Professional Documents
Culture Documents
0. MECH1043_CI Cloud Computing Security. SEM2 2023-2024
0. MECH1043_CI Cloud Computing Security. SEM2 2023-2024
Uploaded by
hanhan.hoho97Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
0. MECH1043_CI Cloud Computing Security. SEM2 2023-2024
0. MECH1043_CI Cloud Computing Security. SEM2 2023-2024
Uploaded by
hanhan.hoho97Copyright:
Available Formats
COURSE INFORMATION
Department/ Computer Science/ Page: 1 of 4
Faculty: Faculty of Engineering
Program Name: Master of Cyber Security
Course code: MECR1043/SECR5043 Academic Session/Semester: 20232024/2
Course name: Cloud Computing Security
Pre/co requisite: Computer Security
Credit hours: 3
Course synopsis In this course, we are going to learn about common cloud misconfigurations, how to perform a
risk assessment and verify compliance for various Cloud Services. Further, we will delve deeper
into identifying security risks in these cloud services and to implement best practices to mitigate
the common cloud misconfigurations. Other topics include topics of data ownership, privacy
protections, data mobility, quality of service and service levels, bandwidth costs, data
protection, and support.
Course coordinator
(if applicable) Dr Mohd. Zamri Bin Osman
Telephone E-mail
Course lecturer(s)/ Name Office
(07) 55- @utm.my
346-19 Level 3 mohdzamri.osman
Dr. Mohd. Zamri Bin Osman 019-9126239
N28 @utm.my
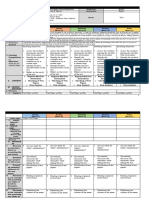
Mapping of the Course Learning Outcomes (CLO) to the Programme Learning Outcomes (PLO), Teaching & Learning
(T&L) methods and Assessment methods:
PLO Taxonomies
Weight Assessment
No. CLO (Code) and T&L methods
(%) methods
generic skills
Analyse fundamental cyber
security issues, requirements Lecture,
PLO1
CLO1 and concepts in Cloud 30 C4 Blended T, IP
(KW)
Computing platform and learning
services.
Evaluate different methods and Project Based
PLO2
CLO2 techniques that address security 45 C5 learning, FE, GP
(CG)
risks in the cloud services. Lecture
Display best practices on
PLO3 Formative
CLO3 handling common cloud security 15 P5 CAD
(PS) Assessment
misconfigurations/issues.
Defend orally the proposed
PLO5
design/framework on providing A4, Project Based
CLO4 (CS) 10 PR
trusted and effective security CS5 learning
and privacy on Cloud.
IP – Individual Project; CAD – Case Analysis and Discussion; GP – Group Project; PR – Presentation; T- Test; FE – Final
Exam
Details on Innovative T&L practices:
No. Type Implementation
1. Blended learning Conducted through in-class activities
2. Assignment/ Project- Conducted through a set of reading assignments. Tasks are given in sequential
based learning steps throughout the semester. Students in a group of 3 (max.) are require to
gather information and discuss the findings with relation to the Cloud Security
introduced in the course.
3. Formative Assessments Conducted through labs practical
Prepared by: Certified by:
Name: Dr Mohd. Zamri Bin Osman Name:
Signature: Signature:
Date: 4 March 2024 Date:
COURSE INFORMATION
Department/ Computer Science Page: 2 of 4
Faculty: Faculty of Engineering
Program Name: Master of Cyber Security
Course code: MECR1043/SECR5043 Academic Session/Semester: 20232024/2
Course name: Cloud Computing Security
Pre/co requisite: Computer Security
Credit hours: 3
Weekly Schedule:
Week 1 Chapter 1 Cloud Computing Fundamentals
Week 2 Chapter 2 Cloud Computing Architecture
Week 3-4 Chapter 3 Cloud Computing Software Security Fundamentals
Week 5-6 Chapter 4 Cloud Computing Risk Issues
Week 7 BREAK
Week 8 Chapter 5 Cloud Computing Security Challenges
Week 9 Chapter 6 Cloud Computing Security Architecture
Week 10-11 Chapter 7 Cloud Computing Life Cycle Issues
Week 12-13 Case Study
Week 14-15 Cloud Security Project & Presentation
Transferable skills (generic skills learned in course of study which can be useful and utilised in other settings):
Student’s scholarship generic skill can be applicable in courses that required the experience of conducting literature
review.
