Professional Documents
Culture Documents
0 ratings0% found this document useful (0 votes)
8 views5 IAM Infrastructure
5 IAM Infrastructure
Uploaded by
stark ?Copyright:
© All Rights Reserved
Available Formats
Download as PPT, PDF, TXT or read online from Scribd
You might also like
- x500 NordVPN AccountsDocument18 pagesx500 NordVPN Accountsalexisduthoit09100% (1)
- AWS Partner - AWS Cloud Practitioner EssentialsDocument135 pagesAWS Partner - AWS Cloud Practitioner EssentialsSahana sonu100% (1)
- Table of Contents-DCPPDocument2 pagesTable of Contents-DCPPAAKASH BHATIANo ratings yet
- Triangle Technology Solutions LTD: To Getaway Services LTDDocument6 pagesTriangle Technology Solutions LTD: To Getaway Services LTDHerbertNo ratings yet
- FISCO BCOS GuidebookDocument24 pagesFISCO BCOS GuidebookandyhNo ratings yet
- FlexPay API v3 Subscription 1Document16 pagesFlexPay API v3 Subscription 1MihaiTanaseNo ratings yet
- Identity and Access Management Reference Architecture For Cloud ComputingDocument26 pagesIdentity and Access Management Reference Architecture For Cloud ComputingJose RosarioNo ratings yet
- 9A02503 Control SystemsDocument4 pages9A02503 Control SystemssivabharathamurthyNo ratings yet
- COIT20248 Assignment 1Document12 pagesCOIT20248 Assignment 1gouthamreddys0% (1)
- TOGAF Demystified: Course DeliveryDocument4 pagesTOGAF Demystified: Course DeliveryRajesh SaxenaNo ratings yet
- CT Dec 2011Document3 pagesCT Dec 2011vpj100No ratings yet
- Report GDPRDocument36 pagesReport GDPRZalonsoNo ratings yet
- Merger of Mahindra SatyamDocument17 pagesMerger of Mahindra SatyamMerlyn Coelho100% (1)
- Regulatory Framework of M&ADocument136 pagesRegulatory Framework of M&ARishabh KatyalNo ratings yet
- Generic Data Processing Systems ListV1 - 19feb2018Document16 pagesGeneric Data Processing Systems ListV1 - 19feb2018DELACRUZNo ratings yet
- Labview Core 2 Course Manual: Instruments Not For DistributionDocument134 pagesLabview Core 2 Course Manual: Instruments Not For DistributionJUAN CARLOS ALVAREZ TREJONo ratings yet
- Eidas Regulation v2 16524Document8 pagesEidas Regulation v2 16524Traducător Autorizat Marilena IordacheNo ratings yet
- Pci-Dss What Does It Mean To Me?: Presented byDocument10 pagesPci-Dss What Does It Mean To Me?: Presented byWes LDNo ratings yet
- PCI DSS Virtualization Guidelines: Information SupplementDocument39 pagesPCI DSS Virtualization Guidelines: Information Supplementcamy0529No ratings yet
- ACM - A Review On Cloud SecurityDocument5 pagesACM - A Review On Cloud SecuritytueurNo ratings yet
- Information Security Management System Analysis and Solutions For Ux UniversityDocument31 pagesInformation Security Management System Analysis and Solutions For Ux UniversityPrajeev PjNo ratings yet
- BDO Assessment Report 2020Document69 pagesBDO Assessment Report 2020Nahida wahediNo ratings yet
- Preview: Comptia Network+ Instructor'S EditionDocument144 pagesPreview: Comptia Network+ Instructor'S EditionAdrian NicolaeNo ratings yet
- Blockchains Era For Public Health@PakistanDocument33 pagesBlockchains Era For Public Health@PakistanOlivia NicoleNo ratings yet
- PCX 951 UserGuide enDocument196 pagesPCX 951 UserGuide enshankari24381No ratings yet
- Hipaa and Hitech Act: Compliance GuideDocument28 pagesHipaa and Hitech Act: Compliance GuideonlysubasNo ratings yet
- Chief Information Officer CIO in London, UK ResumeDocument3 pagesChief Information Officer CIO in London, UK ResumeRCTBLPONo ratings yet
- Identity and Access Management SuiteDocument2 pagesIdentity and Access Management SuiteVladan DabovicNo ratings yet
- Implementation and Performance Evaluation of Load Balanced Routing in SDN Based Fat Tree Data CenterDocument6 pagesImplementation and Performance Evaluation of Load Balanced Routing in SDN Based Fat Tree Data Center23206051025No ratings yet
