Professional Documents
Culture Documents
RFBT - Mock Final Term Exam
RFBT - Mock Final Term Exam
Uploaded by
jolly hotdogOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
RFBT - Mock Final Term Exam
RFBT - Mock Final Term Exam
Uploaded by
jolly hotdogCopyright:
Available Formats
Home FAQ About Log out
DLSU-D RFBT_Mock Final Term Exam
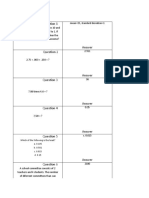
Thank you. Your responses have been automatically graded. Here are your
results.
Score Summary
points points
(Click on question number to jump to question.) earned possible
Question 1 correct 1 1
Question 2 correct 1 1
Question 3 correct 1 1
Question 4 correct 1 1
Question 5 correct 1 1
Question 6 correct 1 1
Question 7 correct 1 1
Question 8 correct 1 1
Question 9 correct 1 1
Question 10 correct 1 1
Question 11 correct 1 1
Question 12 correct 1 1
Question 13 correct 1 1
Question 14 correct 1 1
Question 15 correct 1 1
Question 16 correct 1 1
Question 17 correct 1 1
Question 18 correct 1 1
Question 19 correct 1 1
Question 20 correct 1 1
Question 21 correct 1 1
Question 22 correct 1 1
Question 23 correct 1 1
Question 24 correct 1 1
Question 25 correct 1 1
Question 26 correct 1 1
Question 27 correct 1 1
Question 28 correct 1 1
Question 29 correct 1 1
Question 30 correct 1 1
Question 31 correct 1 1
Question 32 correct 1 1
Question 33 correct 1 1
Question 34 correct 1 1
Question 35 correct 4 4
Question 36 correct 1 1
Question 37 correct 1 1
Question 38 correct 1 1
Question 39 correct 1 1
Question 40 correct 1 1
Question 41 correct 1 1
Question 42 correct 1 1
Question 43 correct 1 1
Question 44 correct 1 1
Question 45 correct 1 1
Question 46 correct 1 1
Question 47 correct 1 1
Question 48 correct 1 1
Question 49 correct 1 1
Question 50 correct 1 1
Score: (100%) 53 53
1. What is the most appropriate type of protection for toy designs of Yoda and R2D2?
• Invention
• Utility Model
• Industrial Design (correct answer, your response)
• None of the above
Points earned: 1 out of 1
2. This is a type of trademark that gives hint at some quality or character of the product at issue
without actually describing the product.
• Coined/Fanciful
• Arbitrary
• Descriptive
• Suggestive (correct answer, your response)
Points earned: 1 out of 1
3. The following are the functions of a trademark, EXCEPT:
• Advertising function
• Source identifier
• Quality indicator
• None of the above (correct answer, your response)
Points earned: 1 out of 1
4. In Section 21 of R.A. No. 8293 or Intellectual Property Code of the Philippines, an invention
can be patented if it is (1) new or novel, (2) has an inventive step, and (3) _______.
• A method of performing mental acts, playing games or doing business
• A discovery, scientific theory and mathematical method
• Industrially Applicable (correct answer, your response)
• An Aesthetic creation
Points earned: 1 out of 1
5. This intellectual property right protection is given to a composition of lines or colors or any
three dimensional form, giving a special appearance to and can serve as pattern for an
industrial product or handicraft.
• Industrial Design (correct answer, your response)
• Layout-Design of Integrated Circuit
• Utility Model
• Invention Patent
Points earned: 1 out of 1
6. The term of protection for a utility model is:
• 5 years from the date of the filing of the application
• 20 years from the date of the filing of the application
• 7 years from the date of the filing of the application (correct answer, your response)
• 10 years from the date of the filing of the application
Points earned: 1 out of 1
7. What protects the aesthetic features of an article of manufacture?
• Utility models
• Patents
• Copyright
• Industrial Design (correct answer, your response)
• Trademarks
Points earned: 1 out of 1
8. The Philippine Flag is not a registrable mark.
• True (correct answer, your response)
• False
Points earned: 1 out of 1
9. The trademark protection allowed by IPOPHL protects the mark only in the Philippines.
• True (correct answer, your response)
• False
Points earned: 1 out of 1
10. Z commissioned X and Y to paint a wall at the main lobby of his building. Z provided for the
materials. After the completion of the project, Z fully paid the artists fee X and Y. Who will own
the copyright in the aforesaid painting?
• Only Y owns the copyright.
• Z owns the copyright.
• Only X own the copyright.
• X, Y, and Z own the copyright.
