate Kubernetes Security Guidecap.rohit550No ratings yet
- Dev OpsDocument37 pagesDev OpsZlatko PažinNo ratings yet
- Mypdf 1Document2 pagesMypdf 1adrien.danzon.sNo ratings yet
- Docker Ecosystem Vulnerability AnalysisDocument19 pagesDocker Ecosystem Vulnerability Analysisraspberries1No ratings yet
- Establishing Application SecurityDocument6 pagesEstablishing Application SecurityKarl Alvin Reyes HipolitoNo ratings yet
- JetBrains CICD ProtectionDocument19 pagesJetBrains CICD ProtectionAlex EnacheNo ratings yet
- 8 Patterns of Secure Sgile Teams WhitepaperDocument3 pages8 Patterns of Secure Sgile Teams WhitepaperKevinNo ratings yet
- Dzone Refcard 275 k8s Security Essentials 2022Document6 pagesDzone Refcard 275 k8s Security Essentials 2022KP SNo ratings yet
- Top 10 CICD Security RisksDocument38 pagesTop 10 CICD Security RisksLmoreira100% (1)
- Mod Security IntroDocument30 pagesMod Security IntroPrem JNo ratings yet
- Devasc Module 6Document93 pagesDevasc Module 6Youssef FatihiNo ratings yet
- DEVASC Module 6Document93 pagesDEVASC Module 6JUAN MAURICIO QUEZADA JAMASMIENo ratings yet
- Secure Cloud Prisma 5Document18 pagesSecure Cloud Prisma 5JORGE TEMBE100% (1)
- Building A Continuously Integrating System With High SafetyDocument11 pagesBuilding A Continuously Integrating System With High SafetyAIRCC - IJNSANo ratings yet
- Supporting Secure Programming in Web Applications THR - 2014 - Journal of AdvancDocument14 pagesSupporting Secure Programming in Web Applications THR - 2014 - Journal of AdvancJohayrah DiangcaNo ratings yet
- F-Secure Security Cloud: Purpose, Function and BenefitsDocument7 pagesF-Secure Security Cloud: Purpose, Function and BenefitsNelson NoclafNo ratings yet
- CISSP Session 05Document74 pagesCISSP Session 05wfelicescNo ratings yet
- Cyber Sec. Int. Ques and Ans.Document15 pagesCyber Sec. Int. Ques and Ans.Harish UmasankarNo ratings yet
- Cloud ComputingDocument25 pagesCloud ComputingGani RKNo ratings yet
- Building Firewall Application To Enhance The Cyber Security: Research ProposalDocument21 pagesBuilding Firewall Application To Enhance The Cyber Security: Research ProposalruhanNo ratings yet
- Security for Containers and Kubernetes: Learn how to implement robust security measures in containerized environments (English Edition)From EverandSecurity for Containers and Kubernetes: Learn how to implement robust security measures in containerized environments (English Edition)No ratings yet
- DevOps and Containers Security: Security and Monitoring in Docker ContainersFrom EverandDevOps and Containers Security: Security and Monitoring in Docker ContainersNo ratings yet
- Running ContainersDocument1 pageRunning ContainersAdrian des RotoursNo ratings yet
- DevOps ContainersDocument3 pagesDevOps ContainersAdrian des RotoursNo ratings yet
- PMJ Dec2007Document81 pagesPMJ Dec2007Adrian des RotoursNo ratings yet
- AP ExecguidetopmDocument51 pagesAP ExecguidetopmAdrian des RotoursNo ratings yet
- Ansible - Webinar ScriptDocument4 pagesAnsible - Webinar ScriptAdrian des RotoursNo ratings yet
- Dec 02Document74 pagesDec 02Adrian des RotoursNo ratings yet
- Human Side of Project LeadershipDocument126 pagesHuman Side of Project LeadershipAdrian des RotoursNo ratings yet
- PM Journal 0412Document76 pagesPM Journal 0412Adrian des RotoursNo ratings yet
- FasesDocument1 pageFasesAdrian des RotoursNo ratings yet
- March PMJ 2009Document149 pagesMarch PMJ 2009Adrian des RotoursNo ratings yet
- Sept 04Document72 pagesSept 04Adrian des RotoursNo ratings yet
- Sept 04Document72 pagesSept 04Adrian des RotoursNo ratings yet
- Leading The Transformation "Applying Agile and Devops Principles at Scale"Document37 pagesLeading The Transformation "Applying Agile and Devops Principles at Scale"Adrian des RotoursNo ratings yet
- Sept 01Document64 pagesSept 01Adrian des RotoursNo ratings yet
- Sept 02Document74 pagesSept 02Adrian des RotoursNo ratings yet
- Automation: Modernizing The Mainframe For Devops: by Don MacvittieDocument16 pagesAutomation: Modernizing The Mainframe For Devops: by Don MacvittieAdrian des RotoursNo ratings yet
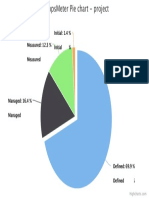
- Measured: 12.3 %: 12.3 % Initial Initial: 1.4 %: 1.4 %Document1 pageMeasured: 12.3 %: 12.3 % Initial Initial: 1.4 %: 1.4 %Adrian des RotoursNo ratings yet