- SACS-003 Cloud Cybersecuirty StandardDocument8 pagesSACS-003 Cloud Cybersecuirty StandardimohammadtariqueNo ratings yet
- TCS Connected Universe Platform - 060918Document4 pagesTCS Connected Universe Platform - 060918abhishek tripathyNo ratings yet
- Serio Availability ManagementDocument18 pagesSerio Availability ManagementDang Ngoc TrungNo ratings yet
- Gartner MQ Data Centre Outsourcing & Infrastructure Utility Services - EuropeDocument38 pagesGartner MQ Data Centre Outsourcing & Infrastructure Utility Services - EuroperossloveladyNo ratings yet
- Teleworking PolicyDocument3 pagesTeleworking Policys.hakimNo ratings yet
- Acquisitions Chart OverviewDocument33 pagesAcquisitions Chart OverviewMelissa AbelNo ratings yet
- HTTP Based File Transfer PatternDocument5 pagesHTTP Based File Transfer PatternAdam NemethNo ratings yet
- Note Assess ReportDocument7 pagesNote Assess Reporten ziaNo ratings yet
- Securosis Secrets Management JAN2018 FINALDocument20 pagesSecurosis Secrets Management JAN2018 FINALSalah AyoubiNo ratings yet
- EX602Document25 pagesEX602jeetendrasidhiNo ratings yet
- PII 30 Minute PresentationDocument19 pagesPII 30 Minute PresentationWalterClayNo ratings yet
- Capability Maturity ModelDocument12 pagesCapability Maturity ModelAnonymous QEcQfTeHlNo ratings yet
- Chapter 2 BlockchainDocument7 pagesChapter 2 BlockchainFarheen AkramNo ratings yet
- Azure Enterprise-Ready NetworkingDocument42 pagesAzure Enterprise-Ready NetworkingspringleeNo ratings yet
- ISO27k Awareness PresentationDocument41 pagesISO27k Awareness PresentationGen VagulaNo ratings yet
- C P Ob Og 2017Document15 pagesC P Ob Og 2017Madhur ChopraNo ratings yet
- FIM White Paper Identity Federation ConceptsDocument36 pagesFIM White Paper Identity Federation ConceptskingnachiNo ratings yet
- Statement of ApplicabilityDocument17 pagesStatement of ApplicabilityMbg ShankarNo ratings yet
- Tickmill LTD Seychelles Privacy PolicyDocument11 pagesTickmill LTD Seychelles Privacy PolicyJalil MochlasNo ratings yet
- Compliance Policy: Antares Systems LimitedDocument10 pagesCompliance Policy: Antares Systems LimitedUsha SNo ratings yet
- Policy Development & The 4 Cobit Domain ProcessesDocument18 pagesPolicy Development & The 4 Cobit Domain ProcessesJasper Bollen100% (1)
- A Report On "Financial Statement Analysis of Yes Bank Limited"Document80 pagesA Report On "Financial Statement Analysis of Yes Bank Limited"Vipul GargNo ratings yet
- Unit 2 Part 2Document41 pagesUnit 2 Part 2Abhishek SrivastavaNo ratings yet
- Org Blockchain-Based Electronic Health Records Management A Comprehensive Review and Future Research DirectionDocument22 pagesOrg Blockchain-Based Electronic Health Records Management A Comprehensive Review and Future Research DirectionMarkho Llallihuaman HuaneNo ratings yet
- RusecDocument522 pagesRusecGeoff ZinderdineNo ratings yet
- Protecting Security of Assets: Domain 2Document24 pagesProtecting Security of Assets: Domain 2Tushita GovindarajNo ratings yet
- GDPR For The Oracle DBADocument34 pagesGDPR For The Oracle DBAAbraham Dev PrasadNo ratings yet
- DPA Presentation - OrientationDocument72 pagesDPA Presentation - OrientationpiapetitaNo ratings yet
- Project Proposal: Product Name: ERM (Electronic Medical Record)Document4 pagesProject Proposal: Product Name: ERM (Electronic Medical Record)Habib SheikhNo ratings yet
- Problems Mergers and AcquisitionDocument12 pagesProblems Mergers and AcquisitionSana SarfarazNo ratings yet
- IT Infrastructure Deployment A Complete Guide - 2020 EditionFrom EverandIT Infrastructure Deployment A Complete Guide - 2020 EditionNo ratings yet
- Az 104Document298 pagesAz 104ISLEM GHOUMA100% (1)
- The Openid Connect Handbook v1Document45 pagesThe Openid Connect Handbook v1Juan Sebastian Romero FernandezNo ratings yet