• X and Y own the copyright. (correct answer, your response)
Points earned: 1 out of 1
11. To determine whether a trademark has been infringed, we must consider the mark as a whole
and not as dissected. If the buyer is deceived, it is attributable to the marks as a totality, not
usually to any part of it.
• a. Holistic test (correct answer, your response)
• b. Dominancy test
• c. Visible test
• d. Vital test
Points earned: 1 out of 1
12. A data privacy violation is considered to be large scale if:
• a. the personal information of a least ten (10) persons is harmed
• b. the personal information of at least twenty (20) persons is harmed
c. the personal information of at least one hundred (100) persons is harmed (correct
•
answer, your response)
• d. the personal information of at least one thousand (1, 000) persons is harmed
Points earned: 1 out of 1
13. The data processor must report data breaches to the NPC within a period of:
• a. 24 hours
• b. 48 hours
• c. 72 hours (correct answer, your response)
• d. Five days
Points earned: 1 out of 1
14. A data subject has the right to access:
I. The address of the personal information controller
II. Sources from which his personal information were obtained.
• a. I only.
• b. II only
• c. Both I and II. (correct answer, your response)
• d. Neither I nor II.
Points earned: 1 out of 1
15. Mr. X was admitted in a hospital. He is suffering from difficulty in breathing, high fever, and
fatigue. His symptoms are quickly worsening. The doctor asked his wife as to previous
admissions, but the wife had no idea. Instead, the wife informed the doctor that he was
previously admitted at BCD Hospital and they have the health records of Mr. X. The doctor
called at BCD Hospital disclosed the health records to the doctor. Is there any breach of the
Data Privacy Act with the disclosure?
• a. Yes, because Mr. X did not give her consent.
b. No, because Mr. X’s wife, as his duty authorized representative, gave her consent for the
•
disclosure.
• c. Yes, because health records are considered as sensitive personal information.
d. No, because the processing of the personal information is necessary for purpose of
•
medical treatment. (correct answer, your response)
Points earned: 1 out of 1
16. Kris joined the raffle draw of Barry’s Supermarket in the hopes of winning a 42” Smart TV. Kris
indicated her mobile phone number and email address in the form given for the raffle entry.
The form looked simple for Kris. It just contained empty fields to be filled out, the logo of
Barry’s Supermarket, and the grand prizes to be won. However, to her surprise, Kris soon
received multiple promotions from different brands asking her to buy products at a discount.
Her email inbox soon became spammed as well with unwanted promotions. Is it a data privacy
principle violated?
• a. No. Everything is legal.
• b. Yes. The Principle of Proportionality was violated.
• c. Yes. The Principle of Legitimate Purpose was violated.
• d. Yes. The Principle of Transparency was violated. (correct answer, your response)
Points earned: 1 out of 1
17. Tanggol, a personal information processor, is charged with the violation of the Data Privacy
Act. The violation consists of two acts. First, Tanggol revealed the salary range of Rigor, an
Administrative Officer III at the Department of Finance. Second, Tanggol, in publishing his
research, disclosed the ages and sexes of the respondents to his survey. Is Tanggol liable for
violation of the Data Privacy Act?
• No. (correct answer, your response)
• Yes, but only as to the first act.
• Yes, but only as to the second act.
• Yes, on both acts.
Points earned: 1 out of 1
18. It refers to an individual whose personal information is processed.
• Personal information provider
• Personal information holder
• Data subject (correct answer, your response)
• Data person
• Data base
Points earned: 1 out of 1
19. It refers to a person or organization who controls the collection, holding, processing, or use of
personal information, including a person or organization who instructs another person or
organization to collect, hold, process, use, transfer or disclose personal information on his or
her behalf.
• Personal information collector
• Personal information controller (correct answer, your response)
• Personal information manager
• Personal information repository
Points earned: 1 out of 1
20. The following are the requisites of Immunity under the Ease of Doing Business and Efficient
Government Service Delivery Act of 2018.
The testimony of said respondent/accused-informant can be substantially corroborated in
•
its material points
• The respondent/accused-informant does not appear to be the most guilty
The respondent/accused-informant has not been previously convicted of a crime involving
•
moral turpitude
• All of the above (correct answer, your response)
Points earned: 1 out of 1
21. I. The Report Card survey shall be a holistic tool that will measure effectiveness of the Citizen's
Charter in reducing regulatory burdens and the impact of the human resource systems and
programs in delivering efficient government service.
II. The Report Card survey shall also be used to obtain information and/or estimates of hidden
costs incurred by applicants or requesting parties to access government services which may
include, but is not limited to, bribes and payment to fixers.
