Professional Documents
Culture Documents
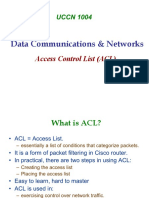
Access Control Lists (ACLs)
Access Control Lists (ACLs)
Uploaded by
Senan AlkaabyOriginal Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Access Control Lists (ACLs)
Access Control Lists (ACLs)
Uploaded by
Senan AlkaabyCopyright:
Available Formats
CCNA2 Routing
172.16.3.0
172.16.4.0
e0
e1
s0
Non-172.16.0.0
Perrine modified by Brierley
Module 11
Access Control
04/27/15
server
172.16.4.13
Page 1
CCNA2 Routing
172.16.2.0
Computer
Module 11
Access Control
172.16.4.0
e0
e1
172.16.2.2
172.16.3.1
s0
172.16.3.0
s1
172.16.3.2
Computer
172.16.4.3
Server
172.16.4.2
Perrine modified by Brierley
04/27/15
Page 2
CCNA2 Routing
High Level View
Module 11
A HIGH LEVEL VIEW of ACLs
Perrine modified by Brierley
04/27/15
Page 3
CCNA2 Routing
Module 11
Access Control Lists
Standard
Extended
Perrine modified by Brierley
04/27/15
Page 4
CCNA2 Routing
High Level View
Module 11
Standard:
Interface Fa 0/0/0
ip access-group 1 out
access-list 1 deny 172.16.4.13 0.0.0.0
access-list 1 permit any
________________________________________________________________
Extended:
Interface Fa 0/0/0
ip access-group 101 in
access-list 101 deny tcp 172.16.4.0 0.0.0.255 172.16.3.0 0.0.0.255 eq www
access-list 101 permit ip any any
Perrine modified by Brierley
04/27/15
Page 5
CCNA2 Routing
Standard Access Control Lists
Module 11
ACLs are instructions that are applied to a router interfaces.
The ACLs describe the kind of packets that are to be permitted or denied.
Permitted or Denial testing can be based on:
source address
destination address
port number
ACLs are configured on the router Interfaces to control access to a network.
ACLs must be defined separately for each protocol; Unique for IP, Unique for
IPX; Unique for AppleTalk, etc.
Some times ACLs are called packet filters.
Perrine modified by Brierley
04/27/15
Page 6
CCNA2 Routing
Perrine modified by Brierley
Standard Access Control Lists
04/27/15
Module 11
Page 7
CCNA2 Routing
Perrine modified by Brierley
Extended ACLs
04/27/15
Module 11
Page 8
CCNA2 Routing
Perrine modified by Brierley
Named ACLs
04/27/15
Module 11
Page 9
CCNA2 Routing
Placing ACLs
Module 11
Standard ACLs should be placed close to the destination.
Extended ACLs should be placed close to the source.
Perrine modified by Brierley
04/27/15
Page 10
CCNA2 Routing
Firewalls
Module 11
A firewall is an architectural structure that
exists between the user and the outside world
to protect the internal network from intruders.
Perrine modified by Brierley
04/27/15
Page 11
CCNA2 Routing
Perrine modified by Brierley
Restricting Virtual Terminal Access
04/27/15
Module 11
Page 12
CCNA2 Routing
Perrine modified by Brierley
Summary
04/27/15
Module 11
Page 13
CCNA2 Routing
ACL - Access Control Lists
Module 11
Reasons to create ACLs:
limit network traffic - hence increase network performance
provide traffic flow - limit traffic through the network
provide for security
ACLs establish
which traffic is blocked
which traffic is not blocked
Perrine modified by Brierley
04/27/15
Page 14
CCNA2 Routing
DETAIL
Module 11
A MORE DETAILED VIEW of ACLs
Perrine modified by Brierley
04/27/15
Page 15
CCNA2 Routing
ACL - Access Control Lists
Module 11
Cisco IOS checks each packet for:
1.
destination address
2.
source address
3.
protocol
4.
port number
access-list 1 deny 192.169.1.0 0.0.255.255
access-list 1 deny 192.168.1.9 0.0.0.0
access-list 1 deny 172.16.4.0 0.0.0.255
access-list 1 permit any
Each ACL statement is checked in a sequential order (first to last) and when
there is a match, no more statements are checked.
If the results are no matches, then the packet (by default) is discarded.
Adding addition ACL statements to the end of an existing list is just a matter of
adding the new statement. BUT, if
deleting an existing ACL statement causes the entire access list to be deleted.
Perrine modified by Brierley
04/27/15
Page 16
CCNA2 Routing
ACL - Access Control Lists
Module 11
When a packet enters a routers interface:
IN (inbound) checking is required. The packet:
1)
Is checked against the ACL list (if one exists)
2)
Here It can be interrogated to permit or deny.
3)
If denied the packet is dropped else,
4)
It is matched against the routing table and passed to an
OUT (outbound interface)
1)
OUT (outbound) checking is required.
Here It can be interrogated to permit or deny.
2) If denied the packet is dropped
3) If permitted then packet is allowed OUT (outbound).
The Outbound interfaces ACL is a different list from the inbound)
Perrine modified by Brierley
04/27/15
Page 17
CCNA2 Routing
ACL - Access Control Lists
Module 11
ACL statements operate in a logical, sequential order. When a match is made
the rest of the statements are not checked.
