Professional Documents
Culture Documents
NCC 042748 19 Ict Risk Management Standard and Procedure
NCC 042748 19 Ict Risk Management Standard and Procedure
Uploaded by
Eqbal GubranOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
NCC 042748 19 Ict Risk Management Standard and Procedure
NCC 042748 19 Ict Risk Management Standard and Procedure
Uploaded by
Eqbal GubranCopyright:
Available Formats
ICT Risk Management Standard
and Procedure
V3 Jan 2020 Page 1 of 8
Revision History
Version Date Detail Author
0.1 28/02/201 First Version Kevin
4 O’Connor
0.2 01/11/201 Copy Document to new format Susan Horobin
7
0.3 09/01/202 Update of Document ready for Process review Susan Horobin
0 in April 2020
V3 Jan 2020 Page 2 of 8
Background
Risk management is the identification, evaluation, and prioritization of risks followed by coordinated and economical
application of resources to minimize, monitor, and control the probability or impact of unfortunate events or to max-
imize the realization of opportunities.
Risks can come from various sources including uncertainty in financial markets, threats from project failures (at any
phase in design, development, production, or sustaining of life-cycles), legal liabilities, credit risk, accidents, natural
causes and disasters, deliberate attack from an adversary, or events of uncertain or unpredictable root-cause. There
are two types of events i.e. negative events can be classified as risks while positive events are classified as opportuni-
ties.
Strategies to manage threats (uncertainties with negative consequences) typically include avoiding the threat, reduc-
ing the negative effect or probability of the threat, transferring all or part of the threat to another party, and even re-
taining some or all the potential or actual consequences of a particular threat.
In Information Technology, Risk management includes "Incident Handling", an action plan for dealing with intrusions,
cyber-theft, denial of service, fire, floods, and other security-related events. For Cyber Security Events this will in-
clude the ICT Cyber Security Incident Process: Preparation, Identification, Containment, Eradication, Recovery, and
Lessons Learned.
Purpose
This Standard is the Management of Risks for the ICT Operational Delivery Group within NCC (Nottinghamshire
County Council). The Procedure follows the M_O_R (Management of Risk) Methodology.
Scope
The scope of this document is to specify the overall standard, procedure and Roles and Responsibilities for the
M_o_R Risk Management Process.
V3 Jan 2020 Page 3 of 8
1. Method and Principles
Method
For the most part, these methods consist of the following elements, performed in the following order.
1. Identify the threats
2. Assess the vulnerability of critical assets to specific threats
3. Determine the risk (i.e. the expected likelihood and consequences of specific types of attacks on specific as-
sets)
4. Identify ways to reduce those risks
5. Prioritize risk reduction measures
Principles
Risk management should:
Create value – resources expended to mitigate risk should be less than the consequence of inaction
Be an integral part of organizational processes
Be part of a decision making process
Explicitly address uncertainty and assumptions
Be a systematic and structured process
Be based on the best available information
Be tailorable
Take human factors into account
Be transparent and inclusive
Be dynamic, iterative and responsive to change
Be capable of continual improvement and enhancement
Be continually or periodically re-assessed
2. Procedure
This involves:
1. observing the context
o the social scope of risk management
o the identity and objectives of stakeholders
o the basis upon which risks will be evaluated, constraints.
2. defining a framework for the activity and an agenda for identification
3. developing an analysis of risks involved in the process
4. mitigation or solution of risks using available technological, human and organizational resources
V3 Jan 2020 Page 4 of 8
Identification
Risks are about events that, when triggered, cause problems or benefits. Risk sources for the ICT Operational Deliv-
ery Risk Management Process are the ICT employees of NCC (Nottinghamshire County Council).
