Professional Documents
Culture Documents
Zero Trust Mind Map v1
Zero Trust Mind Map v1
Uploaded by
fakhritCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Zero Trust Mind Map v1
Zero Trust Mind Map v1
Uploaded by
fakhritCopyright:
Available Formats
Microsoft 365 Zero Trust Mind Map Microsoft Authenticator app
Windows Hello for Business
jads.blog
Multi-Factor Authentication FIDO2 security key
SMS
Voice call
OATH software or hardware tokens
Application Protection Policies
Mobile Device Management Policy
Device health and compliance (Intune Integration)
Secure adaptive access
Sensitive info types Session Policies
Azure AD Conditional Access Policies Session management (Defender for Cloud Apps Integration)
Trainable classifiers Know your data Location/Device States/Application based policies
User Risk
Data Classfication
Risk based policies (Integration with AAD Identity Protection)
Sign In Risk
Integration with Log Analytics (Microsoft Sentinel)
Reports and monitoring Azure AD Workbooks
Conditional Access Insights &Reporting
Identity Secure Score
MIP Unified Labeling Scanner
Automatic Labeling
MIP Unified labeling client
SSO using OpenID Connect
Manual Labeling Sensitivity labels
SSO using SAML
Double Key Encryption (DKE) Protect your data Single Sign on
SSO to on-premises apps (Azure AD Application Proxy)
Office 365 Message Encryption (OME)
Secure your Identities
Microsoft Defender for Cloud Apps
Protect your Sensitive Data Seamless user experience Passwordless Authentication
Windows Hello for Business
File policies
Microsoft Authenticator app
Autolabeling policies
FIDO2 security keys
Microsoft Purview Data Map
MyApps
Self Service portals
MyAccount
Sensitive info types as condition MyAccess (Integration with Azure AD Access Packages)
Sensitivity labels as condition My Signins
Policy templates Microsoft Purview Data Loss Prevention
External Identities
Endpoint DLP
Prevent Data Loss Azure AD B2B Cross tenant Settings
Integration with Defender for Endpoint
Microsoft 365 Zero Trust External Identities
Azure AD B2C
Pass the Hash Synchronisation (PHS)
Pass Through Authenication (PTA)
Unified identity management Hybrid Identity Azure AD Connect
Data Loss Prevention on-premises scanner Federation (ADFS)
DLP for Teams Chat and channel messages Group based licensing
User & Group Management Dynamic groups
Application assignments
Retention policies Managed Identities
Retention Labels Data Retention & Deletion
Cloud Only Accounts
Mailbox archiving
Govern your Data
Records Management Azure AD Access Packages
Sensitive info types Lifecycle management Azure AD Access Reviews
Automated Policies
Auto apply labels
Specific keywords Simplified identity governance HCM driven Provisioning
Hybrind provisioning using Azure AD Connect
Trainablle Classifier
eDiscovery
Content search Azure AD PIM for Azure AD Roles (Just in time access)
Core eDiscovery Azure AD PIM for Azure Resources (JIT access)
Priviliged Identity Management Priviliged role monitoring and auditing
Advanced eDiscovery
Manage permissions and access (Azure, AWS, GCP)
Cross cloud visibility
Entra Permissions Management
Monitoring & least privilege enforcement
Detect and respond to on-premises Identity attacks
Assess the security posture of your hybrid environments
Defender for Identity
Isolate and remediate compromised accounts
Identities Azure AD Identity Protection
Discover vulnerabilities and misconfigurations
Detect and block sophisticated threats and malware
Defender for Endpoint
Microsoft 365 Defender (XDR) Detect and respond to advanced attacks with deep threat monitoring and analysis
Endpoints Simplify endpoint security management
Secure and protect your cloud assets Discover and control the use of shadow IT
Perimeter Control
VPN Gateway Protect your sensitive information anywhere in the cloud (File policies and Threat protection policies)
Azure DDoS Protection Real-time control an (Session policies, Integration with Conditional Access) Native Integration with Microsoft Sentinel using connectors
Applications Defender for Cloud Apps
Azure Front Door Cloud Security Posture
Azure Firewall
Network Security Groups/ASGs Protect your Cloud Workloads Detect and Respond to Threats Protection against advanced attacks (phishing, malware, spam, etc.)