If none the ACL statements match, then there is an implicit deny any rule.
access-list 10 { permit | deny } { test conditions }
access-list 10 { permit | deny } { test conditions }
access-list 10 { permit | deny } { test conditions }
access-list 10 { permit | deny } { test conditions }
access-list 10 deny any
access-list 1 deny 192.169.1.0 0.0.255.255
access-list 1 deny 192.168.1.9 0.0.0.0
access-list 1 deny 172.16.4.0 0.0.0.255
access-list 1 permit any
Perrine modified by Brierley
04/27/15
Page 18
CCNA2 Routing
ACL - Access Control Lists
Module 11
Two types of IP ACL :
standard - has access list value of 1- 99
extended - has access list value of 100 - 199
Must be configured in global configuration mode. Router (config) #
Steps in creating ACLs:
1) create the ACL (in config mode)
2) apply the ACL to an interface
ACLs are used to filter:
inbound traffic, or
outbound traffic
Perrine modified by Brierley
04/27/15
Page 19
CCNA2 Routing
Where to place ACLs
Module 11
Standard ACLs are place as close as possible to the destination.
Extended ACLs are place as close as possible to the source.
Perrine modified by Brierley
04/27/15
Page 20
CCNA2 Routing
Where to place ACLs
Module 11
Configuring an Access List:
Router(config)# access-list <ACL number> { permit | deny } { test conditions }
Router(config)# access-list 1 permit { test conditions }
Router(config)# access-list 50 deny { test conditions }
To delete all ACL statements of an access-list
Router(config)# no access-list <ACL number>
Applying the Access List:
At an interface:
Router(config)# int E0
Router(config-if)# { protocol } access-group <ACL number> [IN | OUT]
Out is the default if not mentioned
Router(config-if)# ip access-group 1
Router(config-if)# ip access-group 50
To delete an ACL group statement (this will not delete the associated list):
Router(config)# no access-group <ACL number>
Perrine modified by Brierley
04/27/15
Page 21
CCNA2 Routing
Wildcard
Module 11
A wildcard is matched with an IP address or protocol address.
It is a 32 bit mask divided into 4 octet, each containing 8 bits.
A 0 in the wildcard means to check the bit in the IP you are testing.
A 1 in the wildcard means ignore the bit in the IP you are testing.
NOTE!!!
Do NOT think subnet mask that is a totally different
meaning not related to the WILDCARD
Perrine modified by Brierley
04/27/15
Page 22
CCNA2 Routing
Module 11
Abbreviations
To permit or deny any address:
0.0.0.0
255.255.255.255
Address
Wildcard
Use the abbreviation any
Router(config)# access-list 1 permit 0.0.0.0 255.255.255.255
Router(config)# access-list 1 permit any
Router(config)# access-list 1 deny 0.0.0.0 255.255.255.255
Router(config)# access-list 1 deny any
Perrine modified by Brierley
04/27/15
Page 23
CCNA2 Routing
Abbreviations
Module 11
To match all the bits of IP address use host:
EX: 172. 30.16. 29 0. 0. 0. 0
Router(config)# access-list 1 permit 172.30.16.29 0.0.0.0
Router(config)# access-list 1 permit host 172.30.16.29
Perrine modified by Brierley
04/27/15
Page 24
CCNA2 Routing
Standard ACLs
Module 11
Criteria:
block all traffic from a network
allow all traffic from a network
deny entire protocol suits
Standard ACLs only check the source address.
Router(config)# access-list <ACL number> { deny | permit } source [ source wildcard] [log]
Perrine modified by Brierley
04/27/15
Page 25
CCNA2 Routing
Standard ACLs
Module 11
What does this statement accomplish?
Access-list 33 permit 172.16.0.0 0.0.255.255 log
Permits all traffic from 172.16.0.0 and sends messages to the console every
time the access list is executed.
Perrine modified by Brierley
04/27/15
Page 26
CCNA2 Routing
Standard ACLs
Module 11
What does this statement accomplish?
Access-list 44 deny 172.16.13.7 0.0.0.0 log
Denies traffic from host 172.16.13.7 and sends message to the console every
time the access list is hit.
Perrine modified by Brierley
04/27/15
Page 27
CCNA2 Routing
Standard ACLs
Module 11
What does this statement accomplish?
Access-list 55 deny 172.16.64.3 0.0.0.255
Denies all traffic from network 172.16.64.0
Perrine modified by Brierley
04/27/15
Page 28
CCNA2 Routing
Standard ACLs
Module 11
The log command:
Prints messages to the console which includes the ACL number, whether
the packet was permitted or denied, the source address, and the number
of packets.
The message is generated for the first packet that matches, and then at
five-minute intervals, including the number of packets permitted or
denied in the prior five-minute interval.
Log is used for debugging only not to be left active on live networks.
Perrine modified by Brierley
04/27/15
Page 29
CCNA2 Routing
Standard ACLs
Module 11
Example of applying the access-list:
Router(config-if)# ip access-group 33 in
Router(config-if)# ip access-group 44 out
Perrine modified by Brierley
04/27/15
Page 30
CCNA2 Routing
Standard ACLs
Module 11
To monitor IP access list: (in EXEC mode)
show access-list
Displays all access lists & their parameters configured on the router.
