Professional Documents
Culture Documents
tracing (2) 3
tracing (2) 3
Uploaded by
ayuzsharma9929Copyright:
Available Formats
You might also like
- Privacy Calculus Theory and Its Applicability-2016Document5 pagesPrivacy Calculus Theory and Its Applicability-2016Muzammil QamarNo ratings yet
- Protools Keyboard ShortcutsDocument27 pagesProtools Keyboard Shortcutsprettycool2No ratings yet
- tracing (2) 4Document9 pagestracing (2) 4ayuzsharma9929No ratings yet
- tracing (2) (1)Document4 pagestracing (2) (1)ayuzsharma9929No ratings yet
- tracing (2)Document4 pagestracing (2)ayuzsharma9929No ratings yet
- A Survey of COVID-19 Contact Tracing AppsDocument23 pagesA Survey of COVID-19 Contact Tracing Appsnawwad65No ratings yet
- A First Look at Privacy Analysis of COVID-19 Contact-Tracing Mobile ApplicationsDocument11 pagesA First Look at Privacy Analysis of COVID-19 Contact-Tracing Mobile ApplicationsNguyễnTrần ThanhLâmNo ratings yet
- Case-Initiated COVID-19Document4 pagesCase-Initiated COVID-19Ikmal ShahromNo ratings yet
- F++1-s2.0-S2214212620308048-mainDocument11 pagesF++1-s2.0-S2214212620308048-mainsandro.nieto.mNo ratings yet
- 3P Framework PDFDocument13 pages3P Framework PDFsujiteduNo ratings yet
- Balancing Privacy at The Time of Pandemic: Global ObservationDocument11 pagesBalancing Privacy at The Time of Pandemic: Global ObservationIJPHSNo ratings yet
- Chapter 2 SampleDocument7 pagesChapter 2 SampleAlexxa Gabrielle JaneoNo ratings yet
- LL.M5230 Introduction To Law - Student Id-36365534Document5 pagesLL.M5230 Introduction To Law - Student Id-36365534Lyn JeninsNo ratings yet
- Unit Article DiscussionsDocument8 pagesUnit Article Discussionsgitaumary045No ratings yet
- DIT1243 Tutorial 12Document4 pagesDIT1243 Tutorial 12Cathay WongNo ratings yet
- 1.0 Synopsis Network Security 14-11-2019Document9 pages1.0 Synopsis Network Security 14-11-2019Irfan Zafar AwanNo ratings yet
- Ethical Concerns in COVID-19 ApplicationsDocument12 pagesEthical Concerns in COVID-19 Applicationssadekinborno07No ratings yet
- EMILIO MORDINI - Biometrics Ethics Algorithms - 20th Int.l Summer School On Biometrics 2022Document33 pagesEMILIO MORDINI - Biometrics Ethics Algorithms - 20th Int.l Summer School On Biometrics 2022Emilio MordiniNo ratings yet
- MSC Project ProposalDocument4 pagesMSC Project ProposalUsman ChaudharyNo ratings yet
- IoT Unit-4 According To RGPVDocument10 pagesIoT Unit-4 According To RGPVMadhav PanditNo ratings yet
- Entropy-Based Face Recognition and Spoof Detection For Security ApplicationsDocument18 pagesEntropy-Based Face Recognition and Spoof Detection For Security ApplicationsIvan FadillahNo ratings yet
- 1 s2.0 S1084804520302794 MainDocument32 pages1 s2.0 S1084804520302794 MainLibrary DaiictNo ratings yet
- Privacy Security and Resilience in Mobile Healthcare ApplicationsDocument16 pagesPrivacy Security and Resilience in Mobile Healthcare ApplicationsMUH.ALFIKRI TRI ANGGORO PAMUNGKASNo ratings yet
- Chapter 1editedDocument8 pagesChapter 1editedDaniel PerrerasNo ratings yet
- Chapter SixDocument15 pagesChapter SixTade GaromaNo ratings yet
- Statement of Research: Background and Current WorkDocument3 pagesStatement of Research: Background and Current WorkReza BarkhordariNo ratings yet
- High Level Privacy and Security Design For NHS COVID-19 Contact Tracing AppDocument13 pagesHigh Level Privacy and Security Design For NHS COVID-19 Contact Tracing AppBrkNo ratings yet
- Pervasive and Mobile Computing: Claudio Bettini, Daniele RiboniDocument16 pagesPervasive and Mobile Computing: Claudio Bettini, Daniele Riboniliviu_xzibit5770No ratings yet
