Professional Documents
Culture Documents
Master's Degree in Digital Forensics: Lponte@mail - Ucf.edu Whicomb@mail - Ucf.edu
Master's Degree in Digital Forensics: Lponte@mail - Ucf.edu Whicomb@mail - Ucf.edu
Uploaded by
Cory HuberCopyright:
Available Formats
You might also like
- The Truth About Gang Stalking: Community Policing and Usage of TechnologiesDocument77 pagesThe Truth About Gang Stalking: Community Policing and Usage of TechnologiesChris Lissa Myers83% (6)
- Individual Membership-EIZ Application Form-10Document4 pagesIndividual Membership-EIZ Application Form-10Timothy KapungweNo ratings yet
- Sample of Short PHD ProposalDocument8 pagesSample of Short PHD Proposalscholarsassist100% (4)
- CDR EA Outcome Letter SampleDocument1 pageCDR EA Outcome Letter Samplesdivya02No ratings yet
- Ssca130212-4.1.7 Bengtech New Program StreamsDocument23 pagesSsca130212-4.1.7 Bengtech New Program StreamsA SNo ratings yet
- Digital Forensics Education in PakistanDocument3 pagesDigital Forensics Education in Pakistanmehmilhabib9No ratings yet
- C&DF CurriculumDocument10 pagesC&DF Curriculumtech2click100% (1)
- Literature Review Computer ForensicsDocument7 pagesLiterature Review Computer Forensicsc5r0qjcf100% (1)
- CBS GradDipCombineDocument2 pagesCBS GradDipCombinegallianomcflyNo ratings yet
- National Law Institute University, Bhopal: Information Brochure 2018-19 Master of Cyber Law and Information SecurityDocument16 pagesNational Law Institute University, Bhopal: Information Brochure 2018-19 Master of Cyber Law and Information SecurityWajid AliNo ratings yet
- Research Paper Topics For Computer ForensicsDocument7 pagesResearch Paper Topics For Computer Forensicsefdwvgt4100% (1)
- 2012 - MoLekol - An Enhanced Learning Support System For Class-Based ScenariosDocument8 pages2012 - MoLekol - An Enhanced Learning Support System For Class-Based ScenariosSameerchand PudaruthNo ratings yet
- Another Brick in The Wall An Exploratory Analysis of Digital Forensics Programs in The United StatesDocument8 pagesAnother Brick in The Wall An Exploratory Analysis of Digital Forensics Programs in The United Stateshenu wigastaNo ratings yet
- ACPO Manager GuideDocument117 pagesACPO Manager Guidemsaamir115851No ratings yet
- Digital Forensics Sample Case Study ReportDocument19 pagesDigital Forensics Sample Case Study Reportdpkvk98157No ratings yet
- Cybersecurity Program For Philippine Higher Education InstitutionsDocument6 pagesCybersecurity Program For Philippine Higher Education InstitutionsCarl Vince BautistaNo ratings yet
- Dissertation Computer ForensicsDocument4 pagesDissertation Computer ForensicsWriteMyCustomPaperCanada100% (1)
- Forensic Evidence in The Digital AgeDocument82 pagesForensic Evidence in The Digital AgeSunny ProjectNo ratings yet
- Computer Forensics Research Paper IdeasDocument6 pagesComputer Forensics Research Paper Ideasmoykicvnd100% (1)
- Forensic ScienceDocument12 pagesForensic Sciencesomya jainNo ratings yet
- Live Time Forensics Brochuredraftv6LRDocument40 pagesLive Time Forensics Brochuredraftv6LRCandy ChungNo ratings yet
- Dissertation Topics in Computer ForensicsDocument4 pagesDissertation Topics in Computer ForensicsAcademicPaperWritersUK100% (1)
- Digital ForensicsDocument15 pagesDigital ForensicsCo VidNo ratings yet
- Course Details - Technology Law and PolicyDocument6 pagesCourse Details - Technology Law and PolicyShivaniNo ratings yet
- Graduate ProgramsDocument8 pagesGraduate Programsapi-316879421No ratings yet
- Dissertation Topics For Digital ForensicsDocument7 pagesDissertation Topics For Digital ForensicsBuyCollegePapersProvo100% (1)
- Jurnal Forensic Digital Analysis2Document39 pagesJurnal Forensic Digital Analysis2nanaNo ratings yet
- Forensic Computing Dissertation IdeasDocument5 pagesForensic Computing Dissertation IdeasHowToWriteMyPaperLittleRock100% (1)
- Digital ForensicsDocument15 pagesDigital ForensicsSIDDHARTHANo ratings yet
- Advanced Certification ProgrammesDocument9 pagesAdvanced Certification ProgrammesಕೇधाR ಗೋDaसेNo ratings yet
- Computer Forensic Dissertation IdeasDocument8 pagesComputer Forensic Dissertation IdeasBestCustomPapersSingapore100% (1)
- HNU Annual Crime and Fire Safety RPT 2012Document59 pagesHNU Annual Crime and Fire Safety RPT 2012Holy Names University100% (1)
- Computer Forensics Dissertation IdeasDocument6 pagesComputer Forensics Dissertation IdeasCustomHandwritingPaperManchester100% (1)
- Final EportDocument20 pagesFinal EportIngrid BayiyanaNo ratings yet
- Computer Forensics Research Paper TopicsDocument7 pagesComputer Forensics Research Paper Topicsaflbtcxfc100% (1)
- Capstone ProjectDocument15 pagesCapstone Projectpandasinghk2001No ratings yet
- Study On Computer Evidence Forensics ZHU ZhenfangDocument3 pagesStudy On Computer Evidence Forensics ZHU ZhenfangInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Dissertation On Cybercrime in IndiaDocument6 pagesDissertation On Cybercrime in IndiaCustomWrittenPaperSingapore100% (1)
- PHD Research Project Proposal: TitleDocument5 pagesPHD Research Project Proposal: Titlethanhtuan.to1993No ratings yet
- Paise Fakoo Tamsa DekhoDocument14 pagesPaise Fakoo Tamsa DekhoveerNo ratings yet
- 18LLB077 Forensic LawDocument16 pages18LLB077 Forensic LawSAI DEEP GADANo ratings yet
- Digital Forensic in The FutureDocument18 pagesDigital Forensic in The FutureHayes JohnNo ratings yet
- Benefits of Participation RFCLDocument3 pagesBenefits of Participation RFCLsilly_rabbitzNo ratings yet
- Law Enforcement Challenges in Digital ForensicsDocument44 pagesLaw Enforcement Challenges in Digital Forensicsblkjack2u100% (1)
- IJDCFFinal 6Document1 pageIJDCFFinal 6IshanNo ratings yet
- A Model For Digital Evidence Admissibility AssessmentDocument17 pagesA Model For Digital Evidence Admissibility AssessmentKikidoo IdNo ratings yet
- Building FBI Computer Forensics Capacity One Lab at A Time 2004 Digital InvestigationDocument6 pagesBuilding FBI Computer Forensics Capacity One Lab at A Time 2004 Digital InvestigationglennallynNo ratings yet
- MCLIS Brochure 2023 24Document27 pagesMCLIS Brochure 2023 24sharadNo ratings yet
- Digital ForensicsDocument4 pagesDigital ForensicsAnand KhotNo ratings yet
- "Managing Cyber Crimes in India - Issues and Challenges": Mrs - Vineetha.P.K Principal, Sarada Vilas Law College, MysoreDocument12 pages"Managing Cyber Crimes in India - Issues and Challenges": Mrs - Vineetha.P.K Principal, Sarada Vilas Law College, MysoreAkash GuptaNo ratings yet