(Does not show you which interface the list is set on.)
show access-list <ACL number>
Shows only the parameters for the access list <ACL number>. (Does not
show you the interface the list is set on.)
show ip access-list
Shows only the IP access lists configured on the router
show ip interface
Shows which interfaces have access lists set (containing an accessgroup).
show running-config
Shows the routers entire configuration
Perrine modified by Brierley
04/27/15
Page 31
CCNA2 Routing
Module 11
Standard ACLs
172.16.3.0
172.16.4.0
e0
e1
s0
Non-172.16.0.0
server
172.16.4.13
R(config)# Interface e0
R(config-if)# ip access-group 1 out
R(config)# Interface e1
R(config-if)# ip access-group 1 out
R(config)# access-list 1 permit 172.16.0.0 0.0.255.255
What does it do?
Perrine modified by Brierley
04/27/15
Page 32
CCNA2 Routing
Module 11
Standard ACLs
One Access list used by multiple Interfaces
172.16.3.0
172.16.4.0
e0
e1
s0
R(config)# Interface e0
Non-172.16.0.0
server
172.16.4.13
R(config-if)# ip access-group 1 out
R(config)# Interface e1
R(config-if)# ip access-group 1 out
R(config)# access-list 1 permit 172.16.0.0 0.0.255.255
Allows only traffic from source network 172.16.0.0 to be forwarded & and
172.16.0.0 traffic is blocked.
Perrine modified by Brierley
04/27/15
nonPage 33
CCNA2 Routing
Module 11
Standard ACLs
172.16.3.0
172.16.4.0
e0
e1
s0
Non-172.16.0.0
server
172.16.4.13
R(config)# Interface e0
R(config-if)# ip access-group 1 out
R(config)# access-list 1 deny 172.16.4.13 0.0.0.0
R(config)# access-list 1 permit any
What does this do?
Perrine modified by Brierley
04/27/15
Page 34
CCNA2 Routing
Module 11
Standard ACLs
172.16.3.0
172.16.4.0
e0
e1
s0
Non-172.16.0.0
server
172.16.4.13
R(config)# Interface e0
R(config-if)# ip access-group 1 out
R(config)# access-list 1 deny 172.16.4.13 0.0.0.0
R(config)# access-list 1 permit any
Denies traffic from a specific device, 172.16.4.13 & allows all other traffic thru e0 to
network 172.16.3.0.
Perrine modified by Brierley
04/27/15
Page 35
CCNA2 Routing
Module 11
Standard ACLs
172.16.3.0
172.16.4.0
e0
e1
s0
Non-172.16.0.0
server
172.16.4.13
Interface e0
ip access-group 1 out
access-list 1 deny 172.16.4.0 0.0.0.255
access-list 1 permit any
What does this do?
Perrine modified by Brierley
04/27/15
Page 36
CCNA2 Routing
Module 11
Standard ACLs
172.16.3.0
172.16.4.0
e0
e1
s0
Non-172.16.0.0
server
172.16.4.13
Interface e0
ip access-group 1 out
access-list 1 deny 172.16.4.0 0.0.0.255
access-list 1 permit any
Denies traffic from the subnet, 172.16.4.0 & allows all other traffic thru e0 to
network 172.16.3.0.
Perrine modified by Brierley
04/27/15
Page 37
CCNA2 Routing
Extended ACLs
Module 11
Criteria:
checks both the packets source & destination addresses
check for specific protocol
check for specific port numbers
permit or denied applications pings, telnets, FTP, etc.
ACL values range between 100 199 (for IP)
Perrine modified by Brierley
04/27/15
Page 38
CCNA2 Routing
Extended ACLs
Port Numbers (decimal)
Module 11
IP Protocol
20
FTP data [TCP]
21
FTP program (control) [TCP]
23
Telnet [TCP]
25
Simple Mail Transport Protocol
[TCP] (SMTP)
53
DNS [TCP, UDP]
69
TFTP [UDP]
80
HTTP [TCP]
Perrine modified by Brierley
04/27/15
Page 39
CCNA2 Routing
Module 11
Extended ACLs
Router(config)# access-list <ACL number> { permit | deny } protocol source source-mask
destination destination-mask operator operand {established}
ACL number
100 199
permit | deny
Packet is allowed or blocked
protocol
IP, TCP, UDP, ICMP, GRE or IGRP
source -- Source address source-wildcard mask
destination -- Destination address destination-wildcard mask
Continued
Perrine modified by Brierley
04/27/15
Page 40
CCNA2 Routing
Extended ACLs
Module 11
Router(config)# access-list <ACL number> { permit | deny } protocol source source-mask
destination destination-mask operator
operand {established}
operator
lt, gt, eq, neq
Operand
Port number
established
Allows TCP traffic to pass if the packet uses an established connection ( for example, has
ACK bits set ).
access-list 101 permit tcp 172.16.4.0 0.0.0.255 any eq 25
Perrine modified by Brierley
04/27/15
Page 41
CCNA2 Routing
Extended ACLs
Module 11
Configuring an extended ACL to an interface:
Router(config-if)# ip access-group <ACL number> { in | out }
Router(config)# int E0
Router(config-if)# ip access-group 101 in
Perrine modified by Brierley
04/27/15
Page 42
CCNA2 Routing
Module 11
Extended ACLs
172.16.3.0
172.16.4.0
e0
e1
s0
Non-172.16.0.0
server
172.16.4.13
Interface e0
ip access-group 101
access-list 101 deny tcp 172.16.4.0 0.0.0.255 172.16.3.0 0.0.0.255 eq 21
access-list 101 permit ip any any
What does this do?
