Professional Documents
Culture Documents
12security and Dependability Specifications
12security and Dependability Specifications
Uploaded by
Anil LamaCopyright:
Available Formats
You might also like
- LOPADocument125 pagesLOPAOlvis Guillen100% (1)
- Element IC5: Work Equipment (General) : Unit IC: Suggested Answers To Revision Questions, IC1-IC5Document4 pagesElement IC5: Work Equipment (General) : Unit IC: Suggested Answers To Revision Questions, IC1-IC5memolidarnahNo ratings yet
- Volume 1 - 2 Day Architect Training Adobe Experience Manager v.6.xDocument102 pagesVolume 1 - 2 Day Architect Training Adobe Experience Manager v.6.xKiril DelovskiNo ratings yet
- 1 Chapter 12 Dependability and Security SpecificationDocument55 pages1 Chapter 12 Dependability and Security Specificationkayosh dhungelNo ratings yet
- 1 Chapter 12 Dependability and Security SpecificationDocument55 pages1 Chapter 12 Dependability and Security SpecificationEr Ravi GuptaNo ratings yet
- Why SIL3? Josse Brys TUV EngineerDocument38 pagesWhy SIL3? Josse Brys TUV Engineersina20795No ratings yet
- Critical Systems Specification: ©ian Sommerville 2004Document50 pagesCritical Systems Specification: ©ian Sommerville 2004jnax101No ratings yet
- Welding Robots Technology System Issues and Applications - J Norberto PiresDocument76 pagesWelding Robots Technology System Issues and Applications - J Norberto PireshetpinNo ratings yet
- Health Care Risk AssessmentDocument81 pagesHealth Care Risk AssessmentWinardoNo ratings yet
- Powerpro ManualDocument24 pagesPowerpro ManualLuis Alberto Castillo MaurtuaNo ratings yet
- ASE Chap3Document56 pagesASE Chap3Thiện LêNo ratings yet
- 09 12 PROT409 GenAbnormalOp-Part4-BreakerFailure 20230703Document69 pages09 12 PROT409 GenAbnormalOp-Part4-BreakerFailure 20230703Álex NágutNo ratings yet
- Fault Dectection Max HohenbergerDocument27 pagesFault Dectection Max HohenbergeryassinebouazziNo ratings yet
- SIL PresentationDocument28 pagesSIL Presentationpradeep1987coolNo ratings yet
- LOPADocument125 pagesLOPABaba Johneh100% (5)
- Energy Efficient Security Techniques For Resource Constrained Wireless DevicesDocument20 pagesEnergy Efficient Security Techniques For Resource Constrained Wireless DevicesSaad MustafaNo ratings yet
- The Bulk Power Supply 2. Reliability Criteria: Disturbance-Performance Table How Are They Used Security StatesDocument28 pagesThe Bulk Power Supply 2. Reliability Criteria: Disturbance-Performance Table How Are They Used Security StatesErgin ÖzdikicioğluNo ratings yet
- Chafai 2013Document6 pagesChafai 2013Mohamed Daw HamoudaNo ratings yet
- Safe Operation of Machines For Metalworking Sector - JLDocument51 pagesSafe Operation of Machines For Metalworking Sector - JLbalamurugan sNo ratings yet
- Introduction To Layers of Protection Analysis (LOPA)Document53 pagesIntroduction To Layers of Protection Analysis (LOPA)Sidi Arief Hidayat HusniNo ratings yet
- Testing Methods Required To Maintain Electrical-Equipment PDFDocument104 pagesTesting Methods Required To Maintain Electrical-Equipment PDFIrfan AshrafNo ratings yet
- Nellcor PM10N Home Use GuideDocument50 pagesNellcor PM10N Home Use GuidetakaminekimoNo ratings yet
- SIL Determination and High Demand Mode: Table 1 IEC 61508 Ed 2 - Modes of OperationDocument8 pagesSIL Determination and High Demand Mode: Table 1 IEC 61508 Ed 2 - Modes of OperationDio NaufalNo ratings yet
- Lecture Material Template - FDocument3 pagesLecture Material Template - FNANDHAKUMAR ANo ratings yet
- Final - Version - Buscano, Jon Hermie A.Document34 pagesFinal - Version - Buscano, Jon Hermie A.api-20012905No ratings yet
- Power System Protection and Switchgear: Fundamentals of Protective Relaying IiDocument25 pagesPower System Protection and Switchgear: Fundamentals of Protective Relaying IiSampath AnbuNo ratings yet
- Power Scada ScheiderDocument313 pagesPower Scada ScheiderMAT SANI NASIRNo ratings yet
- Machine Safety StandardsDocument27 pagesMachine Safety StandardsTanNo ratings yet
- 02 Safety - MT2200 - enDocument28 pages02 Safety - MT2200 - enjackNo ratings yet
- DAY - 2 L10 Risk and Opportunity RevPVDocument39 pagesDAY - 2 L10 Risk and Opportunity RevPVMuthu Ganesh VeerabakuNo ratings yet