- Practical Digital Forensics - Sample ChapterDocument31 pagesPractical Digital Forensics - Sample ChapterPackt Publishing100% (2)
- Memorandum Issuance From CICC (Request For Info)Document5 pagesMemorandum Issuance From CICC (Request For Info)Bert CruzNo ratings yet
- Research Paper Computer CrimeDocument8 pagesResearch Paper Computer Crimev0j0bysyt1m3100% (1)
- A Review On Digital Forensic Investigation Frameworks and Real World Cyber Crime CasesDocument7 pagesA Review On Digital Forensic Investigation Frameworks and Real World Cyber Crime CasesEditor IJRITCCNo ratings yet
- Oa 82Document11 pagesOa 82jariya.attNo ratings yet
- Review of Related Literature and Studies: Tulip St. Area C Camarin, Caloocan City Bachelor of Science in Computer ScienceDocument9 pagesReview of Related Literature and Studies: Tulip St. Area C Camarin, Caloocan City Bachelor of Science in Computer ScienceJohn EricNo ratings yet
- Cybersecurity Program For Philippine Higher Education InstitutionsDocument13 pagesCybersecurity Program For Philippine Higher Education InstitutionsMark FloresNo ratings yet
- EITS Status and Activity Report For April 2015Document4 pagesEITS Status and Activity Report For April 2015accidentalcioNo ratings yet
- Cyber Crimes and Technical Issues Under The Jordanian Information System Crimes LawDocument14 pagesCyber Crimes and Technical Issues Under The Jordanian Information System Crimes LawMagadaNo ratings yet
- Using OSS For Forensic PurposesDocument7 pagesUsing OSS For Forensic PurposesManuel DelgadoNo ratings yet
- Term Paper About Cybercrime LawDocument8 pagesTerm Paper About Cybercrime Lawaflsiosbe100% (1)
- Cyber Crime Research Paper OutlineDocument6 pagesCyber Crime Research Paper Outlineefjddr4z100% (1)
- What Is GeophysicsDocument26 pagesWhat Is Geophysics1234abcdNo ratings yet
- Engineering Council of South Africa: Background: The ECSA Education System DocumentsDocument14 pagesEngineering Council of South Africa: Background: The ECSA Education System Documentsprisca ncuncuNo ratings yet
- Member Assessment GuidanceDocument17 pagesMember Assessment GuidanceAbhishek ShatagopachariNo ratings yet
- CHED Sample OBE Syllabus AT 2 AUTO MECHANICALDocument7 pagesCHED Sample OBE Syllabus AT 2 AUTO MECHANICALMarvin Sarmiento TalimonganNo ratings yet
- Universiti Kuala Lumpur Malaysia France Institute (Unikl Mfi)Document6 pagesUniversiti Kuala Lumpur Malaysia France Institute (Unikl Mfi)cypanNo ratings yet
- 2021 - Advert - Network Planning and Network MaintenanceDocument6 pages2021 - Advert - Network Planning and Network MaintenancecharltonNo ratings yet
- 1293X Master Electrician Exam Information Package 2012Document12 pages1293X Master Electrician Exam Information Package 2012noneco100% (1)
- IAB 252r2 14 SV00 Guideline For Personnel With Qualification For Welding Coordination SVDocument27 pagesIAB 252r2 14 SV00 Guideline For Personnel With Qualification For Welding Coordination SVjimingeorge100% (1)
- Merged Voter Register 2021 June 24Document602 pagesMerged Voter Register 2021 June 24jckapindaNo ratings yet
- EWF QualificationDocument42 pagesEWF Qualificationromanosky11No ratings yet
- Bem Code of Ethics - 2016Document12 pagesBem Code of Ethics - 2016Dan CNo ratings yet
- Application Guidance For Fellow (FCIBSE)Document17 pagesApplication Guidance For Fellow (FCIBSE)ManNo ratings yet
- Schedule of Licensure Examinations For Year 2009 Professional Regulation Commission PRC Manila City Resolution No. 2008 - Series of 2008 Republic of The PhilippinesDocument5 pagesSchedule of Licensure Examinations For Year 2009 Professional Regulation Commission PRC Manila City Resolution No. 2008 - Series of 2008 Republic of The PhilippinesJulio Iñigo López100% (23)
- Admission BS Fall 21Document1 pageAdmission BS Fall 21Abdul Naveed SialNo ratings yet
- The Institute of Mechanical Engineers (Imeche) : 6 CHAPTER 1 Engineers and Designers-Career Paths-InstitutesDocument1 pageThe Institute of Mechanical Engineers (Imeche) : 6 CHAPTER 1 Engineers and Designers-Career Paths-Institutesmasoud132No ratings yet
- Re - Admin Case For Dishonesty - Falsification - Katly (A.m. No. 2003-9-SC, March 25, 2004)Document7 pagesRe - Admin Case For Dishonesty - Falsification - Katly (A.m. No. 2003-9-SC, March 25, 2004)Fatzie MendozaNo ratings yet
- IAB 252r8-07Document24 pagesIAB 252r8-07Jayanta82No ratings yet
- ST LUKES v. NLRCDocument2 pagesST LUKES v. NLRCDanyNo ratings yet
- Chapter 2 MEC600Document50 pagesChapter 2 MEC600Aziful AiemanNo ratings yet
- Engineers (Registration, Etc.) ACT: Main MenuDocument32 pagesEngineers (Registration, Etc.) ACT: Main MenuAdeniji OlusegunNo ratings yet
- LANDAS - LISING - PILAPIL - STEP 1 RechckingDocument66 pagesLANDAS - LISING - PILAPIL - STEP 1 RechckingjeremiahNo ratings yet
- 1E ECSA Candidate AppformDocument9 pages1E ECSA Candidate AppformSilas MangwendeNo ratings yet
- Engineering in SocietyDocument7 pagesEngineering in Societyjahremade jahremadeNo ratings yet
- Tup Taguig - Program OfferingsDocument6 pagesTup Taguig - Program OfferingsRafhael MangalaoNo ratings yet
- Bulletin of Vacant Positions April 1-30, 2015Document89 pagesBulletin of Vacant Positions April 1-30, 2015CscfoAgusanDelNorteNo ratings yet
- IEA Graduate Attributes and Professional Competencies 2021.1 Sept 2021Document23 pagesIEA Graduate Attributes and Professional Competencies 2021.1 Sept 2021ageldresmNo ratings yet
- Guide To Professional Registration With The Engineering CouncilDocument8 pagesGuide To Professional Registration With The Engineering CouncilbassamNo ratings yet
Master's Degree in Digital Forensics: Lponte@mail - Ucf.edu Whicomb@mail - Ucf.edu
Master's Degree in Digital Forensics: Lponte@mail - Ucf.edu Whicomb@mail - Ucf.edu
Uploaded by
Cory HuberOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Master's Degree in Digital Forensics: Lponte@mail - Ucf.edu Whicomb@mail - Ucf.edu
Master's Degree in Digital Forensics: Lponte@mail - Ucf.edu Whicomb@mail - Ucf.edu
Uploaded by
Cory HuberCopyright:
Available Formats
Proceedings of the 40th Hawaii International Conference on System Sciences - 2007
Masters Degree in Digital Forensics