Perrine modified by Brierley
04/27/15
Page 43
CCNA2 Routing
Module 11
Extended ACLs
172.16.3.0
172.16.4.0
e0
e1
s0
Non-172.16.0.0
server
172.16.4.13
Interface e0
ip access-group 101
access-list 101 deny tcp 172.16.4.0 0.0.0.255 172.16.3.0 0.0.0.255 eq 21
access-list 101 permit ip any any
Blocks FTP traffic from all hosts on 172.16.4.0 to any device on 172.16.3.0 & allows
all other traffic.
Perrine modified by Brierley
04/27/15
Page 44
CCNA2 Routing
Module 11
Extended ACLs
172.16.3.0
172.16.4.0
e0
e1
s0
Non-172.16.0.0
server
172.16.4.13
Interface e0
ip access-group 101
access-list 101 deny tcp 172.16.4.0 0.0.0.255 172.16.3.0 0.0.0.255 eq 23
access-list 101 permit ip any any
What does this do?
Perrine modified by Brierley
04/27/15
Page 45
CCNA2 Routing
Module 11
Extended ACLs
172.16.3.0
172.16.4.0
e0
e1
s0
Non-172.16.0.0
server
172.16.4.13
Interface e0
ip access-group 101
access-list 101 deny tcp 172.16.4.0 0.0.0.255 172.16.3.0 0.0.0.255 eq 23
access-list 101 permit ip any any
Denies only telnet traffic from 172.16.4.0 to 172.16.3.0 network, and permits all
other traffic thru e0 to any address.
Perrine modified by Brierley
04/27/15
Page 46
CCNA2 Routing
Extended/Standard ACL numbers for IP
Module 11
NOTE:
Standard ACL numbers: 1-99;
1300-1999
Extended ACL numbers: 100-199;
Perrine modified by Brierley
04/27/15
2000-2699
Page 47
CCNA2 Routing
Standard/Extended ACL
Module 11
You can not add ACL statements into the body of the access-list
(ONLY at the end of the list).
Otherwise the access list must be deleted first, and then rewritten.
Therefore it is prudent to write your access-list in text format using
notepad, and then transfer it to your router.
Perrine modified by Brierley
04/27/15
Page 48
CCNA2 Routing
Configuring Named ACLs
Module 11
NOTE:
A NAMED ACL is an alphanumeric string instead of the ACL
number (1 - 199 )
NAMED ACLs are not compatible with Cisco IOS release prior to
Release 11.2
Named ACLs can be used for either standard & extended
You cannot configure the same name for multiple ACLs.
use Name ACL when you want to intuitively identify ACLs
use Name ACL when you have more than 99 standard & 100
extended ACLs have been configured on a router for a given protocol
Perrine modified by Brierley
04/27/15
Page 49
CCNA2 Routing
Configuring Named ACLs
Module 11
Router(config)# ip access-list { standard | extended } name { deny | permit } { commands }
ip access-list standard internetfilter
deny 172.10.15.0 0.0.0.255
permit 128.88.0.0 0.0.255.255
permit 36.0.0.0 0.0.255.255
ip access-list extended marketing-group
permit tcp any 171.69.0.0 0.255.255.255 eq telnet
deny udp any 171.69.0.0 0.255.255.255 lt 1024
Perrine modified by Brierley
04/27/15
Page 50
CCNA2 Routing
Named ACL
Module 11
A named ACL will allow the deletion of statements, but will only allow
for the statements to be inserted a the end of the list.
Perrine modified by Brierley
04/27/15
Page 51
CCNA2 Routing
Module 11
More Details
access-list 1 permit 172.16.0.0 0.0.255.255
10101100.00010000.00000000.00000000
00000000.00000000.xxxxxxxx. xxxxxxxx
10101100.00010000.xxxxxxxx. xxxxxxxx
Matched value
Incoming packet with address of 172.18.4.2. Will it be permitted?
Source :
10101100.00010010.00000100.00000010
Wildcard mask: 00000000.00000000.xxxxxxxx. xxxxxxxx
10101100.00010010.xxxxxxxx. xxxxxxxx Result
Perrine modified by Brierley
04/27/15
Page 52
CCNA2 Routing
Module 11
access-list 1 permit 172.16.0.0 0.0.255.255
10101100.00010000.00000000.00000000
00000000.00000000.xxxxxxxx. xxxxxxxx
10101100.00010000.xxxxxxxx. xxxxxxxx
Match value
Incoming packet with address of 172.18.4.2. Will it be permitted?
Source :
10101100.00010010.00000100.00000010
Wildcard mask: 00000000.00000000.xxxxxxxx. xxxxxxxx
10101100.00010010.xxxxxxxx. xxxxxxxx Result
Does the result equal the match value?
No! Hence the incoming packet will not be permitted.
Perrine modified by Brierley
04/27/15
Page 53
CCNA2 Routing
Module 11
access-list 1 permit 172.16.0.0 0.0.255.255
10101100.00010000.00000000.00000000
00000000.00000000.xxxxxxxx. xxxxxxxx
10101100.00010000.xxxxxxxx. xxxxxxxx
Match value
Incoming packet with address of 172.16.4.2. Will it be permitted?
Source :
10101100.00010000.00000100.00000010
Wildcard mask: 00000000.00000000.xxxxxxxx. xxxxxxxx
10101100.00010000.xxxxxxxx. xxxxxxxx Result
Does the result equal the match value?
Yes! Hence the incoming packet will be permitted.
Perrine modified by Brierley
04/27/15
Page 54
CCNA2 Routing
Module 11
access-list 1 permit 172.16.0.0 0.0.255.254
10101100.00010000.00000000.00000000
00000000.00000000.xxxxxxxx. xxxxxxx0
10101100.00010000.xxxxxxxx. xxxxxxx0
Matched value
Incoming packet with address of 172.16.4.1. Will it be permitted?