- Lean Mindsets & Behaviors: Creating A High-Performance Climate For Sustained TransformationDocument128 pagesLean Mindsets & Behaviors: Creating A High-Performance Climate For Sustained TransformationAdrian des RotoursNo ratings yet
- Agile Devops Planning Transition TransformationDocument1 pageAgile Devops Planning Transition TransformationAdrian des RotoursNo ratings yet
- 6 Tips For A Successful Continuous Testing EnvironmentDocument16 pages6 Tips For A Successful Continuous Testing EnvironmentAdrian des RotoursNo ratings yet
- Cam - L7Document14 pagesCam - L7Ritik RajNo ratings yet
- MCC Software Development Kit (SDK) - Version 2.0 - License AgreementDocument1 pageMCC Software Development Kit (SDK) - Version 2.0 - License AgreementNguyễnTrọngHoàngViệtNo ratings yet
- ProServe-VBusiness-2019 v2Document9 pagesProServe-VBusiness-2019 v2Roel Antonio PascualNo ratings yet
- Stretchy The Word SnakeDocument6 pagesStretchy The Word SnakeShannon Martin100% (1)
- Service Manual: Room Air ConditionerDocument148 pagesService Manual: Room Air ConditionerQuasistatico PolitropicoNo ratings yet
- DORA - IIT KanpurDocument1 pageDORA - IIT KanpurVeera AadhikshaNo ratings yet
- IT6801 NAAC - SOA Lesson Plan - R2013Document4 pagesIT6801 NAAC - SOA Lesson Plan - R2013addssdfaNo ratings yet
- UFS-Podni RazvodDocument300 pagesUFS-Podni RazvodDEJAN SRECKOVICNo ratings yet
- Track Consignment 232Document2 pagesTrack Consignment 232Mega No01No ratings yet
- Akash Doklan BBA 6th Sem (Strategic Management)Document16 pagesAkash Doklan BBA 6th Sem (Strategic Management)Digvijay SinghNo ratings yet
- English Practice 16: Nga NguyễnDocument10 pagesEnglish Practice 16: Nga NguyễnTú BùiNo ratings yet
- (6-12) A Novel Approach For EEGDocument7 pages(6-12) A Novel Approach For EEGHema KumbharNo ratings yet
- Introduction To Statistics ReviewerDocument4 pagesIntroduction To Statistics ReviewerVianne TabiqueNo ratings yet
- Technical Catalogue - Sandwich Panels (Mineral Wool) (EN)Document108 pagesTechnical Catalogue - Sandwich Panels (Mineral Wool) (EN)rzsoltNo ratings yet
- Maf661 Test 1 - STGDocument6 pagesMaf661 Test 1 - STGAsy syuura YusofNo ratings yet
- 2020-02-01 ADMIN Network and SecurityDocument103 pages2020-02-01 ADMIN Network and SecurityTrọn Trầm XuânNo ratings yet
- Katipunan NG Kabataan ProfilingDocument14 pagesKatipunan NG Kabataan ProfilingVincent CatacutanNo ratings yet
- Clamped Base Support For Horizontal Pipes 2" - 48" NPS: Pipe Standard SupportsDocument2 pagesClamped Base Support For Horizontal Pipes 2" - 48" NPS: Pipe Standard SupportsMainuddin AliNo ratings yet
- Internet Marketing & Web Site Promotion 2001Document286 pagesInternet Marketing & Web Site Promotion 2001Livia MilieșNo ratings yet
- Quotation For OIS PriceDocument4 pagesQuotation For OIS PriceKasarachi AmadiNo ratings yet
- CSEC Information Technology - Practical Paper - January 2008Document6 pagesCSEC Information Technology - Practical Paper - January 2008Marie HenryNo ratings yet
- Lesson Plan For Grade 8 Mathematics 56Document7 pagesLesson Plan For Grade 8 Mathematics 56Charmine DuyagNo ratings yet
- Learning Competency With Code:: Activity Sheets in Mathematics 8Document4 pagesLearning Competency With Code:: Activity Sheets in Mathematics 8Yzell Keith Piores RosanesNo ratings yet
- CPCS204 09 Stacks Implementation ArraysLinkedListDocument32 pagesCPCS204 09 Stacks Implementation ArraysLinkedListHussein A. AlsameeNo ratings yet
- Library Management System (LMS) : Software Requirements SpecificationDocument22 pagesLibrary Management System (LMS) : Software Requirements SpecificationRohit DeshmukhNo ratings yet
- My Intel I9 10900 BillDocument4 pagesMy Intel I9 10900 BillMystica FlaireNo ratings yet
- قوانين عن التسعيرDocument8 pagesقوانين عن التسعيرمحمود الجالسNo ratings yet
- IC Tech Spec AttributesDocument22 pagesIC Tech Spec Attributeshome cecNo ratings yet
- Sy Ee 321 Emw MicroprojectDocument12 pagesSy Ee 321 Emw MicroprojectPari PatilNo ratings yet
Continuous Container Security
Continuous Container Security
Uploaded by
Adrian des RotoursOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Continuous Container Security
Continuous Container Security
Uploaded by
Adrian des RotoursCopyright:
Available Formats
HOW TO ACHIEVE
CONTINUOUS CONTAINER
SECURITY
Build Security Into Your
Container Process
Guide & Tool brought to you by NeuVector
TABLE OF CONTENTS
Build, Ship, and Run Containers Securely 3
Why Secure Containers? 4
Build Securely 5
Ship Securely 6