• Only I is true
• Only II is true
• Both are true (correct answer, your response)
• Both are false
Points earned: 1 out of 1
22. The processing and approval of licenses, clearances, permits, certifications or authorizations
for the installation and operation of telecommunication, broadcast towers, facilities, equipment
and service shall be:
I. a total of 7 working days for those issued by the barangay.
II. a total of 7 working days for those issued by LGUs.
III. a total of 7 working days for those issued by NGAs.
• I only
• I and II only
• II and III only
• I, II, and III (correct answer, your response)
Points earned: 1 out of 1
23. I. Business permits shall be valid for a period of 2 years.
II. The city/municipality may have the option to renew business permits within the first month
of the year or on the anniversary date of the issuance of the business permit.
• Only I is true
• Only II is true (correct answer, your response)
• Both are true
• Both are false
Points earned: 1 out of 1
24. I. Each agency shall establish a public assistance or complaints desk which shall be set-up to,
among others, effectively receive feedback and monitor customer satisfaction, in a
conspicuous area at their official place of business, where an officer or employee
knowledgeable in frontline services shall at all times be available for consultation and advice.
II. The desk may not be attended to during break time.
• Only I is true (correct answer, your response)
• Only II is true
• Both are true
• Both are false
Points earned: 1 out of 1
25. I. The grounds for the denial of request for access to government service must be fair, just,
and reasonable.
II. Any denial of the application or request must have the approval of the immediate
supervisor of the employee or officer who denied the application or request.
• Only I is true
• Only II is true
• Both are true (correct answer, your response)
• Both are false
Points earned: 1 out of 1
26. For applications or requests involving activities which pose danger to public health, public
safety, public morals, public policy, and highly technical application, the prescribed processing
time shall in no case be longer than ____ working days or as determined by the government
agency or instrumentality concerned, whichever is shorter.
• 10
• 15
• 20 (correct answer, your response)
• 25
Points earned: 1 out of 1
27. All applications or requests submitted shall be acted upon by the assigned officer or employee
within the prescribed processing time stated in the Citizen's Charter which shall not be longer
than _____ working days in the case of simple transactions from the date the request and/or
complete application or request was received.
• one
• two
• three (correct answer, your response)
• four
Points earned: 1 out of 1
28. Under the Ease of Doing Business Act. The number of signatories in any document shall be
limited to a maximum of:
• a. Two signatures
• b. Three signatures (correct answer, your response)
• c. Four signatures
• d. Five signatures
Points earned: 1 out of 1
29. As a general rule, an employee cannot be compelled to render overtime work because that is
violative of the constitutional injunction against involuntary servitude.
Only in the following cases can an employer compel employees to render overtime work:
War Emergency Situation- when the country is at war or when any other national or local
•
emergency has been declared by Congress or the Chief Executive;
Disaster/Calamity- When overtime work is necessary to prevent loss of life or property, or
in case of imminent danger to public safety due to actual or impending emergency in the
•
locality caused by serious accident, fire, flood, typhoon, earthquake, epidemic or other
disaster or calamity.
Urgent Repairs- When there is urgent work to be performed on machines, installations or
• equipment in order to avoid serious loss or damage to the employer or some other causes
of similar nature;
Preservation of Perishable Goods- When the work is necessary to prevent loss or damage
•
to perishable goods;
Completion of Work- When completion or continuation of work started before the eight
• hour is necessary to prevent serious obstruction or prejudice to the business or operations
of the employer;
Take Advantage of favorable weather conditions- When overtime work is necessary to avail
• of favorable whether or environmental conditions where performance or quality of work is
dependent thereon.
• All of the above answers are correct. (correct answer, your response)
Points earned: 1 out of 1
30. May the employer and employee
stipulate that the latter’s regular or basic
salary already includes the overtime pay,
such that when the employee actually
works overtime he cannot claim overtime
pay?
• Answer not given.
No, the employer and employee cannot stipulate that the latter‘s regular or basic salary
•
includes the overtime pay; (correct answer, your response)
Yes, provided there is a clear written agreement knowingly and freely entered into by the
•
employees;
Points earned: 1 out of 1
31. Work may be performed beyond eight (8)
hours a day provided that:
Employee is paid for overtime work an additional compensation equivalent to his regular
•
wage plus at least 25% thereof; (correct answer, your response)
Employee is paid for overtime work an additional compensation equivalent to his regular
•
wage plus at least 30% thereof;
Employee is paid for overtime work an additional compensation equivalent to his regular
•
wage plus at least 20% thereof;
• None of the above.
