Professional Documents
Culture Documents
PIC18FXX80 Programing Specification
PIC18FXX80 Programing Specification
Uploaded by
bierny1985pawelOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
PIC18FXX80 Programing Specification
PIC18FXX80 Programing Specification
Uploaded by
bierny1985pawelCopyright:
Available Formats
PIC18FXX80/XX85
Flash Microcontroller Programming Specification
1.0 DEVICE OVERVIEW 2.1 Hardware Requirements
This document includes the programming 2.1.1 HIGH-VOLTAGE ICSP
specifications for the following devices: PROGRAMMING
• PIC18F6585 • PIC18F6680 In High-Voltage ICSP mode, these devices require two
• PIC18F8585 • PIC18F8680 programmable power supplies: one for VDD and one for
MCLR/VPP. Both supplies should have a minimum
resolution of 0.25V. Refer to Section 6.0 “AC/DC
2.0 PROGRAMMING OVERVIEW Characteristics Timing Requirements for Program/
PIC18FXX80/XX85 devices can be programmed using Verify Test Mode” for additional hardware parameters.
either the high-voltage In-Circuit Serial ProgrammingTM
(ICSPTM) method, or the low-voltage ICSP method. 2.1.2 LOW-VOLTAGE ICSP
Both of these programming methods can be done with PROGRAMMING
the device in the user’s system. The low-voltage ICSP In Low-Voltage ICSP mode, these devices can be pro-
method is slightly different than the high-voltage grammed using a VDD source in the operating range.
method, and these differences are noted where appli- This only means that MCLR/VPP does not have to be
cable. This programming specification applies to brought to a different voltage but can instead be left at the
PIC18FXX80/XX85 devices in all package types. normal operating voltage. Refer to Section 6.0 “AC/DC
Characteristics Timing Requirements for Program/
Verify Test Mode” for additional hardware parameters.
2.2 Pin Diagrams
The pin diagrams for the PIC18FXX80/XX85 family are
shown in Figure 2-1, Figure 2-2 and Figure 2-3. The
pin descriptions of these diagrams do not represent the
complete functionality of the device types. Users
should refer to the appropriate device data sheet for
complete pin descriptions.
TABLE 2-1: PIN DESCRIPTIONS (DURING PROGRAMMING): PIC18FXX80/XX85
During Programming
Pin Name
Pin Name Pin Type Pin Description
MCLR/VPP/RA5 VPP P Programming Enable
VDD(2) VDD P Power Supply
VSS(2) VSS P Ground
AVDD(2) AVDD P Analog Power Supply
AVSS(2) AVSS P Analog Ground
RB5 PGM I Low-Voltage ICSP™ Input when LVP Configuration bit equals ‘1’ (1)
RB6 PGC I Serial Clock
RB7 PGD I/O Serial Data
OSC1 OSC1 I Oscillator Input (needs to be pulled high during programming.)
Legend: I = Input, O = Output, P = Power
Note 1: See Section 5.3 “Low-Voltage Programming (LVP) Bit” for more detail.
2: All power supplies and ground must be connected.
2010 Microchip Technology Inc. DS39606E-page 1
PIC18FXX80/XX85
FIGURE 2-1: 64-PIN TQFP PACKAGE DIAGRAM FOR PIC18F6X8X
TQFP
RE7/CCP2(1)
RD0/PSP0
RD1/PSP1
RD2/PSP2
RD3/PSP3
RD4/PSP4
RD5/PSP5
RD6/PSP6
RD7/PSP7
RE5/P1C
RE6/P1B
RE2/CS
RE3
RE4
VDD
VSS
64 63 62 61 60 59 58 57 56 55 54 53 52 51 50 49
RE1/WR 1 48 RB0/INT0
RE0/RD 2 47 RB1/INT1
RG0/CANTX1 3 46 RB2/INT2
RG1/CANTX2 4 45 RB3/INT3
RG2/CANRX 5 44 RB4/KBI0
RG3 6 43 RB5/KBI1/PGM
RG5/MCLR/VPP 7 42 RB6/KBI2/PGC
RG4/P1D PIC18F6X8X VSS
8 41
VSS 9 40 OSC2/CLKO/RA6
VDD 10 39 OSC1/CLKI
RF7/SS 11 38 VDD
RF6/AN11/C1IN- 12 37 RB7/KBI3/PGD
RF5/AN10/C1IN+/CVREF 13 36 RC5/SDO
RF4/AN9/C2IN- 14 35 RC4/SDI/SDA
RF3/AN8/C2IN+ 15 34 RC3/SCK/SCL
RF2/AN7/C1OUT 16 33 RC2/CCP1/P1A
17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32
RF1/AN6/C2OUT
RF0/AN5
RC7/RX/DT
RA2/AN2/VREF-
RC1/T1OSI/CCP2(1)
RA3/AN3/VREF+
RC0/T1OSO/T13CKI
RA5/AN4/LVDIN
RC6/TX/CK
AVDD
RA1/AN1
RA0/AN0
VDD
RA4/T0CKI
AVSS
VSS
Note 1: CCP2 pin placement depends on the Processor mode settings.
DS39606E-page 2 2010 Microchip Technology Inc.
PIC18FXX80/XX85
FIGURE 2-2: 68-PIN PLCC PACKAGE DIAGRAM FOR PIC18F6X8X
PLCC
RE7/CCP2(1)
RD0/PSP0
RD1/PSP1
RD2/PSP2
RD3/PSP3
RD4/PSP4
RD5/PSP5
RD6/PSP6
RD7/PSP7
RE5/P1C
RE6/P1B
RE2/CS
RE3
RE4
VDD
N/C
VSS
9 8 7 6 5 4 3 2 1 68 67 66 65 64 63 62 61
RE1/WR 10 60 RB0/INT0
RE0/RD 11 59 RB1/INT1
Top View
RG0/CANTX1 12 58 RB2/INT2
RG1/CANTX2 13 57 RB3/INT3
RG2/CANRX 14 56 RB4/KBI0
RG3 15 55 RB5/KBI1/PGM
RG5/MCLR/VPP 16 54 RB6/KBI2/PGC
RG4/P1D 17 53 VSS
N/C 18 PIC18F6X8X 52 N/C
VSS 19 51 OSC2/CLKO/RA6
VDD 20 50 OSC1/CLKI
RF7/SS 21 49 VDD
RF6/AN11/C1IN- 22 48 RB7/KBI3/PGD
RF5/AN10/C1IN+/CVREF 23 47 RC5/SDO
RF4/AN9/C2IN- 24 46 RC4/SDI/SDA
RF3/AN8/C2IN+ 25 45 RC3/SCK/SCL
RF2/AN7/C1OUT 26 44 RC2/CCP1/P1A
27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43
VSS
AVSS
AVDD
RA2/AN2/VREF-
VDD
RA4/T0CKI
RC0/T1OSO/T13CKI
RC6/TX/CK
RA3/AN3/VREF+
RA5/AN4/LVDIN
RF0/AN5
RA1/AN1
RA0/AN0
RC1/T1OSI/CCP2(1)
RF1/AN6/C2OUT
RC7/RX/DT
N/C
Note 1: CCP2 pin placement depends on the Processor mode settings.
2010 Microchip Technology Inc. DS39606E-page 3
PIC18FXX80/XX85
FIGURE 2-3: 80-PIN TQFP PACKAGE DIAGRAM FOR PIC18F8X8X
TQFP
RE7/CCP2(2)/AD15
RD0/PSP0(1)/AD0
RD1/PSP1(1)/AD1
RD2/PSP2(1)/AD2
RD3/PSP3(1)/AD3
RD4/PSP4(1)/AD4
RD5/PSP5(1)/AD5
RD6/PSP6(1)/AD6
RD7/PSP7(1)/AD7
RE5/AD13/P1C
RE6/AD14/P1B
RE2/CS/AD10
RE4/AD12
RE3/AD11
RH0/A16
RH1/A17
RJ0/ALE
RJ1/OE
VDD
VSS
80 79 78 77 76 75 74 73 72 71 70 69 68 67 66 65 64 63 62 61
RH2/A18 1 60 RJ2/WRL
RH3/A19 2 59 RJ3/WRH
RE1/WR/AD9 3 58 RB0/INT0
RE0/RD/AD8 4 57 RB1/INT1
RG0/CANTX1 5 56 RB2/INT2
RG1/CANTX2 6 55 RB3/INT3/CCP2(2)
RG2/CANRX 7 54 RB4/KBI0
RG3 8 53 RB5/KBI1/PGM
RG5/MCLR/VPP 9 52 RB6/KBI2/PGC
RG4/P1D 10 PIC18F8X8X 51 VSS
VSS 11 50 OSC2/CLKO/RA6
VDD 12 49 OSC1/CLKI
RF7/SS 13 48 VDD
RF6/AN11/C1IN- 14 47 RB7/KBI3/PGD
RF5/AN10/C1IN+/CVREF 15 46 RC5/SDO
RF4/AN9/C2IN- 16 45 RC4/SDI/SDA
RF3/AN8/C2IN+ 17 44 RC3/SCK/SCL
RF2/AN7/C1OUT 18 43 RC2/CCP1/P1A
RH7/AN15/P1B 19 42 RJ7/UB
RH6/AN14/P1C 20 41 RJ6/LB
21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40
RF1/AN6/C2OUT
RF0/AN5
RJ5/CE
RA2/AN2/VREF-
RJ4/BA0
RA3/AN3/VREF+
RC0/T1OSO/T13CKI
RA5/AN4/LVDIN
RC6/TX/CK
RC7/RX/DT
RC1/T1OSI/CCP2(2)
RH5/AN13
RH4/AN12
AVDD
RA1/AN1
RA0/AN0
VDD
RA4/T0CKI
AVSS
VSS
Note 1: PSP is available only in Microcontroller mode.
2: CCP2 pin placement depends on the Processor mode settings.
DS39606E-page 4 2010 Microchip Technology Inc.
PIC18FXX80/XX85
2.3 Memory Map TABLE 2-2: IMPLEMENTATION OF CODE
MEMORY
The code memory space extends from 0000h to
0FFFFh (64 Kbytes) in four 16-Kbyte blocks. However, Code Memory Size
Device
addresses 0000h through 07FFh define a “Boot Block” (Bytes)
region that is treated separately from Block 1. All of PIC18F6585
these blocks define code protection boundaries within 0000h - 00BFFFh (48K)
the code memory space. PIC18F8585
PIC18F6680
In contrast, code memory panels are defined in 8-Kbyte 0000h -00FFFFh (64K)
boundaries. Panels are discussed in greater detail in PIC18F8680
Section 3.2 “Code Memory Programming”.
FIGURE 2-4: MEMORY MAP AND THE CODE MEMORY SPACE FOR PIC18FXX80/XX85 DEVICES
48 Kbytes 64 Kbytes
000000h 000000h
Code Memory Boot Block Boot Block 0007FFh
00FFFFh Panel 1 Panel 1
Block 1 Block 1 001FFFh
Panel 2 Panel 2
003FFFh
Panel 3 Panel 3
Block 2 Block 2 005FFFh
Unimplemented Panel 4 Panel 4
Read as ‘0’ 007FFFh
Panel 5 Panel 5
Block 3 Block 3 009FFFh
Panel 6 Panel 6
00BFFFh
Unimplemented Panel 7
Block 4 00DFFFh
Read as ‘0’s Panel 8
1FFFFFh 00FFFFh
Configuration
and ID
Space Unimplemented Unimplemented
Read as ‘0’s Read as ‘0’s
3FFFFFh 01FFFFh
Note: Sizes of memory areas are not shown to scale.
2010 Microchip Technology Inc. DS39606E-page 5
PIC18FXX80/XX85
In addition to the code memory space, there are three programmed and are described in Section 5.0
blocks in the configuration and ID space that are acces- “Configuration Word”. These device ID bits read out
sible to the user through table reads and table writes. normally even after code protection.
Their locations in the memory map are shown in
Figure 2-5. 2.3.1 MEMORY ADDRESS POINTER
Users may store identification information (ID) in eight Memory in the address space, 000000h to 3FFFFFh, is
ID registers. These ID registers are mapped in addressed via the Table Pointer which is comprised of
addresses 200000h through 200007h. The ID locations three pointer registers:
read out normally even after code protection is applied. • TBLPTRU, at RAM address 0FF8h
Locations, 300000h through 30000Dh, are reserved for • TBLPTRH, at RAM address 0FF7h
the Configuration bits. These bits select various device • TBLPTRL, at RAM address 0FF6h
options and are described in Section 5.0 “Configura-
tion Word”. These Configuration bits read out TBLPTRU TBLPTRH TBLPTRL
normally even after code protection. Addr[21:16] Addr[15:8] Addr[7:0]
Locations, 3FFFFEh and 3FFFFFh, are reserved for
The 4-bit command, ‘0000’ (core Instruction), is used
the device ID bits. These bits may be used by the
to load the Table Pointer prior to using many read or
programmer to identify what device type is being
write operations.