The risks that are raised are from identified threats, incidents, issues or problems related to the ICT systems and ser-
vices within NCC and are classified as:
Security Risks - Those of unauthorized access, alteration or use of information
Availability Risks - Those of inaccessible business processes or data
Performance Risks - Those of delayed access to business processes or data
Compliance Risks - Those of violating legal, regulatory or IT policy requirements
Reputational Risks – Those that have the potential of loss to financial capital, social capital and/or market share
resulting from damage to a firm's reputation
Assessment
Once risks have been identified, they must then be assessed as to their potential severity of impact (generally a neg-
ative impact, such as damage or loss) and to the probability of occurrence. These quantities can be either simple to
measure, in the case of the value of a lost building, or impossible to know for sure in the case of an unlikely event,
the probability of occurrence of which is unknown. Therefore, in the assessment process, the initial assessment for
every risk is to place it at a Very High status, so that it is communicated to Management and evaluated by the Opera-
tional Delivery Management Team (ODMT). Even a short-term positive improvement can have long-term negative
impacts.
The primary sources of information for risk assessment is made up of best educated opinions and available statistics.
To better understand and communicate risks to senior executives the most widely formula for risk quantification is:
"Rate (or probability) of occurrence multiplied by the impact of the event equals risk magnitude."
Severity and Impact
LIKELIHOOD
1 Rare 0 - 5 % Chance
2 Unlikely 6 to 20% Chance
3 Possible 21 to 50% Chance
4 Likely 51 to 80% Chance
5 Almost Certain 81% + Chance
IMPACT
1 Insignificant 0 - 5% Chance
2 Minor 6 to 20% Chance
3 Moderate 21 to 50% Chance
4 Significant 51 to 80% Chance
5 Catastrophic 81% + Chance
V3 Jan 2020 Page 5 of 8
Potential risk treatments
Once risks have been identified and assessed, all techniques to manage the risk fall into one or more of these four
major categories:
Avoidance (eliminate, withdraw from or not become involved)
Reduction (optimize – mitigate or control)
Sharing (transfer – outsource or insure)
Acceptance (accept and budget)
Risk avoidance
This includes not performing an activity that could present risk. Avoidance may seem like the answer to all risks, but
avoiding risks also means losing out on the potential gain that accepting (retaining) the risk may have allowed.
Risk reduction
Risk reduction or "optimization" involves reducing the severity of the loss or the likelihood of the loss from occurring.
Acknowledging that risks can be positive or negative, optimizing risks means finding a balance between negative risk
and the benefit of the operation or activity; and between risk reduction and effort applied.
Risk sharing
Briefly defined as "sharing with another party or team (including external vendors) the burden of loss or the benefit
of gain, from a risk, and the measures to reduce a risk."
The term of 'risk transfer' is often used in place of risk sharing which means you can transfer a risk to a third party, or
to another team.
Some ways of managing risk will fall into multiple categories.
Risk Acceptance
Risk acceptance involves accepting the loss, or benefit of gain, from a risk when the incident occurs. Risk retention is
a viable strategy for Low risks or for Risks where there is a long term strategy and a workaround in place.
Risk Register and Risk Report
Risks are raised by ICT and added to the Operational Delivery Group Risk Register. Risk mitigation needs to be ap-
proved by Operational Delivery Management Team and updated on the Register and Report.
The risk management register and report should propose applicable and effective security controls for managing the
risks and contain a schedule for the controlled implementation and responsible persons for those actions.
All the decisions about how each of the identified risks should be handled must be documented on the Register and
Report.
V3 Jan 2020 Page 6 of 8
Review and Evaluation of the ICT Risks on the ICT Operational Delivery Group Risk
Register and Risk Reports
The Risk Analysis on the Risk Register is updated bi-weekly and the Top 5 Very High categorized risks are presented
at the Operational Delivery Management Meeting bi-weekly.
Risks are measured by impacts × probability. With bi-weekly reviews, the Very High Risks are re-evaluated depend-
ing on the completion of mitigations or acceptance and can be downgraded for monitoring.
Risks are reported on the Monthly Performance Reporting.