Points earned: 1 out of 1
32. The following are excluded from the
coverage of Book III of the Labor Code of the
Philippines (Conditions of employment)
except:
• Supervisors (correct answer, your response)
• Field personnel
• Managers
• Employees of government-owned and controlled corporations
Points earned: 1 out of 1
33. The workers worked as cargadores at
the warehouse and rice mills of farm A for
several years. As cargadores, they loaded,
unloaded and pilled sacks of rice from the
warehouse to the cargo trucks for delivery
to different places. They were paid by Farm
A on a piece-rate basis. Are the workers
considered regular employees?
a. Yes, because Farm A paid wages directly to these workers without the intervention of
•
any third party independent contractor.
• b. Yes, their work is directly related, necessary and vital to the operations of the farm;
c. No, because Farm A did not have the power to control the workers with respect to the
•
means and methods by which the work is to be accomplished
• d. A and B. (correct answer, your response)
Points earned: 1 out of 1
34. Robert, an employee of ABC Company,
is married to Wanda. One day, Wanda
visited the company office with her three (3)
emaciated minor children, and narrated to
the Manager that Robert had been
squandering his earnings on his mistress,
leaving only a paltry sum for the support of
their children. Wanda tearfully pleaded with
the Manager to let her have one half of
Robert's pay every payday to ensure that
her children would at least have food on the
table. To support her plea, Wanda
presented a Kasulatan signed by Robert
giving her one half of his salary, on the
condition that she would not complain if he
stayed with his mistress on weekends.
If you were the Manager, would you release
one half of Robert's salary to Wanda?
• Yes, because it is Robert's duty to financially support his minor children.
No, because an employer is prohibited from interfering with the freedom of its employees
•
to dispose of their wages. (correct answer, your response)
No, because Robert's Kasulatan is based on an illegal consideration and is of doubtful legal
•
validity.
• Yes, because of Robert's signed authorization to give Wanda one half of his salary.
Points earned: 1 out of 1
35. An employee with a daily wage of P145 who renders 2-hour overtime work on an ordinary day
will receive__________________.
• A. P180.32
• B. P185.32
• C. P190.32 (correct answer, your response)
• D. P200.32
• E. P175.32
Points earned: 4 out of 4
36. Art. 139. Minimum Employment Age- R.A. 7610, as amended by R.A. 7658 & 9231
• A. 21 years old
• B. 7 years old
• C. 13 years old
• D. 18 years old
• E. 15 years old (correct answer, your response)
Points earned: 1 out of 1
37. Parental Leave for Solo Parents (R.A. 8972) otherwise known as Solo Parents’ Act of 2000
• A. Parental Leave for 7 working days (correct answer, your response)
• B. Parental Leave for 10 working days
• C. Parental Leave for 15 working days
• D. Parental Leave for 20 working days
• E. Parental Leave for 30 working days
Points earned: 1 out of 1
38. Paternity Leave (R.A. 8187)
• A. Leave for 10 days
• B. Leave for 7 days (correct answer, your response)
• C. Leave for 15 days
• D. Leave for 20 days
• E. Leave for 30 days
Points earned: 1 out of 1
39. Pursuant to R.A. 11210 known as the Expanded Maternity Leave Act of 2019, MATERNITY
Leave Benefits
-shall be paid daily maternity benefit equivalent to her average daily salary
• A. 30 days normal delivery/78 days caesarean delivery
• B. 60 days normal delivery/90 days caesarean delivery
C. 105 days for live childbirth, regardless of the mode of delivery, and an additional 15
• days paid leave if the female worker qualifies as solo parent under R.A. 8972, or the Solo
Parents’ Welfare Act of 2000 (correct answer, your response)
• D. Answer not given.
Points earned: 1 out of 1
40. Holiday pay is _____percent (%) of the regular daily wage.
• A. Fifty percent (50%)
• B. One Hundred percent (100%) (correct answer, your response)
• C. One Hundred Fifty percent (150%)
• D. Two Hundred Fifty percent (250%)
Points earned: 1 out of 1
41. ART. 93. Compensation for rest day, Sunday, or holiday work.
(a) Where an employee is made or permitted to work on his scheduled rest day, he shall be
paid an additional compensation of at least ______percent (%) of his regular wage.
• A. Ten percent (10%)
• B. Fifteen percent (15%)
• C. Twenty percent (20%)
• D. Thirty percent (30%) (correct answer, your response)
• E. Thirty-five percent (35%)
Points earned: 1 out of 1
42. ART. 87. Overtime work. - Work may be performed beyond eight (8) hours a day provided that
the employee is paid for the overtime work, an additional compensation equivalent to his
regular wage plus at least ______ percent (%) thereof.