Student learning time (SLT) details:
Teaching and Learning Activities
Distribution of
Guided Learning
course content Independent
(Face to Face) Guided Learning TOTAL SLT
Learning
CLO L T P O Non-Face to Face
Non-Face to face
CLO 1 16 10 15 41
CLO 2 16 10 10 36
CLO 3 10 10 9 29
CLO 4 9 10 19
Total SLT 32 10 39 44 115
Continuous Assessment PLO (Code) Percentage Total SLT
1 Individual Project PLO1 (KW) 10 As in CLO1
Prepared by: Certified by:
Name: Dr. Mohd Zamri Osman Name:
Signature: Signature:
Date: 4 March 2024 Date:
COURSE INFORMATION
Department/ Computer Science Page: 3 of 4
Faculty: Faculty of Engineering
Program Name: Master of Cyber Security
Course code: MECR1043/SECR5043 Academic Session/Semester: 20232024/2
Course name: Cloud Computing Security
Pre/co requisite: Computer Security
Credit hours: 3
(6h)
2 Test PLO1 (KW) 20 2h
As in CLO3
3 Labs PLO3 (PS) 15
(6h)
As in CLO2
4 Group Project PLO2 (CG) 15
(3h)
As in CLO4
5 Presentation PLO5 (CS) 10
(3h)
Final Assessment PLO (Code) Percentage Total SLT
6 Final Exam PLO2 (CG) 30 3h
Total SLT 100 120h
Special requirement to deliver the course (e.g: software, nursery, computer lab, simulation room):
Microsoft Azure/ AWS Cloud Computing platform.
Learning resources:
Text book (if applicable)
Main: Ronald L. Krutz, Russell Dean Vines (2010 ). Cloud Security: A Comprehensive Guide to Secure Cloud Computing.
Wiley.
Chandrasekaran, K., (2015). Essentials of Cloud Computing. CRC Press.
Vacca, J.R. ed., (2017). Cloud computing security: Foundations and Challenges. CRC press.
Additional references
Online
http://elearning.utm.my
https://www.iisecurity.in/courses/cloud-computing-security-course.php
Academic honesty and plagiarism:
Assignments are individual tasks and NOT group activities (UNLESS EXPLICITLY INDICATED AS GROUP ACTIVITIES).
Copying of work (texts, lab results etc.) from other students/groups or from other sources is not allowed. Brief
quotations are allowed and then only if indicated as such. Existing texts should be reformulated with your own
words used to explain what you have read. It is not acceptable to retype existing texts and just acknowledge the
source as a reference. Be warned: students who submit copied work will obtain a mark of zero for the assignment
and exams and disciplinary steps may be taken by the Faculty. It is also unacceptable to do somebody else’s
work, to lend your work to them or to make your work available to them to copy.
Other additional information (Course policy, any specific instruction etc.):
1. Attendance is compulsory and will be taken in every lecture session. Student with less than 80% of total attendance
is not allowed to sit for final exam.
2. Students are required to behave and follow the University’s dressing regulation and etiquette all the time.
3. Exercises and tutorial will be given in class and some may be taken for assessment. Students who do not do the
Prepared by: Certified by:
Name: Dr. Mohd Zamri Osman Name:
Signature: Signature:
Date: 4 March 2024 Date:
COURSE INFORMATION
Department/ Computer Science Page: 4 of 4
Faculty: Faculty of Engineering
Program Name: Master of Cyber Security
Course code: MECR1043/SECR5043 Academic Session/Semester: 20232024/2
Course name: Cloud Computing Security
Pre/co requisite: Computer Security
Credit hours: 3
exercise will lose the coursework marks for the exercise.
4. Assignments must be submitted on the due dates. Some points will be deducted for late submissions. Assignments
submitted three days after the due date will not be accepted.
5. Make up exam will not be given, except to students who are sick and submit medical certificate confirmed by UTM
panel doctors. Make up exam can only be given within one week of the initial date of exam.
Disclaimer:
No one is allowed to use texts or excerpts from lectures or other teaching and learning activities at Universiti Teknologi
Malaysia except for the purpose of his/her studies. In particular, making copies of the texts or excerpts in any form at
all for the purpose of publication or distribution is strictly forbidden.
While every effort has been made to ensure the accuracy of the information supplied herein, Universiti Teknologi
Malaysia cannot be held responsible for any errors or omissions.