Run Securely 7
Run-time Preparation 7
Production Security 7
Continuous Security Quick Reference Tool 9
NeuVector Continuous Security 11
Additional Resources 12
Guide & Tool brought to you by NeuVector 2
BUILD, SHIP, AND RUN CONTAINERS
SECURELY
There’s been a lot of progress enabling companies to implement a container-
based continuous integration and continuous delivery (CI/CD) pipeline. But
when it’s time for deployment into production, how can enterprises make
sure continuous security is also built into the process?
Security should be built into the process from the beginning and cover all the
Build, Ship, and Run phases in order to ensure continuous security. Like
CI/CD, continuous security can be a fully automated process or a
combination of automated and manual processes. In today’s rapidly evolving
container technology landscape it’s more likely to require some manual steps
in addition to automation.
Here’s a convenient graphic that shows typical security requirements at each
phase.
You can download the infographic here in the Graphics section.
Guide & Tool brought to you by NeuVector 3
WHY SECURE CONTAINERS?
All applications can be vulnerable to attacks and it is critical to reduce this
risk. Important precautions can be taken during the Build and Ship stages to
reduce the risk of a successful attack. During the Run phase, the entire stack
from the host system and the Docker daemon to the application containers
running on them must be secured and monitored.
Insecure containers are vulnerable to the same threats that non-container
applications and systems face. With the increase in ‘east-west,’ or internal
traffic, generated from containers and microservices, there are many more
potential opportunities to compromise an application and the infrastructure.
Here are examples of threats to containers and the hosts they run on.
Container Threats
☠ Application level DDoS and cross-site scripting attacks on public facing
containers
☠ Compromised containers attempting to download additional malware, or
scan internal systems for weaknesses or sensitive data
☠ Container breakout, allowing unauthorized access across containers,
hosts, or data centers
☠ A container being forced to use up system resources in an attempt to slow
or crash other containers
☠ Live patching of applications which introduces malicious processes;
☠ Use of unsecure applications to flood the network and affect other
containers
There have been many recent examples of application and system attacks
which have seriously impacted businesses. These can apply to containerized
versions (ie, Docker container versions) of these applications as well. Here
are examples of attacks and exploits that could target running containers.
Container Attacks – Examples
☠ The Dirty Cow exploit on the linux kernel allowing root privilege escalation
Guide & Tool brought to you by NeuVector 4
on a host or container;
☠ MongoDB and ElasticSearch ransomware attacks against vulnerable
application containers
☠ Port scanning frequently seen on public cloud container instances, which
can be the first step in the kill chain
☠ OpenSSL heap corruption caused by malformed key header and a crash
caused by the presence of a specific extension
☠ Heap corruption and buffer overflow in Ruby and Python libraries allowing
execution of malicious code
☠ SQL injection attacks that put hackers in control of a database container in
order to steal data
☠ Vulnerabilities like the glibc stack-based buffer overflow, giving hackers
control through the use of man-in-the-middle attacks
☠ Any new zero-day attack on a container that represents an on-going threat
Securing a containerized environment and their application containers
requires, like any public cloud or private data-center, a layered security
strategy which builds in security at multiple layers of the stack.
It’s helpful to look at the security requirements for each phase of the Build-
Ship-Run container deployment process. Incorporating the appropriate
security controls and automating testing throughout the process will help
ensure compliance with internal and external requirements.
BUILD SECURELY
The first step to continuous security is to build secure applications. This
requires that developers become knowledgeable - through application
security training if necessary – about techniques for reducing the attack risk
in application code.
