Professional Documents
Culture Documents
Diploma 6th Sem Model Answer Paper. 22620 - Diploma 6th Sem Model Answer Paper
Diploma 6th Sem Model Answer Paper. 22620 - Diploma 6th Sem Model Answer Paper
Uploaded by
Vishnu MaskarCopyright:
Available Formats
You might also like
- Ansible Hands OnDocument8 pagesAnsible Hands Onu952No ratings yet
- Diploma 6th Sem Model Answer PaperDocument26 pagesDiploma 6th Sem Model Answer Paperommane31200375% (4)
- S23 Model SolutionDocument25 pagesS23 Model Solutiontanupandav333No ratings yet
- NIS Model Answer 2022Document28 pagesNIS Model Answer 2022Rishi100% (13)
- Modelans W g22Document28 pagesModelans W g22ommane312003No ratings yet
- 17514-2019-Winter-Model-Answer-Paper (Msbte Study Resources)Document29 pages17514-2019-Winter-Model-Answer-Paper (Msbte Study Resources)aryasurve1210No ratings yet
- Ans W 22 NisDocument28 pagesAns W 22 NisCo- 65 Madhukanth PoojaryNo ratings yet
- NIS Winter 2022Document27 pagesNIS Winter 2022aniket100% (1)
- Nis 22620 Sample Papers S-22, w22, s23Document81 pagesNis 22620 Sample Papers S-22, w22, s23Rutuja ShindeNo ratings yet
- Winter Nis Model Ans 2022Document28 pagesWinter Nis Model Ans 2022AloneNo ratings yet
- Nis S-22Document28 pagesNis S-2251 IF Nilesh sabaleNo ratings yet
- Winter Nis Model Ans 2022Document28 pagesWinter Nis Model Ans 2022Pranit ShitoleNo ratings yet
- Important Instructions To Examiners:: What Is Computer Security & Its Need?Document40 pagesImportant Instructions To Examiners:: What Is Computer Security & Its Need?Gaurang NakumNo ratings yet
- S23 CND 22634Document27 pagesS23 CND 22634harshy0816100% (1)
- Ans W 22 NisDocument28 pagesAns W 22 NisbsjssbjdNo ratings yet
- 2016 Summer Model Answer Paper PDFDocument31 pages2016 Summer Model Answer Paper PDFMahesh DahiwalNo ratings yet
- S 2023 22414Document22 pagesS 2023 22414vinay.niranjan006No ratings yet
- 2015 Summer Model Answer Paper PDFDocument49 pages2015 Summer Model Answer Paper PDFMahesh DahiwalNo ratings yet
- Unit 2 - MCQDocument37 pagesUnit 2 - MCQShubham TayadeNo ratings yet
- Assignment Cyber Security Principles 600 ASS 2Document3 pagesAssignment Cyber Security Principles 600 ASS 2Saieesh RamgobinNo ratings yet
- 420240-DCC w23, s23, w22, s22, w19, s19Document148 pages420240-DCC w23, s23, w22, s22, w19, s19hackermh862No ratings yet
- Msbte w22 22417Document21 pagesMsbte w22 22417jacksparrowcom4100% (1)
- Corrected Summer 2016 Model Answer PaperDocument25 pagesCorrected Summer 2016 Model Answer PaperSuyog KadamNo ratings yet
- Course Code: CSYS1102 Duration: 1 Week Course Name: Introduction To Computer Security Coursework Weight: 10%Document6 pagesCourse Code: CSYS1102 Duration: 1 Week Course Name: Introduction To Computer Security Coursework Weight: 10%RammyBradNo ratings yet
- 22634-2022-Winter-Model-Answer-Paper (Msbte Study Resources)Document25 pages22634-2022-Winter-Model-Answer-Paper (Msbte Study Resources)ashusonkamble979No ratings yet
- CNE Model Answer PaperDocument47 pagesCNE Model Answer Paperop gamerNo ratings yet
- 22417Document30 pages22417Hack ManiaNo ratings yet
- Winter 22Document25 pagesWinter 22rohitmhaske0208No ratings yet
- 2018 Winter Model Answer PaperDocument25 pages2018 Winter Model Answer PaperVarad KhopkarNo ratings yet
- Model Answers Winter 2018Document26 pagesModel Answers Winter 2018kiritoblackswordsmen07No ratings yet
- Ilovepdf MergedDocument21 pagesIlovepdf Mergedd.soniNo ratings yet
- DCC Winter 22 Removed OrganizedDocument24 pagesDCC Winter 22 Removed Organizedsayedshaad02No ratings yet
- Detection of Logic Bombs PDFDocument3 pagesDetection of Logic Bombs PDFManoharrNo ratings yet
- ACN s23Document29 pagesACN s23kalpakpatil2004No ratings yet
- 6th Sem Pyq'sDocument17 pages6th Sem Pyq'sManeeshMahajanNo ratings yet
- DCC Summer 2023 AnswerDocument20 pagesDCC Summer 2023 Answertejasnarwade2k5No ratings yet
- SEN Winter2019Document23 pagesSEN Winter2019Sujal SonawaneNo ratings yet
- CS CIA1 2019-20 ME FinalDocument1 pageCS CIA1 2019-20 ME FinalvikNo ratings yet
- 22414DCC Summer 2023Document20 pages22414DCC Summer 2023nvoid7166No ratings yet
- Winter - 18 Examination: Important Instructions To ExaminersDocument34 pagesWinter - 18 Examination: Important Instructions To ExaminersMahesh DahiwalNo ratings yet
- Nis W-22Document27 pagesNis W-22Sahil MulayNo ratings yet
- WMN Model Summer-23Document19 pagesWMN Model Summer-23navteshdeore19100% (3)
- 2018 Winter OOP 3I - M - 22316 - CODocument26 pages2018 Winter OOP 3I - M - 22316 - CO14adisunnyNo ratings yet
- w22 SolutionDocument24 pagesw22 SolutionVaishnavi KadamNo ratings yet
- 4 DcoDocument62 pages4 DcoSachin KondawarNo ratings yet
- Model Answer Winter 2019Document22 pagesModel Answer Winter 2019IF21 Minit ChitrodaNo ratings yet
- MohamedshafiqueDocument10 pagesMohamedshafiquethalaaskar55No ratings yet
- RSAI Assignment 1Document6 pagesRSAI Assignment 1Shisa ChhotrayNo ratings yet
- XXXXX: Important Instructions To ExaminersDocument31 pagesXXXXX: Important Instructions To ExaminersYogesh DumaneNo ratings yet
- 22413-2019-Winter-Model-Answer-Paper (Msbte Study Resources)Document22 pages22413-2019-Winter-Model-Answer-Paper (Msbte Study Resources)arvi.sardarNo ratings yet
- Summer 22 Model AnsDocument29 pagesSummer 22 Model Ansaniketsarpate786No ratings yet
- ISE Question PapersDocument21 pagesISE Question Papersd.soniNo ratings yet
- 22620-Network and Information Security 241219Document8 pages22620-Network and Information Security 241219darshit rupareliyaNo ratings yet
- Approved Syllabus - 6th Semester (2015-2019)Document14 pagesApproved Syllabus - 6th Semester (2015-2019)MD Rakib HasanNo ratings yet
- Cryptography and System Security: K J Somaiya Institute of Engineering and Information TechnologyDocument11 pagesCryptography and System Security: K J Somaiya Institute of Engineering and Information TechnologyWhatNo ratings yet
- 220244-Data Communication and Computer Network - 22414 - 2023 - Summer Model AnswerDocument21 pages220244-Data Communication and Computer Network - 22414 - 2023 - Summer Model Answerommane312003100% (2)
- Software Eng NotesDocument23 pagesSoftware Eng Notessudarshan badwarNo ratings yet
- Vineet Sharma KeyloggerDocument51 pagesVineet Sharma KeyloggervineetNo ratings yet
- Cyber Riskmgmt AwarenessDocument33 pagesCyber Riskmgmt AwarenessDaniel EsterNo ratings yet
- SEN 22413summer-22-Model-AnsDocument28 pagesSEN 22413summer-22-Model-Ansnvoid7166100% (1)
- CC Certified in Cybersecurity The Complete ISC2 Certification Study GuideFrom EverandCC Certified in Cybersecurity The Complete ISC2 Certification Study GuideNo ratings yet