- Applications of Wireless Sensor Networks in HealthcareDocument34 pagesApplications of Wireless Sensor Networks in HealthcaresaisreeknsNo ratings yet
- ICT EditedDocument6 pagesICT Editedwangathioli 1No ratings yet
- Gerek Jordan Ethics Essay Final DraftDocument10 pagesGerek Jordan Ethics Essay Final Draftapi-756848761No ratings yet
- Designing ProjectDocument4 pagesDesigning Projectvinaydevrukhkar2629No ratings yet
- International Journal of Information Management: Kane J. Smith, Gurpreet Dhillon, Lemuria Carter TDocument15 pagesInternational Journal of Information Management: Kane J. Smith, Gurpreet Dhillon, Lemuria Carter TLuster LeesaNo ratings yet
- Ethicsessay v2Document10 pagesEthicsessay v2api-727268225No ratings yet
- Unit 4 - Internet of Things - WWW - Rgpvnotes.in PDFDocument12 pagesUnit 4 - Internet of Things - WWW - Rgpvnotes.in PDFVinutha MNo ratings yet
- Individual AssignmentDocument13 pagesIndividual AssignmentLife of LokiniNo ratings yet
- Wireless Applications and PrivacyDocument5 pagesWireless Applications and PrivacyYoussef ZinounNo ratings yet
- Chapter 6 Ethics NewDocument24 pagesChapter 6 Ethics NewAshenafi PaulosNo ratings yet
- Cyber Security EthicsDocument8 pagesCyber Security Ethicsngolodedan2No ratings yet
- Effective Risk Detection and Summary Risk Communication For Android AppsDocument9 pagesEffective Risk Detection and Summary Risk Communication For Android AppsInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- The Dialogue Response - FRTDocument8 pagesThe Dialogue Response - FRTSacredly YoursNo ratings yet
- Digital TracingDocument3 pagesDigital TracingAryan AgarwalNo ratings yet
- C2 English Lesson On AiDocument6 pagesC2 English Lesson On Aimartha cullenNo ratings yet
- Foreign LiteratureDocument5 pagesForeign Literaturekris jericho buenabilesNo ratings yet
- Ethical Considerations To Guide The Use of Digital Proximity Tracking Technologies For COVID-19 Contact TracingDocument6 pagesEthical Considerations To Guide The Use of Digital Proximity Tracking Technologies For COVID-19 Contact TracingM NaszriNo ratings yet
- HW4 IamanviDocument2 pagesHW4 IamanviiamanviNo ratings yet
- Broadening The Conversation Around Facial RecognitionDocument18 pagesBroadening The Conversation Around Facial RecognitionThe Wilson CenterNo ratings yet
- A Framework For Personal Data Protection in The IoTDocument8 pagesA Framework For Personal Data Protection in The IoTSAIDCAMARGONo ratings yet
- Ambient Audio AuthenticationDocument25 pagesAmbient Audio AuthenticationTina SukhijaNo ratings yet
- Data Sharing in Mobile Apps - User Privacy Expectations in EuropeDocument13 pagesData Sharing in Mobile Apps - User Privacy Expectations in EuropeNguyễnTrần ThanhLâmNo ratings yet
- Internet of Things For Healthcare: Research Challenges and Future ProspectsDocument14 pagesInternet of Things For Healthcare: Research Challenges and Future Prospectspaps007No ratings yet
- GPEN Sweep 2024Document15 pagesGPEN Sweep 2024Darwin HerreraNo ratings yet
- A Mobile App Development Guideline For Hospital SeDocument15 pagesA Mobile App Development Guideline For Hospital SeMaxipincoNo ratings yet
- Liu, 2022Document19 pagesLiu, 2022Rizky HanzNo ratings yet
- IC 2020 05 0041.R2 - SaxenaDocument10 pagesIC 2020 05 0041.R2 - SaxenaSREEJA PNo ratings yet
- 1 s2.0 S0040162523007138 MainDocument13 pages1 s2.0 S0040162523007138 MainGrace FournierNo ratings yet
- Schoentgen WilkinsonDocument20 pagesSchoentgen Wilkinsonourtablet1418No ratings yet
- Digital Contact Tracing For COVID-19Document4 pagesDigital Contact Tracing For COVID-19Ikmal ShahromNo ratings yet
- PAPER - Analysis of Cybersecurity Standard and FrameworkDocument16 pagesPAPER - Analysis of Cybersecurity Standard and FrameworkFrancisco CastilloNo ratings yet