Philip Craiger Dept. of Engineering Technology & National Center for Forensic Science, philip@craiger.net Lucille Ponte Dept. of Legal Studies, lponte@mail.ucf.edu Carrie Whitcomb National Center for Forensic Science, whicomb@mail.ucf.edu Mark Pollitt Dept. of Engineering Technology, & National Center for Forensic Science, mpollitt@mail.ucf.edu Ronald Eaglin Dept. of Engineering Technology, reaglin@mail.ucf.edu University of Central Florida Orlando, FL 32816 Abstract
Law enforcement agents at the local, state, and Federal levels have informed us of backlogs of computer-related crime cases ranging from 18 months to three years. The primary cause of these backlogs is the lack of educated and trained personnel to serve as digital forensics examiners. In response to this need, the University of Central Florida has created a Masters in Digital Forensics. This 30-hour degree is an interdisciplinary mix of technical, legal, ethical, and courtroom testimony-based courses. Students must complete a capstone course as well as a graduate internship to demonstrate proficiency in the knowledge and skills acquired from the courses. information from computers captured during military actions. Unfortunately, the growth of computer-based crime has outpaced law enforcement and industries ability to manage these events. This growth has resulted in backlogs in the case of law enforcement, and in businesses quietly letting employees go who use computers for illegal or unethical purposes because of the lack of requisite personnel to handle these problems. The primary cause of these problems is the lack of forensics-educated personnel students or law enforcement agents required to examine and process the growing amounts of digital evidence. Backlogs are widespread phenomena for law enforcement at the local, state, and national level. Several agencies from around the country have informed us of backlogs ranging from eighteen months to three years. The lack of educated computer crime personnel is more apparent for rural communities who often lack funding for travel and the fee of educational programs, the total cost of which commonly exceeds tens of thousands of dollars per person per year. Even when an agency has funding, computer crime investigators are only allowed brief amounts of in-service training, and therefore offsite training is impractical. The burgeoning role of digital forensics in civil litigation and for government regulatory agencies will only put further stresses and demands on the digital forensics profession. The need for education and training programs is a national phenomenon. A study by the Institute for Security Technology Studies at Dartmouth College [7] found that 7% of computer crime investigators had no formal training, and only 11% had completed a full course of academic study in a related field. 90% of the survey respondents indicated an urgent need for additional training and education. Better-educated
1. Introduction
Digital Forensics has been called both a profession and a science that involves the identification, preservation, extraction, documentation, and interpretation of digital media for evidentiary purposes [15]. Business and industry use digital forensics to assemble information within their own businesses regarding intellectual property theft, fraud, network and computer intrusions, and unauthorized use of computers and other digital media. Law enforcement agencies employ digital forensics to gather digital evidence for a variety of crimes including child pornography, fraud, terrorism, extortion, cyberstalking, money laundering, forgery, and identity theft. Government agencies utilize digital forensics in ensuring compliance with relevant administrative regulations. Military and government intelligence agencies use digital forensics to collect intelligence
Proceedings of the 40th Annual Hawaii International Conference on System Sciences (HICSS'07) 0-7695-2755-8/07 $20.00 2007 1530-1605/07 $20.00 2007 IEEE
Proceedings of the 40th Hawaii International Conference on System Sciences - 2007
digital forensics professionals will help to gain further trust of and respect for the field of digital forensics. The backlogs of criminal and civil cases will increase as computers continue to permeate nearly every corner of everyday life, and as criminals, terrorists, and those engaged in civil wrongdoing become more proficient in the use of computers to further their illegal activities. The inability to efficiently prosecute criminals and terrorists or to bring appropriate civil actions because of a lack of educated personnel can only have negative effects upon our nations safety, security, competitiveness, economic stability, and sense of due process.
3. Student Outcomes
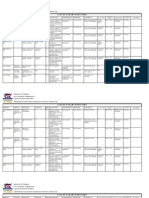
The 30-hour degree is composed of five required core courses, four elective courses (selected from a predefined set of courses), and a graduate internship. As required by the University guidelines, 15 of the 30 hours of course work must be taken at the 6000 level. (5000-level courses are open to both senior undergraduate and graduate students, whereas 6000level courses are graduate student only courses). It is a fact of academic life that departments usually work on a tight budget, therefore, administration frowns upon newly proposed courses that overlap with existing courses. This constraint required us to draw upon existing courses from several departments across the university. This not only provides the degree with a very multidisciplinary flavor, but also allows the degree program to draw upon the strengths of the various departments, which include engineering technology, computer science, chemistry, criminal justice and legal studies. The philosophy of the curriculum is to provide each student with: 1. 2. Technical computer skills, including detailed knowledge on computers and networks; Digital forensics knowledge and skills covering all aspects of the field, including all procedures to be used in the identification, collection, and examination/analysis of digital evidence from a myriad of digital devices; Criminal and civil legal issues so that the student understands the legal implications that may occur as a result of his/her actions; Numerous practical experiences to reduce the transition time from student to working professional.