- DS JetNet4510 V1.3Document12 pagesDS JetNet4510 V1.3Assad ShafiqueNo ratings yet
- (Solutions Guide) Reverse ProxyDocument6 pages(Solutions Guide) Reverse ProxydecorlakeindiaNo ratings yet
- HX-CCD20 People Counter Manual - en - V1.0Document10 pagesHX-CCD20 People Counter Manual - en - V1.0Mafosk8No ratings yet
- Understanding Open Ports in Android Applications: Discovery, Diagnosis, and Security AssessmentDocument14 pagesUnderstanding Open Ports in Android Applications: Discovery, Diagnosis, and Security AssessmentJames CuasmayanNo ratings yet
- Manipulating SIP Headers and Messages in AOSDocument45 pagesManipulating SIP Headers and Messages in AOSabidouNo ratings yet
- Silver Pitch Deck by SlidesgoDocument52 pagesSilver Pitch Deck by SlidesgoCESÉ Samaniego ChNo ratings yet
- Get Access To The Comprehensive Teacher Email List Provided by The Education Data ListsDocument2 pagesGet Access To The Comprehensive Teacher Email List Provided by The Education Data ListsEducation Data ListsNo ratings yet
- Google-Android Basics With Compose Process DocumentDocument45 pagesGoogle-Android Basics With Compose Process DocumentsreedatthapuvvalaNo ratings yet
- Dumpter DrivingDocument7 pagesDumpter Drivingaurox3dNo ratings yet
- Marketing Seminarski RadDocument15 pagesMarketing Seminarski RadMiloš MitrovićNo ratings yet
- TRBOnet Telephony User Guide v5.2Document20 pagesTRBOnet Telephony User Guide v5.2Christian ChavezNo ratings yet
- SOSLITDocument4 pagesSOSLITnoahseth delaguaNo ratings yet
- OOPS in Automation FrameworkDocument3 pagesOOPS in Automation FrameworkSaravanan MuruganNo ratings yet
- Inventario GlassDocument3 pagesInventario GlassLIL EMILUCCINo ratings yet
- Wollega University: College of Engineering and Technology Department of Informatics Program of Computer ScienceDocument77 pagesWollega University: College of Engineering and Technology Department of Informatics Program of Computer ScienceAxl CarbonillaNo ratings yet
- Balon Et Al-2023-Education and Information TechnologiesDocument33 pagesBalon Et Al-2023-Education and Information Technologiesfx_ww2001No ratings yet
- Syllabus For Network Programming PDFDocument1 pageSyllabus For Network Programming PDFMuhammed yashifNo ratings yet
- Allworx Administration Guide 9.1Document422 pagesAllworx Administration Guide 9.1brian browneNo ratings yet
- Mukashifat Ainiyyah - Persian With Urdu TranslationDocument165 pagesMukashifat Ainiyyah - Persian With Urdu TranslationJalalludin Ahmad Ar-Rowi100% (1)
- Gokulan ResumeDocument4 pagesGokulan ResumeyessivaganeshNo ratings yet
- נספח לצו - 1.7.21Document15 pagesנספח לצו - 1.7.21Brock McConnelNo ratings yet
- IQ Option Wiki Portfolio: DealflowDocument35 pagesIQ Option Wiki Portfolio: DealflowErnane Luis PaixãoNo ratings yet
- Comandos Uteis Pentest WebDocument5 pagesComandos Uteis Pentest WebEstaçao Coruja NewsNo ratings yet
- Best Apps To Make Money OnlineDocument6 pagesBest Apps To Make Money OnlineNi Ne33% (3)
- ReadmeDocument25 pagesReadmeRooselvet GalindoNo ratings yet
- Osimis Web Viewer DocumentationDocument15 pagesOsimis Web Viewer DocumentationleandrovaffonsoNo ratings yet
- CV MD - AshikuzzamanDocument2 pagesCV MD - AshikuzzamanrazzakNo ratings yet
- KaliDocument10 pagesKalikarthik hcNo ratings yet
- HD Webcam c615 GSWDocument112 pagesHD Webcam c615 GSWStanislavaGavrilovicNo ratings yet
Diploma 6th Sem Model Answer Paper. 22620 - Diploma 6th Sem Model Answer Paper
Diploma 6th Sem Model Answer Paper. 22620 - Diploma 6th Sem Model Answer Paper
Uploaded by
Vishnu MaskarOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Diploma 6th Sem Model Answer Paper. 22620 - Diploma 6th Sem Model Answer Paper
Diploma 6th Sem Model Answer Paper. 22620 - Diploma 6th Sem Model Answer Paper
Uploaded by
Vishnu MaskarCopyright:
Available Formats
lOMoARcPSD|39849591
22620 - Diploma 6th sem model answer paper.
Information Technology (Maharashtra State Board of Technical Education)
Scan to open on Studocu
Studocu is not sponsored or endorsed by any college or university
Downloaded by Satyam Maurya (satyammaurya1409@gmail.com)
lOMoARcPSD|39849591
MAHARASHTRA STATE BOARD OF TECHNICAL EDUCATION
(Autonomous)
(ISO/IEC - 27001 - 2005 Certified)
SUMMER – 2023 EXAMINATION
MODEL ANSWER-Only for the Use of RAC Assessors
Subject: Network and Information Security Subject Code: 22620
Important Instructions to examiners:
1) The answers should be examined by key words and not as word-to-word as given in the
model answer scheme.
2) The model answer and the answer written by candidate may vary but the examiner may
try to assess the understanding level of the candidate.
3) The language errors such as grammatical, spelling errors should not be given more
Importance (Not applicable for subject English and Communication Skills.
4) While assessing figures, examiner may give credit for principal components indicated in
the figure. The figures drawn by candidate and model answer may vary. The examiner
may give credit for anyequivalent figure drawn.
5) Credits may be given step wise for numerical problems. In some cases, the assumed
constant values may vary and there may be some difference in the candidate’s answers
and model answer.
6) In case of some questions credit may be given by judgement on part of examiner of
relevant answer based on candidate’s understanding.
7) For programming language papers, credit may be given to any other program based on
equivalent concept.
8) As per the policy decision of Maharashtra State Government, teaching in English/Marathi
and Bilingual (English + Marathi) medium is introduced at first year of AICTE diploma
Programme from academic year 2021-2022. Hence if the students in first year (first and
second semesters) write answers in Marathi or bilingual language (English +Marathi), the
Examiner shall consider the same and assess the answer based on matching of concepts
with model answer.
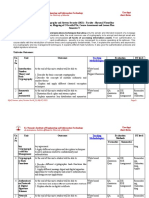
Q. Sub Answer Marking
No Q.N. Scheme
1. Attempt any FIVE of the following 10M
a) Compare virus and logic bomb (any two points) 2M
Ans. virus Logic bomb Any two
Virus is a program which A logic bomb is a set of points 1M
each
attaches itself to another instructions in a program
program and causes damage carrying a malicious payload
to the computer system or the that can attack an operating
network. It is loaded onto system, program, or network.
your computer without your It only goes off after certain
knowledge and runs against conditions are met. A simple
your wishes example of these conditions
is a specific date or time.