- Name: Malick Gai Mat#: 21716053 Course: Info Tech For Dev (Ict4D) Assignment 1Document5 pagesName: Malick Gai Mat#: 21716053 Course: Info Tech For Dev (Ict4D) Assignment 1Malick GaiNo ratings yet
- The Industry's First Diaphragm Integrity Monitor: Models NTA, TTA, FXTDocument2 pagesThe Industry's First Diaphragm Integrity Monitor: Models NTA, TTA, FXTCarlos A. MurilloNo ratings yet
- Clariants Catofin Technology Drives Worlds Largest Propane Dehydrogenation Unit enDocument2 pagesClariants Catofin Technology Drives Worlds Largest Propane Dehydrogenation Unit enstavros7No ratings yet
- Event Budget - Scout CampDocument6 pagesEvent Budget - Scout CampBobbyNichols0% (1)
- GPOADmin Quick Start Guide 58Document25 pagesGPOADmin Quick Start Guide 58Harikrishnan DhanapalNo ratings yet
- MPOWA Web3Foundation POC ProjectDocument13 pagesMPOWA Web3Foundation POC ProjectKonstantinos PappasNo ratings yet
- Microcode Update GuidanceDocument14 pagesMicrocode Update Guidanceproxymo1No ratings yet
- Paul Pignataro Leveraged BuyoutsDocument11 pagesPaul Pignataro Leveraged Buyoutspriyanshu14No ratings yet
- Virtual LabDocument21 pagesVirtual LabHusain AliNo ratings yet
- Maharshi Dayanand University, Rohtak: A Project Report On "E-Commerce"Document58 pagesMaharshi Dayanand University, Rohtak: A Project Report On "E-Commerce"Shivraj CyberNo ratings yet
- Professional Adjectives To Describe PersonalityDocument3 pagesProfessional Adjectives To Describe PersonalitymiteacherNo ratings yet
- GM 1927-16 - PcpaDocument12 pagesGM 1927-16 - PcpaNeumar NeumannNo ratings yet
- Module OutlineDocument27 pagesModule Outlinebw929518No ratings yet
- Notes in Fluid MachineryDocument36 pagesNotes in Fluid MachineryIvanNo ratings yet
- Computer Notes 1 Year Chapter # 1 Short Questions (According To Alp)Document4 pagesComputer Notes 1 Year Chapter # 1 Short Questions (According To Alp)Nb KashifNo ratings yet
- GTVET College: Information SheetDocument19 pagesGTVET College: Information SheetmengistuNo ratings yet
- Elango COUNCILSNOTABLESPOLITICS 1987Document24 pagesElango COUNCILSNOTABLESPOLITICS 1987Ota Benga BengaNo ratings yet
- YPDNDocument39 pagesYPDNSeyi WilliamsNo ratings yet
- 587 enDocument2 pages587 enabhayundaleNo ratings yet
- H-Bridges Motor Drivers - NXP SemiconductorsDocument60 pagesH-Bridges Motor Drivers - NXP SemiconductorsNadine HmaidanNo ratings yet
- Ramsbottom Carbon Residue of Petroleum Products: Standard Test Method ForDocument9 pagesRamsbottom Carbon Residue of Petroleum Products: Standard Test Method ForMuhannad NasifNo ratings yet
- WHO NetDocument50 pagesWHO Nettummalapalli venkateswara raoNo ratings yet
- Configuring Apache HTTP Server and Tomcat With Mod JKDocument3 pagesConfiguring Apache HTTP Server and Tomcat With Mod JKPravin UttarwarNo ratings yet
- Military Courtesy and DisciplineDocument33 pagesMilitary Courtesy and DisciplineCherry EyreNo ratings yet
- Article 1545 1560 ExplanationsDocument6 pagesArticle 1545 1560 ExplanationsWesNo ratings yet
- Block Armour Recommended by Ministry of Information Technology, Govt. of India and DSCIDocument12 pagesBlock Armour Recommended by Ministry of Information Technology, Govt. of India and DSCIBlock ArmourNo ratings yet
- Nitration of Methyl BenzoateDocument7 pagesNitration of Methyl BenzoateJanel Pauline G. Chua100% (1)
- Walk-in-Interview at S.V.Ayurvedic College, TTD, TirupatiDocument3 pagesWalk-in-Interview at S.V.Ayurvedic College, TTD, TirupatiKirankumar MutnaliNo ratings yet
- Processes and Types of Rolling MillsDocument7 pagesProcesses and Types of Rolling Millsdroy21No ratings yet
