Professional Documents
Culture Documents
Muddywise Ygffffff
Muddywise Ygffffff
Uploaded by
seddmshakOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Muddywise Ygffffff
Muddywise Ygffffff
Uploaded by
seddmshakCopyright:
Available Formats
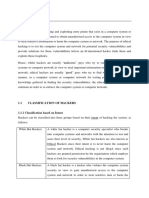
Trespass refers to unauthorized access to a computer system, network, or data.
It involves bypassing
security measures to gain entry into restricted areas, often with malicious intent. Trespass can take
various forms, including hacking into a system, exploiting vulnerabilities, or using social engineering
tactics to trick users into revealing sensitive information.
1. Unauthorized Access: Someone sneaks into a company's network by exploiting weak spots like
passwords or outdated software, to steal data or cause chaos.
2. Phishing Attacks: Scammers send fake emails, pretending to be from trusted sources, to trick people
into giving away passwords or downloading harmful files.
3. SQL Injection: Hackers inject nasty code into website forms to sneak into databases and steal sensitive
info or mess with the site's content.
4. Insider Threats: Trusted insiders misuse their access to the system for personal gain or to harm the
company, like stealing secrets or breaking things.
5. Remote Code Execution: Bad actors find holes in software to run their own code on distant systems,
gaining control for data theft or system hijacking.
6. DDoS Attacks: Attackers flood a system with so much fake traffic that it crashes, making it
unreachable for legitimate users.
You might also like
- Computer Fraud and Abuse TechniquesDocument41 pagesComputer Fraud and Abuse TechniquesAaron DinNo ratings yet
- Hacking : The Ultimate Comprehensive Step-By-Step Guide to the Basics of Ethical HackingFrom EverandHacking : The Ultimate Comprehensive Step-By-Step Guide to the Basics of Ethical HackingRating: 5 out of 5 stars5/5 (3)
- TrespassDocument5 pagesTrespassseddmshakNo ratings yet
- Cyber Attacks On Operating Systems Can Take Various Form1Document3 pagesCyber Attacks On Operating Systems Can Take Various Form1Idrissa SalehNo ratings yet
- What Is Cyber Attacks and Its TypesDocument2 pagesWhat Is Cyber Attacks and Its TypesShubham DNo ratings yet
- Top 50 Attack 1702614908Document4 pagesTop 50 Attack 1702614908rotaractorsuhasNo ratings yet
- BSOTM Unit 4Document12 pagesBSOTM Unit 4Aditi SharmaNo ratings yet
- Cyber Security Notes Unit 2Document6 pagesCyber Security Notes Unit 2Reshma BasuNo ratings yet
- Lec 4 - Threats and AttacksDocument51 pagesLec 4 - Threats and AttacksgNo ratings yet
- User Awareness ControlDocument2 pagesUser Awareness ControlMuhammad MurtazaNo ratings yet
- Q1 Common Types of Cybersecurity Attacks: 1. MalwareDocument32 pagesQ1 Common Types of Cybersecurity Attacks: 1. MalwareKhateeb AhmadNo ratings yet
- Cyber SecurityDocument61 pagesCyber SecurityTech ProffesorNo ratings yet
- CYBERSECURITYDocument41 pagesCYBERSECURITYDominique EijansantosNo ratings yet
- Unit 1a Awareness of Cyber Crimes and SecurityDocument32 pagesUnit 1a Awareness of Cyber Crimes and SecurityBarsaNo ratings yet
- CH 2 CsDocument16 pagesCH 2 CsDeeksha GuptaNo ratings yet
- Security 3Document2 pagesSecurity 3Ayoub ZahRaouiNo ratings yet
- Unit 1 Cyber AttacksDocument5 pagesUnit 1 Cyber AttacksVikas KumarNo ratings yet
- Ethical Hacking ScriptDocument3 pagesEthical Hacking Scriptuhafduhkjhas100% (1)
- SummaryDocument44 pagesSummaryDominique Eijansantos100% (1)
- Presentation 1Document5 pagesPresentation 1darshan1988No ratings yet
- 01 - Introduction To Ethical HackingDocument26 pages01 - Introduction To Ethical HackingHACKER HACKERNo ratings yet
- Topic 2 Ethics, Fraud and Internal Control in AIS A182-AdditionalDocument29 pagesTopic 2 Ethics, Fraud and Internal Control in AIS A182-AdditionalHema DarshiniNo ratings yet
