Professional Documents
Culture Documents
XWorm RAT Malware
XWorm RAT Malware
Uploaded by
Farah YaminCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
XWorm RAT Malware
XWorm RAT Malware
Uploaded by
Farah YaminCopyright:
Available Formats
Summary:
A malware campaign targeting Ukraine has been identified, orchestrated by the UAC-0184 threat
actor group. This campaign marks a continuation of their persistent efforts to infiltrate Ukrainian
entities, utilizing tactics to deploy the XWorm Remote Access Trojan (RAT). The attackers employ
deceptive lure documents and advanced malware delivery mechanisms, posing a significant threat to
targeted systems and data security.
The malware campaign begins with the distribution of a malicious LNK file hidden within phishing
emails. When executed, the LNK file triggers a PowerShell script that downloads a ZIP archive
containing legitimate and malicious Python components, including an encrypted payload. Through
techniques like DLL sideloading and Shadowloader, the final payload, XWorm RAT, is executed. This
malware is designed for remote access and exhibits capabilities such as data theft, DDoS attacks, and
facilitating additional malware downloads. Despite current analysis showing an inactive Command-
and-Control server, the potential for future malicious activities remains high.
UAC-0184's campaign underscores their persistent targeting of Ukrainian sectors, utilizing evolving
tactics to evade detection and maintain access to compromised systems. The deployment of XWorm
RAT highlights their intent to establish persistent remote access, posing ongoing security risks.
Organizations are urged to enhance their defenses against phishing attacks and remain vigilant against
such threats targeting critical infrastructure and sensitive data.
Threat Profile:
Tactic Technique Id Technique
Execution T1059 Command and Scripting Interpreter
T1547 Boot or Logon Autostart Execution
Persistence
T1574 Hijack Execution Flow
Defense Evasion T1055 Process Injection
T1027 Obfuscated Files or Information
T1140 Deobfuscate/Decode Files or Information
T1057 Process Discovery
Discovery
T1518 Software Discovery
T1071 Application Layer Protocol
Command and Control
T1105 Ingress Tool Transfer
You might also like
- OilRig - A Profile of The Threat ActorDocument30 pagesOilRig - A Profile of The Threat Actorejan100% (1)
- MITRE ATT&CK Wheel of FortuneDocument122 pagesMITRE ATT&CK Wheel of FortuneMilin ShahNo ratings yet
- Venus Ransomware Analyst NoteDocument5 pagesVenus Ransomware Analyst NoteCyprien YENo ratings yet
- Conti (s0575)Document5 pagesConti (s0575)anup.tilekar.86No ratings yet
- APT39 AnswersDocument4 pagesAPT39 Answersimane sadaniNo ratings yet
- Mitre ATT&CK Top TecnicasDocument4 pagesMitre ATT&CK Top TecnicasInfonet MundoNo ratings yet
- Containers MatrixDocument1 pageContainers MatrixNuryadin Usman Abdurrahim AsSampiti IINo ratings yet
- Making Mitre Att&Ck Framework New Hunting Standard: January 2020 SentineloneDocument14 pagesMaking Mitre Att&Ck Framework New Hunting Standard: January 2020 SentineloneShreekanth MuraliNo ratings yet
- Mobile Attack Cheat Sheet 1708115239Document1 pageMobile Attack Cheat Sheet 1708115239Joash MacentonNo ratings yet
- Incident Response Techniques For Ransomware Attacks Understand Modern Ransomware Attacks - BibisDocument228 pagesIncident Response Techniques For Ransomware Attacks Understand Modern Ransomware Attacks - BibisSpace Spark100% (2)
- Mitre Overview 2021-01-16Document5 pagesMitre Overview 2021-01-16iaas labsNo ratings yet
- Network MatrixDocument1 pageNetwork MatrixrakivanatanNo ratings yet
- iOS AttackDocument1 pageiOS AttackrakivanatanNo ratings yet
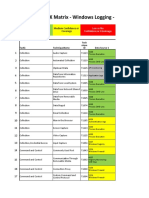
- Mitre ATT@CK Matrix - Windows Logging - Basic: High Confidence or Covereage Medium Confidence or CoverageDocument27 pagesMitre ATT@CK Matrix - Windows Logging - Basic: High Confidence or Covereage Medium Confidence or CoverageTuba ŞengünNo ratings yet
- Uncovering The Threat of BlueBravo With GraphicalNeutrino and BEATDROP - TA2023055Document6 pagesUncovering The Threat of BlueBravo With GraphicalNeutrino and BEATDROP - TA2023055tekjaNo ratings yet
- CSA - TTPs of Indicted APT40 Actors Associated With China MSS Hainan State Security DepartmentDocument14 pagesCSA - TTPs of Indicted APT40 Actors Associated With China MSS Hainan State Security Departmentmalikjavaid093No ratings yet
- Mitre Att&ck v9Document22 pagesMitre Att&ck v9Fabiano DiscacciatiNo ratings yet
- Tactic, Techniques and Procedures (Incident Respone)Document41 pagesTactic, Techniques and Procedures (Incident Respone)ASAD ULLAHNo ratings yet