Cost formulae can be associated with Risks to determine budget:
the cost associated with the risk if it arises, estimated by multiplying employee costs per unit time by the es-
timated time lost (cost impact, C where C = cost accrual ratio * S)
the probable increase in time associated with a risk (schedule variance due to risk, Rs where Rs = P * S):
o Sorting on this value puts the highest risks to the schedule first. This is intended to cause the great-
est risks to any process or project to be attempted first so that risk is minimized as quickly as possi-
ble.
o This is slightly misleading as schedule variances with a large P and small S and vice versa are not
equivalent. (The risk of the RMS Titanic sinking vs. the passengers' meals being served at slightly the
wrong time).
the probable increase in cost associated with a risk (cost variance due to risk, Rc where Rc = P*C = P*CAR*S =
P*S*CAR)
o sorting on this value puts the highest risks to the budget first.
o see concerns about schedule variance as this is a function of it, as illustrated in the equation above.
Risk in a project or process can be due either to Special Cause Variation or Common Cause Variation and requires ap-
propriate treatment.
3. Roles and Responsibilities
Risk Identifier
The Risk Identifier is anyone who puts forward to the Risk Manager (Via the process) a “Potential Risk”. The Potential
Risk can be anything that the raiser believes will have an impact on the business.
Risk Manager
The Risk Manager is the owner of the Risk process and is responsible for:
Appointing ownership of risks
Chair of the Risk Forum Review Meetings
Reviewing, Rejecting, Logging, Activating and Escalating any potential risk.
The management and update of the Risk register, ensuring that actions are delivered.
V3 Jan 2020 Page 7 of 8
Communications and feedback to all stake holders (via the Risk Report).
Closing completed risks
Gaining sign off for “Accepted “risks.
Risk Owner
The Risk Owner is responsible for:
• Defining the specific risk.
• Defining any mitigations in the short term
• Creating solutions in the long term
• Communicating with all stakeholders
• Updating the Risk log and Risk manager in a timely and accurate manner.
Operational Delivery Group Manager
The Operational Delivery Group Manager is responsible for:
• Providing Guidance
• Escalating to the IT Director
• Reporting to the IT Director
• Chairing the Operational Delivery Group Management Team (ODMT) Meetings
• Signing off Risk Acceptance
V3 Jan 2020 Page 8 of 8
You might also like
- DOH V Phil Pharma Wealth, Inc.Document2 pagesDOH V Phil Pharma Wealth, Inc.Antonio Rebosa100% (1)
- Risk Assessment and Identifications The Pivot of Risk Management in An Organization.Document18 pagesRisk Assessment and Identifications The Pivot of Risk Management in An Organization.enbassey100% (1)
- BSBWHS401 Risk Management Procedures PDFDocument6 pagesBSBWHS401 Risk Management Procedures PDFdavidNo ratings yet
- Risk Heat Map: A Risk Assessment Tool To Assist in Risk Assessment ProductivityDocument6 pagesRisk Heat Map: A Risk Assessment Tool To Assist in Risk Assessment ProductivityRiz DeenNo ratings yet
- Kamiesberg IT RISK MANAGEMENT POLICYDocument7 pagesKamiesberg IT RISK MANAGEMENT POLICYU Myint ThanNo ratings yet