Characteristic of a virus is, Characteristic of a logic
How it spread. bomb is, how it's triggered.
Page 1 / 25
Downloaded by Satyam Maurya (satyammaurya1409@gmail.com)
lOMoARcPSD|39849591
MAHARASHTRA STATE BOARD OF TECHNICAL EDUCATION
(Autonomous)
(ISO/IEC - 27001 - 2005 Certified)
SUMMER – 2023 EXAMINATION
MODEL ANSWER-Only for the Use of RAC Assessors
Subject: Network and Information Security Subject Code: 22620
b) Identify any four user responsibility in computer security. 2M
Ans. i) Do not share passwords, OTP etc to anyone. Any four
ii) Do not leave sensitive information unprotected. points
1/2M each
iii) Secure storage media which contains sensitive information.
iv) Shredding paper containing organizational information before
discarding it.
c) Define following terms 2M
(i) Cryptography
(ii) Cryptology. Definition
Ans. Cryptography: Cryptography is the art and science of achieving of
Each term
security by encoding messages to make them non-readable. 1M
Cryptology: It is the art and science of transforming the intelligent
data into unintelligent data and unintelligent data back to intelligent
data.
Cryptology = Cryptography + Cryptanalysis
d) Construct digital signature using cryptool. 2M
Ans. Step 1: Open Cryptool application. Correct
Step 2: Open the file and enter message to create digital signature. steps 2M
Step 3: Select menu Digital signature -> Sign Document
Step 4: Select any Hash function and choose private key.
Step 5: Enter PIN number and Click on Sign button to generate
digital signature.
e) List any two types of active and passive attacks 2M
Ans. Active Attack: Any two
Masquerade active
attacks
Replay 1M,
Message Modification
Denial-Of-Service Any two
passive
attacks 1M
Passive Attack:
Eavesdropping
Traffic Analysis
Page 2 / 25
Downloaded by Satyam Maurya (satyammaurya1409@gmail.com)
lOMoARcPSD|39849591
MAHARASHTRA STATE BOARD OF TECHNICAL EDUCATION
(Autonomous)
(ISO/IEC - 27001 - 2005 Certified)
SUMMER – 2023 EXAMINATION
MODEL ANSWER-Only for the Use of RAC Assessors
Subject: Network and Information Security Subject Code: 22620
f) State any two policies of the firewall 2M
Ans. Service control: Determines the types of Internet services that can
Any two
be accessed, inbound or outbound. The firewall may filter traffic policies 2M
on the basis of IP address, protocol, or port number; may provide
proxy software that receives and interprets each service request
before passing it on; or may host the server software itself, such as
a Web or mail service.
Direction control: Determines the direction in which particular
service requests may be initiated and allowed to flow through the
firewall.
User control: Controls access to a service according to which user
is attempting to access it. This feature is typically applied to users
inside the firewall perimeter (local users).
Behavior control: Controls how particular services are used. For
example, the firewall may filter e-mail to eliminate spam, or it may
enable external access to only a portion of the information on a
local Web server.
g) List any types of cybercrimes 2M
Ans. Types of cyber crime :- Any four
1. Hacking types 1/2M
each
2. Digital Forgery
3. Cyber Stalking / Harassment
4. Cyber Pornography
5. Identity Theft and Fraud
6. Cyber Terrorism
7. Cyber Defamation
2. Attempt any THREE of the following: 12M
a) Describe CIA model with suitable diagram. 4M
Ans. 1. Confidentiality: the principle of confidentiality specifies that only
Explanatio
sender and intended recipients should be able to access the contents n with
of a message. Confidentiality gets compromised if an unauthorized diagram
4M
person is able to access the contents of a message. Example of
compromising the Confidentiality of a message is shown in fig.
Page 3 / 25
Downloaded by Satyam Maurya (satyammaurya1409@gmail.com)
lOMoARcPSD|39849591
MAHARASHTRA STATE BOARD OF TECHNICAL EDUCATION
(Autonomous)
(ISO/IEC - 27001 - 2005 Certified)
SUMMER – 2023 EXAMINATION
MODEL ANSWER-Only for the Use of RAC Assessors
Subject: Network and Information Security Subject Code: 22620
Fig. Loss of confidentiality
Here, the user of a computer A send a message to user of computer B.
another user C gets access to this message, which is not desired and
therefore, defeats the purpose of Confidentiality. This type of attack
is also called as interception
2. Authentication: Authentication helps to establish proof of
identities. The Authentication process ensures that the origin of a
message is correctly identified. For example, suppose that user C
sends a message over the internet to user B. however, the trouble is
that user C had posed as user A when he sent a message to user B.
how would user B know that the message has come from user C, who
posing as user A? This concept is shown in fig. below. This type of
attack is called as fabrication.
Fig. absence of authentication
3. Integrity: when the contents of the message are changed after the
sender sends it, but before it reaches the intended recipient, we say
that the integrity of the message is lost. For example, here user C
tampers with a message originally sent by user A, which is actually
destined for user B. user C somehow manages to access it, change its
contents and send the changed message to user B. user B has no way
of knowing that the contents of the message were changed after user
A had sent it. User A also does not know about this change. This type
of attack is called as modification.
Page 4 / 25
Downloaded by Satyam Maurya (satyammaurya1409@gmail.com)
lOMoARcPSD|39849591
MAHARASHTRA STATE BOARD OF TECHNICAL EDUCATION
(Autonomous)
(ISO/IEC - 27001 - 2005 Certified)
SUMMER – 2023 EXAMINATION
MODEL ANSWER-Only for the Use of RAC Assessors
Subject: Network and Information Security Subject Code: 22620
Fig. Loss of Integrity
b) Define the following with suitable example 4M
i) DAC
Definition
ii) MAC with
i) DAC: DAC (discretionary access control) policy utilizes user example of
Ans. DAC 2M
identification procedures to identify and restrict object access .It
restricts access to objects based on the identity of subjects and or
groups to which they belongs to. The owner of information or any
resource is able to change its permissions at his discretion .Data
Owners can transfer ownership of information to other users .Data
Owners can determine the type of access given to other users (read,
write etc.)
Features of DAC policy are as follows :-
Flexible –In DAC policy owner of information or resource can
change its permission.
Backup - Discretionary access control allows organizations to
backup security policies and data to ensure effective access points.
Usability - Discretionary access control is easy to use. Data Owners
can transfer ownership of information to other users easily.
Definition
ii) MAC :It is used in environments where different levels of security with
are classified. It is much more restrictive. It is sensitivity based example of
MAC 2M
restriction, formal authorization subject to sensitivity. In MAC the
owner or User cannot determine whether access is granted to or not.
i.e. Operating system rights. Security mechanism controls access to
all objects and individual cannot change that access.
Page 5 / 25
Downloaded by Satyam Maurya (satyammaurya1409@gmail.com)
lOMoARcPSD|39849591
MAHARASHTRA STATE BOARD OF TECHNICAL EDUCATION
(Autonomous)
(ISO/IEC - 27001 - 2005 Certified)
SUMMER – 2023 EXAMINATION
MODEL ANSWER-Only for the Use of RAC Assessors
Subject: Network and Information Security Subject Code: 22620
c) Differentiate between symmetric and asymmetric key 4M
cryptography (any four points)
Ans. Any four
points 1M
each
d) Explain Steganography with suitable example. 4M
Ans. Steganography: Steganography is the art and science of writing
hidden message in such a way that no one apart from sender and Correct
explanatio
intended recipient suspects the existence of the message. n with
Steganography works by replacing bits of useless or unused data in suitable
example
regular computer files (such as graphics, sound, text, html or even
4M
floppy disks) with bits of different, invisible information. This hidden
information can be plain text, cipher text or even images. In modern
steganography, data is first encrypted by the usual means and then
inserted, using a special algorithm, into redundant data that is part of
a particular file format such as a JPEG image.