• A. Twenty-five percent (25%) (correct answer, your response)
• B. Thirty percent (30%)
• C. Twenty percent (20%)
• D. Fifteen percent (15%)
• E. One Hundred percent (100%)
Points earned: 1 out of 1
43. The minimum wage rates for agri and non-agri employees and workers shall be those
prescribed by the________________.
• A. Board of Directors
• B. Labor Management Council
• C. Reg’l. Tripartite Wages and Productivity Board (correct answer, your response)
• D. POEA
• E. OWWA
Points earned: 1 out of 1
44. I. Hacking or cracking which refers to unauthorized access into or interference in a computer
system/server or information and communication system; or any access in order to corrupt,
alter, steal, or destroy using a computer or other similar information and communication
devices, without the knowledge and consent of the owner of the computer or information and
communications system, including the introduction of computer viruses and the like, resulting
in the corruption, destruction, alteration, theft or loss of electronic data messages or electronic
document.
II. Piracy or the unauthorized copying, reproduction, dissemination, distribution, importation,
use, removal, alteration, substitution, modification, storage, uploading, downloading,
communication, making available to the public, or broadcasting of protected material,
electronic signature or copyrighted works including legally protected sound recordings or
phonograms or information material on protected works, through the use of
telecommunication networks, such as, but not limited to, the internet, in a manner that
infringes intellectual property rights.
• Statement I is true, Statement II is false.
• Statement I is false, Statement II is true.
• Both statements are true. (correct answer, your response)
• Both statements are false.
Points earned: 1 out of 1
45. I. No person or party shall be subject to any civil or criminal liability in respect of the electronic
data message or electronic document for which the person or party acting as a service
provider as defined in Section 5 merely provides access if such liability is founded on 1) The
obligations and liabilities of the parties under the electronic data message or electronic
document; and 2) The making, publication, dissemination or distribution of such material or
any statement made in such material, including possible infringement of any right subsisting in
or in relation to such material.
II. Access to an electronic file, or an electronic signature of an electronic data message or
electronic document shall only be authorized and enforced in favor of the individual or entity
having a legal right to the possession or the use of the plaintext, electronic signature or file
and solely for the authorized purposes. The electronic key for identity or integrity shall not be
made available to any person or party without the consent of the individual or entity in lawful
possession of that electronic key.
• Statement I is true, Statement II is false.
• Statement I is false, Statement II is true.
• Both statements are true. (correct answer, your response)
• Both statements are false.
Points earned: 1 out of 1
46. I. If a right is to be granted to, or an obligation is to be acquired by, one person and no other
person, and if the law requires that, in order to effect this, the right or obligation must be
conveyed to that person by the transfer, or use of, a paper document, that requirement is met
if the right or obligation is conveyed by using one or more electronic data messages or
electronic documents unique.
II. If a rule of law is compulsorily applicable to a contract of carriage of goods which is in, or is
evidenced by, a paper document, that rule shall not be inapplicable to such a contract of
carriage of goods which is evidenced by one or more electronic data messages or electronic
documents by reason of the fact that the contract is evidenced by such electronic data
messages or electronic documents instead of by a paper document.
• Statement I is true, Statement II is false.
• Statement I is false, Statement II is true.
• Both statements are true. (correct answer, your response)
• Both statements are false.
Points earned: 1 out of 1
47. I. Subject to applicable laws and/or rules and guidelines promulgated by the Department of
Trade and Industry with other appropriate government agencies, parties to any electronic
transaction shall be free to determine the type and level of electronic data message and
electronic document security needed, and to select and use or implement appropriate
technological methods that suit their needs.
II. Where the law requires that any action referred to contract of carriage of goods be carried
out in writing or by using a paper document, that requirement is met if the action is carried
out by using one or more data messages or electronic documents.
• Statement I is true, Statement II is false.
• Statement I is false, Statement II is true.
• Both statements are true. (correct answer, your response)
• Both statements are false.
Points earned: 1 out of 1
48. I. “Electronic signature” refers to a secret code which secures and defends sensitive
information that crosses over public channels into a form decipherable only with a matching
electronic key.
II. “Intermediary” refers to a person who in behalf of another person and with respect to a
particular electronic document sends, receives and/or stores or provides other services in
respect of that electronic document.
• Statement I is true, Statement II is false.
• Statement I is false, Statement II is true. (correct answer, your response)
• Both statements are true.