FIGURE 2-5: CONFIGURATION AND ID LOCATIONS FOR PIC18FXX80/XX85 DEVICES
000000h
Code Memory
00FFFFh ID Location 1 200000h
or ID Location 2 200001h
00BFFFh
ID Location 3 200002h
ID Location 4 200003h
ID Location 5 200004h
ID Location 6 200005h
Unimplemented
Read as ‘0’ ID Location 7 200006h
ID Location 8 200007h
CONFIG1L 300000h
CONFIG1H 300001h
CONFIG2L 300002h
CONFIG2H 300003h
1FFFFFh CONFIG3L 300004h
CONFIG3H 300005h
Configuration CONFIG4L 300006h
and ID CONFIG4H 300007h
Space CONFIG5L 300008h
CONFIG5H 300009h
CONFIG6L 30000Ah
2FFFFFh CONFIG6H 30000Bh
CONFIG7L 30000Ch
CONFIG7H 30000Dh
Device ID1 3FFFFEh
Device ID2 3FFFFFh
3FFFFFh
Note: Sizes of memory areas are not shown to scale.
DS39606E-page 6 2010 Microchip Technology Inc.
PIC18FXX80/XX85
2.4 High-Level Overview of the FIGURE 2-7: HIGH-LEVEL
Programming Process PROGRAMMING FLOW
Figure 2-7 shows the high-level overview of the
Start
programming process. First, a Bulk Erase is performed.
Next, the code memory, ID locations and data
EEPROM are programmed. These memories are then Perform Bulk
verified to ensure that programming was successful. If Erase
no errors are detected, the Configuration bits are then
programmed and verified.
Program Memory
2.5 Entering High-Voltage ICSP
Program/Verify Mode
Program IDs
The High-Voltage ICSP Program/Verify mode is
entered by holding PGC and PGD low and then raising
MCLR/VPP to VIHH (high voltage). Once in this mode,
the code memory, data EEPROM, ID locations and Program Data
Configuration bits can be accessed and programmed in
serial fashion.
The sequence that enters the device into the Program/ Verify Program
Verify mode places all unused I/Os in the high-impedance
state.
Verify IDs
2.5.1 ENTERING LOW-VOLTAGE ICSP
PROGRAM/VERIFY MODE
When the LVP Configuration bit is ‘1’ (see Section 5.3 Verify Data
“Low-Voltage Programming (LVP) Bit”), the Low-
Voltage ICSP mode is enabled. Low-Voltage ICSP
Program/Verify mode is entered by holding PGC and
Program
PGD low, placing a logic high on PGM and then raising Configuration Bits
MCLR/VPP to VIH. In this mode, the RB5/PGM pin is
dedicated to the programming function and ceases to
be a general purpose I/O pin. Verify
The sequence that enters the device into the Program/ Configuration Bits
Verify mode places all unused I/Os in the high-impedance
state. Done
FIGURE 2-8: ENTERING LOW-VOLTAGE
FIGURE 2-6: ENTERING HIGH-VOLTAGE PROGRAM/VERIFY MODE
PROGRAM/VERIFY MODE
P15 P12
P13 P12 VIH
MCLR/VPP
P1
D110
VDD
MCLR/VPP
VIH
VDD PGM
PGD
PGD
PGC
PGC
PGD = Input
PGD = Input
2010 Microchip Technology Inc. DS39606E-page 7
PIC18FXX80/XX85
2.6 Serial Program/Verify Operation TABLE 2-3: COMMANDS FOR
PROGRAMMING
The PGC pin is used as a clock input pin and the PGD
pin is used for entering command bits and data input/ 4-Bit
Description
output during serial operation. Commands and data are Command
transmitted on the rising edge of PGC, latched on the Core Instruction 0000
falling edge of PGC and are Least Significant bit (LSb) (shift in16-bit instruction)
first.
Shift out TABLAT register 0010
2.6.1 4-BIT COMMANDS Table Read 1000
Table Read, Post-Increment 1001
All instructions are 20 bits, consisting of a leading 4-bit
command followed by a 16-bit operand, which depends Table Read, Post-Decrement 1010
on the type of command being executed. To input a Table Read, Pre-Increment 1011
command, PGC is cycled four times. The commands Table Write 1100
needed for programming and verification are shown in
Table Write, Post-Increment by 2 1101
Table 2-3.
Table Write, Post-Decrement by 2 1110
Depending on the 4-bit command, the 16-bit operand
Table Write, Start Programming 1111
represents 16 bits of input data or 8 bits of input data
and 8 bits of output data.
Throughout this specification, commands and data are
presented as illustrated in Table 2-4. The 4-bit com- TABLE 2-4: SAMPLE COMMAND
mand is shown Most Significant bit (MSb) first. The SEQUENCE
command operand, or “Data Payload”, is shown 4-Bit Data
<MSB><LSB>. Figure 2-9 demonstrates how to Core Instruction
Command Payload
serially present a 20-bit command/operand to the
device. 1101 3C 40 Table Write,
post-increment by 2
2.6.2 CORE INSTRUCTION
The core instruction passes a 16-bit instruction to the
CPU core for execution. This is needed to set up
registers as appropriate for use with other commands.
FIGURE 2-9: TABLE WRITE, POST-INCREMENT TIMING (‘1101’)
P2 P2A
P2B
1 2 3 4 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 1 2 3 4
PGC
P5 P5A
P4
P3
PGD 1 0 1 1 0 0 0 0 0 0 1 0 0 0 1 1 1 1 0 0 n n n n
0 4 C 3
4-Bit Command 16-Bit Data Payload Fetch Next 4-Bit Command
PGD = Input
DS39606E-page 8 2010 Microchip Technology Inc.
PIC18FXX80/XX85
3.0 DEVICE PROGRAMMING TABLE 3-2: BULK ERASE COMMAND
SEQUENCE
3.1 High-Voltage ICSP Bulk Erase 4-Bit Data
Core Instruction
Command Payload
Erasing code or data EEPROM is accomplished by
writing an “Erase Option” to address 3C0004h. Code 0000 8E A6 BSF EECON1, EEPGD
memory may be erased portions at a time, or the user 0000 8C A6 BSF EECON1, CFGS
may erase the entire device in one action. “Bulk Erase” 0000 0E 3C MOVLW 3Ch
operations will also clear any code-protect settings 0000 6E F8 MOVWF TBLPTRU
associated with the memory block erased. Erase 0000 0E 00 MOVLW 00h
options are detailed in Table 3-1. 0000 6E F7 MOVWF TBLPTRH
0000 0E 04 MOVLW 04h
0000 6E F6 MOVWF TBLPTRL
TABLE 3-1: BULK ERASE OPTIONS 1100 00 80 Write 80h TO 3C0004h to
Description Data erase entire device.
0000 00 00 NOP
Chip Erase 80h 0000 00 00 Hold PGD low until
Erase Data EEPROM 81h erase completes.
Erase Boot Block 83h
Erase Block 1 88h
Erase Block 2 89h FIGURE 3-1: BULK ERASE FLOW
Erase Block 3 8Ah
Start
Erase Block 4 8Bh
The actual Bulk Erase function is a self-timed opera- Load Address
tion. Once the erase has started (falling edge of the 4th Pointer to
PGC after the “Write” command), serial execution will 3C0004h
cease until the erase completes (parameter P11).
During this time, PGC may continue to toggle but PGD
Write 80h
must be held low. to Erase
The code sequence to erase the entire device is shown Entire Device
in Table 3-2 and the flowchart is shown in Figure 3-1.
Note: A Bulk Erase is the only way to reprogram Delay P11+P10
code-protect bits from an ON state to an Time
OFF state.
Non code-protect bits are not returned to Done
default settings by a Bulk Erase. These
bits should be programmed to ‘1’s, as out-
lined in Section 3.6 “Configuration Bits
Programming”.
FIGURE 3-2: BULK ERASE TIMING
P10
1 2 3 4 1 2 15 16 1 2 3 4 1 2 15 16 1 2 3 4 1 2
PGC
P5 P5A P5 P5A P11
PGD 0 0 1 1 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 n n
4-Bit Command 16-Bit 4-Bit Command 16-Bit 4-Bit Command Erase Time 16-Bit
Data Payload Data Payload Data Payload
PGD = Input
2010 Microchip Technology Inc. DS39606E-page 9
PIC18FXX80/XX85
3.1.1 LOW-VOLTAGE ICSP BULK ERASE erase within each panel is the same (see Figure 3-5).
Multi-panel single row erase is enabled by appropriately
When using low-voltage ICSP, the part must be sup-
configuring the Programming Control register located at
plied by the voltage specified in parameter D111 if a
3C0006h.
Bulk Erase is to be executed. All other Bulk Erase
details as described above apply. The multi-panel single row erase duration is externally
timed and is controlled by PGC. After a “Start Program-
If it is determined that a program memory erase must
ming” command is issued (4-bit, ‘1111’), a NOP is
be performed at a supply voltage below the Bulk Erase
issued, where the 4th PGC is held high for the duration
limit, refer to the erase methodology described in
of the programming time, P9.
Section 3.1.2 “ICSP Multi-Panel Single Row Erase”
and Section 3.2.2 “Modifying Code Memory”. After PGC is brought low, the programming sequence
is terminated. PGC must be held low for the time spec-
If it is determined that a data EEPROM erase must be
ified by parameter P10 to allow high-voltage discharge
performed at a supply voltage below the Bulk Erase
of the memory array.
limit, follow the methodology described in Section 3.3
“Data EEPROM Programming” and write ‘1’s to the The code sequence to program a PIC18FXX80/XX85
array. device is shown in Table 3-3. The flowchart shown in
Figure 3-3 depicts the logic necessary to completely
3.1.2 ICSP MULTI-PANEL SINGLE ROW erase a PIC18FXX80/XX85 device. The timing dia-
ERASE gram that details the “Start Programming” command
and parameters P9 and P10 is shown in Figure 3-6.
Irrespective of whether high or low-voltage ICSP is
used, it is possible to erase single row (64 bytes of data) Note: The TBLPTR register must contain the
in all panels at once. For example, in the case of a same offset value when initiating the pro-
64-Kbyte device (8 panels), 512 bytes through 64 bytes gramming sequence as it did when the
in each panel can be erased simultaneously during write buffers were loaded.
each erase sequence. In this case, the offset of the
TABLE 3-3: ERASE CODE MEMORY CODE SEQUENCE
4-Bit
Data Payload Core Instruction
Command
Step 1: Direct access to configuration memory.
0000 8E A6 BSF EECON1, EEPGD
0000 8C A6 BSF EECON1, CFGS
0000 86 A6 BSF EECON1, WREN
Step 2: Configure device for multi-panel writes.
0000 0E 3C MOVLW 3Ch
0000 6E F8 MOVWF TBLPTRU
0000 0E 00 MOVLW 00h
0000 6E F7 MOVWF TBLPTRH
0000 0E 06 MOVLW 06h
0000 6E F6 MOVWF TBLPTRL
1100 00 40 Write 40h to 3C0006h to enable multi-panel erase.
Step 3: Direct access to code memory and enable erase.
0000 8E A6 BSF EECON1, EEPGD
0000 9C A6 BCF EECON1, CFGS
0000 88 A6 BSF EECON1, FREE
0000 6A F8 CLRF TBLPTRU
0000 6A F7 CLRF TBLPTRH
0000 6A F6 CLRF TBLPTRL
Step 4: Erase single row of all panels at an offset.
1111 <DummyLSB> Write 2 dummy bytes and start programming.
<DummyMSB>
0000 00 00 NOP - hold PGC high for time P9.
Step 5: Repeat step 4, with Address Pointer incremented by 64 until all panels are erased.
DS39606E-page 10 2010 Microchip Technology Inc.
PIC18FXX80/XX85
FIGURE 3-3: MULTI-PANEL SINGLE ROW ERASE CODE MEMORY FLOW
Start
Addr = 0
Configure
Device for
Multi-Panel Erase
Start Erase Sequence
and Hold PGC High
until Done
Addr = Addr + 64
Delay P9 + P10
Time for Erase
to Occur
All
No Panels
Done?
Yes
Done
3.2 Code Memory Programming The programming duration is externally timed and is
controlled by PGC. After a “Start Programming” com-
Programming code memory is accomplished by first mand is issued (4-bit command, ‘1111’), a NOP is
loading data into the appropriate write buffers and then issued, where the 4th PGC is held high for the duration
initiating a programming sequence. Each panel in the of the programming time, P9.
code memory space (see Figure 2-4) has an 8-byte
deep write buffer that must be loaded prior to initiating After PGC is brought low, the programming sequence
a write sequence. The actual memory write sequence is terminated. PGC must be held low for the time spec-
takes the contents of these buffers and programs the ified by parameter P10 to allow high-voltage discharge
associated EEPROM code memory. of the memory array.
Typically, all of the program buffers are written in paral- The code sequence to program a PIC18FXX80/XX85
lel (Multi-Panel Write mode). For example, in the case device is shown in Table 3-4. The flowchart shown in
of a 64-Kbyte device (8 panels with an 8-byte buffer per Figure 3-5 depicts the logic necessary to completely
panel), 64 bytes will be simultaneously programmed write a PIC18FXX80/XX85 device. The timing diagram
during each programming sequence. In this case, the that details the “Start Programming” command and
offset of the write within each panel is the same (see parameters P9 and P10 is shown in Figure 3-6.