Prepared by: Certified by:
Name: Dr. Mohd Zamri Osman Name:
Signature: Signature:
Date: 4 March 2024 Date:
You might also like
- Higher Nationals in Computing: Unit 16: Cloud Computing Assignment 2Document18 pagesHigher Nationals in Computing: Unit 16: Cloud Computing Assignment 2Nguyen Manh TaiNo ratings yet
- THANGLNGCS18608 Unit 16. Assignment 02Document45 pagesTHANGLNGCS18608 Unit 16. Assignment 02Nguyen Manh TaiNo ratings yet
- (CE-408) CIS-Theory+Lab Course-Fall-2022Document8 pages(CE-408) CIS-Theory+Lab Course-Fall-2022nawal 109No ratings yet
- Course Module & Course Outline - Computer NetworksDocument7 pagesCourse Module & Course Outline - Computer NetworksSAMEER AHMADNo ratings yet
- DSF-112023 Module Introduction v2Document18 pagesDSF-112023 Module Introduction v2Yik WeiiNo ratings yet
- Course Outline - Computer Networks v2.1Document7 pagesCourse Outline - Computer Networks v2.1Ikram SyedNo ratings yet
- ITS205 - Cloud Technology ArchitectureDocument5 pagesITS205 - Cloud Technology ArchitectureRedan JonnaNo ratings yet
- Unit 16. Assignment 02 - BriefDocument39 pagesUnit 16. Assignment 02 - BriefNguyen Manh TaiNo ratings yet
- CIS (Cloud Computing) BESEDocument3 pagesCIS (Cloud Computing) BESEhassamNo ratings yet
- Cloud Technology Associate: Certificate: Duration: Course Delivery: Accreditor: Course Id: Language: Pmi PdusDocument3 pagesCloud Technology Associate: Certificate: Duration: Course Delivery: Accreditor: Course Id: Language: Pmi PdusDayiriNo ratings yet
- CesyllDocument70 pagesCesyllaspatilsukNo ratings yet
- The Superior College, Lahore: Faculty of Computer Science & Information TechnologyDocument8 pagesThe Superior College, Lahore: Faculty of Computer Science & Information TechnologyRana TayyabaNo ratings yet
- 1ET1080606 - Cloud and Fog ComputingDocument3 pages1ET1080606 - Cloud and Fog ComputingjasoniictspceNo ratings yet
- Cyber securityDocument6 pagesCyber securityAshutosh SinghNo ratings yet
- Course Outline: CE112 - Computer Programming: Air UniversityDocument10 pagesCourse Outline: CE112 - Computer Programming: Air UniversityMuhammad HasnainNo ratings yet
- Obls 6it2Document11 pagesObls 6it2eigertechnoNo ratings yet
- Sample Format: Academic Year 2018-19 - Semester B.EDocument3 pagesSample Format: Academic Year 2018-19 - Semester B.EShobha KumarNo ratings yet
- Course InformationDocument5 pagesCourse InformationBAHARUDIN BURAHNo ratings yet
- COS6077B Cloud ComputingDocument53 pagesCOS6077B Cloud ComputingmahendrasuryavanshiNo ratings yet
- Unit 16.assignment 2 Frontsheet (2018-2019)Document17 pagesUnit 16.assignment 2 Frontsheet (2018-2019)RAY LEENo ratings yet
- Syllabus Computer SecurityDocument9 pagesSyllabus Computer Security체인지No ratings yet
- CIS Fall 2022-TCP IPDocument5 pagesCIS Fall 2022-TCP IPMahnoor SiddiquiNo ratings yet
- Unit 16 Assignment 2 FullDocument29 pagesUnit 16 Assignment 2 FullNguyễn Hồng DânNo ratings yet
- Cloud ComputingDocument233 pagesCloud ComputingFahad Ahmad100% (1)
- CNS Lab Course FileDocument14 pagesCNS Lab Course Fileswetha sastryNo ratings yet
- 05 Ad8602 Dis Unit 5Document70 pages05 Ad8602 Dis Unit 5BRINDHANo ratings yet
- CSCS442 - Cyber Security AlgorithmsDocument7 pagesCSCS442 - Cyber Security AlgorithmsAishwarya RajeshNo ratings yet
- 04 Ad8602 Dis Unit 4Document95 pages04 Ad8602 Dis Unit 4BRINDHANo ratings yet
- BSC DFS (2022-23)Document101 pagesBSC DFS (2022-23)Anita Sofia KeyserNo ratings yet
- Alliance College of Engineering and DesignDocument8 pagesAlliance College of Engineering and Designpunam kumariNo ratings yet
- CS 111 Syllabus NewDocument5 pagesCS 111 Syllabus Newqasem alqasemNo ratings yet
- Assignment 2 Front Sheet: Qualification BTEC Level 5 HND Diploma in ComputingDocument40 pagesAssignment 2 Front Sheet: Qualification BTEC Level 5 HND Diploma in ComputingDũng Hoàng TiếnNo ratings yet