- Id With QR Code Bn1 SampleDocument3 pagesId With QR Code Bn1 SampleMichael Bong GabatNo ratings yet
- Formative Paper AssignmentDocument6 pagesFormative Paper AssignmentAnnie JonesNo ratings yet
- SN EssDocument1 pageSN EssCnopsize AzaNo ratings yet
- Layxu Nlrkost%: A. User Basic DetailsDocument1 pageLayxu Nlrkost%: A. User Basic Detailssunil hinukaleNo ratings yet
- NxstyyywasrawrarwarDocument2 pagesNxstyyywasrawrarwarKrzysztof TadeusiakNo ratings yet
- Mod 1-10 QuizDocument26 pagesMod 1-10 QuizDensolusNo ratings yet
- Calling Script FlipkartDocument2 pagesCalling Script Flipkartminazabbasi130No ratings yet
- Preparing For PCA WorkbookDocument87 pagesPreparing For PCA WorkbookThomas YosefNo ratings yet
- Mapping On Prem Cloud v4Document45 pagesMapping On Prem Cloud v4Wael HAMDINo ratings yet
- Authentication and Authorization Interview QuestionDocument1 pageAuthentication and Authorization Interview QuestionAnna MalaiNo ratings yet
- Sap Netweaver Identity Management Security GuideDocument25 pagesSap Netweaver Identity Management Security Guidekumar.indianNo ratings yet
- Adm Circular DegpDocument3 pagesAdm Circular DegpsasnewidNo ratings yet
- TOC - GCP Cloud Architect (Advanced) - 3 DaysDocument4 pagesTOC - GCP Cloud Architect (Advanced) - 3 Daysilyas2sapNo ratings yet
- The Forrester Wave™: Cloud Workload Security, Q1 2024Document2 pagesThe Forrester Wave™: Cloud Workload Security, Q1 2024sebastienNo ratings yet
- OCI Foundations QnADocument14 pagesOCI Foundations QnAikrudisNo ratings yet
- CDL Exam Test 01Document23 pagesCDL Exam Test 01Dies IraeNo ratings yet
- FGT1 04 Firewall AuthenticationDocument42 pagesFGT1 04 Firewall AuthenticationAnca Floriana RaduNo ratings yet
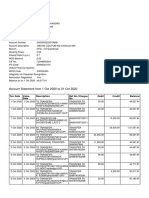
- Account Statement From 1 Oct 2020 To 31 Oct 2020: TXN Date Value Date Description Ref No./Cheque No. Debit Credit BalanceDocument3 pagesAccount Statement From 1 Oct 2020 To 31 Oct 2020: TXN Date Value Date Description Ref No./Cheque No. Debit Credit BalanceJayachandra JcNo ratings yet
- Prisma Cloud IAM Security - AssessmentDocument5 pagesPrisma Cloud IAM Security - Assessmentkya1005No ratings yet
- 5yucujj - GhostbinDocument6 pages5yucujj - GhostbinAndy MartinNo ratings yet
- Data DictionaryDocument5 pagesData DictionaryEric P. PobleteNo ratings yet
- ICT Security Policy PDFDocument39 pagesICT Security Policy PDFSamaira KhanNo ratings yet
- 1 Information Security Fundamentals 27-04-2023Document122 pages1 Information Security Fundamentals 27-04-2023Dipanshu MandalNo ratings yet
- Mock Test Qs For Professional Certification 2Document137 pagesMock Test Qs For Professional Certification 2Pradip RoychowdhuryNo ratings yet
- Manual Pengguna - Penetapan Semula Kata Laluan Active Directory (AD)Document19 pagesManual Pengguna - Penetapan Semula Kata Laluan Active Directory (AD)mohdzakimustaphaNo ratings yet
- 06-01-2024Document10 pages06-01-2024anabstpNo ratings yet
5 IAM Infrastructure
5 IAM Infrastructure
Uploaded by
stark ?0 ratings0% found this document useful (0 votes)
8 views11 pagesOriginal Title
5_IAM_Infrastructure.ppt
Copyright
© © All Rights Reserved
Available Formats
PPT, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as PPT, PDF, TXT or read online from Scribd
Download as ppt, pdf, or txt
0 ratings0% found this document useful (0 votes)
8 views11 pages5 IAM Infrastructure
5 IAM Infrastructure
Uploaded by
stark ?Copyright:
© All Rights Reserved
Available Formats
Download as PPT, PDF, TXT or read online from Scribd
Download as ppt, pdf, or txt
You are on page 1of 11
IAM Infrastructure
Introduction
• Security administrators have traditionally been concerned
with managing the identities of and controlling access for the
people that are part of or interact with their technology
infrastructure.