- Hospitality Management and Public Relations Solved MCQs (Set-1)Document5 pagesHospitality Management and Public Relations Solved MCQs (Set-1)Gilbert C NgomaNo ratings yet
tracing (2) 3
tracing (2) 3
Uploaded by
ayuzsharma9929Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
tracing (2) 3
tracing (2) 3
Uploaded by
ayuzsharma9929Copyright:
Available Formats
1
Introduction
In several countries, contact tracing apps have been introduced as a way to prevent the
spread of COVID-19. These apps work by identifying the people who have tested positive
from the COVID-19, prompting the people to share the information, locating the individuals
who have been in close contact with them and then notifying the people. In this report the
brief about the ethical issue related to uses of contact tracing apps is discussed. Also, some of
the case studies relevant to clauses of ACS Code of Professional conduct are provided which
are summarizes the values related to professional work by the members. The report discusses
the virtue ethics as well to resolve the ethical problems in ICT.
Ethical Issues regarding contact tracing Apps
Monitoring of the people by the contact tracing apps compromises with the privacy of
the people because the personal data of the people can fall into the wrong hands and can used
for maleficent activities. These apps use GPS or Bluetooth to detect the proximity of an
individual with another. Bluetooth Low Energy (BLE) enables the mobile of a person to
broadcasts the information with unique ID. Different apps works in different ways but all of
them follow the same basic steps (Ahmed, et al., 2020).
However, this process sounds so feasible and doable but the case is not that simple as
it looks because being monitored by these apps for 24 hours raises the question of privacy of
people and potential abuse. These apps stores log of the ongoing locations and timestamps of
a person with the help of GPS in the devices, hence compromising with the privacy of
peopleby revealing their whereabouts and travels over a period of time. A balance should be
maintained between privacy and security because poor implementation of standards of
2
security can put the private data of the people at risk. Some of apps which uses GPS are
SafePaths ,Hamgen and AarogyaSetu app (Trang, Trenz, Weiger, Tarafdar, & Cheung, 2020).
There are two different type of approaches used by these apps. In centralized
approach, public health authorities are able to analyse the information of the people by
checking the log of their devices which is uploaded to a central server. However, through this
process the privacy of the people is invaded because their location and the information of the
other people with whom they have met is stored in the servers. NHS COVID-19,
TraceTogether and COVIDSafe are some of the apps which uses this centralized approach.
In decentralized approach, minimum amount of information of a person is uploaded on the
servers and the log remains on the mobile device. Users who have tested positive, their IDs
are downloaded anonymously by the apps and the same information is matched with the logs
stored on their devices. PrivateTracer is one of the apps which uses decentralized approach
(Rowe, 2020).
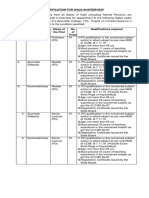
There are four types of challenges that people face related to the privacy and security
of these apps:
1. If the process which uses the Bluetooth Low Energy by the apps in
broadcasting the data packets in order to identify other devices is not set
properly, the device of a person can get hacked by interlinking various devices
and their respective identification packets (Chan & Saqib, 2021).