Source :
10101100.00010000.00000100.00000001
Wildcard mask: 00000000.00000000. xxxxxxxx. xxxxxxx0
10101100.00010000.xxxxxxxx. xxxxxxx1 Result
Incoming packet with address of 172.16.4.4. Will it be permitted?
Source :
10101100.00010000.00000100.00000100
Wildcard mask: 00000000.00000000. xxxxxxxx. xxxxxxx0
10101100.00010000. xxxxxxxx. xxxxxxx0 Result
Perrine modified by Brierley
04/27/15
Page 55
CCNA2 Routing
Module 11
access-list 1 permit 172.16.0.0 0.0.255.254
10101100.00010000.00000000.00000000
00000000.00000000.xxxxxxxx. xxxxxxx0
10101100.00010000.xxxxxxxx. xxxxxxx0
Matched value
Incoming packet with address of 172.16.4.5. Will it be permitted?
Source :
10101100.00010000.00000100.00000101
Wildcard mask: 00000000.00000000.xxxxxxxx. xxxxxxx0
10101100.00010000.xxxxxxxx. xxxxxxx1 Result
So the access list perform what operation? Permits 172.16.4.4, and denies
172.16.4.1 and 172.16.4.5
Permits all even addresses from the network 172.16.0.0
Perrine modified by Brierley
04/27/15
Page 56
CCNA2 Routing
Permit/Deny BLOCKS of addresses
Module 11
One can permit or deny a block of addresses. However, the blocks must be
a power of 2! (Example, 2, 4, 8, 16, 32, 64, 128, etc.)
When you need to specify a range of addresses, you choose the closet
block size for your needs.
You want to block access to part of network that is in the range from
198.16.99.0 through 198.16.99.7. This is a block size of 8. Hence:
198.16.99.0 0.0.0.7
Also in this case for a block of 8, the beginning address must either start at
0, 8, 16, etc.
Perrine modified by Brierley
04/27/15
Page 57
CCNA2 Routing
Permit/Deny BLOCKS of addresses
Module 11
One has a subnet whose addresses range from 200.17.2.128 to 200.17.2.191.
One wants to divide this network so the top half are permitted and the
bottom half is denied to any other network. What is the access lists?
The block range
is:
64
What is the access-list for the bottom?
access-list 101 deny ip 200.17.2.128 0.0.0.31 any
What is the access-list for the top?
access-list 101 permit ip 200.17.2.160 0.0.0.31 any
Perrine modified by Brierley
04/27/15
Page 58
CCNA2 Routing
Permit/Deny BLOCKS of addresses
Module 11
What does this do?
access-list 10 deny 200.16.88.64 0.0.0.63
Denies a block of 64 address starting at 200.16.88.64
Perrine modified by Brierley
04/27/15
Page 59
CCNA2 Routing
Virtual Terminal ACL
Module 11
You can control access via the VTY ports controlling telnet sessions
coming into the router.
You write the ACL as usual, but use access-class to apply it.
As an example:
Router(config t)# access-list 1 permit 172.16.1.0 0.0.0.255
Router(config t)# line vty 0 4
Router(config-line)# login
Router(config-line)# password cisco
Router(config-line)# access-class 1 in
Note: only numbered access lists can be applied to VTY virtual lines!
Perrine modified by Brierley
04/27/15
Page 60
CCNA2 Routing
Module 11
Established option
The establish option in an access-list used only with TCP datagrams.
There are cases when you want to stop host B from initiating a
connection with a host A while permitting A to initiate connections with
B.
establish
MacintoshSE
MacintoshSE
response
establish
Perrine modified by Brierley
04/27/15
Page 61
CCNA2 Routing
Established option
Module 11
As a practical example:
172.16.3.0
e1
e0
INTERNET
172.16.4.0
172.16.3.13
Allow host 172.16.3.13 with Internet connection, but dont allow the
internet to initialize any sessions.
Perrine modified by Brierley
04/27/15
Page 62
CCNA2 Routing
Established option
Module 11
172.16.3.0
e1
e0
INTERNET
172.16.4.0
172.16.3.13
Router(config)# int e1
Router(config-if)# ip access-group 101 in
Router(config)# access-list 101 permit tcp any 172.16.3.0 0.0.255.255
established
Perrine modified by Brierley
04/27/15
Page 63
CCNA2 Routing
Established option
Module 11
172.16.3.0
e1
e0
INTERNET
172.16.4.0
172.16.3.13
Router(config)# int e1
Router(config-if)# ip access-group 101 in
Router(config)# access-list 101 permit tcp any host 172.16.3.13 eq www established
Perrine modified by Brierley
04/27/15
Page 64
CCNA2 Routing
Established option
Module 11
172.16.3.0
e1
e0
INTERNET
172.16.4.0
172.16.3.13
Note: established argument is limited to tcp which means UDP, ICMP and all
other IP protocols will not match, and will be denied, unless specifically
allowed. Hence
Router(config)# int e1
Router(config-if)# ip access-group 101 in
Router(config)# access-list 101 permit tcp any 172.16.3.0 0.0.0.255 eq www established
Router(config)# access-list 101 permit icmp any any
Router(config)# access-list 101 permit udp any any eq 53
Perrine modified by Brierley
04/27/15
Page 65
CCNA2 Routing
Where to Place ACLs?