You might also like
- Apt MCQ Aqa As Eco U1Document140 pagesApt MCQ Aqa As Eco U1jiayuwu57No ratings yet
- Wa0002.Document3 pagesWa0002.fatimah dinNo ratings yet
- Zach Garage Solution 21 YearsDocument19 pagesZach Garage Solution 21 YearsOshma Bhatia0% (1)
- Prelim Quiz 2 - Attempt Review PDFDocument6 pagesPrelim Quiz 2 - Attempt Review PDFPeter EcleviaNo ratings yet
- Quia - Prueba de OrtografíaDocument1 pageQuia - Prueba de OrtografíamarielaNo ratings yet
- RFBT - Mock Final Term ExamDocument13 pagesRFBT - Mock Final Term ExamMa. Yelena Italia TalabocNo ratings yet
- Quia - States of Matter TestDocument7 pagesQuia - States of Matter TestChas ShaferNo ratings yet
- Quia - Week 5 Grammar - Simple Past TenseDocument5 pagesQuia - Week 5 Grammar - Simple Past TenseLISETH ALEXANDRA JOJOA RODRIGUEZNo ratings yet
- Quia - Prueba de Ortografía Kenny PertuzDocument5 pagesQuia - Prueba de Ortografía Kenny PertuzHeri AntonioNo ratings yet
- Quia - Subnet QuestionsDocument7 pagesQuia - Subnet QuestionsFrancisco JosephNo ratings yet
- Quia - Week 5 Grammar - Simple Past TenseDocument7 pagesQuia - Week 5 Grammar - Simple Past TenseJHON ELVER BURGOS NARVAEZNo ratings yet
- Quia - Week 5 Grammar - Simple Past TenseDocument7 pagesQuia - Week 5 Grammar - Simple Past TenseJHON ELVER BURGOS NARVAEZNo ratings yet
- SAT PracticeTestDocument81 pagesSAT PracticeTesthafidov100% (1)
- Home FAQ About Log in Subscribe Now 30-Day Free TrialDocument3 pagesHome FAQ About Log in Subscribe Now 30-Day Free TrialkyansongeNo ratings yet
- Summary Report - TestNavDocument2 pagesSummary Report - TestNavadriansean853No ratings yet
- Summary Report - TestNavDocument2 pagesSummary Report - TestNavamilcar.aleman75No ratings yet
- FORM 4 ANALYSISDocument5 pagesFORM 4 ANALYSISAmelia CalistroNo ratings yet
- Class-4 Science: Lesson - 8 Lesson - 9 Lesson - 10 Lesson - 11 Lesson - 12 Lesson - 13 Lesson - 14Document2 pagesClass-4 Science: Lesson - 8 Lesson - 9 Lesson - 10 Lesson - 11 Lesson - 12 Lesson - 13 Lesson - 14SUNBEAM musicNo ratings yet
- 2012 Mark SchemeDocument13 pages2012 Mark SchemeΒασιλεία ΕυαγγέλουNo ratings yet
- GRAFIKDocument6 pagesGRAFIKIqbal KholidiNo ratings yet
- GoMath! Lesson (GoPlayer v3 - 0 Mobile)Document1 pageGoMath! Lesson (GoPlayer v3 - 0 Mobile)Federica MigliaresiNo ratings yet
- Quia - 2008 National Spanish Examination - Achievement - Level 3Document13 pagesQuia - 2008 National Spanish Examination - Achievement - Level 3zssamusNo ratings yet
- Calculus 2 Prelim ExamDocument18 pagesCalculus 2 Prelim ExamJohnjacob Gerardo100% (1)
- Preliminary Examination - Attempt Review PDFDocument9 pagesPreliminary Examination - Attempt Review PDFPeter EcleviaNo ratings yet
- MATH-6103-2013T (UGRD) Calculus 2: Prelim ExamDocument18 pagesMATH-6103-2013T (UGRD) Calculus 2: Prelim ExamJitlee PapaNo ratings yet
- Latihan Add m3 1Document9 pagesLatihan Add m3 1Mohana RomanNo ratings yet
- Item Set 1 Grade 7 Social Studies Practice Resource: Item Set 1 Number Student's Score Maximum ScoreDocument1 pageItem Set 1 Grade 7 Social Studies Practice Resource: Item Set 1 Number Student's Score Maximum ScoreStudent Michael CastilloNo ratings yet
- BIN - XI - Final Examination Guidelines 1st Semester 2023-2024Document2 pagesBIN - XI - Final Examination Guidelines 1st Semester 2023-2024AMIROTUL NABILAH BIG171No ratings yet
- Screenshot 2021-05-05 at 20.34.30Document1 pageScreenshot 2021-05-05 at 20.34.30Nguyen Quynh VyNo ratings yet
- Skema E2l P1 T2 IgcseDocument4 pagesSkema E2l P1 T2 IgcseAizat Zulhilmi YusupNo ratings yet
- TRIGONOMETRY Best QuestionsDocument124 pagesTRIGONOMETRY Best QuestionsDevanshu DwivediNo ratings yet