2. Sensitive information like contacts logs and encryptions keys which are stored
by contact tracing apps should be kept encrypted and stored in an application
called sandbox rather connecting them with shared locations. Still with the
sandbox approach, a hacker can hack the device if the hacker gets physical
access (Bengio, et al., 2021).
3
3. Devicesofpeople can be targeted with the attacks like “man-in-the-middle” at
the intercept of the trafficif the communication with the backend of the server
of an application is not encrypted properly (Yasaka, Lehrich, & Sahyouni,
2020).
4. When the information, such as diagnoses of the user and contacts logs, is
submitted to the servers, authentication must be performedbecause if the
proper authorization is not done, servers can receive fake health reports which
undermines the reliability of the system (Wen, Zhao, Lin, Xuan, & Shroff,
2020).
Tracing apps should be downloaded from the official stores only, as there are many
fake apps has been reported during the pandemic because these fake apps are made by the
mischievous people which can gain access to the devices of the people and apps related to
security solution should also be installed by the users to scan the applications and protect the
device from the malware.
Codes Guide in Ethical Choices
To abide by codes of ethics is an essential characteristic of professionfor the
members. These codes are established as the Code of Professional Conduct and is the part of
the regulations of the society which are applicable to every member of ACS working in the
field of information and communications technology. The ACS code of ethics agree with the
argument that “Codes guide the members of a profession in ethical choices” because these
codes are relevant to standards of professional legislation and if the codes are not abided then
the failure can be used as grounds for a claim of professional negligence.
4
For example, An ACS member, Katherina has provided an extensive and voluntary
aid to many infirmities supports groups. These groups use ICT to benefit the clients and
provide an efficient working of the organisation. The clauses related to professional conduct
in this ASC code includes a) Public Interest: To consider other professions and social systems
and organizations to be traversed by the profession of a member. b) Quality of Life: To
recognize the role of ICT in people’s life particularly for disadvantaged. c) Professional
Development: To increase the awareness regarding issues which affects profession and the
professional public relationship. d) Professionalism: To extend the knowledge and
understanding of public towards ICT.
Another example is that the ASC Disciplinary Committee decided to do the meeting
on Camera and avoid making results of the determinations to their complainants or general
membership to protect the reputation and status of the members. In this aspect the ASC
conduct clauses related to professionalism to take appropriate actions against the breaking of
the codes and to promote trustworthiness and professionalism in ICT.
Conclusion
To conclude the report, the contact tracing apps may have playing a significant role in
the technological sectors or aspects but the risks related to these apps cannot be avoided and
keeping in mind the security and privacy concerns strict rules should be taken into
consideration. The ASC Code guides the public effectively regarding their ethical choices
and to improve quality of life of individuals. In this attribute, the Virtue ethics also play a
essential part to resolve the ICT ethical issues as these traits can be acquired by one’s own
choice and are necessary to maintain ethnicity in the ICT area.