Before moving on to integration and testing of an application, code analysis
tools can also be run to report on potential vulnerabilities in the code.
Images should be hardened to reduce the attack surface by removing any
Guide & Tool brought to you by NeuVector 5
unnecessary libraries or packages.
Finally, vulnerability scanning should be performed on container images as a
final step before the Ship phase. Vulnerability scanning in registries should
occur frequently, as new vulnerabilities can be discovered which apply to
existing images.
Automating Continuous Security: Automatically run code analysis tools
and vulnerability scans on new builds. Automation can be applied in
development, test, and registries, where appropriate.
SHIP SECURELY
It is critical when getting ready to deploy images that appropriate controls
and verifications are put in place. Image signing, for example with Docker’s
Content Trust features, ensure that an image has not been tampered with,
and that the author or publisher has been verified.
It’s also critical to establish and enforce access controls for registries,
orchestration tools, and other deployment tools/systems. These include the
human identities for managing and building applications on the Docker
infrastructure.
The Docker Bench for Security can help test for content trust and access
control issues.
Automating Continuous Security: Images should be automatically signed
and tagged for production use. Access controls for registry and deployment
tools should integrate with directories such as Active Directory or LDAP
directories. Run Docker Bench for Security tests as a standard, automated
process.
Guide & Tool brought to you by NeuVector 6
RUN SECURELY
Running containers securely in production requires both run-time
preparation and production security steps.
RUN-TIME PREPARATION
The run-time environment must be secured before running application
containers live in production. This includes the host, kernel, Docker daemon,
and any network or system services such as load balancers and name
services.
Container management and orchestration tools can help to secure the
environment by setting appropriate names, labels, and networking policies.
They can also ensure that security containers always run on every host.
Make sure to audit security settings before and during run-time with tools
such as the Docker Bench for Security and the Kubernetes 1.6 CIS
Benchmark. This can help with compliance requirements for containers.
For an excellent, detailed technical guide for securing the OS, platforms, and
systems, see the NCC Group report linked in the Additional Resources
Appendix.
Automating Continuous Security: Use orchestration tools to ensure
security containers always run and appropriate network and container
settings are deployed. Make sure security tools are integrated with
orchestration tools to ensure automated policy updates as configurations
change and to enhance the visualization of the application and system
containers. Finally, automate security testing with industry standard CIS
benchmarks to ensure compliance with security requirements.
PRODUCTION SECURITY
Securing and monitoring containers at run-time, in production environments,
is the most critical requirement for continuous security. Experienced security
Guide & Tool brought to you by NeuVector 7
professionals know that somehow, some way, a hacker will find a
vulnerability and try to exploit it. There is usually a series of events, often
called a ‘kill chain’ where the hacker moves from host or container to
container to eventually find an exploit point. So there are often several
opportunities to detect suspicious behavior.
Detecting suspicious activity by inspecting network behavior is the most
convenient and effective monitoring point for run-time security. This is where
detection is best as attacks spread and real-time response is required.
Monitoring other run-time activities such as container and host processes
can also provide visibility into suspicious activity.
Encryption can be an important layer of a run-time security strategy.
Encryption can protect against stealing of secrets or sensitive data during
transmission. But it can’t protect against application attacks or other break
outs from a container or host. Security architects should evaluate the trade-
offs between performance, manageability, and security to determine which,
if any connections should be encrypted.
Even if network connections are encrypted between hosts or containers, all
communication should be monitored at the network layer to determine if
unauthorized connections are being attempted
Automating Continuous Security: Ensure security tools are automatically
deployed on each host and new container behavior is automatically learned
and locked down, or programmatically added to the security policy. Do real-
time monitoring and alerting from local consoles or from logs exported to
SIEM systems such as Splunk.
See the Continuous Security Quick Reference Tool on the next page for
a summary with detailed security requirements.
Guide & Tool brought to you by NeuVector 8
CONTINUOUS SECURITY QUICK
REFERENCE TOOL
Here is a quick reference tool that summarizes the security controls that should be
put in place to ensure continuous container security. Add additional requirements
in the ‘Other’ rows, add additional rows, and verify the Plan for each requirement.