- DA-2101 PSDI Using Light Curtains Revision 1.4 25SE06Document22 pagesDA-2101 PSDI Using Light Curtains Revision 1.4 25SE06Manuel ParejaNo ratings yet
- Machine Safety Risk Assessment SafetyIIDocument67 pagesMachine Safety Risk Assessment SafetyIIMarian Ion100% (3)
- Lecture 4 Power System ProtectionDocument23 pagesLecture 4 Power System ProtectionMichael Parohinog GregasNo ratings yet
- SWE 205 - Introduction To Software Engineering: - Critical System Specifications (Chapter 9)Document22 pagesSWE 205 - Introduction To Software Engineering: - Critical System Specifications (Chapter 9)s.b.v.seshagiri1407No ratings yet
- Relays CompressDocument30 pagesRelays CompressjoNo ratings yet
- Power System Protection1Document7 pagesPower System Protection1Mrrajesh RajeshNo ratings yet
- 20 Critical SystemsDocument58 pages20 Critical SystemsSai Santhosh ManepallyNo ratings yet
- Reliability Analysis in An Electrical Drive System 104355-241916-2-PBDocument4 pagesReliability Analysis in An Electrical Drive System 104355-241916-2-PBNoname_user989No ratings yet
- 3 StandardsDocument22 pages3 Standardschris panjaitanNo ratings yet
- Medical Equipment Quality Assurance: Compression UnitsDocument11 pagesMedical Equipment Quality Assurance: Compression UnitsJayson JasminNo ratings yet
- PANDA P3 User ManualDocument50 pagesPANDA P3 User ManualLuis Antonio Olguin VivarNo ratings yet
- 2 Fall22-Lecture2QualityMetricsDocument68 pages2 Fall22-Lecture2QualityMetricsTarikul IslamNo ratings yet
- SafeguardingDocument57 pagesSafeguardingDayglis CostaNo ratings yet
- CHAI OpenqPCR Manual 原廠使用手冊Document59 pagesCHAI OpenqPCR Manual 原廠使用手冊William ManrokiNo ratings yet
- Ch9 - Crtical Systems SpecificationDocument50 pagesCh9 - Crtical Systems SpecificationYemen BrokerNo ratings yet
- S280-70-3 Above SN 10000 or CP570000000Document48 pagesS280-70-3 Above SN 10000 or CP570000000Josué Miranda da SilvaNo ratings yet
- Sentry Original Instructions (EN) Revc 2TLC010002M0201 PDFDocument65 pagesSentry Original Instructions (EN) Revc 2TLC010002M0201 PDFGilnei LoschNo ratings yet
- RelaysDocument30 pagesRelaysujjwalNo ratings yet
- Manual Smart AlarmDocument27 pagesManual Smart AlarmJoaquim FernandesNo ratings yet
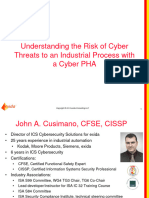
- Wednesday Cusimano 140207220932 Phpapp02Document27 pagesWednesday Cusimano 140207220932 Phpapp02Gli OxalNo ratings yet
- Read Chapter 1!: The 2 Components Security Assessment From Operators View NercDocument43 pagesRead Chapter 1!: The 2 Components Security Assessment From Operators View NercilluminityNo ratings yet
- IEC 61508 & Functional Safety-2022Document24 pagesIEC 61508 & Functional Safety-2022viswanathan.thiruvayyarNo ratings yet
- Dependability and Security SpecificationsDocument42 pagesDependability and Security SpecificationsYrreg GerryNo ratings yet
- 80DA0AAAd01 PDFDocument19 pages80DA0AAAd01 PDFdelviyolandaNo ratings yet
- Problems Booklet SolutionDocument109 pagesProblems Booklet Solutionridha Ben AliNo ratings yet
- 545M - Parr - 6775 6775A Digital Thermometer InstDocument12 pages545M - Parr - 6775 6775A Digital Thermometer InstNguyen Minh NhutNo ratings yet
- Haffa NshsDocument18 pagesHaffa NshsAbel TasfirNo ratings yet
- Manual Book F6Document44 pagesManual Book F6Adib Darul QuthniNo ratings yet
- Reliability Best Practices: Review TheseDocument18 pagesReliability Best Practices: Review TheseSV SANKARAMOORTHYNo ratings yet
- Ch12 Safety EngineeringDocument70 pagesCh12 Safety EngineeringGraceNo ratings yet
- HiKam - A7 - en US New V1.3Document2 pagesHiKam - A7 - en US New V1.3klopNo ratings yet
- Concept of Customer Hierarchy in SAP SD PDFDocument9 pagesConcept of Customer Hierarchy in SAP SD PDFمحمد شعيبNo ratings yet
- Bash Tips & Tricks: CTRL + Y To Paste It (As in Delete and Copy) All Text in Front of The CursorDocument4 pagesBash Tips & Tricks: CTRL + Y To Paste It (As in Delete and Copy) All Text in Front of The CursorLaxman RathodNo ratings yet
- No, Satoshi Nakamoto Didn't Just Move His Bitcoin - DecryptDocument5 pagesNo, Satoshi Nakamoto Didn't Just Move His Bitcoin - DecryptHidayat PurnamaNo ratings yet
- Motor Control With Basic PLC Programming: Presented By: JS MorenoDocument33 pagesMotor Control With Basic PLC Programming: Presented By: JS MorenoNiño John Jayme100% (1)