• Relatively recently, the concept of bring your own device
(BYOD) was introduced, which allowed authorized
individuals to associate mobile phones or laptops with their
corporate account to receive network services on their
personal devices.
Introduction contd...
• The IoT introduces a much richer connectivity environment than
BYOD.
• Many more IoT devices are expected to be deployed throughout an
organization than the usual one or two mobile phones or laptops
for each employee.
• IAM infrastructures must be designed to scale to the number of
devices that an organization will eventually support, potentially
orders of magnitude higher than today.
• New IoT subsystems will continually be added to an organization as
new capabilities arise to enable and streamline business processes.
IoT IAM
• IoT IAM is one aspect of an overarching security
program that must be designed to mitigate this
dynamic new environment where:
• New devices can be securely added to the network at
a rapid pace and for diverse functions.
• Data and even devices can share not only within the
organization but with other organizations.
• Privacy is maintained despite consumer data being
collected, stored, and frequently shared with others.
Holistic IAM program for IoT
The identity lifecycle
• The identity lifecycle for an IoT device begins with defining the naming
conventions for the device; it ends with the removal of the device's identity from
the system. The following figure provides a view of the process flow:
• This lifecycle procedure should be established and applied to
all IoT devices that are procured, configured, and ultimately
attached to an organization's network.
• The first aspect requires a coordinated understanding of the
categories of IoT devices and systems that will be introduced
within your organization, both now and in the future.
• Establishing a structured identity namespace will significantly
help manage the identities of the thousands or millions of
devices that will eventually be added to your organization.
Digital certificates
• Public key-based digital certificates are a preferred
method for providing authentication functionality in
the IoT.
• Certificates come with a highly organized hierarchical
naming structure that consists of organization,
organizational unit(s), and distinguished names (DN)
or common names (CN).
Authorization and access control within
publish/subscribe protocols
• The MQTT protocol provides a good exemplar for
understanding the need for finer-grained access
controls. As a publish/subscribe protocol, MQTT
allows clients to write and read topics. Not all clients
will have permissions to write all topics.
• Not all clients will have permissions to read all topics
either. Indeed, controls must be put in place that
restrict the permissions of clients at the topic level.
Identity and Access Management Solutions for the IoT
• This can be achieved in a MQTT broker by keeping an access control
list that pairs
topics with authorized publishers and authorized subscribers.
• The access controls can take as input the client ID of the MQTT
client, or depending on the broker implementation, the username
that is transmitted in the MQTT connect message.
• The broker performs a topic lookup when applicable MQTT
messages arrive to determine if the clients are authorized to read,
write, or subscribe to topics.
• Alternatively, since MQTT is often implemented to operate over
TLS, it is possible to configure the MQTT broker to require
certificate-based authentication of the MQTT client.
• The MQTT broker can then perform a mapping of information in
the MQTT client X.509 certificate to determine the topics to which
the client has permission to subscribe or publish.
Access controls within communication
protocols
• There are different access control configurations that can be set in
other communication protocols as well. For example, ZigBee
includes the ability for each transceiver to manage an access
control list to determine whether a neighbor is trusted or not.
• The ACL includes information such as the address of the neighbor
node, the security policy in use by the node, the key, and the last
initialization vector (IV) used.