2. Masters Degree in Digital Forensics
An interdisciplinary team of faculty members at the University of Central Florida (Orlando) has completed a proposal for a Masters of Science in Digital Forensics. The degree is a collaborative effort between various UCF academic departments and the National Center for Forensic Science (a State of Florida Type II Center and a member of the Department of Justices National Institute of Justice, Forensic Resource Network). The Masters in Digital Forensics is a professionally-oriented as opposed to research-oriented degree given the professions applied nature. Digital forensics is a highly interdisciplinary profession, combining subject matter from engineering technology, computer science, legal studies, criminal justice, and forensic science. Consequently, to be proficient digital examiners, students must acquire knowledge and skills in computing, file systems and operating systems, and networks; the legal justice system, relevant laws, expert testimony, and ethics; and knowledge of forensic science processes and procedures. The Masters in Digital Forensics is an extension of UCFs Graduate Certificate in Computer Forensics, which was initiated in 2001 to meet the growing demand for students with expertise in computer forensics. The certificate program includes five required courses encompassing technical, legal, and forensic science material. To date, there have been 50 students who have completed the graduate certificate. The five required courses that currently constitute the Graduate Certificate in Computer Forensics would serve as core-required courses in the Masters of Science in Digital Forensics.
3. 4.
In 2003, the National Institute of Justice created a committee composed of academicians and industry practitioners from the various forensic sciences to develop a model forensic science curriculum. This curriculum was published as Education and Training in Forensic Science: A Guide for Forensic Science Laboratories, Educational Institutions, and Students. The curriculum was targeted at biological and physical sciences, as the core requirements are fairly homogenous. What was not included was digital forensics, as the subject matter and student outcomes are significantly different from the traditional forensic sciences. As a consequence, in 2005 the National Institute of Justice created a similar committee Technical Working Group for Education and Training in Digital Forensics to develop a model curriculum for associate, undergraduate, and graduate degrees in
Proceedings of the 40th Annual Hawaii International Conference on System Sciences (HICSS'07) 0-7695-2755-8/07 $20.00 2007
Proceedings of the 40th Hawaii International Conference on System Sciences - 2007
digital forensics. The model curriculum was completed in early 2006, and will be published as Education and Training in Digital Forensics: A Guide for Forensic Science Laboratories, Educational Institutions, and Students. The Technical Working Group on Education and Training in Digital Evidence identified important professional student outcomes for undergraduate and graduate degrees in digital forensics. These objectives include: 1. 2. 3. 4. 5. 6. 7. Preparation for becoming a digital forensics professional Opportunities to establish a network of digital forensics contacts An educational background directly linked to the work in a digital forensics laboratory Exposure to the breadth of forensic science disciplines Acculturation into the digital forensics and justice communities Provision of a foundation for professional certification Emphasis on a wide range of courses (e.g., public speaking, ethics, and statistics) that may not be required in the curriculums of other natural science majors
e.
f. g.
h.
4. Curriculum
The required courses provide students with a technical background required to be a proficient examiner. These courses include: a. CHS 5503: Topics in Forensic Science (Dept. of Chemistry: three credits) This course covers the history of forensic science, basic forensic science principles as applied in various forensic specialties; current issues in digital evidence and professionalism. b. Computer Forensics I (Dept. of Computer Science: three credits) Covers the seizure and forensic examination of computer systems. Legal issues regarding seizure and chain of custody. Technical issues in acquiring computer evidence. Popular file systems are examined. Reporting issues in the legal system. c. Computer Forensics II (Dept. of Computer Science: three credits) This course covers the concepts of computer system security models, fundamentals of computer networking and the layered protocol architectures, detection and prevention of intrusion and attack, digital evidence collection and evaluation, and the legal issues involved in computer forensic analysis. d. CET 6000: Operating Systems and File Systems Forensics (Dept. of Engineering Technology:
i.
three credits) The course will provide students with a practical understanding of various operating systems, file systems, and applications that are relevant to digital forensics processes. CET 6001: Practice of Digital Forensics (Dept. of Engineering Technology: three credits) This is a capstone course where students demonstrate the ability to incorporate the knowledge and skills from previous courses. CET 6946: Graduate Internship (Dept. of Engineering Technology: three hours minimum). Elective Set 1: These courses provide a background on the legal and ethical issues. i. PLA 5587: Current Issues in Cyberlaw (Dept. of Legal Studies: three credits) Advanced examination and discussion of free speech, copyright, trademark, patent and privacy issues in the online environment through interactive class discussions, online discussions, postings, case study reviews, and legal research projects. ii. CJE 5688: Cybercrime and Criminal Justice (Dept. of Criminal Justice: three credits) Deals with the problem of cyber crime and the criminal use of the Internet. Includes investigation, enforcement and legal issues. Elective Set 2: These courses provide a background on courtroom/expert testimony a culmination of the examiners work. Student must choose a minimum of one of two courses. i. CHS 5518: Collection/Examination of Digital Evidence (Dept. of Chemistry: three credits) This course will cover the nature of Digital Evidence collection and examination under the constraints of Law and courtroom procedures. ii. CHS 5596: Forensic Expert in the Courtroom (Dept. of Chemistry: 3 credits) A study of the uses of technically and scientifically trained expert witnesses at trial. Elective set three: These courses provide specialized technical expertise. Students must choose a minimum one of two. i. CET 6000: Incident Response Technologies (Dept. of Engineering Technology: three credits) This course deals with computer intrusions and network attacks. ii. CAP 6133: Advanced Topics in Computer Security and Computer Forensics (Dept. of Computer Science: three credits) This course deals with current issues in computer security.
Students must select an additional three-hour course to complete their coursework requirements. Appropriate courses would include technical courses (such as computer security or incident response), legal
Proceedings of the 40th Annual Hawaii International Conference on System Sciences (HICSS'07) 0-7695-2755-8/07 $20.00 2007
Proceedings of the 40th Hawaii International Conference on System Sciences - 2007
studies or criminal justice (such as online privacy laws or crime scene investigative techniques), or accounting courses (such as forensic accounting). Allowing students some leeway in the selection of their electives provides them with the opportunity to truly tailor their degree to their interests or current profession. Electives are typically three-hour credit courses.