Figure 3-4). Multi-Panel Write mode is enabled by Note: The TBLPTR register must contain the
appropriately configuring the Programming Control same offset value when initiating the pro-
register located at 3C0006h. gramming sequence as it did when the
write buffers were loaded.
2010 Microchip Technology Inc. DS39606E-page 11
PIC18FXX80/XX85
FIGURE 3-4: ERASE AND WRITE BOUNDARIES
Panel n
TBLPTR<21:13> = (n – 1)
TBLPTR<2:0> = 7 Erase Region
8-Byte Write Buffer
TBLPTR<2:0> = 6 (64 bytes)
TBLPTR<2:0> = 5
TBLPTR<2:0> = 4
TBLPTR<2:0> = 3
TBLPTR<2:0> = 2
TBLPTR<2:0> = 1
TBLPTR<2:0> = 0
Offset = TBLPTR<12:3> Offset = TBLPTR<12:6>
Panel 3
TBLPTR<21:13> = 2
TBLPTR<2:0> = 7 Erase Region
8-Byte Write Buffer
TBLPTR<2:0> = 6 (64 bytes)
TBLPTR<2:0> = 5
TBLPTR<2:0> = 4
TBLPTR<2:0> = 3
TBLPTR<2:0> = 2
TBLPTR<2:0> = 1
TBLPTR<2:0> = 0
Offset = TBLPTR<12:3> Offset = TBLPTR<12:6>
Panel 2
TBLPTR<21:13> = 1
TBLPTR<2:0> = 7 Erase Region
8-Byte Write Buffer
TBLPTR<2:0> = 6 (64 bytes)
TBLPTR<2:0> = 5
TBLPTR<2:0> = 4
TBLPTR<2:0> = 3
TBLPTR<2:0> = 2
TBLPTR<2:0> = 1
TBLPTR<2:0> = 0
Offset = TBLPTR<12:3> Offset = TBLPTR<12:6>
Panel 1
TBLPTR<21:13> = 0
TBLPTR<2:0> = 7 Erase Region
8-Byte Write Buffer
TBLPTR<2:0> = 6 (64 bytes)
TBLPTR<2:0> = 5
TBLPTR<2:0> = 4
TBLPTR<2:0> = 3
TBLPTR<2:0> = 2
TBLPTR<2:0> = 1
TBLPTR<2:0> = 0
Offset = TBLPTR<12:3> Offset = TBLPTR<12:6>
Note: TBLPTR = TBLPTRU:TBLPTRH:TBLPTRL.
DS39606E-page 12 2010 Microchip Technology Inc.
PIC18FXX80/XX85
TABLE 3-4: WRITE CODE MEMORY CODE SEQUENCE
4-Bit
Data Payload Core Instruction
Command
Step 1: Direct access to configuration memory.
0000 8E A6 BSF EECON1, EEPGD
0000 8C A6 BSF EECON1, CFGS
0000 86 A6 BSF EECON1, WREN
Step 2: Configure device for multi-panel writes.
0000 0E 3C MOVLW 3Ch
0000 6E F8 MOVWF TBLPTRU
0000 0E 00 MOVLW 00h
0000 6E F7 MOVWF TBLPTRH
0000 0E 06 MOVLW 06h
0000 6E F6 MOVWF TBLPTRL
1100 00 40 Write 40h to 3C0006h to enable multi-panel writes.
Step 3: Direct access to code memory.
0000 8E A6 BSF EECON1, EEPGD
0000 9C A6 BCF EECON1, CFGS
Step 4: Load write buffer for Panel 1.
0000 0E <Addr[21:16]> MOVLW <Addr[21:16]>
0000 6E F8 MOVWF TBLPTRU
0000 0E <Addr[15:8]> MOVLW <Addr[15:8]>
0000 6E F7 MOVWF TBLPTRH
0000 0E <Addr[7:0]> MOVLW <Addr[7:0]>
0000 6E F6 MOVWF TBLPTRL
1101 <LSB><MSB> Write 2 bytes and post-increment address by 2
1101 <LSB><MSB> Write 2 bytes and post-increment address by 2
1101 <LSB><MSB> Write 2 bytes and post-increment address by 2
1100 <LSB><MSB> Write 2 bytes
Step 5: Repeat for Panel 2.
Step 6: Repeat for all but the last panel (N – 1).
Step 7: Load write buffer for last panel.
0000 0E <Addr[21:16]> MOVLW <Addr[21:16]>
0000 6E F8 MOVWF TBLPTRU
0000 0E <Addr[15:8]> MOVLW <Addr[15:8]>
0000 6E F7 MOVWF TBLPTRH
0000 0E <Addr[7:0]> MOVLW <Addr[7:0]>
0000 6E F6 MOVWF TBLPTRL
1101 <LSB><MSB> Write 2 bytes and post-increment address by 2
1101 <LSB><MSB> Write 2 bytes and post-increment address by 2
1101 <LSB><MSB> Write 2 bytes and post-increment address by 2
1111 <LSB><MSB> Write 2 bytes and start programming
0000 00 00 NOP - hold PGC high for time P9
To continue writing data, repeat steps 2 through 5, where the Address Pointer is incremented by 8 in each panel at each iteration of
the loop.
2010 Microchip Technology Inc. DS39606E-page 13
PIC18FXX80/XX85
FIGURE 3-5: PROGRAM CODE MEMORY FLOW
Start
N=1
LoopCount = 0
Configure
Device for
Multi-Panel Writes
Panel Base Address =
(N – 1) x 2000h
Addr = Panel Base Address
+ (8 x LoopCount)
Load 8 Bytes
N=N+1 to Panel N Write
Buffer at <Addr>
All
No Panel Buffers
Written?
N=1 Yes
LoopCount =
LoopCount + 1 Start Write Sequence
and Hold PGC
High until Done
Delay P9 + P10 Time
for Write to Occur
No All
Locations
Done?
Yes
Done
FIGURE 3-6: TABLE WRITE AND START PROGRAMMING INSTRUCTION TIMING (‘1111’)
P10
1 2 3 4 1 2 3 4 5 6 15 16 1 2 3 4 1 2 3
PGC P9
P5 P5A
PGD 1 1 1 1 n n n n n n n n 0 0 0 0 0 0 0
4-Bit Command 16-Bit Data Payload 4-Bit Command Programming Time 16-Bit
Data Payload
PGD = Input
DS39606E-page 14 2010 Microchip Technology Inc.
PIC18FXX80/XX85
3.2.1 SINGLE PANEL PROGRAMMING The minimum amount of code memory that may be
erased at a given time is 64 bytes. Again, the device
The programming example presented in Section 3.2
must be placed in Single Panel Write mode. The
“Code Memory Programming” utilizes multi-panel
EECON1 register must then be used to erase the
programming. This technique greatly decreases the
64-byte target space prior to writing the data.
total amount of time necessary to completely program
a device and is the recommended method of When using the EECON1 register to act on code mem-
completely programming a device. ory, the EEPGD bit must be set (EECON1<7> = 1) and
the CFGS bit must be cleared (EECON1<6> = 0). The
There may be situations, however, where it is advanta-
WREN bit must be set (EECON1<2> = 1) to enable
geous to limit writes to a single panel. In such cases,
writes of any sort (e.g., erases) and this must be done
the user only needs to disable the multi-panel write
prior to initiating a write sequence. The FREE bit must
feature of the device by appropriately configuring the
be set (EECON1<4> = 1) in order to erase the program
Programming Control register located at 3C0006h.
space being pointed to by the Table Pointer. The erase
The single panel that will be written will automatically sequence is initiated by setting the WR bit
be enabled based on the value of the Table Pointer. (EECON1<1> = 1). It is strongly recommended that the
Note: Even though multi-panel writes are dis- WREN bit be set only when absolutely necessary.
abled, the user must still fill the 8-byte To help prevent inadvertent writes when using the
write buffer for the given panel. EECON1 register, EECON2 is used to “enable” the WR
bit. This register must be sequentially loaded with 55h
3.2.2 MODIFYING CODE MEMORY and then AAh, immediately prior to asserting the WR bit
All of the programming examples up to this point have in order for the write to occur.
assumed that the device has been Bulk Erased prior to The erase will begin on the falling edge of the 4th PGC
programming (see Section 3.1 “High-Voltage ICSP after the WR bit is set. After the erase sequence termi-
Bulk Erase”). However, it may be the case that the nates, PGC must still be held low for the time specified
user wishes to modify only a section of an already by parameter P10 to allow high-voltage discharge of
programmed device. the memory array.
The minimum amount of data that can be written to the
device is 8 bytes. This is accomplished by placing the
device in Single Panel Write mode (see Section 3.2.1
“Single Panel Programming”), loading the 8-byte
write buffer for the panel and then initiating a write
sequence. In this case, it is assumed that the address
space to be written already has data in it (i.e., it is not
blank).
2010 Microchip Technology Inc. DS39606E-page 15
PIC18FXX80/XX85
TABLE 3-5: MODIFYING CODE MEMORY
4-Bit
Data Payload Core Instruction
Command
Step 1: Direct access to configuration memory.
0000 8E A6 BSF EECON1, EEPGD
0000 8C A6 BSF EECON1, CFGS
Step 2: Configure device for single panel writes.
0000 0E 3C MOVLW 3Ch
0000 6E F8 MOVWF TBLPTRU
0000 0E 00 MOVLW 00h
0000 6E F7 MOVWF TBLPTRH
0000 0E 06 MOVLW 06h
0000 6E F6 MOVWF TBLPTRL
1100 00 00 Write 00h to 3C0006h to enable single-panel writes.
Step 3: Direct access to code memory.
0000 8E A6 BSF EECON1, EEPGD
0000 9C A6 BCF EECON1, CFGS
Step 4: Set the Table Pointer for the block to be erased.
0000 0E <Addr[21:16]> MOVLW <Addr[21:16]>
0000 6E F8 MOVWF TBLPTRU
0000 0E <Addr[8:15]> MOVLW <Addr[8:15]>
0000 6E F7 MOVWF TBLPTRH
0000 0E <Addr[7:0]> MOVLW <Addr[7:0]>
0000 6E F6 MOVWF TBLPTRL
Step 5: Enable memory writes and set up an erase.
0000 84 A6 BSF EECON1, WREN
0000 88 A6 BSF EECON1, FREE
Step 6: Perform required sequence.
0000 0E 55 MOVLW 55h
0000 6E A7 MOVWF EECON2
0000 0E AA MOVLW 0AAh
0000 6E A7 MOVWF EECON2
Step 7: Initiate erase.
0000 82 A6 BSF EECON1, WR
0000 00 00 NOP
Step 8: Wait for P11 + P10 and then disable writes.
0000 94 A6 BCF EECON1, WREN
Step 9: Load write buffer for panel. The correct panel will be selected based on the Table Pointer.
0000 0E <Addr[8:15]> MOVLW <Addr[8:15]>
0000 6E F7 MOVWF TBLPTRH
0000 0E <Addr[7:0]> MOVLW <Addr[7:0]>
0000 6E F6 MOVWF TBLPTRL
1101 <LSB><MSB> Write 2 bytes and post-increment address by 2
1101 <LSB><MSB> Write 2 bytes and post-increment address by 2
1101 <LSB><MSB> Write 2 bytes and post-increment address by 2
1111 <LSB><MSB> Write 2 bytes and start programming
0000 00 00 NOP - hold PGC high for time P9
To continue writing data, repeat step 8, where the Address Pointer is incremented by 8 at each iteration of the loop.
DS39606E-page 16 2010 Microchip Technology Inc.
PIC18FXX80/XX85
3.3 Data EEPROM Programming FIGURE 3-7: PROGRAM DATA FLOW
Data EEPROM is accessed one byte at a time via an
Start
Address Pointer (register pair, EEADR:EEADRH) and
a data latch (EEDATA). Data EEPROM is written by
loading EEADR:EEADRH with the desired memory Set Address
location, EEDATA with the data to be written and initiat-
ing a memory write by appropriately configuring the
EECON1 and EECON2 registers. A byte write auto- Set Data
matically erases the location and writes the new data
(erase-before-write).
When using the EECON1 register to perform a data Enable Write
EEPROM write, both the EEPGD and CFGS bits must
be cleared (EECON1<7:6> = 00). The WREN bit must
Unlock Sequence
be set (EECON1<2> = 1) to enable writes of any sort, 55h – EECON2
and this must be done prior to initiating a write AAh – EECON2
sequence. The write sequence is initiated by setting the
WR bit (EECON1<1> = 1). It is strongly recommended
Start Write
that the WREN bit be set only when absolutely Sequence
necessary.
To help prevent inadvertent writes when using the WR bit No
EECON1 register, EECON2 is used to “enable” the WR Clear?
bit. This register must be sequentially loaded with 55h
Yes
and then AAh immediately prior to asserting the WR bit
in order for the write to occur. No Done
The write begins on the falling edge of the 4th PGC ?
after the WR bit is set. It ends when the WR bit is Yes
cleared by hardware.
Done
After the programming sequence terminates, PGC must
still be held low for the time specified by parameter P10
to allow high-voltage discharge of the memory array.