Module 11
ACL Rules:
Standard ACL
Place the ACL as near the destination as possible.
Extended ACL
Put the ACL as close as possible to the source
Perrine modified by Brierley
04/27/15
Page 66
CCNA2 Routing
Module 11
Access Lists
Standard
Extended
End of Session
Perrine modified by Brierley
04/27/15
Page 67
You might also like
- Maths No ProblemDocument14 pagesMaths No ProblemJamila Mammadova100% (2)
- The Rich Get Richer and The Poor Get PrisonDocument1 pageThe Rich Get Richer and The Poor Get PrisonGunasundaryChandramohanNo ratings yet
- Network Security All-in-one: ASA Firepower WSA Umbrella VPN ISE Layer 2 SecurityFrom EverandNetwork Security All-in-one: ASA Firepower WSA Umbrella VPN ISE Layer 2 SecurityNo ratings yet
- Substation Automation Systems: Design and ImplementationFrom EverandSubstation Automation Systems: Design and ImplementationRating: 4.5 out of 5 stars4.5/5 (3)
- Cisco CCNA Command Guide: An Introductory Guide for CCNA & Computer Networking Beginners: Computer Networking, #3From EverandCisco CCNA Command Guide: An Introductory Guide for CCNA & Computer Networking Beginners: Computer Networking, #3No ratings yet
- Revision Guide For Anthology TextsDocument11 pagesRevision Guide For Anthology TextsIbra Elmahdy100% (2)
- Access Control List (ACL)Document37 pagesAccess Control List (ACL)Nikhil Patel50% (2)
- Computer System Engineering Department ENCS413 Network Lab Access ListDocument13 pagesComputer System Engineering Department ENCS413 Network Lab Access Listak akNo ratings yet
- Alcatel-Lucent Service Routing Architect (SRA) Self-Study Guide: Preparing for the BGP, VPRN and Multicast ExamsFrom EverandAlcatel-Lucent Service Routing Architect (SRA) Self-Study Guide: Preparing for the BGP, VPRN and Multicast ExamsNo ratings yet
- AutomationDocument36 pagesAutomationParvez AlamNo ratings yet
- Access Control List DemonstrationDocument3 pagesAccess Control List DemonstrationJayNo ratings yet
- 4.1.4 Packet Tracer - ACL DemonstrationDocument3 pages4.1.4 Packet Tracer - ACL DemonstrationAbid EkaNo ratings yet
- Access ListsDocument6 pagesAccess ListsTheofanous ConstantinaNo ratings yet
- Packet Tracer - Access Control List Demonstration: ObjectivesDocument3 pagesPacket Tracer - Access Control List Demonstration: ObjectivesMaría ArmijosNo ratings yet
- UCCN1004 - Lect7 - ACL and Packet FilteringDocument40 pagesUCCN1004 - Lect7 - ACL and Packet FilteringVickRam RaViNo ratings yet
- Clase 17. Packet FilteringDocument70 pagesClase 17. Packet FilteringKarolina GuamanNo ratings yet
- 4.1.4 Packet Tracer - ACL Demonstration - ILMDocument3 pages4.1.4 Packet Tracer - ACL Demonstration - ILMlizardohilarioNo ratings yet
- Lab 8 Packet Tracer VersionDocument6 pagesLab 8 Packet Tracer VersionOsGuIsNo ratings yet
- 12.3.4 Packet Tracer - ACL DemonstrationDocument2 pages12.3.4 Packet Tracer - ACL DemonstrationGee CloudNo ratings yet
- CCNA Lab M4 5.5.1Document6 pagesCCNA Lab M4 5.5.1vadancorneliuNo ratings yet
- ACL2Document88 pagesACL2万尼杨No ratings yet
- Introducing ACL Operation: Access Control ListsDocument38 pagesIntroducing ACL Operation: Access Control Listsblue.jupiter9x154No ratings yet
- Ccna4 5.2.8.2 PDFDocument6 pagesCcna4 5.2.8.2 PDFUNATCONo ratings yet
- (CCNA) Cisco Commands Cheat Sheet #4 - Boubakr TechDocument3 pages(CCNA) Cisco Commands Cheat Sheet #4 - Boubakr TechJosé PedroNo ratings yet
- Modul 5 Access Control List PDFDocument48 pagesModul 5 Access Control List PDFSlamet AchwandyNo ratings yet
- UCCN1004 - Lect07 - ACL and Packet FilteringDocument63 pagesUCCN1004 - Lect07 - ACL and Packet FilteringSharanVsNo ratings yet
- Chapter 10 - Access Control ListsDocument45 pagesChapter 10 - Access Control ListstrietbuivienNo ratings yet
- Experiment#7: Access Control List Basics and Extended Ping: ObjectiveDocument4 pagesExperiment#7: Access Control List Basics and Extended Ping: ObjectiveqweqweNo ratings yet
- CCNA 4 Chapter 5 V4Document14 pagesCCNA 4 Chapter 5 V4Matthew HernandezNo ratings yet
- QuintoARonyZambrano5 4 13Document4 pagesQuintoARonyZambrano5 4 13roniakolaNo ratings yet
- 3-Access - List Ccna Security Ipv4 Ipv6Document101 pages3-Access - List Ccna Security Ipv4 Ipv6abou amer ابو عامرNo ratings yet