• Upon receiving a packet from a neighbor node, the receiver
consults the ACL and if the neighbor is trusted, then the
communication is allowed. If not, the communication is either
denied or an authentication function is invoked.
You might also like
- x500 NordVPN AccountsDocument18 pagesx500 NordVPN Accountsalexisduthoit09100% (1)
- AWS Partner - AWS Cloud Practitioner EssentialsDocument135 pagesAWS Partner - AWS Cloud Practitioner EssentialsSahana sonu100% (1)
- Table of Contents-DCPPDocument2 pagesTable of Contents-DCPPAAKASH BHATIANo ratings yet
- Triangle Technology Solutions LTD: To Getaway Services LTDDocument6 pagesTriangle Technology Solutions LTD: To Getaway Services LTDHerbertNo ratings yet
- FISCO BCOS GuidebookDocument24 pagesFISCO BCOS GuidebookandyhNo ratings yet
- FlexPay API v3 Subscription 1Document16 pagesFlexPay API v3 Subscription 1MihaiTanaseNo ratings yet
- Identity and Access Management Reference Architecture For Cloud ComputingDocument26 pagesIdentity and Access Management Reference Architecture For Cloud ComputingJose RosarioNo ratings yet
- 9A02503 Control SystemsDocument4 pages9A02503 Control SystemssivabharathamurthyNo ratings yet
- COIT20248 Assignment 1Document12 pagesCOIT20248 Assignment 1gouthamreddys0% (1)
- TOGAF Demystified: Course DeliveryDocument4 pagesTOGAF Demystified: Course DeliveryRajesh SaxenaNo ratings yet
- CT Dec 2011Document3 pagesCT Dec 2011vpj100No ratings yet
- Report GDPRDocument36 pagesReport GDPRZalonsoNo ratings yet
- Merger of Mahindra SatyamDocument17 pagesMerger of Mahindra SatyamMerlyn Coelho100% (1)
- Regulatory Framework of M&ADocument136 pagesRegulatory Framework of M&ARishabh KatyalNo ratings yet
- Generic Data Processing Systems ListV1 - 19feb2018Document16 pagesGeneric Data Processing Systems ListV1 - 19feb2018DELACRUZNo ratings yet
- Labview Core 2 Course Manual: Instruments Not For DistributionDocument134 pagesLabview Core 2 Course Manual: Instruments Not For DistributionJUAN CARLOS ALVAREZ TREJONo ratings yet
- Eidas Regulation v2 16524Document8 pagesEidas Regulation v2 16524Traducător Autorizat Marilena IordacheNo ratings yet
- Pci-Dss What Does It Mean To Me?: Presented byDocument10 pagesPci-Dss What Does It Mean To Me?: Presented byWes LDNo ratings yet
- PCI DSS Virtualization Guidelines: Information SupplementDocument39 pagesPCI DSS Virtualization Guidelines: Information Supplementcamy0529No ratings yet
- ACM - A Review On Cloud SecurityDocument5 pagesACM - A Review On Cloud SecuritytueurNo ratings yet
- Information Security Management System Analysis and Solutions For Ux UniversityDocument31 pagesInformation Security Management System Analysis and Solutions For Ux UniversityPrajeev PjNo ratings yet
- BDO Assessment Report 2020Document69 pagesBDO Assessment Report 2020Nahida wahediNo ratings yet
- Preview: Comptia Network+ Instructor'S EditionDocument144 pagesPreview: Comptia Network+ Instructor'S EditionAdrian NicolaeNo ratings yet
- Blockchains Era For Public Health@PakistanDocument33 pagesBlockchains Era For Public Health@PakistanOlivia NicoleNo ratings yet
- PCX 951 UserGuide enDocument196 pagesPCX 951 UserGuide enshankari24381No ratings yet
- Hipaa and Hitech Act: Compliance GuideDocument28 pagesHipaa and Hitech Act: Compliance GuideonlysubasNo ratings yet
- Chief Information Officer CIO in London, UK ResumeDocument3 pagesChief Information Officer CIO in London, UK ResumeRCTBLPONo ratings yet