Steganography process:
Cover-media + Hidden data + Stego-key = Stego-medium
Fig : Steganography
Page 6 / 25
Downloaded by Satyam Maurya (satyammaurya1409@gmail.com)
lOMoARcPSD|39849591
MAHARASHTRA STATE BOARD OF TECHNICAL EDUCATION
(Autonomous)
(ISO/IEC - 27001 - 2005 Certified)
SUMMER – 2023 EXAMINATION
MODEL ANSWER-Only for the Use of RAC Assessors
Subject: Network and Information Security Subject Code: 22620
Cover media is the file in which we will hide the hidden data, which
may also be encrypted using stego-key. The resultant file is stego-
medium. Cover-media can be image or audio file. Stenography takes
cryptography a step further by hiding an encrypted message so that
no one suspects it exists. Ideally, anyone scanning your data will fail
to know it contains encrypted data. Stenography has a number of
drawbacks when compared to encryption. It requires a lot of overhead
to hide a relatively few bits of information. I.e. One can hide text,
data, image, sound, and video, behind image.
Applications :
1. Confidential communication and secret data storing
2. Protection of data alteration
3. Access control system for digital content distribution
4. Media Database systems
3. Attempt any THREE of the following 12M
a) Describe piggy backing and shoulder surfing 4M
Ans. Piggybacking: It is the simple process of following closely behind a
Descriptio
person who has just used their own access card or PIN to gain n of piggy
physical access to a room or building. An attacker can thus gain backing
access to the facility without having to know the access code or 2M
having to acquire an access card. i.e. Access of wireless internet
connection by bringing one's own computer within range of another
wireless connection & using that without explicit permission, it
means when an authorized person allows (intentionally or
unintentionally) others to pass through a secure door. Piggybacking
on Internet access is the practice of establishing a wireless Internet
connection by using another subscriber's wireless Internet access
service without the subscriber’s explicit permission or knowledge.
Piggybacking is sometimes referred to as "Wi-Fi squatting." The
usual purpose of piggybacking is simply to gain free network access
rather than any malicious intent, but it can slow down data transfer
for legitimate users of the network.
Page 7 / 25
Downloaded by Satyam Maurya (satyammaurya1409@gmail.com)
lOMoARcPSD|39849591
MAHARASHTRA STATE BOARD OF TECHNICAL EDUCATION
(Autonomous)
(ISO/IEC - 27001 - 2005 Certified)
SUMMER – 2023 EXAMINATION
MODEL ANSWER-Only for the Use of RAC Assessors
Subject: Network and Information Security Subject Code: 22620
Shoulder surfing: Shoulder surfing a similar procedure in which
Descriptio
attackers position themselves in such a way as to- be-able to observe n of
the authorized user entering the correct access code. Shoulder surfing shoulder
is an effective way to get information in crowded places because it's surfing
2M
relatively easy to stand next to someone and watch as they fill out a
form, enter a PIN number at an ATM machine, or use a calling card
at a public pay phone. Shoulder surfing can also be done long
distance with the aid of binoculars or other vision enhancing devices.
Shoulder surfing is using direct observation techniques, such as
looking over someone's shoulder, to get information.
b) Convert plain text into cipher text by using single columnar 4M
technique of the following sentence:
―Maharashtra State board of Technical Education‖ 2M for
plain text
Ans. 1 2 3 4 5 table
M A H A R
2M for
A S T R A cipher text
S T A T E
B O A R D
O F T E C
H N I C A
L E D U C
A T I O N
PLAIN TEXT:
MAHARASTRA STATE BOARD OF TECHNICAL EDUCATION
LET ORDER BE:4,5,3,2,1
CIPHER
TEXT:ARTRECUORAEDCACNHTAATIDIASTOFNETMASBOH
LA
Note: Any relevant order shall be considered.
Page 8 / 25
Downloaded by Satyam Maurya (satyammaurya1409@gmail.com)
lOMoARcPSD|39849591
MAHARASHTRA STATE BOARD OF TECHNICAL EDUCATION
(Autonomous)
(ISO/IEC - 27001 - 2005 Certified)
SUMMER – 2023 EXAMINATION
MODEL ANSWER-Only for the Use of RAC Assessors
Subject: Network and Information Security Subject Code: 22620
c) State any four difference between Firewall and Intrusion 4M
Detection System
Ans.
Any four
differences
1M each
d) Describe any four password selection criteria. 4M
Ans. Password: Password is a secret word or expression used by Any four
criteria’s
authorized persons to prove their right to access, information, etc. 1M each
Components of good password:
1. It should be at least eight characters long.
2. It should include uppercase and lowercase letters, numbers, special
characters or punctuation marks.
3. It should not contain dictionary words.
4. It should not contain the user's personal information such as their
name, family member's name, birth date, pet name, phone number or
any other detail that can easily be identified.
5. It should not be the same as the user's login name.
6. It should not be the default passwords as supplied by the system
vendor such as password, guest, and admin and so on.
Page 9 / 25
Downloaded by Satyam Maurya (satyammaurya1409@gmail.com)
lOMoARcPSD|39849591
MAHARASHTRA STATE BOARD OF TECHNICAL EDUCATION
(Autonomous)
(ISO/IEC - 27001 - 2005 Certified)
SUMMER – 2023 EXAMINATION
MODEL ANSWER-Only for the Use of RAC Assessors
Subject: Network and Information Security Subject Code: 22620
4. Attempt any THREE of the following 12M
a) Convert the given plain text, encrypt it with the help of Caesor‟s 4M
cipher technique.
“Network and Information Security”. 2M for
plain text
Ans. table
2M for
Caesor’s
cipher
technique
PLAIN TEXT: NETWORK AND INFORMATION SECURITY
CIPHER TEXT:QHWZRUNDQGLQIRUPDWLRQVHFXULWB
b) Demonstrate configuration of Firewall setting windows operating 4M
system.
Ans. Correct
A firewall is a device which monitors and filters all the incoming and explanatio
outgoing network traffic and prevents unauthorized access to/within n 4M
the network. The firewall is the most important line of defense in
maintaining the security of the network and the application. Every
firewall has a set of rules predefined to allow type of data within the
network; accordingly, it allows or denies the incoming traffic within
the network.
Configuring firewalls on Windows 10
Since Windows is widely used at personal level, this article has been
written specifically for configuring firewalls on Windows.
These are the steps for opening any specific port on the Windows 10
firewall:
1) Search ―firewall‖ and click on Windows Defender Firewall, as
shown below:
Page 10 / 25
Downloaded by Satyam Maurya (satyammaurya1409@gmail.com)
lOMoARcPSD|39849591
MAHARASHTRA STATE BOARD OF TECHNICAL EDUCATION
(Autonomous)
(ISO/IEC - 27001 - 2005 Certified)
SUMMER – 2023 EXAMINATION
MODEL ANSWER-Only for the Use of RAC Assessors
Subject: Network and Information Security Subject Code: 22620
2) Click on Inbound Rules, as shown.
3) Click on New Rule, select port and click Next as shown:
Page 11 / 25
Downloaded by Satyam Maurya (satyammaurya1409@gmail.com)
lOMoARcPSD|39849591
MAHARASHTRA STATE BOARD OF TECHNICAL EDUCATION
(Autonomous)
(ISO/IEC - 27001 - 2005 Certified)
SUMMER – 2023 EXAMINATION
MODEL ANSWER-Only for the Use of RAC Assessors
Subject: Network and Information Security Subject Code: 22620
4) Enter a specific port number. In this case, it’s 443. Click Next.