- 5.4.13 Packet Tracer - Configure Extended IPv4 ACLs - Scenario 2Document4 pages5.4.13 Packet Tracer - Configure Extended IPv4 ACLs - Scenario 2WerrtyNo ratings yet
- Answer CCNA Discovery 3 Ver 4 0 Chapter 8 U Can Get 90 2%Document9 pagesAnswer CCNA Discovery 3 Ver 4 0 Chapter 8 U Can Get 90 2%poentren100% (10)
- 26.2.2 Packet Tracer - Configure Extended IPv4 ACLs - Scenario 2 - ILMDocument4 pages26.2.2 Packet Tracer - Configure Extended IPv4 ACLs - Scenario 2 - ILMTRYST CHAMANo ratings yet
- Lab 1.4.3 Introductory Lab 3 - Access Control List Basics and Extended PingDocument5 pagesLab 1.4.3 Introductory Lab 3 - Access Control List Basics and Extended PingnickNo ratings yet
- Iws Lab RecordDocument50 pagesIws Lab RecordPathivadaSantoshNaiduNo ratings yet
- CCNA4CH5SGDocument4 pagesCCNA4CH5SGAustin LivengoodNo ratings yet
- (CCNA) Cisco Commands Cheat Sheet #4Document3 pages(CCNA) Cisco Commands Cheat Sheet #4Md IrfANNo ratings yet
- Soal-03 Packet Tracer - Configuring Standard ACLs - Reza Ramadhan - KeamananJaringan - ACDocument4 pagesSoal-03 Packet Tracer - Configuring Standard ACLs - Reza Ramadhan - KeamananJaringan - ACReza RamadhanNo ratings yet
- Access Control List: Topology DiagramDocument6 pagesAccess Control List: Topology DiagramsovannlyNo ratings yet
- Lab 6: Firewalls - Static Packet Filtering: 2.2 DetailsDocument25 pagesLab 6: Firewalls - Static Packet Filtering: 2.2 Detailscharles81No ratings yet
- Exercices ACLDocument9 pagesExercices ACLPapa NiangNo ratings yet
- Introducing ACL Operation: Access Control ListsDocument18 pagesIntroducing ACL Operation: Access Control Listsธนวรรณ โภคาอนนต์No ratings yet
- 5.2.2.4 Packet Tracer - ACL Demonstration - NAVALDocument3 pages5.2.2.4 Packet Tracer - ACL Demonstration - NAVALCarlo NavalNo ratings yet
- Packet Tracer - Configure Numbered Standard Ipv4 Acls: Addressing TableDocument5 pagesPacket Tracer - Configure Numbered Standard Ipv4 Acls: Addressing TableEsteban TapiaNo ratings yet
- Packet Tracer - Configure Numbered Standard Ipv4 Acls: Addressing TableDocument4 pagesPacket Tracer - Configure Numbered Standard Ipv4 Acls: Addressing TableEsteban TapiaNo ratings yet
- Lab 5.5.1: Basic Access Control Lists: Topology DiagramDocument10 pagesLab 5.5.1: Basic Access Control Lists: Topology DiagramMohammed O Baheddad0% (1)
- ACL (Access Control List)Document5 pagesACL (Access Control List)RAKIB ভাইয়োNo ratings yet
- (CCNA) Cisco Commands Cheat Sheet #4 - Boubakr TechDocument3 pages(CCNA) Cisco Commands Cheat Sheet #4 - Boubakr TechPrabhashKumarJhaNo ratings yet
- Lab Worksheet 7: Basic Access Control ListDocument5 pagesLab Worksheet 7: Basic Access Control ListCj LlemosNo ratings yet
- CCNA 2 v5.0 Routing and SwitchingDocument9 pagesCCNA 2 v5.0 Routing and SwitchingCarlos Castillo PalmaNo ratings yet
- CCNA Presentation - ACLDocument58 pagesCCNA Presentation - ACLArslanNo ratings yet
- Module 5 ACLsDocument69 pagesModule 5 ACLsCao Hồng MinhNo ratings yet
- Access Control Lists: CCNA 2 Module 11Document19 pagesAccess Control Lists: CCNA 2 Module 11AlbertoNo ratings yet
- Sybex CCNA 640-802 Chapter 12Document30 pagesSybex CCNA 640-802 Chapter 12xkerberosxNo ratings yet
- 9IP Access Control List (ACL)Document6 pages9IP Access Control List (ACL)King DeedNo ratings yet
- 9.2.1.10 Packet Tracer Configuring Standard ACLs Instructions IGDocument7 pages9.2.1.10 Packet Tracer Configuring Standard ACLs Instructions IGcamilo veraNo ratings yet
- WAN TECHNOLOGY FRAME-RELAY: An Expert's Handbook of Navigating Frame Relay NetworksFrom EverandWAN TECHNOLOGY FRAME-RELAY: An Expert's Handbook of Navigating Frame Relay NetworksNo ratings yet
- CISCO PACKET TRACER LABS: Best practice of configuring or troubleshooting NetworkFrom EverandCISCO PACKET TRACER LABS: Best practice of configuring or troubleshooting NetworkNo ratings yet
- Ethernet Networks: Design, Implementation, Operation, ManagementFrom EverandEthernet Networks: Design, Implementation, Operation, ManagementRating: 4 out of 5 stars4/5 (1)
- Network with Practical Labs Configuration: Step by Step configuration of Router and Switch configurationFrom EverandNetwork with Practical Labs Configuration: Step by Step configuration of Router and Switch configurationNo ratings yet