5. Target Populations for the Degree
We believe there are three somewhat distinct populations of students for the degree. First are graduate or advanced undergraduate students from computer science, engineering technology, information technology, or similar technical programs. The second group are security and IT workers from business and industry. We predict that many industry workers would participate in an online version of this degree, based on the numbers of industry workers who attend vendor training for related computer forensics products. The third, and perhaps largest customer would be local, state, and national law enforcement. There are hundreds of law enforcement digital evidence laboratories in the United States, and many more throughout Europe and Asia. Examiners at these laboratories have told us that an online version of our program would provide exactly what they are looking for: high-quality accessible online computer forensics courses. In addition, forensic examiner positions, as well as other IT security related professional certifications require continuing education credits to keep current with changes in technology. For instance, the CISSP certification requires 120 hours of continuing education credit every three years, as does the Guidance Software Certified EnCase Examiner certification. Continuing education is a requirement for most examiners and security specialists in business and industry; this holds equally true for all law enforcement forensic examiners. Therefore the numbers cited above would increase significantly due to interest from those seeking continuing education.
other intellectual property from a companys computer. Finally, an examiner in the military or intelligence communities may be responsible for identifying and recovering plans for poisoning a major water system from computers seized from a terrorist organization. Graduates from UCFs Graduate Certificate in Computer Forensics have been placed in a variety of positions. Several graduates now work as examiners for local law enforcement agencies. Other graduates now work as examiners for Federal law enforcement agencies, including the Drug Enforcement Agency and the FBI. Several graduates work in the private sector and industry in the capacity of systems and/or network administrators.
7. Role of Law in Digital Forensics
There is a common misconception among laypersons that digital forensics is primarily a technical field, dealing with computers and networks. Although digital forensics does require a good deal of technical skills, it is just as important that students understand the legal basis for their actions. Clearly, law is an integral component of any digital forensics educational program, providing digital forensics students with a solid legal foundation for executing their practical duties, as demonstrated in our program requirements and course descriptions. Undoubtedly, digital forensics courses should familiarize students with the mandates of relevance, authenticity, and integrity at the core of the admissibility of evidence in judicial proceedings [4][2][3]. However, digital forensics programs should also provide students with a broad-based understanding of various aspects of substantive and procedural law and landmark cases interpreting these relevant areas of law. Many programs offer foundation courses directly pertaining to the tasks and responsibilities of the digital forensics scientist in the context of criminal investigations and criminal court proceedings [6][2]. These courses are primarily geared toward aiding law enforcement in handling the dramatic rise in online child pornography, fraud, identity theft, white-collar crime, and cyberterrorism [6]. Typically, these core courses address the evidentiary rules and court procedures related to the search, seizure, identification, collection, preservation, and analysis of digital evidence in criminal matters [6][2]. In addition, a comprehensive understanding of the parameters of Fourth Amendment constitutional law is essential for digital forensics technologists dealing with criminal matters [2][12]. Programs should explore in detail the complexities of the Fourth Amendment and interpretive cases at the state and federal levels.
6. Jobs for Graduates
A typical position for someone with a degree in digital forensics would be a digital forensics examiner. Examiners are responsible for the identification, collection, and examination of digital media, written reports of their findings, and their presentation in court or other legal proceedings. For instance, an examiner working in law enforcement may be responsible for identifying and recovering fake drivers license graphics or pornographic images of children from a computer. An examiner in industry may be responsible for identifying and recovering stolen trade secrets or
Proceedings of the 40th Annual Hawaii International Conference on System Sciences (HICSS'07) 0-7695-2755-8/07 $20.00 2007
Proceedings of the 40th Hawaii International Conference on System Sciences - 2007
However, digital forensics is fast becoming an essential aspect of civil litigation, including employment, commercial and intellectual property disputes as well as government regulatory actions concerning online privacy and deceptive consumer practices [9][11][1]. Parties to civil cases or administrative actions are now calling upon digital forensics experts to examine and recover e-mails and documents stored on individual computers or network servers to prove their cases for damages and/or injunctive relief [9][11][1]. In addition, the judiciary is experimenting with the use of virtual courts in handling civil lawsuits in which some or all evidence will be supplied digitally [10][14]. As this demand grows, so will the need for digital forensics investigators with an understanding of the civil discovery process, civil liability claims, and civil court and administrative law procedures. At a Masters level, students need to consider their role in a broader context, moving beyond the practical demands of the field to an in-depth understanding of the evolving legal, social, and policy issues in cyberlaw. Unlike many other areas of law, cyberlaw is unsettled and still in its early development. Digital forensics graduates must be equipped to play influential roles in those future advancements as well as prepare for potential roles as instructors or researchers. In a Masters in Digital Forensics program, faculty should engage their students in a manner that encourages them to explore, examine, and debate cutting edge legal and ethical issues in the online environment [8][13]. Some key areas for inquiry include Internet governance and regulation, free speech, defamation, obscenity, copyright, trademark, patent, security, professional ethics, and privacy issues [8][13]. In oral and written formats, graduate students should be able to synthesize different perspectives and articulate their own views on these online topics. A challenging Masters curriculum should advance the participants critical analysis and thinking skills through a review of seminal court cases and case studies, interactive class discussions, online discussion postings, and substantive research projects. Graduates of digital forensics programs can play important roles in the development of cyberlaw and forensic practice if their education intertwines their technological skills with a comprehensive knowledge and understanding of substantive and procedural law as well as current legal and ethical policy concerns.
equally well in both technical and non-technical ways. For instance, examiners must be able to communicate with technical peers (other examiners) to describe the procedures used and their findings. Our experiences suggest that our technically-inclined students from computer-related fields have little trouble expressing themselves technically, but often have difficulty in explaining technical details to lay persons. (In our experience, formal, written reports are not a strong tradition in many, if not most, computer-related university courses, which may be part of the problem) In contrast, we found students with less technical backgrounds (law enforcement, criminal justice, etc.) have more trouble in expressing themselves in technical terms. Communication ability is an acquired skill, which mandates that all courses in the degree include written communication (e.g. written forensic reports) where the student must write a technical section as well as a non-technical section that is understandable to judges, attorneys, and jurors. It is important that each students communication ability is assessed throughout the program so that each graduates with the requisite skill. Oral communication is just as important as writing skill as many examiners are required to testify in front of a jury as part of their duties. The degrees capstone course, Practice of Digital Forensics, includes a moot court where students are required to create an exhibit for a case on which they have worked. The moot court is usually held in an actual courtroom over a weekend to provide a realistic setting. During the moot court, students are exposed to an hour of cross-examination conducted by retired Federal agents, local law enforcement agents, and attorneys. Moot court provides students an element of realism and a realistic job preview of an examiner. Perhaps most importantly it allows students to demonstrate their ability to communicate orally and think on their feet.
