Professional Documents
Culture Documents
Index CNS 57
Index CNS 57
Uploaded by
sekecik9440 ratings0% found this document useful (0 votes)
3 views1 pageOriginal Title
INDEX_CNS_57[2]
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
Download as pdf or txt
0 ratings0% found this document useful (0 votes)
3 views1 pageIndex CNS 57
Index CNS 57
Uploaded by
sekecik944Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
Download as pdf or txt
You are on page 1of 1
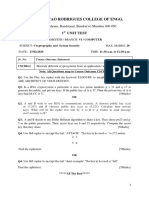
INDEX
PEN : 220843131008
NAME : Patil Rohan Manoj
SUBJECT : Cryptography & Network Security (3161606)
SR. DATE TITLE PG. GRADE SIGNATURE
NO. NO.
Implement RSA algorithm. Take plaintext
1
message M, Ciphertext C=Me mod n. To get
plaintext from ciphertext M=Cd mod n
Implement Playfair cipher. The plaintext is
2
paired in two characters. Discuss the advantage
of polyalphabetic cipher over monoalphabetic
cipher Key=MONARCHY
Plaintext = ar mu hs ea
Ciphertext = RM CM BP IM
Implement Caesar and Hill cipher. Both are
3 substitution cipher.Caesar cipher - You are given
plaintext Hello, Welcome. The key used is 3.
Implement Euclid algorithm to find GCD.
4
GCD(16,12) = 4 GCD (12,4) = 0 Then 4 is the
GCD (16,12)
Implement Euler’s totient function (n). It is
5
defined as the number of positive integers less
than n and relatively prime to n. Find (35) and
(37). Observe the value and analyze the
behaviour of totient function
Implement rail Fence and transposition cipher
6
7 To implement Simple DES to generate key
Implement Diffie-Hellman Key exchange
8 Method
9 Write a program to generate SHA-1 hash
Read traffic going on network. Analyze the
10 traffic. Connect to internet and read what is
going on internet. Hint: Use Wireshark
You might also like
- Cryptography and Message AuthenticationDocument96 pagesCryptography and Message Authenticationnitin saraswatNo ratings yet
- Cs8792 Cryptography and Network Security KeyDocument9 pagesCs8792 Cryptography and Network Security KeyLATHA PNo ratings yet
- Mca Cns RecordDocument86 pagesMca Cns Recordanilwurity5727No ratings yet
- CSS - Lab Manual 2023-24 Even SemDocument40 pagesCSS - Lab Manual 2023-24 Even SempokemonruseNo ratings yet
- A Brief Talk On RSADocument18 pagesA Brief Talk On RSAআশিষকুমারঘোষNo ratings yet
- Cryptography: Pratiksha PatilDocument48 pagesCryptography: Pratiksha PatilNune SrinivasRaoNo ratings yet
- Cacd 15,16Document27 pagesCacd 15,16Ajay KumarNo ratings yet
- 9.public Key Cryptography and RSADocument33 pages9.public Key Cryptography and RSAemmanuelauko4No ratings yet
- CryptoDocument24 pagesCryptoshivani.cs1995No ratings yet
- 2 Marks and 16 MarksDocument14 pages2 Marks and 16 Markssathyaaaaa1No ratings yet
- Hybrid Public Key Cryptosystem Combining RSA & DES AlgorithmsDocument6 pagesHybrid Public Key Cryptosystem Combining RSA & DES Algorithmskisi diribaNo ratings yet
- CSS Lab ManualDocument32 pagesCSS Lab ManualQaif AmzNo ratings yet
- 19 Asymmetric Key Cryptography 1Document32 pages19 Asymmetric Key Cryptography 1mohanNo ratings yet
- Diffie Hellman Key & ELiptic Curve - 3Document23 pagesDiffie Hellman Key & ELiptic Curve - 3RAMESH M (RA2113003011001)No ratings yet
- A Positive Lattice Application To RSA CryptosystemDocument5 pagesA Positive Lattice Application To RSA CryptosystemInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- INS - Assignment 1 (TCS2223033)Document8 pagesINS - Assignment 1 (TCS2223033)Kavinesh 123No ratings yet
- RSA AlgorithmDocument22 pagesRSA AlgorithmmathpalsonuNo ratings yet
- Unit 3 Network SecurityDocument18 pagesUnit 3 Network SecurityPrecious MposaNo ratings yet
- Cryptography and Network SecurityDocument24 pagesCryptography and Network SecuritykavithamargretNo ratings yet
- Asymmetric or Public Key CryptographyDocument55 pagesAsymmetric or Public Key CryptographySriharshitha DeepalaNo ratings yet
- RC 4Document17 pagesRC 4CHAITANYA KRISHNA CHAUHANNo ratings yet
- Lecture 2 C Public Key CryptographyDocument27 pagesLecture 2 C Public Key CryptographyKedir MohammedNo ratings yet
- Chapter 9 - Public Key Cryptography and RSADocument26 pagesChapter 9 - Public Key Cryptography and RSAswarna_793238588No ratings yet