Emails and documents Defender for Office 365
Protection beyond email (Microsoft Teams, SharePoint, OneDrive, and Office apps)
UDRs
Subnets Virtual Networks Internal email protection
Inboud/Outbound Control
IoT Devices Defender for IoT Asset discovery and context
Risk-based vulnerability management
Threat detection with IoT and OT behavioral analytics
Managed Identities
Double Key Encryption Key & Secrets Management
Hold your Own Key Microsoft Native connectors
Integration with Azure Key Vault Data Connectors
Application passwords Third party connectors
Data Collection
Bring your Own Key
Syslog
Key auto-rotation
Microsoft Sentinel Data Collector API
Custom Log format (Log Analytics Agent)
Azure Functions and the REST API
Common Event Format (CEF) over Syslog
Fusion (Advanced Multi stage attacks)
Microsoft Sentinel Detection
Build in detection rules
Machine Learning behavioral analytics
Microsoft Defender for IoT IoT Workloads
Anomaly rule templates
Scheduled rules
Microsoft Defender for Azure Cosmos DB Cosmos Environments
Near Real time rules
Detect Threats
Microsoft Defender for DNS DNS
Microsoft Defender for Servers Servers
Kusto Query Language (KQL)
Custom rules
Microsoft Defender for Storage Azure Storage Query Scheduling/Thresholds
Microsoft Defender for SQL SQL Servers
Incident breakdown
Microsoft Defender for Containers Containers
Investigation
Notebooks
App services User and Entity Behavior Analytics (UEBA)
Microsoft Defender for App Service
Workbooks
Microsoft Defender for Key Vault Key Vault
Hunting Queries
Entity Pages
Microsoft Defender for Resource Manager Resource deployment
Triggers
Automation Rules Conditions
Threat Detection alerts
Actions
Security Orchestration, Automation, and Response (SOAR)
Advanced protection & remediation
Insights and visibility Workload protections dashboard
Connectors (Managed or Custom)
Playbooks (Integration with Azure Logic Apps) Triggers
Playbooks (Integration with Logic Apps)
Actions
Integration with Microsoft Sentinel (connectors) Investigate and respond
Alerts and Incidents
Workbooks
Azure Databricks/Apache Spark
Bring your own Machine Learning (ML)
Azure Monitor logs and metrics Jupyter Notebooks
Telemetry logs
Logs & Traces
Diagnosis
Audit
Security policies Enforce
Security Initiaties (created in Azure Policy)
Azure Security Benchmark (default)
Cloud Security Posture Management (CSPM) Requirements & Regulations
Third party regulations (CIS, NIST, etc.)