- Webinar 1 RISK IDENTIFICATION AND FRAMEWORKSDocument17 pagesWebinar 1 RISK IDENTIFICATION AND FRAMEWORKSbcbberenger2No ratings yet
- Risk Management Worksheets Risk Assessment WorksheetDocument4 pagesRisk Management Worksheets Risk Assessment Worksheetkapil ajmaniNo ratings yet
- Info Sheet Assessing RiskDocument5 pagesInfo Sheet Assessing RiskalkalkiaNo ratings yet
- Arslan Gohar IRMDocument11 pagesArslan Gohar IRMUzma SheikhNo ratings yet
- Attachment 4-Risk Management ProceduresDocument6 pagesAttachment 4-Risk Management ProceduresZhao LinNo ratings yet
- AF W12 - Fraud Risk Assessment - ENGDocument17 pagesAF W12 - Fraud Risk Assessment - ENGjokitugasbro.idNo ratings yet
- Chapter 10Document18 pagesChapter 10Tamim All HasanNo ratings yet
- Risk Management SopDocument8 pagesRisk Management SopLi QiNo ratings yet
- Risk Management SopDocument8 pagesRisk Management SopLi QiNo ratings yet
- Risk Management Approach For ISO27001Document3 pagesRisk Management Approach For ISO27001Canal HannasNo ratings yet
- Identifying and Categorizing Risks: WHO / Fredrik NaumannDocument26 pagesIdentifying and Categorizing Risks: WHO / Fredrik NaumannDiegoNo ratings yet
- The Risk Matrix: Jenmark John F. Jacolbe Gapor TahaDocument14 pagesThe Risk Matrix: Jenmark John F. Jacolbe Gapor TahaJheonology Fernando100% (1)
- Unec 1695844500Document22 pagesUnec 1695844500nicatmamedov794No ratings yet
- Risk Management ToolkitDocument24 pagesRisk Management ToolkitusmancaNo ratings yet
- Knowledge Area - Risk ManagementDocument16 pagesKnowledge Area - Risk ManagementViswanath2013No ratings yet
- Module 5 - Risk Management 1Document14 pagesModule 5 - Risk Management 1Teresa BuracNo ratings yet
- Supply Chain Risk Management Concept... Presentation 2nd SemDocument29 pagesSupply Chain Risk Management Concept... Presentation 2nd SemIsaac Tetteh CharnorNo ratings yet
- METHODOLOGYDocument3 pagesMETHODOLOGYSyakirin Spears100% (1)
- Risk and Risk ManagementDocument8 pagesRisk and Risk ManagementMARY JUSTINE PAQUIBOTNo ratings yet
- Introduction To Risk ManagementDocument44 pagesIntroduction To Risk Managementpikamau100% (1)
- Session Risk - and - Risk - ManagementDocument19 pagesSession Risk - and - Risk - ManagementMohit RawatNo ratings yet
- Important Definations - Risk ManagmentDocument11 pagesImportant Definations - Risk ManagmentomerNo ratings yet
- Unec 1695844500Document22 pagesUnec 1695844500nicatmamedov794No ratings yet
- IoD Adedipe Enterprise Risk ManagementDocument22 pagesIoD Adedipe Enterprise Risk ManagementSeye AwojobiNo ratings yet
- White Paper - Risk Management, Rev.8 en 2009-10-10Document10 pagesWhite Paper - Risk Management, Rev.8 en 2009-10-10enjoymenowNo ratings yet
- A. N - Bhagat - Risk Officer C.M.Chugh, AGM (Civil) - Resource Person Anand Trivedi, MGR (U&S) - Resource PersonDocument67 pagesA. N - Bhagat - Risk Officer C.M.Chugh, AGM (Civil) - Resource Person Anand Trivedi, MGR (U&S) - Resource PersonAnil100% (1)
- Risk Management TrainingDocument14 pagesRisk Management TrainingbsjathaulNo ratings yet
- Risk Management: Prof Mahesh Kumar Amity Business SchoolDocument41 pagesRisk Management: Prof Mahesh Kumar Amity Business SchoolasifanisNo ratings yet
- Risk Management in Agile ProjectsDocument4 pagesRisk Management in Agile ProjectspapimorokaNo ratings yet