9. Delivery
There will be a two-stage delivery of the curriculum. In the first year approximately half of the courses will be taught in a purely distance learning format. The remaining courses will be delivered through a hybrid format, i.e., face-to-face with supporting learning technologies. In year two we expect to have our degree entirely online. All of the current faculty members participating in the program have successfully completed a course provided by the UCF Distance Learning Department on how to develop online courses. The online format provides several advantages over traditional classroom delivery, including the ability to reach non-traditional, working and mature students and the ability to reach a geographically
8. The Importance of Communication Abilities
The ability to communicate in both written and oral form is a critical skill for forensic scientists. As a scientist, examiners must be able to express themselves
Proceedings of the 40th Annual Hawaii International Conference on System Sciences (HICSS'07) 0-7695-2755-8/07 $20.00 2007
Proceedings of the 40th Hawaii International Conference on System Sciences - 2007
dispersed student population. We expect our primary student population to be working professionals who are incapable of taking time off during the day to attend live courses. A disadvantage to online courses is that students do not have access to laboratories with the special hardware and software that is frequently encountered in the profession of digital forensics. From our experience, we have found that there are several methods of providing students with real-world type of assignments that obviates the need for special hardware and software. The first is to structure assignments so that students are able to download evidence (typically forensic images of floppy disks, CD disks, and even small hard drives that have been compressed to reduce download time). The students then use free and/or Open Source tools that run under Linux (which is itself free) to conduct forensic analyses. One perceived drawback is that most of these tools require knowledge of the Linux command line, as most tools do not come with a graphical user interface. We believe this to be an advantage: students are forced to work at a level closer to the operating system and file system, resulting in a more intimate familiarity with each. We predict that perhaps 25-50% of students will enter the program with some Linux experience. Nevertheless, we have found that students are quickly able to learn the commands required to complete assignments. The second method is to require students to spend a short, intensive laboratory period onsite at the end of the semester for certain classes, particularly the computer and network-based classes. Here students will spend eight to ten hours a day for several days working with special hardware and software that they are likely to encounter in digital forensics practice. We are also considering holding flexible lab periods so that students can select from several weekends at the end of the semester for those students to accommodate all students.
(FBI) and over 20 years of combined experience of digital forensics as law enforcement officers.
11. References
[1] B. A. Howell, Digital Forensics: Sleuthing on Hard Drives and Networks, 31 Ver. B. J. & L. Dig. 39, 2005. [2] Department of Justice, Computer Crime & Intellectual Prop. Section, Criminal Div., Searching and Seizing Computers and Obtaining Electronic Evidence in Criminal Investigations, 2002, available at http://www.cybercrime.gov/s&smanual2002.htm (last visited June 7, 2006). [3] E. Kenneally, Confluence of Digital Evidence and the Law: On the Forensic Soundness of Live-Remote Digital Evidence Collection, UCLA J. L Tech. 5 (2005). [4] Federal Rules of Evidence (F.R.E.) 702, 901. [5] Federal Trade Commissions Official Website http://www.ftc.gov (last visited June 12, 2006). [6] Graduate Certificate in Digital Forensics, University of central Florida, available at http://ncfs.ucf.edu/home.html (last visited June 7, 2006). [7] Institute for Security and Technology Studies, Dartmouth College, Law Enforcement Tools And Technologies for Investigating Cyber Attacks: A National Needs Assessment, Dartmouth College, Hanover NH, 2002. [8] L. Burgunder, Legal Aspects Of Managing Technology, 3rd ed., New York, Thomson South-Western, 2004. [9] L. M. Arent, R. D. Brownstone & W. A. Fenwick, EDiscovery: Preserving, Requesting & Producing Electronic Information, 19, Santa Clara Computer & High Tech. L. J. 131, December, 2002. [10] L. M. Ponte, The Michigan Cyber Court: A Bold Experiment in the Development of the First Public Virtual Courthouse, 4 N.C. J. L. & Tech. 51 (Fall 2002). [11] Mark Ballard, Digital Headache, E-discovery costs soar into the millions, and litigants seek guidance, 25 NATL L. J. A18 (February 10, 2003). [12] O. S. Kerr, Searches and Seizures in a Digital World, 119 HARV. L. REV. 531, (2005). [13] R. A. Spinello, CyberEthics: Morality and Law in Cyberspace, New York, Jones and Bartlett, 2003. [14] S. C. Sandstrom & A. Bloomberg, An ancient art jazzed by high tech, 3, Leg. Tech. News 1, Spring 2002. [15] W. G. Kruse II and J. G. Heiser, Computer Forensics: Incident Response Essentials. Addison-Wesley, 2002.