- Course Policy - CC 202122Document11 pagesCourse Policy - CC 202122Pratiksha PatilNo ratings yet
- css full manualDocument53 pagescss full manualpathaklisa780No ratings yet
- COMP532 IT Infrastructure ICPC 20212Document14 pagesCOMP532 IT Infrastructure ICPC 20212hamzaNo ratings yet
- New SyllabusDocument3 pagesNew SyllabusÅřījīt ÑāñdïNo ratings yet
- Course Outcomes (Cos) : Program Name: Computer Engineering Program Group Semester: SixthDocument1 pageCourse Outcomes (Cos) : Program Name: Computer Engineering Program Group Semester: SixthashaNo ratings yet
- A Proposed Curriculum of Cryptography Courses: September 2005Document9 pagesA Proposed Curriculum of Cryptography Courses: September 2005Ahmad El TahanNo ratings yet
- BSC Comp Sci Cyb Sec 2023 24Document84 pagesBSC Comp Sci Cyb Sec 2023 24manasabezawada04No ratings yet
- Slide Pembentangan HLP QursiahDocument15 pagesSlide Pembentangan HLP QursiahNorqursiah SaadNo ratings yet
- Unit 16.assignment Brief 2 (2018 - 2019)Document3 pagesUnit 16.assignment Brief 2 (2018 - 2019)LePhanTuanAnhNo ratings yet
- Network Security Protocols - S8 CSE-2019 Scheme-SyllabusDocument9 pagesNetwork Security Protocols - S8 CSE-2019 Scheme-SyllabusASHNA ANo ratings yet
- 7-Cloud_Computing_MCAE1131-Anurag GuptaDocument8 pages7-Cloud_Computing_MCAE1131-Anurag GuptaDr. Neetu SharmaNo ratings yet
- Assignment 2 Front Sheet: Qualification BTEC Level 5 HND Diploma in Computing Unit Number and Title Submission DateDocument18 pagesAssignment 2 Front Sheet: Qualification BTEC Level 5 HND Diploma in Computing Unit Number and Title Submission DateNguyen Manh TaiNo ratings yet
- B.Sc. III Sem22-23Document34 pagesB.Sc. III Sem22-23radhakrishn0729No ratings yet
- Seminar and Technical Communication Presentation OnDocument15 pagesSeminar and Technical Communication Presentation OnGhost StatusNo ratings yet
- Cloud HandoutDocument3 pagesCloud HandoutJohn EdNo ratings yet
- KTU S7 Elective: CST433 Security in ComputingDocument8 pagesKTU S7 Elective: CST433 Security in ComputingJishnu ManikkothNo ratings yet
- CT037 3.5 2 Network SecurityDocument6 pagesCT037 3.5 2 Network SecurityYogeswaran NathanNo ratings yet
- CIS6006-Cyber Security WRIT1Document14 pagesCIS6006-Cyber Security WRIT1Shehan LasinduNo ratings yet
- CIS - (Data Structures and Algorithms) SPRING-20241Document9 pagesCIS - (Data Structures and Algorithms) SPRING-20241Umer FarooqNo ratings yet
- Department of Computer Science and EngineeringDocument22 pagesDepartment of Computer Science and EngineeringNishitha PriyankaNo ratings yet
- BCIT14 Course Specification of Cloud Computing2Document6 pagesBCIT14 Course Specification of Cloud Computing2safwansadaan7No ratings yet
- Course Outline - Network Security-BESE-3AB-Fall15 - 2 PDFDocument5 pagesCourse Outline - Network Security-BESE-3AB-Fall15 - 2 PDFPriya SatyaniNo ratings yet
- Folder-Cyber-Security-and-Resilience Copy 2Document6 pagesFolder-Cyber-Security-and-Resilience Copy 2chastisetartness927No ratings yet
- School of Science and Technology: Referral Coursework Assessment Specification (PG)Document11 pagesSchool of Science and Technology: Referral Coursework Assessment Specification (PG)Vishal PadharNo ratings yet
- File 1704210712 0006745 IntroductoryCNDocument18 pagesFile 1704210712 0006745 IntroductoryCNcutiemegha512No ratings yet
- MODULE SPECIFICATION FORM. Module Title Network Management Level 6 Credit Value 20. COM635 Cost Centre GACP JACS3 Code G420Document5 pagesMODULE SPECIFICATION FORM. Module Title Network Management Level 6 Credit Value 20. COM635 Cost Centre GACP JACS3 Code G420ronicaNo ratings yet