- Project Risk Management - PM0007 SET-1Document5 pagesProject Risk Management - PM0007 SET-1mbaguideNo ratings yet
- PRM (Chapter 5 & 6)Document23 pagesPRM (Chapter 5 & 6)Mikias EphremNo ratings yet
- VIU Risk Management FrameworkDocument9 pagesVIU Risk Management FrameworkkharistiaNo ratings yet
- 3 - 2. Risk Identification and ClassificationDocument35 pages3 - 2. Risk Identification and Classification23Mochammad DwikyNo ratings yet
- Section 7 Slides 2022Document70 pagesSection 7 Slides 2022Sathappan KasiNo ratings yet
- Risk: Definition: Effect of Uncertainties On Objectives (ISO 31000:2018)Document40 pagesRisk: Definition: Effect of Uncertainties On Objectives (ISO 31000:2018)sskiitbNo ratings yet
- Quality Risk ManagementDocument5 pagesQuality Risk ManagementA VegaNo ratings yet
- Risk Assessment - Risk Assessment Framework 1Document12 pagesRisk Assessment - Risk Assessment Framework 1Jovche KrstitelcheNo ratings yet
- Introduct Ion To Risk Managem ENT: Jessica Lile - 18042044Document32 pagesIntroduct Ion To Risk Managem ENT: Jessica Lile - 18042044Jessica LileNo ratings yet
- Assessment Task 2Document9 pagesAssessment Task 2Muhammad Sheharyar MohsinNo ratings yet
- Module 2 - Risk Management ProcessDocument13 pagesModule 2 - Risk Management ProcessLara Camille CelestialNo ratings yet
- Risk Managementin InformatizationDocument12 pagesRisk Managementin InformatizationcherifdjNo ratings yet
- Risk ManagementDocument14 pagesRisk ManagementMateta Elie100% (2)
- Chapter 6 NDocument20 pagesChapter 6 Nyossef. kassayNo ratings yet
- CGR 501 Assignment 1Document16 pagesCGR 501 Assignment 1Sadia KabeerNo ratings yet
- ISO27k - RA - Spreadsheet - Version - 2Document98 pagesISO27k - RA - Spreadsheet - Version - 2monicaboNo ratings yet
- Risk Analytics - Tutorial - w1Document21 pagesRisk Analytics - Tutorial - w1palasek182No ratings yet
- ICAEW - Bus - Fin - Chapter 5 - StudentDocument123 pagesICAEW - Bus - Fin - Chapter 5 - StudentMai HuyenNo ratings yet
- Risk Management ManualDocument18 pagesRisk Management ManualSavio SunnyNo ratings yet
- Risk ManagementDocument12 pagesRisk ManagementParasYadavNo ratings yet
- PM NOTES Chapter No 4Document4 pagesPM NOTES Chapter No 4Ashish KhadakhadeNo ratings yet
- Risk Management Phylosophy: Erman A SumiratDocument61 pagesRisk Management Phylosophy: Erman A SumiratDhea Yulianti PNo ratings yet
- Risk Assesment 1Document13 pagesRisk Assesment 1Dian Kristina RusmanaNo ratings yet
- Risk ManagementDocument26 pagesRisk ManagementRajaPal80% (5)
- Adventurer's Guide to Risk Management: Fictional Tales about Risk ManagementFrom EverandAdventurer's Guide to Risk Management: Fictional Tales about Risk ManagementNo ratings yet
- Foundations of Quality Risk Management: A Practical Approach to Effective Risk-Based ThinkingFrom EverandFoundations of Quality Risk Management: A Practical Approach to Effective Risk-Based ThinkingNo ratings yet
- Disaster Recovery Planning (1)Document4 pagesDisaster Recovery Planning (1)Eqbal GubranNo ratings yet
- ITGC Expected Evidence SpreadsheetDocument54 pagesITGC Expected Evidence SpreadsheetEqbal GubranNo ratings yet
- OpensourcesoftwareDocument7 pagesOpensourcesoftwareEqbal GubranNo ratings yet
- TMackey Ssca Forum 053123Document31 pagesTMackey Ssca Forum 053123Eqbal GubranNo ratings yet