10. Faculty
Interdisciplinary programs require interdisciplinary teams of faculty members. Faculty members teaching courses in the degree include five full-time tenuretrack/tenured professors, two non-tenure track professors, one instructor, and one adjunct instructor. It was clear from the outset that the professional realworld nature of the degree would require that the program have faculty members with real-world experience in law enforcement and digital forensics. Consequently we have hired two non-tenure track faculty members who have 15-20 years of law enforcement experience at the state and Federal levels
Proceedings of the 40th Annual Hawaii International Conference on System Sciences (HICSS'07) 0-7695-2755-8/07 $20.00 2007
You might also like
- The Truth About Gang Stalking: Community Policing and Usage of TechnologiesDocument77 pagesThe Truth About Gang Stalking: Community Policing and Usage of TechnologiesChris Lissa Myers83% (6)
- Individual Membership-EIZ Application Form-10Document4 pagesIndividual Membership-EIZ Application Form-10Timothy KapungweNo ratings yet
- Sample of Short PHD ProposalDocument8 pagesSample of Short PHD Proposalscholarsassist100% (4)
- CDR EA Outcome Letter SampleDocument1 pageCDR EA Outcome Letter Samplesdivya02No ratings yet
- Ssca130212-4.1.7 Bengtech New Program StreamsDocument23 pagesSsca130212-4.1.7 Bengtech New Program StreamsA SNo ratings yet
- Digital Forensics Education in PakistanDocument3 pagesDigital Forensics Education in Pakistanmehmilhabib9No ratings yet
- C&DF CurriculumDocument10 pagesC&DF Curriculumtech2click100% (1)
- Literature Review Computer ForensicsDocument7 pagesLiterature Review Computer Forensicsc5r0qjcf100% (1)
- CBS GradDipCombineDocument2 pagesCBS GradDipCombinegallianomcflyNo ratings yet
- National Law Institute University, Bhopal: Information Brochure 2018-19 Master of Cyber Law and Information SecurityDocument16 pagesNational Law Institute University, Bhopal: Information Brochure 2018-19 Master of Cyber Law and Information SecurityWajid AliNo ratings yet
- Research Paper Topics For Computer ForensicsDocument7 pagesResearch Paper Topics For Computer Forensicsefdwvgt4100% (1)
- 2012 - MoLekol - An Enhanced Learning Support System For Class-Based ScenariosDocument8 pages2012 - MoLekol - An Enhanced Learning Support System For Class-Based ScenariosSameerchand PudaruthNo ratings yet
- Another Brick in The Wall An Exploratory Analysis of Digital Forensics Programs in The United StatesDocument8 pagesAnother Brick in The Wall An Exploratory Analysis of Digital Forensics Programs in The United Stateshenu wigastaNo ratings yet
- ACPO Manager GuideDocument117 pagesACPO Manager Guidemsaamir115851No ratings yet
- Digital Forensics Sample Case Study ReportDocument19 pagesDigital Forensics Sample Case Study Reportdpkvk98157No ratings yet
- Cybersecurity Program For Philippine Higher Education InstitutionsDocument6 pagesCybersecurity Program For Philippine Higher Education InstitutionsCarl Vince BautistaNo ratings yet
- Dissertation Computer ForensicsDocument4 pagesDissertation Computer ForensicsWriteMyCustomPaperCanada100% (1)
- Forensic Evidence in The Digital AgeDocument82 pagesForensic Evidence in The Digital AgeSunny ProjectNo ratings yet
- Computer Forensics Research Paper IdeasDocument6 pagesComputer Forensics Research Paper Ideasmoykicvnd100% (1)
- Forensic ScienceDocument12 pagesForensic Sciencesomya jainNo ratings yet
- Live Time Forensics Brochuredraftv6LRDocument40 pagesLive Time Forensics Brochuredraftv6LRCandy ChungNo ratings yet
- Dissertation Topics in Computer ForensicsDocument4 pagesDissertation Topics in Computer ForensicsAcademicPaperWritersUK100% (1)
- Digital ForensicsDocument15 pagesDigital ForensicsCo VidNo ratings yet
- Course Details - Technology Law and PolicyDocument6 pagesCourse Details - Technology Law and PolicyShivaniNo ratings yet
- Graduate ProgramsDocument8 pagesGraduate Programsapi-316879421No ratings yet
- Dissertation Topics For Digital ForensicsDocument7 pagesDissertation Topics For Digital ForensicsBuyCollegePapersProvo100% (1)
- Jurnal Forensic Digital Analysis2Document39 pagesJurnal Forensic Digital Analysis2nanaNo ratings yet
- Forensic Computing Dissertation IdeasDocument5 pagesForensic Computing Dissertation IdeasHowToWriteMyPaperLittleRock100% (1)
- Digital ForensicsDocument15 pagesDigital ForensicsSIDDHARTHANo ratings yet
- Advanced Certification ProgrammesDocument9 pagesAdvanced Certification ProgrammesಕೇधाR ಗೋDaसेNo ratings yet
- Computer Forensic Dissertation IdeasDocument8 pagesComputer Forensic Dissertation IdeasBestCustomPapersSingapore100% (1)
- HNU Annual Crime and Fire Safety RPT 2012Document59 pagesHNU Annual Crime and Fire Safety RPT 2012Holy Names University100% (1)
- Computer Forensics Dissertation IdeasDocument6 pagesComputer Forensics Dissertation IdeasCustomHandwritingPaperManchester100% (1)
- Final EportDocument20 pagesFinal EportIngrid BayiyanaNo ratings yet
- Computer Forensics Research Paper TopicsDocument7 pagesComputer Forensics Research Paper Topicsaflbtcxfc100% (1)
- Capstone ProjectDocument15 pagesCapstone Projectpandasinghk2001No ratings yet
- Study On Computer Evidence Forensics ZHU ZhenfangDocument3 pagesStudy On Computer Evidence Forensics ZHU ZhenfangInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Dissertation On Cybercrime in IndiaDocument6 pagesDissertation On Cybercrime in IndiaCustomWrittenPaperSingapore100% (1)
- PHD Research Project Proposal: TitleDocument5 pagesPHD Research Project Proposal: Titlethanhtuan.to1993No ratings yet
- Paise Fakoo Tamsa DekhoDocument14 pagesPaise Fakoo Tamsa DekhoveerNo ratings yet
- 18LLB077 Forensic LawDocument16 pages18LLB077 Forensic LawSAI DEEP GADANo ratings yet
- Digital Forensic in The FutureDocument18 pagesDigital Forensic in The FutureHayes JohnNo ratings yet
- Benefits of Participation RFCLDocument3 pagesBenefits of Participation RFCLsilly_rabbitzNo ratings yet
- Law Enforcement Challenges in Digital ForensicsDocument44 pagesLaw Enforcement Challenges in Digital Forensicsblkjack2u100% (1)
- IJDCFFinal 6Document1 pageIJDCFFinal 6IshanNo ratings yet
- A Model For Digital Evidence Admissibility AssessmentDocument17 pagesA Model For Digital Evidence Admissibility AssessmentKikidoo IdNo ratings yet