- Cortex XDRDocument6 pagesCortex XDRStacy Marie100% (1)
- Dokumen - Tips - Installation Runbook For Mirantis Runbook For Palo Alto Networks Virtual FirewallDocument55 pagesDokumen - Tips - Installation Runbook For Mirantis Runbook For Palo Alto Networks Virtual Firewalltoe koNo ratings yet
- Sicam A8000 Series Rtus Toolbox II Devicemanager Admin Security EngDocument192 pagesSicam A8000 Series Rtus Toolbox II Devicemanager Admin Security EngpedrovvfNo ratings yet
- Alarm Viewer On U2000Document15 pagesAlarm Viewer On U2000Huynh DaveNo ratings yet
- ClearVue 650 OB-GYN BrochureDocument8 pagesClearVue 650 OB-GYN BrochureAmani ArafatNo ratings yet
- BSD BS 5400Document51 pagesBSD BS 5400Fredrik AndresenNo ratings yet
- Web Tech Cat CodesDocument46 pagesWeb Tech Cat Codesdasari yashwanthNo ratings yet
- Cpe201 - Object Oriented Programming (Advanced Prog.) Spring 2021 Assignment 2: FunctionsDocument3 pagesCpe201 - Object Oriented Programming (Advanced Prog.) Spring 2021 Assignment 2: FunctionsHazem AlmasryNo ratings yet
- SAP BW4HANA TasklistDocument3 pagesSAP BW4HANA TasklistTejashree NNo ratings yet
- Ijgi 09 00257Document16 pagesIjgi 09 00257Nur RahmaNo ratings yet
- Mass Repeat Print Sales OrderDocument2 pagesMass Repeat Print Sales OrderChaitanya M100% (1)
- Computer Security Fundamentals 5Th Edition William Chuck Easttom Full ChapterDocument51 pagesComputer Security Fundamentals 5Th Edition William Chuck Easttom Full Chapterjose.ferguson966100% (18)
- Lab ManualDocument14 pagesLab Manualhak creationNo ratings yet
- Sketching User Experiences Getting The Design Right and The Right Design Interactive Technologies - 1-235Document235 pagesSketching User Experiences Getting The Design Right and The Right Design Interactive Technologies - 1-235Monica Gisselle Auler SimonisNo ratings yet
- Atrex ManualDocument455 pagesAtrex Manualblufoot36100% (1)
- The Little Black Book Of: Native AdvertisingDocument18 pagesThe Little Black Book Of: Native AdvertisingVishakhaNo ratings yet
- Apache Cassandra: by Chethan GowdaDocument12 pagesApache Cassandra: by Chethan GowdaChaithu GowdruNo ratings yet
- Timing Closure Exploration Tools With Smartxplorer and Planahead ToolsDocument7 pagesTiming Closure Exploration Tools With Smartxplorer and Planahead ToolsSovi SoviNo ratings yet
- System Parameters For Drawings: Parameter NameDocument5 pagesSystem Parameters For Drawings: Parameter NameStanley kNo ratings yet
- HDL Project Report On Automatic WashingDocument17 pagesHDL Project Report On Automatic WashingMuyeez AktharNo ratings yet
- UGRD-MIS6211 Computer Fundamentals Prelim ExamDocument15 pagesUGRD-MIS6211 Computer Fundamentals Prelim ExamNathan CalmsNo ratings yet
- GPA Calculator Using VisualDocument4 pagesGPA Calculator Using VisualOmotara AkinsowonNo ratings yet
- Dx200 Setup Procedure ManualDocument44 pagesDx200 Setup Procedure ManualSergayNo ratings yet
- SC-300 StudyGuide ENU v220 FY23Q1.1Document7 pagesSC-300 StudyGuide ENU v220 FY23Q1.1Bisi TeruNo ratings yet
12security and Dependability Specifications
12security and Dependability Specifications
Uploaded by
Anil LamaOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
12security and Dependability Specifications
12security and Dependability Specifications
Uploaded by
Anil LamaCopyright:
Available Formats
Chapter 12 – Dependability
and Security Specification
1
Chapter 12 Dependability and Security Specification 1
12.1 Risk-driven specification
• Critical systems specification should be risk-driven.
• Widely used in safety and security-critical systems.
• EXAMPLES?
• Goals
• Understand risks
• Define requirements to address risks
Chapter 12 Dependability and Security Specification 2
Chapter 12 Dependability and Security Specification 3
Stages of risk-based analysis
• Risk identification
• Train doesn’t stop, goes over speed, runs on wrong track
• Risk analysis and classification
• Life threatening, dangerous to property / probable, highly unlikely
• Risk decomposition – root causes
• Incorrect sensor reading, incorrect computation,.
• Risk reduction assessment – how to mitigate
• Self test of sensors, secondary sensors, ...