- Number Patterns and SeriesDocument4 pagesNumber Patterns and SeriesChris PatlingraoNo ratings yet
- 1994 Ajhsme Problems: Aops WikiDocument1 page1994 Ajhsme Problems: Aops WikiKevin LeeNo ratings yet
- Assignment Sheet CHAPTER 1: Variables, Expressions & IntegersDocument1 pageAssignment Sheet CHAPTER 1: Variables, Expressions & Integersamanda2979No ratings yet
- EM ASSIGNMENT BOOK-cs-is PDFDocument6 pagesEM ASSIGNMENT BOOK-cs-is PDFtvayush559No ratings yet
- Makalah TapDocument25 pagesMakalah TapBudi Leh UgaNo ratings yet
- 5s Audit: Company: Auditor: Area: DayDocument2 pages5s Audit: Company: Auditor: Area: DayJohn PaeNo ratings yet
- AMC Math ExamsDocument1 pageAMC Math ExamsKevin LeeNo ratings yet
- Transforming Lives Through Education With Quality Assurance Transforming Lives Through Education With Quality AssuranceDocument2 pagesTransforming Lives Through Education With Quality Assurance Transforming Lives Through Education With Quality AssuranceDarwin Dela CruzNo ratings yet
- Presentation, Creating A Video, Using Technology, Etc.) - Your Child Will Work in A Team, Guided by Me. We Will Be Working With Other Teachers in Year 2 EDUSNDocument3 pagesPresentation, Creating A Video, Using Technology, Etc.) - Your Child Will Work in A Team, Guided by Me. We Will Be Working With Other Teachers in Year 2 EDUSNCin Kyal LinNo ratings yet
- Milestone 2 College Logic and MathDocument6 pagesMilestone 2 College Logic and MathXyra ArsolerNo ratings yet
- AS Level FunctionDocument19 pagesAS Level FunctionJanet HussainNo ratings yet
- Rubric Unit5 Activity1Document1 pageRubric Unit5 Activity1Jesus is LordNo ratings yet
- AMC Math ExamsDocument1 pageAMC Math ExamsKevin LeeNo ratings yet
- Key For Pat 1 ReadingDocument2 pagesKey For Pat 1 ReadingNur FarahinNo ratings yet
- 1996 Ajhsme Problems: Aops WikiDocument1 page1996 Ajhsme Problems: Aops WikiKevin LeeNo ratings yet
- 2008 Amc 10B Problems: Aops WikiDocument1 page2008 Amc 10B Problems: Aops WikiKevin LeeNo ratings yet
- Quia - Check Your Knowledge of GrammarDocument7 pagesQuia - Check Your Knowledge of GrammarDavinia LongoNo ratings yet
- Midterm Quiz 1Document9 pagesMidterm Quiz 1Ace Ace ace babyNo ratings yet
- MCQ Chapter4Document11 pagesMCQ Chapter4bharath834No ratings yet
- Mark Scheme Summer 2009: IGCSE English As A Second Language (4357)Document10 pagesMark Scheme Summer 2009: IGCSE English As A Second Language (4357)Mohamed HaridyNo ratings yet
- 2022 Year 10 5.3 AT3Document14 pages2022 Year 10 5.3 AT3nichNo ratings yet
- Computational Thinking Worksheet 1 Thinking Abstractly-1Document2 pagesComputational Thinking Worksheet 1 Thinking Abstractly-1zhouzhouNo ratings yet
- Silva, G. B. 12-AJ. PT-2 (Module2 - ETech)Document6 pagesSilva, G. B. 12-AJ. PT-2 (Module2 - ETech)Gian Boiser SilvaNo ratings yet
- 2005 Amc 10B Problems: Aops WikiDocument1 page2005 Amc 10B Problems: Aops WikiKevin LeeNo ratings yet
- Attempt History: Due Mar 16 at 19:45 Available Mar 16 at 17:45 - Mar 16 at 19:45 1 / 1 PtsDocument5 pagesAttempt History: Due Mar 16 at 19:45 Available Mar 16 at 17:45 - Mar 16 at 19:45 1 / 1 PtsmlaNo ratings yet
- Reliability Testing 1Document397 pagesReliability Testing 1Tiqui, Charity Joy T.No ratings yet
- Turnitin - Online - Tutorial My ResultDocument1 pageTurnitin - Online - Tutorial My Resultjf1785No ratings yet
- E CatalogueDocument7 pagesE CatalogueÇağatay İşbilenNo ratings yet
- S7 N Open ItemDocument1,387 pagesS7 N Open ItemLet's know about it.No ratings yet