Page 12 / 25
Downloaded by Satyam Maurya (satyammaurya1409@gmail.com)
lOMoARcPSD|39849591
MAHARASHTRA STATE BOARD OF TECHNICAL EDUCATION
(Autonomous)
(ISO/IEC - 27001 - 2005 Certified)
SUMMER – 2023 EXAMINATION
MODEL ANSWER-Only for the Use of RAC Assessors
Subject: Network and Information Security Subject Code: 22620
5) Allow or block the connection as needed.
6) Name the rule and description as needed.
7) The same steps need to be followed for allowing outbound
connection. In step 1, instead of selecting Inbound Rules, select
Outbound Rules and follow the same steps as above.
That’s easy it is to configure to allow or deny any connection for a
particular port on Windows 10.
Page 13 / 25
Downloaded by Satyam Maurya (satyammaurya1409@gmail.com)
lOMoARcPSD|39849591
MAHARASHTRA STATE BOARD OF TECHNICAL EDUCATION
(Autonomous)
(ISO/IEC - 27001 - 2005 Certified)
SUMMER – 2023 EXAMINATION
MODEL ANSWER-Only for the Use of RAC Assessors
Subject: Network and Information Security Subject Code: 22620
c) Describe DMZ with suitable diagram. 4M
Ans. DMZ (Demilitarized Zone): It is a computer host or small network
inserted as a ―neutral zone‖ in a company‟s private network and the Explanatio
outside public network. It avoids outside users from getting direct n 2M
access to a company‟s data server. A DMZ is an optional but more
secure approach to a firewall. It can effectively acts as a proxy server.
Diagram
The typical DMZ configuration has a separate computer or host in 2M
network which receives requests from users within the private
network to access a web sites or public network. Then DMZ host
initiates sessions for such requests on the public network but it is not
able to initiate a session back into the private network. It can only
forward packets which have been requested by a host. The public
network‟s users who are outside the company can access only the
DMZ host. It can store the company‟s web pages which can be
served to the outside users. Hence, the DMZ can‟t give access to the
other company‟s data. By any way, if an outsider penetrates the
DMZ‟s security the web pages may get corrupted but other
company‟s information can be safe.
d) Describe PGP with suitable diagram. 4M
Ans. PGP is Pretty Good Privacy. It is a popular program used to encrypt
and decrypt email over the internet. It becomes a standard for email Explanatio
n 2M
security. It is used to send encrypted code (digital signature) that lets
the receiver verify the sender’s identity and takes care that the route
of message should not change. PGP can be used to encrypt files being
stored so that they are in unreadable form and not readable by users
or intruders It is available in Low cost and Freeware version. It is
Page 14 / 25
Downloaded by Satyam Maurya (satyammaurya1409@gmail.com)
lOMoARcPSD|39849591
MAHARASHTRA STATE BOARD OF TECHNICAL EDUCATION
(Autonomous)
(ISO/IEC - 27001 - 2005 Certified)
SUMMER – 2023 EXAMINATION
MODEL ANSWER-Only for the Use of RAC Assessors
Subject: Network and Information Security Subject Code: 22620
most widely used privacy ensuring program used by individuals as
well as many corporations.
Diagram
2M
There are five steps as shown below:
1. Digital signature: it consists of the creation a message digest of the
email message using SHA-1 algorithm. The resulting MD is then
encrypted with the sender’s private key. The result is the sender’s
digital signature.
2. Compression: The input message as well as p digital signature are
compressed together to reduce the size of final message that will be
transmitted. For this the Lempel -Ziv algorithm is used.
3. Encryption: The compressed output of step 2 (i.e. the compressed
form of the original email and the digital signature together) are
encrypted with a symmetric key.
4. Digital enveloping: the symmetric key used for encryption in step 3
is now encrypted with the receiver’s public key. The output of step 3
and 4 together form a digital envelope.
5. Base -64 encoding: this process transforms arbitrary binary input
into printable character output. The binary input is processed in
blocks of 3 octets (24-bits).these 24 bits are considered to be made up
of 4 sets, each of 6 bits. Each such set of 6 bits is mapped into an 8-
bit output character in this process.
e) Find the output of initial permutation box when the input is given 4M
in hexadecimal as
0 x 0003 0000 0000 0001
Page 15 / 25
Downloaded by Satyam Maurya (satyammaurya1409@gmail.com)
lOMoARcPSD|39849591
MAHARASHTRA STATE BOARD OF TECHNICAL EDUCATION
(Autonomous)
(ISO/IEC - 27001 - 2005 Certified)
SUMMER – 2023 EXAMINATION
MODEL ANSWER-Only for the Use of RAC Assessors
Subject: Network and Information Security Subject Code: 22620
Ans.
0 0 0 3 Hexadecimal
0000 0000 0000 0011 Binary
Correct
0 0 0 0 Hexadecimal output 4M
0000 0000 0000 0000 Binary
0 0 0 0 Hexadecimal
0000 0000 0000 0000 Binary
0 0 0 1 Hexadecimal
0000 0000 0000 0001 Binary
Input
1 2 3 4 5 6
1 0 0 0 0 0 0
2 0 0 0 0 0 0
3 0 0 0 0 0 0
4 0 0 0 0 0 0
5 0 0 0 0 0 0
6 0 0 0 0 0 0
7 0 0 0 0 0 0
8 0 0 0 0 0 0
Permutation table
1 2 3 4 5 6
1 58 50 42 34 26 18
2 60 52 44 36 28 20
3 62 54 46 38 30 22
4 64 56 48 40 32 24
5 57 49 41 33 25 17
6 59 51 43 35 27 19
7 61 53 45 37 29 21
8 63 55 47 39 31 23
Page 16 / 25
Downloaded by Satyam Maurya (satyammaurya1409@gmail.com)
lOMoARcPSD|39849591
MAHARASHTRA STATE BOARD OF TECHNICAL EDUCATION
(Autonomous)
(ISO/IEC - 27001 - 2005 Certified)
SUMMER – 2023 EXAMINATION
MODEL ANSWER-Only for the Use of RAC Assessors
Subject: Network and Information Security Subject Code: 22620
Output
1 2 3 4 5 6
1 0 0 0 0 0 0
2 0 0 0 0 0 0
3 0 0 0 0 0 0
4 1 0 0 0 0 0
5 0 0 0 0 0 0
6 0 0 0 0 0 0
7 0 0 0 0 0 0
8 0 0 0 0 0 0
Hexadecimal
0000 0082 0000 0002
Note: Any other relevant logic shall be considered.
5. Attempt any TWO of the following 12M
a) Describe the following terms 6M
i) Asset
ii) Vulnerability
iii) Risks
Ans. i) Asset: Asset is any data, device, or other component of the
environment that supports information-related activities. Assets
Descriptio
generally include hardware, software and confidential information. n of each
term 2M
ii) Vulnerability: It is a weakness in computer system & network.
The term "vulnerability" refers to the security flaws in a system that
allows an attack to be successful. Vulnerability testing should be
performed on an on-going basis by the parties responsible for
resolving such vulnerabilities, and helps to provide data used to
identify unexpected dangers to security that need to be addressed.
Such vulnerabilities are not particular to technology — they can also
apply to social factors such as individual authentication and
authorization policies.
iii) Risks: Risk is probability of threats that may occur because of
presence of vulnerability in a system.