FIGURE 3-8: DATA EEPROM WRITE TIMING
P10
1 2 3 4 1 2 15 16 1 2
PGC
P5 P5A
PGD 0 0 0 0 n n
4-Bit Command BSF EECON1, WR Poll WR Bit, Repeat Until Clear 16-Bit Data
(see below) Payload
PGD = Input
1 2 3 4 1 2 15 16 1 2 3 4 1 2 15 16
PGC
P5 P5A P5 P5A
Poll WR Bit
PGD 0 0 0 0 0 0 0 0
4-Bit Command MOVF EECON1, W, 0 4-Bit Command MOVWF TABLAT Shift Out Data
(see Figure 4-4)
PGD = Input PGD = Output
2010 Microchip Technology Inc. DS39606E-page 17
PIC18FXX80/XX85
TABLE 3-6: PROGRAMMING DATA MEMORY
4-Bit
Data Payload Core Instruction
Command
Step 1: Direct access to data EEPROM.
0000 9E A6 BCF EECON1, EEPGD
0000 9C A6 BCF EECON1, CFGS
Step 2: Set the data EEPROM Address Pointer.
0000 0E <Addr> MOVLW <Addr>
0000 6E A9 MOVWF EEADR
0000 OE <AddrH> MOVLW <AddrH>
0000 6E AA MOVWF EEADRH
Step 3: Load the data to be written.
0000 0E <Data> MOVLW <Data>
0000 6E A8 MOVWF EEDATA
Step 4: Enable memory writes.
0000 84 A6 BSF EECON1, WREN
Step 5: Perform required sequence.
0000 0E 55 MOVLW 55h
0000 6E A7 MOVWF EECON2
0000 0E AA MOVLW 0AAh
0000 6E A7 MOVWF EECON2
Step 6: Initiate write.
0000 82 A6 BSF EECON1, WR
Step 7: Poll WR bit, repeat until the bit is clear.
0000 50 A6 MOVF EECON1, W, 0
0000 6E F5 MOVWF TABLAT
0010 <LSB><MSB> Shift out data(1)
Step 8: Disable writes.
0000 94 A6 BCF EECON1, WREN
Repeat steps 2 through 8 to write more data.
Note 1: See Figure 4-4 for details on shift out data timing.
DS39606E-page 18 2010 Microchip Technology Inc.
PIC18FXX80/XX85
3.4 ID Location Programming Note: Even though multi-panel writes are dis-
The ID locations are programmed much like the code abled, the user must still fill the 8-byte data
memory except that multi-panel writes must be dis- buffer for the panel.
abled. The single panel that will be written will automat- Table 3-7 demonstrates the code sequence required to
ically be enabled based on the value of the Table write the ID locations.
Pointer. The ID registers are mapped in addresses,
200000h through 200007h. These locations read out
normally even after code protection.
TABLE 3-7: WRITE ID SEQUENCE
4-Bit
Data Payload Core Instruction
Command
Step 1: Direct access to configuration memory.
0000 8E A6 BSF EECON1, EEPGD
0000 8C A6 BSF EECON1, CFGS
Step 2: Configure device for single panel writes.
0000 0E 3C MOVLW 3Ch
0000 6E F8 MOVWF TBLPTRU
0000 0E 00 MOVLW 00h
0000 6E F7 MOVWF TBLPTRH
0000 0E 06 MOVLW 06h
0000 6E F6 MOVWF TBLPTRL
1100 00 00 Write 00h to 3C0006h to enable single panel writes.
Step 3: Direct access to code memory.
0000 8E A6 BSF EECON1, EEPGD
0000 9C A6 BCF EECON1, CFGS
Step 4: Load write buffer. Panel will be automatically determined by address.
0000 0E 20 MOVLW 20h
0000 6E F8 MOVWF TBLPTRU
0000 0E 00 MOVLW 00h
0000 6E F7 MOVWF TBLPTRH
0000 0E 00 MOVLW 00h
0000 6E F6 MOVWF TBLPTRL
1101 <LSB><MSB> Write 2 bytes and post-increment address by 2
1101 <LSB><MSB> Write 2 bytes and post-increment address by 2
1101 <LSB><MSB> Write 2 bytes and post-increment address by 2
1111 <LSB><MSB> Write 2 bytes and start programming
0000 00 00 NOP - hold PGC high for time P9
In order to modify the ID locations, refer to the method-
ology described in Section 3.2.2 “Modifying Code
Memory”. As with code memory, the ID locations must
be erased before modified.
2010 Microchip Technology Inc. DS39606E-page 19
PIC18FXX80/XX85
3.5 Boot Block Programming 3.6 Configuration Bits Programming
The Boot Block segment is programmed in exactly the Unlike code memory, the Configuration bits are
same manner as the ID locations (see Section 3.4 “ID programmed a byte at a time. The “Table Write, Begin
Location Programming”). Multi-panel writes must be Programming” 4-bit command (‘1111’) is used, but only
disabled so that only addresses in the range, 0000h to 8 bits of the following 16-bit payload will be written. The
07FFh, will be written. LSB of the payload will be written to even addresses
The code sequence detailed in Table 3-7 should be and the MSB will be written to odd addresses. The
used, except that the address data used in “Step 2” will code sequence to program two consecutive
be in the range, 000000h to 0007FFh. configuration locations is shown in Table 3-8.
Note: Execute four NOPs between every
configuration byte programming.
TABLE 3-8: SET ADDRESS POINTER TO CONFIGURATION LOCATION
4-Bit
Data Payload Core Instruction
Command
Step 1: Direct access to configuration memory.
0000 8E A6 BSF EECON1, EEPGD
0000 8C A6 BSF EECON1, CFGS
Step 2: Position the program counter.(1)
0000 EF 00 GOTO 100000h
0000 F8 00
Step 3: Set Table Pointer for configuration byte to be written. Write even/odd addresses.(2)
0000 0E 30 MOVLW 30h
0000 6E F8 MOVWF TBLPTRU
0000 0E 00 MOVLW 00h
0000 6E F7 MOVWF TBLPRTH
0000 0E 00 MOVLW 00h
0000 6E F6 MOVWF TBLPTRL
1111 <LSB><MSB ignored> Load 2 bytes and start programming
0000 00 00 NOP - hold PGC high for time P9
0000 2A F6 INCF TBLPTRL
1111 <LSB ignored><MSB> Load 2 bytes and start programming
0000 00 00 NOP - hold PGC high for time P9
Step 4: Execute four NOPs.
0000 00 00
0000 00 00
0000 00 00
0000 00 00
Note 1: If the code protection bits are programmed while the program counter resides in the same block, then the interaction of
code protection logic may prevent further table write. To avoid this situation, move the program counter outside the
code protection area (e.g., GOTO 100000h).
2: Enabling the write protection of Configuration bits (WRTC = 0 in CONFIG6H) will prevent further writing of Configuration
bits. Always write all the Configuration bits before enabling the write protection for Configuration bits.
DS39606E-page 20 2010 Microchip Technology Inc.
PIC18FXX80/XX85
FIGURE 3-9: CONFIGURATION PROGRAMMING FLOW
Start Start
Load Even Load Odd
Configuration Configuration
Address Address
Program Program
LSB MSB
Delay P9 Time Delay P9 Time
for Write for Write
Execute Execute
Four NOPs Four NOPs
Done Done
2010 Microchip Technology Inc. DS39606E-page 21
PIC18FXX80/XX85
4.0 READING THE DEVICE The 4-bit command is shifted in LSb first. The read is
executed during the next 8 clocks, then shifted out on
PGD during the last 8 clocks, LSb to MSb. A delay of
4.1 Read Code Memory, ID Locations
P6 must be introduced after the falling edge of the 8th
and Configuration Bits PGC of the operand to allow PGD to transition from an
Code memory is accessed one byte at a time via the input to an output. During this time, PGC must be held
4-bit command, ‘1001’ (table read, post-increment). low (see Figure 4-1). This operation also increments
The contents of memory pointed to by the Table Pointer the Table Pointer by one, pointing to the next byte in
(TBLPTRU:TBLPTRH:TBLPTRL) are loaded into the code memory for the next read.
table latch and then serially output on PGD. This technique will work to read any memory in the
000000h to 3FFFFFh address space, so it also applies
to the reading of the ID and Configuration registers.
TABLE 4-1: READ CODE MEMORY SEQUENCE
4-Bit
Data Payload Core Instruction
Command
Step 1: Set Table Pointer.
0000 0E <Addr[21:16]> MOVLW Addr[21:16]
0000 6E F8 MOVWF TBLPTRU
0000 0E <Addr[15:8]> MOVLW <Addr[15:8]>
0000 6E F7 MOVWF TBLPTRH
0000 0E <Addr[7:0]> MOVLW <Addr[7:0]>
0000 6E F6 MOVWF TBLPTRL
Step 2: Read memory into table latch and then shift out on PGD, LSb to MSb.
1001 00 00 TBLRD *+
FIGURE 4-1: TABLE READ POST-INCREMENT INSTRUCTION TIMING (‘1001’)
1 2 3 4 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 1 2 3 4
PGC
P5 P6 P5A
P14
PGD 1 0 0 1 LSb 1 2 3 4 5 6 MSb n n n n
Shift Data Out Fetch Next
4-Bit Command
PGD = Input PGD = Output PGD = Input
DS39606E-page 22 2010 Microchip Technology Inc.
PIC18FXX80/XX85
4.2 Verify Code Memory and ID The Table Pointer must be manually set to 200000h
Locations (base address of the ID locations) once the code mem-
ory has been verified. The post-increment feature of
The verify step involves reading back the code memory the table read 4-bit command may not be used to
space and comparing against the copy held in the pro- increment the Table Pointer beyond the code memory
grammer’s buffer. Memory reads occur a single byte at space. In a 48-Kbyte device, for example, a post-
a time, so two bytes must be read to compare against increment read of address 0BFFFh will wrap the Table
the word in the programmer’s buffer. Refer to Pointer back to 0000h, rather than point to
Section 4.1 “Read Code Memory, ID Locations and unimplemented address, 0C000h.
Configuration Bits” for implementation details of
reading code memory.
FIGURE 4-2: VERIFY CODE MEMORY FLOW
Start
Set Pointer = 0 Set Pointer = 200000h
Read Low Byte Read Low Byte
Read High Byte Read High Byte
Does Does
No No
Word = Expect Failure, Word = Expect Failure,
Data? Report Data? Report
Error Error
Yes Yes
All All
No Code Memory No ID Locations
Verified? Verified?
Yes Yes
Done
2010 Microchip Technology Inc. DS39606E-page 23
PIC18FXX80/XX85
4.3 Verify Configuration Bits FIGURE 4-3: READ DATA EEPROM
FLOW
A configuration address may be read and output on
PGD via the 4-bit command, ‘1001’. Configuration data
is read and written in a byte-wise fashion, so it is not Start
necessary to merge two bytes into a word prior to a
compare. The result may then be immediately
Set
compared to the appropriate configuration data in the Address
programmer’s memory for verification. Refer to
Section 4.1 “Read Code Memory, ID Locations and
Configuration Bits” for implementation details of Read
reading configuration data. Byte
4.4 Read Data EEPROM Memory
Move to TABLAT
Data EEPROM is accessed one byte at a time via an
Address Pointer (register pair, EEADR:EEADRH) and
a data latch (EEDATA). Data EEPROM is read by load-
ing EEADR:EEADRH with the desired memory location Shift Out Data
and initiating a memory read by appropriately configur-
ing the EECON1 register. The data will be loaded into
EEDATA, where it may be serially output on PGD via No Done
the 4-bit command, ‘0010’ (Shift Out Data Holding ?
register). A delay of P6 must be introduced after the
Yes
falling edge of the 8th PGC of the operand to allow
PGD to transition from an input to an output. During this Done
time, PGC must be held low (see Figure 4-4).
The command sequence to read a single byte of data
is shown in Table 4-2.
TABLE 4-2: READ DATA EEPROM MEMORY
4-Bit
Data Payload Core Instruction
Command
Step 1: Direct access to data EEPROM.
0000 9E A6 BCF EECON1, EEPGD
0000 9C A6 BCF EECON1, CFGS
Step 2: Set the data EEPROM Address Pointer.
0000 0E <Addr> MOVLW <Addr>
0000 6E A9 MOVWF EEADR
0000 OE <AddrH> MOVLW <AddrH>
0000 6E AA MOVWF EEADRH
Step 3: Initiate a memory read.
0000 80 A6 BSF EECON1, RD
Step 4: Load data into the Serial Data Holding register.
0000 50 A8 MOVF EEDATA, W, 0
0000 6E F5 MOVWF TABLAT
0010 <LSB><MSB> Shift Out Data(1)
Note 1: The <LSB> is undefined. The <MSB> is the data.
DS39606E-page 24 2010 Microchip Technology Inc.
PIC18FXX80/XX85
FIGURE 4-4: SHIFT OUT DATA HOLDING REGISTER TIMING (‘0010’)
1 2 3 4 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 1 2 3 4
PGC
P5 P6 P5A
P14
PGD 0 1 0 0 LSb 1 2 3 4 5 6 MSb n n n n
Shift Data Out Fetch Next
4-Bit Command
PGD = Input PGD = Output PGD = Input
4.5 Verify Data EEPROM Given that “Blank Checking” is merely code and data
EEPROM verification with FFh expect data, refer to
A data EEPROM address may be read via a sequence of Section 4.2 “Verify Code Memory and ID Locations”
core instructions (4-bit command, ‘0000’) and then out- and Section 4.4 “Read Data EEPROM Memory” for
put on PGD via the 4-bit command, ‘0010’ (Shift Out implementation details.