- Identity and Access Management SuiteDocument2 pagesIdentity and Access Management SuiteVladan DabovicNo ratings yet
- Implementation and Performance Evaluation of Load Balanced Routing in SDN Based Fat Tree Data CenterDocument6 pagesImplementation and Performance Evaluation of Load Balanced Routing in SDN Based Fat Tree Data Center23206051025No ratings yet
- SACS-003 Cloud Cybersecuirty StandardDocument8 pagesSACS-003 Cloud Cybersecuirty StandardimohammadtariqueNo ratings yet
- TCS Connected Universe Platform - 060918Document4 pagesTCS Connected Universe Platform - 060918abhishek tripathyNo ratings yet
- Serio Availability ManagementDocument18 pagesSerio Availability ManagementDang Ngoc TrungNo ratings yet
- Gartner MQ Data Centre Outsourcing & Infrastructure Utility Services - EuropeDocument38 pagesGartner MQ Data Centre Outsourcing & Infrastructure Utility Services - EuroperossloveladyNo ratings yet
- Teleworking PolicyDocument3 pagesTeleworking Policys.hakimNo ratings yet
- Acquisitions Chart OverviewDocument33 pagesAcquisitions Chart OverviewMelissa AbelNo ratings yet
- HTTP Based File Transfer PatternDocument5 pagesHTTP Based File Transfer PatternAdam NemethNo ratings yet
- Note Assess ReportDocument7 pagesNote Assess Reporten ziaNo ratings yet
- Securosis Secrets Management JAN2018 FINALDocument20 pagesSecurosis Secrets Management JAN2018 FINALSalah AyoubiNo ratings yet
- EX602Document25 pagesEX602jeetendrasidhiNo ratings yet
- PII 30 Minute PresentationDocument19 pagesPII 30 Minute PresentationWalterClayNo ratings yet
- Capability Maturity ModelDocument12 pagesCapability Maturity ModelAnonymous QEcQfTeHlNo ratings yet
- Chapter 2 BlockchainDocument7 pagesChapter 2 BlockchainFarheen AkramNo ratings yet
- Azure Enterprise-Ready NetworkingDocument42 pagesAzure Enterprise-Ready NetworkingspringleeNo ratings yet
- ISO27k Awareness PresentationDocument41 pagesISO27k Awareness PresentationGen VagulaNo ratings yet
- C P Ob Og 2017Document15 pagesC P Ob Og 2017Madhur ChopraNo ratings yet
- FIM White Paper Identity Federation ConceptsDocument36 pagesFIM White Paper Identity Federation ConceptskingnachiNo ratings yet
- Statement of ApplicabilityDocument17 pagesStatement of ApplicabilityMbg ShankarNo ratings yet
- Tickmill LTD Seychelles Privacy PolicyDocument11 pagesTickmill LTD Seychelles Privacy PolicyJalil MochlasNo ratings yet
- Compliance Policy: Antares Systems LimitedDocument10 pagesCompliance Policy: Antares Systems LimitedUsha SNo ratings yet
- Policy Development & The 4 Cobit Domain ProcessesDocument18 pagesPolicy Development & The 4 Cobit Domain ProcessesJasper Bollen100% (1)
- A Report On "Financial Statement Analysis of Yes Bank Limited"Document80 pagesA Report On "Financial Statement Analysis of Yes Bank Limited"Vipul GargNo ratings yet
- Unit 2 Part 2Document41 pagesUnit 2 Part 2Abhishek SrivastavaNo ratings yet
- Org Blockchain-Based Electronic Health Records Management A Comprehensive Review and Future Research DirectionDocument22 pagesOrg Blockchain-Based Electronic Health Records Management A Comprehensive Review and Future Research DirectionMarkho Llallihuaman HuaneNo ratings yet
- RusecDocument522 pagesRusecGeoff ZinderdineNo ratings yet
- Protecting Security of Assets: Domain 2Document24 pagesProtecting Security of Assets: Domain 2Tushita GovindarajNo ratings yet
- GDPR For The Oracle DBADocument34 pagesGDPR For The Oracle DBAAbraham Dev PrasadNo ratings yet
- DPA Presentation - OrientationDocument72 pagesDPA Presentation - OrientationpiapetitaNo ratings yet