Page 17 / 25
Downloaded by Satyam Maurya (satyammaurya1409@gmail.com)
lOMoARcPSD|39849591
MAHARASHTRA STATE BOARD OF TECHNICAL EDUCATION
(Autonomous)
(ISO/IEC - 27001 - 2005 Certified)
SUMMER – 2023 EXAMINATION
MODEL ANSWER-Only for the Use of RAC Assessors
Subject: Network and Information Security Subject Code: 22620
OR
Risk is any event or action that could cause a loss or damage to
computer hardware, software, data, or information.
b) Describe network base IDS with suitable diagram 6M
Ans.
Diagram
2M
1. Network-based IDS focuses on network traffic —the bits & bytes
Explanatio
traveling along the cables & wires that interconnect the system. n 4M
2. A network IDS should check the network traffic when it passes &
it is able to analyse traffic according to protocol type, amount, source,
destination, content, traffic already seen etc.
3. Such an analysis must occur quickly, &the IDS must be able to
handle traffic at any speed the network operates on to be effective.
4. Network-based IDSs are generally deployed so that they can
monitor traffic in &out of an organization’s major links like
connection to the Internet, remote offices, partner etc.
Network-based IDSs looks for certain activities like:
Denial of service attacks
Port scans or sweeps
Malicious content in the data payload of a packet or packets
Vulnerability scanning Trojans, viruses, or worms
Tunneling
Brute-force attacks
OR
1. Traffic collector: This component collects activity or events from
the IDS to examine. On Host-based IDS, this can be log files, audit
logs, or traffic coming to or leaving a specific system. On Network-
based IDS, this is typically a mechanism for copying traffic of the
network link.
Page 18 / 25
Downloaded by Satyam Maurya (satyammaurya1409@gmail.com)
lOMoARcPSD|39849591
MAHARASHTRA STATE BOARD OF TECHNICAL EDUCATION
(Autonomous)
(ISO/IEC - 27001 - 2005 Certified)
SUMMER – 2023 EXAMINATION
MODEL ANSWER-Only for the Use of RAC Assessors
Subject: Network and Information Security Subject Code: 22620
2. Analysis Engine: This component examines the collected network
traffic & compares it to known patterns of suspicious or malicious
activity stored in the signature database. The analysis engine acts like
a brain of the IDS.
3. Signature database: It is a collection of patterns & definitions of
known suspicious or malicious activity.
4. User Interface & Reporting: This is the component that interfaces
with the human element, providing alerts when suitable & giving the
user a means to interact with & operate the IDS.
Advantages:
O.S specific and detailed signatures.
Examine data after it has been decrypted.
Very application specific.
Determine whether or not an alarm may impact that specific.
Disadvantages:
Should a process on every system to watch.
High cost of ownership and maintenance.
Uses local system resources.
If logged locally, could be compromised or disable.
c) Describe COBIT framework with neat diagram 6M
Ans.
Diagram
2M
COBIT stands for ―Control Objectives for Information and related Explanatio
Technology‖, it is a framework that was developed by ISACA n 4M
(Information System Audit and Control Association). It is a set of
guidance material for IT governance to manage their requirements,
technical issues, and business risks.
Page 19 / 25
Downloaded by Satyam Maurya (satyammaurya1409@gmail.com)
lOMoARcPSD|39849591
MAHARASHTRA STATE BOARD OF TECHNICAL EDUCATION
(Autonomous)
(ISO/IEC - 27001 - 2005 Certified)
SUMMER – 2023 EXAMINATION
MODEL ANSWER-Only for the Use of RAC Assessors
Subject: Network and Information Security Subject Code: 22620
COBIT connects IT initiatives with business requirements, monitors
and improves IT management practices, and ensures quality control
and reliability of information systems in an organization.
Plan and Organize: This domain addresses direction to solutions,
Information architecture, managing IT investments, assess the
risks, quality, and project.
Acquire and Implement: This domain acquires and maintains
application software and technology infrastructure, develops as
well as maintains procedures and manages changes, implements
desired solutions and passes them to be turned into services.
Deliver and Support: This domain defines and manages service
levels, ensures the security of the system, educates or trains, and
advises users. It receives solutions and makes them usable for end
users.
Monitor and Evaluate: This domain monitors the process, assesses
internal control capability, finds independent assurance, and
provides independent audit.
Principle of COBIT:
Providing service of delivering information that an organization
requires.
Undesired events will be prevented, detected, and corrected.
Managing and controlling IT resources using a structured set of
processes.
Fulfilling client’s requirements.
Note: Any other relevant framework shall be considered
6. Attempt any TWO of the following 12M
a) Describe any three phases of virus with suitable example 6M
Ans. Definition: Virus is a program which attaches itself to another
program and causes damage to the computer system or the network. It Any three
Phases 3M
is loaded onto your computer without your knowledge and runs
against your wishes. Suitable
During the lifecycle of virus it goes through the following four example
phases: 3M
Page 20 / 25
Downloaded by Satyam Maurya (satyammaurya1409@gmail.com)
lOMoARcPSD|39849591
MAHARASHTRA STATE BOARD OF TECHNICAL EDUCATION
(Autonomous)
(ISO/IEC - 27001 - 2005 Certified)
SUMMER – 2023 EXAMINATION
MODEL ANSWER-Only for the Use of RAC Assessors
Subject: Network and Information Security Subject Code: 22620
1. Dormant phase: The virus is idle and activated by some event.
2. Propagation phase: It places an identical copy of itself into
other programs or into certain system areas on the disk.
3. Triggering phase: The virus is activated to perform the function
for which it was intended.
4. Execution phase: The function of virus is performed
Note: Any other relevant example shall be considered
b) Describe „ Kerberos‟ protocol with suitable diagram 6M
Ans. Kerberos: Kerberos is a network authentication protocol. It is
designed to provide strong authentication for client/server
applications by using secret-key cryptography. It uses secret key Descriptio
cryptography. It is a solution to network security problems. It n with
provides tools for authentication and strong cryptography over the suitable
network to help you secure your information system There are 4 diagram of
parties involved in Kerberos protocol Authentica
tion service
i) User (AS)
ii) Authentication service (AS) 3M
iii) Ticket granting server (TGS)
iv) Service server
Working of Kerberos: Descriptio
n with
1. The authentication service, or AS, receivers the request by the suitable
client and verifies that the client is indeed the computer it claims to diagram of
be. This is usually just a simple database lookup of the user’s ID. Ticket
granting
server
(TGS)
3M
Page 21 / 25
Downloaded by Satyam Maurya (satyammaurya1409@gmail.com)
lOMoARcPSD|39849591
MAHARASHTRA STATE BOARD OF TECHNICAL EDUCATION
(Autonomous)
(ISO/IEC - 27001 - 2005 Certified)
SUMMER – 2023 EXAMINATION
MODEL ANSWER-Only for the Use of RAC Assessors
Subject: Network and Information Security Subject Code: 22620
2. Upon verification, a timestamp is created. This puts the current
time in a user session, along with an expiration date. The default
expiration date of a timestamp is 8 hours. The encryption key is then
created. The timestamp ensures that when 8 hours is up, the
encryption key is useless.
3. The key is sent back to the client in the form of a ticket-granting
ticket, or TGT. This is a simple ticket that is issued by the
authentication service. It is used for authentication the client for
future reference.
1. The client submits the ticket-granting ticket to the ticket-granting
server, or TGS, to get authenticated.
2. The TGS creates an encrypted key with a timestamp, and grants the
client a service ticket.
3. The client decrypts the ticket, tells the TGS it has done so, and then
sends its own encrypted key to the service.
Page 22 / 25
Downloaded by Satyam Maurya (satyammaurya1409@gmail.com)
lOMoARcPSD|39849591
MAHARASHTRA STATE BOARD OF TECHNICAL EDUCATION
(Autonomous)
(ISO/IEC - 27001 - 2005 Certified)
SUMMER – 2023 EXAMINATION
MODEL ANSWER-Only for the Use of RAC Assessors
Subject: Network and Information Security Subject Code: 22620
4. The service decrypts the key, and makes sure the timestamp is still
valid. If it is, the service contacts the key distribution center to
receive a session that is returned to the client.