Phase Requirement Description Plan
Build Code Analysis Analyze code for application
specific vulnerabilities
Hardening Remove unneeded libraries and
packages; restrict functions
Image Scanning Scan images for vulnerabilities at
build; regularly in registries
Other
Ship Image Signing, Ensure trust with signing and
e.g. Content Trust author / publisher verification
User Access Restrict and monitor access to
Controls, e.g. trusted registries and deployment
Registries tools
Other
Run: Host and Kernel Use SECCOMP, AppArmor, or
Prep- Security SELinux or equivalent host
ara- security settings
tion Secure Docker Ensure authorized access to
daemon Docker commands and settings
Access Controls Enable restricted access to system
and Docker daemon
Secrets Encrypt and protect secrets for
Management applications and API access
Auditing, e.g. Perform security audit using
Docker Bench Docker CIS benchmark
Orchestration Use orchestration features to
Security & restrict access, set network
Networking policies, and ensure security
containers are running
Other
Guide & Tool brought to you by NeuVector 9
Run: Network Inspect all container to container
Pro- Inspection & connections and build
duct- Visualization visualization for application stack
ion behavior
Encryption Use when necessary for
connection encryption
Layer 7-based Isolate and protect based on
Application application protocols and
Isolation container meta-data inspection,
not simply L3/4 network settings;
and block (if desired) without
affecting containers
Threat Detection Monitor applications for DDoS,
DNS attacks and other network
based application attacks
Host & Container Detect privilege escalations on
Privilege hosts and containers to predict
Escalation break outs and attacks
Detection
Container Quarantine suspicious containers,
Quarantine allowing for investigation
Run-Time Ensure all running containers are
Vulnerability scanned, and new ones get
Scanning immediately scanned
Process Inspect container processes to
Monitoring determine suspicious activity
Packet Capture & Capture packets and event logs to
Event Logging enable forensics
Other
You can download an Excel based version of the tool here, complete with
NeuVector security container capabilities mapped to the requirements.
Guide & Tool brought to you by NeuVector 10
NEUVECTOR CONTINUOUS SECURITY
There are four integration points for building in security into the container
deployment process.
1. Build - Integrate Code Security
2. Ship - Integrate Content Controls & Trust
3. Run/Preparation - Use Security Best Practices & Audit Settings
4. Run/Production - Integrate Security Tools & Automate Policy
NeuVector provides a leading solution which can be integrated to any
workflow designed to ensure continuous container security for CI/CD
processes and help with container compliance requirements.
NeuVector helps automate the continuous security process by:
• Automatically auditing security settings for hosts and containers
• Incorporating behavioral learning to create and update security policies
• Integrating with orchestration tools and networking plug-ins
• Providing a CLI & REST API for integration with other tools & systems.
Find out more at http://neuvector.com.
Guide & Tool brought to you by NeuVector 11
ADDITIONAL RESOURCES
The following additional resources are recommended to research deeper
technical advice for securing containers. Existing resources focus mainly on
securing the environment and integration process before run-time. There
aren’t many resources for securing and preventing container attacks during
run-time because this is a new area where companies like NeuVector are
pioneering run-time security solutions.
✓ Understanding and Hardening Linux Containers. By the NCC Group,
Author: Aaron Grattafiori
✓ Docker Security. By Docker Inc.
✓ Docker security. Using containers safely in production. BY ADRIAN
MOUAT
✓ Securing Your Deployment Pipeline With Docker. SLIDESHARE BY
MAXIMILIAN SCHÖFMANN – CONTAINER SOLUTIONS
✓ Container Security Guide. Red Hat Enterprise Linux Atomic Host.
✓ Introduction to Container Security. By Docker Inc.
Guide & Tool brought to you by NeuVector 12
You might also like
- The Devsecops Security Checklist: 2Nd EditionDocument28 pagesThe Devsecops Security Checklist: 2Nd Editionjhon due0% (1)