Chapter 12 Dependability and Security Specification 4
12.2 Safety specification
• Phases
• Identification
• Assessment
• Analysis
• Specification
Chapter 12 Dependability and Security Specification 5
Hazard identification
• Types of hazard:
• Physical hazards
• Electrical hazards
• Biological hazards
• Service failure hazards
• Etc.
Chapter 12 Dependability and Security Specification 6
Insulin pump risks
• Insulin overdose (service failure).
• Insulin underdose (service failure).
• Power failure due to exhausted battery (electrical).
• Electrical interference with other medical equipment
(electrical).
• Poor sensor and actuator contact (physical).
• Parts of machine break off in body (physical).
• Infection caused by introduction of machine (biological).
• Allergic reaction to materials or insulin (biological).
Chapter 12 Dependability and Security Specification 7
Hazard assessment
• Identifying
• likelihood that a risk will arise
• potential consequences
• Risks may be categorised as:
• Intolerable. Must never arise or result in an accident
• As low as reasonably practical (ALARP). Must minimise the possibility
of risk given cost and schedule constraints
• Acceptable. The consequences of the risk are acceptable and no extra
costs should be incurred to reduce hazard probability
Chapter 12 Dependability and Security Specification 8
Social acceptability of risk
• The acceptability of a risk is determined by human, social
and political considerations.
• boundaries between the regions are pushed upwards with
time
• i.e. society is less willing to accept risk
• (Seldom do people conclude that something intolerable in the past is
OK now)
• Risk assessment is subjective
• Risks are identified as probable, unlikely, etc. This depends on who is
making the assessment.
Chapter 12 Dependability and Security Specification 9
Risk classification for the insulin pump
Identified hazard Hazard probability Accident severity Estimated risk Acceptability
1.Insulin overdose Medium High High Intolerable
computation
2. Insulin underdose Medium Low Low Acceptable
computation
3. Failure of Medium Medium Low ALARP
hardware monitoring
system
4. Power failure High Low Low Acceptable
5. Machine High High High Intolerable
incorrectly fitted
6. Machine breaks in Low High Medium ALARP
patient
7. Machine causes Medium Medium Medium ALARP
infection
8. Electrical Low High Medium ALARP
interference
9. Allergic reaction Low Low Low Acceptable
Chapter 12 Dependability and Security Specification 10
Risk Reduction Strategies
• Risk reduction strategies
• Risk avoidance (never set train speed above a given level)
• Risk detection and removal (detect over speed and reduce speed)
• Damage limitation.
Chapter 12 Dependability and Security Specification 11
Strategy combination
• Normally, in critical systems, a mix of risk reduction strategies are
used.
• Train control system
• Set train speed
• Monitor speed from separate sensor
• Estimate speeds given train time and locations.
Chapter 12 Dependability and Security Specification 12
Examples of safety requirements
SR1: The system shall not deliver a single dose of insulin that is greater than a
specified maximum dose for a system user.
SR2: The system shall not deliver a daily cumulative dose of insulin that is greater
than a specified maximum daily dose for a system user.
SR3: The system shall include a hardware diagnostic facility that shall be
executed at least four times per hour.
SR4: The system shall include an exception handler for all of the exceptions that
are identified in Table 3.
SR5: The audible alarm shall be sounded when any hardware or software
anomaly is discovered and a diagnostic message, as defined in Table 4, shall be
displayed.
SR6: In the event of an alarm, insulin delivery shall be suspended until the user
has reset the system and cleared the alarm.
Chapter 12 Dependability and Security Specification 13
12.3 Reliability
Chapter 12 Dependability and Security Specification 14
• Reliability requirements are of two kinds:
• 1. Non-functional requirements, which define the number of failures
that are acceptable during normal use of the system, or the time in
which the system is unavailable for use. These are quantitative
reliability requirements.
• 2. Functional requirements, which define system and software
functions that avoid, detect, or tolerate faults in the software and so
ensure that these faults do not lead to system failure.
Chapter 12 Dependability and Security Specification 15
Probability of failure on demand (POFOD)
• Probability that the system will fail when a service request is
made.
• Expressed as probability
• .001 means that there will probably be one failure in every 1000 requests
• Appropriate for protection systems where
• services are demanded occasionally
• there are serious consequence if the service is not delivered.
Chapter 12 Dependability and Security Specification 16
POFD Examples
• Software Installation should not require reboot
• Fingerprint identification should not block a valid user
• Fingerprint identification should not allow an invalid user
• Conversion of street data to occur
Chapter 12 Dependability and Security Specification 17
Rate of Fault Occurrence (ROCOF)
• Reflects the rate of occurrence of failure in the system in a
time period.
• 0.002 means 2 failures are likely in each 1000 operational
time units (say hours)
• Relevant where
• system has to process a large number of similar requests in a short time
• Example: Credit card processing system, airline booking system.
• Reciprocal of ROCOF is Mean time to Failure (MTTF)
Chapter 12 Dependability and Security Specification 18
Availability
• fraction of the time that the system is available for use.