5. The client decrypts the ticket. If the keys are still valid,
communication is initiated between client and server.
c) Write a brief note on firewall configuration 6M
i) Packet filter as a firewall
ii) Application level gateway firewall
iii) Circuit level gateway firewall Explanatio
Ans. n with
1. Packet filter as a firewall : As per the diagram given below diagram
Firewall will act according to the table given for example source IP 2M
150.150.0.0 is the IP address of a network , all the packets which are each
coming from this network will be blocked by the firewall in this way
it is acting as a firewall. Table also having port 80, IP Address
200.75.10.8 & port 23 firewall will act in the similar fashion. Port 23
is for Telnet remote login in this case firewall won’t allow to login
onto this server. IP Address 200.75.10.8 is the IP address of
individual Host, all the packet having this IP address as a destination
Address will be denied. Port 80 no HTTP request allowed by firewall
Page 23 / 25
Downloaded by Satyam Maurya (satyammaurya1409@gmail.com)
lOMoARcPSD|39849591
MAHARASHTRA STATE BOARD OF TECHNICAL EDUCATION
(Autonomous)
(ISO/IEC - 27001 - 2005 Certified)
SUMMER – 2023 EXAMINATION
MODEL ANSWER-Only for the Use of RAC Assessors
Subject: Network and Information Security Subject Code: 22620
2. Application level gateway Firewalls: Application level firewalls
decide whether to drop a packet or send them through based on the
application information (available in the packet). They do this by
setting up various proxies on a single firewall for different
applications. Both the client and the server connect to these proxies
instead of connecting directly to each other. So, any suspicious data
or connections are dropped by these proxies. Application level
firewalls ensure protocol conformance. For example, attacks over http
that violates the protocol policies like sending Non-ASCII data in the
header fields or overly long string along with Non ASCII characters
in the host field would be dropped because they have been tampered
with, by the intruders.
Page 24 / 25
Downloaded by Satyam Maurya (satyammaurya1409@gmail.com)
lOMoARcPSD|39849591
MAHARASHTRA STATE BOARD OF TECHNICAL EDUCATION
(Autonomous)
(ISO/IEC - 27001 - 2005 Certified)
SUMMER – 2023 EXAMINATION
MODEL ANSWER-Only for the Use of RAC Assessors
Subject: Network and Information Security Subject Code: 22620
3. Circuit level gateway Firewalls: The circuit level gateway firewalls
work at the session layer of the OSI model. They monitor TCP handshaking
between the packets to determine if a requested session is legitimate. And
the information passed through a circuit level gateway, to the internet,
appears to have come from the circuit level gateway. So, there is no way for
a remote computer or a host to determine the internal private ip addresses of
an organization, for example. This technique is also called Network Address
Translation where the private IP addresses originating from the different
clients inside the network are all mapped to the public IP address available
through the internet service provider and then sent to the outside world
(Internet). This way, the packets are tagged with only the Public IP address
(Firewall level) and the internal private IP addresses are not exposed to
potential intruders
Page 25 / 25
Downloaded by Satyam Maurya (satyammaurya1409@gmail.com)
You might also like
- Ansible Hands OnDocument8 pagesAnsible Hands Onu952No ratings yet
- Diploma 6th Sem Model Answer PaperDocument26 pagesDiploma 6th Sem Model Answer Paperommane31200375% (4)
- S23 Model SolutionDocument25 pagesS23 Model Solutiontanupandav333No ratings yet
- NIS Model Answer 2022Document28 pagesNIS Model Answer 2022Rishi100% (13)
- Modelans W g22Document28 pagesModelans W g22ommane312003No ratings yet
- 17514-2019-Winter-Model-Answer-Paper (Msbte Study Resources)Document29 pages17514-2019-Winter-Model-Answer-Paper (Msbte Study Resources)aryasurve1210No ratings yet
- Ans W 22 NisDocument28 pagesAns W 22 NisCo- 65 Madhukanth PoojaryNo ratings yet
- NIS Winter 2022Document27 pagesNIS Winter 2022aniket100% (1)
- Nis 22620 Sample Papers S-22, w22, s23Document81 pagesNis 22620 Sample Papers S-22, w22, s23Rutuja ShindeNo ratings yet
- Winter Nis Model Ans 2022Document28 pagesWinter Nis Model Ans 2022AloneNo ratings yet
- Nis S-22Document28 pagesNis S-2251 IF Nilesh sabaleNo ratings yet
- Winter Nis Model Ans 2022Document28 pagesWinter Nis Model Ans 2022Pranit ShitoleNo ratings yet
- Important Instructions To Examiners:: What Is Computer Security & Its Need?Document40 pagesImportant Instructions To Examiners:: What Is Computer Security & Its Need?Gaurang NakumNo ratings yet
- S23 CND 22634Document27 pagesS23 CND 22634harshy0816100% (1)
- Ans W 22 NisDocument28 pagesAns W 22 NisbsjssbjdNo ratings yet
- 2016 Summer Model Answer Paper PDFDocument31 pages2016 Summer Model Answer Paper PDFMahesh DahiwalNo ratings yet
- S 2023 22414Document22 pagesS 2023 22414vinay.niranjan006No ratings yet
- 2015 Summer Model Answer Paper PDFDocument49 pages2015 Summer Model Answer Paper PDFMahesh DahiwalNo ratings yet
- Unit 2 - MCQDocument37 pagesUnit 2 - MCQShubham TayadeNo ratings yet
- Assignment Cyber Security Principles 600 ASS 2Document3 pagesAssignment Cyber Security Principles 600 ASS 2Saieesh RamgobinNo ratings yet
- 420240-DCC w23, s23, w22, s22, w19, s19Document148 pages420240-DCC w23, s23, w22, s22, w19, s19hackermh862No ratings yet
- Msbte w22 22417Document21 pagesMsbte w22 22417jacksparrowcom4100% (1)
- Corrected Summer 2016 Model Answer PaperDocument25 pagesCorrected Summer 2016 Model Answer PaperSuyog KadamNo ratings yet
- Course Code: CSYS1102 Duration: 1 Week Course Name: Introduction To Computer Security Coursework Weight: 10%Document6 pagesCourse Code: CSYS1102 Duration: 1 Week Course Name: Introduction To Computer Security Coursework Weight: 10%RammyBradNo ratings yet
- 22634-2022-Winter-Model-Answer-Paper (Msbte Study Resources)Document25 pages22634-2022-Winter-Model-Answer-Paper (Msbte Study Resources)ashusonkamble979No ratings yet
- CNE Model Answer PaperDocument47 pagesCNE Model Answer Paperop gamerNo ratings yet
- 22417Document30 pages22417Hack ManiaNo ratings yet
- Winter 22Document25 pagesWinter 22rohitmhaske0208No ratings yet
- 2018 Winter Model Answer PaperDocument25 pages2018 Winter Model Answer PaperVarad KhopkarNo ratings yet
- Model Answers Winter 2018Document26 pagesModel Answers Winter 2018kiritoblackswordsmen07No ratings yet
- Ilovepdf MergedDocument21 pagesIlovepdf Mergedd.soniNo ratings yet