Data Holding register). The result may then be immedi-
ately compared to the appropriate data in the program-
FIGURE 4-5: BLANK CHECK FLOW
mer’s memory for verification. Refer to Section 4.4
“Read Data EEPROM Memory” for implementation
details of reading data EEPROM. Start
4.6 Blank Check Blank Check Device
The term “Blank Check” means to verify that the device
has no programmed memory cells. All memories must
be verified: code memory, data EEPROM, ID locations Is
Device Yes
and Configuration bits. The Device ID registers Continue
(3FFFFEh:3FFFFFh) should be ignored. Blank?
A “blank” or “erased” memory cell will read as a ‘1’. So, No
“Blank Checking” a device merely means to verify that
all bytes read as FFh, except the Configuration bits. Abort
Unused (reserved) Configuration bits will read ‘0’ (pro-
grammed). Refer to Table 5-2 for blank configuration
expect data for the various PIC18FXX80/XX85
devices.
2010 Microchip Technology Inc. DS39606E-page 25
PIC18FXX80/XX85
5.0 CONFIGURATION WORD 5.3 Low-Voltage Programming
(LVP) Bit
The PIC18FXX80/XX85 devices have several Configu-
ration Words. These bits can be set or cleared to select The LVP bit in Configuration register, CONFIG4L,
various device configurations. All other memory areas enables low-voltage ICSP programming. The LVP bit
should be programmed and verified prior to setting defaults to a ‘1’ from the factory.
Configuration Words. These bits may be read out
If Low-Voltage Programming mode is not used, the LVP
normally even after read or code-protected.
bit can be programmed to a ‘0’ and RB5/PGM becomes
a digital I/O pin. However, the LVP bit may only be pro-
5.1 ID Locations grammed by entering the High-Voltage ICSP mode,
A user may store identification information (ID) in eight where MCLR/VPP is raised to VIHH. Once the LVP bit is
ID locations, mapped in 200000h:200007h. It is recom- programmed to a ‘0’, only the High-Voltage ICSP mode
mended that the Most Significant nibble of each ID be is available and only the High-Voltage ICSP mode can
0Fh. In doing so, if the user code inadvertently tries to be used to program the device.
execute from the ID space, the ID data will execute as Note 1: The normal ICSP mode is always avail-
a NOP. able, regardless of the state of the LVP
bit, by applying VIHH to the MCLR/VPP
5.2 Device ID Word pin.
The Device ID Word for the PIC18FXX80/XX85 2: While in Low-Voltage ICSP mode, the
devices is located at 3FFFFEh:3FFFFFh. These bits RB5 pin can no longer be used as a
may be used by the programmer to identify what device general purpose I/O.
type is being programmed and read out normally even
after code or read-protected.
TABLE 5-1: DEVICE ID VALUES
Device ID Value
Device
DEVID2 DEVID1
PIC18F6585 0Ah 011x xxxx
PIC18F6680 0Ah 001x xxxx
PIC18F8585 0Ah 010x xxxx
PIC18F8680 0Ah 000x xxxx
DS39606E-page 26 2010 Microchip Technology Inc.
PIC18FXX80/XX85
TABLE 5-2: PIC18FXX80/XX85 CONFIGURATION BITS AND DEVICE IDS
Default/
File Name Bit 7 Bit 6 Bit 5 Bit 4 Bit 3 Bit 2 Bit 1 Bit 0 Unprogrammed
Value
300001h CONFIG1H — — OSCSEN — FOSC3 FOSC2 FOSC1 FOSC0 --1- 1111
300002h CONFIG2L — — — — BORV1 BORV0 BODEN PWRTEN ---- 1111
300003h CONFIG2H — — — WDTPS3 WDTPS2 WDTPS1 WDTPS0 WDTEN ---1 1111
300004h(1) CONFIG3L WAIT — — — — — PM1 PM0 1--- --11
300005h CONFIG3H MCLRE — — — — — ECCPMX(3) CCP2MX 1--- --11
300006h CONFIG4L DEBUG — — — — LVP — STVREN 1--- -1-1
300008h CONFIG5L — — — — CP3(2) CP2 CP1 CP0 ---- 1111
300009h CONFIG5H CPD CPB — — — — — — 11-- ----
30000Ah CONFIG6L — — — — WRT3(2) WRT2 WRT1 WRT0 ---- 1111
30000Bh CONFIG6H WRTD WRTB WRTC — — — — — 111- ----
(2)
30000Ch CONFIG7L — — — — EBTR3 EBTR2 EBTR1 EBTR0 ---- 1111
30000Dh CONFIG7H — EBTRB — — — — — — -1-- ----
3FFFFEh DEVID1 DEV2 DEV1 DEV0 REV4 REV3 REV2 REV1 REV0 Table 5-1
3FFFFFh DEVID2 DEV10 DEV9 DEV8 DEV7 DEV6 DEV5 DEV4 DEV3 Table 5-1
Legend: - = unimplemented. Shaded cells are unimplemented, read as ‘0’.
Note 1: Unimplemented in PIC18F6X8X devices; maintain this bit set.
2: Unimplemented in PIC18FX585 devices; maintain this bit set.
3: Reserved in PIC18F6X8X devices; maintain this bit set.
2010 Microchip Technology Inc. DS39606E-page 27
PIC18FXX80/XX85
TABLE 5-3: PIC18FXX80/XX85 CONFIGURATION BIT DESCRIPTIONS
Configuration
Bit Name Description
Bytes
OSCEN Low Power System Clock Option (Timer1) Enable bit
1 = Disabled
0 = Timer1 oscillator system clock option enabled
FOSC3:FOSC0 Oscillator Selection bits
1111 = RC oscillator w/OSC2 configured as RA6
1110 = HS oscillator w/software controlled PLL
1101 = EC oscillator with OSC2 configured as RA6 w/SW controlled PLL
1100 = EC oscillator with OSC2 configured as RA6 w/PLL enabled
1011 = Reserved; do not use
CONFIG1H 1010 = Reserved; do not use
1001 = Reserved; do not use
1000 = Reserved; do not use
0111 = RC oscillator w/OSC2 configured as RA6
0110 = HS oscillator w/PLL enabled
0101 = EC oscillator w/OSC2 configured as RA6
0100 = EC oscillator w/OSC2 configured as “divide by 4 clock output”
0011 = RC oscillator
0010 = HS oscillator
0001 = XT oscillator
0000 = LP oscillator
BORV1:BORV0 Brown-out Reset Voltage bits
11 =VBOR set to 2.0V
10 =VBOR set to 2.7V
01 =VBOR set to 4.2V
00 =VBOR set to 4.5V
BOREN CONFIG2L Brown-out Reset Enable bit
1 = Brown-out Reset enabled
0 = Brown-out Reset disabled
PWRTEN Power-up Timer Enable bit
1 = PWRT disabled
0 = PWRT enabled
WDTPS3:WDTPS0 Watchdog Timer Postscaler Select bits
1111 = 1:32768
1110 = 1:16384
1101 = 1:8192
1100 = 1:4096
1011 = 1:2048
1010 = 1:1024
1001 = 1:512
1000 = 1:256
0111 = 1:128
CONFIG2H 0110 = 1:64
0101 = 1:32
0100 = 1:16
0011 = 1:8
0010 = 1:4
0001 = 1:2
0000 = 1:1
WDTEN Watchdog Timer Enable bit
1 = WDT enabled
0 = WDT disabled (control is placed on SWDTEN bit)
Note 1: Unimplemented in PIC18F6X8X (64-pin) devices; maintain this bit set.
2: Unimplemented in PIC18FX585 devices; maintain this bit set.
3: Reserved for PIC18F6X8X devices; maintain this bit set.
DS39606E-page 28 2010 Microchip Technology Inc.
PIC18FXX80/XX85
TABLE 5-3: PIC18FXX80/XX85 CONFIGURATION BIT DESCRIPTIONS (CONTINUED)
Configuration
Bit Name Description
Bytes
WAIT(1) External Bus Data Wait Enable bit
1 = Wait selections unavailable
0 = Wait selections determined by WAIT1:WAIT0 bits of MEMCOM register
PM1:PM0(1) CONFIG3L Processor Mode Select bits
11 = Microcontroller mode
10 = Microprocessor mode
01 = Microprocessor with Boot Block mode
00 = Extended Microcontroller mode
MCLRE MCLR Enable bit
1 = MCLR pin enabled, RG5 disabled
0 = MCLR pin disabled, RG5 enabled
ECCPMX CCP1 PWM Outputs P1B, P1C MUX bit (PIC18F8X8X devices only)(3)
1 = P1B, P1C are multiplexed with RE6, RE5
0 = P1B, P1C are multiplexed with RH7, RH6
CCP2MX CONFIG3H In Microcontroller mode:
1 = CCP2 input/output is multiplexed with RC1
0 = CCP2 input/output is multiplexed with RE7
In Microprocessor, Microprocessor with Boot Block and Extended
Microcontroller modes (PIC18F8X8X devices only):
1 = CCP2 input/output is multiplexed with RC1
0 = CCP2 input/output is multiplexed with RB3
DEBUG Background Debugger Enable bit
1 = Background debugger disabled (RB6, RB7 are I/O pins)
0 = Background debugger enabled (RB6, RB7 are ISCP™ pins)
LVP Low-Voltage Programming Enable bit
CONFIG4L 1 = Low-voltage programming enabled
0 = Low-voltage programming disabled
STVREN Stack Overflow/Underflow Reset Enable bit
1 = Stack overflow/underflow will cause Reset
0 = Stack overflow/underflow will not cause Reset
CP0 Code Protection bits (code memory area 0800h-3FFFh)
1 = Code memory not code-protected
0 = Code memory code-protected
CP1 Code Protection bits (code memory area 4000h-7FFFh)
1 = Code memory not code-protected
0 = Code memory code-protected
CONFIG5L
CP2 Code Protection bits (code memory area 8000h-0BFFFh)
1 = Code memory not code-protected
0 = Code memory code-protected
CP3(2) Code Protection bits (code memory area 0C000h-0FFFFh)
1 = Code memory not code-protected
0 = Code memory code-protected
CPD Code Protection bits (data EEPROM)
1 = Data EEPROM not code-protected
0 = Data EEPROM code-protected
CONFIG5H
CPB Code Protection bits (boot block, memory area 0000h-07FFh)
1 = Boot block not code-protected
0 = Boot block code-protected
Note 1: Unimplemented in PIC18F6X8X (64-pin) devices; maintain this bit set.
2: Unimplemented in PIC18FX585 devices; maintain this bit set.
3: Reserved for PIC18F6X8X devices; maintain this bit set.
2010 Microchip Technology Inc. DS39606E-page 29
PIC18FXX80/XX85
TABLE 5-3: PIC18FXX80/XX85 CONFIGURATION BIT DESCRIPTIONS (CONTINUED)
Configuration
Bit Name Description
Bytes
WRT0 Table Write Protection bit (code memory area 0800h-3FFFh)
1 = Code memory not write-protected
0 = Code memory write-protected
WRT1 Table Write Protection bit (code memory area 4000h-7FFFh)
1 = Code memory not write-protected
0 = Code memory write-protected
CONFIG6L
WRT2 Table Write Protection bit (code memory area 8000h-0BFFFh)
1 = Code memory not write-protected
0 = Code memory write-protected
WRT3(2) Table Write Protection bit (code memory area 0C000h-0FFFFh)
1 = Code memory not write-protected
0 = Code memory write-protected
WRTD Table Write Protection bit (data EEPROM)
1 = Data EEPROM not write-protected
0 = Data EEPROM write-protected
WRTB Table Write Protection bit (Boot Block, memory area 0000h-07FFh)
CONFIG6H 1 = Boot block not write-protected
0 = Boot block write-protected
WRTC Table Write Protection bit (Configuration registers)
1 = Configuration registers not write-protected
0 = Configuration registers write-protected
EBTR0 Table Read Protection bit (code memory area 0800h-3FFFh)
1 = Code memory not protected from table reads executed in other blocks
0 = Code memory protected from table reads executed in other blocks
EBTR1 Table Read Protection bit (code memory area 4000h-7FFFh)
1 = Code memory not protected from table reads executed in other blocks
0 = Code memory protected from table reads executed in other blocks
CONFIG7L
EBTR2 Table Read Protection bit (code memory area 8000h-0BFFFh)
1 = Code memory not protected from table reads executed in other blocks
0 = Code memory protected from table reads executed in other blocks
EBTR3(2) Table Read Protection bit (code memory area 0C000h-0FFFFh)
1 = Code memory not protected from table reads executed in other blocks
0 = Code memory protected from table reads executed in other blocks
EBTRB Table Read Protection bit (Boot Block, memory area 0000h-07FFh)
CONFIG7H 1 = Boot block not protected from table reads executed in other blocks
0 = Boot block protected from table reads executed in other blocks
DEV10:DEV3 DEVID2 Device ID bits
These bits are used with the DEV2:DEV0 bits in the DEVID1 register to
identify part number.