- Class 4: Ideation Phase: Prototyping Overview of Ideation Phase: PrototypingDocument15 pagesClass 4: Ideation Phase: Prototyping Overview of Ideation Phase: Prototypingdreamer4077No ratings yet
- Value Added Tax Act, 1991 Vs Value Added Tax and Supplementary Duty Act, 2012: A Comparison Dr. Md. Abdur RoufDocument6 pagesValue Added Tax Act, 1991 Vs Value Added Tax and Supplementary Duty Act, 2012: A Comparison Dr. Md. Abdur RoufMD Saiful IslamNo ratings yet
- 3 03.02.2020 NCLT Court No - Iii - 0Document2 pages3 03.02.2020 NCLT Court No - Iii - 0Vbs ReddyNo ratings yet
- Iloilo Investment and DevelopmentDocument51 pagesIloilo Investment and DevelopmentMarc Myer De AsisNo ratings yet
- 1 HRMP OL Cap Performance p69 Mo Hinh Hooi2020 XemDocument24 pages1 HRMP OL Cap Performance p69 Mo Hinh Hooi2020 XemPhạm NhungNo ratings yet
- Corporate Valuation Literature ReviewDocument4 pagesCorporate Valuation Literature Reviewsgfdsvbnd100% (1)
- CHAPTER 4 - Matching Supply and DemandDocument79 pagesCHAPTER 4 - Matching Supply and DemandFarah Hanim ShahruddinNo ratings yet
- Gmail Rediffmail Lottery: RequiredDocument27 pagesGmail Rediffmail Lottery: RequiredHR Nitin SharmaNo ratings yet
- List of VN Establishments To Korea 6.2016Document119 pagesList of VN Establishments To Korea 6.2016Thảo Pallet NhựaNo ratings yet
- Tob LLCDocument14 pagesTob LLCSarah BursteinNo ratings yet
- Coca Cola Training BookletDocument22 pagesCoca Cola Training BookletrameelNo ratings yet
- 2018 - Kuldeep Bishnoi - NLU NagpurDocument2 pages2018 - Kuldeep Bishnoi - NLU NagpurLife Hacks Stunt PerfectNo ratings yet
- Sbi Nifty Index Fund Factsheet (December-2020!13!11) PDFDocument1 pageSbi Nifty Index Fund Factsheet (December-2020!13!11) PDFSubscriptionNo ratings yet
- Financial Statement Analysis - Group 3Document15 pagesFinancial Statement Analysis - Group 3Nayna MangliyaNo ratings yet
- ADAPTERS WOODCOUSApdfDocument36 pagesADAPTERS WOODCOUSApdfsebastian zorroNo ratings yet
- NACVA Annual Consultants' Conference BrochureDocument24 pagesNACVA Annual Consultants' Conference BrochureNational Association of Certified Valuation AnalystsNo ratings yet
- Macro Economics: GNP GDPDocument9 pagesMacro Economics: GNP GDPmahesani_128_suhaiNo ratings yet
- 20 LinkedInDocument186 pages20 LinkedInAkhil Kumar50% (2)
- Are Western Leadership Development Approaches Appropriate in China or Are Chinese Approaches Better 2005Document3 pagesAre Western Leadership Development Approaches Appropriate in China or Are Chinese Approaches Better 2005Thuong NguyenNo ratings yet
- Policy Number: 920222223112157278 Proposal/Covernote No: R05092256949Document11 pagesPolicy Number: 920222223112157278 Proposal/Covernote No: R05092256949ajinkya patwardhanNo ratings yet
- Sarkozy Sentenced To 3 Years' Jail Over Corruption Pact With JudgeDocument18 pagesSarkozy Sentenced To 3 Years' Jail Over Corruption Pact With JudgeGrafo Bogdanov Novi SadNo ratings yet
- GDP in An Open Economy With Government: Lipsey & Chrystal Economics 12EDocument25 pagesGDP in An Open Economy With Government: Lipsey & Chrystal Economics 12EShubham DixitNo ratings yet
- NFO Bandhan Nifty Alpha50 Index FundDocument28 pagesNFO Bandhan Nifty Alpha50 Index Fundpwrsys18No ratings yet
- 4 Ways AI Will Transform Contact Centers in 2023Document10 pages4 Ways AI Will Transform Contact Centers in 2023Kyle De WaalNo ratings yet
- Ladder Risk AssessmentDocument3 pagesLadder Risk AssessmentPearl TeresaNo ratings yet
- Presented By: Sania NisarDocument15 pagesPresented By: Sania Nisarsanya-nisar-2818No ratings yet
- Employment Visa Designation ListDocument4 pagesEmployment Visa Designation ListAhtesham ArshadNo ratings yet