Custom Initiaties
Policy enforcement
Security Recommendations
Remedation steps
Microsoft Defender for Cloud
Azure
Security Posture
Google Cloud Platform (GCP)
Amazon Web Services (AWS)
Security Alerts & Incidents
Cloud Workload Protection
Behavioral Analytics
Threat Intelligence
Anomaly detection
Integration with SIEM/SOAR
You might also like
- Locksmith Training Course (NEW)Document134 pagesLocksmith Training Course (NEW)andrew100% (3)
- Using BPM For Agility in A Globalized WorldDocument6 pagesUsing BPM For Agility in A Globalized WorldWonderware Skelta BPM100% (1)
- Beckhoff Main Catalog 2016 PDFDocument1,009 pagesBeckhoff Main Catalog 2016 PDFChi Lac PhungNo ratings yet
- 12 Multiple Choice QuestionsDocument2 pages12 Multiple Choice QuestionsChax Cruise0% (1)
- Microsoft 365 Zero Trust Mind MapDocument1 pageMicrosoft 365 Zero Trust Mind MapBarkaoui brahimNo ratings yet
- Armatura One 5 Fold Brochure 10mar2023Document2 pagesArmatura One 5 Fold Brochure 10mar2023Refaat BenbayaNo ratings yet
- TCI Reference Architecture v1.1Document1 pageTCI Reference Architecture v1.1Archil GogorishviliNo ratings yet
- EBI DiagramaDocument1 pageEBI DiagramaJULIAN MENESESNo ratings yet
- Microsoft Modern Work Plan Comparison Education 11 2021Document7 pagesMicrosoft Modern Work Plan Comparison Education 11 2021Nana Kwame Agyire-TetteyNo ratings yet
- Uni-Ds6: User ManualDocument24 pagesUni-Ds6: User ManualErgin ÖzdikicioğluNo ratings yet
- Unids6 Manual v100Document24 pagesUnids6 Manual v100oya27910No ratings yet
- Data 11052022Document1 pageData 11052022aljarrahcs2431No ratings yet
- Accops HS5020 DatasheetDocument6 pagesAccops HS5020 DatasheetAjit Pratap KundanNo ratings yet
- Mikroboard For Arm 64-Pin: User ManualDocument20 pagesMikroboard For Arm 64-Pin: User ManualDaniel GalarzaNo ratings yet
- AWS Periodic TableDocument1 pageAWS Periodic Tabledouglas.dvferreiraNo ratings yet
- Software Engineering Final Exam Chapter QuestionsDocument2 pagesSoftware Engineering Final Exam Chapter QuestionsMelike KeçelioğluNo ratings yet
- 016 SkillFront ISO IEC 27001 Information SecurityDocument63 pages016 SkillFront ISO IEC 27001 Information SecurityAbNo ratings yet
- 016 SkillFront ISO IEC 27001 Information SecurityDocument63 pages016 SkillFront ISO IEC 27001 Information Securitythiyaga1988No ratings yet
- Kloudynet - Microsoft Modern XDRSOC Offering 2022Document1 pageKloudynet - Microsoft Modern XDRSOC Offering 2022Rohit SinghNo ratings yet
- Poster PA 2015 en A1Document1 pagePoster PA 2015 en A1Dalat TigonNo ratings yet
- The Search EcosystemDocument1 pageThe Search EcosystemOmar CorralNo ratings yet
- Huawei Technology Campus Network Solution BrochureDocument16 pagesHuawei Technology Campus Network Solution BrochureHailay WeldegebrielNo ratings yet
- Poster Ys80634 Ai-Assistred Attendence IdDocument1 pagePoster Ys80634 Ai-Assistred Attendence IdvxlrNo ratings yet
- Mikroboard For Arm 144-Pin: User ManualDocument20 pagesMikroboard For Arm 144-Pin: User ManualSlobodan ŠošićNo ratings yet
- Projmatic Case StudyDocument1 pageProjmatic Case Studyk4gs62x9vdNo ratings yet
- PSOP 6 Traceability MatrixDocument1 pagePSOP 6 Traceability MatrixLapid BakeshopNo ratings yet
- ECommerce Basics 1667870298Document1 pageECommerce Basics 1667870298Thanh UzumakiNo ratings yet
- Autos PoolDocument8 pagesAutos PoolPARASCADD Private LimitedNo ratings yet