• Takes repair and restart time into account
• 0.998 means software is available for 998 out of 1000 time units.
• Relevant for non-stop, continuously running systems
• telephone switching systems, railway signalling systems.
Chapter 12 Dependability and Security Specification 19
Thinking Another Way
Availability Explanation
0.9 The system is available for 90% of the time. This means that, in
a 24-hour period (1,440 minutes), the system will be
unavailable for 144 minutes.
0.99 In a 24-hour period, the system is unavailable for 14.4 minutes.
0.999 The system is unavailable for 84 seconds in a 24-hour period.
0.9999 The system is unavailable for 8.4 seconds in a 24-hour period.
Roughly, one minute per week.
Chapter 12 Dependability and Security Specification 20
Quantitative Methods
• have been used much more for safety
• not so much for business
• testing for .0001 POFOD or ROCOF could be very difficult
• Continuous monitoring and measuring useful
Chapter 12 Dependability and Security Specification 21
Over-specification of reliability
• high-level of reliability is specified
• but it is not cost-effective to achieve this.
• May be cheaper to accept and deal with failures rather than avoid
them occurring.
Chapter 12 Dependability and Security Specification 22
Examples of Functional Reliability
Requirements for MHC-PMS
RR1: A pre-defined range for all operator inputs shall be defined and the
system shall check that all operator inputs fall within this pre-defined range.
(Checking)
RR2:Copies of the patient database shall be maintained on two separate servers
that are not housed in the same building. (Recovery, redundancy)
RR3:N-version programming shall be used to implement the braking control
system. (Redundancy)
RR4:The system must be implemented in a safe subset of Ada and checked using
static analysis. (Process)
Chapter 12 Dependability and Security Specification 23
Security Specification
• Different than Safety
• Accidental vs Intentional
• Discovery of root cause – in an attack, this may be concealed.
• Security challenges increase over time. An attacker can probe defenses over
time to discover weaknesses.
Chapter 12 Dependability and Security Specification 24
Types of security requirement
• Identification requirements.
• Authentication requirements.
• Authorization requirements.
• Intrusion detection requirements.
• Non-repudiation requirements.
• Privacy requirements.
• Security auditing requirements.
• System maintenance security requirements.
Chapter 12 Dependability and Security Specification 25
Security risk assessment
• Asset identification
• Identify the key system assets (or services) that have to be protected.
• Asset value assessment
• Estimate the value of the identified assets.
• Exposure assessment
• Assess the potential losses associated with each asset.
• Threat identification
• Identify the most probable threats to the system assets
Chapter 12 Dependability and Security Specification 26
Security risk assessment
• Attack assessment
• Decompose threats into possible attacks on the system and the ways that
these may occur.
• Control identification
• Propose the controls that may be put in place to protect an asset.
• Feasibility assessment
• Assess the technical feasibility and cost of the controls.
• Security requirements definition
• Define system security requirements. These can be infrastructure or
application system requirements.
Chapter 12 Dependability and Security Specification 27
Asset analysis in a preliminary risk
assessment report for the MHC-PMS
Asset Value Exposure
The information system High. Required to support all High. Financial loss as clinics
clinical consultations. Potentially may have to be canceled. Costs
safety-critical. of restoring system. Possible
patient harm if treatment cannot
be prescribed.
The patient database High. Required to support all High. Financial loss as clinics
clinical consultations. Potentially may have to be canceled. Costs
safety-critical. of restoring system. Possible
patient harm if treatment cannot
be prescribed.
An individual patient record Normally low although may be Low direct losses but possible
high for specific high-profile loss of reputation.
patients.
Chapter 12 Dependability and Security Specification 28
Threat and control analysis in a preliminary
risk assessment report
Threat Probability Control Feasibility
Unauthorized user Low Only allow system Low cost of implementation but
gains access as management from care must be taken with key
system manager and specific locations that are distribution and to ensure that
makes system physically secure. keys are available in the event
unavailable of an emergency.
Unauthorized user High Require all users to Technically feasible but high-
gains access as authenticate themselves cost solution. Possible user
system user and using a biometric resistance.
accesses confidential mechanism.
information Simple and transparent to
Log all changes to implement and also supports
patient information to recovery.
track system usage.
Chapter 12 Dependability and Security Specification 29
Security policy
• Defined by organization
• Identifies
• Who can access systems, data
• When can they access systems, data
• Overall policy to drive needs.
Chapter 12 Dependability and Security Specification 30
Security requirements for the MHC-PMS
• Patient information shall be downloaded at the start of a clinic
session to a secure area on the system client that is used by clinical
staff.
• All patient information on the system client shall be encrypted.
• Patient information shall be uploaded to the database after a clinic
session has finished and deleted from the client computer.
• A log on a separate computer from the database server must be
maintained of all changes made to the system database.
Chapter 12 Dependability and Security Specification 31
Formal methods and critical systems
• Formal specification is part of a more general collection of
techniques that are known as ‘formal methods’.
• These are all based on mathematical representation and analysis of
software.
• Formal methods include
– Formal specification;
– Specification analysis and proof;
– Transformational development;
– Program verification.