DEV2:DEV0 DEVID1 Device ID bits
These bits are used with the DEV10:DEV3 bits in the DEVID2 register to
identify part number.
REV4:REV0 These bits are used to indicate the revision of the device.
Note 1: Unimplemented in PIC18F6X8X (64-pin) devices; maintain this bit set.
2: Unimplemented in PIC18FX585 devices; maintain this bit set.
3: Reserved for PIC18F6X8X devices; maintain this bit set.
DS39606E-page 30 2010 Microchip Technology Inc.
PIC18FXX80/XX85
5.4 Embedding Configuration Word 5.5 Checksum Computation
Information in the HEX File The checksum is calculated by summing the following:
To allow portability of code, a PIC18FXX80/XX85 • The contents of all code memory locations
programmer is required to read the Configuration Word • The Configuration Word, appropriately masked
locations from the HEX file. If Configuration Word infor-
• ID locations
mation is not present in the HEX file, then a simple
warning message should be issued. Similarly, while The Least Significant 16 bits of this sum are the
saving a HEX file, all Configuration Word information checksum.
must be included. An option to not include the Configu- Table 5-4 (pages 32 through 35) describes how to
ration Word information may be provided. When calculate the checksum for each device.
embedding Configuration Word information in the HEX
file, it should start at address 300000h. Note: The checksum calculation differs depend-
ing on the code-protect setting. Since the
Microchip Technology Inc. feels strongly that this
code memory locations read out differently
feature is important for the benefit of the end customer.
depending on the code-protect setting, the
table describes how to manipulate the
actual code memory values to simulate
the values that would be read from a
protected device. When calculating a
checksum by reading a device, the entire
code memory can simply be read and
summed. The Configuration Word and ID
locations can always be read.
2010 Microchip Technology Inc. DS39606E-page 31
PIC18FXX80/XX85
TABLE 5-4: CHECKSUM COMPUTATION
0AAh at 0
Blank
Device Code-Protect Checksum and Max
Value
Address
None SUM(0000:07FFh) + SUM(0800:3FFFh) + SUM(4000:7FFFh) + 0C357h 0C2ADh
SUM(8000:0BFFFh) + (CFGW1L & 00h) + (CFGW1H & 2Fh) +
(CFGW2L & 0Fh) + (CFGW2H & 1Fh) + (CFGW3L & 00h) +
(CFGW3H & 80h) + (CFGW4L & 85h) + (CFGW4H & 00h) +
(CFGW5L & 07h) + (CFGW5H & 0C0h) + (CFGW6L & 07h) +
(CFGW6H & 0E0h) + (CFGW7L & 07h) + (CFGW7H & 40h)
Boot Block SUM(0800:3FFFh) + SUM(4000:7FFFh) + SUM(8000:0BFFFh) + 0BB32h 0BAE7h
(CFGW1L & 00h) + (CFGW1H & 2Fh) + (CFGW2L & 0Fh) +
(CFGW2H & 1Fh) + (CFGW3L & 00h) + (CFGW3H & 80h) +
(CFGW4L & 85h) + (CFGW4H & 00h) + (CFGW5L & 07h) +
(CFGW5H & 80h) + (CFGW6L & 07h) + (CFGW6H & 0E0h) +
PIC18F6585 (CFGW7L & 07h) + (CFGW7H & 40h) + SUM(IDs)
Boot/ SUM(8000:0BFFFh) + (CFGW1L & 00h) + (CFGW1H & 2Fh) + 432Fh 42E4h
Block 0/ (CFGW2L & 0Fh) + (CFGW2H & 1Fh) + (CFGW3L & 00h) +
Block 1 (CFGW3H & 80h) + (CFGW4L & 85h) + (CFGW4H & 00h) +
(CFGW5L & 04h) + (CFGW5H & 80h) + (CFGW6L & 07h) +
(CFGW6H & 0E0h) + (CFGW7L & 07h) + (CFGW7H & 40h) +
SUM(IDs)
All (CFGW1L & 00h) + (CFGW1H & 2Fh) + (CFGW2L & 0Fh) + 02A6h 02B5h
(CFGW2H & 1Fh) + (CFGW3L & 00h) + (CFGW3H & 80h) +
(CFGW4L & 85h) + (CFGW4H & 00h) + (CFGW5L & 00h) +
(CFGW5H & 00h) + (CFGW6L & 07h) + (CFGW6H & 0E0h) +
(CFGW7L & 07h) + (CFGW7H & 40h) + SUM(IDs)
Legend: Item Description
CFGW = Configuration Word
SUM[a:b] = Sum of locations, a to b inclusive
SUM_ID = Byte-wise sum of lower four bits of all customer ID locations
+ = Addition
& = Bit-wise AND
DS39606E-page 32 2010 Microchip Technology Inc.
PIC18FXX80/XX85
TABLE 5-4: CHECKSUM COMPUTATION (CONTINUED)
0AAh at 0
Blank
Device Code-Protect Checksum and Max
Value
Address
None SUM(0000:07FFh) + SUM(0800:3FFFh) + SUM(4000:7FFFh) + 036Fh 02C5h
SUM(8000:0BFFFh) + SUM(0C000:0FFFFh) + (CFGW1L & 00h) +
(CFGW1H & 2Fh) + (CFGW2L & 0Fh ) + (CFGW2H & 1Fh) +
(CFGW3L & 00h) + (CFGW3H & 80h) + (CFGW4L & 85h) +
(CFGW4H & 00h) + (CFGW5L & 0Fh) + (CFGW5H & 0C0h) +
(CFGW6L & 0Fh) + (CFGW6H & 0E0h) + (CFGW7L & 0Fh) +
(CFGW7H & 40h)
Boot Block SUM(0800:3FFFh) + SUM(4000:7FFFh) + SUM(8000:0BFFFh) + 0FB47h 0FAEDh
SUM(0C000:0FFFFh) + (CFGW1L & 00h) + (CFGW1H & 2Fh) +
(CFGW2L & 0Fh) + (CFGW2H & 1Fh) + (CFGW3L & 00h) +
(CFGW3H & 80h) + (CFGW4L & 85h) + (CFGW4H & 00h) +
(CFGW5L & 0Fh) + (CFGW5H & 80h) + (CFGW6L & 0Fh) +
PIC18F6680 (CFGW6H & 0E0h) + (CFGW7L & 0Fh) + (CFGW7H & 40h) +
SUM(IDs)
Boot/ SUM(8000:0BFFFh) + SUM(0C000:0FFFFh) + (CFGW1L & 00h) + 8344h 82EAh
Block1/ (CFGW1H & 2Fh) + (CFGW2L & 0Fh) + (CFGW2H & 1Fh) +
Block2 (CFGW3L & 00h) + (CFGW3H & 80h) + (CFGW4L & 85h) +
(CFGW4H & 00h) + (CFGW5L & 0Ch) + (CFGW5H & 80h) +
(CFGW6L & 0Fh) + (CFGW6H & 0E0h) + (CFGW7L & 0Fh) +
(CFGW7H & 40h) + SUM(IDs)
All (CFGW1L & 00h) + (CFGW1H & 2Fh) + (CFGW2L & 0Fh) + 02B8h 02B3h
(CFGW2H & 1Fh) + (CFGW3L & 00h) + (CFGW3H & 80h) +
(CFGW4L & 85h) + (CFGW4H & 00h) + (CFGW5L & 00h) +
(CFGW5H & 00h) + (CFGW6L & 0Fh) + (CFGW6H & 0E0h) +
(CFGW7L & 0Fh) + (CFGW7H & 40h) + SUM(IDs)
Legend: Item Description
CFGW = Configuration Word
SUM[a:b] = Sum of locations, a to b inclusive
SUM_ID = Byte-wise sum of lower four bits of all customer ID locations
+ = Addition
& = Bit-wise AND
2010 Microchip Technology Inc. DS39606E-page 33
PIC18FXX80/XX85
TABLE 5-4: CHECKSUM COMPUTATION (CONTINUED)
0AAh at 0
Blank
Device Code-Protect Checksum and Max
Value
Address
None SUM(0000:07FFh) + SUM(0800:3FFFh) + SUM(4000:7FFFh) + 0C3DAh 0C330h
SUM(8000:0BFFFh) + (CFGW1L & 00h) + (CFGW1H & 2Fh) +
(CFGW2L & 0Fh) + (CFGW2H & 1Fh) + (CFGW3L & 83h) +
(CFGW3H & 80h) + (CFGW4L & 85h) + (CFGW4H & 00h) +
(CFGW5L & 07h) + (CFGW5H & 0C0h) + (CFGW6L & 07h) +
(CFGW6H & 0E0h) + (CFGW7L & 07h) + (CFGW7H & 40h)
Boot Block SUM(0800:3FFFh) + SUM(4000:7FFFh) + SUM(8000:0BFFFh) + 0BBC0h 0BB57h
(CFGW1L & 00h) + (CFGW1H & 2Fh) + (CFGW2L & 0Fh) +
(CFGW2H & 1Fh) + (CFGW3L & 83h) + (CFGW3H & 80h) +
(CFGW4L & 85h) + (CFGW4H & 00h) + (CFGW5L & 07h) +
(CFGW5H & 80h) + (CFGW6L & 07h) + (CFGW6H & 0E0h) +
PIC18F8585 (CFGW7L & 07h) + (CFGW7H & 40h) + SUM(IDs)
Boot/ SUM(8000:0BFFFh) + (CFGW1L & 00h) + (CFGW1H & 2Fh) + 43BDh 4354h
Block1/ (CFGW2L & 0Fh) + (CFGW2H & 1Fh) + (CFGW3L & 83h) +
Block2 (CFGW3H & 80h) + (CFGW4L & 85h) + (CFGW4H & 00h) +
(CFGW5L & 04h) + (CFGW5H & 80h) + (CFGW6L & 07h) +
(CFGW6H & 0E0h) + (CFGW7L & 07h) + (CFGW7H & 40h) +
SUM(IDs)
All (CFGW1L & 00h) + (CFGW1H & 2Fh) + (CFGW2L & 0Fh) + 0339h 0325h
(CFGW2H & 1Fh) + (CFGW3L & 83h) + (CFGW3H & 80h) +
(CFGW4L & 85h) + (CFGW4H & 00h) + (CFGW5L & 00h) +
(CFGW5H & 00h) + (CFGW6L & 07h) + (CFGW6H & 0E0h) +
(CFGW7L & 07h) + (CFGW7H & 40h) + SUM(IDs)
Legend: Item Description
CFGW = Configuration Word
SUM[a:b] = Sum of locations, a to b inclusive
SUM_ID = Byte-wise sum of lower four bits of all customer ID locations
+ = Addition
& = Bit-wise AND
DS39606E-page 34 2010 Microchip Technology Inc.
PIC18FXX80/XX85
TABLE 5-4: CHECKSUM COMPUTATION (CONTINUED)
0AAh at 0
Blank
Device Code-Protect Checksum and Max
Value
Address
None SUM(0000:07FFh) + SUM(0800:3FFFh) + SUM(4000:7FFFh) + 03F2h 0348h
SUM(8000:0BFFFh) + SUM(0C000:0FFFFh) + (CFGW1L & 00h) +
(CFGW1H & 2Fh) + (CFGW2L & 0Fh) + (CFGW2H & 1Fh) +
(CFGW3L & 83h) + (CFGW3H & 80h) + (CFGW4L & 85h) +
(CFGW4H & 00h) + (CFGW5L & 0Fh) + (CFGW5H & 0C0h) +
(CFGW6L & 0Fh) + (CFGW6H & 0E0h) + (CFGW7L & 0Fh) +
(CFGW7H & 40h)
Boot Block SUM(0800:3FFFh) + SUM(4000:7FFFh) + SUM(8000:0BFFFh) + 0FBC6h 0FB6Ch
SUM(0C000:0FFFFh) + (CFGW1L & 00h) + (CFGW1H & 2Fh) +
(CFGW2L & 0Fh) + (CFGW2H & 1Fh) + (CFGW3L & 83h) +
(CFGW3H & 80h) + (CFGW4L & 85h) + (CFGW4H & 00h) +
(CFGW5L & 0Fh) + (CFGW5H & 80h) + (CFGW6L & 0Fh) +
PIC18F8680 (CFGW6H & 0E0h) + (CFGW7L & 0Fh) + (CFGW7H & 40h) +
SUM(IDs)
Boot/ SUM(8000:0BFFFh) + SUM(0C000:0FFFFh) + (CFGW1L & 00h) + 83C3h 8369h
Block1/ (CFGW1H & 2Fh) + (CFGW2L & 0Fh) + (CFGW2H & 1Fh) +
Block2 (CFGW3L & 83h) + (CFGW3H & 80h) + (CFGW4L & 85h) +
(CFGW4H & 00h) + (CFGW5L & 0Ch) + (CFGW5H & 80h) +
(CFGW6L & 0Fh) + (CFGW6H & 0E0h) + (CFGW7L & 0Fh) +
(CFGW7H & 40h) + SUM(IDs)
All (CFGW1L & 00h) + (CFGW1H & 2Fh) + (CFGW2L & 0Fh) + 0337h 0332h
(CFGW2H & 1Fh) + (CFGW3L & 83h) + (CFGW3H & 80h) +
(CFGW4L & 85h) + (CFGW4H & 00h) + (CFGW5L & 00h) +
(CFGW5H & 00h) + (CFGW6L & 0Fh) + (CFGW6H & 0E0h) +
(CFGW7L & 0Fh) + (CFGW7H & 40h) + SUM(IDs)
Legend: Item Description
CFGW = Configuration Word
SUM[a:b] = Sum of locations, a to b inclusive
SUM_ID = Byte-wise sum of lower four bits of all customer ID locations
+ = Addition
& = Bit-wise AND
5.6 Embedding Data EEPROM should be issued. Similarly, when saving a HEX file, all
Information in the HEX File data EEPROM information must be included. An option
to not include the data EEPROM information may be
To allow portability of code, a PIC18FXX80/XX85 provided. When embedding data EEPROM information
programmer is required to read the data EEPROM in the HEX file, it should start at address F00000h.
information from the HEX file. If data EEPROM infor-
Microchip Technology Inc. believes that this feature is
mation is not present, a simple warning message
important for the benefit of the end customer.