- CCSP Certified Cloud Security Professional A Step by Step Study Guide to Ace the ExamFrom EverandCCSP Certified Cloud Security Professional A Step by Step Study Guide to Ace the ExamNo ratings yet
- CompTIA Cloud+ (Plus) Certification Practice Questions, Answers and Master the ExamFrom EverandCompTIA Cloud+ (Plus) Certification Practice Questions, Answers and Master the ExamNo ratings yet
- Pearson Edexel Igcse Science GuideDocument17 pagesPearson Edexel Igcse Science GuideteachmeraghavNo ratings yet
- CPHQ ResponseSummaryDocument21 pagesCPHQ ResponseSummaryAlex AlemanNo ratings yet
- Subject-Verb AgreementDocument4 pagesSubject-Verb AgreementKay BelgaNo ratings yet
- Jindal Global Business School: Course OutlineDocument10 pagesJindal Global Business School: Course Outlineshivani khareNo ratings yet
- Study GuideDocument11 pagesStudy GuideAli AyubNo ratings yet
- Aqa Geography Coursework Grade BoundariesDocument5 pagesAqa Geography Coursework Grade Boundariesafayeejka100% (2)
- REPORT CARD FORMAT For Class 9 & 10 2023Document5 pagesREPORT CARD FORMAT For Class 9 & 10 2023saifulla saikhNo ratings yet
- Latest - CHEGG QA GuidelinesDocument35 pagesLatest - CHEGG QA GuidelinesSambhav ThakurNo ratings yet
- S2 Placement TestDocument6 pagesS2 Placement TestThet HtarNo ratings yet
- Apics CourseworkDocument6 pagesApics Courseworkf5dpebax100% (2)
- SainikscDocument1 pageSainikscskc4xvbk64No ratings yet
- Insight: Mathematics StandardDocument596 pagesInsight: Mathematics StandardSasha van Onselen100% (1)
- TCP FINAL EXAM Assessment of LearningDocument19 pagesTCP FINAL EXAM Assessment of LearningGes MoletaNo ratings yet
- Unit 1 - Task 2 - Write Your Obligations and Needs in Your Daily Role-LiscethDocument6 pagesUnit 1 - Task 2 - Write Your Obligations and Needs in Your Daily Role-LiscethLisceth ArmeroNo ratings yet
- Aqa Health and Social Care Coursework Mark SchemeDocument5 pagesAqa Health and Social Care Coursework Mark Schemedut0s0hitan3100% (1)
- 12th Commerce EM Centum Questions 2022 Model Question Paper PadasalaiDocument8 pages12th Commerce EM Centum Questions 2022 Model Question Paper PadasalaiRahul RockNo ratings yet
- Life As A Darktrace CustomerDocument16 pagesLife As A Darktrace CustomerTenny Thomas KulathakalNo ratings yet
- Cambridge International AS & A Level: PHYSICS 9702/36Document8 pagesCambridge International AS & A Level: PHYSICS 9702/36Jean-Michel RatnaNo ratings yet
- English 7 First Quarter ExamDocument7 pagesEnglish 7 First Quarter ExamJAYCEE GONZALESNo ratings yet
- CSC 6 - CSE Complete Reviewer For 2017 WWW - Teachpinas.com - BookletDocument24 pagesCSC 6 - CSE Complete Reviewer For 2017 WWW - Teachpinas.com - BookletConeygrace BlasquezNo ratings yet
- Application 102279Document1 pageApplication 102279ranajoy biswasNo ratings yet
- 0743 B Asoiu Azerbaijan 2686 KBDocument36 pages0743 B Asoiu Azerbaijan 2686 KBelektrik.uangNo ratings yet
- CTET Admit CardDocument2 pagesCTET Admit CardVikas PalNo ratings yet
- Ib Aahl - Topic 4 p3 - RV QuestionbankDocument5 pagesIb Aahl - Topic 4 p3 - RV Questionbankan.wita.jkt15No ratings yet
- Reasoning Classification Questions PDF For SSC ExamsDocument13 pagesReasoning Classification Questions PDF For SSC Examsdebdipsen939No ratings yet
- OutSystems Training & Certification PlaybookDocument11 pagesOutSystems Training & Certification PlaybookFelipe lipilef2ndNo ratings yet
- DLL-Q3-W5 - Mam LouDocument4 pagesDLL-Q3-W5 - Mam LouChello Ann Pelaez AsuncionNo ratings yet
- IELTS Speaking Lesson 123Document46 pagesIELTS Speaking Lesson 123md shahidullahNo ratings yet
- How I Cheated On My Matura Exam With AI - MetawersumDocument2 pagesHow I Cheated On My Matura Exam With AI - MetawersumbasiaNo ratings yet
- Hoang Van Thu - Hoa BinhDocument23 pagesHoang Van Thu - Hoa Binhducduy.1242006No ratings yet