- DevSecOps PresentationDocument20 pagesDevSecOps Presentationcheenu100% (4)
- Method Statement & ITP For Construction of Tunnel Retaining Wall at S10 Part 3-5 and 5-5 PDFDocument10 pagesMethod Statement & ITP For Construction of Tunnel Retaining Wall at S10 Part 3-5 and 5-5 PDFrayNo ratings yet
- Complete Guide To Enterprise Container Security: Released: February 20, 2018Document24 pagesComplete Guide To Enterprise Container Security: Released: February 20, 2018VictorNo ratings yet
- Docker Container Security in Cloud Computing: Kelly Brady, Seung Moon, Tuan Nguyen, Joel CoffmanDocument6 pagesDocker Container Security in Cloud Computing: Kelly Brady, Seung Moon, Tuan Nguyen, Joel CoffmanShubham SarohaNo ratings yet
- Devsecops Security ChecklistDocument18 pagesDevsecops Security ChecklistDigambar S TatkareNo ratings yet
- Palo Alto Networks Ebook Prisma Container Security101 PDFDocument8 pagesPalo Alto Networks Ebook Prisma Container Security101 PDFRavi KiranNo ratings yet
- Aqua Security Ebook Container Security-10 Things DevOps Need To DoDocument12 pagesAqua Security Ebook Container Security-10 Things DevOps Need To DoJulio Cesar Juan LuisNo ratings yet
- Container Security For DummiessssDocument6 pagesContainer Security For DummiessssRAMANAN MAGESHNo ratings yet
- NeuVector SP800 190 Report - Final1Document12 pagesNeuVector SP800 190 Report - Final1toxiw75730No ratings yet
- Devops Security ChecklistDocument14 pagesDevops Security ChecklistNatalie Penso100% (2)
- Container Security Going Beyond Image ScanningDocument18 pagesContainer Security Going Beyond Image ScanningnicolepetrescuNo ratings yet
- OWASPDocument226 pagesOWASPNguyen Hong PhuNo ratings yet
- Container IzationDocument5 pagesContainer IzationabcdNo ratings yet
- Container Security Best Practices Cheat SheetDocument9 pagesContainer Security Best Practices Cheat SheetmcskumarNo ratings yet
- Ai Web Report 1 1Document25 pagesAi Web Report 1 1Suraj TheekshanaNo ratings yet
- Methods To Manage and Secure The Container LifecycleContainer+Lifecycle+Security+-+WPDocument15 pagesMethods To Manage and Secure The Container LifecycleContainer+Lifecycle+Security+-+WPuserNo ratings yet
- CyBOK v1.1.0-4Document200 pagesCyBOK v1.1.0-4Adrian NNo ratings yet
- Real-Time DevOps WorkFlow by DevOps ShackDocument6 pagesReal-Time DevOps WorkFlow by DevOps ShackRohit KulkarniNo ratings yet
- Deep Security DatasheetDocument5 pagesDeep Security DatasheetDecentsmart SmartNo ratings yet
- Bitdefender Practical Container Security PDFDocument8 pagesBitdefender Practical Container Security PDFDiego OrjuelaNo ratings yet
- Experiment 10 CCLDocument20 pagesExperiment 10 CCL41Remje SiddhantPNo ratings yet
- OWASP SCP Quick Reference Guide - en-USDocument17 pagesOWASP SCP Quick Reference Guide - en-USheloNo ratings yet
- Secure Web Based System Development: Oluleke Bamodu Benson OtafuDocument4 pagesSecure Web Based System Development: Oluleke Bamodu Benson OtafuNihaNo ratings yet
- Secdevops: Description and PrimerDocument37 pagesSecdevops: Description and PrimerPeter LamarNo ratings yet
- UNIT-4 Security in CloudsDocument41 pagesUNIT-4 Security in Cloudssaradaganerchukundham45No ratings yet
- Web Application Security and StandardsDocument12 pagesWeb Application Security and StandardsReshma WawhalNo ratings yet
- Ecommerce and Web Security (Cber 705) : Assignment # 1Document5 pagesEcommerce and Web Security (Cber 705) : Assignment # 1Mohit SangwanNo ratings yet
- DevSecops AllThingsOpen 2019Document37 pagesDevSecops AllThingsOpen 2019Peter LamarNo ratings yet
- Vivian ResumeDocument4 pagesVivian Resumeashh3417No ratings yet
- Kubernetes Security Ebook Tips Tricks Best Practices PDFDocument20 pagesKubernetes Security Ebook Tips Tricks Best Practices PDFSam SonyNo ratings yet
- Abhinav SinghDocument23 pagesAbhinav SinghGouri ShankerNo ratings yet
- CloudDefense - White PaperDocument42 pagesCloudDefense - White PaperBinuNo ratings yet
- Security Risk Assessment of Project Dependencies and Counter MeasureDocument10 pagesSecurity Risk Assessment of Project Dependencies and Counter MeasurevishalNo ratings yet
- Nodejs Security HandbookDocument28 pagesNodejs Security Handbookisshin22No ratings yet