- DCC Winter 22 Removed OrganizedDocument24 pagesDCC Winter 22 Removed Organizedsayedshaad02No ratings yet
- Detection of Logic Bombs PDFDocument3 pagesDetection of Logic Bombs PDFManoharrNo ratings yet
- ACN s23Document29 pagesACN s23kalpakpatil2004No ratings yet
- 6th Sem Pyq'sDocument17 pages6th Sem Pyq'sManeeshMahajanNo ratings yet
- DCC Summer 2023 AnswerDocument20 pagesDCC Summer 2023 Answertejasnarwade2k5No ratings yet
- SEN Winter2019Document23 pagesSEN Winter2019Sujal SonawaneNo ratings yet
- CS CIA1 2019-20 ME FinalDocument1 pageCS CIA1 2019-20 ME FinalvikNo ratings yet
- 22414DCC Summer 2023Document20 pages22414DCC Summer 2023nvoid7166No ratings yet
- Winter - 18 Examination: Important Instructions To ExaminersDocument34 pagesWinter - 18 Examination: Important Instructions To ExaminersMahesh DahiwalNo ratings yet
- Nis W-22Document27 pagesNis W-22Sahil MulayNo ratings yet
- WMN Model Summer-23Document19 pagesWMN Model Summer-23navteshdeore19100% (3)
- 2018 Winter OOP 3I - M - 22316 - CODocument26 pages2018 Winter OOP 3I - M - 22316 - CO14adisunnyNo ratings yet
- w22 SolutionDocument24 pagesw22 SolutionVaishnavi KadamNo ratings yet
- 4 DcoDocument62 pages4 DcoSachin KondawarNo ratings yet
- Model Answer Winter 2019Document22 pagesModel Answer Winter 2019IF21 Minit ChitrodaNo ratings yet
- MohamedshafiqueDocument10 pagesMohamedshafiquethalaaskar55No ratings yet
- RSAI Assignment 1Document6 pagesRSAI Assignment 1Shisa ChhotrayNo ratings yet
- XXXXX: Important Instructions To ExaminersDocument31 pagesXXXXX: Important Instructions To ExaminersYogesh DumaneNo ratings yet
- 22413-2019-Winter-Model-Answer-Paper (Msbte Study Resources)Document22 pages22413-2019-Winter-Model-Answer-Paper (Msbte Study Resources)arvi.sardarNo ratings yet
- Summer 22 Model AnsDocument29 pagesSummer 22 Model Ansaniketsarpate786No ratings yet
- ISE Question PapersDocument21 pagesISE Question Papersd.soniNo ratings yet
- 22620-Network and Information Security 241219Document8 pages22620-Network and Information Security 241219darshit rupareliyaNo ratings yet
- Approved Syllabus - 6th Semester (2015-2019)Document14 pagesApproved Syllabus - 6th Semester (2015-2019)MD Rakib HasanNo ratings yet
- Cryptography and System Security: K J Somaiya Institute of Engineering and Information TechnologyDocument11 pagesCryptography and System Security: K J Somaiya Institute of Engineering and Information TechnologyWhatNo ratings yet
- 220244-Data Communication and Computer Network - 22414 - 2023 - Summer Model AnswerDocument21 pages220244-Data Communication and Computer Network - 22414 - 2023 - Summer Model Answerommane312003100% (2)
- Software Eng NotesDocument23 pagesSoftware Eng Notessudarshan badwarNo ratings yet
- Vineet Sharma KeyloggerDocument51 pagesVineet Sharma KeyloggervineetNo ratings yet
- Cyber Riskmgmt AwarenessDocument33 pagesCyber Riskmgmt AwarenessDaniel EsterNo ratings yet
- SEN 22413summer-22-Model-AnsDocument28 pagesSEN 22413summer-22-Model-Ansnvoid7166100% (1)
- CC Certified in Cybersecurity The Complete ISC2 Certification Study GuideFrom EverandCC Certified in Cybersecurity The Complete ISC2 Certification Study GuideNo ratings yet
- DS JetNet4510 V1.3Document12 pagesDS JetNet4510 V1.3Assad ShafiqueNo ratings yet
- (Solutions Guide) Reverse ProxyDocument6 pages(Solutions Guide) Reverse ProxydecorlakeindiaNo ratings yet
- HX-CCD20 People Counter Manual - en - V1.0Document10 pagesHX-CCD20 People Counter Manual - en - V1.0Mafosk8No ratings yet
- Understanding Open Ports in Android Applications: Discovery, Diagnosis, and Security AssessmentDocument14 pagesUnderstanding Open Ports in Android Applications: Discovery, Diagnosis, and Security AssessmentJames CuasmayanNo ratings yet
- Manipulating SIP Headers and Messages in AOSDocument45 pagesManipulating SIP Headers and Messages in AOSabidouNo ratings yet
- Silver Pitch Deck by SlidesgoDocument52 pagesSilver Pitch Deck by SlidesgoCESÉ Samaniego ChNo ratings yet
- Get Access To The Comprehensive Teacher Email List Provided by The Education Data ListsDocument2 pagesGet Access To The Comprehensive Teacher Email List Provided by The Education Data ListsEducation Data ListsNo ratings yet
- Google-Android Basics With Compose Process DocumentDocument45 pagesGoogle-Android Basics With Compose Process DocumentsreedatthapuvvalaNo ratings yet
- Dumpter DrivingDocument7 pagesDumpter Drivingaurox3dNo ratings yet
- Marketing Seminarski RadDocument15 pagesMarketing Seminarski RadMiloš MitrovićNo ratings yet
- TRBOnet Telephony User Guide v5.2Document20 pagesTRBOnet Telephony User Guide v5.2Christian ChavezNo ratings yet
- SOSLITDocument4 pagesSOSLITnoahseth delaguaNo ratings yet
- OOPS in Automation FrameworkDocument3 pagesOOPS in Automation FrameworkSaravanan MuruganNo ratings yet
- Inventario GlassDocument3 pagesInventario GlassLIL EMILUCCINo ratings yet
- Wollega University: College of Engineering and Technology Department of Informatics Program of Computer ScienceDocument77 pagesWollega University: College of Engineering and Technology Department of Informatics Program of Computer ScienceAxl CarbonillaNo ratings yet
- Balon Et Al-2023-Education and Information TechnologiesDocument33 pagesBalon Et Al-2023-Education and Information Technologiesfx_ww2001No ratings yet
- Syllabus For Network Programming PDFDocument1 pageSyllabus For Network Programming PDFMuhammed yashifNo ratings yet
- Allworx Administration Guide 9.1Document422 pagesAllworx Administration Guide 9.1brian browneNo ratings yet
- Mukashifat Ainiyyah - Persian With Urdu TranslationDocument165 pagesMukashifat Ainiyyah - Persian With Urdu TranslationJalalludin Ahmad Ar-Rowi100% (1)
- Gokulan ResumeDocument4 pagesGokulan ResumeyessivaganeshNo ratings yet
- נספח לצו - 1.7.21Document15 pagesנספח לצו - 1.7.21Brock McConnelNo ratings yet
- IQ Option Wiki Portfolio: DealflowDocument35 pagesIQ Option Wiki Portfolio: DealflowErnane Luis PaixãoNo ratings yet
- Comandos Uteis Pentest WebDocument5 pagesComandos Uteis Pentest WebEstaçao Coruja NewsNo ratings yet
- Best Apps To Make Money OnlineDocument6 pagesBest Apps To Make Money OnlineNi Ne33% (3)
- ReadmeDocument25 pagesReadmeRooselvet GalindoNo ratings yet
- Osimis Web Viewer DocumentationDocument15 pagesOsimis Web Viewer DocumentationleandrovaffonsoNo ratings yet
- CV MD - AshikuzzamanDocument2 pagesCV MD - AshikuzzamanrazzakNo ratings yet
- KaliDocument10 pagesKalikarthik hcNo ratings yet
- HD Webcam c615 GSWDocument112 pagesHD Webcam c615 GSWStanislavaGavrilovicNo ratings yet