- Building FBI Computer Forensics Capacity One Lab at A Time 2004 Digital InvestigationDocument6 pagesBuilding FBI Computer Forensics Capacity One Lab at A Time 2004 Digital InvestigationglennallynNo ratings yet
- MCLIS Brochure 2023 24Document27 pagesMCLIS Brochure 2023 24sharadNo ratings yet
- Digital ForensicsDocument4 pagesDigital ForensicsAnand KhotNo ratings yet
- "Managing Cyber Crimes in India - Issues and Challenges": Mrs - Vineetha.P.K Principal, Sarada Vilas Law College, MysoreDocument12 pages"Managing Cyber Crimes in India - Issues and Challenges": Mrs - Vineetha.P.K Principal, Sarada Vilas Law College, MysoreAkash GuptaNo ratings yet
- Practical Digital Forensics - Sample ChapterDocument31 pagesPractical Digital Forensics - Sample ChapterPackt Publishing100% (2)
- Memorandum Issuance From CICC (Request For Info)Document5 pagesMemorandum Issuance From CICC (Request For Info)Bert CruzNo ratings yet
- Research Paper Computer CrimeDocument8 pagesResearch Paper Computer Crimev0j0bysyt1m3100% (1)
- A Review On Digital Forensic Investigation Frameworks and Real World Cyber Crime CasesDocument7 pagesA Review On Digital Forensic Investigation Frameworks and Real World Cyber Crime CasesEditor IJRITCCNo ratings yet
- Oa 82Document11 pagesOa 82jariya.attNo ratings yet
- Review of Related Literature and Studies: Tulip St. Area C Camarin, Caloocan City Bachelor of Science in Computer ScienceDocument9 pagesReview of Related Literature and Studies: Tulip St. Area C Camarin, Caloocan City Bachelor of Science in Computer ScienceJohn EricNo ratings yet
- Cybersecurity Program For Philippine Higher Education InstitutionsDocument13 pagesCybersecurity Program For Philippine Higher Education InstitutionsMark FloresNo ratings yet
- EITS Status and Activity Report For April 2015Document4 pagesEITS Status and Activity Report For April 2015accidentalcioNo ratings yet
- Cyber Crimes and Technical Issues Under The Jordanian Information System Crimes LawDocument14 pagesCyber Crimes and Technical Issues Under The Jordanian Information System Crimes LawMagadaNo ratings yet
- Using OSS For Forensic PurposesDocument7 pagesUsing OSS For Forensic PurposesManuel DelgadoNo ratings yet
- Term Paper About Cybercrime LawDocument8 pagesTerm Paper About Cybercrime Lawaflsiosbe100% (1)
- Cyber Crime Research Paper OutlineDocument6 pagesCyber Crime Research Paper Outlineefjddr4z100% (1)
- What Is GeophysicsDocument26 pagesWhat Is Geophysics1234abcdNo ratings yet
- Engineering Council of South Africa: Background: The ECSA Education System DocumentsDocument14 pagesEngineering Council of South Africa: Background: The ECSA Education System Documentsprisca ncuncuNo ratings yet
- Member Assessment GuidanceDocument17 pagesMember Assessment GuidanceAbhishek ShatagopachariNo ratings yet
- CHED Sample OBE Syllabus AT 2 AUTO MECHANICALDocument7 pagesCHED Sample OBE Syllabus AT 2 AUTO MECHANICALMarvin Sarmiento TalimonganNo ratings yet
- Universiti Kuala Lumpur Malaysia France Institute (Unikl Mfi)Document6 pagesUniversiti Kuala Lumpur Malaysia France Institute (Unikl Mfi)cypanNo ratings yet
- 2021 - Advert - Network Planning and Network MaintenanceDocument6 pages2021 - Advert - Network Planning and Network MaintenancecharltonNo ratings yet
- 1293X Master Electrician Exam Information Package 2012Document12 pages1293X Master Electrician Exam Information Package 2012noneco100% (1)
- IAB 252r2 14 SV00 Guideline For Personnel With Qualification For Welding Coordination SVDocument27 pagesIAB 252r2 14 SV00 Guideline For Personnel With Qualification For Welding Coordination SVjimingeorge100% (1)
- Merged Voter Register 2021 June 24Document602 pagesMerged Voter Register 2021 June 24jckapindaNo ratings yet
- EWF QualificationDocument42 pagesEWF Qualificationromanosky11No ratings yet
- Bem Code of Ethics - 2016Document12 pagesBem Code of Ethics - 2016Dan CNo ratings yet
- Application Guidance For Fellow (FCIBSE)Document17 pagesApplication Guidance For Fellow (FCIBSE)ManNo ratings yet
- Schedule of Licensure Examinations For Year 2009 Professional Regulation Commission PRC Manila City Resolution No. 2008 - Series of 2008 Republic of The PhilippinesDocument5 pagesSchedule of Licensure Examinations For Year 2009 Professional Regulation Commission PRC Manila City Resolution No. 2008 - Series of 2008 Republic of The PhilippinesJulio Iñigo López100% (23)
- Admission BS Fall 21Document1 pageAdmission BS Fall 21Abdul Naveed SialNo ratings yet
- The Institute of Mechanical Engineers (Imeche) : 6 CHAPTER 1 Engineers and Designers-Career Paths-InstitutesDocument1 pageThe Institute of Mechanical Engineers (Imeche) : 6 CHAPTER 1 Engineers and Designers-Career Paths-Institutesmasoud132No ratings yet
- Re - Admin Case For Dishonesty - Falsification - Katly (A.m. No. 2003-9-SC, March 25, 2004)Document7 pagesRe - Admin Case For Dishonesty - Falsification - Katly (A.m. No. 2003-9-SC, March 25, 2004)Fatzie MendozaNo ratings yet
- IAB 252r8-07Document24 pagesIAB 252r8-07Jayanta82No ratings yet
- ST LUKES v. NLRCDocument2 pagesST LUKES v. NLRCDanyNo ratings yet
- Chapter 2 MEC600Document50 pagesChapter 2 MEC600Aziful AiemanNo ratings yet
- Engineers (Registration, Etc.) ACT: Main MenuDocument32 pagesEngineers (Registration, Etc.) ACT: Main MenuAdeniji OlusegunNo ratings yet
- LANDAS - LISING - PILAPIL - STEP 1 RechckingDocument66 pagesLANDAS - LISING - PILAPIL - STEP 1 RechckingjeremiahNo ratings yet
- 1E ECSA Candidate AppformDocument9 pages1E ECSA Candidate AppformSilas MangwendeNo ratings yet
- Engineering in SocietyDocument7 pagesEngineering in Societyjahremade jahremadeNo ratings yet
- Tup Taguig - Program OfferingsDocument6 pagesTup Taguig - Program OfferingsRafhael MangalaoNo ratings yet
- Bulletin of Vacant Positions April 1-30, 2015Document89 pagesBulletin of Vacant Positions April 1-30, 2015CscfoAgusanDelNorteNo ratings yet
- IEA Graduate Attributes and Professional Competencies 2021.1 Sept 2021Document23 pagesIEA Graduate Attributes and Professional Competencies 2021.1 Sept 2021ageldresmNo ratings yet
- Guide To Professional Registration With The Engineering CouncilDocument8 pagesGuide To Professional Registration With The Engineering CouncilbassamNo ratings yet