5
You might also like
- Privacy Calculus Theory and Its Applicability-2016Document5 pagesPrivacy Calculus Theory and Its Applicability-2016Muzammil QamarNo ratings yet
- Protools Keyboard ShortcutsDocument27 pagesProtools Keyboard Shortcutsprettycool2No ratings yet
- tracing (2) 4Document9 pagestracing (2) 4ayuzsharma9929No ratings yet
- tracing (2) (1)Document4 pagestracing (2) (1)ayuzsharma9929No ratings yet
- tracing (2)Document4 pagestracing (2)ayuzsharma9929No ratings yet
- A Survey of COVID-19 Contact Tracing AppsDocument23 pagesA Survey of COVID-19 Contact Tracing Appsnawwad65No ratings yet
- A First Look at Privacy Analysis of COVID-19 Contact-Tracing Mobile ApplicationsDocument11 pagesA First Look at Privacy Analysis of COVID-19 Contact-Tracing Mobile ApplicationsNguyễnTrần ThanhLâmNo ratings yet
- Case-Initiated COVID-19Document4 pagesCase-Initiated COVID-19Ikmal ShahromNo ratings yet
- F++1-s2.0-S2214212620308048-mainDocument11 pagesF++1-s2.0-S2214212620308048-mainsandro.nieto.mNo ratings yet
- 3P Framework PDFDocument13 pages3P Framework PDFsujiteduNo ratings yet
- Balancing Privacy at The Time of Pandemic: Global ObservationDocument11 pagesBalancing Privacy at The Time of Pandemic: Global ObservationIJPHSNo ratings yet
- Chapter 2 SampleDocument7 pagesChapter 2 SampleAlexxa Gabrielle JaneoNo ratings yet
- LL.M5230 Introduction To Law - Student Id-36365534Document5 pagesLL.M5230 Introduction To Law - Student Id-36365534Lyn JeninsNo ratings yet
- Unit Article DiscussionsDocument8 pagesUnit Article Discussionsgitaumary045No ratings yet
- DIT1243 Tutorial 12Document4 pagesDIT1243 Tutorial 12Cathay WongNo ratings yet
- 1.0 Synopsis Network Security 14-11-2019Document9 pages1.0 Synopsis Network Security 14-11-2019Irfan Zafar AwanNo ratings yet
- Ethical Concerns in COVID-19 ApplicationsDocument12 pagesEthical Concerns in COVID-19 Applicationssadekinborno07No ratings yet
- EMILIO MORDINI - Biometrics Ethics Algorithms - 20th Int.l Summer School On Biometrics 2022Document33 pagesEMILIO MORDINI - Biometrics Ethics Algorithms - 20th Int.l Summer School On Biometrics 2022Emilio MordiniNo ratings yet
- MSC Project ProposalDocument4 pagesMSC Project ProposalUsman ChaudharyNo ratings yet
- IoT Unit-4 According To RGPVDocument10 pagesIoT Unit-4 According To RGPVMadhav PanditNo ratings yet
- Entropy-Based Face Recognition and Spoof Detection For Security ApplicationsDocument18 pagesEntropy-Based Face Recognition and Spoof Detection For Security ApplicationsIvan FadillahNo ratings yet
- 1 s2.0 S1084804520302794 MainDocument32 pages1 s2.0 S1084804520302794 MainLibrary DaiictNo ratings yet
- Privacy Security and Resilience in Mobile Healthcare ApplicationsDocument16 pagesPrivacy Security and Resilience in Mobile Healthcare ApplicationsMUH.ALFIKRI TRI ANGGORO PAMUNGKASNo ratings yet
- Chapter 1editedDocument8 pagesChapter 1editedDaniel PerrerasNo ratings yet
- Chapter SixDocument15 pagesChapter SixTade GaromaNo ratings yet
- Statement of Research: Background and Current WorkDocument3 pagesStatement of Research: Background and Current WorkReza BarkhordariNo ratings yet
- High Level Privacy and Security Design For NHS COVID-19 Contact Tracing AppDocument13 pagesHigh Level Privacy and Security Design For NHS COVID-19 Contact Tracing AppBrkNo ratings yet
- Pervasive and Mobile Computing: Claudio Bettini, Daniele RiboniDocument16 pagesPervasive and Mobile Computing: Claudio Bettini, Daniele Riboniliviu_xzibit5770No ratings yet
- Applications of Wireless Sensor Networks in HealthcareDocument34 pagesApplications of Wireless Sensor Networks in HealthcaresaisreeknsNo ratings yet
- ICT EditedDocument6 pagesICT Editedwangathioli 1No ratings yet