- Supply Chain Risk ManagementDocument33 pagesSupply Chain Risk ManagementEqbal GubranNo ratings yet
- RMM 2021 01 Excerpt 4Document14 pagesRMM 2021 01 Excerpt 4Eqbal GubranNo ratings yet
- Utmb Third Party Risk Management ReportDocument7 pagesUtmb Third Party Risk Management ReportEqbal GubranNo ratings yet
- Template DocsDocument3 pagesTemplate DocsEqbal GubranNo ratings yet
- APPLICATION PENETRATION TEST CHECKLIST (1)Document4 pagesAPPLICATION PENETRATION TEST CHECKLIST (1)Eqbal GubranNo ratings yet
- Checklist of Mandatory Documentation ReqDocument22 pagesChecklist of Mandatory Documentation ReqEqbal GubranNo ratings yet
- ISMS Awareness TrainingDocument29 pagesISMS Awareness TrainingEqbal GubranNo ratings yet
- XM IS GovernanceDocument1 pageXM IS GovernanceEqbal GubranNo ratings yet
- Sustainability Planning Using The GRC Framework AnnouncementDocument2 pagesSustainability Planning Using The GRC Framework AnnouncementEqbal GubranNo ratings yet
- IT Governance WikipediaDocument6 pagesIT Governance WikipediaEqbal GubranNo ratings yet
- FSANZ Governance Framework 2023Document15 pagesFSANZ Governance Framework 2023Eqbal GubranNo ratings yet
- Implement GRC Technology The Right WayDocument4 pagesImplement GRC Technology The Right WayEqbal GubranNo ratings yet
- IM Infographic Interoperatability Maturity Model V2 2022Document12 pagesIM Infographic Interoperatability Maturity Model V2 2022Eqbal GubranNo ratings yet
- GRC Case Study 3 Property Fund ManagerDocument1 pageGRC Case Study 3 Property Fund ManagerEqbal GubranNo ratings yet
- I T R M P: Nformation Echnology ISK Anagement LANDocument26 pagesI T R M P: Nformation Echnology ISK Anagement LANEqbal GubranNo ratings yet
- ISM March 2024 Changes (March 2024)Document2 pagesISM March 2024 Changes (March 2024)Eqbal GubranNo ratings yet
- Rini Au 2Document10 pagesRini Au 2Eqbal GubranNo ratings yet
- Sample Digital Asset Support AssessmentDocument3 pagesSample Digital Asset Support AssessmentEqbal GubranNo ratings yet
- PeaceCorpsITRiskMP 2016intranetmod 2017Document24 pagesPeaceCorpsITRiskMP 2016intranetmod 2017Eqbal GubranNo ratings yet
- Using Information Technology Governance Risk ManagDocument11 pagesUsing Information Technology Governance Risk ManagEqbal GubranNo ratings yet
- Itil SDLC ContextDocument2 pagesItil SDLC ContextEqbal GubranNo ratings yet
- IT Governance Adoption in Banking and inDocument26 pagesIT Governance Adoption in Banking and inEqbal GubranNo ratings yet
- Risk Analysis Vs Security ControlsDocument15 pagesRisk Analysis Vs Security ControlsEqbal GubranNo ratings yet
- COBIT Security AssetsDocument5 pagesCOBIT Security AssetsEqbal GubranNo ratings yet
- Windows Interoperability Automated Test CasesDocument26 pagesWindows Interoperability Automated Test CasesEqbal GubranNo ratings yet
- Risk Management Workshop PPT Jun 23Document35 pagesRisk Management Workshop PPT Jun 23Eqbal GubranNo ratings yet
- Green Logistics and Transportation - A Sustainable Supply Chain Perspective PDFDriveDocument198 pagesGreen Logistics and Transportation - A Sustainable Supply Chain Perspective PDFDriveMigle BloomNo ratings yet
- Candyland Novella Term ProjectDocument15 pagesCandyland Novella Term Projectbatool mehdiNo ratings yet
- INF788 2024 Lecture 2Document37 pagesINF788 2024 Lecture 2u19236931No ratings yet