- TLP WHITE UNCLASSIFIED 20200416-AzoRult MalwareDocument20 pagesTLP WHITE UNCLASSIFIED 20200416-AzoRult Malwaremanu_zachariaNo ratings yet
- Cloud MatrixDocument1 pageCloud MatrixrakivanatanNo ratings yet
- Red Team OperationsDocument16 pagesRed Team OperationsandreyaguiarazeNo ratings yet
- Red Team OperationsDocument15 pagesRed Team OperationsMarcelo JuniorNo ratings yet
- Advanced Threat Detection and Response Tech BriefDocument4 pagesAdvanced Threat Detection and Response Tech Briefsimrankarki880No ratings yet
- Red Team TrainingDocument16 pagesRed Team TrainingFernando da Costa CorreaNo ratings yet
- MITRE LockBit 3.0Document2 pagesMITRE LockBit 3.0kuronekonokanojoNo ratings yet
- Beyond FTP White PaperDocument8 pagesBeyond FTP White Paper1986puneetNo ratings yet
- DTRAK Training SlideDocument15 pagesDTRAK Training SlideIHOMP EVRMCNo ratings yet
- China-Linked Cyber Actors Hide in Router FirmwareDocument12 pagesChina-Linked Cyber Actors Hide in Router FirmwareChristian René Moreno Sánchez de la VegaNo ratings yet
- Chapter - 3.1: FTP and TelnetDocument16 pagesChapter - 3.1: FTP and TelnetNandgulabDeshmukhNo ratings yet
- 6 - InterruptDocument32 pages6 - InterruptMohamed AlfarashNo ratings yet
- Account Security ChecklistDocument15 pagesAccount Security ChecklistRyalapeta Venu YadavNo ratings yet
- Data Loss PreventionDocument20 pagesData Loss Preventiondeepak4315No ratings yet
- Living Off Theland An APT Case StudyDocument30 pagesLiving Off Theland An APT Case StudyfelixNo ratings yet
- RFC7457Document13 pagesRFC7457dasNo ratings yet
- Fortios 5.4.0 Log ReferenceDocument127 pagesFortios 5.4.0 Log ReferencemarketingPerNegatiNo ratings yet
- 5100 Remote Administration GuideDocument21 pages5100 Remote Administration GuideFarouk AnçaNo ratings yet
- T1 PRI Troubleshooting Flowchart: Document ID: 9344Document3 pagesT1 PRI Troubleshooting Flowchart: Document ID: 9344Gil HaleNo ratings yet
- Tripwire ReportDocument34 pagesTripwire ReportSanjeev Yadav75% (4)
- Penetration Testing SlidesDocument64 pagesPenetration Testing SlidestesterforallneedsNo ratings yet
- Summit Archive 1569863860Document50 pagesSummit Archive 1569863860mangelchavezNo ratings yet
- Command and Control - HTTPSDocument9 pagesCommand and Control - HTTPSbrunodiaz2038No ratings yet
- Windows ATT&CK - Logging Cheat Sheet - Ver - Sept - 2018Document15 pagesWindows ATT&CK - Logging Cheat Sheet - Ver - Sept - 2018Ike ChenNo ratings yet
- Fireeye HX SeriesDocument2 pagesFireeye HX Serieslingo.chichalaNo ratings yet
- Stop Ramsonware Phobos RansomwareDocument18 pagesStop Ramsonware Phobos RansomwareafeeshNo ratings yet
- AA20 183A Defending Against Malicious Cyber Activity OriginatingDocument8 pagesAA20 183A Defending Against Malicious Cyber Activity OriginatingKabu BabNo ratings yet
- Us 17 Quarta Breaking The Laws of Robotics Attacking Industrial RobotsDocument82 pagesUs 17 Quarta Breaking The Laws of Robotics Attacking Industrial Robotsandre.fronemanzaNo ratings yet
- Atex - PM 2Document3 pagesAtex - PM 2normatividad teletrabajoNo ratings yet
- Use The Internet To Determine The Purpose/uses of FTP and Telnet. Write A Short Paragraph Explain The Purpose, Pros, and Cons of Each ApplicationDocument1 pageUse The Internet To Determine The Purpose/uses of FTP and Telnet. Write A Short Paragraph Explain The Purpose, Pros, and Cons of Each Applicationghsdsd1No ratings yet
- Internet Protocol (IP)Document5 pagesInternet Protocol (IP)JAMESTALAN JUDO KONSIKANNo ratings yet
- Penetration Testing LabDocument9 pagesPenetration Testing LabnvNo ratings yet
- Black Hat USA 2011 - Weapons of Targeted Attack: Modern Document Exploit Techniques (Slides)Document95 pagesBlack Hat USA 2011 - Weapons of Targeted Attack: Modern Document Exploit Techniques (Slides)sttsaiNo ratings yet
- ATTCK Matrix For EnterpriseDocument1 pageATTCK Matrix For EnterpriseNuryadin Usman Abdurrahim AsSampiti IINo ratings yet
- AA21-265A-Conti Ransomware TLP WHITEDocument9 pagesAA21-265A-Conti Ransomware TLP WHITEZERO 900No ratings yet
- File Transfer Protocol Using MPLAB Harmonyv3 TCPIP DS00003475ADocument25 pagesFile Transfer Protocol Using MPLAB Harmonyv3 TCPIP DS00003475AMarin JuniorNo ratings yet
- Global en Queue Services Deadlock.Document11 pagesGlobal en Queue Services Deadlock.Neerajroy GNo ratings yet
- NetNumen T31 EMS Principle Introduction - R1 - T30-T31-T32Document70 pagesNetNumen T31 EMS Principle Introduction - R1 - T30-T31-T32DavoodNo ratings yet
- Stuxnet Review 1645451085Document25 pagesStuxnet Review 1645451085hiehie272No ratings yet
- Securing Erp Systems Final PresentationDocument18 pagesSecuring Erp Systems Final Presentationimad khanNo ratings yet