- Gerek Jordan Ethics Essay Final DraftDocument10 pagesGerek Jordan Ethics Essay Final Draftapi-756848761No ratings yet
- Designing ProjectDocument4 pagesDesigning Projectvinaydevrukhkar2629No ratings yet
- International Journal of Information Management: Kane J. Smith, Gurpreet Dhillon, Lemuria Carter TDocument15 pagesInternational Journal of Information Management: Kane J. Smith, Gurpreet Dhillon, Lemuria Carter TLuster LeesaNo ratings yet
- Ethicsessay v2Document10 pagesEthicsessay v2api-727268225No ratings yet
- Unit 4 - Internet of Things - WWW - Rgpvnotes.in PDFDocument12 pagesUnit 4 - Internet of Things - WWW - Rgpvnotes.in PDFVinutha MNo ratings yet
- Individual AssignmentDocument13 pagesIndividual AssignmentLife of LokiniNo ratings yet
- Wireless Applications and PrivacyDocument5 pagesWireless Applications and PrivacyYoussef ZinounNo ratings yet
- Chapter 6 Ethics NewDocument24 pagesChapter 6 Ethics NewAshenafi PaulosNo ratings yet
- Cyber Security EthicsDocument8 pagesCyber Security Ethicsngolodedan2No ratings yet
- Effective Risk Detection and Summary Risk Communication For Android AppsDocument9 pagesEffective Risk Detection and Summary Risk Communication For Android AppsInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- The Dialogue Response - FRTDocument8 pagesThe Dialogue Response - FRTSacredly YoursNo ratings yet
- Digital TracingDocument3 pagesDigital TracingAryan AgarwalNo ratings yet
- C2 English Lesson On AiDocument6 pagesC2 English Lesson On Aimartha cullenNo ratings yet
- Foreign LiteratureDocument5 pagesForeign Literaturekris jericho buenabilesNo ratings yet
- Ethical Considerations To Guide The Use of Digital Proximity Tracking Technologies For COVID-19 Contact TracingDocument6 pagesEthical Considerations To Guide The Use of Digital Proximity Tracking Technologies For COVID-19 Contact TracingM NaszriNo ratings yet
- HW4 IamanviDocument2 pagesHW4 IamanviiamanviNo ratings yet
- Broadening The Conversation Around Facial RecognitionDocument18 pagesBroadening The Conversation Around Facial RecognitionThe Wilson CenterNo ratings yet
- A Framework For Personal Data Protection in The IoTDocument8 pagesA Framework For Personal Data Protection in The IoTSAIDCAMARGONo ratings yet
- Ambient Audio AuthenticationDocument25 pagesAmbient Audio AuthenticationTina SukhijaNo ratings yet
- Data Sharing in Mobile Apps - User Privacy Expectations in EuropeDocument13 pagesData Sharing in Mobile Apps - User Privacy Expectations in EuropeNguyễnTrần ThanhLâmNo ratings yet
- Internet of Things For Healthcare: Research Challenges and Future ProspectsDocument14 pagesInternet of Things For Healthcare: Research Challenges and Future Prospectspaps007No ratings yet
- GPEN Sweep 2024Document15 pagesGPEN Sweep 2024Darwin HerreraNo ratings yet
- A Mobile App Development Guideline For Hospital SeDocument15 pagesA Mobile App Development Guideline For Hospital SeMaxipincoNo ratings yet
- Liu, 2022Document19 pagesLiu, 2022Rizky HanzNo ratings yet
- IC 2020 05 0041.R2 - SaxenaDocument10 pagesIC 2020 05 0041.R2 - SaxenaSREEJA PNo ratings yet
- 1 s2.0 S0040162523007138 MainDocument13 pages1 s2.0 S0040162523007138 MainGrace FournierNo ratings yet
- Schoentgen WilkinsonDocument20 pagesSchoentgen Wilkinsonourtablet1418No ratings yet
- Digital Contact Tracing For COVID-19Document4 pagesDigital Contact Tracing For COVID-19Ikmal ShahromNo ratings yet
- PAPER - Analysis of Cybersecurity Standard and FrameworkDocument16 pagesPAPER - Analysis of Cybersecurity Standard and FrameworkFrancisco CastilloNo ratings yet