- RSA AlgorithmDocument6 pagesRSA AlgorithmthiyagupsgNo ratings yet
- Improvised Asymmetric Key Encryption Algorithm Using MATLABDocument6 pagesImprovised Asymmetric Key Encryption Algorithm Using MATLABIOSRjournalNo ratings yet
- ISS Notes Unit-3Document48 pagesISS Notes Unit-3CHIRAG GUPTA PCE19IT010No ratings yet
- This Article Is About An Algorithm For Public-Key Encryption. For The U.S. Encryption and Network Security Company, See - For Other Uses, SeeDocument27 pagesThis Article Is About An Algorithm For Public-Key Encryption. For The U.S. Encryption and Network Security Company, See - For Other Uses, SeeSonali PanigrahiNo ratings yet
- New Crypto Lab FileDocument24 pagesNew Crypto Lab FilemyteamalokNo ratings yet
- QP UT1 CSC401 CryptographyandSystemSecurityDocument1 pageQP UT1 CSC401 CryptographyandSystemSecuritysunil chaudhariNo ratings yet
- RSA Algorithm: D e D EdDocument31 pagesRSA Algorithm: D e D EdSmrithy JichinNo ratings yet
- Chapter-3 Computer SecurityDocument67 pagesChapter-3 Computer SecurityKetoran OliNo ratings yet
- Chapter 3 - Cryptography and Encryption TechniquesDocument88 pagesChapter 3 - Cryptography and Encryption TechniquesEthio FanaNo ratings yet
- L 05 Cryptographyandapplications 160825094546Document73 pagesL 05 Cryptographyandapplications 160825094546kavisandeepaniNo ratings yet
- Cryptography and Network Security: by William StallingsDocument26 pagesCryptography and Network Security: by William StallingsPriyanka Singh SengarNo ratings yet
- Cryptography and Network SecurityDocument18 pagesCryptography and Network Securityashodhiya14No ratings yet
- Rsa and Elgamal AlgorithmsDocument13 pagesRsa and Elgamal AlgorithmsAbhinav ChinnalaNo ratings yet
- RSA in Prac4ce: Public Key Encryp4on From Trapdoor Permuta4onsDocument9 pagesRSA in Prac4ce: Public Key Encryp4on From Trapdoor Permuta4onssmslcaNo ratings yet
- Cryptosystem An Implementation of RSA Using VerilogDocument8 pagesCryptosystem An Implementation of RSA Using VerilogInternational Journal of Computer Networks and Communications SecurityNo ratings yet
- Fault AttackDocument100 pagesFault Attackaishik2002aNo ratings yet
- FCoDS - W7 - Public Key CryptographyDocument58 pagesFCoDS - W7 - Public Key CryptographyTrần Lưu Hồng PhươngNo ratings yet
- InfoSecurity Lect Week3Document31 pagesInfoSecurity Lect Week3Shaheer ArshadNo ratings yet
- Modified RSA Public Key Cryptosystem Using Two Key PairsDocument3 pagesModified RSA Public Key Cryptosystem Using Two Key PairsJainul AbudinNo ratings yet
- Rsa (Cryptosystem) : RsaisaDocument10 pagesRsa (Cryptosystem) : RsaisaXerus AnatasNo ratings yet
- A Comparison Between Encryption and Decryption'Document15 pagesA Comparison Between Encryption and Decryption'2010roomiNo ratings yet
- CNS Question Bank For CIA 1Document3 pagesCNS Question Bank For CIA 1aswinsee796No ratings yet
- An Algorithm To Enhance Security in RSADocument5 pagesAn Algorithm To Enhance Security in RSAENNAJARNo ratings yet
- Rsa AlgorithmDocument11 pagesRsa AlgorithmChronicleNo ratings yet
- Crypto TPDocument13 pagesCrypto TPSk SharmaNo ratings yet
- PKC AlgorithmDocument20 pagesPKC AlgorithmRicha SinghNo ratings yet
- 2.Cnvt Ins Lab (Std-Net2) ConvDocument62 pages2.Cnvt Ins Lab (Std-Net2) ConvkanchanaNo ratings yet
- Smt. Radhikatai Pandav College of Engineering NagpurDocument34 pagesSmt. Radhikatai Pandav College of Engineering NagpurMadhuri RahangdaleNo ratings yet
- Gautam Gambhir Unit 2Document19 pagesGautam Gambhir Unit 2huntfortechNo ratings yet
- Unit2 Cryptography and Cyber SecurityDocument4 pagesUnit2 Cryptography and Cyber SecuritypraveenaNo ratings yet
- Chapter 4Document84 pagesChapter 4Ahmed MohammedNo ratings yet
- Cryptography Lab Manual-FinalDocument36 pagesCryptography Lab Manual-FinalPraveen TPNo ratings yet
- Private-Key CryptographyDocument30 pagesPrivate-Key CryptographySrikar DuddukuriNo ratings yet
- Lecture 9Document86 pagesLecture 9Alhussain DarbiNo ratings yet
- CB3491-CCS 2marksDocument12 pagesCB3491-CCS 2markssmitcse2021No ratings yet
- Public Key CryptographyDocument13 pagesPublic Key CryptographyNaga sai ChallaNo ratings yet