2010 Microchip Technology Inc. DS39606E-page 35
PIC18FXX80/XX85
6.0 AC/DC CHARACTERISTICS TIMING REQUIREMENTS FOR
PROGRAM/VERIFY TEST MODE
Standard Operating Conditions
Operating Temperature: 25C is recommended
Param
Sym Characteristic Min Max Units Conditions
No.
D110 VIHH High-Voltage Programming Voltage on 9.00 13.25 V
MCLR/VPP
D110A VIHL Low-Voltage Programming Voltage on 2.00 5.50 V
MCLR/VPP
D111 VDD Supply Voltage During Programming 2.00 5.50 V Normal programming
4.50 5.50 V Bulk Erase operations
D112 IPP Programming Current on MCLR/VPP — 300 A
D113 IDDP Supply Current During Programming — 10 mA
D031 VIL Input Low Voltage VSS 0.2 VDD V
D041 VIH Input High Voltage 0.8 VDD VDD V
D080 VOL Output Low Voltage — 0.6 V IOL = 8.5 mA @ 4.5V
D090 VOH Output High Voltage VDD – 0.7 — V IOH = -3.0 mA @ 4.5V
D012 CIO Capacitive Loading on I/O pin (PGD) — 50 pF To meet AC specifications
P1 Tr MCLR/VPP Rise Time to Enter — 1.0 s (Note 1)
Program/Verify mode
P2 Tsclk Serial Clock (PGC) Period 100 — ns
P2A TsclkL Serial Clock (PGC) Low Time 40 — ns
P2B TsclkH Serial Clock (PGC) High Time 40 — ns
P3 Tset1 Input Data Setup Time to Serial Clock 15 — ns
P4 Thld1 Input Data Hold Time from PGC 15 — ns
P5 Tdly1 Delay Between 4-Bit Command and 40 — ns
Command Operand
P5A Tdly1a Delay Between 4-Bit Command 40 — ns
Operand and Next 4-Bit Command
P6 Tdly2 Delay Between Last PGC of 20 — ns
Command Byte to First PGC of Read
of Data Word
P9 Tdly5 PGC High Time 1 — ms
(minimum programming time)
P10 Tdly6 PGC Low Time After Programming 5 — s
(high-voltage discharge time)
P11 Tdly7 Delay to Allow Self-Timed Data Write or 10 — ms
Bulk Erase to Occur
P11A Tdrwt Data Write Polling Time 4 — ms
P12 Thld2 Input Data Hold Time from MCLR/VPP 2 — s
P13 Tset2 VDD Setup Time to MCLR/VPP 100 — ns
P14 Tvalid Data Out Valid from PGC 10 — ns
P15 Tset3 PGM Setup Time to MCLR/VPP 2 — s
Note 1: Do not allow excess time when transitioning MCLR between VIL and VIHH; this can cause spurious program
executions to occur. The maximum transition time is:
1 TCY + TPWRT (if enabled) + 1024 TOSC (for LP, HS, HS/PLL and XT modes only)
+ 2 ms (for HS/PLL mode only) + 1.5 s (for EC mode only)
where TCY is the instruction cycle time, TPWRT is the Power-up Timer period and TOSC is the oscillator period.
For specific values, refer to the Electrical Characteristics section of the device data sheet for the particular device.
DS39606E-page 36 2010 Microchip Technology Inc.
Note the following details of the code protection feature on Microchip devices:
• Microchip products meet the specification contained in their particular Microchip Data Sheet.
• Microchip believes that its family of products is one of the most secure families of its kind on the market today, when used in the
intended manner and under normal conditions.
• There are dishonest and possibly illegal methods used to breach the code protection feature. All of these methods, to our
knowledge, require using the Microchip products in a manner outside the operating specifications contained in Microchip’s Data
Sheets. Most likely, the person doing so is engaged in theft of intellectual property.
• Microchip is willing to work with the customer who is concerned about the integrity of their code.
• Neither Microchip nor any other semiconductor manufacturer can guarantee the security of their code. Code protection does not
mean that we are guaranteeing the product as “unbreakable.”
Code protection is constantly evolving. We at Microchip are committed to continuously improving the code protection features of our
products. Attempts to break Microchip’s code protection feature may be a violation of the Digital Millennium Copyright Act. If such acts
allow unauthorized access to your software or other copyrighted work, you may have a right to sue for relief under that Act.
Information contained in this publication regarding device Trademarks
applications and the like is provided only for your convenience
The Microchip name and logo, the Microchip logo, dsPIC,
and may be superseded by updates. It is your responsibility to
KEELOQ, KEELOQ logo, MPLAB, PIC, PICmicro, PICSTART,
ensure that your application meets with your specifications.
rfPIC and UNI/O are registered trademarks of Microchip
MICROCHIP MAKES NO REPRESENTATIONS OR
Technology Incorporated in the U.S.A. and other countries.
WARRANTIES OF ANY KIND WHETHER EXPRESS OR
IMPLIED, WRITTEN OR ORAL, STATUTORY OR FilterLab, Hampshire, HI-TECH C, Linear Active Thermistor,
OTHERWISE, RELATED TO THE INFORMATION, MXDEV, MXLAB, SEEVAL and The Embedded Control
INCLUDING BUT NOT LIMITED TO ITS CONDITION, Solutions Company are registered trademarks of Microchip
QUALITY, PERFORMANCE, MERCHANTABILITY OR Technology Incorporated in the U.S.A.
FITNESS FOR PURPOSE. Microchip disclaims all liability Analog-for-the-Digital Age, Application Maestro, CodeGuard,
arising from this information and its use. Use of Microchip dsPICDEM, dsPICDEM.net, dsPICworks, dsSPEAK, ECAN,
devices in life support and/or safety applications is entirely at ECONOMONITOR, FanSense, HI-TIDE, In-Circuit Serial
the buyer’s risk, and the buyer agrees to defend, indemnify and Programming, ICSP, Mindi, MiWi, MPASM, MPLAB Certified
hold harmless Microchip from any and all damages, claims, logo, MPLIB, MPLINK, mTouch, Octopus, Omniscient Code
suits, or expenses resulting from such use. No licenses are Generation, PICC, PICC-18, PICDEM, PICDEM.net, PICkit,
conveyed, implicitly or otherwise, under any Microchip PICtail, PIC32 logo, REAL ICE, rfLAB, Select Mode, Total
intellectual property rights. Endurance, TSHARC, UniWinDriver, WiperLock and ZENA
are trademarks of Microchip Technology Incorporated in the
U.S.A. and other countries.
SQTP is a service mark of Microchip Technology Incorporated
in the U.S.A.
All other trademarks mentioned herein are property of their
respective companies.
© 2010, Microchip Technology Incorporated, Printed in the
U.S.A., All Rights Reserved.
Printed on recycled paper.
Microchip received ISO/TS-16949:2002 certification for its worldwide
headquarters, design and wafer fabrication facilities in Chandler and
Tempe, Arizona; Gresham, Oregon and design centers in California
and India. The Company’s quality system processes and procedures
are for its PIC® MCUs and dsPIC® DSCs, KEELOQ® code hopping
devices, Serial EEPROMs, microperipherals, nonvolatile memory and
analog products. In addition, Microchip’s quality system for the design
and manufacture of development systems is ISO 9001:2000 certified.
2010 Microchip Technology Inc. DS39606E-page 37
WORLDWIDE SALES AND SERVICE
AMERICAS ASIA/PACIFIC ASIA/PACIFIC EUROPE
Corporate Office Asia Pacific Office India - Bangalore Austria - Wels
2355 West Chandler Blvd. Suites 3707-14, 37th Floor Tel: 91-80-3090-4444 Tel: 43-7242-2244-39
Chandler, AZ 85224-6199 Tower 6, The Gateway Fax: 91-80-3090-4123 Fax: 43-7242-2244-393
Tel: 480-792-7200 Harbour City, Kowloon Denmark - Copenhagen
India - New Delhi
Fax: 480-792-7277 Hong Kong Tel: 45-4450-2828
Tel: 91-11-4160-8631
Technical Support: Tel: 852-2401-1200 Fax: 45-4485-2829
Fax: 91-11-4160-8632
http://support.microchip.com Fax: 852-2401-3431
India - Pune France - Paris
Web Address:
Australia - Sydney Tel: 91-20-2566-1512 Tel: 33-1-69-53-63-20
www.microchip.com
Tel: 61-2-9868-6733 Fax: 91-20-2566-1513 Fax: 33-1-69-30-90-79
Atlanta Fax: 61-2-9868-6755
Japan - Yokohama Germany - Munich
Duluth, GA
China - Beijing Tel: 49-89-627-144-0
Tel: 678-957-9614 Tel: 81-45-471- 6166
Tel: 86-10-8528-2100 Fax: 49-89-627-144-44
Fax: 678-957-1455 Fax: 81-45-471-6122
Fax: 86-10-8528-2104 Italy - Milan
Boston Korea - Daegu
China - Chengdu Tel: 39-0331-742611
Westborough, MA Tel: 82-53-744-4301
Tel: 86-28-8665-5511 Fax: 39-0331-466781
Tel: 774-760-0087 Fax: 82-53-744-4302
Fax: 86-28-8665-7889 Netherlands - Drunen
Fax: 774-760-0088 Korea - Seoul
China - Chongqing Tel: 82-2-554-7200 Tel: 31-416-690399
Chicago
Tel: 86-23-8980-9588 Fax: 82-2-558-5932 or Fax: 31-416-690340
Itasca, IL
Tel: 630-285-0071 Fax: 86-23-8980-9500 82-2-558-5934 Spain - Madrid
Fax: 630-285-0075 China - Hong Kong SAR Tel: 34-91-708-08-90
Malaysia - Kuala Lumpur
Tel: 852-2401-1200 Tel: 60-3-6201-9857 Fax: 34-91-708-08-91
Cleveland
Independence, OH Fax: 852-2401-3431 Fax: 60-3-6201-9859 UK - Wokingham
Tel: 216-447-0464 China - Nanjing Tel: 44-118-921-5869
Malaysia - Penang
Fax: 216-447-0643 Tel: 86-25-8473-2460 Fax: 44-118-921-5820
Tel: 60-4-227-8870
Dallas Fax: 86-25-8473-2470 Fax: 60-4-227-4068
Addison, TX China - Qingdao Philippines - Manila
Tel: 972-818-7423 Tel: 86-532-8502-7355 Tel: 63-2-634-9065
Fax: 972-818-2924 Fax: 86-532-8502-7205 Fax: 63-2-634-9069
Detroit China - Shanghai Singapore
Farmington Hills, MI Tel: 86-21-5407-5533 Tel: 65-6334-8870
Tel: 248-538-2250 Fax: 86-21-5407-5066 Fax: 65-6334-8850
Fax: 248-538-2260
China - Shenyang Taiwan - Hsin Chu
Kokomo Tel: 86-24-2334-2829 Tel: 886-3-6578-300
Kokomo, IN Fax: 86-24-2334-2393 Fax: 886-3-6578-370
Tel: 765-864-8360
Fax: 765-864-8387 China - Shenzhen Taiwan - Kaohsiung
Tel: 86-755-8203-2660 Tel: 886-7-536-4818
Los Angeles Fax: 86-755-8203-1760 Fax: 886-7-536-4803
Mission Viejo, CA
Tel: 949-462-9523 China - Wuhan Taiwan - Taipei
Fax: 949-462-9608 Tel: 86-27-5980-5300 Tel: 886-2-2500-6610
Fax: 86-27-5980-5118 Fax: 886-2-2508-0102
Santa Clara
Santa Clara, CA China - Xian Thailand - Bangkok
Tel: 408-961-6444 Tel: 86-29-8833-7252 Tel: 66-2-694-1351
Fax: 408-961-6445 Fax: 86-29-8833-7256 Fax: 66-2-694-1350
Toronto China - Xiamen
Mississauga, Ontario, Tel: 86-592-2388138
Canada Fax: 86-592-2388130
Tel: 905-673-0699 China - Zhuhai
Fax: 905-673-6509 Tel: 86-756-3210040
Fax: 86-756-3210049
01/05/10
DS39606E-page 38 2010 Microchip Technology Inc.