Chapter 12 Dependability and Security Specification 32
Use of formal methods
• The principal benefits of formal methods are in reducing the number
of faults in systems.
• Consequently, their main area of applicability is in critical systems
engineering. There have been several successful projects where formal
methods have been used in this area.
• In this area, the use of formal methods is most likely to be cost
effective because high system failure costs must be avoided.
Chapter 12 Dependability and Security Specification 33
Specification in the software proces
• Specification and design are inextricably intermingled.
• Architectural design is essential to structure a specification and the
specification process.
• Formal specifications are expressed in a mathematical notation with
precisely defined vocabulary, syntax and semantics.
Chapter 12 Dependability and Security Specification 34
Formal specification in a plan-based software
process
Chapter 12 Dependability and Security Specification 35
Benefits of formal specification
• Developing a formal specification requires the system requirements
to be analyzed in detail. This helps to detect problems,
inconsistencies and incompleteness in the requirements.
• As the specification is expressed in a formal language, it can be
automatically analyzed to discover inconsistencies and
incompleteness.
• If you use a formal method such as the B method, you can transform
the formal specification into a ‘correct’ program.
• Program testing costs may be reduced if the program is formally
verified against its specification.
Chapter 12 Dependability and Security Specification 36
You might also like
- LOPADocument125 pagesLOPAOlvis Guillen100% (1)
- Element IC5: Work Equipment (General) : Unit IC: Suggested Answers To Revision Questions, IC1-IC5Document4 pagesElement IC5: Work Equipment (General) : Unit IC: Suggested Answers To Revision Questions, IC1-IC5memolidarnahNo ratings yet
- Volume 1 - 2 Day Architect Training Adobe Experience Manager v.6.xDocument102 pagesVolume 1 - 2 Day Architect Training Adobe Experience Manager v.6.xKiril DelovskiNo ratings yet
- 1 Chapter 12 Dependability and Security SpecificationDocument55 pages1 Chapter 12 Dependability and Security Specificationkayosh dhungelNo ratings yet
- 1 Chapter 12 Dependability and Security SpecificationDocument55 pages1 Chapter 12 Dependability and Security SpecificationEr Ravi GuptaNo ratings yet
- Why SIL3? Josse Brys TUV EngineerDocument38 pagesWhy SIL3? Josse Brys TUV Engineersina20795No ratings yet
- Critical Systems Specification: ©ian Sommerville 2004Document50 pagesCritical Systems Specification: ©ian Sommerville 2004jnax101No ratings yet
- Welding Robots Technology System Issues and Applications - J Norberto PiresDocument76 pagesWelding Robots Technology System Issues and Applications - J Norberto PireshetpinNo ratings yet
- Health Care Risk AssessmentDocument81 pagesHealth Care Risk AssessmentWinardoNo ratings yet
- Powerpro ManualDocument24 pagesPowerpro ManualLuis Alberto Castillo MaurtuaNo ratings yet
- ASE Chap3Document56 pagesASE Chap3Thiện LêNo ratings yet
- 09 12 PROT409 GenAbnormalOp-Part4-BreakerFailure 20230703Document69 pages09 12 PROT409 GenAbnormalOp-Part4-BreakerFailure 20230703Álex NágutNo ratings yet
- Fault Dectection Max HohenbergerDocument27 pagesFault Dectection Max HohenbergeryassinebouazziNo ratings yet
- SIL PresentationDocument28 pagesSIL Presentationpradeep1987coolNo ratings yet
- LOPADocument125 pagesLOPABaba Johneh100% (5)
- Energy Efficient Security Techniques For Resource Constrained Wireless DevicesDocument20 pagesEnergy Efficient Security Techniques For Resource Constrained Wireless DevicesSaad MustafaNo ratings yet
- The Bulk Power Supply 2. Reliability Criteria: Disturbance-Performance Table How Are They Used Security StatesDocument28 pagesThe Bulk Power Supply 2. Reliability Criteria: Disturbance-Performance Table How Are They Used Security StatesErgin ÖzdikicioğluNo ratings yet
- Chafai 2013Document6 pagesChafai 2013Mohamed Daw HamoudaNo ratings yet
- Safe Operation of Machines For Metalworking Sector - JLDocument51 pagesSafe Operation of Machines For Metalworking Sector - JLbalamurugan sNo ratings yet
- Introduction To Layers of Protection Analysis (LOPA)Document53 pagesIntroduction To Layers of Protection Analysis (LOPA)Sidi Arief Hidayat HusniNo ratings yet