- Final Thesis Cha 1&3 (New)Document14 pagesFinal Thesis Cha 1&3 (New)Hikma HamzaNo ratings yet
- Erp Case StudyDocument7 pagesErp Case Study207-Sulman TariqNo ratings yet
- Business Plan (Fish Farming)Document9 pagesBusiness Plan (Fish Farming)ceo solaNo ratings yet
- BlackbookDocument46 pagesBlackbookunknowgamer9820680832No ratings yet
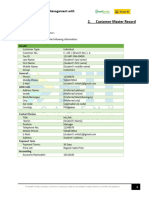
- Customer Master Record: Smartbooks Operations Management With Analytics Workbook Exercise 2.1Document8 pagesCustomer Master Record: Smartbooks Operations Management With Analytics Workbook Exercise 2.1jennicaashley.chua.engNo ratings yet
- Masbate Mobo Water District Organizational ChartDocument2 pagesMasbate Mobo Water District Organizational ChartSheena Jean Krystle LabaoNo ratings yet
- Entrepreneurship Trends and IssuesDocument55 pagesEntrepreneurship Trends and IssuesKatelyn RellitaNo ratings yet
- Chapter 2 Acctg 221Document26 pagesChapter 2 Acctg 221Crisciel Carzano CadungogNo ratings yet
- Lecture Note - Cost ConceptDocument23 pagesLecture Note - Cost ConceptPHƯƠNG HOÀNG HOÀINo ratings yet
- Additive Manufacturing InfographicDocument1 pageAdditive Manufacturing InfographicSergio Cantillo Luna0% (1)
- Water Treatment ForecastingDocument10 pagesWater Treatment Forecastingvaldi sNo ratings yet
- Problems: "Ch. 19-Inventory Theory" LINGO File For Selected ExamplesDocument12 pagesProblems: "Ch. 19-Inventory Theory" LINGO File For Selected ExamplesOmbasNo ratings yet
- Credit and Collection Wk1 2 StudDocument39 pagesCredit and Collection Wk1 2 StudAhyessa GetesNo ratings yet
- New - Blockchain Legal & Regulatory GuidanceDocument236 pagesNew - Blockchain Legal & Regulatory GuidanceChristian M Nino-Moris FANo ratings yet
- More Than A Sex Crime: A Feminist Political Economy of The 2014 Icloud HackDocument17 pagesMore Than A Sex Crime: A Feminist Political Economy of The 2014 Icloud HackSo AppalledNo ratings yet
- 3 The Balance of Payments: Chapter ObjectivesDocument12 pages3 The Balance of Payments: Chapter ObjectivesJayant312002 ChhabraNo ratings yet
- LC ZiaDocument3 pagesLC Ziasohelmatubbar2010No ratings yet
- Case Study SeminarDocument2 pagesCase Study SeminarkiloihackerNo ratings yet
- Tax Drills Weeks 1-7 & DiagnosticDocument119 pagesTax Drills Weeks 1-7 & DiagnosticMitch MinglanaNo ratings yet
- Project Management Essential NotesDocument36 pagesProject Management Essential NotesMarco GaspariNo ratings yet
- Top 10 List: For Preparedness On A BudgetDocument1 pageTop 10 List: For Preparedness On A BudgetMichael MccannNo ratings yet
- Knowledge and Human Capital As Sustainable Competitive Advantage in Human Resource Management2019Sustainability SwitzerlandDocument18 pagesKnowledge and Human Capital As Sustainable Competitive Advantage in Human Resource Management2019Sustainability SwitzerlandMary RodchenkoNo ratings yet
- Impact of GATT and WTO On Indian ForeignDocument30 pagesImpact of GATT and WTO On Indian Foreignshipra29No ratings yet
- ............ May 21 U3 QP - 20Document28 pages............ May 21 U3 QP - 20Yuvipro gidwaniNo ratings yet
- Dokumen - Tips Case Study 55c610649fb79Document9 pagesDokumen - Tips Case Study 55c610649fb79Mario ChandraNo ratings yet
- 1.1 BackgroundDocument27 pages1.1 BackgroundrahulprajapNo ratings yet