You might also like
- Brand Positioning The Battle of The Mind: Mccormick vs. FuchsDocument12 pagesBrand Positioning The Battle of The Mind: Mccormick vs. FuchsLaura Mng100% (1)
- 41439ADocument38 pages41439AHugo LoureiroNo ratings yet
- Tai Lieu Thi Nghiem VXL Top 100 - ModifyDocument33 pagesTai Lieu Thi Nghiem VXL Top 100 - ModifyTrần Anh KhoaNo ratings yet
- PIC18FXX2/XX8: Flash Microcontroller Programming SpecificationDocument36 pagesPIC18FXX2/XX8: Flash Microcontroller Programming Specificationhkn89No ratings yet
- GPSUser ManualDocument15 pagesGPSUser ManualaravindbprasadNo ratings yet
- PIC16F88X Memory Programming Specification PDFDocument36 pagesPIC16F88X Memory Programming Specification PDFMarcio FreitasNo ratings yet
- PIC16F87XDocument218 pagesPIC16F87Xaprilila5555No ratings yet
- KeypadDocument1 pageKeypadPhap Nguyen100% (1)
- 16F88Document24 pages16F88thetkhinechoNo ratings yet
- 41208CDocument16 pages41208CFernando ANo ratings yet
- DatasheetDocument52 pagesDatasheetSergio CastilloNo ratings yet
- 16F87X Datasheet - Version ResumidaDocument69 pages16F87X Datasheet - Version ResumidamowliwhiteNo ratings yet
- Datasheet PIC16f870Document9 pagesDatasheet PIC16f870Esteban AdrianNo ratings yet
- 16F877 Data SheetDocument201 pages16F877 Data Sheetjohn11221No ratings yet
- Datasheet Pic 16 F 871Document172 pagesDatasheet Pic 16 F 871Sound AplicacionNo ratings yet
- PIC16F88X Memory Programming SpecificationDocument36 pagesPIC16F88X Memory Programming Specificationwin.halongNo ratings yet
- Da DKCNDocument3 pagesDa DKCNTrọng LêNo ratings yet
- ELD310Document44 pagesELD310Nhật Tú TrầnNo ratings yet
- PIC-WEB-BOX, Board Revision C - PORT PINOUTDocument1 pagePIC-WEB-BOX, Board Revision C - PORT PINOUTalo 247No ratings yet
- SDNL 1Document1 pageSDNL 1Trọng LêNo ratings yet
- 11PDSPL2Document9 pages11PDSPL2MokbelNo ratings yet
- 21ee602 Microcontrollers Based System DesignDocument3 pages21ee602 Microcontrollers Based System Designdhanush.ee21No ratings yet
- 7.3. Analog Input: Embedded System DesignDocument23 pages7.3. Analog Input: Embedded System DesignGia HuyNo ratings yet
- Circuito EletrônicoDocument1 pageCircuito EletrônicoLucas Pardinho MoraisNo ratings yet
- Mitsubishi Melsec ACPUeaDocument15 pagesMitsubishi Melsec ACPUeaismail yılmazNo ratings yet
- Delta PLC ManualDocument7 pagesDelta PLC ManualRoyal Ritesh SharmaNo ratings yet
- Gesture Controlled Slide NavigatorDocument17 pagesGesture Controlled Slide NavigatorAnkur GuptaNo ratings yet
- Digitronik CPL Communication SDC40A/40G User's ManualDocument66 pagesDigitronik CPL Communication SDC40A/40G User's ManualnarkomanizcaNo ratings yet
- PIC16C773Document202 pagesPIC16C773Luis Oliveira SilvaNo ratings yet
- BAI 1 - Led Don - 7 DoanDocument7 pagesBAI 1 - Led Don - 7 DoanTrần Ngọc Thiên DiNo ratings yet
- Lector de Bus de Datos IÂ CDocument4 pagesLector de Bus de Datos IÂ CGiancarloRichardRivadeneyraMiranda100% (1)
- MẠCH ĐIỆNDocument1 pageMẠCH ĐIỆNThịnh Nguyễn vănNo ratings yet
- INTERFACE_BOARD_MANUAL_A5Document20 pagesINTERFACE_BOARD_MANUAL_A5SHIREESHA.RNo ratings yet
- Datasheet - HK Pic16f73 271716 PDFDocument168 pagesDatasheet - HK Pic16f73 271716 PDFAbdul QadirNo ratings yet
- Acrosser Technology AR B1673 DatasheetDocument5 pagesAcrosser Technology AR B1673 DatasheetWaleed MareeNo ratings yet
- About The Device/PLC Connection ManualsDocument27 pagesAbout The Device/PLC Connection Manualskoniks519No ratings yet
- Dokumen - Tips - 11 Siemens s5s7 Series M2icokr Siemen11 Siemens s5s7 Series s5 95uDocument20 pagesDokumen - Tips - 11 Siemens s5s7 Series M2icokr Siemen11 Siemens s5s7 Series s5 95uzahra ghaziNo ratings yet
- AR-B5500 MANUAL: Setting Up The SystemDocument5 pagesAR-B5500 MANUAL: Setting Up The SystemTrentungcaysoBombodealopNo ratings yet
- About The Device/PLC Connection ManualsDocument7 pagesAbout The Device/PLC Connection ManualsDenisNo ratings yet
- Lecture 3Document39 pagesLecture 3Nour Ziad Ibrahim AlkurdiNo ratings yet
- DS8884B 01Document46 pagesDS8884B 01semar bypasNo ratings yet
- NFCDocument8 pagesNFCkorada sai kumarNo ratings yet
- PIC16F87XA: TABLE 8-5: Registers Associated With PWM and Timer2Document5 pagesPIC16F87XA: TABLE 8-5: Registers Associated With PWM and Timer2vitor valeNo ratings yet
- PIC16F882/883/884/886/887: 28/40/44-Pin Flash-Based, 8-Bit CMOS MicrocontrollersDocument78 pagesPIC16F882/883/884/886/887: 28/40/44-Pin Flash-Based, 8-Bit CMOS Microcontrollersfranklin monteroNo ratings yet
- 10RPG2Document7 pages10RPG2MokbelNo ratings yet
- PC Term Rj45 8pin Altpin Db9fDocument1 pagePC Term Rj45 8pin Altpin Db9fAntonioNo ratings yet
- Architecture of PIC18F4550Document1 pageArchitecture of PIC18F4550veeramaniks408No ratings yet
- Manual GPW Shimaden Mh01eDocument31 pagesManual GPW Shimaden Mh01esyafi udinNo ratings yet
- EBB_v23_schDocument1 pageEBB_v23_schحساب 1No ratings yet
- Esmsr 2 KV 6Document10 pagesEsmsr 2 KV 6Procurement PardisanNo ratings yet
- Usbmod1: USB Plug and Play Serial Development ModuleDocument5 pagesUsbmod1: USB Plug and Play Serial Development ModuleMaiChiVuNo ratings yet
- Rak3172-Sip Wisduo Lpwan Sip Datasheet: DescriptionDocument9 pagesRak3172-Sip Wisduo Lpwan Sip Datasheet: DescriptionoliviercorianNo ratings yet
- Maintenance Manual: Vbm/Vfm/Vfs/Vtm/Vps Series Abm/Afm/Afs/Atm/Aps SeriesDocument72 pagesMaintenance Manual: Vbm/Vfm/Vfs/Vtm/Vps Series Abm/Afm/Afs/Atm/Aps SeriesTian TianNo ratings yet
- Basic 16f877Document1 pageBasic 16f877api-27535945100% (1)
- About The Device/PLC Connection ManualsDocument10 pagesAbout The Device/PLC Connection Manualshitesh sanchaniyaNo ratings yet
- PICmem Prog SpecDocument38 pagesPICmem Prog SpecdkelicNo ratings yet
- PIC16F877A[001-003]Document3 pagesPIC16F877A[001-003]RitzysQNo ratings yet
- PIC16F87XA: 28/40/44-Pin Enhanced Flash MicrocontrollersDocument235 pagesPIC16F87XA: 28/40/44-Pin Enhanced Flash MicrocontrollersEmmanuel PeralesNo ratings yet
- PLC: Programmable Logic Controller – Arktika.: EXPERIMENTAL PRODUCT BASED ON CPLD.From EverandPLC: Programmable Logic Controller – Arktika.: EXPERIMENTAL PRODUCT BASED ON CPLD.No ratings yet
- IEEE 1149.6 - A Practical PerspectiveDocument9 pagesIEEE 1149.6 - A Practical Perspective18810175224No ratings yet
- Strap Grid Tubular Plate - A New Positive Plate For Lead-Acid BatteriesDocument36 pagesStrap Grid Tubular Plate - A New Positive Plate For Lead-Acid Batteriesantony2288No ratings yet
- Service Experience (OCSE) Using The Emerging Consensus Technique (ECT)Document41 pagesService Experience (OCSE) Using The Emerging Consensus Technique (ECT)Naveen KNo ratings yet
- Code Switching and Code MixingDocument2 pagesCode Switching and Code MixingAtif HaiderNo ratings yet
- Cure My Addiction: The Unofficial Walkthrough and Event GuideDocument71 pagesCure My Addiction: The Unofficial Walkthrough and Event GuideImron GinanjarNo ratings yet
- 5976 24273 1 PBDocument11 pages5976 24273 1 PBDaisy Mee CrujidoNo ratings yet
- II Quickwrite 2016Document2 pagesII Quickwrite 2016api-292711328No ratings yet
- Pressure Die Casting - Al - NewDocument17 pagesPressure Die Casting - Al - Newhardeep SinghNo ratings yet
- Experience Gokul BoopathiDocument4 pagesExperience Gokul BoopathiKeerthi VarshiniNo ratings yet
- Eco MCQ 1 Multiple Choice Questions MCQ For Economics 1 BallbbballbDocument10 pagesEco MCQ 1 Multiple Choice Questions MCQ For Economics 1 BallbbballbsanchiNo ratings yet
- Mathematics 3Document2 pagesMathematics 3Tony StarkNo ratings yet
- Curs 11Document29 pagesCurs 11Aniculaesi MirceaNo ratings yet
- SNGPL - Web BillDocument1 pageSNGPL - Web BillNazeer Ahmed100% (1)
- Automatic Fire Control System in Railways 1Document44 pagesAutomatic Fire Control System in Railways 1RAJ50% (2)
- Seminar Report DemoDocument5 pagesSeminar Report Demonomaan_farooqiNo ratings yet
- Barton Floco Fra Automatic Sampler User ManualDocument40 pagesBarton Floco Fra Automatic Sampler User ManualedwinmenaNo ratings yet
- DBA CockpitDocument337 pagesDBA Cockpithimanshu.singh0011282No ratings yet
- Cat 2007 Productline EnglishDocument24 pagesCat 2007 Productline EnglishDan PatchNo ratings yet
- MC3x063A 1.5-A Peak Boost/Buck/Inverting Switching RegulatorsDocument30 pagesMC3x063A 1.5-A Peak Boost/Buck/Inverting Switching RegulatorsImadMehdiNo ratings yet
- Brunswick Manual Preinstalacion GSXDocument33 pagesBrunswick Manual Preinstalacion GSXroberto dominguezNo ratings yet
- Japanese Book Recipes Digital VerDocument5 pagesJapanese Book Recipes Digital VerTheagenes ThasosNo ratings yet
- 03 Big Data Concepts - Providing Stucture To Unstructured DataDocument26 pages03 Big Data Concepts - Providing Stucture To Unstructured DataLow Wai LeongNo ratings yet
- Measures of Central Tendency and Dispersion (Week-07)Document44 pagesMeasures of Central Tendency and Dispersion (Week-07)Sarmad Altaf Hafiz Altaf HussainNo ratings yet
- Project ProposalDocument4 pagesProject ProposalQueenie Diane MontañoNo ratings yet
- Skylab 3 PAO Mission Commentary 3 of 6Document851 pagesSkylab 3 PAO Mission Commentary 3 of 6Bob AndrepontNo ratings yet
- Example of Business Case ReportDocument3 pagesExample of Business Case ReportCORINE NDLOVUNo ratings yet
- Global Issues Data Response Questions AdviceDocument9 pagesGlobal Issues Data Response Questions Adviceapi-261914272No ratings yet
- User Manual: Promia 50 Application - Material HandlingDocument110 pagesUser Manual: Promia 50 Application - Material Handlingred_shobo_85100% (2)
- T REC G.984.4 200911 I!Amd2!PDF EDocument164 pagesT REC G.984.4 200911 I!Amd2!PDF ERoberto CardosoNo ratings yet



















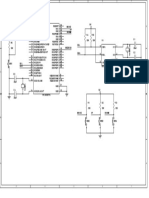

































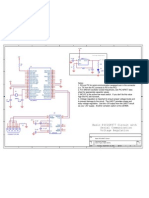


![PIC16F877A[001-003]](https://imgv2-2-f.scribdassets.com/img/document/749441096/149x198/6dd2f74fc1/1720630417?v=1)