- 1 Containerized AppDocument2 pages1 Containerized AppDebojyoti MukherjeeNo ratings yet
- اربعون 40يوماDocument14 pagesاربعون 40يوماmurtida33No ratings yet
- Module 6 - Application Deployment and SecurityDocument86 pagesModule 6 - Application Deployment and SecurityDaniilNo ratings yet
- Ultimate Kubernetes Security GuideDocument30 pagesUltimate Kubernetes Security Guidecap.rohit550No ratings yet
- Dev OpsDocument37 pagesDev OpsZlatko PažinNo ratings yet
- Mypdf 1Document2 pagesMypdf 1adrien.danzon.sNo ratings yet
- Docker Ecosystem Vulnerability AnalysisDocument19 pagesDocker Ecosystem Vulnerability Analysisraspberries1No ratings yet
- Establishing Application SecurityDocument6 pagesEstablishing Application SecurityKarl Alvin Reyes HipolitoNo ratings yet
- JetBrains CICD ProtectionDocument19 pagesJetBrains CICD ProtectionAlex EnacheNo ratings yet
- 8 Patterns of Secure Sgile Teams WhitepaperDocument3 pages8 Patterns of Secure Sgile Teams WhitepaperKevinNo ratings yet
- Dzone Refcard 275 k8s Security Essentials 2022Document6 pagesDzone Refcard 275 k8s Security Essentials 2022KP SNo ratings yet
- Top 10 CICD Security RisksDocument38 pagesTop 10 CICD Security RisksLmoreira100% (1)
- Mod Security IntroDocument30 pagesMod Security IntroPrem JNo ratings yet
- Devasc Module 6Document93 pagesDevasc Module 6Youssef FatihiNo ratings yet
- DEVASC Module 6Document93 pagesDEVASC Module 6JUAN MAURICIO QUEZADA JAMASMIENo ratings yet
- Secure Cloud Prisma 5Document18 pagesSecure Cloud Prisma 5JORGE TEMBE100% (1)
- Building A Continuously Integrating System With High SafetyDocument11 pagesBuilding A Continuously Integrating System With High SafetyAIRCC - IJNSANo ratings yet
- Supporting Secure Programming in Web Applications THR - 2014 - Journal of AdvancDocument14 pagesSupporting Secure Programming in Web Applications THR - 2014 - Journal of AdvancJohayrah DiangcaNo ratings yet
- F-Secure Security Cloud: Purpose, Function and BenefitsDocument7 pagesF-Secure Security Cloud: Purpose, Function and BenefitsNelson NoclafNo ratings yet
- CISSP Session 05Document74 pagesCISSP Session 05wfelicescNo ratings yet
- Cyber Sec. Int. Ques and Ans.Document15 pagesCyber Sec. Int. Ques and Ans.Harish UmasankarNo ratings yet
- Cloud ComputingDocument25 pagesCloud ComputingGani RKNo ratings yet
- Building Firewall Application To Enhance The Cyber Security: Research ProposalDocument21 pagesBuilding Firewall Application To Enhance The Cyber Security: Research ProposalruhanNo ratings yet
- Security for Containers and Kubernetes: Learn how to implement robust security measures in containerized environments (English Edition)From EverandSecurity for Containers and Kubernetes: Learn how to implement robust security measures in containerized environments (English Edition)No ratings yet
- DevOps and Containers Security: Security and Monitoring in Docker ContainersFrom EverandDevOps and Containers Security: Security and Monitoring in Docker ContainersNo ratings yet
- Running ContainersDocument1 pageRunning ContainersAdrian des RotoursNo ratings yet
- DevOps ContainersDocument3 pagesDevOps ContainersAdrian des RotoursNo ratings yet
- PMJ Dec2007Document81 pagesPMJ Dec2007Adrian des RotoursNo ratings yet
- AP ExecguidetopmDocument51 pagesAP ExecguidetopmAdrian des RotoursNo ratings yet
- Ansible - Webinar ScriptDocument4 pagesAnsible - Webinar ScriptAdrian des RotoursNo ratings yet
- Dec 02Document74 pagesDec 02Adrian des RotoursNo ratings yet
- Human Side of Project LeadershipDocument126 pagesHuman Side of Project LeadershipAdrian des RotoursNo ratings yet
- PM Journal 0412Document76 pagesPM Journal 0412Adrian des RotoursNo ratings yet
- FasesDocument1 pageFasesAdrian des RotoursNo ratings yet
- March PMJ 2009Document149 pagesMarch PMJ 2009Adrian des RotoursNo ratings yet
- Sept 04Document72 pagesSept 04Adrian des RotoursNo ratings yet
- Sept 04Document72 pagesSept 04Adrian des RotoursNo ratings yet
- Leading The Transformation "Applying Agile and Devops Principles at Scale"Document37 pagesLeading The Transformation "Applying Agile and Devops Principles at Scale"Adrian des RotoursNo ratings yet
- Sept 01Document64 pagesSept 01Adrian des RotoursNo ratings yet
- Sept 02Document74 pagesSept 02Adrian des RotoursNo ratings yet