- Project Proposal: Product Name: ERM (Electronic Medical Record)Document4 pagesProject Proposal: Product Name: ERM (Electronic Medical Record)Habib SheikhNo ratings yet
- Problems Mergers and AcquisitionDocument12 pagesProblems Mergers and AcquisitionSana SarfarazNo ratings yet
- IT Infrastructure Deployment A Complete Guide - 2020 EditionFrom EverandIT Infrastructure Deployment A Complete Guide - 2020 EditionNo ratings yet
- Az 104Document298 pagesAz 104ISLEM GHOUMA100% (1)
- The Openid Connect Handbook v1Document45 pagesThe Openid Connect Handbook v1Juan Sebastian Romero FernandezNo ratings yet
- Id With QR Code Bn1 SampleDocument3 pagesId With QR Code Bn1 SampleMichael Bong GabatNo ratings yet
- Formative Paper AssignmentDocument6 pagesFormative Paper AssignmentAnnie JonesNo ratings yet
- SN EssDocument1 pageSN EssCnopsize AzaNo ratings yet
- Layxu Nlrkost%: A. User Basic DetailsDocument1 pageLayxu Nlrkost%: A. User Basic Detailssunil hinukaleNo ratings yet
- NxstyyywasrawrarwarDocument2 pagesNxstyyywasrawrarwarKrzysztof TadeusiakNo ratings yet
- Mod 1-10 QuizDocument26 pagesMod 1-10 QuizDensolusNo ratings yet
- Calling Script FlipkartDocument2 pagesCalling Script Flipkartminazabbasi130No ratings yet
- Preparing For PCA WorkbookDocument87 pagesPreparing For PCA WorkbookThomas YosefNo ratings yet
- Mapping On Prem Cloud v4Document45 pagesMapping On Prem Cloud v4Wael HAMDINo ratings yet
- Authentication and Authorization Interview QuestionDocument1 pageAuthentication and Authorization Interview QuestionAnna MalaiNo ratings yet
- Sap Netweaver Identity Management Security GuideDocument25 pagesSap Netweaver Identity Management Security Guidekumar.indianNo ratings yet
- Adm Circular DegpDocument3 pagesAdm Circular DegpsasnewidNo ratings yet
- TOC - GCP Cloud Architect (Advanced) - 3 DaysDocument4 pagesTOC - GCP Cloud Architect (Advanced) - 3 Daysilyas2sapNo ratings yet
- The Forrester Wave™: Cloud Workload Security, Q1 2024Document2 pagesThe Forrester Wave™: Cloud Workload Security, Q1 2024sebastienNo ratings yet
- OCI Foundations QnADocument14 pagesOCI Foundations QnAikrudisNo ratings yet
- CDL Exam Test 01Document23 pagesCDL Exam Test 01Dies IraeNo ratings yet
- FGT1 04 Firewall AuthenticationDocument42 pagesFGT1 04 Firewall AuthenticationAnca Floriana RaduNo ratings yet
- Account Statement From 1 Oct 2020 To 31 Oct 2020: TXN Date Value Date Description Ref No./Cheque No. Debit Credit BalanceDocument3 pagesAccount Statement From 1 Oct 2020 To 31 Oct 2020: TXN Date Value Date Description Ref No./Cheque No. Debit Credit BalanceJayachandra JcNo ratings yet
- Prisma Cloud IAM Security - AssessmentDocument5 pagesPrisma Cloud IAM Security - Assessmentkya1005No ratings yet
- 5yucujj - GhostbinDocument6 pages5yucujj - GhostbinAndy MartinNo ratings yet
- Data DictionaryDocument5 pagesData DictionaryEric P. PobleteNo ratings yet
- ICT Security Policy PDFDocument39 pagesICT Security Policy PDFSamaira KhanNo ratings yet
- 1 Information Security Fundamentals 27-04-2023Document122 pages1 Information Security Fundamentals 27-04-2023Dipanshu MandalNo ratings yet
- Mock Test Qs For Professional Certification 2Document137 pagesMock Test Qs For Professional Certification 2Pradip RoychowdhuryNo ratings yet
- Manual Pengguna - Penetapan Semula Kata Laluan Active Directory (AD)Document19 pagesManual Pengguna - Penetapan Semula Kata Laluan Active Directory (AD)mohdzakimustaphaNo ratings yet
- 06-01-2024Document10 pages06-01-2024anabstpNo ratings yet