- Eth CHP2Document9 pagesEth CHP2Liladhar VanjoleNo ratings yet
- InternetDocument16 pagesInternetkamal jyotiNo ratings yet
- Cyber Security and Ethical HackingDocument58 pagesCyber Security and Ethical HackingAkashNo ratings yet
- Introduction To HackingDocument7 pagesIntroduction To Hackingbhagwatgayal10No ratings yet
- Ethical Hacking NotesDocument25 pagesEthical Hacking NotesMayank AgarwalNo ratings yet
- Assignment 5 - Grazelyn RabeDocument3 pagesAssignment 5 - Grazelyn RabeGrazelyn RabeNo ratings yet
- Hacking IpcDocument9 pagesHacking IpcArun Sundar KanjirapuzhaNo ratings yet
- Cristo Rey Reforsado - Assignment 5Document3 pagesCristo Rey Reforsado - Assignment 5Grazelyn RabeNo ratings yet
- Unit 3 CybercrimeqandansDocument18 pagesUnit 3 Cybercrimeqandansrohankumar5471No ratings yet
- EhDocument7 pagesEhifgabhayNo ratings yet
- Cyber Security ThreatsDocument5 pagesCyber Security Threatsronin150101No ratings yet
- Assignment 1Document4 pagesAssignment 12027 Tasfia IsratNo ratings yet
- CSS4-Q1 Module 2Document10 pagesCSS4-Q1 Module 2Lielanie NavarroNo ratings yet
- Computer FraudDocument32 pagesComputer FraudnaufalarifNo ratings yet
- Cyber Security Presentation2Document25 pagesCyber Security Presentation2lenovo AccountNo ratings yet
- Unit 5Document26 pagesUnit 5davidowuna5No ratings yet
- 1.0 Threats, Attacks and VulnerabilitiesDocument11 pages1.0 Threats, Attacks and Vulnerabilitiesjerryagbenyo7No ratings yet
- 1.intro To Ethical HackingDocument67 pages1.intro To Ethical Hackingmadhu reddy100% (1)
- Ethical Hacking NotesDocument11 pagesEthical Hacking NotesB Rohit RajNo ratings yet
- .trashed-1701350038-CYBER SECURITY INTERNALDocument3 pages.trashed-1701350038-CYBER SECURITY INTERNALcreativegamerz00No ratings yet
- Introduction To Cyber Security & Ethical HackingDocument30 pagesIntroduction To Cyber Security & Ethical Hacking000kabboNo ratings yet
- Lec 02Document26 pagesLec 02Misbah IrumNo ratings yet
- THREATSDocument10 pagesTHREATSF19BA110Mehrose FatimaNo ratings yet
- Cyber Security Notes Unit 3Document8 pagesCyber Security Notes Unit 3Reshma BasuNo ratings yet
- Network & Information Security TrainingDocument58 pagesNetwork & Information Security TrainingUmarfarooque Mursal100% (1)
- How To HackDocument2 pagesHow To Hackbronbyhater69No ratings yet
- 21GECDAU-Ethical Hacking Dr.V.UsharaniDocument27 pages21GECDAU-Ethical Hacking Dr.V.UsharaniA19BCM059Vijaya raghavan.BNo ratings yet
- Hacking and Data TheftDocument5 pagesHacking and Data TheftAhmed AdelNo ratings yet
- 3 PPT - CopyDocument26 pages3 PPT - CopyDurga Prasad SmartNo ratings yet
- IntroductionDocument11 pagesIntroductionManushi KhatriNo ratings yet
- Activity On Chapter 3Document4 pagesActivity On Chapter 3Aiyue MadiusNo ratings yet
- 3-UNITDocument14 pages3-UNITdhruvdixit8141No ratings yet
- Types of Cyber Attack or ThreatsDocument5 pagesTypes of Cyber Attack or ThreatsJean Yves AmbroiseNo ratings yet
- SS SemDocument42 pagesSS Semnachiketn101No ratings yet
- ETHICAL HACKING GUIDE-Part 1: Comprehensive Guide to Ethical Hacking worldFrom EverandETHICAL HACKING GUIDE-Part 1: Comprehensive Guide to Ethical Hacking worldNo ratings yet
- Your System's Sweetspots: CEO's Advice on Basic Cyber Security: CEO's Advice on Computer ScienceFrom EverandYour System's Sweetspots: CEO's Advice on Basic Cyber Security: CEO's Advice on Computer ScienceNo ratings yet
- HACKING: Unveiling the Secrets of Cybersecurity and Ethical Hacking (2024 Guide for Beginners)From EverandHACKING: Unveiling the Secrets of Cybersecurity and Ethical Hacking (2024 Guide for Beginners)No ratings yet
- Cybersecurity and Ethical Hacking: Exploring the Dark Art of Ethical Hacking and Penetration TestingFrom EverandCybersecurity and Ethical Hacking: Exploring the Dark Art of Ethical Hacking and Penetration TestingNo ratings yet