- Automation: Modernizing The Mainframe For Devops: by Don MacvittieDocument16 pagesAutomation: Modernizing The Mainframe For Devops: by Don MacvittieAdrian des RotoursNo ratings yet
- Measured: 12.3 %: 12.3 % Initial Initial: 1.4 %: 1.4 %Document1 pageMeasured: 12.3 %: 12.3 % Initial Initial: 1.4 %: 1.4 %Adrian des RotoursNo ratings yet
- Lean Mindsets & Behaviors: Creating A High-Performance Climate For Sustained TransformationDocument128 pagesLean Mindsets & Behaviors: Creating A High-Performance Climate For Sustained TransformationAdrian des RotoursNo ratings yet
- Agile Devops Planning Transition TransformationDocument1 pageAgile Devops Planning Transition TransformationAdrian des RotoursNo ratings yet
- 6 Tips For A Successful Continuous Testing EnvironmentDocument16 pages6 Tips For A Successful Continuous Testing EnvironmentAdrian des RotoursNo ratings yet
- Cam - L7Document14 pagesCam - L7Ritik RajNo ratings yet
- MCC Software Development Kit (SDK) - Version 2.0 - License AgreementDocument1 pageMCC Software Development Kit (SDK) - Version 2.0 - License AgreementNguyễnTrọngHoàngViệtNo ratings yet
- ProServe-VBusiness-2019 v2Document9 pagesProServe-VBusiness-2019 v2Roel Antonio PascualNo ratings yet
- Stretchy The Word SnakeDocument6 pagesStretchy The Word SnakeShannon Martin100% (1)
- Service Manual: Room Air ConditionerDocument148 pagesService Manual: Room Air ConditionerQuasistatico PolitropicoNo ratings yet
- DORA - IIT KanpurDocument1 pageDORA - IIT KanpurVeera AadhikshaNo ratings yet
- IT6801 NAAC - SOA Lesson Plan - R2013Document4 pagesIT6801 NAAC - SOA Lesson Plan - R2013addssdfaNo ratings yet
- UFS-Podni RazvodDocument300 pagesUFS-Podni RazvodDEJAN SRECKOVICNo ratings yet
- Track Consignment 232Document2 pagesTrack Consignment 232Mega No01No ratings yet
- Akash Doklan BBA 6th Sem (Strategic Management)Document16 pagesAkash Doklan BBA 6th Sem (Strategic Management)Digvijay SinghNo ratings yet
- English Practice 16: Nga NguyễnDocument10 pagesEnglish Practice 16: Nga NguyễnTú BùiNo ratings yet
- (6-12) A Novel Approach For EEGDocument7 pages(6-12) A Novel Approach For EEGHema KumbharNo ratings yet
- Introduction To Statistics ReviewerDocument4 pagesIntroduction To Statistics ReviewerVianne TabiqueNo ratings yet
- Technical Catalogue - Sandwich Panels (Mineral Wool) (EN)Document108 pagesTechnical Catalogue - Sandwich Panels (Mineral Wool) (EN)rzsoltNo ratings yet
- Maf661 Test 1 - STGDocument6 pagesMaf661 Test 1 - STGAsy syuura YusofNo ratings yet
- 2020-02-01 ADMIN Network and SecurityDocument103 pages2020-02-01 ADMIN Network and SecurityTrọn Trầm XuânNo ratings yet
- Katipunan NG Kabataan ProfilingDocument14 pagesKatipunan NG Kabataan ProfilingVincent CatacutanNo ratings yet
- Clamped Base Support For Horizontal Pipes 2" - 48" NPS: Pipe Standard SupportsDocument2 pagesClamped Base Support For Horizontal Pipes 2" - 48" NPS: Pipe Standard SupportsMainuddin AliNo ratings yet
- Internet Marketing & Web Site Promotion 2001Document286 pagesInternet Marketing & Web Site Promotion 2001Livia MilieșNo ratings yet
- Quotation For OIS PriceDocument4 pagesQuotation For OIS PriceKasarachi AmadiNo ratings yet
- CSEC Information Technology - Practical Paper - January 2008Document6 pagesCSEC Information Technology - Practical Paper - January 2008Marie HenryNo ratings yet
- Lesson Plan For Grade 8 Mathematics 56Document7 pagesLesson Plan For Grade 8 Mathematics 56Charmine DuyagNo ratings yet
- Learning Competency With Code:: Activity Sheets in Mathematics 8Document4 pagesLearning Competency With Code:: Activity Sheets in Mathematics 8Yzell Keith Piores RosanesNo ratings yet
- CPCS204 09 Stacks Implementation ArraysLinkedListDocument32 pagesCPCS204 09 Stacks Implementation ArraysLinkedListHussein A. AlsameeNo ratings yet
- Library Management System (LMS) : Software Requirements SpecificationDocument22 pagesLibrary Management System (LMS) : Software Requirements SpecificationRohit DeshmukhNo ratings yet
- My Intel I9 10900 BillDocument4 pagesMy Intel I9 10900 BillMystica FlaireNo ratings yet
- قوانين عن التسعيرDocument8 pagesقوانين عن التسعيرمحمود الجالسNo ratings yet
- IC Tech Spec AttributesDocument22 pagesIC Tech Spec Attributeshome cecNo ratings yet
- Sy Ee 321 Emw MicroprojectDocument12 pagesSy Ee 321 Emw MicroprojectPari PatilNo ratings yet