- Testing Methods Required To Maintain Electrical-Equipment PDFDocument104 pagesTesting Methods Required To Maintain Electrical-Equipment PDFIrfan AshrafNo ratings yet
- Nellcor PM10N Home Use GuideDocument50 pagesNellcor PM10N Home Use GuidetakaminekimoNo ratings yet
- SIL Determination and High Demand Mode: Table 1 IEC 61508 Ed 2 - Modes of OperationDocument8 pagesSIL Determination and High Demand Mode: Table 1 IEC 61508 Ed 2 - Modes of OperationDio NaufalNo ratings yet
- Lecture Material Template - FDocument3 pagesLecture Material Template - FNANDHAKUMAR ANo ratings yet
- Final - Version - Buscano, Jon Hermie A.Document34 pagesFinal - Version - Buscano, Jon Hermie A.api-20012905No ratings yet
- Power System Protection and Switchgear: Fundamentals of Protective Relaying IiDocument25 pagesPower System Protection and Switchgear: Fundamentals of Protective Relaying IiSampath AnbuNo ratings yet
- Power Scada ScheiderDocument313 pagesPower Scada ScheiderMAT SANI NASIRNo ratings yet
- Machine Safety StandardsDocument27 pagesMachine Safety StandardsTanNo ratings yet
- 02 Safety - MT2200 - enDocument28 pages02 Safety - MT2200 - enjackNo ratings yet
- DAY - 2 L10 Risk and Opportunity RevPVDocument39 pagesDAY - 2 L10 Risk and Opportunity RevPVMuthu Ganesh VeerabakuNo ratings yet
- DA-2101 PSDI Using Light Curtains Revision 1.4 25SE06Document22 pagesDA-2101 PSDI Using Light Curtains Revision 1.4 25SE06Manuel ParejaNo ratings yet
- Machine Safety Risk Assessment SafetyIIDocument67 pagesMachine Safety Risk Assessment SafetyIIMarian Ion100% (3)
- Lecture 4 Power System ProtectionDocument23 pagesLecture 4 Power System ProtectionMichael Parohinog GregasNo ratings yet
- SWE 205 - Introduction To Software Engineering: - Critical System Specifications (Chapter 9)Document22 pagesSWE 205 - Introduction To Software Engineering: - Critical System Specifications (Chapter 9)s.b.v.seshagiri1407No ratings yet
- Relays CompressDocument30 pagesRelays CompressjoNo ratings yet
- Power System Protection1Document7 pagesPower System Protection1Mrrajesh RajeshNo ratings yet
- 20 Critical SystemsDocument58 pages20 Critical SystemsSai Santhosh ManepallyNo ratings yet
- Reliability Analysis in An Electrical Drive System 104355-241916-2-PBDocument4 pagesReliability Analysis in An Electrical Drive System 104355-241916-2-PBNoname_user989No ratings yet
- 3 StandardsDocument22 pages3 Standardschris panjaitanNo ratings yet
- Medical Equipment Quality Assurance: Compression UnitsDocument11 pagesMedical Equipment Quality Assurance: Compression UnitsJayson JasminNo ratings yet
- PANDA P3 User ManualDocument50 pagesPANDA P3 User ManualLuis Antonio Olguin VivarNo ratings yet
- 2 Fall22-Lecture2QualityMetricsDocument68 pages2 Fall22-Lecture2QualityMetricsTarikul IslamNo ratings yet
- SafeguardingDocument57 pagesSafeguardingDayglis CostaNo ratings yet
- CHAI OpenqPCR Manual 原廠使用手冊Document59 pagesCHAI OpenqPCR Manual 原廠使用手冊William ManrokiNo ratings yet
- Ch9 - Crtical Systems SpecificationDocument50 pagesCh9 - Crtical Systems SpecificationYemen BrokerNo ratings yet
- S280-70-3 Above SN 10000 or CP570000000Document48 pagesS280-70-3 Above SN 10000 or CP570000000Josué Miranda da SilvaNo ratings yet
- Sentry Original Instructions (EN) Revc 2TLC010002M0201 PDFDocument65 pagesSentry Original Instructions (EN) Revc 2TLC010002M0201 PDFGilnei LoschNo ratings yet
- RelaysDocument30 pagesRelaysujjwalNo ratings yet
- Manual Smart AlarmDocument27 pagesManual Smart AlarmJoaquim FernandesNo ratings yet
- Wednesday Cusimano 140207220932 Phpapp02Document27 pagesWednesday Cusimano 140207220932 Phpapp02Gli OxalNo ratings yet
- Read Chapter 1!: The 2 Components Security Assessment From Operators View NercDocument43 pagesRead Chapter 1!: The 2 Components Security Assessment From Operators View NercilluminityNo ratings yet
- IEC 61508 & Functional Safety-2022Document24 pagesIEC 61508 & Functional Safety-2022viswanathan.thiruvayyarNo ratings yet
- Dependability and Security SpecificationsDocument42 pagesDependability and Security SpecificationsYrreg GerryNo ratings yet
- 80DA0AAAd01 PDFDocument19 pages80DA0AAAd01 PDFdelviyolandaNo ratings yet
- Problems Booklet SolutionDocument109 pagesProblems Booklet Solutionridha Ben AliNo ratings yet