- Samsung Door Lock ManualDocument2 pagesSamsung Door Lock ManualBudi BudiNo ratings yet
- GVM ST300R User ManualDocument1 pageGVM ST300R User ManualPaco Jiménez BarbaNo ratings yet
- Add Sector: ANTOML/MI/ME/MUDocument129 pagesAdd Sector: ANTOML/MI/ME/MUshashank.prajapati9389No ratings yet
- SP35 Plus Card Printer: Quick Install GuideDocument4 pagesSP35 Plus Card Printer: Quick Install GuideDiego CamposNo ratings yet
- SCHNEIDER DIA5ED1161001EN - v7.0Document20 pagesSCHNEIDER DIA5ED1161001EN - v7.0flaviosistemasNo ratings yet
- Encryption Mechanism Software Requirement Specifications Changed To Dokumentation Version 1.3.0Document13 pagesEncryption Mechanism Software Requirement Specifications Changed To Dokumentation Version 1.3.0Akshat JainNo ratings yet
- CarDocument25 pagesCardownload181No ratings yet
- SAS Banking - Basel II SolutionsDocument12 pagesSAS Banking - Basel II Solutionsashfaqultanim007No ratings yet
- CashlessConsumer - UPI Applist, Issuer PSP List, VPAs, StatsDocument25 pagesCashlessConsumer - UPI Applist, Issuer PSP List, VPAs, Statsphone2hireNo ratings yet
- Products at A Glance: Management Tools Port Extenders Extreme Innovation ExtensibilityDocument8 pagesProducts at A Glance: Management Tools Port Extenders Extreme Innovation ExtensibilityMoe El-ChafeiNo ratings yet
- Alex Murray: Embedded Software Engineer InternDocument1 pageAlex Murray: Embedded Software Engineer Internapi-569631990No ratings yet
- Sejal Divekar Resume1Document2 pagesSejal Divekar Resume1Jason StanleyNo ratings yet
- Apple's CSAM Detection MechanismDocument12 pagesApple's CSAM Detection MechanismMike WuertheleNo ratings yet
- Az 900Document1 pageAz 900olivier larocheNo ratings yet
- Sigma Coating SDocument1,106 pagesSigma Coating SCamilo VillaNo ratings yet
- Vishnu Dutt PMDocument2 pagesVishnu Dutt PMvishnu choudharyNo ratings yet
- With Intel Xeon Processors: Cisco Unif Ied Computing SystemDocument2 pagesWith Intel Xeon Processors: Cisco Unif Ied Computing SystemPavan NavNo ratings yet
- D9T Electrical SystemDocument4 pagesD9T Electrical SystemPablo PorrasNo ratings yet
- Smart Lock p100 ManualDocument1 pageSmart Lock p100 ManualZulrock KlateNo ratings yet
- 040 SkillFront ISO IEC 20000 IT Service Management SystemsDocument80 pages040 SkillFront ISO IEC 20000 IT Service Management SystemsAriel TatumNo ratings yet
- HASP LM GuideDocument38 pagesHASP LM GuideRiki AsmadiNo ratings yet
- Deep Learning-Based Semantic Segmentation in Autonomous DrivingDocument7 pagesDeep Learning-Based Semantic Segmentation in Autonomous Drivingprajna acharyaNo ratings yet
- Attachment 1Document10 pagesAttachment 1GeorginaNo ratings yet
- Voice Control Third-Party Hardware Partners: Complete Smart Home SolutionsDocument2 pagesVoice Control Third-Party Hardware Partners: Complete Smart Home SolutionsNicolas J Silberay PerezNo ratings yet
- Caio - Ferraz Da Cunha - CV E PDFDocument2 pagesCaio - Ferraz Da Cunha - CV E PDFCaio FerrazNo ratings yet
- Delloite Operator Value MapDocument1 pageDelloite Operator Value MapDiogo Pimenta Barreiros0% (1)
- Trend Micro Solution Poster PDFDocument1 pageTrend Micro Solution Poster PDFVăn HảiNo ratings yet
- Order Cash 1Document14 pagesOrder Cash 1Alecia ChenNo ratings yet
- (PREVIEW - ONLY) SH SCCCI Flyer - 20160815 - 4Document2 pages(PREVIEW - ONLY) SH SCCCI Flyer - 20160815 - 4me2 monkNo ratings yet