- Name: Malick Gai Mat#: 21716053 Course: Info Tech For Dev (Ict4D) Assignment 1Document5 pagesName: Malick Gai Mat#: 21716053 Course: Info Tech For Dev (Ict4D) Assignment 1Malick GaiNo ratings yet
- The Industry's First Diaphragm Integrity Monitor: Models NTA, TTA, FXTDocument2 pagesThe Industry's First Diaphragm Integrity Monitor: Models NTA, TTA, FXTCarlos A. MurilloNo ratings yet
- Clariants Catofin Technology Drives Worlds Largest Propane Dehydrogenation Unit enDocument2 pagesClariants Catofin Technology Drives Worlds Largest Propane Dehydrogenation Unit enstavros7No ratings yet
- Event Budget - Scout CampDocument6 pagesEvent Budget - Scout CampBobbyNichols0% (1)
- GPOADmin Quick Start Guide 58Document25 pagesGPOADmin Quick Start Guide 58Harikrishnan DhanapalNo ratings yet
- MPOWA Web3Foundation POC ProjectDocument13 pagesMPOWA Web3Foundation POC ProjectKonstantinos PappasNo ratings yet
- Microcode Update GuidanceDocument14 pagesMicrocode Update Guidanceproxymo1No ratings yet
- Paul Pignataro Leveraged BuyoutsDocument11 pagesPaul Pignataro Leveraged Buyoutspriyanshu14No ratings yet
- Virtual LabDocument21 pagesVirtual LabHusain AliNo ratings yet
- Maharshi Dayanand University, Rohtak: A Project Report On "E-Commerce"Document58 pagesMaharshi Dayanand University, Rohtak: A Project Report On "E-Commerce"Shivraj CyberNo ratings yet
- Professional Adjectives To Describe PersonalityDocument3 pagesProfessional Adjectives To Describe PersonalitymiteacherNo ratings yet
- GM 1927-16 - PcpaDocument12 pagesGM 1927-16 - PcpaNeumar NeumannNo ratings yet
- Module OutlineDocument27 pagesModule Outlinebw929518No ratings yet
- Notes in Fluid MachineryDocument36 pagesNotes in Fluid MachineryIvanNo ratings yet
- Computer Notes 1 Year Chapter # 1 Short Questions (According To Alp)Document4 pagesComputer Notes 1 Year Chapter # 1 Short Questions (According To Alp)Nb KashifNo ratings yet
- GTVET College: Information SheetDocument19 pagesGTVET College: Information SheetmengistuNo ratings yet
- Elango COUNCILSNOTABLESPOLITICS 1987Document24 pagesElango COUNCILSNOTABLESPOLITICS 1987Ota Benga BengaNo ratings yet
- YPDNDocument39 pagesYPDNSeyi WilliamsNo ratings yet
- 587 enDocument2 pages587 enabhayundaleNo ratings yet
- H-Bridges Motor Drivers - NXP SemiconductorsDocument60 pagesH-Bridges Motor Drivers - NXP SemiconductorsNadine HmaidanNo ratings yet
- Ramsbottom Carbon Residue of Petroleum Products: Standard Test Method ForDocument9 pagesRamsbottom Carbon Residue of Petroleum Products: Standard Test Method ForMuhannad NasifNo ratings yet
- WHO NetDocument50 pagesWHO Nettummalapalli venkateswara raoNo ratings yet
- Configuring Apache HTTP Server and Tomcat With Mod JKDocument3 pagesConfiguring Apache HTTP Server and Tomcat With Mod JKPravin UttarwarNo ratings yet
- Military Courtesy and DisciplineDocument33 pagesMilitary Courtesy and DisciplineCherry EyreNo ratings yet
- Article 1545 1560 ExplanationsDocument6 pagesArticle 1545 1560 ExplanationsWesNo ratings yet
- Block Armour Recommended by Ministry of Information Technology, Govt. of India and DSCIDocument12 pagesBlock Armour Recommended by Ministry of Information Technology, Govt. of India and DSCIBlock ArmourNo ratings yet
- Nitration of Methyl BenzoateDocument7 pagesNitration of Methyl BenzoateJanel Pauline G. Chua100% (1)
- Walk-in-Interview at S.V.Ayurvedic College, TTD, TirupatiDocument3 pagesWalk-in-Interview at S.V.Ayurvedic College, TTD, TirupatiKirankumar MutnaliNo ratings yet
- Processes and Types of Rolling MillsDocument7 pagesProcesses and Types of Rolling Millsdroy21No ratings yet
- Hospitality Management and Public Relations Solved MCQs (Set-1)Document5 pagesHospitality Management and Public Relations Solved MCQs (Set-1)Gilbert C NgomaNo ratings yet