- 545M - Parr - 6775 6775A Digital Thermometer InstDocument12 pages545M - Parr - 6775 6775A Digital Thermometer InstNguyen Minh NhutNo ratings yet
- Haffa NshsDocument18 pagesHaffa NshsAbel TasfirNo ratings yet
- Manual Book F6Document44 pagesManual Book F6Adib Darul QuthniNo ratings yet
- Reliability Best Practices: Review TheseDocument18 pagesReliability Best Practices: Review TheseSV SANKARAMOORTHYNo ratings yet
- Ch12 Safety EngineeringDocument70 pagesCh12 Safety EngineeringGraceNo ratings yet
- HiKam - A7 - en US New V1.3Document2 pagesHiKam - A7 - en US New V1.3klopNo ratings yet
- Concept of Customer Hierarchy in SAP SD PDFDocument9 pagesConcept of Customer Hierarchy in SAP SD PDFمحمد شعيبNo ratings yet
- Bash Tips & Tricks: CTRL + Y To Paste It (As in Delete and Copy) All Text in Front of The CursorDocument4 pagesBash Tips & Tricks: CTRL + Y To Paste It (As in Delete and Copy) All Text in Front of The CursorLaxman RathodNo ratings yet
- No, Satoshi Nakamoto Didn't Just Move His Bitcoin - DecryptDocument5 pagesNo, Satoshi Nakamoto Didn't Just Move His Bitcoin - DecryptHidayat PurnamaNo ratings yet
- Motor Control With Basic PLC Programming: Presented By: JS MorenoDocument33 pagesMotor Control With Basic PLC Programming: Presented By: JS MorenoNiño John Jayme100% (1)
- Cortex XDRDocument6 pagesCortex XDRStacy Marie100% (1)
- Dokumen - Tips - Installation Runbook For Mirantis Runbook For Palo Alto Networks Virtual FirewallDocument55 pagesDokumen - Tips - Installation Runbook For Mirantis Runbook For Palo Alto Networks Virtual Firewalltoe koNo ratings yet
- Sicam A8000 Series Rtus Toolbox II Devicemanager Admin Security EngDocument192 pagesSicam A8000 Series Rtus Toolbox II Devicemanager Admin Security EngpedrovvfNo ratings yet
- Alarm Viewer On U2000Document15 pagesAlarm Viewer On U2000Huynh DaveNo ratings yet
- ClearVue 650 OB-GYN BrochureDocument8 pagesClearVue 650 OB-GYN BrochureAmani ArafatNo ratings yet
- BSD BS 5400Document51 pagesBSD BS 5400Fredrik AndresenNo ratings yet
- Web Tech Cat CodesDocument46 pagesWeb Tech Cat Codesdasari yashwanthNo ratings yet
- Cpe201 - Object Oriented Programming (Advanced Prog.) Spring 2021 Assignment 2: FunctionsDocument3 pagesCpe201 - Object Oriented Programming (Advanced Prog.) Spring 2021 Assignment 2: FunctionsHazem AlmasryNo ratings yet
- SAP BW4HANA TasklistDocument3 pagesSAP BW4HANA TasklistTejashree NNo ratings yet
- Ijgi 09 00257Document16 pagesIjgi 09 00257Nur RahmaNo ratings yet
- Mass Repeat Print Sales OrderDocument2 pagesMass Repeat Print Sales OrderChaitanya M100% (1)
- Computer Security Fundamentals 5Th Edition William Chuck Easttom Full ChapterDocument51 pagesComputer Security Fundamentals 5Th Edition William Chuck Easttom Full Chapterjose.ferguson966100% (18)
- Lab ManualDocument14 pagesLab Manualhak creationNo ratings yet
- Sketching User Experiences Getting The Design Right and The Right Design Interactive Technologies - 1-235Document235 pagesSketching User Experiences Getting The Design Right and The Right Design Interactive Technologies - 1-235Monica Gisselle Auler SimonisNo ratings yet
- Atrex ManualDocument455 pagesAtrex Manualblufoot36100% (1)
- The Little Black Book Of: Native AdvertisingDocument18 pagesThe Little Black Book Of: Native AdvertisingVishakhaNo ratings yet
- Apache Cassandra: by Chethan GowdaDocument12 pagesApache Cassandra: by Chethan GowdaChaithu GowdruNo ratings yet
- Timing Closure Exploration Tools With Smartxplorer and Planahead ToolsDocument7 pagesTiming Closure Exploration Tools With Smartxplorer and Planahead ToolsSovi SoviNo ratings yet
- System Parameters For Drawings: Parameter NameDocument5 pagesSystem Parameters For Drawings: Parameter NameStanley kNo ratings yet
- HDL Project Report On Automatic WashingDocument17 pagesHDL Project Report On Automatic WashingMuyeez AktharNo ratings yet
- UGRD-MIS6211 Computer Fundamentals Prelim ExamDocument15 pagesUGRD-MIS6211 Computer Fundamentals Prelim ExamNathan CalmsNo ratings yet
- GPA Calculator Using VisualDocument4 pagesGPA Calculator Using VisualOmotara AkinsowonNo ratings yet
- Dx200 Setup Procedure ManualDocument44 pagesDx200 Setup Procedure ManualSergayNo ratings yet
- SC-300 StudyGuide ENU v220 FY23Q1.1Document7 pagesSC-300 StudyGuide ENU v220 FY23Q1.1Bisi TeruNo ratings yet