- Poster Incose Is 2016 1Document1 pagePoster Incose Is 2016 1bobblejotNo ratings yet
- Key-Aggregate Cryptosystem For Scalable Data Sharing in Cloud Storage-A ReviewDocument5 pagesKey-Aggregate Cryptosystem For Scalable Data Sharing in Cloud Storage-A ReviewSiddhartha BashettyNo ratings yet
- An Enhanced Anonymity Control Scheme Based On Quantum Cryptography in Cloud EnvironmentDocument6 pagesAn Enhanced Anonymity Control Scheme Based On Quantum Cryptography in Cloud EnvironmentsujeethNo ratings yet
- 5000 Fresh Hits AccountDocument1,362 pages5000 Fresh Hits AccountreezereturnsNo ratings yet
- How To Solve ORA-28001 - The Password Has Expired - Hectorino's BlogDocument3 pagesHow To Solve ORA-28001 - The Password Has Expired - Hectorino's BlogManohar ReddyNo ratings yet
- Iptv Smarters by Kimo 2024Document4 pagesIptv Smarters by Kimo 2024yahya cleverNo ratings yet
- DNS Security: A.Lioy, F.Maino, M. Marian, D.MazzocchiDocument14 pagesDNS Security: A.Lioy, F.Maino, M. Marian, D.MazzocchiFundeanu RobertNo ratings yet
- Hakin9: An Interview With Dr. Gary McGrawDocument3 pagesHakin9: An Interview With Dr. Gary McGrawdasxaxNo ratings yet
- Humans-The Weakest Link-Group 4Document33 pagesHumans-The Weakest Link-Group 4MadMagga0% (1)
- About The PresentationsDocument54 pagesAbout The PresentationsAnish SharmaNo ratings yet
- Securing A Java EE 7 ApplicationDocument15 pagesSecuring A Java EE 7 ApplicationLuís MeloNo ratings yet
- ISO 27001 2013 Appendix ADocument12 pagesISO 27001 2013 Appendix AssglcnNo ratings yet
- First TC Programs Latest Update1Document3 pagesFirst TC Programs Latest Update1rizahilmiNo ratings yet
- Bin HarmoniDocument137 pagesBin HarmonijokoNo ratings yet
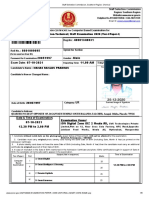
- Staff Selection Commission, Southern Region, Chennai ADMIT CARDDocument6 pagesStaff Selection Commission, Southern Region, Chennai ADMIT CARDManas RanjanNo ratings yet
- CSCL 1 MarksDocument4 pagesCSCL 1 MarksSurendra DawadiNo ratings yet
- CEH BroucherDocument2 pagesCEH BroucherManal SaeedNo ratings yet
- 7safe Prospectus Jan 2017Document19 pages7safe Prospectus Jan 2017MikeNo ratings yet
- DFD DiagramDocument2 pagesDFD DiagramAlishbah AhmedNo ratings yet
- Logrhythm and Forescout Counteract™: Integrated Enterprise SecurityDocument2 pagesLogrhythm and Forescout Counteract™: Integrated Enterprise SecurityPablo ReyesNo ratings yet
- Authentication: Apcosoft Infoway COES Ver1.2 Function Test CaseDocument1 pageAuthentication: Apcosoft Infoway COES Ver1.2 Function Test CaseVISHAL MESHRAMNo ratings yet
- Harshit AadharDocument1 pageHarshit Aadhardadpitt023No ratings yet
- Digital Forensics PDFDocument116 pagesDigital Forensics PDFPrateek NagpalNo ratings yet
- DashboardDocument1 pageDashboardshreeshNo ratings yet
- Ib 848 849 Wss OutboundDocument6 pagesIb 848 849 Wss OutboundMadhu MandavaNo ratings yet
- Block Chain: WEEK:1: PerspectiveDocument7 pagesBlock Chain: WEEK:1: PerspectiveSNIGDHA BHAT U 1940157No ratings yet
- Ethical Hacking: Presented By: Sadia Siddique ID: 2023032048Document18 pagesEthical Hacking: Presented By: Sadia Siddique ID: 2023032048Fardin Sabahat KhanNo ratings yet
- Syllabus VPNDocument8 pagesSyllabus VPNLaasyaSweetNo ratings yet
- Lahore College For Women University: Department of Computer ScienceDocument2 pagesLahore College For Women University: Department of Computer SciencesabaNo ratings yet