- Data Communication and Networking: For Under-graduate StudentsFrom EverandData Communication and Networking: For Under-graduate StudentsNo ratings yet
- Packet Tracer - Configuring VPNs (Optional)Document7 pagesPacket Tracer - Configuring VPNs (Optional)Senan AlkaabyNo ratings yet
- CSR in Aws CVDDocument50 pagesCSR in Aws CVDSenan AlkaabyNo ratings yet
- Activity 3Document5 pagesActivity 3Jose Rafael Cruz SoriagaNo ratings yet
- Integrating Active Directory With Sign-On Splash PageDocument6 pagesIntegrating Active Directory With Sign-On Splash PageSenan AlkaabyNo ratings yet
- Cisco (DMVPN) NHRP Phase 1-2-3Document9 pagesCisco (DMVPN) NHRP Phase 1-2-3Gayloard FockerNo ratings yet
- CLBADocument43 pagesCLBASenan AlkaabyNo ratings yet
- Standard ACL PracticeDocument1 pageStandard ACL PracticeSenan AlkaabyNo ratings yet
- Extended Access ListsDocument3 pagesExtended Access ListsSenan AlkaabyNo ratings yet
- By Karawan Student: 1660 9234 05-DEC-2013 09:49PM 380807927Document10 pagesBy Karawan Student: 1660 9234 05-DEC-2013 09:49PM 380807927Senan AlkaabyNo ratings yet
- Module 1 Concepts of ICT Chapter 2 HardwareDocument23 pagesModule 1 Concepts of ICT Chapter 2 HardwareSenan AlkaabyNo ratings yet
- Concepts of ICT - General ConceptsDocument9 pagesConcepts of ICT - General ConceptsSenan AlkaabyNo ratings yet
- Resume For Frame RelayDocument7 pagesResume For Frame RelaySenan AlkaabyNo ratings yet
- BB FiberOpticCommandmentsDocument4 pagesBB FiberOpticCommandmentsDand LongNo ratings yet
- Major Fractures of The Pilon The Talus and The Calcaneus Current Concepts of TreatmentDocument241 pagesMajor Fractures of The Pilon The Talus and The Calcaneus Current Concepts of TreatmentPaul Radulescu - FizioterapeutNo ratings yet
- Diasporic Writing QuestionsDocument31 pagesDiasporic Writing QuestionsMEIMOONA HUSNAIN100% (1)
- 3 - APUSH Period 8 Notes 3 - Eisenhowers Cold WarDocument60 pages3 - APUSH Period 8 Notes 3 - Eisenhowers Cold WarChrisNo ratings yet
- EBTax Tax Simulator Webcast 16 Jul 14pdfDocument49 pagesEBTax Tax Simulator Webcast 16 Jul 14pdfM.MedinaNo ratings yet
- MutamaDocument72 pagesMutamaAndrew MashavaNo ratings yet
- The Leads Science Academy: Write Short Answers of The Following QuestionsDocument2 pagesThe Leads Science Academy: Write Short Answers of The Following Questionssir zahidNo ratings yet
- Biology HL Student GuideDocument134 pagesBiology HL Student GuideYesenia JassoNo ratings yet
- Teachers Manual in Filipino 10 PDFDocument2 pagesTeachers Manual in Filipino 10 PDFIan Dagame0% (1)
- Some Remarks On Fuzzy N-Normed SpacesDocument7 pagesSome Remarks On Fuzzy N-Normed SpacesRyanEliasNo ratings yet
- Body Repairs General Body RepairsDocument87 pagesBody Repairs General Body RepairsergdegNo ratings yet
- GU 0009. Leisegang Colposcope Directions ForUseDocument44 pagesGU 0009. Leisegang Colposcope Directions ForUseGabriela Ponce GuerrerpNo ratings yet
- Short Keys f1-f12Document2 pagesShort Keys f1-f12Farhan Khan NiaZiNo ratings yet
- Forex Trade Plan ExampleDocument5 pagesForex Trade Plan ExampleNagy100% (3)
- Huff ManDocument4 pagesHuff Mangopal_svsemails8998No ratings yet
- Zapanta Vs PeopleDocument7 pagesZapanta Vs PeopleEricson Sarmiento Dela CruzNo ratings yet
- Biogas NotesDocument35 pagesBiogas NotesNupur BhadraNo ratings yet
- Problem Set No. 4 PDFDocument1 pageProblem Set No. 4 PDFKent Lawrence LordanNo ratings yet
- Advice On Effective Deposition Witness TechniquesDocument9 pagesAdvice On Effective Deposition Witness TechniquesKalbian Hagerty LLP100% (2)
- 978 1 62948 492 1 - EbookDocument221 pages978 1 62948 492 1 - EbookAmparoNo ratings yet
- RPD QuestionsDocument77 pagesRPD QuestionsDontoNo ratings yet
- Datasheet: Delastic Preformed Pavement SealsDocument1 pageDatasheet: Delastic Preformed Pavement SealsUnited Construction Est. TechnicalNo ratings yet
- Ruis LK TW Iv 2022Document157 pagesRuis LK TW Iv 2022Ragil ArdianNo ratings yet
- Chapter 1 Nature of OrganizationDocument29 pagesChapter 1 Nature of OrganizationNicole VelascoNo ratings yet
- Malaysian Online Journal of Educational Sciences: JANUARY 2021, 9Document19 pagesMalaysian Online Journal of Educational Sciences: JANUARY 2021, 9guanyitorNo ratings yet
- 1 Year Bachillerato VERB TENSES REVIEWDocument4 pages1 Year Bachillerato VERB TENSES REVIEWLucía CatalinaNo ratings yet